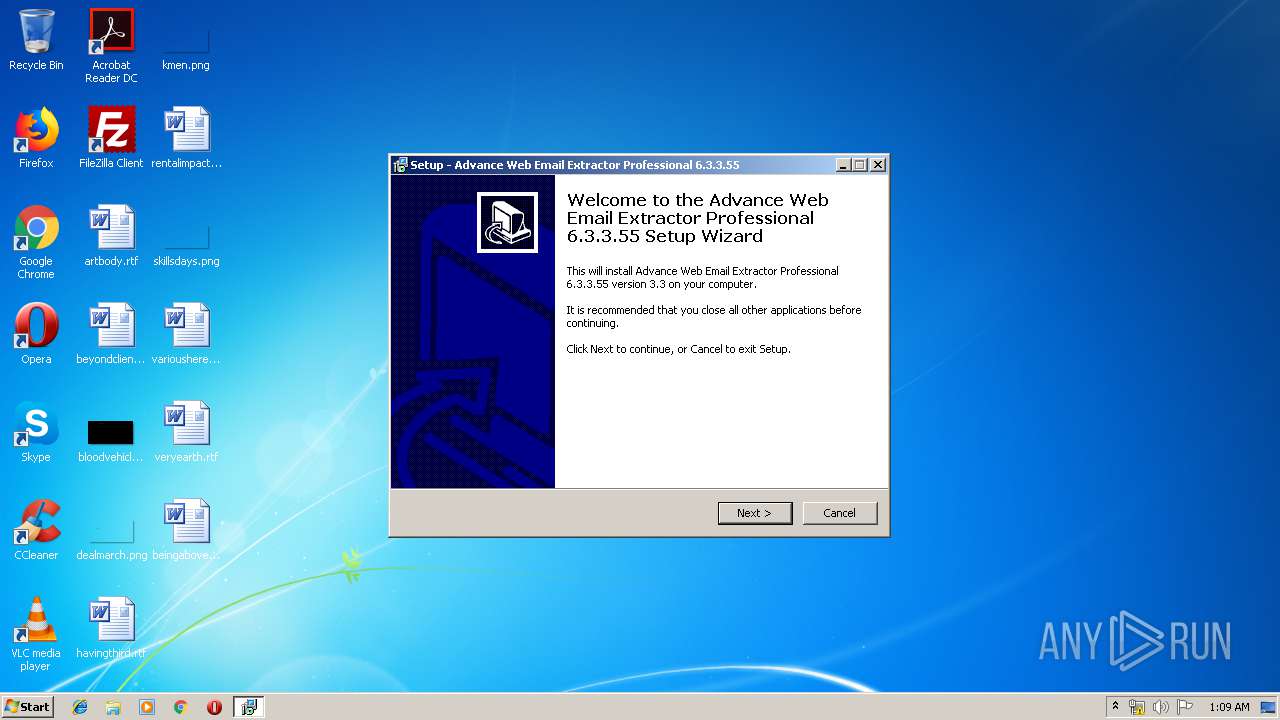
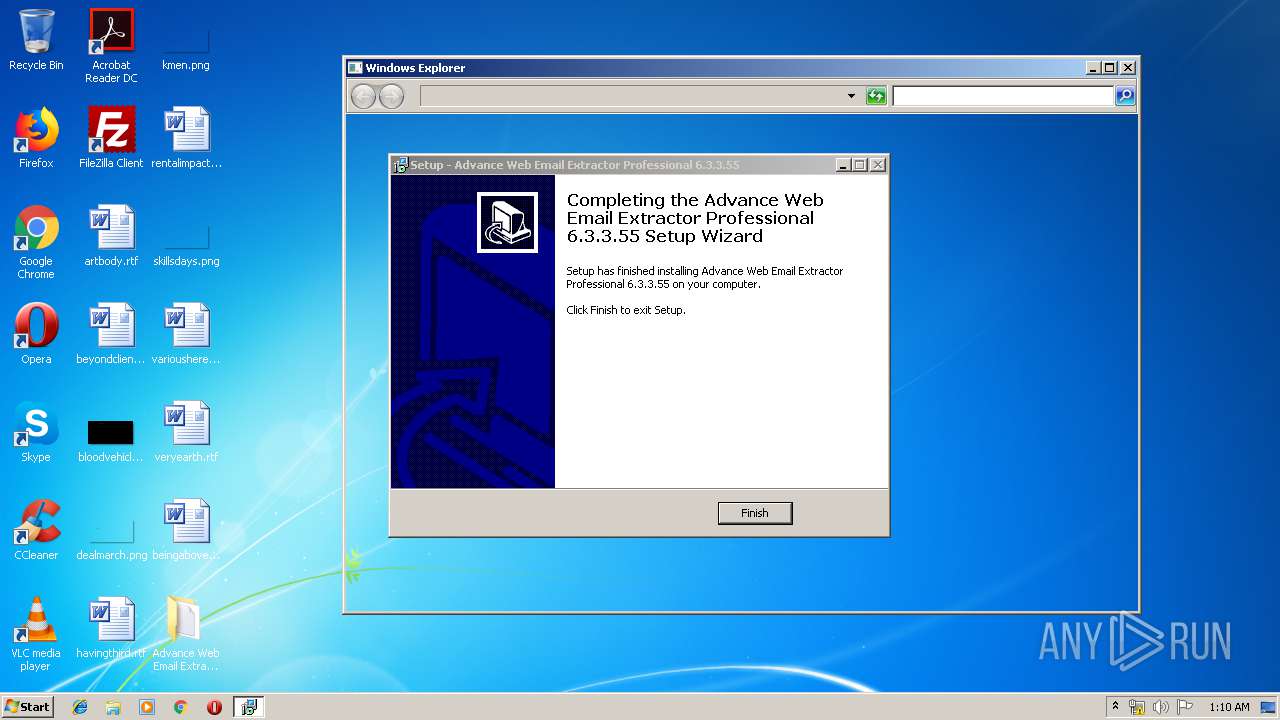
| File name: | Advance Web Email Extractor Professional 6.3.3.55.exe |
| Full analysis: | https://app.any.run/tasks/be4e6792-01ef-4767-b6fb-a9b297c59f8e |
| Verdict: | Suspicious activity |
| Analysis date: | January 15, 2020, 01:09:35 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 7B54ED227758C6AF7A23E99C19707A71 |
| SHA1: | 12D4088AFAE1437F368AC2BF80294D3B74062BD7 |
| SHA256: | CF9115193878B4F13A72E64478BC2B835F6D86B1F2C6BF4D0DB3C1394A659F8D |
| SSDEEP: | 12288:uaHc64b888888888888W88888888888tsscV7/9GqeMo3JM5oDhDjxiZl8zAeON9:F868XW7/9oJT191BoQ9uZUR+zZdv |
MALICIOUS
Application was dropped or rewritten from another process
- utc.exe (PID: 3596)
Loads the Task Scheduler COM API
- schtasks.exe (PID: 1792)
- schtasks.exe (PID: 3496)
Uses Task Scheduler to run other applications
- utc.exe (PID: 3596)
SUSPICIOUS
Executable content was dropped or overwritten
- Advance Web Email Extractor Professional 6.3.3.55.exe (PID: 1524)
- Advance Web Email Extractor Professional 6.3.3.55.tmp (PID: 3460)
- Advance Web Email Extractor Professional 6.3.3.55.exe (PID: 2440)
- 7za.exe (PID: 2088)
Reads Windows owner or organization settings
- Advance Web Email Extractor Professional 6.3.3.55.tmp (PID: 3460)
Reads the Windows organization settings
- Advance Web Email Extractor Professional 6.3.3.55.tmp (PID: 3460)
Creates files in the user directory
- Advance Web Email Extractor Professional 6.3.3.55.tmp (PID: 3460)
- utc.exe (PID: 3596)
Reads Internet Cache Settings
- explorer.exe (PID: 3580)
Executed via COM
- explorer.exe (PID: 3580)
INFO
Application was dropped or rewritten from another process
