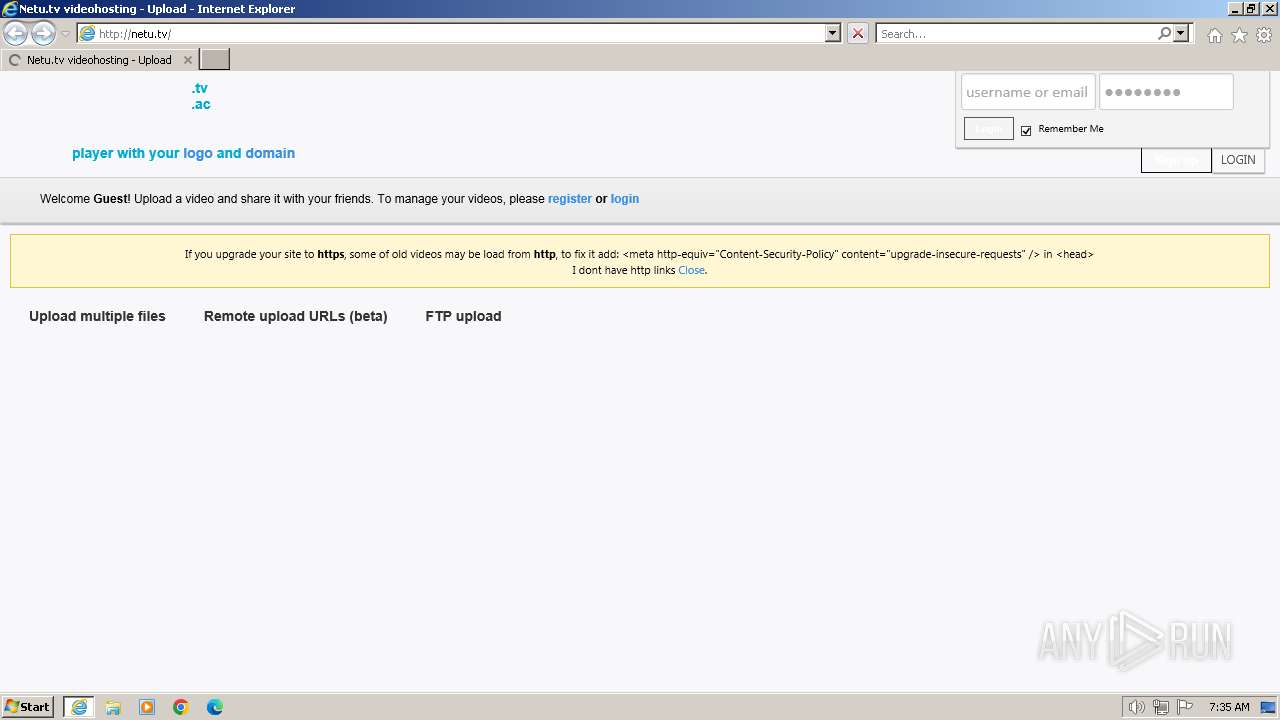
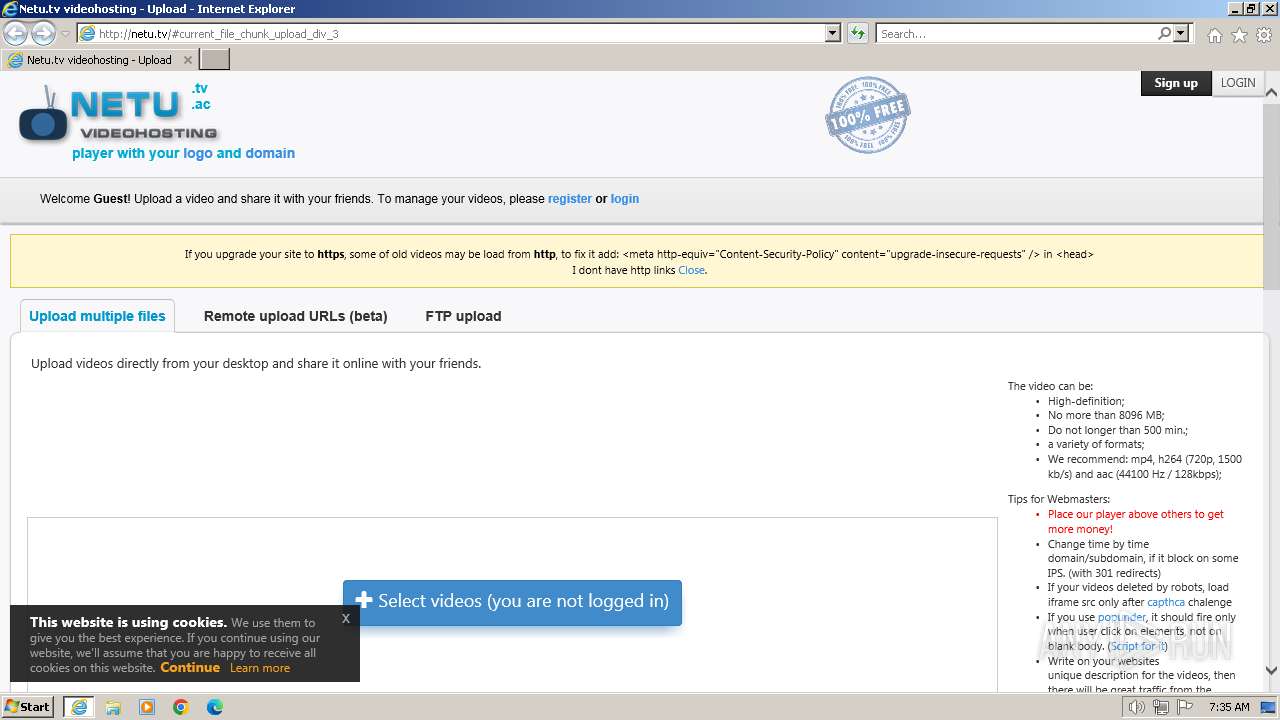
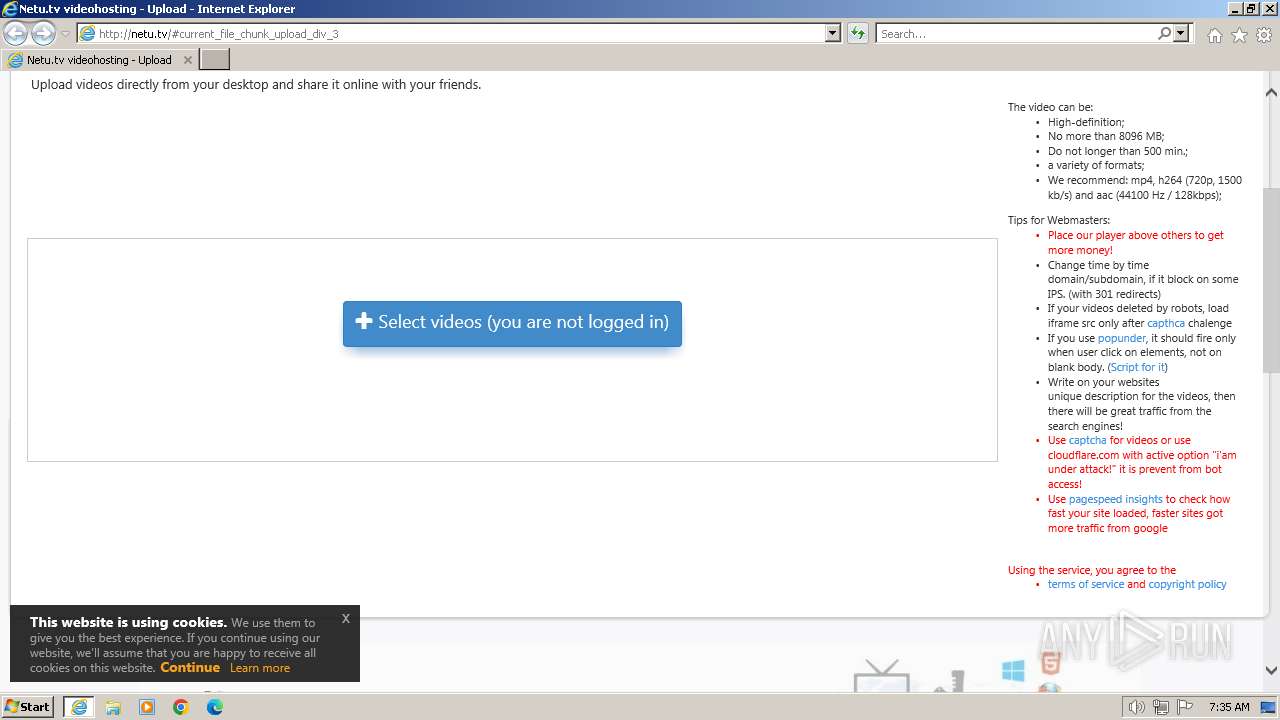
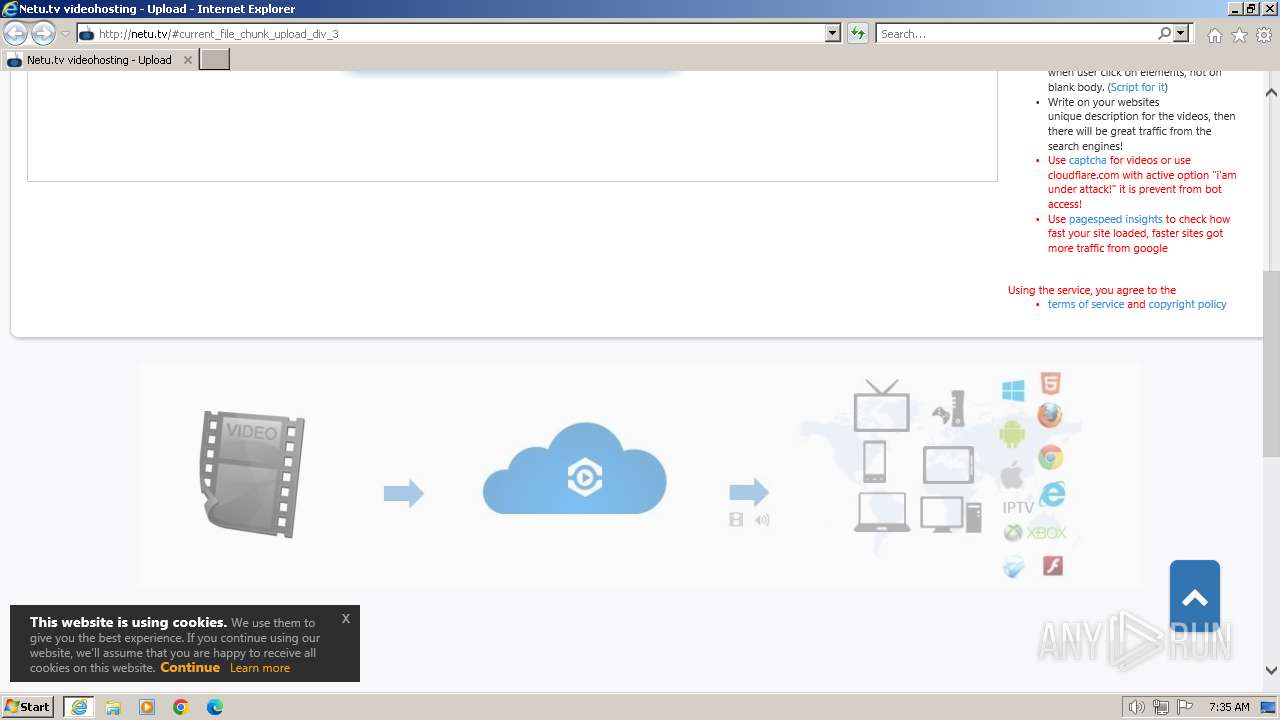
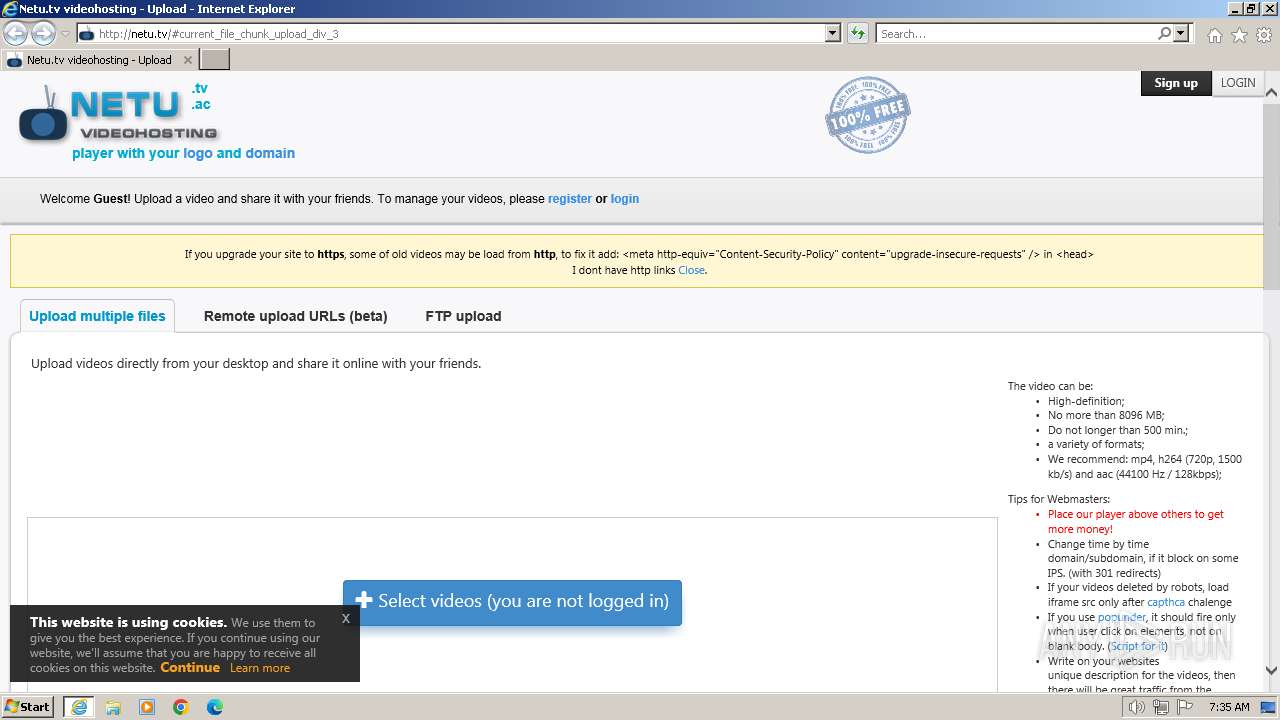
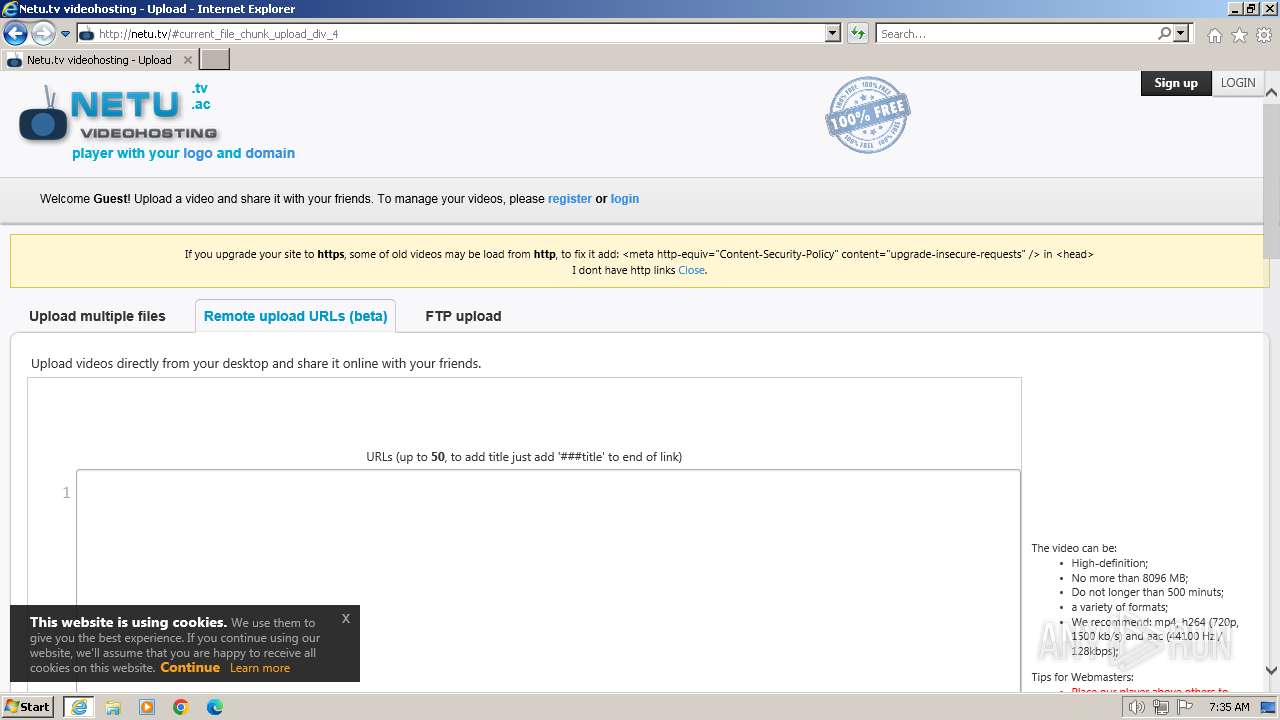
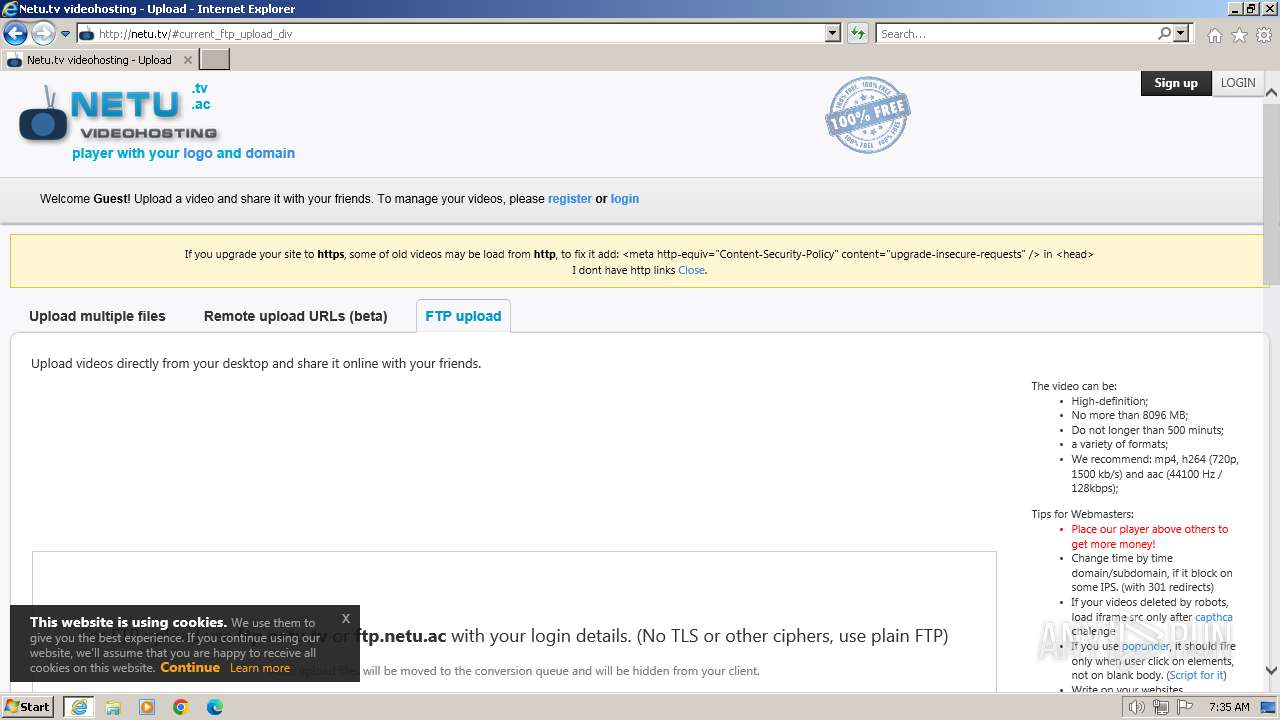
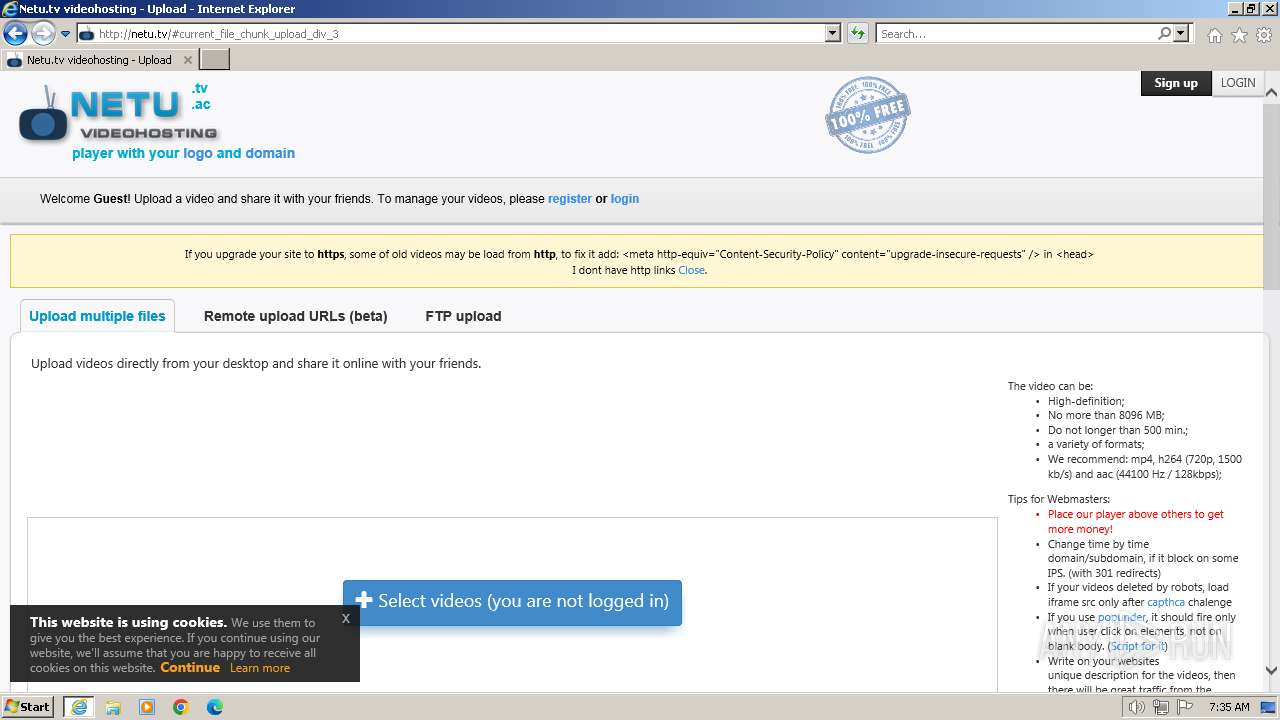
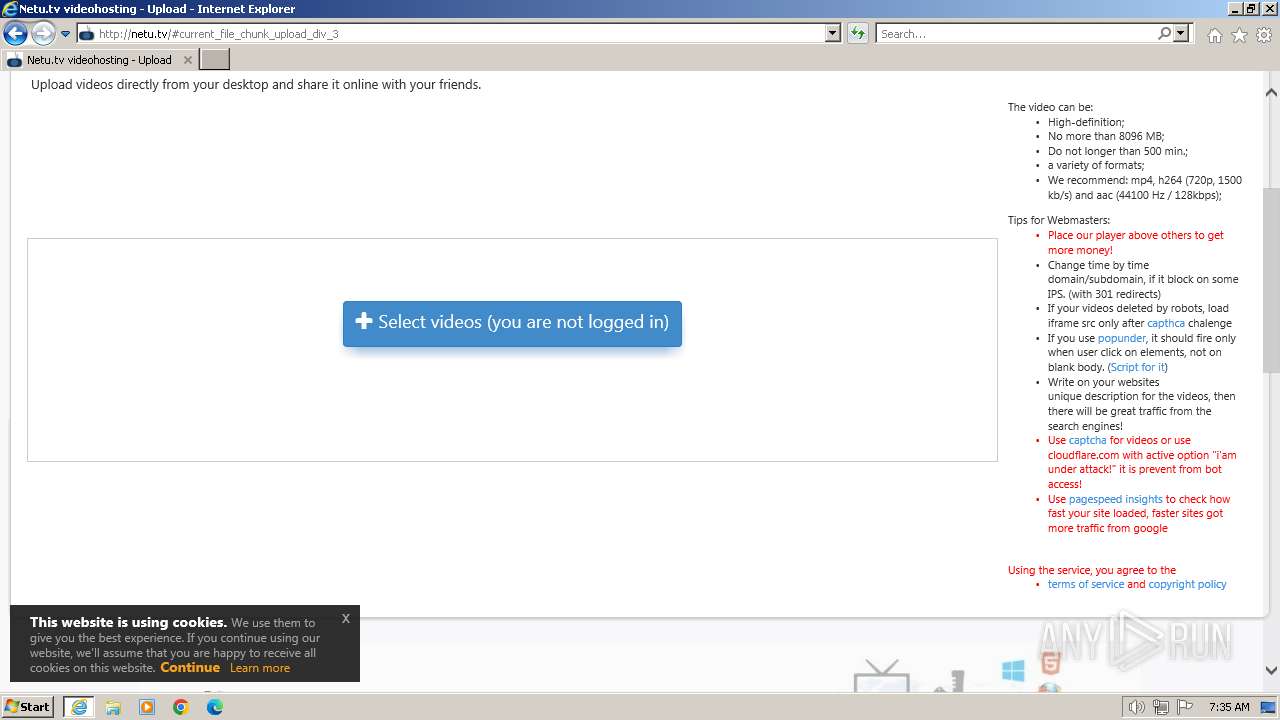
| URL: | netu.tv |
| Full analysis: | https://app.any.run/tasks/9aa7a5c3-5cac-4338-920a-19302bdd8bad |
| Verdict: | Malicious activity |
| Analysis date: | January 11, 2024, 07:35:26 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | CE1C68D1AEEAF56E3E9D13A967D4202B |
| SHA1: | F486218EA0BFD6EA25582349D9E4112054ACE84E |
| SHA256: | CFC7BE6F799C4EC5D4FD46F2005FD45040FC951810CFAD23A7161F5B4818CD27 |
| SSDEEP: | 3:ZRTn:L |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
The process uses the downloaded file
- FlashUtil32_32_0_0_453_ActiveX.exe (PID: 452)
Application launched itself
