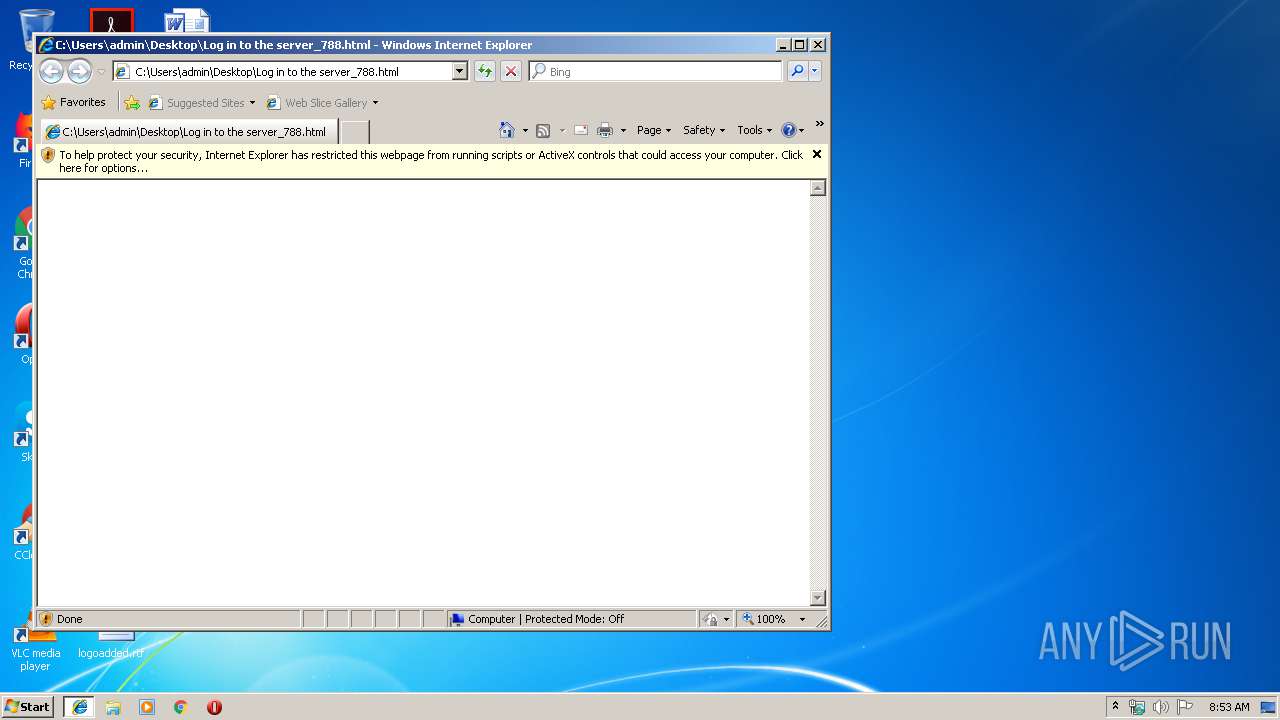
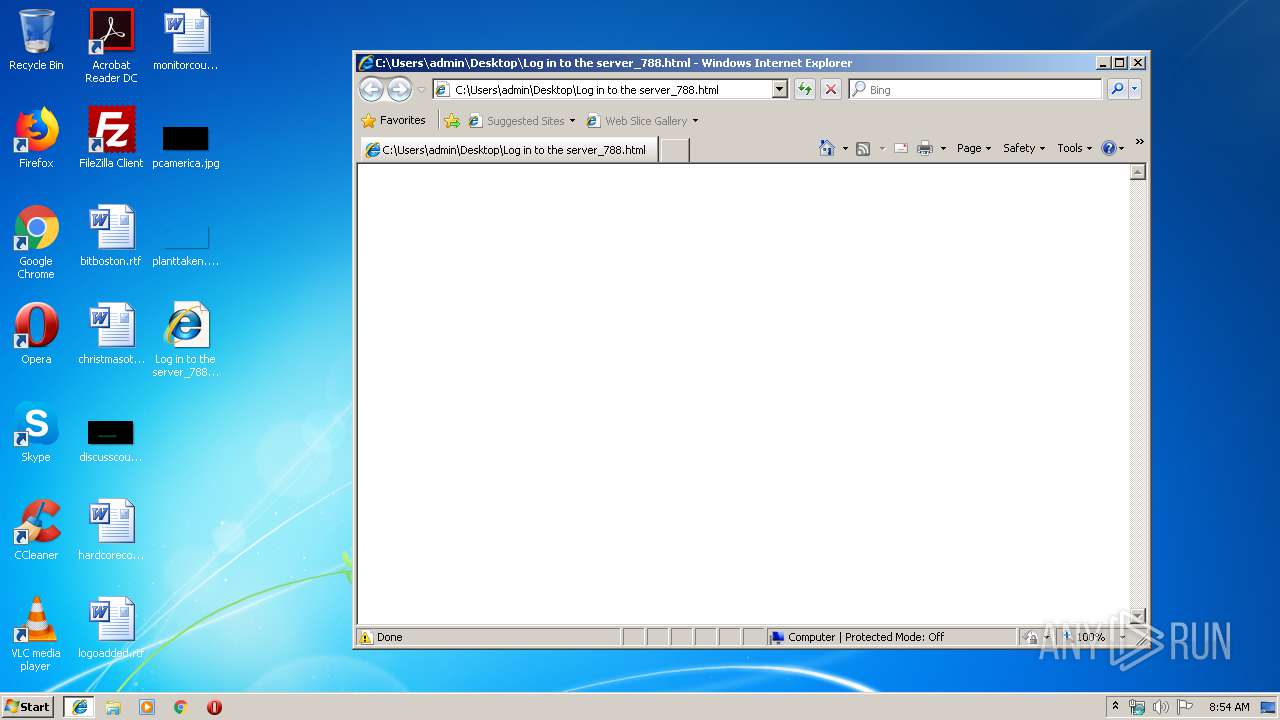
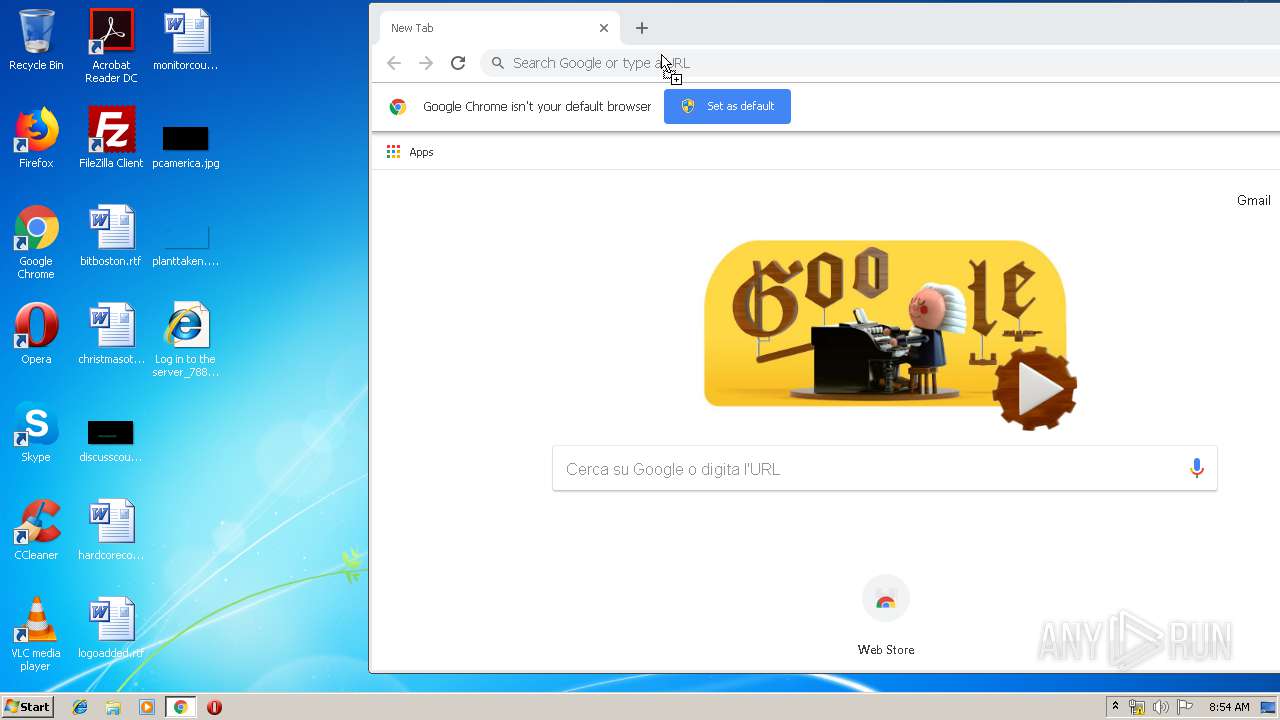
| File name: | Log in to the server_788.html |
| Full analysis: | https://app.any.run/tasks/e995b7f8-c9d7-45ee-a65b-c131001821f5 |
| Verdict: | Malicious activity |
| Analysis date: | March 21, 2019, 08:53:09 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/html |
| File info: | HTML document, ASCII text, with CRLF line terminators |
| MD5: | 35FE4A6C1903331CCB469DD7CE7DA67C |
| SHA1: | 18D0A562762A6772D8B80864B35F28D2388DE765 |
| SHA256: | CFAABF7C5F4A71687C0A2E67CC2DF86E6CC2DE75F13398D03DA5935025EB9DE0 |
| SSDEEP: | 3:gkJR9dBSAKDDnYPuChIVpaays9WTH7SH9fpd+n+rr8oxzIs0EjNh1ksf9ME7Mv:P7GdDpVVp5y5709T++rr5xMV0lMv |
MALICIOUS
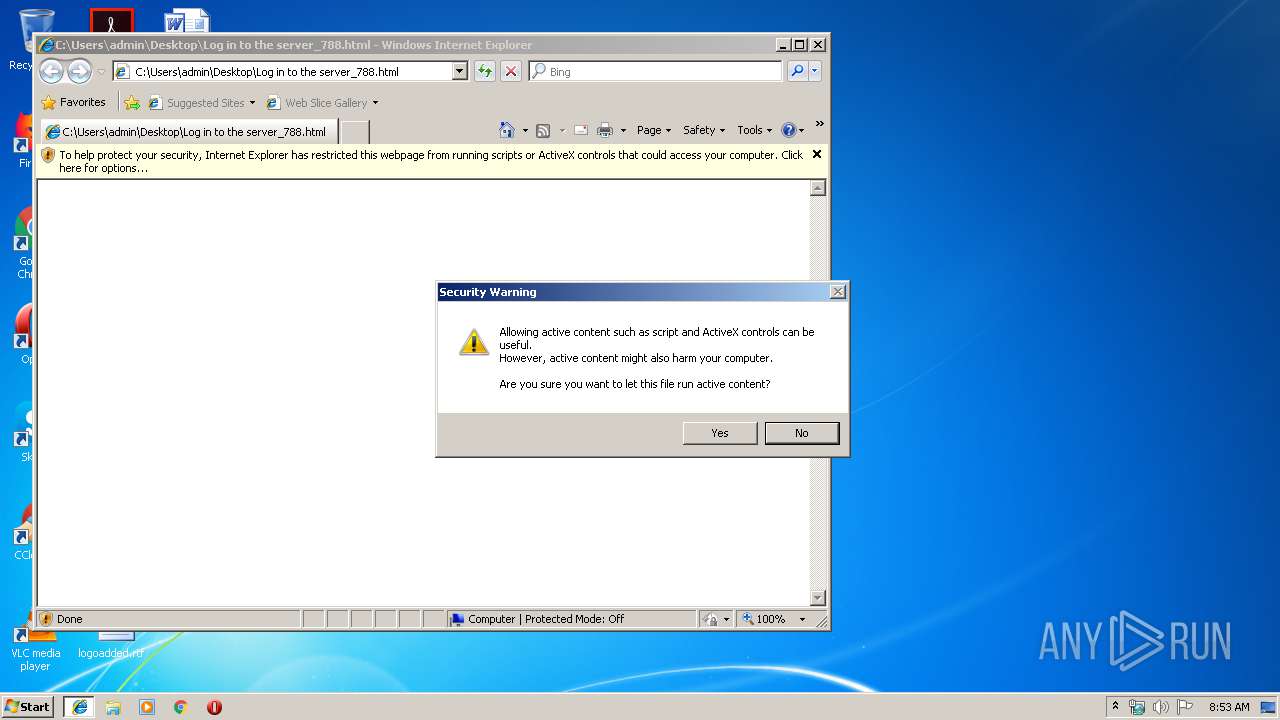
Runs injected code in another process
- chrome.exe (PID: 3908)
Application was injected by another process
- dllhost.exe (PID: 1472)
SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 3908)
INFO
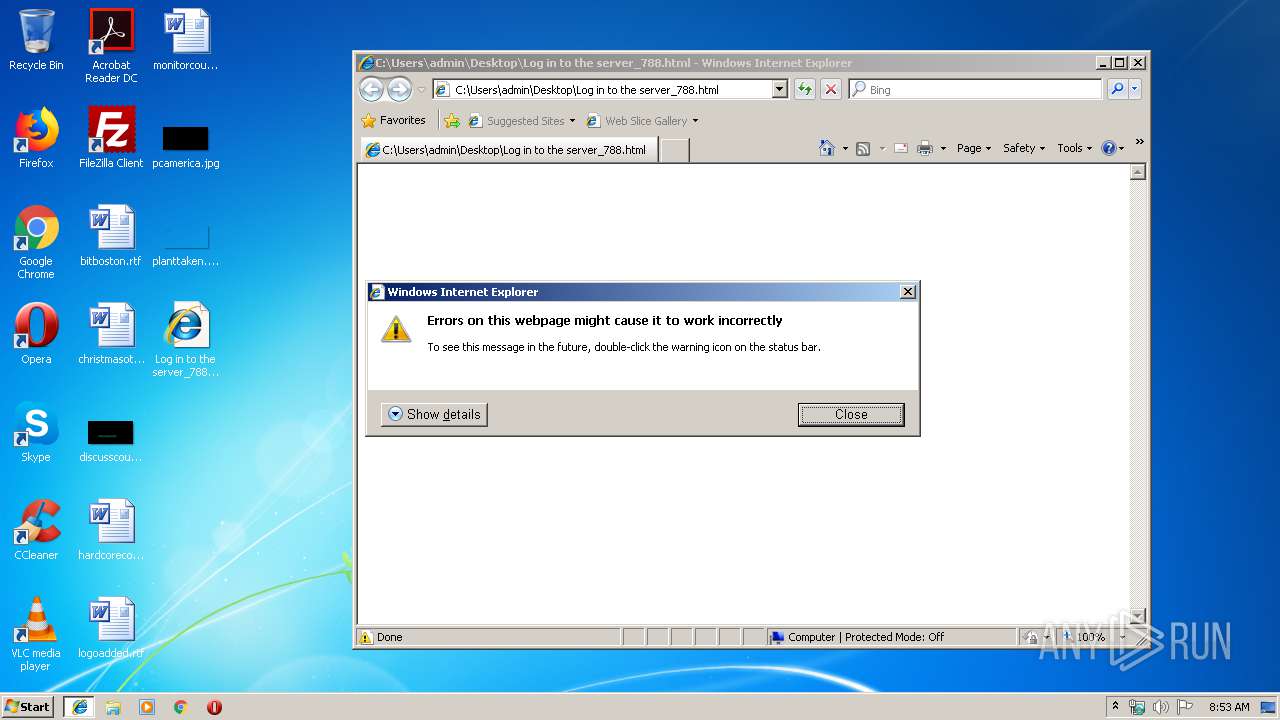
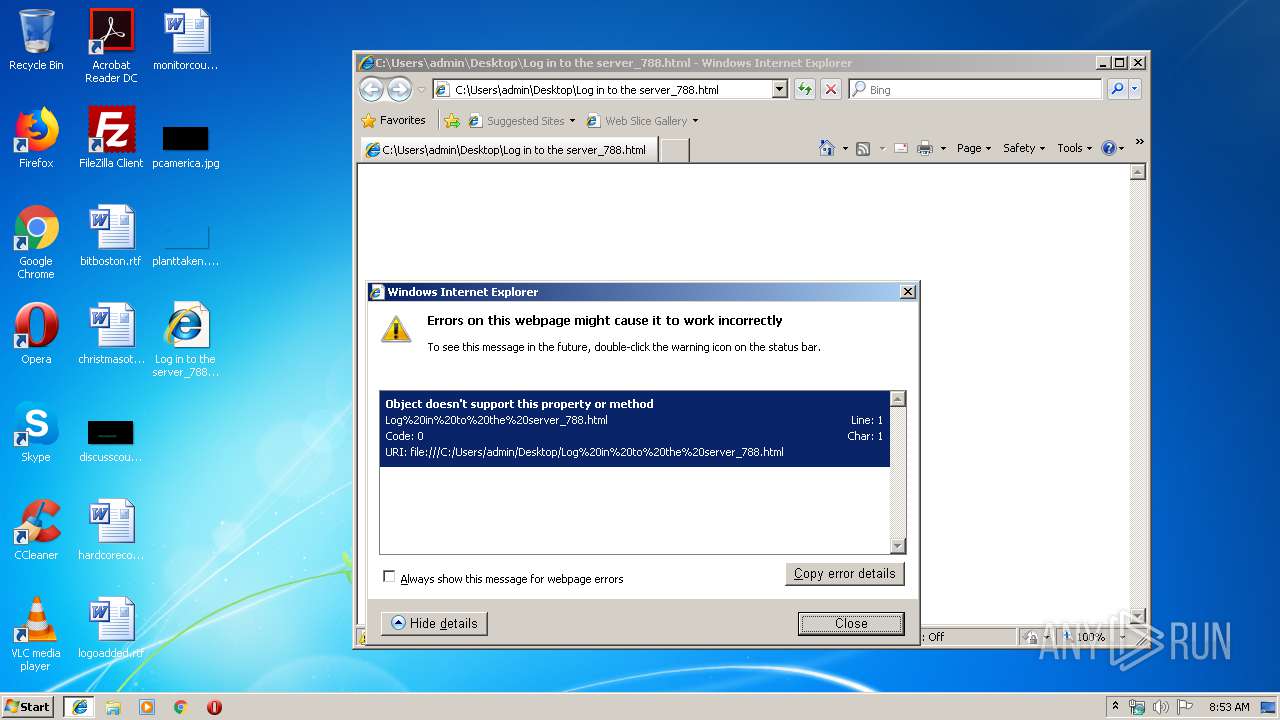
Reads Internet Cache Settings
- iexplore.exe (PID: 3508)
- iexplore.exe (PID: 1832)
Changes internet zones settings
- iexplore.exe (PID: 3508)
Reads internet explorer settings
- iexplore.exe (PID: 1832)
Application launched itself
- chrome.exe (PID: 3908)
- iexplore.exe (PID: 3508)
Creates files in the user directory