- Advance Web Email Extractor Professional 6.3.3.55.tmp (PID: 3460)
- Advance Web Email Extractor Professional 6.3.3.55.tmp (PID: 2004)
- 7za.exe (PID: 4084)
- 7za.exe (PID: 2088)
- 7za.exe (PID: 616)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable Delphi generic (45.2) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (20.9) |
| .exe | | | Win32 Executable (generic) (14.3) |
| .exe | | | Win16/32 Executable Delphi generic (6.6) |
| .exe | | | Generic Win/DOS Executable (6.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:06:14 15:27:46+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 66560 |
| InitializedDataSize: | 53760 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1181c |
| OSVersion: | 5 |
| ImageVersion: | 6 |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 3.3.0.0 |
| ProductVersionNumber: | 3.3.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | |
| FileDescription: | |
| FileVersion: | 3.3 |
| LegalCopyright: | |
| ProductName: | |
| ProductVersion: | 3.3 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 14-Jun-2018 13:27:46 |
| Detected languages: |
|
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | - |
| FileDescription: | - |
| FileVersion: | 3.3 |
| LegalCopyright: | - |
| ProductName: | - |
| ProductVersion: | 3.3 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 14-Jun-2018 13:27:46 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0000F25C | 0x0000F400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.37588 |
.itext | 0x00011000 | 0x00000FA4 | 0x00001000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.77877 |
.data | 0x00012000 | 0x00000C8C | 0x00000E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.30283 |
