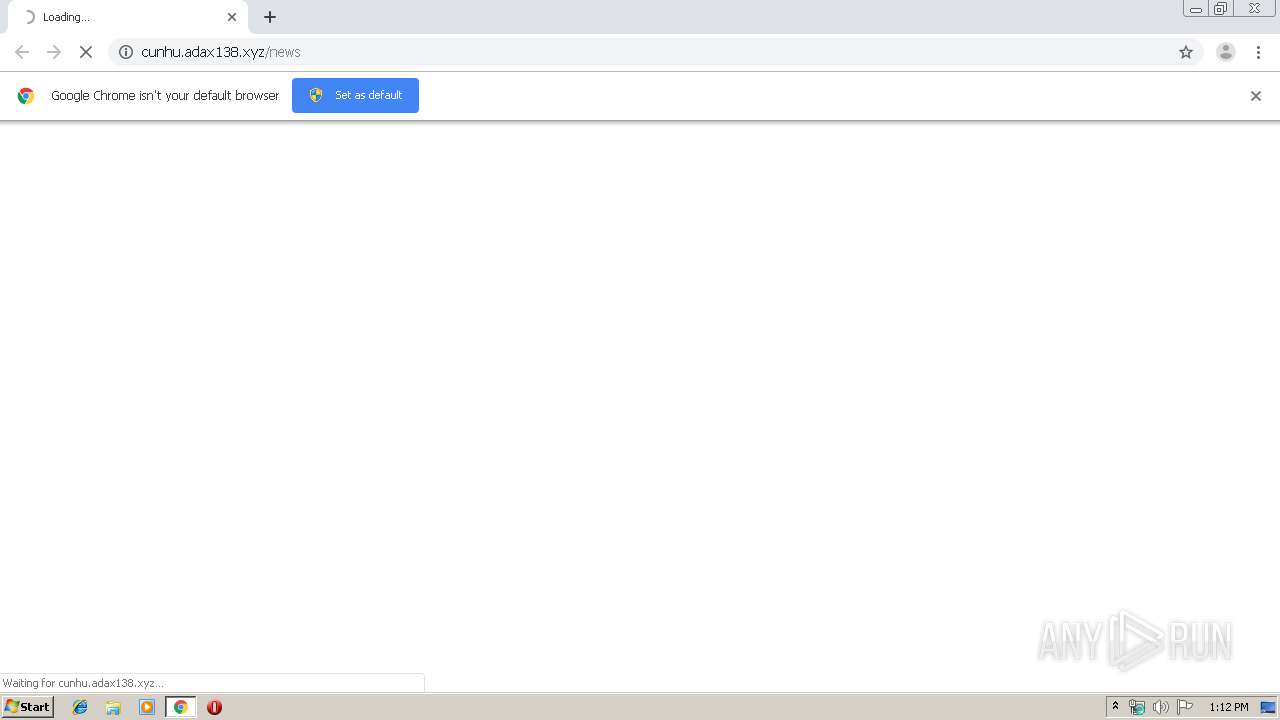
| URL: | http://cunhu.aDax138.xyz/news |
| Full analysis: | https://app.any.run/tasks/3f3096b5-88b6-4801-b461-835dd1e9f5f8 |
| Verdict: | Malicious activity |
| Analysis date: | October 14, 2019, 12:11:45 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 8ED8FDDCB9E9C9093C16E485F3528387 |
| SHA1: | B4EA8E76D71960F758291F2E4B51DCDD8F4C8D39 |
| SHA256: | CF9514BCEC04936274313917F70C004B4DF59F673566D3202B4FF3A7274DEB0A |
| SSDEEP: | 3:N1KdQxWdMK0l:CSxaL0l |
MALICIOUS
No malicious indicators.SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 2300)
INFO
Application launched itself
- chrome.exe (PID: 2300)
Reads the hosts file
- chrome.exe (PID: 2300)
- chrome.exe (PID: 1896)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
64
Monitored processes
29
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 184 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1020,11730090466670949264,8819684291380496565,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=17349325008888405291 --mojo-platform-channel-handle=4048 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 444 