| File name: | Zoom_cm_fo42anktZ9vvrZo4_mOz818SP8uPmdwI23GXfMZU7+T0wgvz3Fq-NT@sJCLzt-VIDffrDKx_k87278f807068a9ba_.exe |
| Full analysis: | https://app.any.run/tasks/2bb148d7-f778-47d5-bb20-a22fa0d1963c |
| Verdict: | Malicious activity |
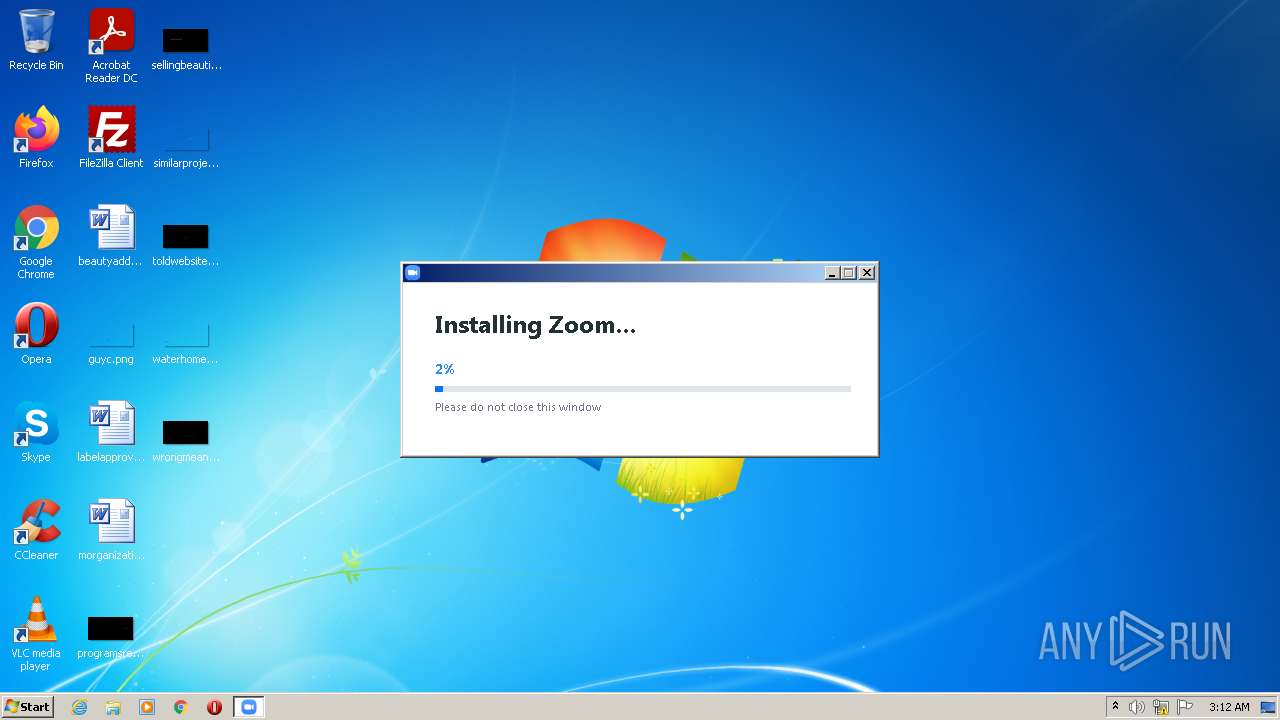
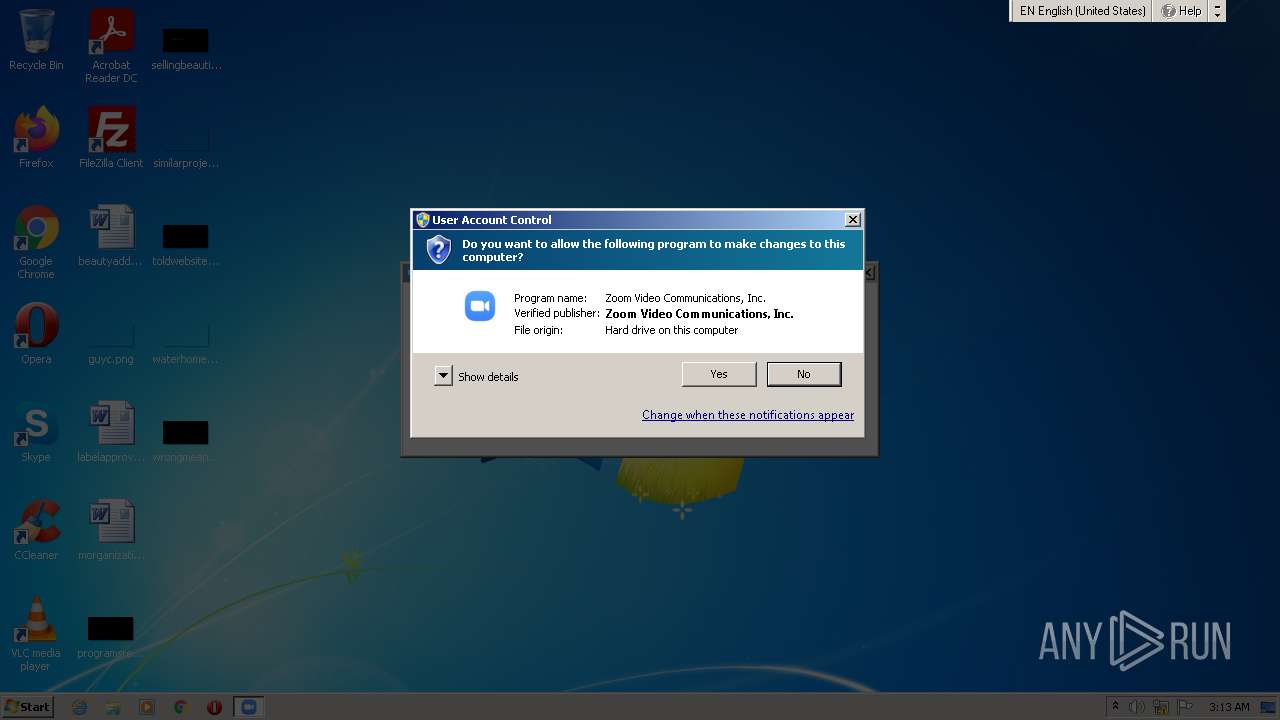
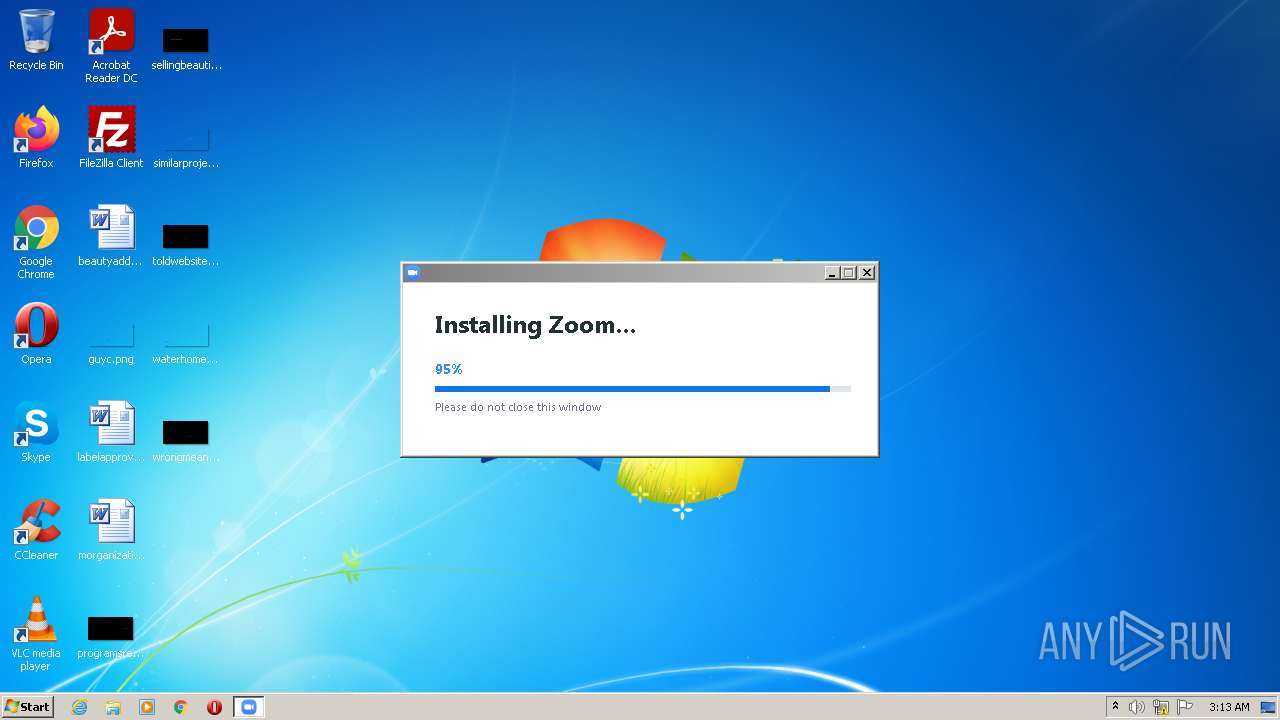
| Analysis date: | January 12, 2022, 03:12:48 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 8CAFF4CC2912C52106D9056A7DB5EB2D |
| SHA1: | EEE8742AC37E85E9C9B8A1D22477F080485AD9F9 |
| SHA256: | CFC5ADFC61D1F34802AC65A474ACE9FFE5007F859B2062B2297A1F047DA96BDA |
| SSDEEP: | 3072:NPWaH6A2h2nX+oJGpmIwfqN4fu3CaMKyg5P:VWaX7nX9LfNG |
MALICIOUS
Application was dropped or rewritten from another process
- Installer.exe (PID: 1296)
- Installer.exe (PID: 804)
- Zoom.exe (PID: 1660)
- Zoom.exe (PID: 3448)
Loads dropped or rewritten executable
- Zoom.exe (PID: 1660)
- Installer.exe (PID: 1296)
- Zoom.exe (PID: 3448)
SUSPICIOUS
Checks supported languages
- Zoom_cm_fo42anktZ9vvrZo4_mOz818SP8uPmdwI23GXfMZU7+T0wgvz3Fq-NT@sJCLzt-VIDffrDKx_k87278f807068a9ba_.exe (PID: 3980)
- Installer.exe (PID: 1296)
- Zoom.exe (PID: 1660)
- zm7E37.tmp (PID: 1748)
- Zoom.exe (PID: 3448)
- Installer.exe (PID: 804)
Reads the computer name
- Installer.exe (PID: 1296)
- Zoom_cm_fo42anktZ9vvrZo4_mOz818SP8uPmdwI23GXfMZU7+T0wgvz3Fq-NT@sJCLzt-VIDffrDKx_k87278f807068a9ba_.exe (PID: 3980)
- Installer.exe (PID: 804)
- Zoom.exe (PID: 1660)
- Zoom.exe (PID: 3448)
Executable content was dropped or overwritten
- Zoom_cm_fo42anktZ9vvrZo4_mOz818SP8uPmdwI23GXfMZU7+T0wgvz3Fq-NT@sJCLzt-VIDffrDKx_k87278f807068a9ba_.exe (PID: 3980)
- Installer.exe (PID: 1296)
Drops a file with a compile date too recent
- Zoom_cm_fo42anktZ9vvrZo4_mOz818SP8uPmdwI23GXfMZU7+T0wgvz3Fq-NT@sJCLzt-VIDffrDKx_k87278f807068a9ba_.exe (PID: 3980)
- Installer.exe (PID: 1296)
Creates files in the user directory