.bss | 0x00013000 | 0x000056BC | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x00019000 | 0x00000E04 | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.59781 |
.tls | 0x0001A000 | 0x00000008 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x0001B000 | 0x00000018 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 0.204488 |
.rsrc | 0x0001C000 | 0x0000B200 | 0x0000B200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.13736 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.13965 | 1580 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 3.47151 | 1384 | UNKNOWN | Dutch - Netherlands | RT_ICON |
3 | 3.91708 | 744 | UNKNOWN | Dutch - Netherlands | RT_ICON |
4 | 3.91366 | 2216 | UNKNOWN | Dutch - Netherlands | RT_ICON |
4091 | 2.56031 | 104 | UNKNOWN | UNKNOWN | RT_STRING |
4092 | 3.25287 | 212 | UNKNOWN | UNKNOWN | RT_STRING |
4093 | 3.26919 | 164 | UNKNOWN | UNKNOWN | RT_STRING |
4094 | 3.33268 | 684 | UNKNOWN | UNKNOWN | RT_STRING |
4095 | 3.34579 | 844 | UNKNOWN | UNKNOWN | RT_STRING |
4096 | 3.28057 | 660 | UNKNOWN | UNKNOWN | RT_STRING |
Imports
advapi32.dll |
comctl32.dll |
kernel32.dll |
oleaut32.dll |
user32.dll |
Total processes
54
Monitored processes
13
Malicious processes
2
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 616 | "C:\Users\admin\AppData\Local\Temp\is-7A90U.tmp\7za.exe" x "C:\Users\admin\AppData\Local\Temp\is-7A90U.tmp\misc.res" -p"b1lig@n_vl" | C:\Users\admin\AppData\Local\Temp\is-7A90U.tmp\7za.exe | — | Advance Web Email Extractor Professional 6.3.3.55.tmp | |||||||||||
User: admin Company: Igor Pavlov Integrity Level: HIGH Description: 7-Zip Standalone Console Exit code: 0 Version: 4.65 Modules
| |||||||||||||||
