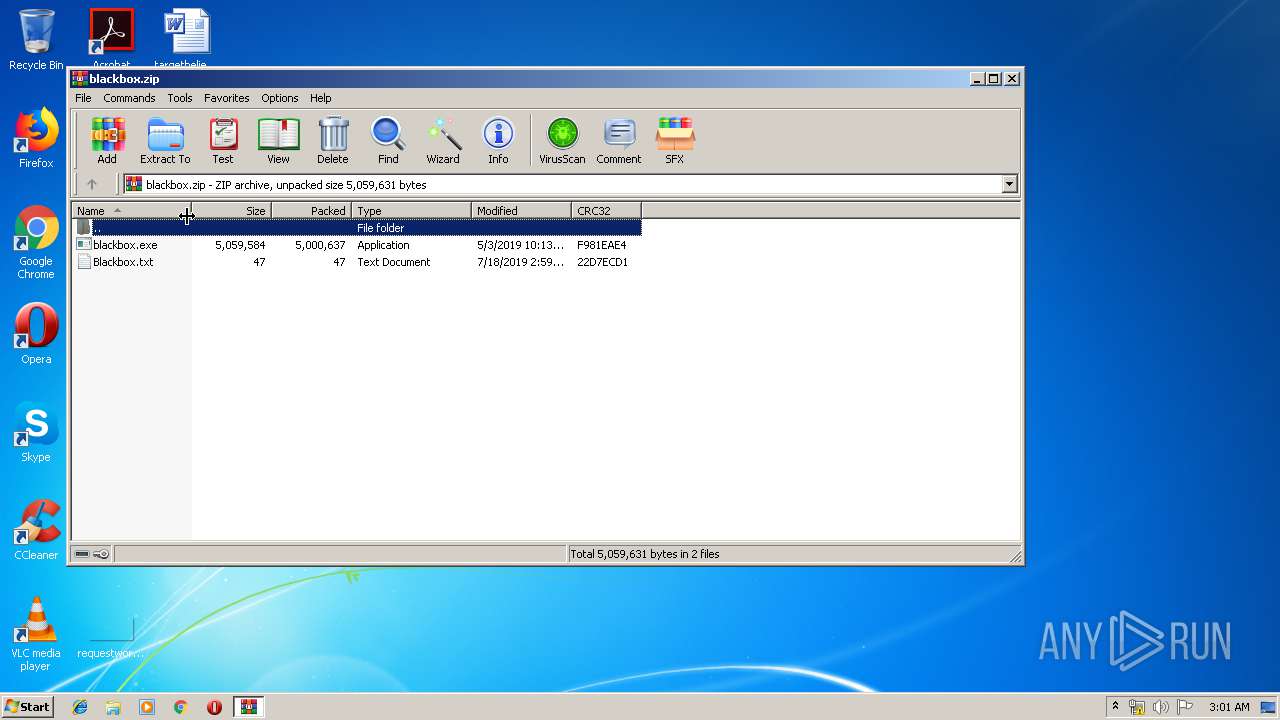
| File name: | blackbox.zip |
| Full analysis: | https://app.any.run/tasks/68ae6fed-4a0c-43ca-8797-70e218dffb5f |
| Verdict: | Malicious activity |
| Analysis date: | July 18, 2019, 02:00:40 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | D1A9A0266C96F7E7030359F8F844D46E |
| SHA1: | 80328D4FF58145E934EF02788682770218AA4449 |
| SHA256: | CFB1B2E554A5A65D71BFFCA9B0EA5D1A9E73D2C7ADE3937A8F5A912B6F13C4F6 |
| SSDEEP: | 98304:62txuClZyfdEYJjSvHDU8FJrjLEUf/74DmWOJwIjGHWxXLipVqQDyIMdXi/vJbF:6auSZL6W/g8XHLzTk80HACyIM9qvJ5 |
MALICIOUS
Application was dropped or rewritten from another process
- blackbox.exe (PID: 2772)
Loads dropped or rewritten executable
- blackbox.exe (PID: 2772)
SUSPICIOUS