- Zoom_cm_fo42anktZ9vvrZo4_mOz818SP8uPmdwI23GXfMZU7+T0wgvz3Fq-NT@sJCLzt-VIDffrDKx_k87278f807068a9ba_.exe (PID: 3980)
- Zoom.exe (PID: 1660)
- Zoom.exe (PID: 3448)
- Installer.exe (PID: 1296)
Drops a file that was compiled in debug mode
- Zoom_cm_fo42anktZ9vvrZo4_mOz818SP8uPmdwI23GXfMZU7+T0wgvz3Fq-NT@sJCLzt-VIDffrDKx_k87278f807068a9ba_.exe (PID: 3980)
- Installer.exe (PID: 1296)
Application launched itself
- Installer.exe (PID: 1296)
- Zoom.exe (PID: 1660)
Drops a file with too old compile date
- Installer.exe (PID: 1296)
Changes default file association
- Installer.exe (PID: 1296)
Starts application with an unusual extension
- Zoom_cm_fo42anktZ9vvrZo4_mOz818SP8uPmdwI23GXfMZU7+T0wgvz3Fq-NT@sJCLzt-VIDffrDKx_k87278f807068a9ba_.exe (PID: 3980)
Starts itself from another location
- Zoom_cm_fo42anktZ9vvrZo4_mOz818SP8uPmdwI23GXfMZU7+T0wgvz3Fq-NT@sJCLzt-VIDffrDKx_k87278f807068a9ba_.exe (PID: 3980)
Creates a software uninstall entry
- Installer.exe (PID: 1296)
Changes IE settings (feature browser emulation)
- Installer.exe (PID: 1296)
INFO
Reads settings of System Certificates
- Zoom_cm_fo42anktZ9vvrZo4_mOz818SP8uPmdwI23GXfMZU7+T0wgvz3Fq-NT@sJCLzt-VIDffrDKx_k87278f807068a9ba_.exe (PID: 3980)
- Installer.exe (PID: 1296)
- Zoom.exe (PID: 1660)
- Zoom.exe (PID: 3448)
Checks Windows Trust Settings
- Zoom_cm_fo42anktZ9vvrZo4_mOz818SP8uPmdwI23GXfMZU7+T0wgvz3Fq-NT@sJCLzt-VIDffrDKx_k87278f807068a9ba_.exe (PID: 3980)
- Installer.exe (PID: 1296)
- Zoom.exe (PID: 1660)
- Zoom.exe (PID: 3448)
Dropped object may contain Bitcoin addresses
- Installer.exe (PID: 1296)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| ProductVersion: | 5,6,6,880 |
|---|---|
| ProductName: | Zoom Opener |
| OriginalFileName: | Zoom Opener |
| LegalTrademarks: | Zoom Opener |
| LegalCopyright: | © Zoom Video Communications, Inc. All rights reserved. |
| InternalName: | Zoom Opener |
| FileVersion: | 5,6,6,880 |
| FileDescription: | Zoom Opener |
| CompanyName: | Zoom Video Communications, Inc. |