| 1524 | "C:\Users\admin\AppData\Local\Temp\Advance Web Email Extractor Professional 6.3.3.55.exe" | C:\Users\admin\AppData\Local\Temp\Advance Web Email Extractor Professional 6.3.3.55.exe | explorer.exe | ||||||||||||
User: admin Company: Integrity Level: MEDIUM Description: Exit code: 0 Version: 3.3 Modules
| |||||||||||||||
| 1792 | "C:\Windows\system32\schtasks.exe" /Delete /tn "Microsoft\Windows\Time Synchronization\ViewUtcTime" /f | C:\Windows\system32\schtasks.exe | — | utc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Manages scheduled tasks Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2004 | "C:\Users\admin\AppData\Local\Temp\is-Q0A7D.tmp\Advance Web Email Extractor Professional 6.3.3.55.tmp" /SL5="$30128,365962,121344,C:\Users\admin\AppData\Local\Temp\Advance Web Email Extractor Professional 6.3.3.55.exe" | C:\Users\admin\AppData\Local\Temp\is-Q0A7D.tmp\Advance Web Email Extractor Professional 6.3.3.55.tmp | — | Advance Web Email Extractor Professional 6.3.3.55.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 2088 | "C:\Users\admin\AppData\Local\Temp\is-7A90U.tmp\7za.exe" x "C:\Users\admin\AppData\Local\Temp\is-7A90U.tmp\form.res" -p"b1lig@n_vl" | C:\Users\admin\AppData\Local\Temp\is-7A90U.tmp\7za.exe | Advance Web Email Extractor Professional 6.3.3.55.tmp | ||||||||||||
User: admin Company: Igor Pavlov Integrity Level: HIGH Description: 7-Zip Standalone Console Exit code: 0 Version: 4.65 Modules
| |||||||||||||||
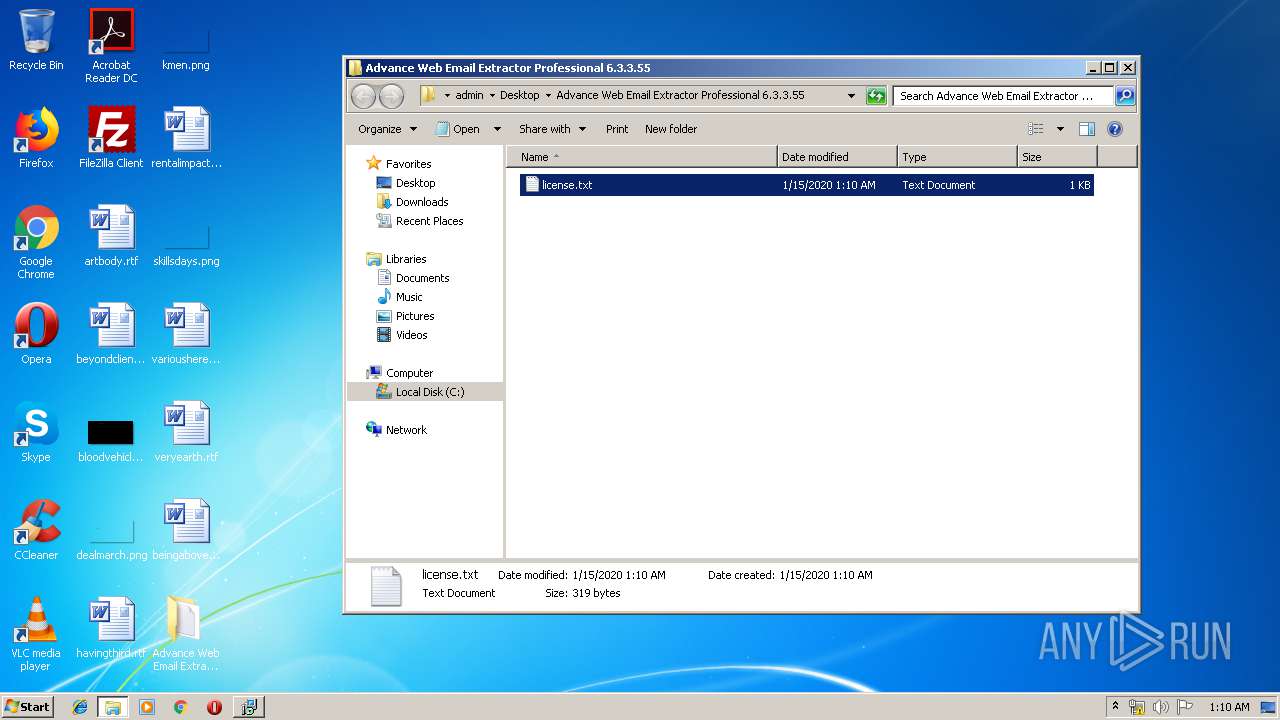