- iexplore.exe (PID: 116)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
37
Monitored processes
3
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 116 | "C:\Program Files\Internet Explorer\iexplore.exe" "netu.tv" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 296 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:116 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 452 | C:\Windows\system32\Macromed\Flash\FlashUtil32_32_0_0_453_ActiveX.exe -Embedding | C:\Windows\System32\Macromed\Flash\FlashUtil32_32_0_0_453_ActiveX.exe | — | svchost.exe | |||||||||||
User: admin Company: Adobe Integrity Level: MEDIUM Description: Adobe® Flash® Player Installer/Uninstaller 32.0 r0 Exit code: 0 Version: 32,0,0,453 Modules
| |||||||||||||||
Total events
75 921
Read events
75 812
Write events
107
Delete events
2
Modification events
| (PID) Process: | (116) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 0 | |||
| (PID) Process: | (116) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30847387 | |||
| (PID) Process: | (116) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30847437 | |||
| (PID) Process: | (116) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (116) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (116) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (116) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (116) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (116) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (116) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
0
Suspicious files
157
Text files
255
Unknown types
8
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 296 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\3XG1DOXF.htm | html | |
MD5:658E6C623E3C2900C82CD433D1B27393 | SHA256:237A2805D81F94D8E5128E687BDF062E4F8A738FEFDC7AE8E5DC8DDA54B3C555 | |||
| 296 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5IWPIAR9\font-awesome.min[1].css | text | |