- iexplore.exe (PID: 3508)
- iexplore.exe (PID: 1832)
Reads settings of System Certificates
- chrome.exe (PID: 3204)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
55
Monitored processes
23
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1076 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=972,15237543322964082855,7740822831717582897,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=13021303047102877018 --mojo-platform-channel-handle=2820 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1356 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=972,15237543322964082855,7740822831717582897,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=5431978148308239012 --mojo-platform-channel-handle=3632 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1472 | dllhost.exe | svchost.exe | |||||||||||||
Integrity Level: UNKNOWN Exit code: 0 Modules
| |||||||||||||||
| 1472 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=972,15237543322964082855,7740822831717582897,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAACAAwAAAQAAAAAAAAAAAGAAAAAAAAEAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=10383007127274131320 --mojo-platform-channel-handle=976 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1796 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=972,15237543322964082855,7740822831717582897,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=7919058957360723873 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=7919058957360723873 --renderer-client-id=19 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3548 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1832 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3508 CREDAT:79873 | C:\Program Files\Internet Explorer\iexplore.exe | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2636 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=73.0.3683.75 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6fa50f18,0x6fa50f28,0x6fa50f34 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2800 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=972,15237543322964082855,7740822831717582897,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=10326910996023556001 --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=10326910996023556001 --renderer-client-id=16 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2744 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2804 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=972,15237543322964082855,7740822831717582897,131072 --enable-features=PasswordImport --service-pipe-token=11525086601392128695 --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=11525086601392128695 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2376 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2852 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=972,15237543322964082855,7740822831717582897,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAACAAwAAAQAAAAAAAAAAAGAAAAAAAAEAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=14818058742165822499 --mojo-platform-channel-handle=3944 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
Total events
971
Read events
802
Write events
163
Delete events
6
Modification events
| (PID) Process: | (3508) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3508) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3508) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3508) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (3508) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3508) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 460000006E000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3508) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {C86AF69B-4BB6-11E9-B63D-5254004A04AF} |
Value: 0 | |||
| (PID) Process: | (3508) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Type |
Value: 4 | |||
| (PID) Process: | (3508) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Count |
Value: 1 | |||
| (PID) Process: | (3508) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Time |
Value: E3070300040015000800350018008001 | |||
Executable files
0
Suspicious files
67
Text files
172
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3508 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFD69D7C89719DDFB6.TMP | — | |
MD5:— | SHA256:— | |||
| 3508 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF2FC3C21020E8AE06.TMP | — | |
MD5:— | SHA256:— | |||
| 3508 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF9423C472592C0E1A.TMP | — | |
MD5:— | SHA256:— | |||
| 3508 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\{C86AF69C-4BB6-11E9-B63D-5254004A04AF}.dat | — | |
MD5:— | SHA256:— | |||
| 3508 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\9FZR4O070M1GHA54NL7N.temp | — | |
MD5:— | SHA256:— | |||
| 3508 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFB9DD1E17985B6A59.TMP | — | |
MD5:— | SHA256:— | |||
| 3508 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\RecoveryStore.{C86AF69B-4BB6-11E9-B63D-5254004A04AF}.dat | — | |
MD5:— | SHA256:— | |||
| 3908 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 3908 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 3908 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
45
TCP/UDP connections
68
DNS requests
23
Threats
45
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
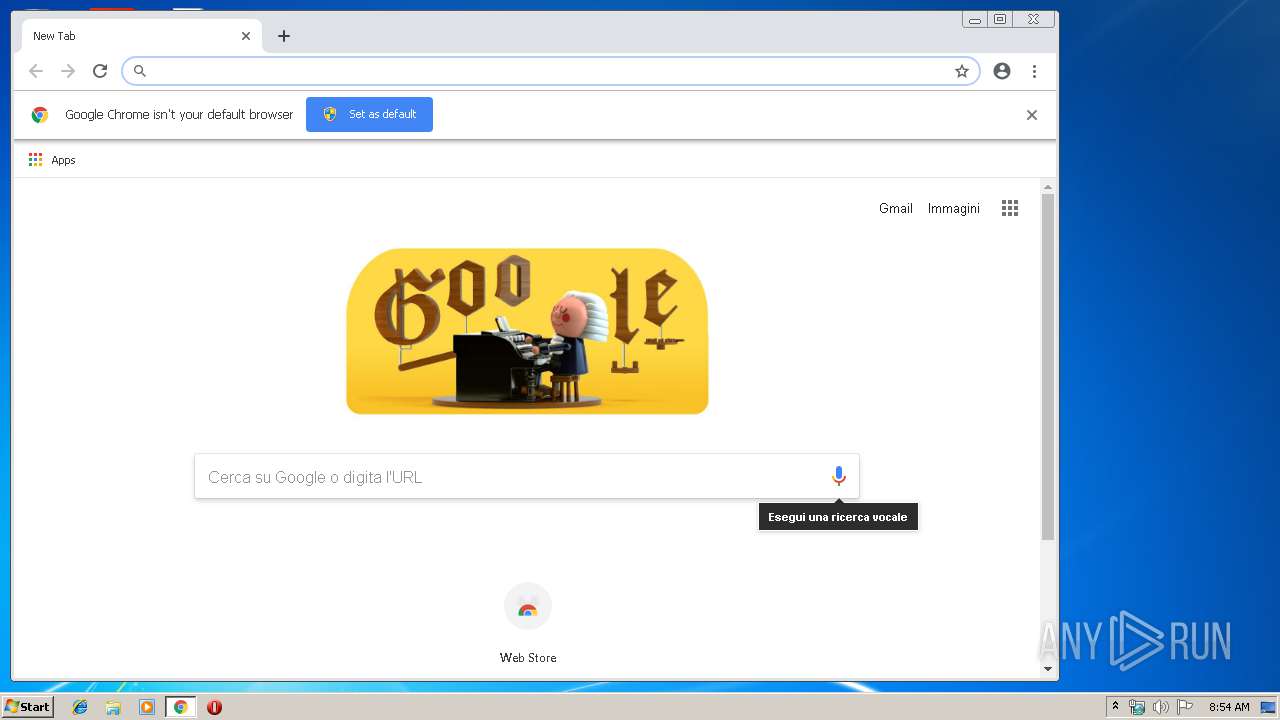
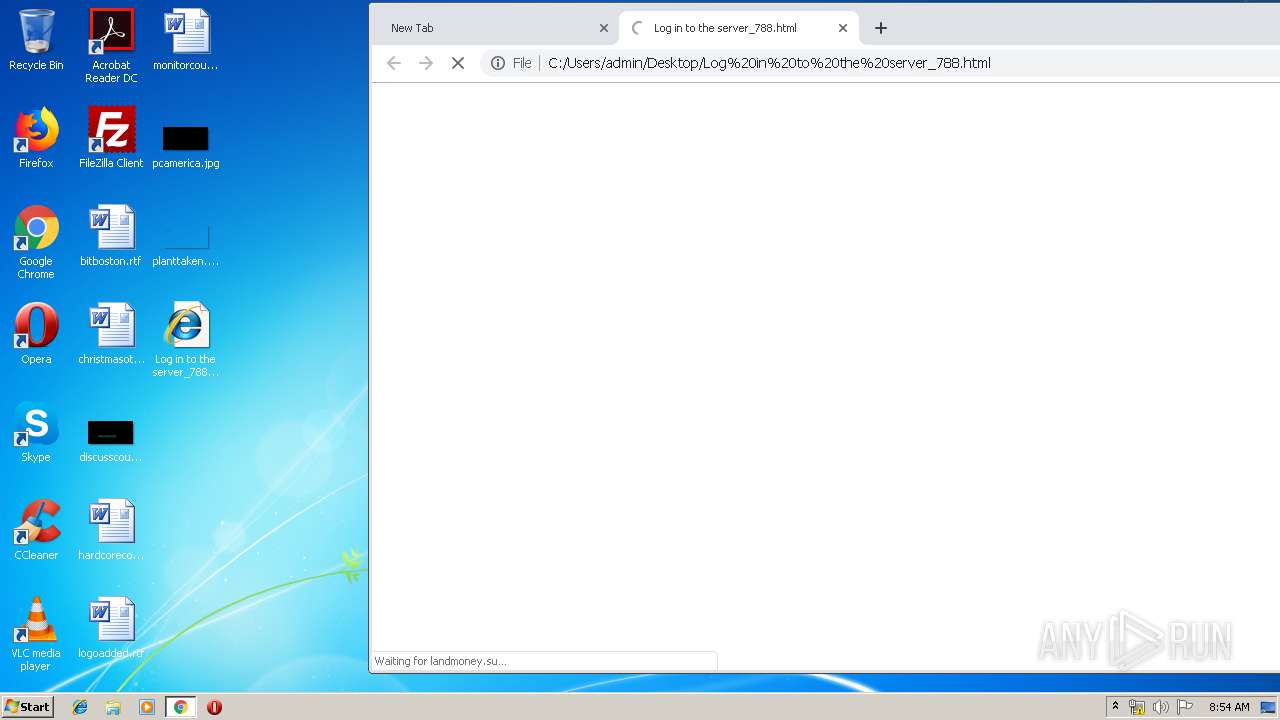
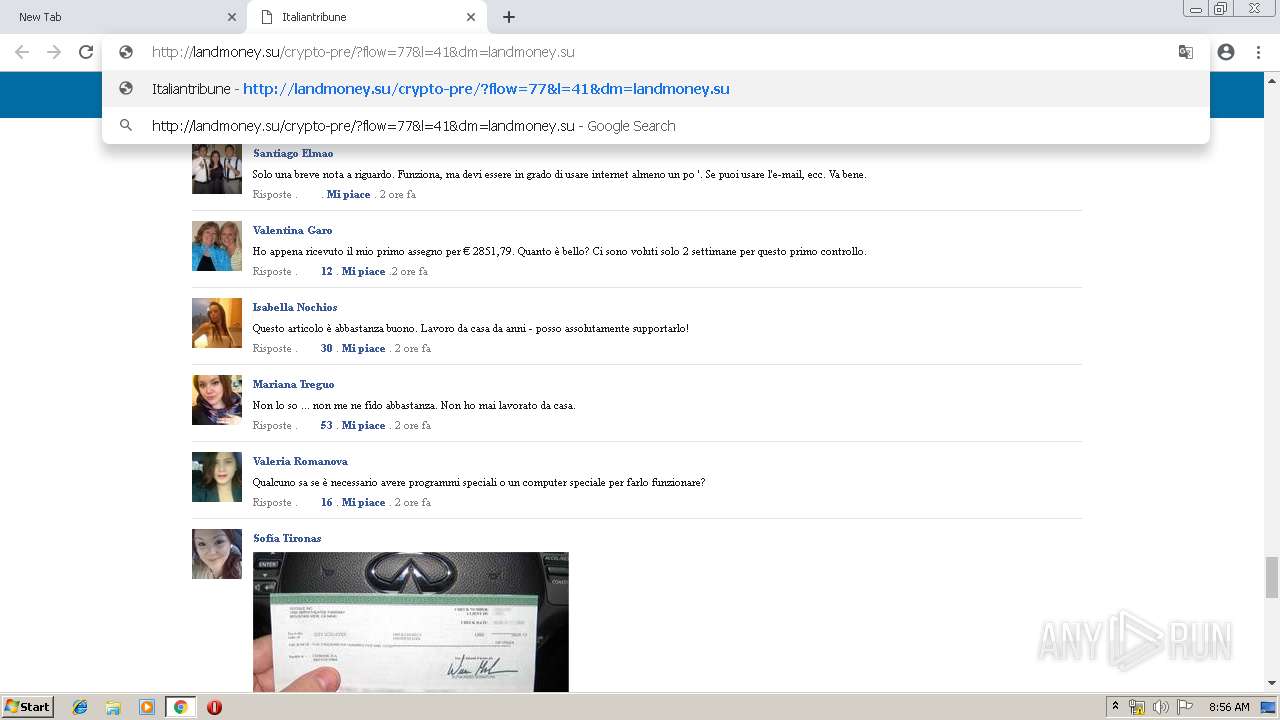
3204 | chrome.exe | GET | — | 47.254.145.114:80 | http://landmoney.su/crypto-pre/937/pre/css/74Z12AG3CD8H.css | US | — | — | suspicious |
3204 | chrome.exe | GET | 302 | 91.215.153.90:80 | http://top.nov.ru/hBm79Q | BG | — | — | suspicious |
3204 | chrome.exe | GET | 302 | 47.254.145.114:80 | http://moneyone.su/go77 | US | — | — | suspicious |
3204 | chrome.exe | GET | — | 47.254.145.114:80 | http://landmoney.su/crypto-pre/937/pre/js/getdetector.js | US | — | — | suspicious |
3204 | chrome.exe | GET | 200 | 47.254.145.114:80 | http://landmoney.su/crypto-pre/937/pre/images/HIO83KMCJYI5.png | US | image | 28.6 Kb | suspicious |
3204 | chrome.exe | GET | 200 | 47.254.145.114:80 | http://landmoney.su/crypto-pre/937/pre/css/22SDUZWFC7AT.css | US | text | 21.1 Kb | suspicious |
3204 | chrome.exe | GET | 200 | 74.125.11.169:80 | http://r4---sn-hgn7yn7l.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvMjJlQUFXRC12Ny1ldUFnMXF3SDlXZDlFZw/7319.128.0.1_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=185.128.27.133&mm=28&mn=sn-hgn7yn7l&ms=nvh&mt=1553158339&mv=m&pl=24&shardbypass=yes | US | crx | 842 Kb | whitelisted |
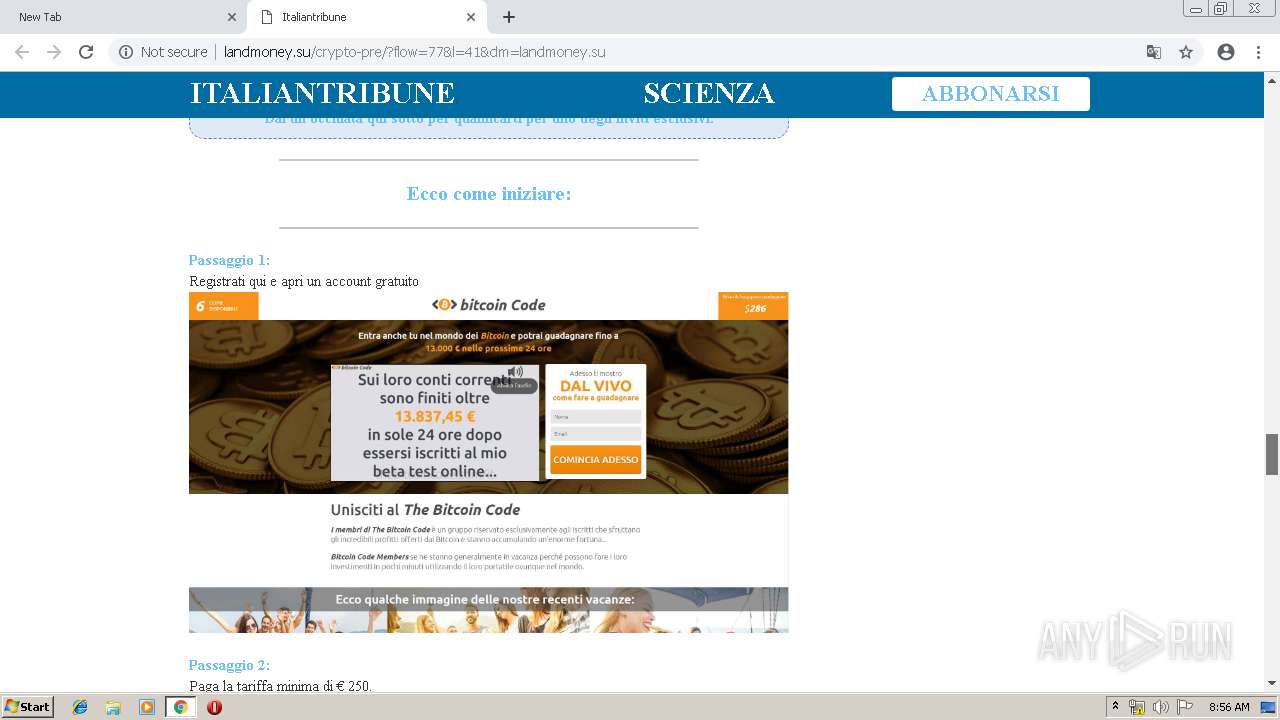
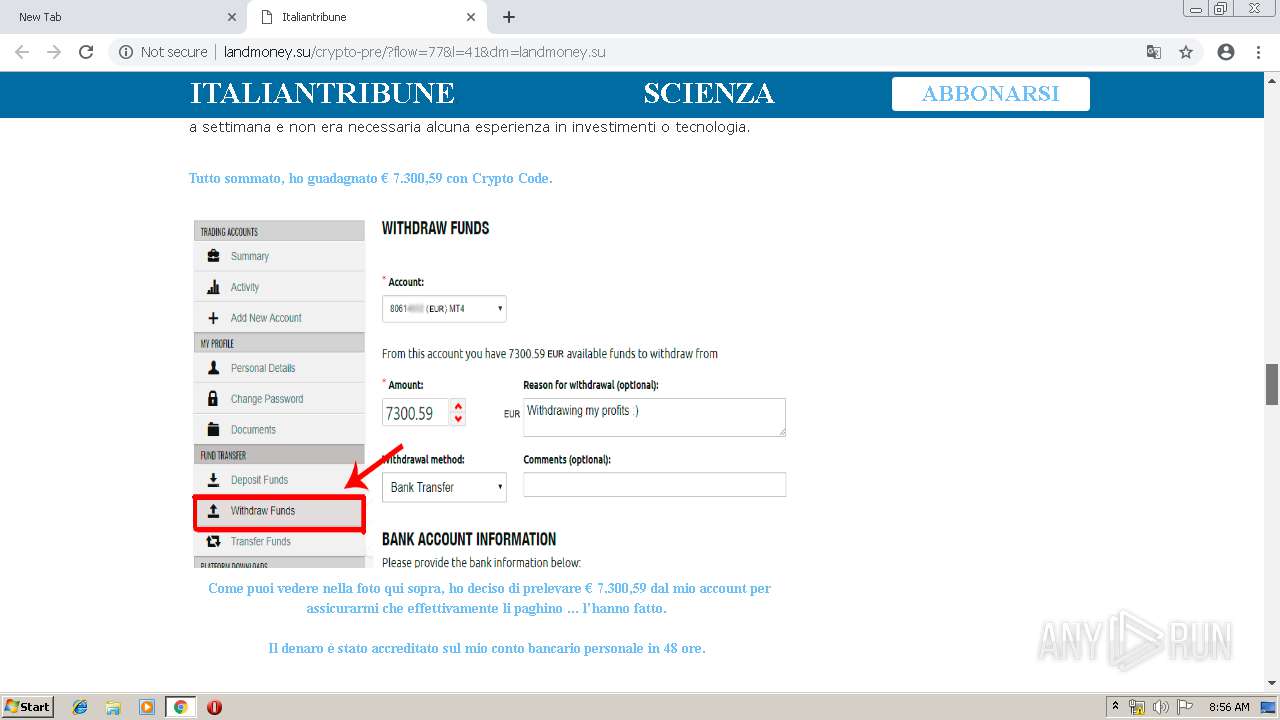
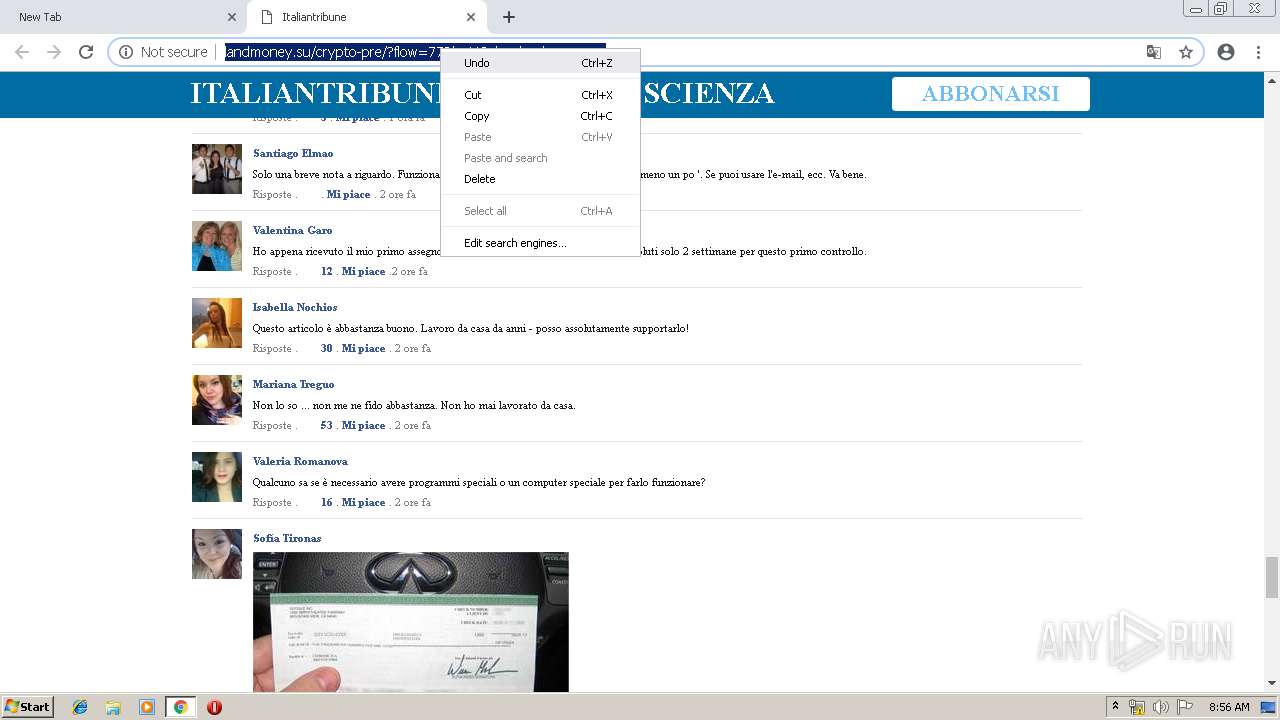
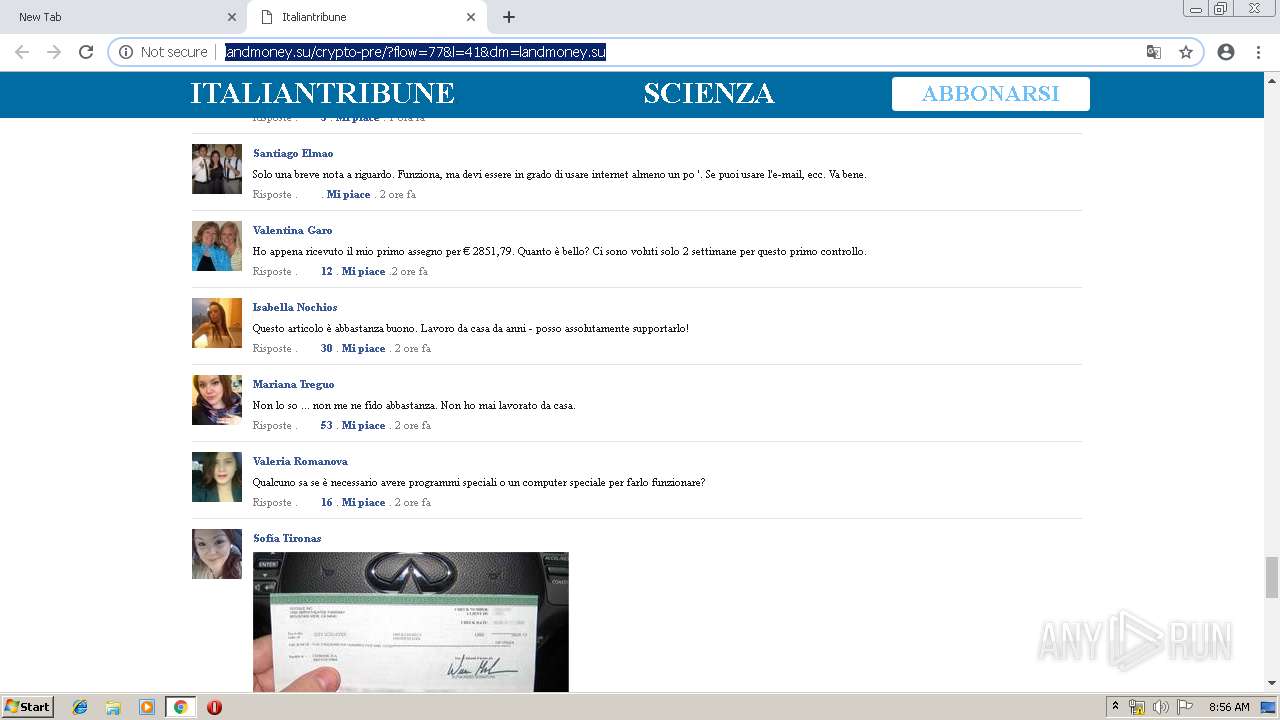
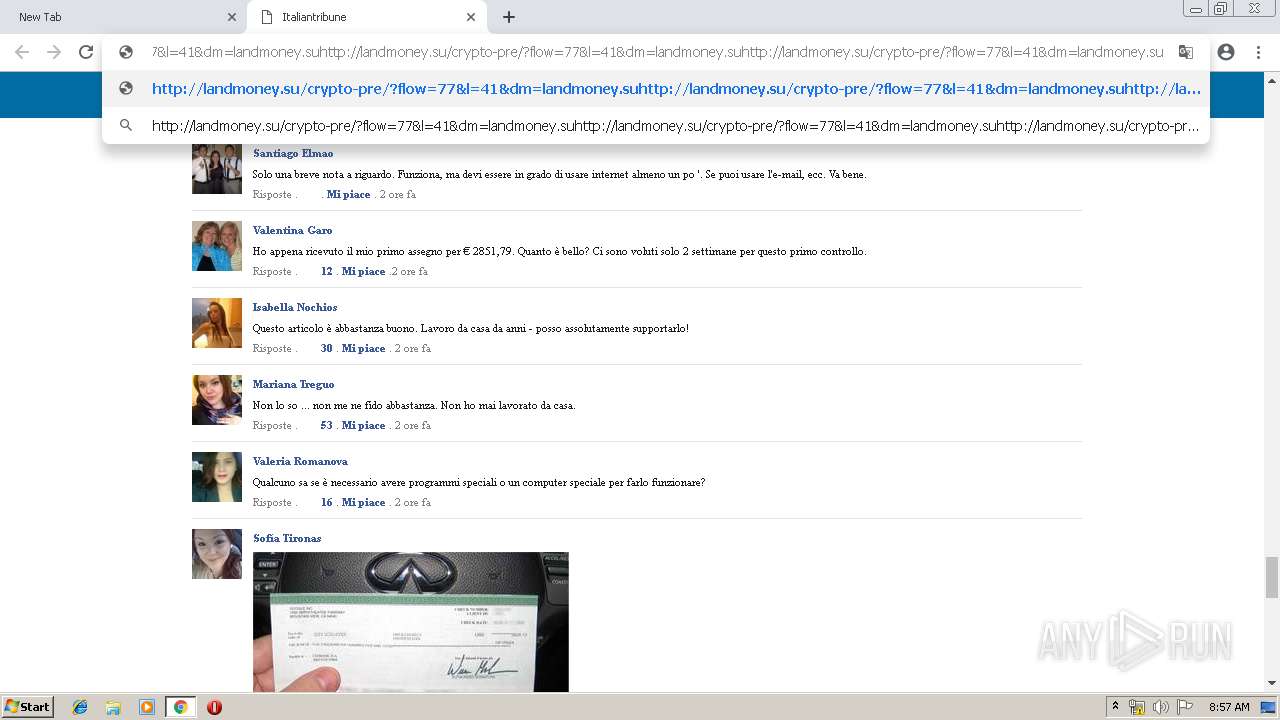
3204 | chrome.exe | GET | 200 | 47.254.145.114:80 | http://landmoney.su/crypto-pre/?flow=77&l=41&dm=landmoney.su | US | html | 13.1 Kb | suspicious |
3204 | chrome.exe | GET | 200 | 47.254.145.114:80 | http://landmoney.su/crypto-pre/937/pre/images/TH4RG10EWM3V.png | US | image | 4.33 Kb | suspicious |
3204 | chrome.exe | GET | 200 | 47.254.145.114:80 | http://landmoney.su/crypto-pre/937/pre/css/DSUCP0X14H8C.css | US | text | 3.48 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3508 | iexplore.exe | 13.107.21.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3508 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3204 | chrome.exe | 216.58.210.4:443 | www.google.com | Google Inc. | US | whitelisted |
3204 | chrome.exe | 172.217.23.131:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3204 | chrome.exe | 216.58.208.35:443 | www.gstatic.com | Google Inc. | US | whitelisted |
3204 | chrome.exe | 216.58.205.234:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
3204 | chrome.exe | 216.58.207.46:443 | apis.google.com | Google Inc. | US | whitelisted |
3204 | chrome.exe | 172.217.22.10:443 | ajax.googleapis.com | Google Inc. | US | whitelisted |
3204 | chrome.exe | 104.111.241.197:443 | jseigbxz.us14.list-manage.com | Akamai International B.V. | NL | whitelisted |
3204 | chrome.exe | 74.125.11.169:80 | r4---sn-hgn7yn7l.gvt1.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
dns.msftncsi.com |
| shared |
www.google.com |
| malicious |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
ssl.gstatic.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
ajax.googleapis.com |
| whitelisted |
apis.google.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1048 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .su TLD (Soviet Union) Often Malware Related |
3204 | chrome.exe | Potentially Bad Traffic | ET POLICY HTTP Request to .su TLD (Soviet Union) Often Malware Related |
1048 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .su TLD (Soviet Union) Often Malware Related |
3204 | chrome.exe | Potentially Bad Traffic | ET CURRENT_EVENTS Possible Keitaro TDS Redirect |
3204 | chrome.exe | Potentially Bad Traffic | ET POLICY HTTP Request to .su TLD (Soviet Union) Often Malware Related |
3204 | chrome.exe | Potentially Bad Traffic | ET POLICY HTTP Request to .su TLD (Soviet Union) Often Malware Related |
3204 | chrome.exe | Potentially Bad Traffic | ET POLICY HTTP Request to .su TLD (Soviet Union) Often Malware Related |
3204 | chrome.exe | Potentially Bad Traffic | ET POLICY HTTP Request to .su TLD (Soviet Union) Often Malware Related |
3204 | chrome.exe | Potentially Bad Traffic | ET POLICY HTTP Request to .su TLD (Soviet Union) Often Malware Related |
3204 | chrome.exe | Potentially Bad Traffic | ET POLICY HTTP Request to .su TLD (Soviet Union) Often Malware Related |