| 2192 | "explorer.exe" "C:\Users\admin\Desktop\Advance Web Email Extractor Professional 6.3.3.55" | C:\Windows\explorer.exe | — | Advance Web Email Extractor Professional 6.3.3.55.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2440 | "C:\Users\admin\AppData\Local\Temp\Advance Web Email Extractor Professional 6.3.3.55.exe" /SPAWNWND=$3012C /NOTIFYWND=$30128 | C:\Users\admin\AppData\Local\Temp\Advance Web Email Extractor Professional 6.3.3.55.exe | Advance Web Email Extractor Professional 6.3.3.55.tmp | ||||||||||||
User: admin Company: Integrity Level: HIGH Description: Exit code: 0 Version: 3.3 Modules
| |||||||||||||||
| 3460 | "C:\Users\admin\AppData\Local\Temp\is-NR9I2.tmp\Advance Web Email Extractor Professional 6.3.3.55.tmp" /SL5="$40150,365962,121344,C:\Users\admin\AppData\Local\Temp\Advance Web Email Extractor Professional 6.3.3.55.exe" /SPAWNWND=$3012C /NOTIFYWND=$30128 | C:\Users\admin\AppData\Local\Temp\is-NR9I2.tmp\Advance Web Email Extractor Professional 6.3.3.55.tmp | Advance Web Email Extractor Professional 6.3.3.55.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 3496 | "C:\Windows\system32\schtasks.exe" /Create /f /XML "C:\Users\admin\AppData\Roaming\UtcTimer\data.xml" /tn "Microsoft\Windows\Time Synchronization\ViewUtcTime" | C:\Windows\system32\schtasks.exe | — | utc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Manages scheduled tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3580 | C:\Windows\explorer.exe /factory,{75dff2b7-6936-4c06-a8bb-676a7b00b24b} -Embedding | C:\Windows\explorer.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 243
Read events
1 123
Write events
116
Delete events
4
Modification events
| (PID) Process: | (3460) Advance Web Email Extractor Professional 6.3.3.55.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Owner |
Value: 840D000040960D7F40CBD501 | |||
| (PID) Process: | (3460) Advance Web Email Extractor Professional 6.3.3.55.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | SessionHash |
Value: 6E583D224C51309D46436A7B60466735DDE071F98DF08F2A555DFACF32FE7E63 | |||
| (PID) Process: | (3460) Advance Web Email Extractor Professional 6.3.3.55.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Sequence |
Value: 1 | |||
| (PID) Process: | (3460) Advance Web Email Extractor Professional 6.3.3.55.tmp | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3580) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | NodeSlots |
Value: 020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202 | |||
| (PID) Process: | (3580) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | MRUListEx |
Value: 01000000070000000200000009000000080000000000000006000000030000000500000004000000FFFFFFFF | |||
| (PID) Process: | (3580) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU\1\0\0\0 |
| Operation: | write | Name: | 2 |
Value: 7A003100000000002F50420911004465736B746F7000640008000400EFBE454B814A2F5042092A0000007B0100000000020000000000000000003A00000000004400650073006B0074006F007000000040007300680065006C006C00330032002E0064006C006C002C002D0032003100370036003900000016000000 | |||
| (PID) Process: | (3580) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU\1\0\0\0 |
| Operation: | write | Name: | MRUListEx |
Value: 020000000000000001000000FFFFFFFF | |||
| (PID) Process: | (3580) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU\1\0\0\0\2 |
| Operation: | write | Name: | 0 |
Value: AA003100000000002F5042091000414456414E437E312E353500900008000400EFBE2F5042092F5042092A000000E1CB000000000E00000000000000000000000000000041006400760061006E00630065002000570065006200200045006D00610069006C00200045007800740072006100630074006F0072002000500072006F00660065007300730069006F006E0061006C00200036002E0033002E0033002E003500350000001A000000 | |||