| Comments: | Zoom Opener |
| CharacterSet: | Windows, Latin1 |
| LanguageCode: | English (U.S.) |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Win32 |
| FileFlags: | (none) |
| FileFlagsMask: | 0x003f |
| ProductVersionNumber: | 5.6.6.880 |
| FileVersionNumber: | 5.6.6.880 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 5.2 |
| ImageVersion: | - |
| OSVersion: | 5.2 |
| EntryPoint: | 0x7a10 |
| UninitializedDataSize: | - |
| InitializedDataSize: | 45568 |
| CodeSize: | 65536 |
| LinkerVersion: | 14.27 |
| PEType: | PE32 |
| TimeStamp: | 2021:05:12 09:48:08+02:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 12-May-2021 07:48:08 |
| Detected languages: |
|
| Debug artifacts: |
|
| Comments: | Zoom Opener |
| CompanyName: | Zoom Video Communications, Inc. |
| FileDescription: | Zoom Opener |
| FileVersion: | 5,6,6,880 |
| InternalName: | Zoom Opener |
| LegalCopyright: | © Zoom Video Communications, Inc. All rights reserved. |
| LegalTrademarks: | Zoom Opener |
| OriginalFilename: | Zoom Opener |
| ProductName: | Zoom Opener |
| ProductVersion: | 5,6,6,880 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000F8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 12-May-2021 07:48:08 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0000FFD8 | 0x00010000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.49326 |
.rdata | 0x00011000 | 0x00006E96 | 0x00007000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.20588 |
.data | 0x00018000 | 0x00000D94 | 0x00000800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 1.93047 |
.rsrc | 0x00019000 | 0x00001EE0 | 0x00002000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.96008 |
.reloc | 0x0001B000 | 0x00001368 | 0x00001400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.64731 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.40141 | 924 | UNKNOWN | English - United States | RT_VERSION |
2 | 2.21059 | 34 | UNKNOWN | English - United States | RT_GROUP_ICON |