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1020,11730090466670949264,8819684291380496565,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=4655097082995395890 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2252 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 616 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1020,11730090466670949264,8819684291380496565,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=7919859288330055052 --mojo-platform-channel-handle=3928 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1636 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1020,11730090466670949264,8819684291380496565,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=6868166930992467196 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2468 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1712 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1020,11730090466670949264,8819684291380496565,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=11806951783017346997 --mojo-platform-channel-handle=4488 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1788 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1020,11730090466670949264,8819684291380496565,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=349643286496266000 --mojo-platform-channel-handle=4820 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1896 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1020,11730090466670949264,8819684291380496565,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=3742970383937583335 --mojo-platform-channel-handle=1640 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1904 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1020,11730090466670949264,8819684291380496565,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=18318041569521720841 --mojo-platform-channel-handle=4816 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2132 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2644 --on-initialized-event-handle=312 --parent-handle=316 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2208 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1020,11730090466670949264,8819684291380496565,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=1566934347848407712 --mojo-platform-channel-handle=3940 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
632
Read events
531
Write events
96
Delete events
5
Modification events
| (PID) Process: | (2300) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2300) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2300) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2300) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2300) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2132) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2300-13215528720311250 |
Value: 259 | |||
| (PID) Process: | (2300) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2300) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2300) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1512-13197841398593750 |
Value: 0 | |||
| (PID) Process: | (2300) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
154
Text files
252
Unknown types
8
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2300 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\8c4d9234-4d70-411c-8270-7d6d97fe7bef.tmp | — | |
MD5:— | SHA256:— | |||