| (PID) Process: | (3580) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU\1\0\0\0\2 |
| Operation: | write | Name: | MRUListEx |
Value: 00000000FFFFFFFF | |||
Executable files
5
Suspicious files
3
Text files
5
Unknown types
0
Dropped files
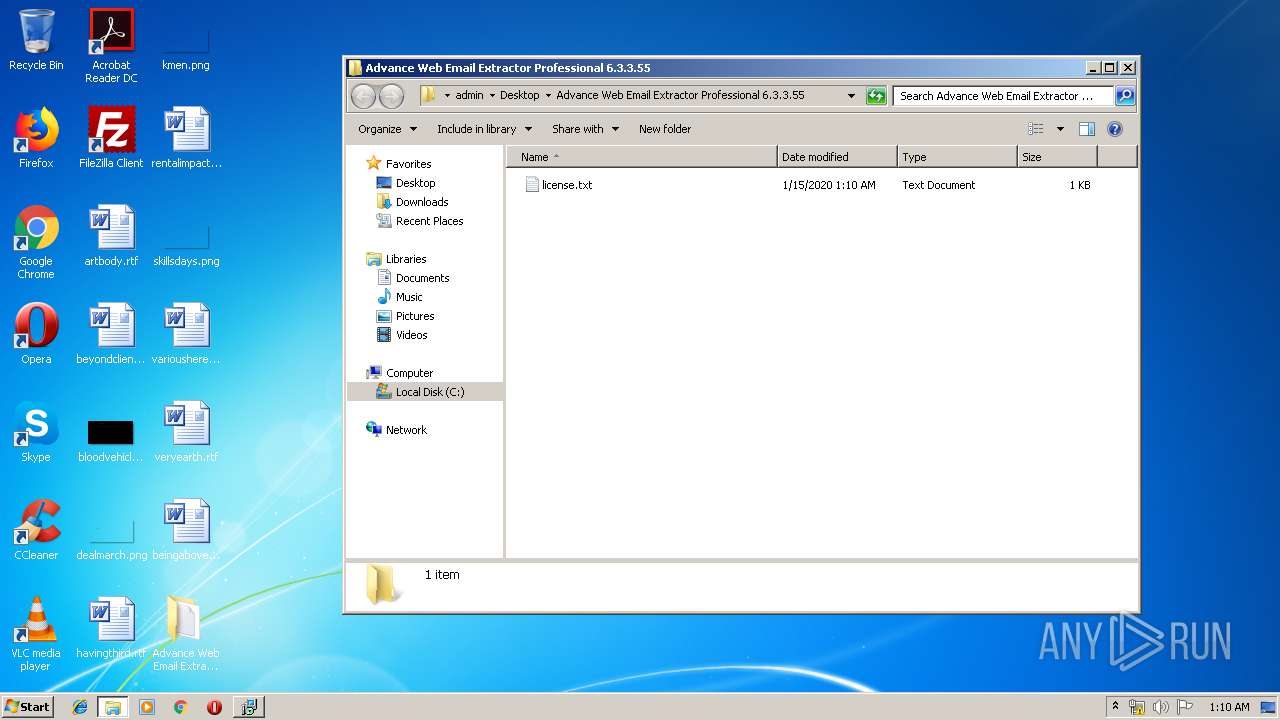
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3460 | Advance Web Email Extractor Professional 6.3.3.55.tmp | C:\Users\admin\AppData\Local\Temp\{BD52791F-3393-459A-8A0F-387464792DE2}\is-GMB8P.tmp | — | |
MD5:— | SHA256:— | |||
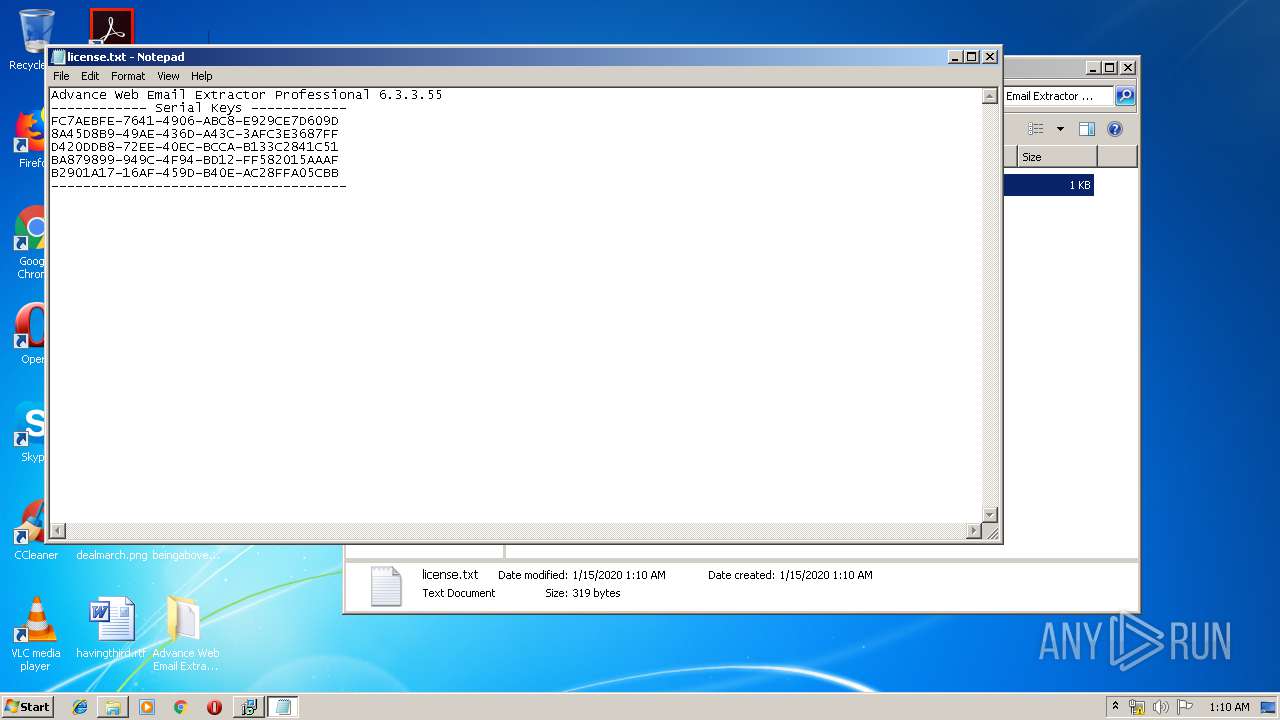
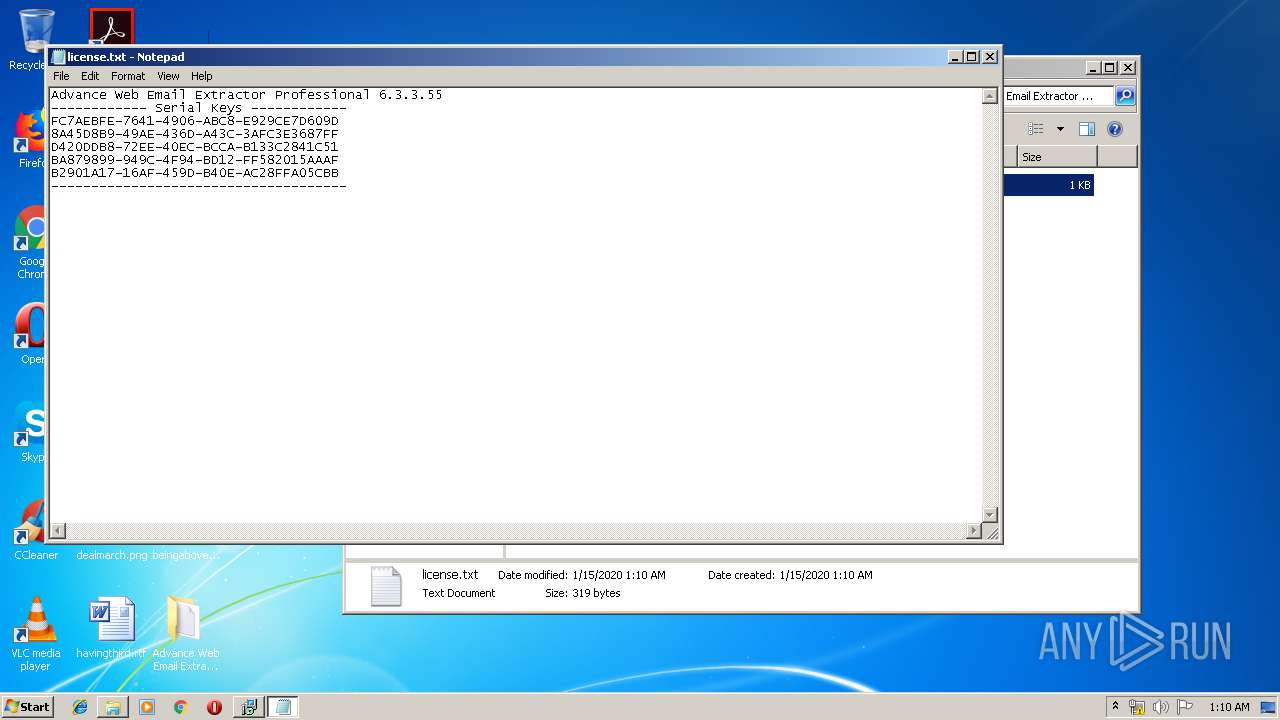
| 3460 | Advance Web Email Extractor Professional 6.3.3.55.tmp | C:\Users\admin\AppData\Local\Temp\{BD52791F-3393-459A-8A0F-387464792DE2}\license.txt | — | |
MD5:— | SHA256:— | |||
| 3596 | utc.exe | C:\Users\admin\AppData\Roaming\UtcTimer\data.xml | — | |
MD5:— | SHA256:— | |||
| 3460 | Advance Web Email Extractor Professional 6.3.3.55.tmp | C:\Users\admin\AppData\Local\Temp\is-7A90U.tmp\form.res | compressed | |
MD5:— | SHA256:— | |||
| 1524 | Advance Web Email Extractor Professional 6.3.3.55.exe | C:\Users\admin\AppData\Local\Temp\is-Q0A7D.tmp\Advance Web Email Extractor Professional 6.3.3.55.tmp | executable | |
MD5:34ACC2BDB45A9C436181426828C4CB49 | SHA256:9C81817ACD4982632D8C7F1DF3898FCA1477577738184265D735F49FC5480F07 | |||
| 3460 | Advance Web Email Extractor Professional 6.3.3.55.tmp | C:\Users\admin\AppData\Local\Temp\is-7A90U.tmp\7za.exe | executable | |
MD5:E92604E043F51C604B6D1AC3BCD3A202 | SHA256:FA252E501332B7486A972E7E471CF6915DAA681AF35C6AA102213921093EB2A3 | |||