7 | 2.77789 | 142 | UNKNOWN | English - United States | RT_STRING |
32 | 3.10562 | 352 | UNKNOWN | English - United States | RT_STRING |
33 | 3.31299 | 600 | UNKNOWN | English - United States | RT_STRING |
Imports
ADVAPI32.dll |
CRYPT32.dll |
GDI32.dll |
KERNEL32.dll |
OLEAUT32.dll |
SHELL32.dll |
SHLWAPI.dll |
USER32.dll |
WINTRUST.dll |
ole32.dll |
Total processes
44
Monitored processes
6
Malicious processes
4
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 804 | "C:\Users\admin\AppData\Roaming\Zoom\ZoomDownload\Installer.exe" /addfwexception --bin_home="C:\Users\admin\AppData\Roaming\Zoom\bin" | C:\Users\admin\AppData\Roaming\Zoom\ZoomDownload\Installer.exe | Installer.exe | ||||||||||||
User: admin Company: Zoom Video Communications, Inc. Integrity Level: HIGH Description: Zoom Installer Exit code: 0 Version: 5,9,1,2581 Modules
| |||||||||||||||
| 1296 | "C:\Users\admin\AppData\Roaming\Zoom\ZoomDownload\Installer.exe" ZInstaller --conf.mode=silent --ipc_wnd=917830 | C:\Users\admin\AppData\Roaming\Zoom\ZoomDownload\Installer.exe | Zoom_cm_fo42anktZ9vvrZo4_mOz818SP8uPmdwI23GXfMZU7+T0wgvz3Fq-NT@sJCLzt-VIDffrDKx_k87278f807068a9ba_.exe | ||||||||||||
User: admin Company: Zoom Video Communications, Inc. Integrity Level: MEDIUM Description: Zoom Installer Exit code: 0 Version: 5,9,1,2581 Modules
| |||||||||||||||
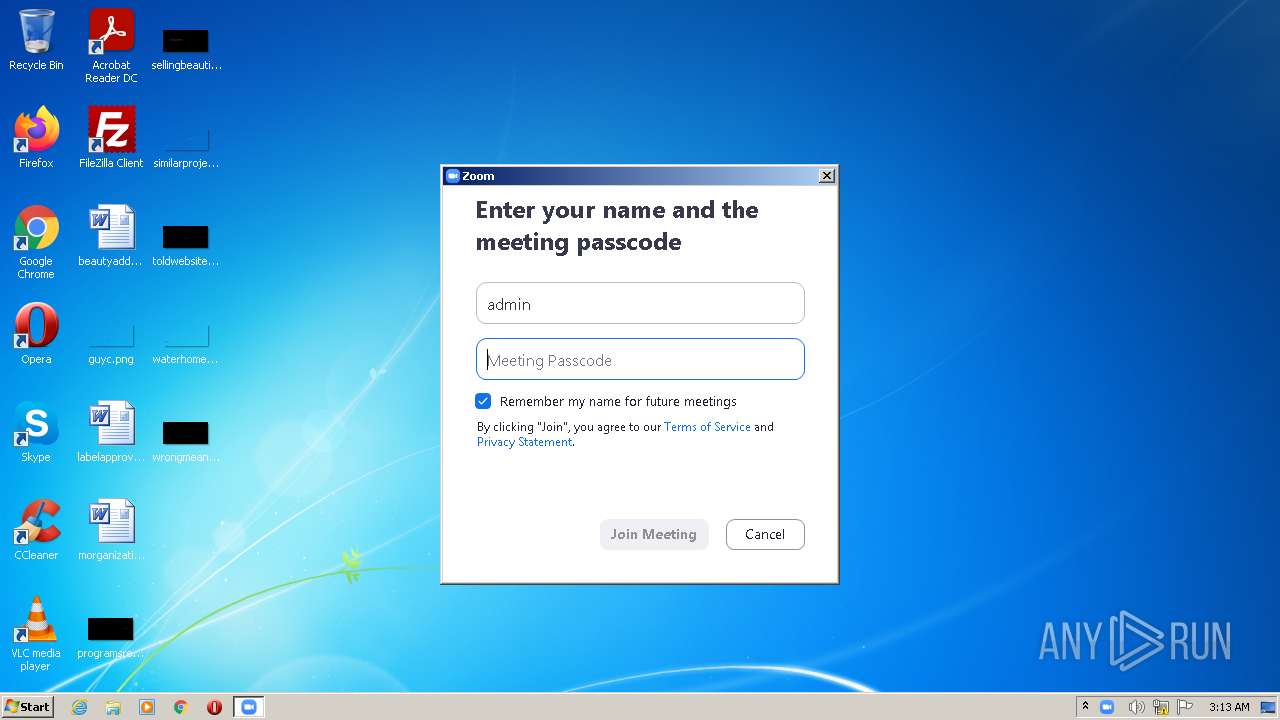
| 1660 | "C:\Users\admin\AppData\Roaming\Zoom\bin\Zoom.exe" "--url=zoommtg://win.launch?h.domain=us02web.zoom.us&h.path=join&stype=0&zc=0&action=join&confno=84768104924" | C:\Users\admin\AppData\Roaming\Zoom\bin\Zoom.exe | Zoom_cm_fo42anktZ9vvrZo4_mOz818SP8uPmdwI23GXfMZU7+T0wgvz3Fq-NT@sJCLzt-VIDffrDKx_k87278f807068a9ba_.exe | ||||||||||||
User: admin Company: Zoom Video Communications, Inc. Integrity Level: MEDIUM Description: Zoom Meetings Exit code: 0 Version: 5,9,1,2581 Modules
| |||||||||||||||
| 1748 | "C:\Users\admin\AppData\Local\Temp\zm7E37.tmp" -DAF8C715436E44649F1312698287E6A5=C:\Users\admin\AppData\Local\Temp\Zoom_cm_fo42anktZ9vvrZo4_mOz818SP8uPmdwI23GXfMZU7+T0wgvz3Fq-NT@sJCLzt-VIDffrDKx_k87278f807068a9ba_.exe | C:\Users\admin\AppData\Local\Temp\zm7E37.tmp | — | Zoom_cm_fo42anktZ9vvrZo4_mOz818SP8uPmdwI23GXfMZU7+T0wgvz3Fq-NT@sJCLzt-VIDffrDKx_k87278f807068a9ba_.exe | |||||||||||
User: admin Company: Zoom Video Communications, Inc. Integrity Level: MEDIUM Description: Zoom Opener Exit code: 0 Version: 5,6,6,880 Modules
| |||||||||||||||
| 3448 | "C:\Users\admin\AppData\Roaming\Zoom\bin\Zoom.exe" --action=join --runaszvideo=TRUE | C:\Users\admin\AppData\Roaming\Zoom\bin\Zoom.exe | Zoom.exe | ||||||||||||
User: admin Company: Zoom Video Communications, Inc. Integrity Level: MEDIUM Description: Zoom Meetings Exit code: 0 Version: 5,9,1,2581 Modules
| |||||||||||||||
| 3980 | "C:\Users\admin\AppData\Local\Temp\Zoom_cm_fo42anktZ9vvrZo4_mOz818SP8uPmdwI23GXfMZU7+T0wgvz3Fq-NT@sJCLzt-VIDffrDKx_k87278f807068a9ba_.exe" | C:\Users\admin\AppData\Local\Temp\Zoom_cm_fo42anktZ9vvrZo4_mOz818SP8uPmdwI23GXfMZU7+T0wgvz3Fq-NT@sJCLzt-VIDffrDKx_k87278f807068a9ba_.exe | Explorer.EXE | ||||||||||||
User: admin Company: Zoom Video Communications, Inc. Integrity Level: MEDIUM Description: Zoom Opener Exit code: 0 Version: 5,6,6,880 Modules
| |||||||||||||||
Total events
29 290
Read events
29 149
Write events
141
Delete events
0
Modification events
| (PID) Process: | (3980) Zoom_cm_fo42anktZ9vvrZo4_mOz818SP8uPmdwI23GXfMZU7+T0wgvz3Fq-NT@sJCLzt-VIDffrDKx_k87278f807068a9ba_.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3980) Zoom_cm_fo42anktZ9vvrZo4_mOz818SP8uPmdwI23GXfMZU7+T0wgvz3Fq-NT@sJCLzt-VIDffrDKx_k87278f807068a9ba_.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3980) Zoom_cm_fo42anktZ9vvrZo4_mOz818SP8uPmdwI23GXfMZU7+T0wgvz3Fq-NT@sJCLzt-VIDffrDKx_k87278f807068a9ba_.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3980) Zoom_cm_fo42anktZ9vvrZo4_mOz818SP8uPmdwI23GXfMZU7+T0wgvz3Fq-NT@sJCLzt-VIDffrDKx_k87278f807068a9ba_.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3980) Zoom_cm_fo42anktZ9vvrZo4_mOz818SP8uPmdwI23GXfMZU7+T0wgvz3Fq-NT@sJCLzt-VIDffrDKx_k87278f807068a9ba_.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 460000003B010000090000000000000000000000000000000400000000000000C0E333BBEAB1D3010000000000000000000000000100000002000000C0A80164000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3980) Zoom_cm_fo42anktZ9vvrZo4_mOz818SP8uPmdwI23GXfMZU7+T0wgvz3Fq-NT@sJCLzt-VIDffrDKx_k87278f807068a9ba_.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3980) Zoom_cm_fo42anktZ9vvrZo4_mOz818SP8uPmdwI23GXfMZU7+T0wgvz3Fq-NT@sJCLzt-VIDffrDKx_k87278f807068a9ba_.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3980) Zoom_cm_fo42anktZ9vvrZo4_mOz818SP8uPmdwI23GXfMZU7+T0wgvz3Fq-NT@sJCLzt-VIDffrDKx_k87278f807068a9ba_.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3980) Zoom_cm_fo42anktZ9vvrZo4_mOz818SP8uPmdwI23GXfMZU7+T0wgvz3Fq-NT@sJCLzt-VIDffrDKx_k87278f807068a9ba_.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (3980) Zoom_cm_fo42anktZ9vvrZo4_mOz818SP8uPmdwI23GXfMZU7+T0wgvz3Fq-NT@sJCLzt-VIDffrDKx_k87278f807068a9ba_.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Wpad\{362E934C-743B-4588-8259-D2482DB771A8} |
| Operation: | write | Name: | WpadDecisionReason |
Value: 1 | |||
Executable files
159
Suspicious files
84
Text files
16
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3980 | Zoom_cm_fo42anktZ9vvrZo4_mOz818SP8uPmdwI23GXfMZU7+T0wgvz3Fq-NT@sJCLzt-VIDffrDKx_k87278f807068a9ba_.exe | C:\Users\admin\AppData\Roaming\Zoom\ZoomDownload\Zoom.msi | — | |
MD5:— | SHA256:— | |||
| 3980 | Zoom_cm_fo42anktZ9vvrZo4_mOz818SP8uPmdwI23GXfMZU7+T0wgvz3Fq-NT@sJCLzt-VIDffrDKx_k87278f807068a9ba_.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\H8LTQSA7.txt | text | |
MD5:— | SHA256:— | |||
| 3980 | Zoom_cm_fo42anktZ9vvrZo4_mOz818SP8uPmdwI23GXfMZU7+T0wgvz3Fq-NT@sJCLzt-VIDffrDKx_k87278f807068a9ba_.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 3980 | Zoom_cm_fo42anktZ9vvrZo4_mOz818SP8uPmdwI23GXfMZU7+T0wgvz3Fq-NT@sJCLzt-VIDffrDKx_k87278f807068a9ba_.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\7423F88C7F265F0DEFC08EA88C3BDE45_D975BBA8033175C8D112023D8A7A8AD6 | binary | |
MD5:— | SHA256:— | |||
| 3980 | Zoom_cm_fo42anktZ9vvrZo4_mOz818SP8uPmdwI23GXfMZU7+T0wgvz3Fq-NT@sJCLzt-VIDffrDKx_k87278f807068a9ba_.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\7423F88C7F265F0DEFC08EA88C3BDE45_D975BBA8033175C8D112023D8A7A8AD6 | der | |
MD5:— | SHA256:— | |||
| 3980 | Zoom_cm_fo42anktZ9vvrZo4_mOz818SP8uPmdwI23GXfMZU7+T0wgvz3Fq-NT@sJCLzt-VIDffrDKx_k87278f807068a9ba_.exe | C:\Users\admin\AppData\Roaming\Zoom\ZoomDownload\Installer.exe | executable | |
MD5:— | SHA256:— | |||
| 3980 | Zoom_cm_fo42anktZ9vvrZo4_mOz818SP8uPmdwI23GXfMZU7+T0wgvz3Fq-NT@sJCLzt-VIDffrDKx_k87278f807068a9ba_.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\XAQ9FGJC.txt | text | |
MD5:— | SHA256:— | |||
| 1296 | Installer.exe | C:\Users\admin\AppData\Roaming\Zoom\zoom_install_src\dingdong.pcm | binary | |
MD5:54511224E61E71D2915FF67E57DCB268 | SHA256:7AADF0E317831D287B51E41992B43F0F381AE48A312CB77A426EEB3B6129D6D7 | |||
| 1296 | Installer.exe | C:\Users\admin\AppData\Roaming\Zoom\zoom_install_src\archival.pcm | binary | |
MD5:135DBED64D143BA06E65F149CC9AFC78 | SHA256:354807D23BBC4AA1A8CA9E4BF0519D1EFD6CA08A417958CCCCFA1B611902201F | |||
| 1296 | Installer.exe | C:\Users\admin\AppData\Roaming\Zoom\zoom_install_src\crashrpt_lang.ini | text | |
MD5:FCF61AED8F093BFCF571CDD8F8162A05 | SHA256:1F5B45A5411F7FC71B9DA789D6D1EAD8AD30551FBEA7BBB40FC7EA576D581ABB | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
11
DNS requests
6
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3980 | Zoom_cm_fo42anktZ9vvrZo4_mOz818SP8uPmdwI23GXfMZU7+T0wgvz3Fq-NT@sJCLzt-VIDffrDKx_k87278f807068a9ba_.exe | GET | 200 | 92.123.195.41:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?e331279027da9cea | unknown | compressed | 4.70 Kb | whitelisted |
3980 | Zoom_cm_fo42anktZ9vvrZo4_mOz818SP8uPmdwI23GXfMZU7+T0wgvz3Fq-NT@sJCLzt-VIDffrDKx_k87278f807068a9ba_.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAH9o%2BtuynXIiEOLckvPvJE%3D | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 3.235.71.132:443 | zoom.us | — | US | unknown |
3980 | Zoom_cm_fo42anktZ9vvrZo4_mOz818SP8uPmdwI23GXfMZU7+T0wgvz3Fq-NT@sJCLzt-VIDffrDKx_k87278f807068a9ba_.exe | 92.123.195.41:80 | ctldl.windowsupdate.com | Akamai International B.V. | — | whitelisted |
3448 | Zoom.exe | 3.235.71.134:443 | www3.zoom.us | — | US | unknown |
3980 | Zoom_cm_fo42anktZ9vvrZo4_mOz818SP8uPmdwI23GXfMZU7+T0wgvz3Fq-NT@sJCLzt-VIDffrDKx_k87278f807068a9ba_.exe | 143.204.97.253:443 | cdn.zoom.us | — | US | unknown |
3980 | Zoom_cm_fo42anktZ9vvrZo4_mOz818SP8uPmdwI23GXfMZU7+T0wgvz3Fq-NT@sJCLzt-VIDffrDKx_k87278f807068a9ba_.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3980 | Zoom_cm_fo42anktZ9vvrZo4_mOz818SP8uPmdwI23GXfMZU7+T0wgvz3Fq-NT@sJCLzt-VIDffrDKx_k87278f807068a9ba_.exe | 3.235.73.123:443 | us02web.zoom.us | — | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
us02web.zoom.us |
| whitelisted |
cdn.zoom.us |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
zoom.us |
| whitelisted |
www3.zoom.us |
| whitelisted |
Threats
Process | Message |
|---|---|
Installer.exe | [ProductPathHelper::RecursiveRemoveDirA] Path is: |
Installer.exe | C:\Users\admin\AppData\Roaming\Zoom\zoom_install_src |
Installer.exe | |
Installer.exe | [ProductPathHelper::RecursiveRemoveDirA] Path is: |
Installer.exe | C:\Users\admin\AppData\Roaming\Zoom\tmp_uninstall |
Installer.exe | |
Installer.exe | [ProductPathHelper::RecursiveRemoveDirA] Path is: |
Installer.exe | C:\Users\admin\AppData\Roaming\Zoom\tmp_bin |
Installer.exe | |
Installer.exe | [ProductPathHelper::RecursiveRemoveDirA] Path is: |