| 2300 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2300 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2300 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2300 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2300 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF39a91b.TMP | text | |
MD5:— | SHA256:— | |||
| 2300 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF39a92b.TMP | text | |
MD5:— | SHA256:— | |||
| 2300 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 2300 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2300 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
64
TCP/UDP connections
62
DNS requests
32
Threats
62
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1896 | chrome.exe | GET | 302 | 47.254.173.118:80 | http://cunhu.adax138.xyz/news | US | — | — | suspicious |
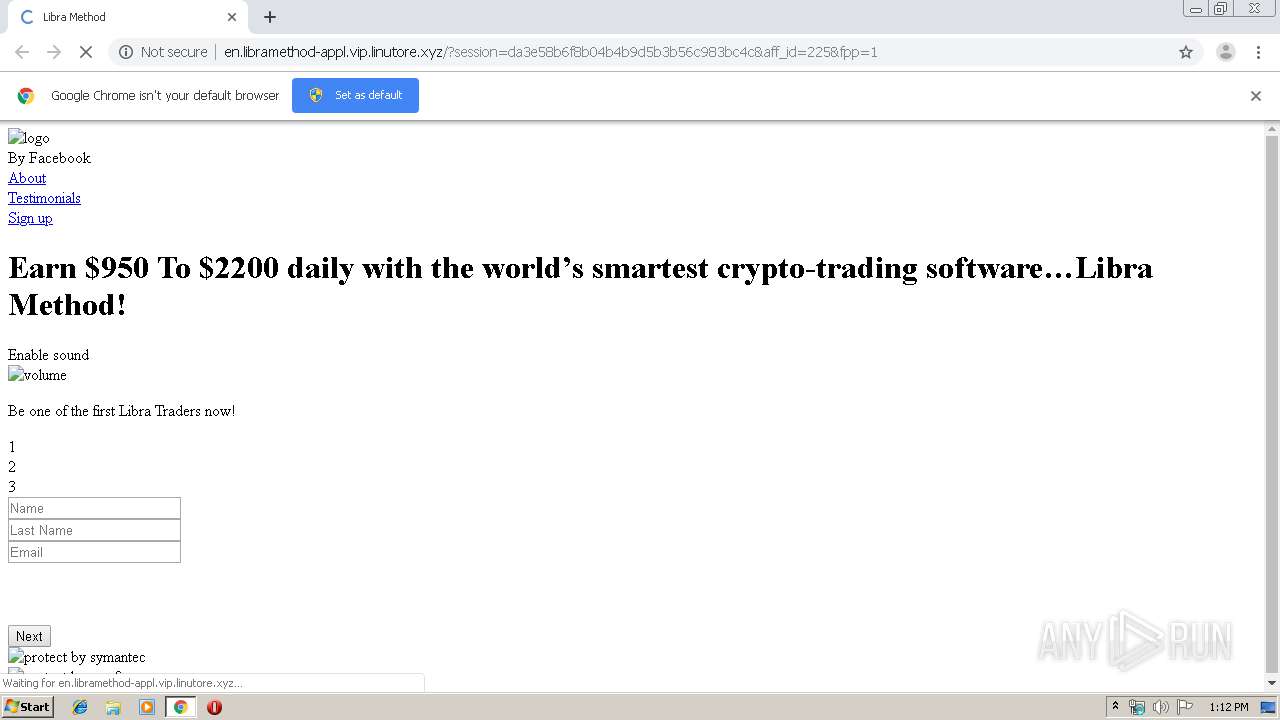
1896 | chrome.exe | GET | 302 | 104.27.163.243:80 | http://vip.linutore.xyz/tracker?s_id=7&aff_id=225 | US | — | — | suspicious |
1896 | chrome.exe | GET | — | 51.15.253.163:80 | http://allinvest.space/favicon.ico | FR | — | — | suspicious |
1896 | chrome.exe | GET | 200 | 51.15.253.163:80 | http://allinvest.space/sl.html | FR | html | 132 b | suspicious |
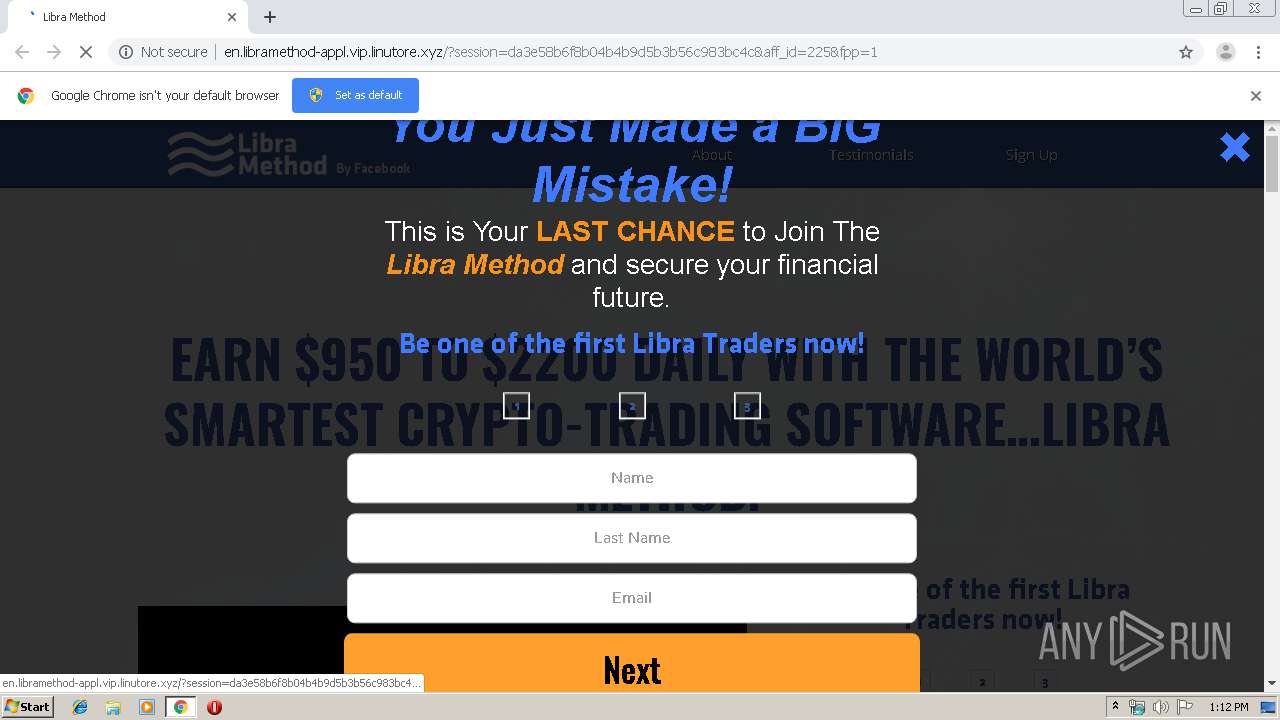