| 4084 | 7za.exe | C:\Users\admin\AppData\Local\Temp\is-7A90U.tmp\sub.xml | xml | |
MD5:C047508A4A1F583B7ED31EC7B0DF9695 | SHA256:CD999BAA036D44D442FE43A541D69F04BA206C58938F3C22EC0F226493C63E35 | |||
| 3460 | Advance Web Email Extractor Professional 6.3.3.55.tmp | C:\Users\admin\AppData\Local\Temp\is-7A90U.tmp\misc.res | compressed | |
MD5:2787C3F64F404F62C9147A961F4A82AB | SHA256:EED036BDAB93F40398BA6389EC02B26CAB4173164D8029D9F48F15BCAEC4264C | |||
| 3460 | Advance Web Email Extractor Professional 6.3.3.55.tmp | C:\Users\admin\AppData\Local\Temp\is-7A90U.tmp\sub.res | compressed | |
MD5:AE50AD46B7EF3517F5DF5EDF2B96443E | SHA256:F4A2B3FA7460606D58AD078D320AFCEAD400285304DC49E8F2BA3FA9800854DC | |||
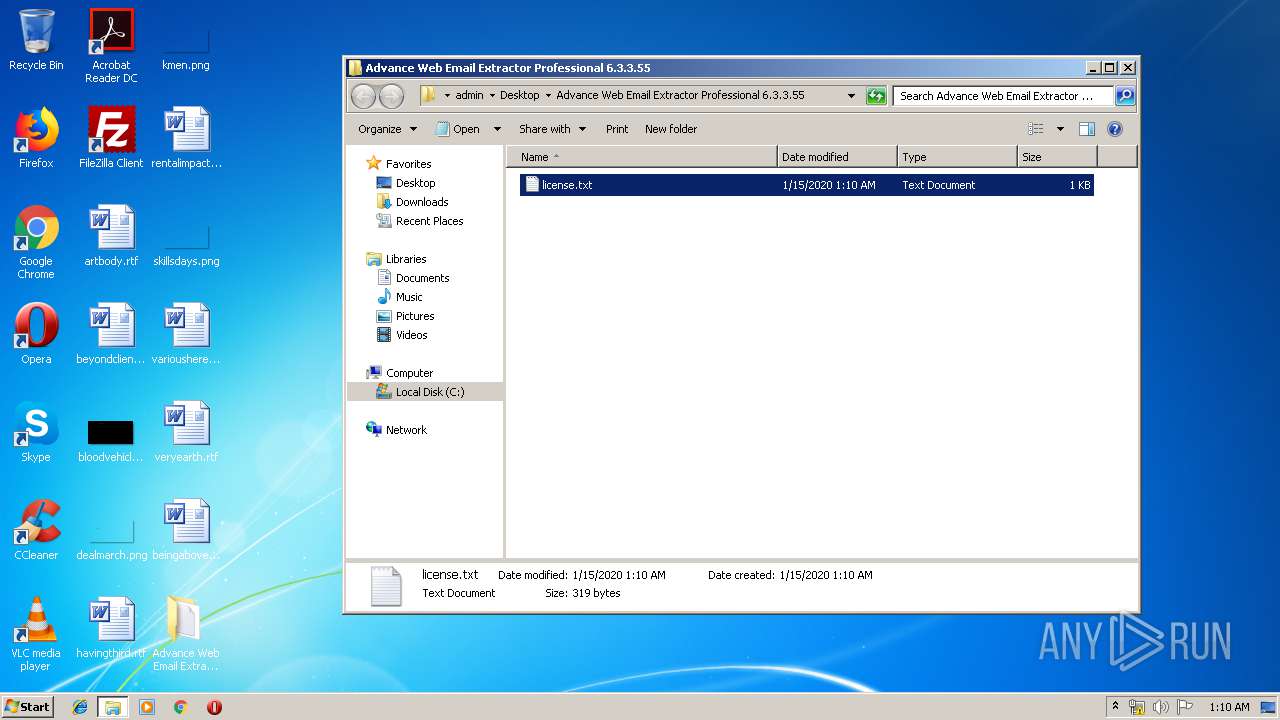
| 3460 | Advance Web Email Extractor Professional 6.3.3.55.tmp | C:\Users\admin\Desktop\Advance Web Email Extractor Professional 6.3.3.55\license.txt | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
3
DNS requests
2
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3460 | Advance Web Email Extractor Professional 6.3.3.55.tmp | GET | 301 | 104.27.141.42:80 | http://crackdownloadz.com/provider | US | — | — | shared |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3460 | Advance Web Email Extractor Professional 6.3.3.55.tmp | 216.58.207.46:80 | www.google-analytics.com | Google Inc. | US | whitelisted |
3460 | Advance Web Email Extractor Professional 6.3.3.55.tmp | 104.27.141.42:80 | crackdownloadz.com | Cloudflare Inc | US | shared |
3460 | Advance Web Email Extractor Professional 6.3.3.55.tmp | 104.27.141.42:443 | crackdownloadz.com | Cloudflare Inc | US | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.google-analytics.com |
| whitelisted |
crackdownloadz.com |
| unknown |