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2168)
- blackbox.exe (PID: 2772)
Reads the BIOS version
- blackbox.exe (PID: 2772)
Reads Internet Cache Settings
- blackbox.exe (PID: 2772)
Creates files in the user directory
- blackbox.exe (PID: 2772)
Reads the machine GUID from the registry
- blackbox.exe (PID: 2772)
Reads CPU info
- blackbox.exe (PID: 2772)
INFO
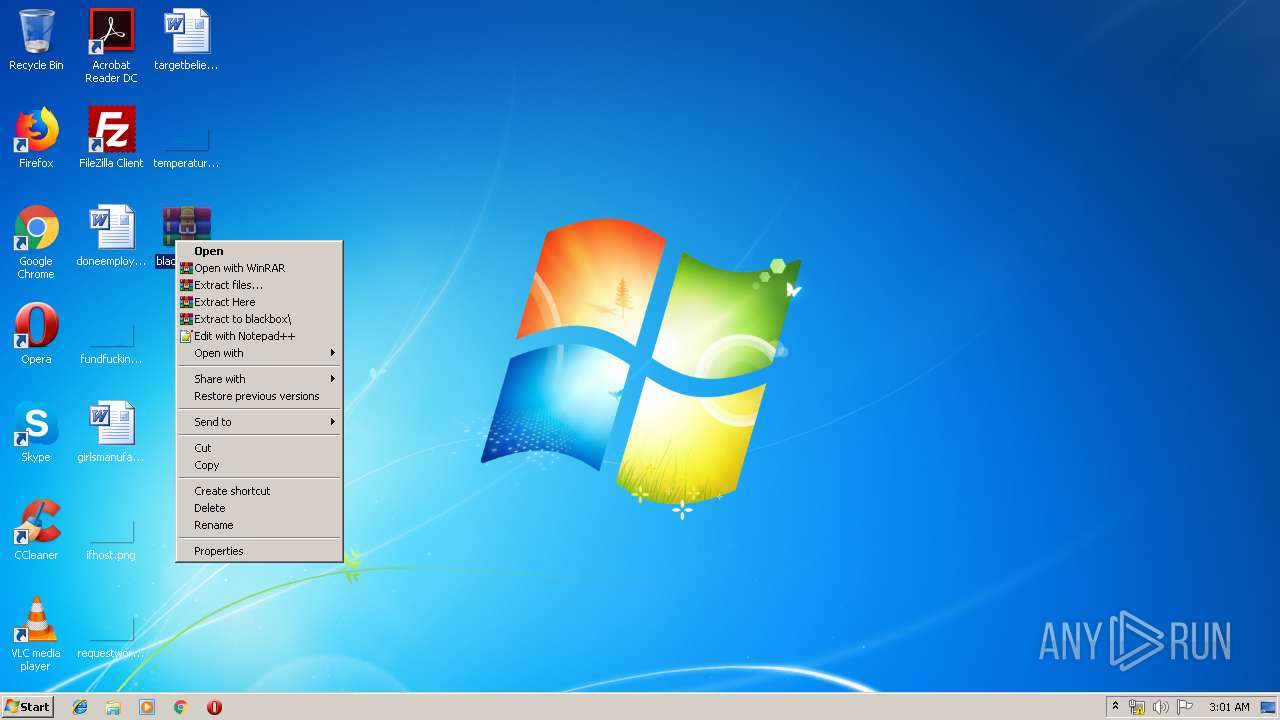
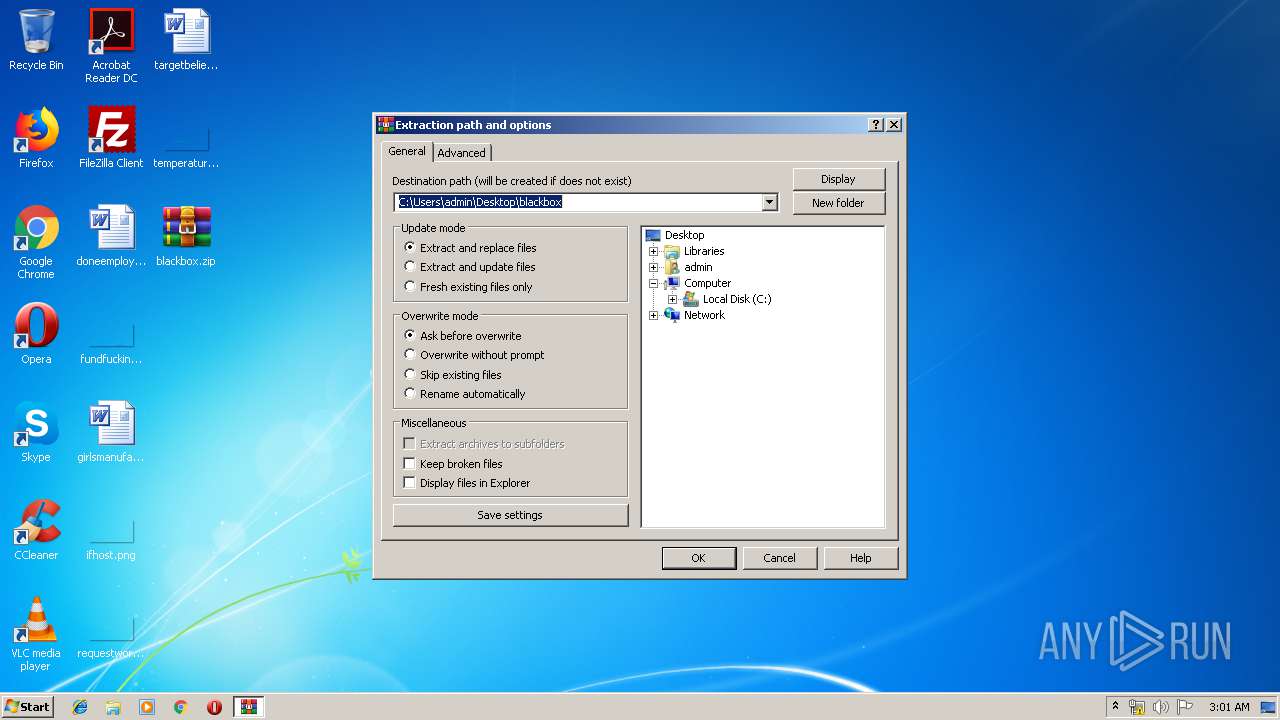
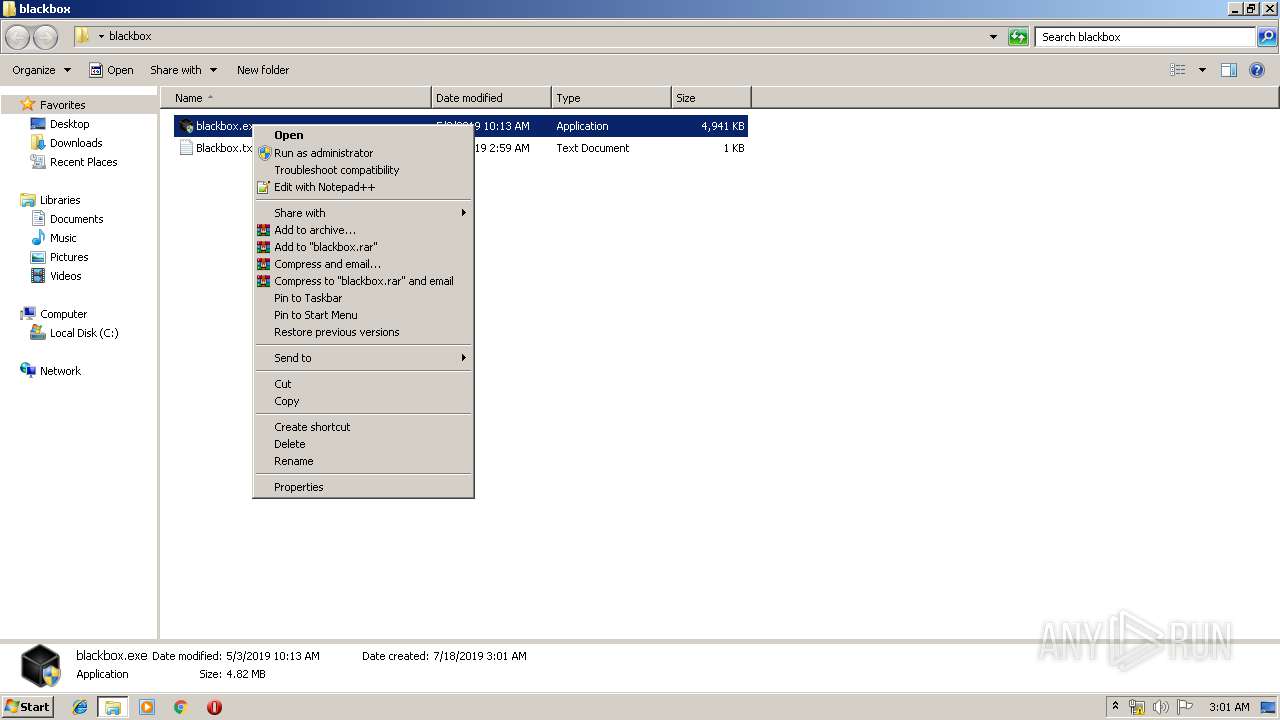
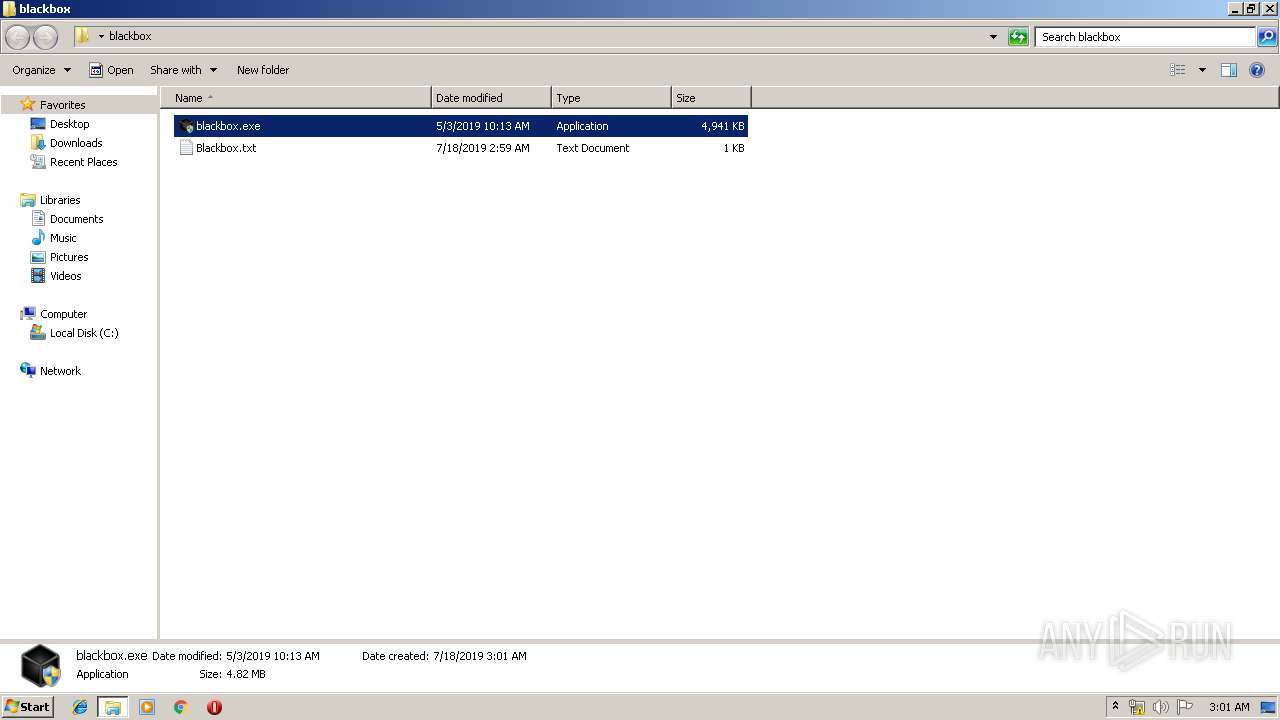
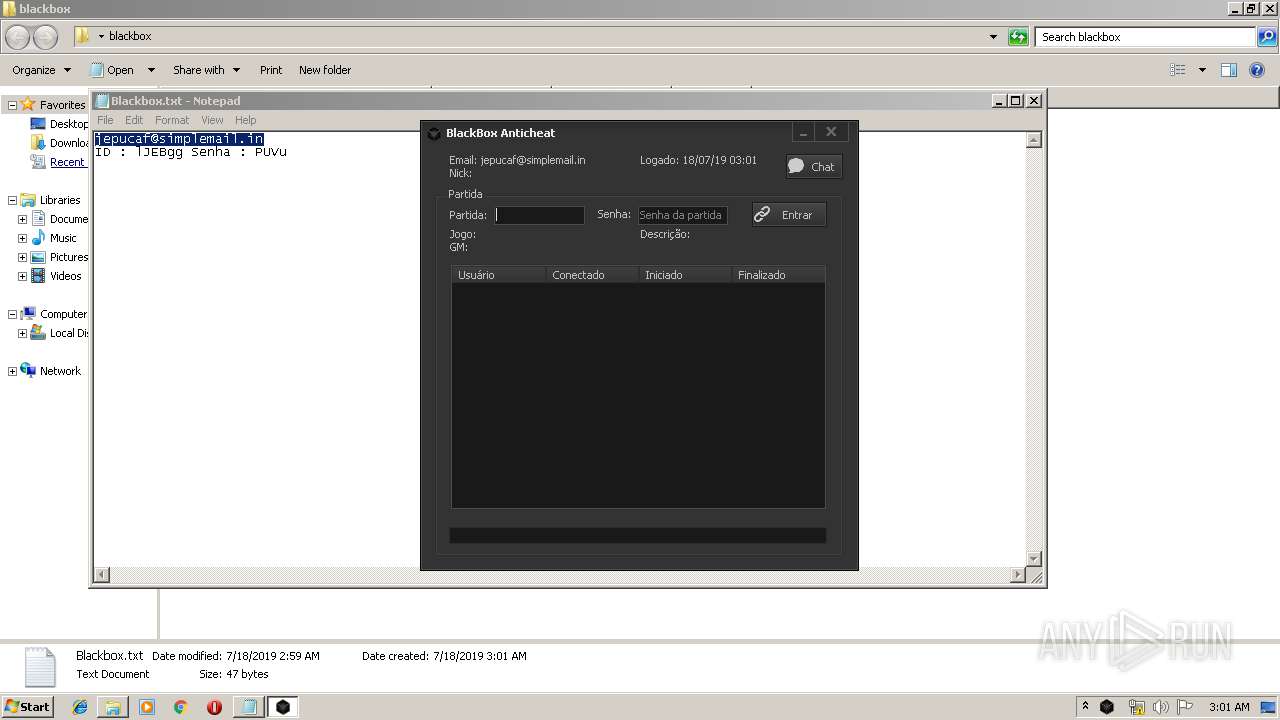
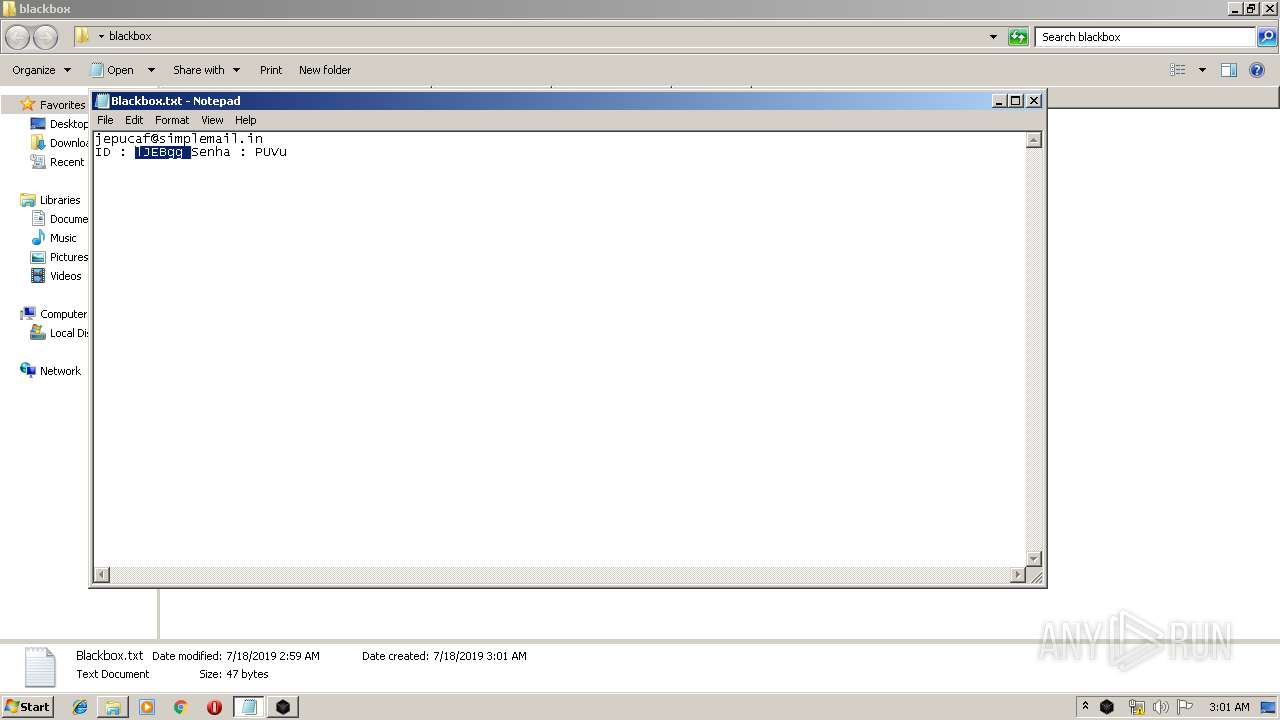
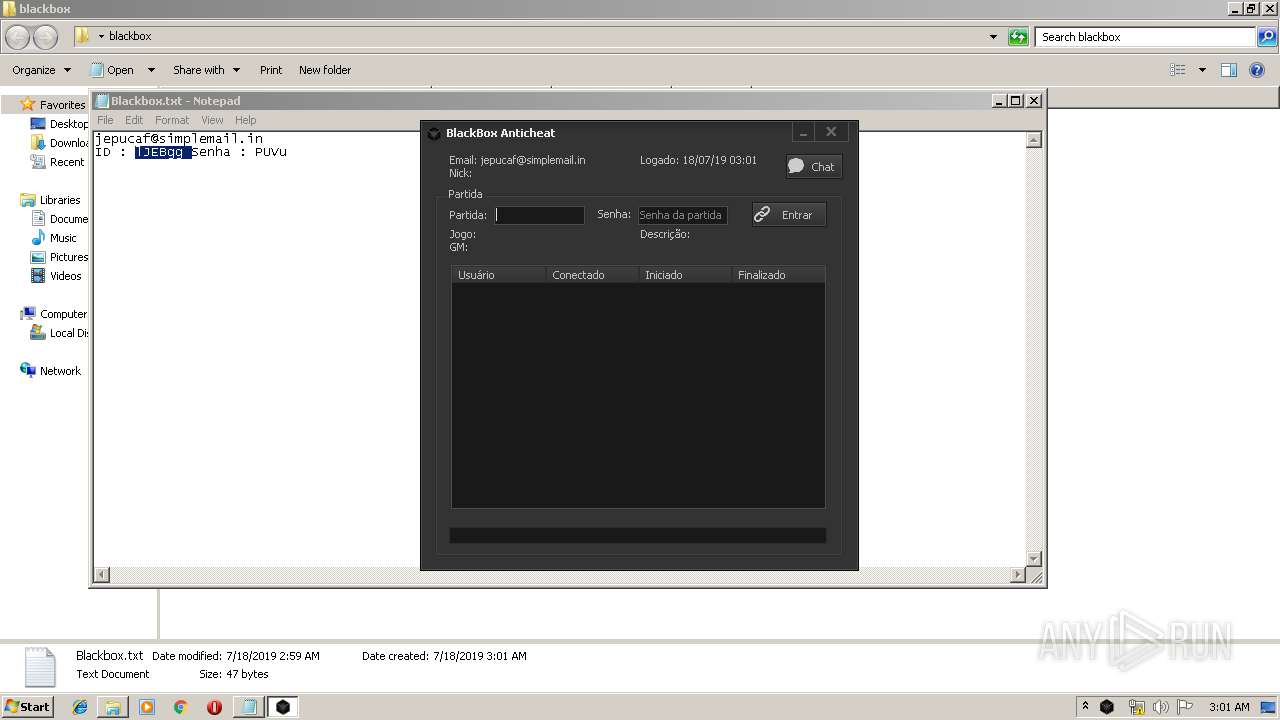
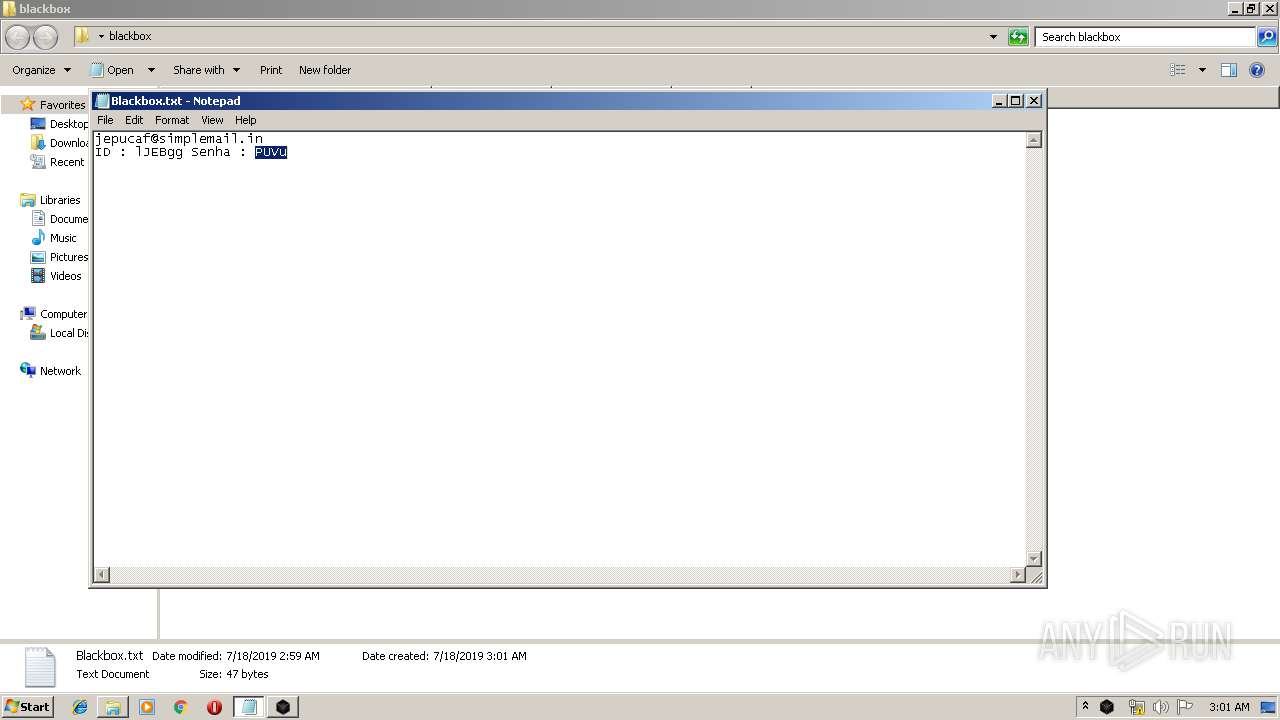
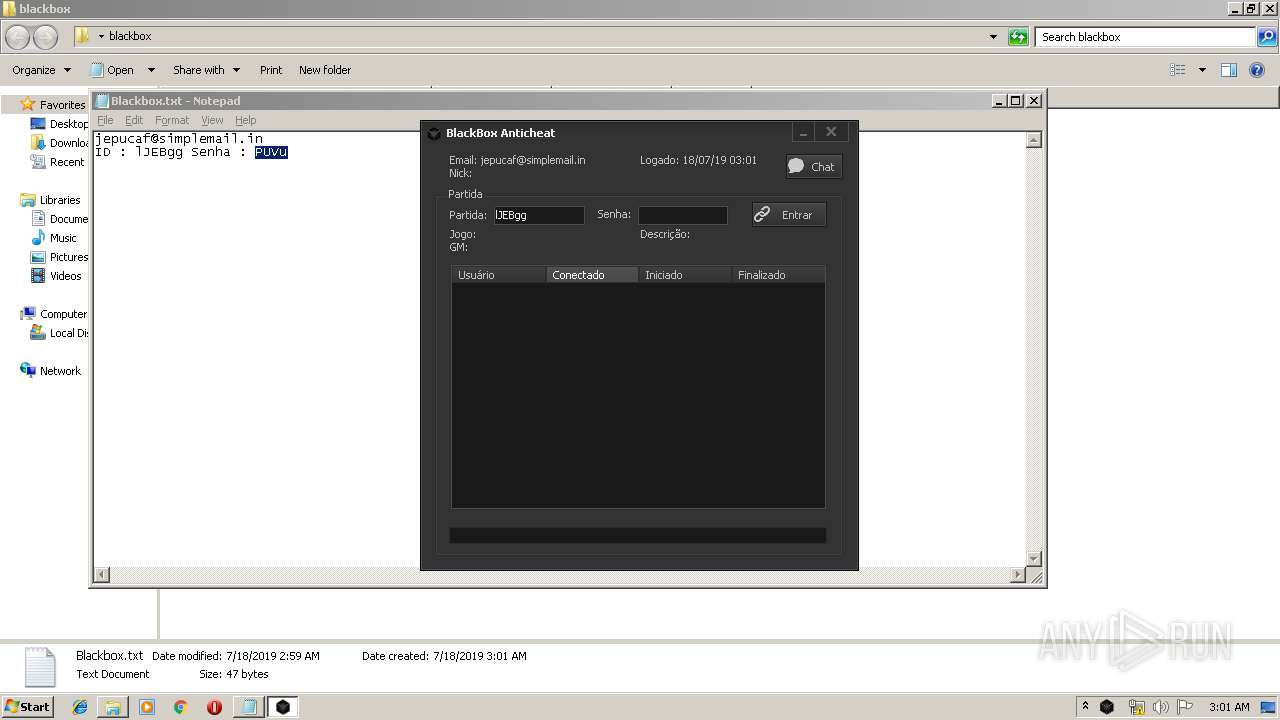
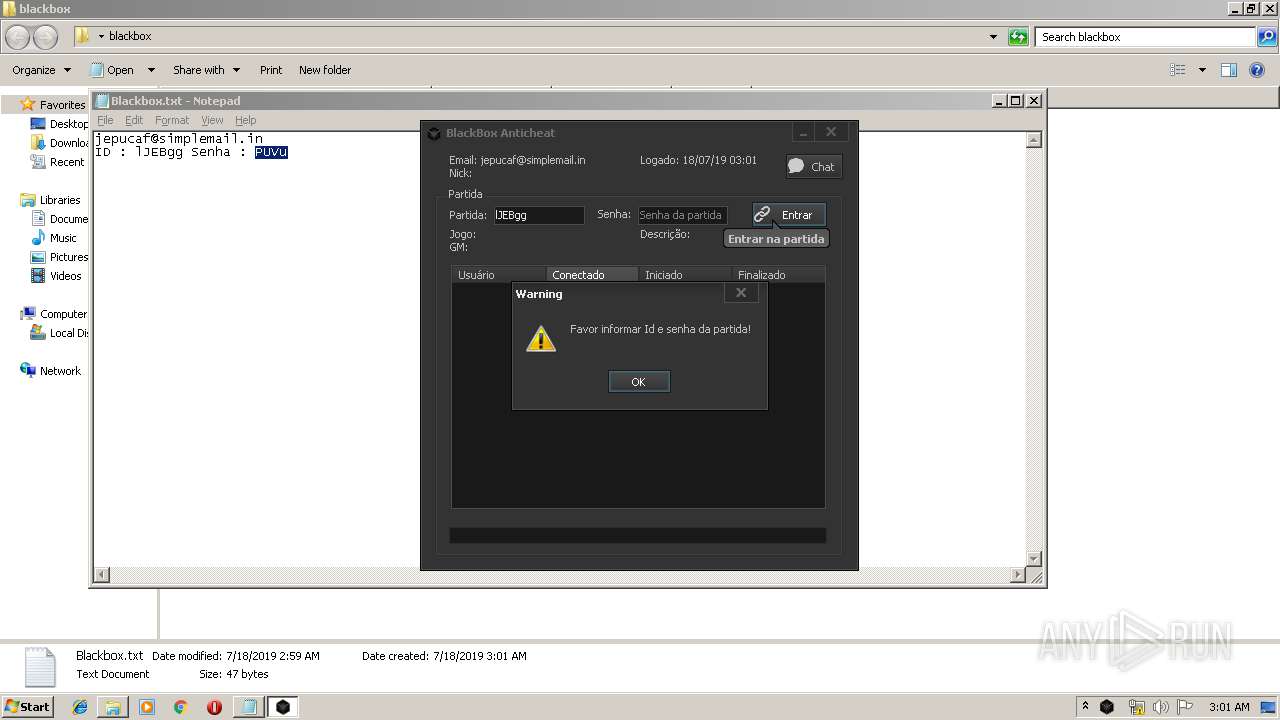
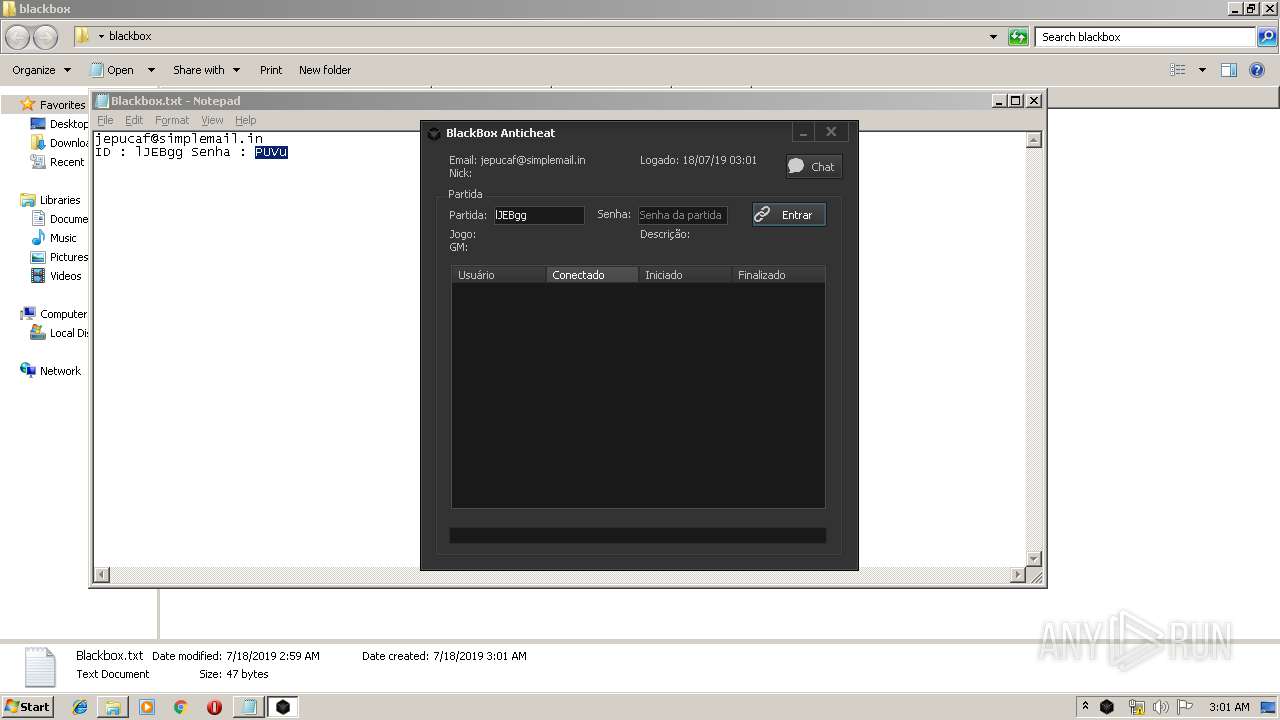
Manual execution by user
- WinRAR.exe (PID: 2168)
- blackbox.exe (PID: 2772)
- NOTEPAD.EXE (PID: 2548)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2019:07:17 22:59:00 |
| ZipCRC: | 0x22d7ecd1 |
| ZipCompressedSize: | 47 |
| ZipUncompressedSize: | 47 |
| ZipFileName: | Blackbox.txt |
Total processes
43
Monitored processes
4
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 116 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Desktop\blackbox.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 2168 | "C:\Program Files\WinRAR\WinRAR.exe" x -iext -ow -ver -- "C:\Users\admin\Desktop\blackbox.zip" "?\" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
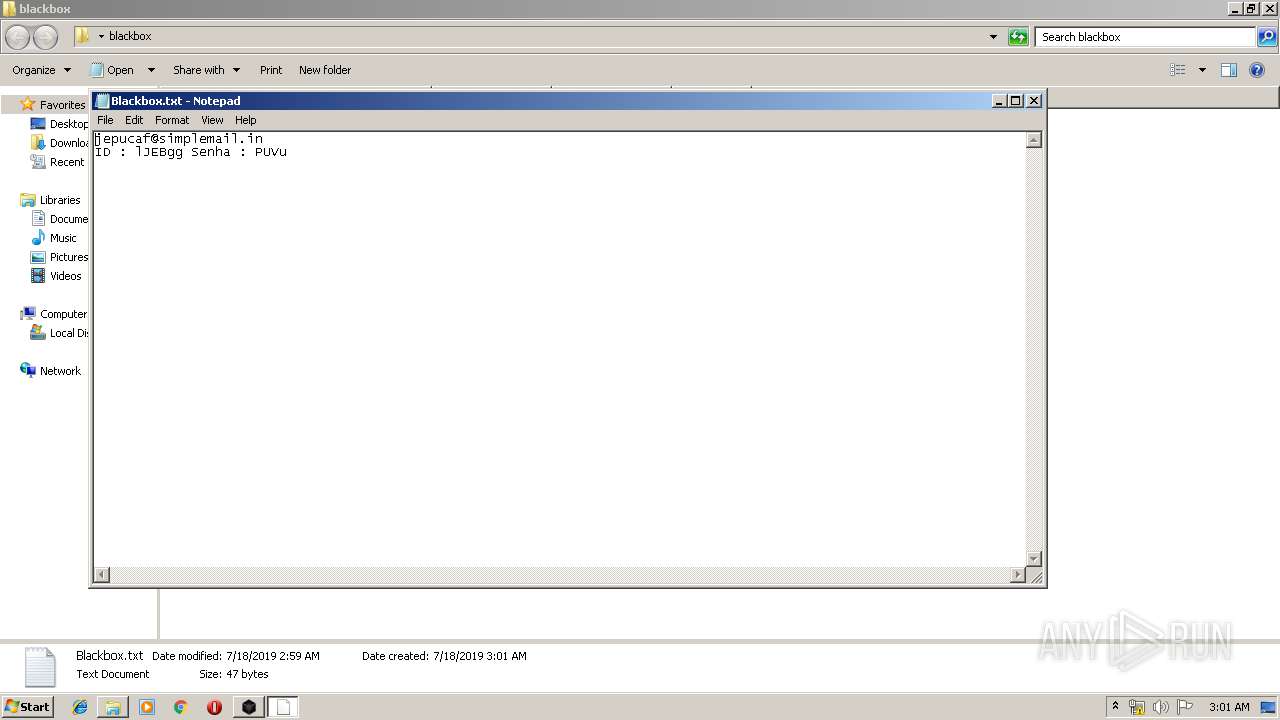
| 2548 | "C:\Windows\system32\NOTEPAD.EXE" C:\Users\admin\Desktop\blackbox\Blackbox.txt | C:\Windows\system32\NOTEPAD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
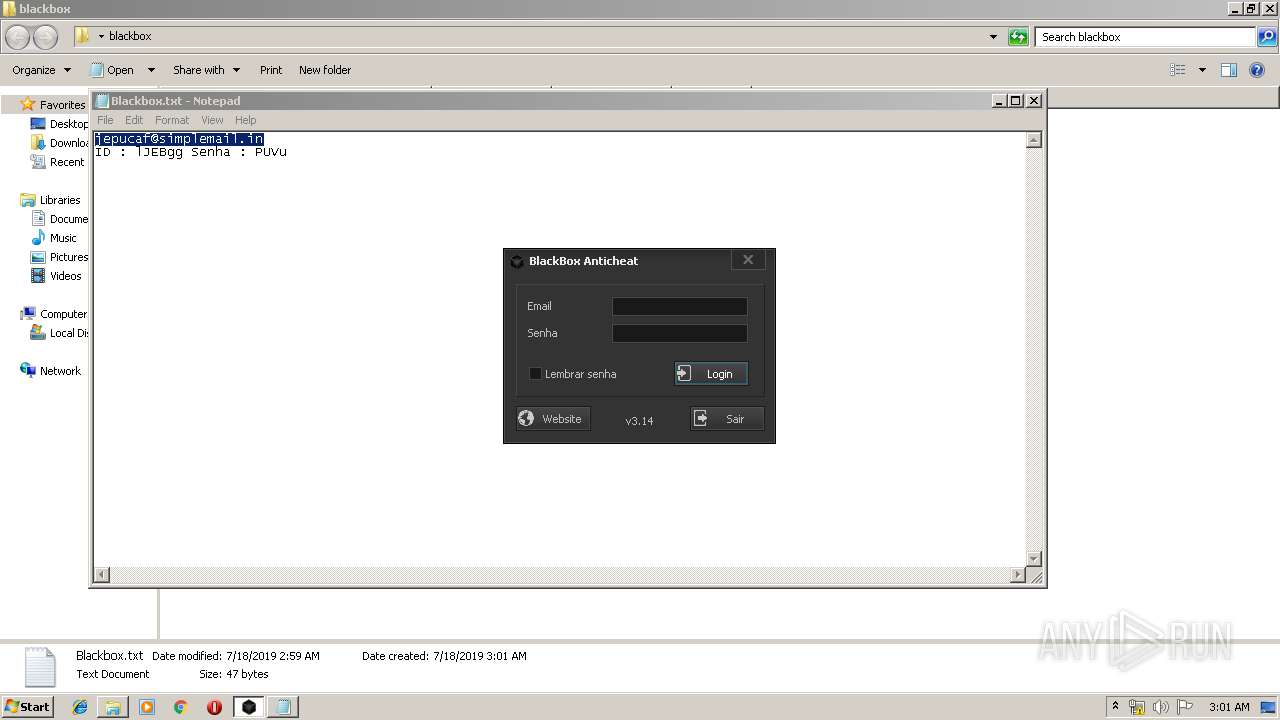
| 2772 | "C:\Users\admin\Desktop\blackbox\blackbox.exe" | C:\Users\admin\Desktop\blackbox\blackbox.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: blackbox Exit code: 0 Version: 0.1.0.0 Modules
| |||||||||||||||
Total events
564
Read events
507
Write events
57
Delete events
0
Modification events
| (PID) Process: | (116) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (116) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (116) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\70\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (116) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\blackbox.zip | |||
| (PID) Process: | (116) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (116) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (116) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (116) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (116) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF42000000420000000204000037020000 | |||
| (PID) Process: | (116) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\General |
| Operation: | write | Name: | LastFolder |
Value: C:\Users\admin\Desktop | |||
Executable files
5
Suspicious files
0
Text files
5
Unknown types
0
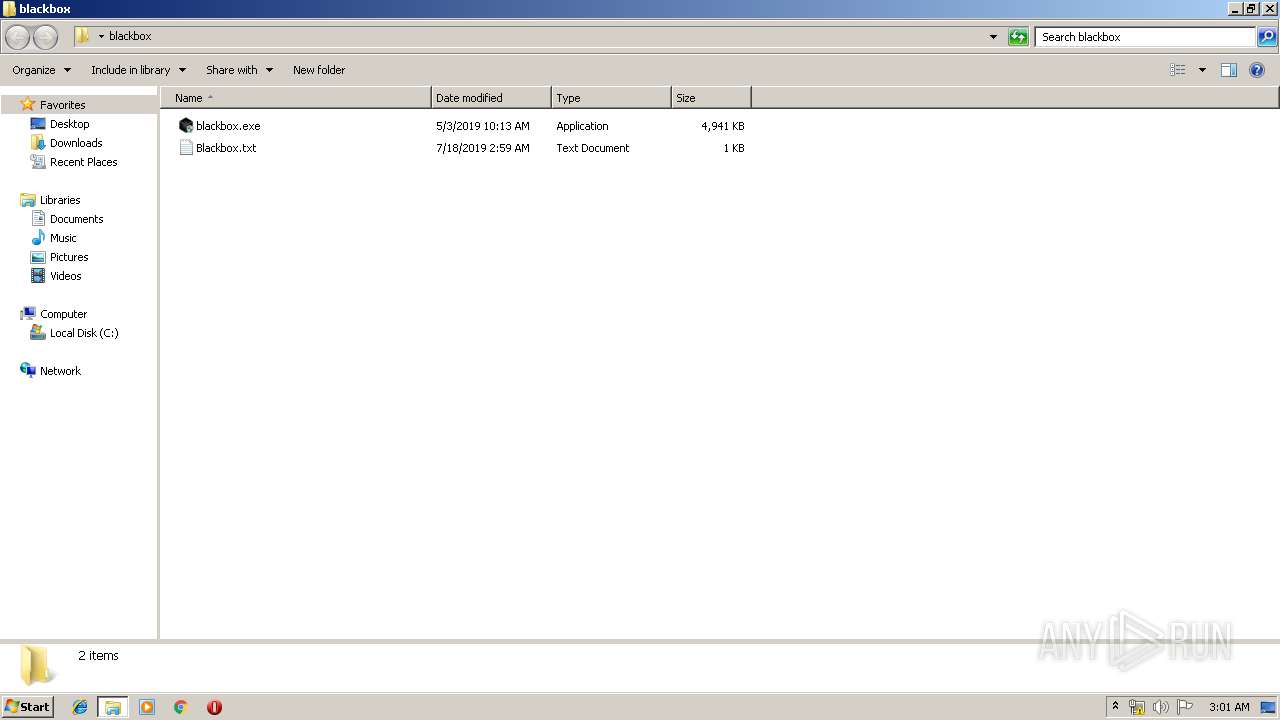
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2772 | blackbox.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\admin@blackbox[1].txt | — | |
MD5:— | SHA256:— | |||
| 2168 | WinRAR.exe | C:\Users\admin\Desktop\blackbox\Blackbox.txt | text | |
MD5:— | SHA256:— | |||
| 2168 | WinRAR.exe | C:\Users\admin\Desktop\blackbox\blackbox.exe | executable | |
MD5:— | SHA256:— | |||
| 2772 | blackbox.exe | C:\Users\admin\AppData\Roaming\BlackBox Anticheat\login.ini | text | |
MD5:— | SHA256:— | |||
| 2772 | blackbox.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\admin@blackbox[2].txt | text | |
MD5:— | SHA256:— | |||
| 2772 | blackbox.exe | C:\Users\admin\AppData\Local\Temp\tmp69D1.tmp | executable | |
MD5:75848ACD43300F5C5BC6E84192C9D9E3 | SHA256:C1114E4E476EDEEE26F20C17E6405E647415B3DD61A8288A505C164D3CC889BC | |||
| 2772 | blackbox.exe | C:\Users\admin\AppData\Local\Temp\tmp69D2.tmp | executable | |
MD5:86FEDF3C7B32B121AA72E171185699D5 | SHA256:E00F727BDFBF07C0AFF400F79B7B509F46FE8FD882154CF029B59FEDFC1BAC7C | |||
| 2772 | blackbox.exe | C:\Users\admin\AppData\Local\Temp\bbossl102q-944593\ssleay32.dll | executable | |
MD5:284E004B654306F8DB1A63CFF0E73D91 | SHA256:2D11228520402EF49443AADC5D0F02C9544A795A4AFC89FB0434B3B81EBDD28C | |||
| 2772 | blackbox.exe | C:\Users\admin\AppData\Local\Temp\bbossl102q-944593\libeay32.dll | executable | |
MD5:DE484D5DAFE3C1208DA6E24AF40E0A97 | SHA256:007342C6B9B956F416F556B4BD6F1077E25BD077CC4F4AC136E3FCCB803746E3 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
5
DNS requests
3
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2772 | blackbox.exe | GET | 200 | 188.166.87.218:80 | http://direct.blackbox.ac/update | NL | text | 70 b | unknown |
2772 | blackbox.exe | POST | 200 | 188.166.87.218:80 | http://direct.blackbox.ac/backend | NL | binary | 132 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2772 | blackbox.exe | 188.166.87.218:80 | direct.blackbox.ac | Digital Ocean, Inc. | NL | unknown |
2772 | blackbox.exe | 104.27.156.50:443 | blackbox.ac | Cloudflare Inc | US | shared |
2772 | blackbox.exe | 46.137.171.101:10000 | data.logentries.com | Amazon.com, Inc. | IE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
direct.blackbox.ac |
| unknown |
blackbox.ac |
| whitelisted |
data.logentries.com |
| unknown |