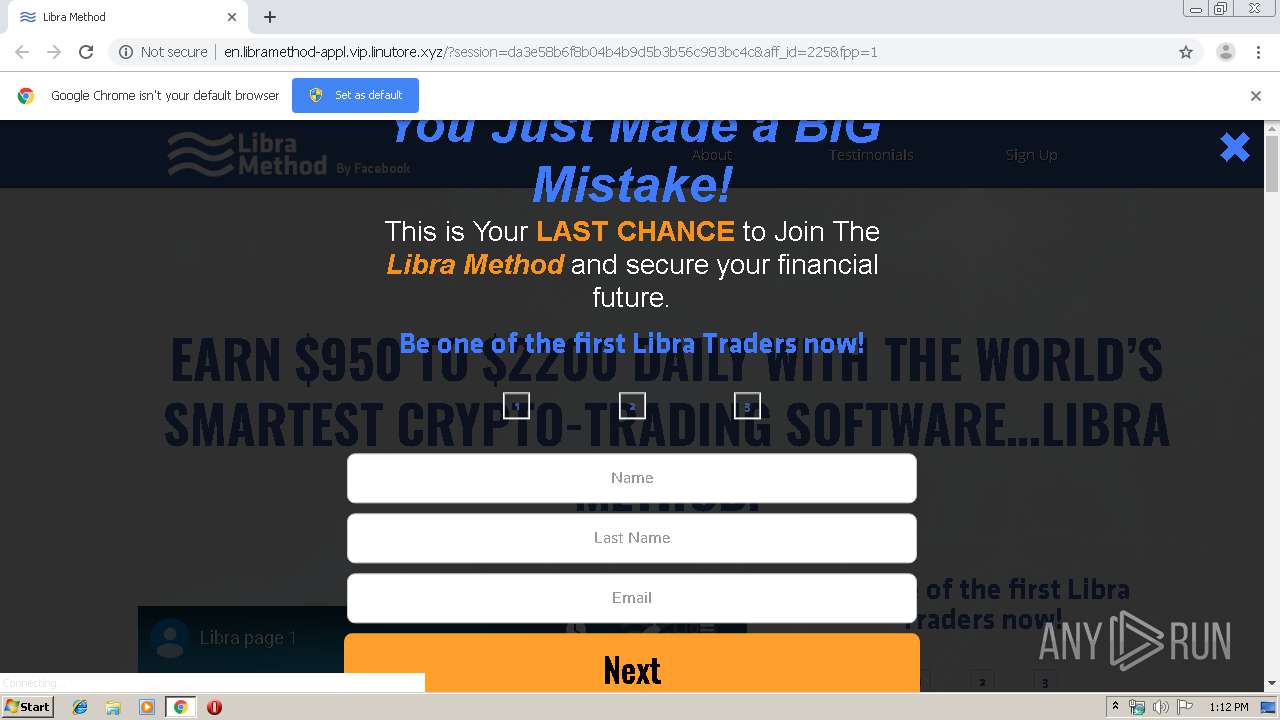
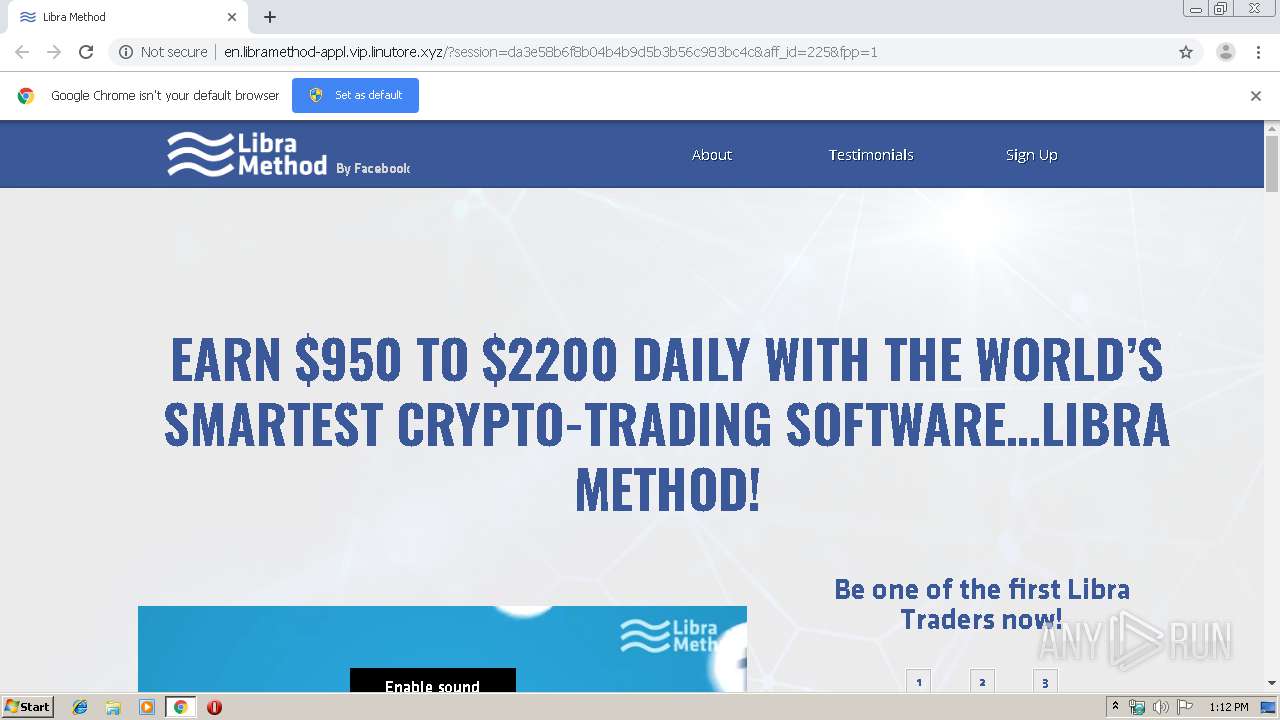
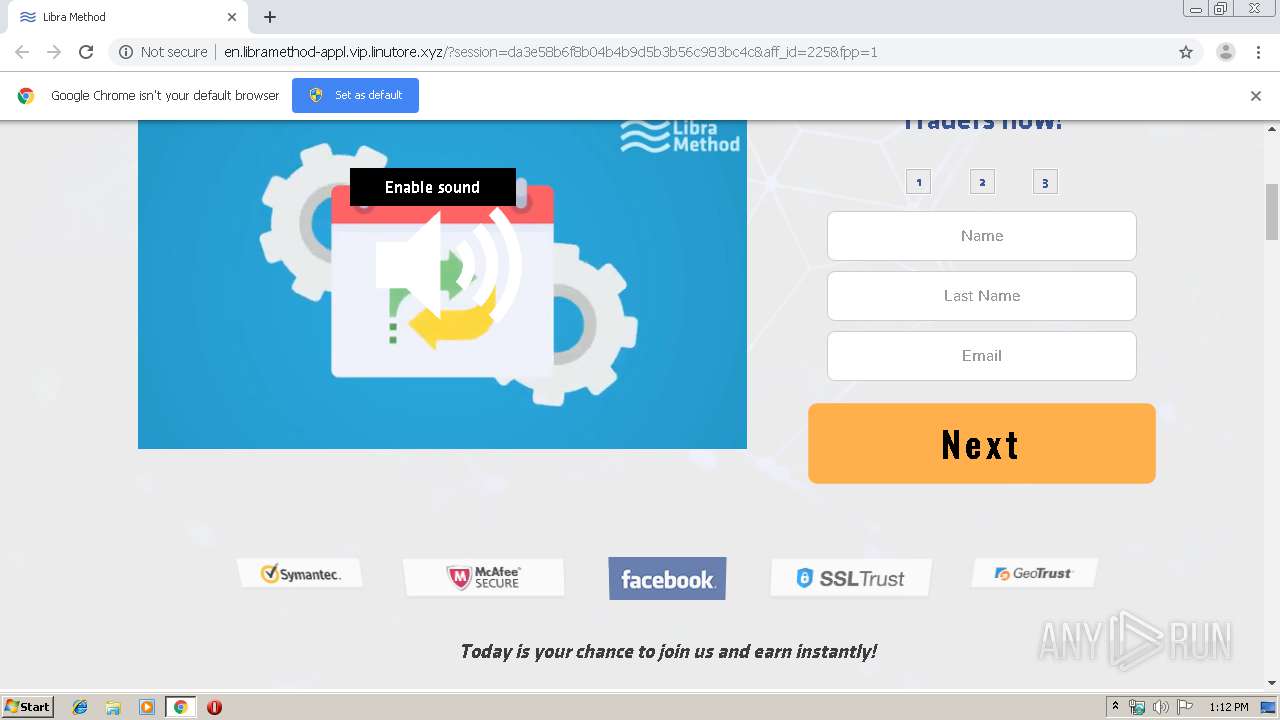
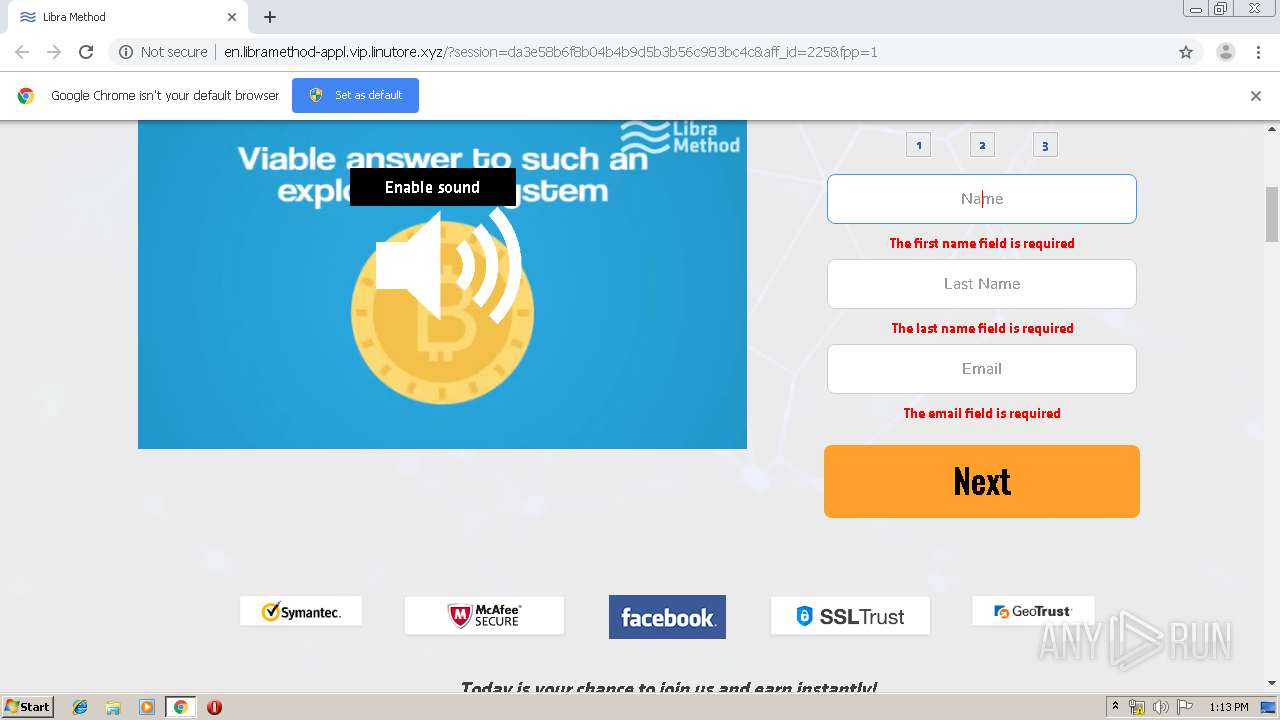
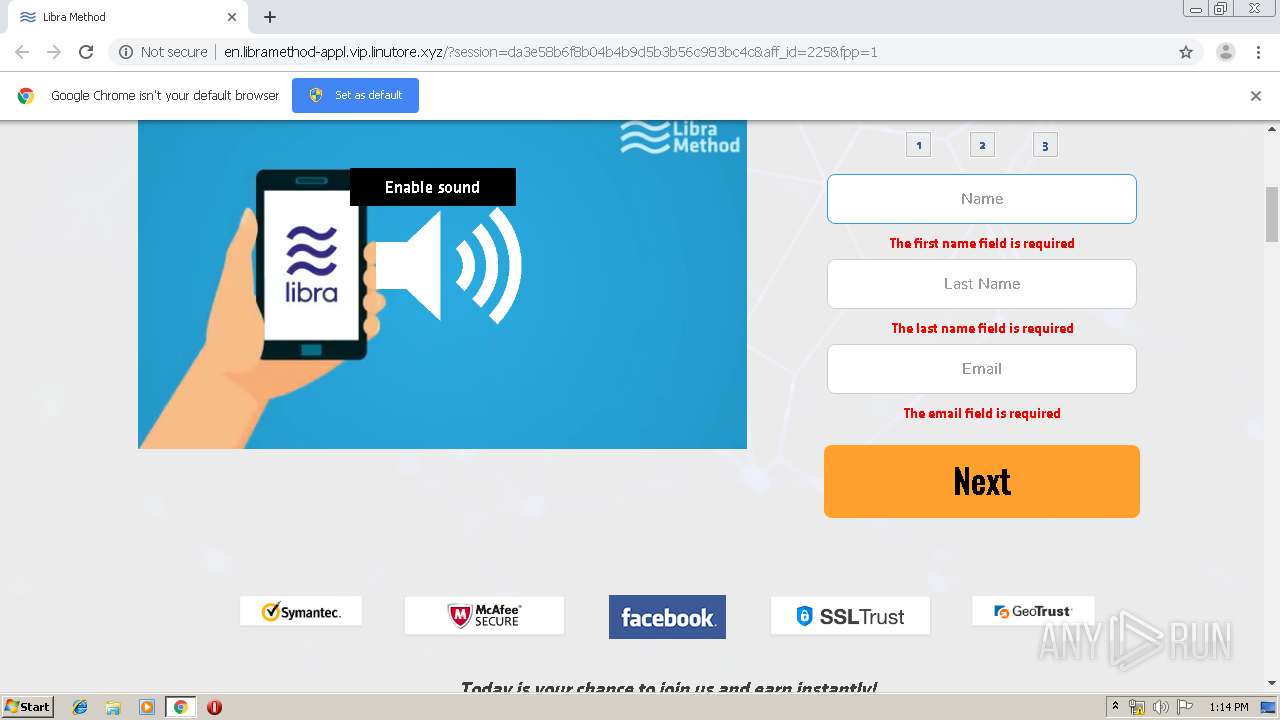
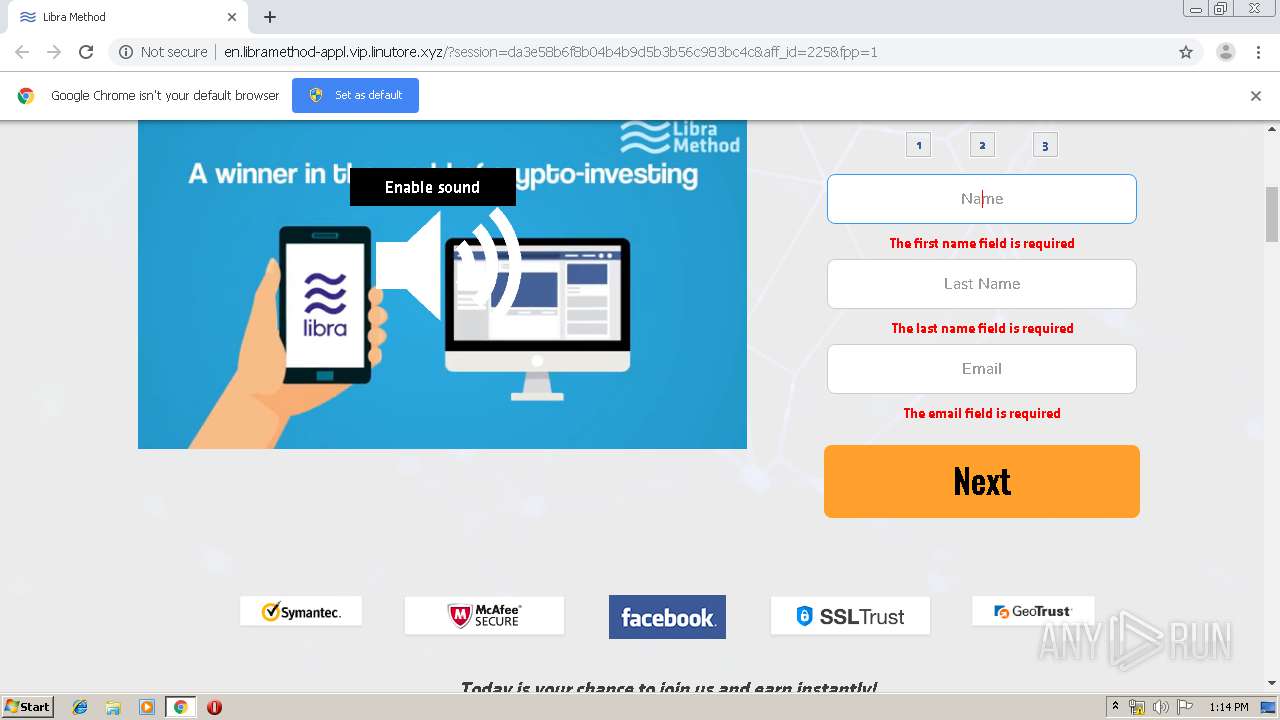
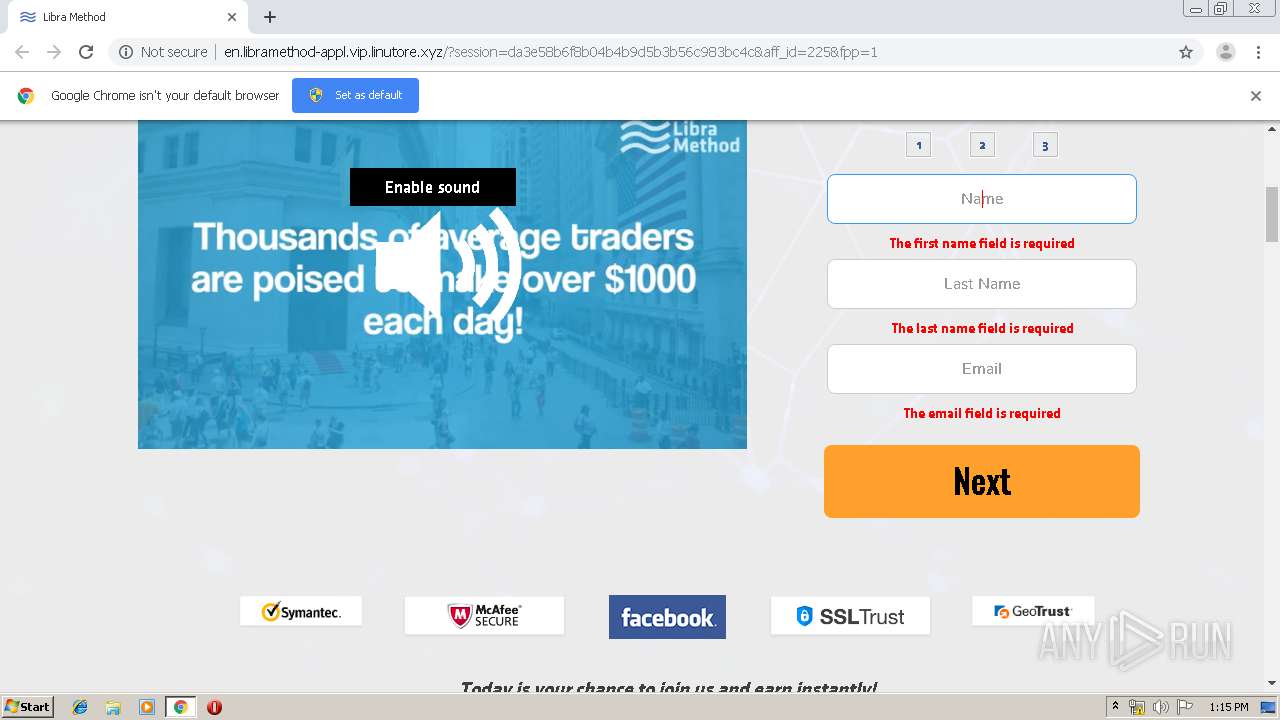
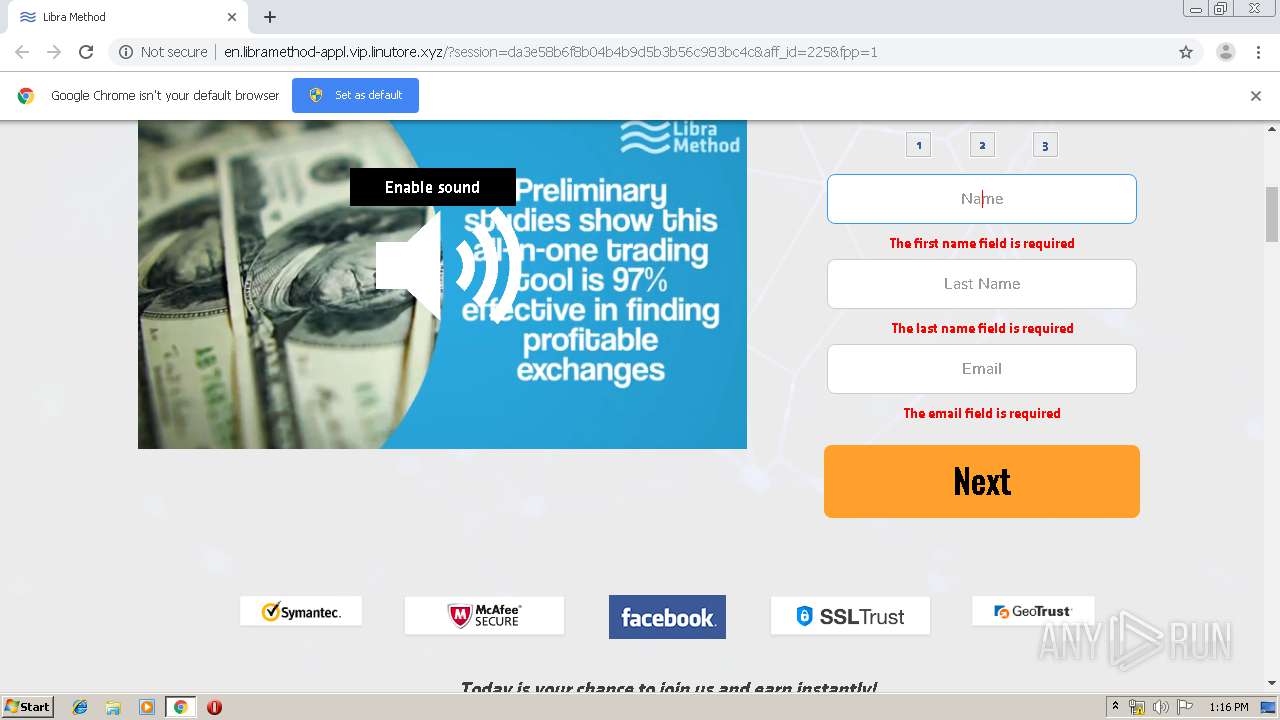
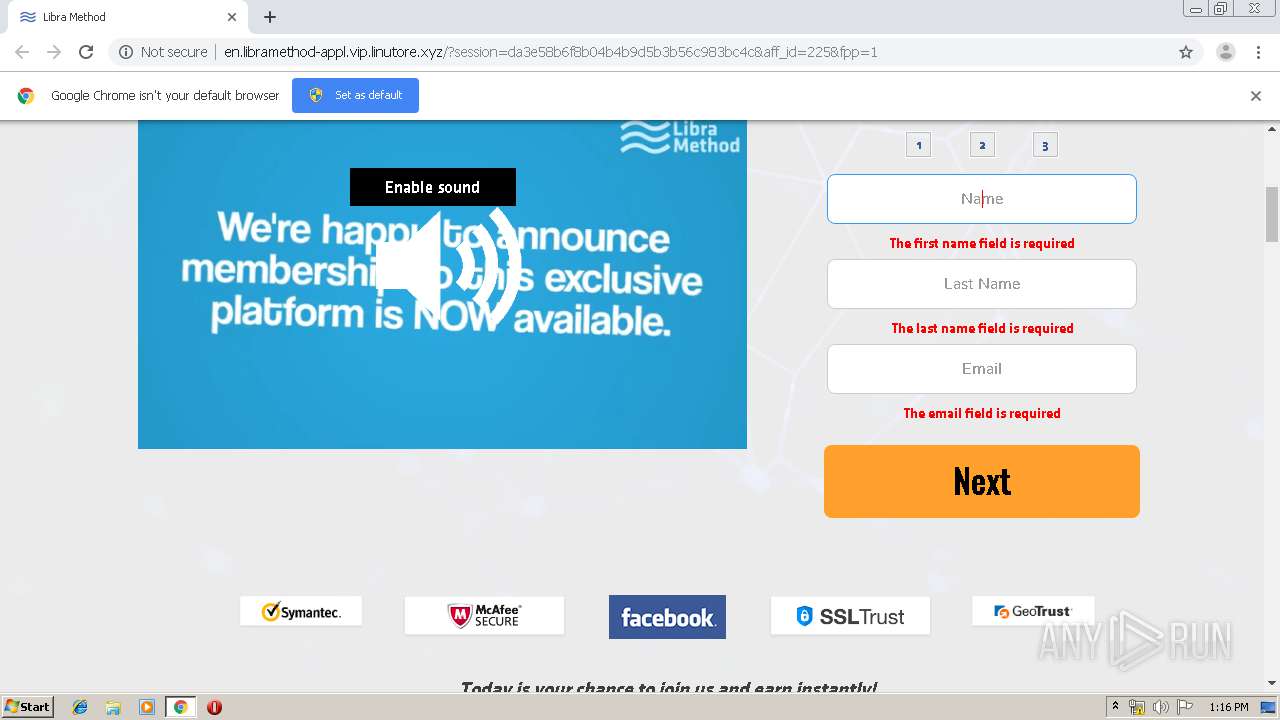
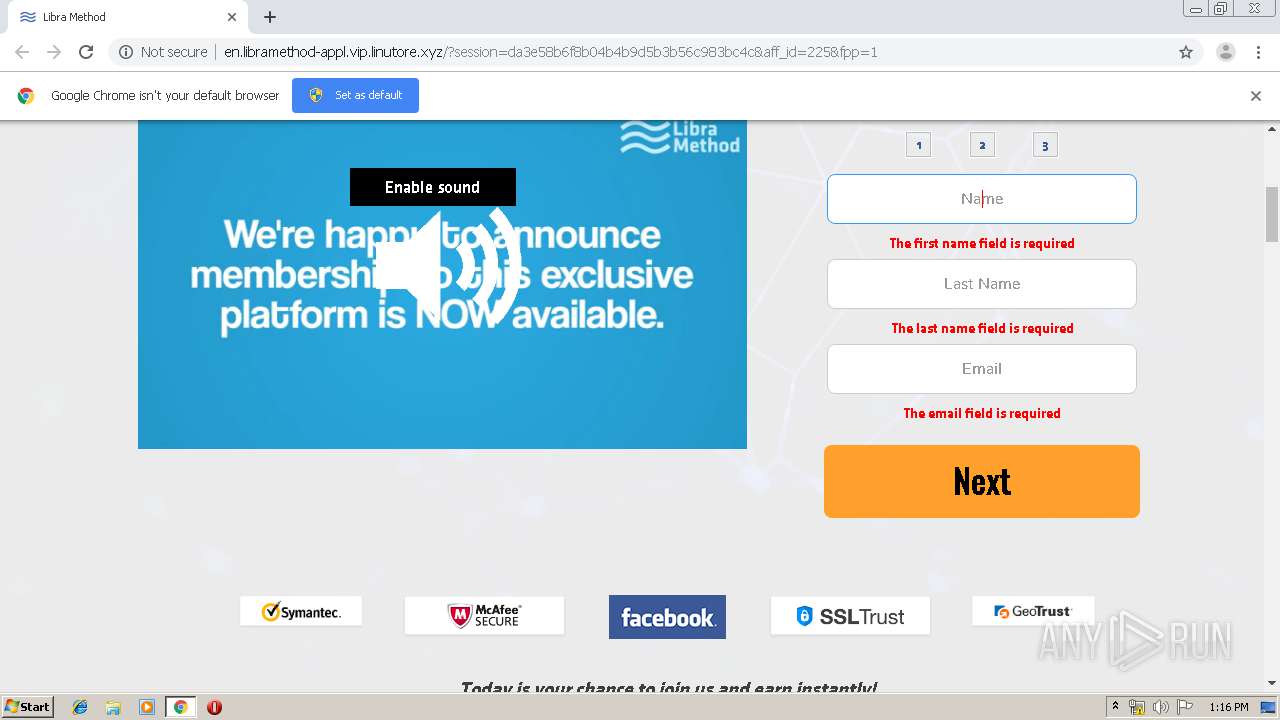
1896 | chrome.exe | GET | 200 | 104.27.162.243:80 | http://en.libramethod-appl.vip.linutore.xyz/?session=da3e58b6f8b04b4b9d5b3b56c983bc4c&aff_id=225&fpp=1 | US | html | 9.84 Kb | suspicious |
1896 | chrome.exe | GET | 200 | 104.27.162.243:80 | http://en.libramethod-appl.vip.linutore.xyz/css/bootstrap.min.css | US | text | 19.2 Kb | suspicious |
1896 | chrome.exe | GET | 200 | 104.27.162.243:80 | http://en.libramethod-appl.vip.linutore.xyz/css/components.css | US | text | 2.45 Kb | suspicious |
1896 | chrome.exe | GET | 200 | 104.27.162.243:80 | http://en.libramethod-appl.vip.linutore.xyz/css/intlTelInput.css | US | text | 2.88 Kb | suspicious |
1896 | chrome.exe | GET | 200 | 104.27.162.243:80 | http://en.libramethod-appl.vip.linutore.xyz/css/font-awesome.min.css | US | text | 5.80 Kb | suspicious |