MD5:4FBD15CB6047AF93373F4F895639C8BF | SHA256:DDD92F10AD162C7449EFF0ACAF40598C05B1111739587EDB75E5326B6697C5D5 | |||
| 296 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\YTOWV792\jquery_ui[1].css | text | |
MD5:838C84DC66BF63DF6592BFDB73372AC2 | SHA256:9096D2488EB9AA69A1C465D68D53394E9BA23C211DED78DFA2ED2E6FAEFAF638 | |||
| 296 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\blueimp-gallery.min[1].css | text | |
MD5:B47F312315EA584CEA38C2EC2861D845 | SHA256:D0A700A27646235F3BDA958B00968FF4DA460C1BA632A4F79D4BF42FF9FD4E3D | |||
| 296 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\dropdowns-enhancement[1].css | text | |
MD5:2E4768ED1D8B5A80FE042D1E30A816B4 | SHA256:885D22D6FCB9F7F069F5D591F3E61DD7A53D47F889E7A6F0378A697B09CA841F | |||
| 296 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\sweetalert2@10[1] | text | |
MD5:FDA44910DEB1A460BE4AC5D56D61D837 | SHA256:933B971C6388D594A23FA1559825DB5BEC8ADE2DB1240AA8FC9D0C684949E8C9 | |||
| 296 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\swfobject[1].js | text | |
MD5:892A543F3ABB54E8EC1ADA55BE3B0649 | SHA256:8677971B119CCDB82AF697FF0E08F218490D15116F221D44301F1CC8797E67D4 | |||
| 296 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\counter[1].css | text | |
MD5:2B9A882614641AE4E425F1F2A2B83471 | SHA256:21B2CA9AEA620F6912338FA4A2573736ABD7055790A15E47E265CB8FDDBD3A30 | |||
| 296 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\YTOWV792\jquery-ui[1].js | text | |
MD5:CAEDCD0D9B40346F7533890CB04ACBBD | SHA256:FF6B70D8459332E298276D8616BE97E6F3C5D64925E666FBE67A667CCE0950F5 | |||
| 296 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5IWPIAR9\cookie[1].js | text | |
MD5:B868077CBAB37A24E9ADB49500414799 | SHA256:22983C77BF209689726DE7455C0C02CA28306B1889E5008E30DC0847CE4067BB | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
166
TCP/UDP connections
524
DNS requests
194
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
296 | iexplore.exe | GET | 200 | 190.115.19.71:80 | http://netu.tv/ | unknown | html | 30.2 Kb | unknown |
296 | iexplore.exe | GET | 200 | 190.115.19.71:80 | http://netu.tv/js/jQuery-File-Upload-10.32.0/css/jquery.fileupload.css | unknown | text | 403 b | unknown |
296 | iexplore.exe | GET | 200 | 190.115.19.71:80 | http://netu.tv/styles/cbv2new/theme/animate.css?56 | unknown | text | 6.15 Kb | unknown |
296 | iexplore.exe | GET | 200 | 190.115.19.71:80 | http://netu.tv/styles/cbv2new/theme/counter.css? | unknown | text | 1.42 Kb | unknown |
296 | iexplore.exe | GET | 200 | 190.115.19.71:80 | http://netu.tv/styles/cbv2new/theme/bootstrap.css?17 | unknown | text | 19.9 Kb | unknown |
296 | iexplore.exe | GET | 200 | 190.115.19.71:80 | http://netu.tv/styles/cbv2new/theme/main.css?232 | unknown | text | 20.9 Kb | unknown |
296 | iexplore.exe | GET | 200 | 172.217.16.194:80 | http://pagead2.googlesyndication.com/pagead/js/adsbygoogle.js | unknown | text | 61.3 Kb | unknown |
296 | iexplore.exe | GET | 200 | 190.115.19.71:80 | http://netu.tv/styles/global/jquery_ui.css | unknown | text | 7.06 Kb | unknown |
296 | iexplore.exe | GET | 200 | 142.250.186.170:80 | http://ajax.googleapis.com/ajax/libs/swfobject/2.2/swfobject.js | unknown | text | 3.88 Kb | unknown |
296 | iexplore.exe | GET | 200 | 190.115.19.71:80 | http://netu.tv/js/jquery_plugs/jquery-ui.js | unknown | text | 131 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
296 | iexplore.exe | 190.115.19.71:80 | netu.tv | DDOS-GUARD CORP. | BZ | unknown |
296 | iexplore.exe | 104.18.10.207:80 | maxcdn.bootstrapcdn.com | CLOUDFLARENET | — | unknown |
296 | iexplore.exe | 190.115.19.71:443 | netu.tv | DDOS-GUARD CORP. | BZ | unknown |
296 | iexplore.exe | 172.217.16.194:80 | pagead2.googlesyndication.com | GOOGLE | US | whitelisted |
296 | iexplore.exe | 142.250.186.170:443 | ajax.googleapis.com | GOOGLE | US | whitelisted |
296 | iexplore.exe | 142.250.186.170:80 | ajax.googleapis.com | GOOGLE | US | whitelisted |
296 | iexplore.exe | 104.21.5.49:80 | waaw1.tv | CLOUDFLARENET | — | unknown |
296 | iexplore.exe | 104.17.24.14:443 | cdnjs.cloudflare.com | CLOUDFLARENET | — | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
netu.tv |
| whitelisted |
maxcdn.bootstrapcdn.com |
| whitelisted |
pagead2.googlesyndication.com |
| whitelisted |
hqq.tv |
| whitelisted |
yandexcdn.com |
| unknown |
waaw.tv |
| whitelisted |
waaw1.tv |
| unknown |
ajax.googleapis.com |
| whitelisted |
www.recaptcha.net |
| whitelisted |
cdnjs.cloudflare.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
296 | iexplore.exe | Not Suspicious Traffic | INFO [ANY.RUN] A free CDN for open source projects (jsdelivr .net) |
1080 | svchost.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup Domain (iplogger .com in DNS lookup) |
296 | iexplore.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup Domain (iplogger .com in TLS SNI) |
296 | iexplore.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup Domain (iplogger .com in TLS SNI) |
2 ETPRO signatures available at the full report