1896 | chrome.exe | GET | 200 | 104.27.162.243:80 | http://en.libramethod-appl.vip.linutore.xyz/css/libra-method.css | US | text | 4.26 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1896 | chrome.exe | 109.206.188.42:443 | rest.investmen.pw | Serverel Inc. | NL | suspicious |
1896 | chrome.exe | 172.217.22.6:443 | static.doubleclick.net | Google Inc. | US | whitelisted |
1896 | chrome.exe | 172.217.22.97:443 | yt3.ggpht.com | Google Inc. | US | whitelisted |
1896 | chrome.exe | 172.217.18.162:443 | googleads.g.doubleclick.net | Google Inc. | US | whitelisted |
1896 | chrome.exe | 216.58.205.227:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
1896 | chrome.exe | 172.217.18.163:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
1896 | chrome.exe | 47.254.173.118:80 | cunhu.adax138.xyz | Alibaba (China) Technology Co., Ltd. | US | malicious |
1896 | chrome.exe | 51.15.253.163:80 | allinvest.space | Online S.a.s. | FR | unknown |
1896 | chrome.exe | 104.27.163.243:80 | vip.linutore.xyz | Cloudflare Inc | US | suspicious |
1896 | chrome.exe | 104.27.162.243:80 | vip.linutore.xyz | Cloudflare Inc | US | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
cunhu.adax138.xyz |
| suspicious |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
allinvest.space |
| unknown |
vip.linutore.xyz |
| suspicious |
en.libramethod-appl.vip.linutore.xyz |
| suspicious |
www.google.com |
| malicious |
gladwin933.xyz |
| suspicious |
www.googletagmanager.com |
| whitelisted |
www.google-analytics.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1896 | chrome.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
1896 | chrome.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
1896 | chrome.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
1896 | chrome.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
1896 | chrome.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
1896 | chrome.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
1896 | chrome.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
1896 | chrome.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
1896 | chrome.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
1896 | chrome.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |