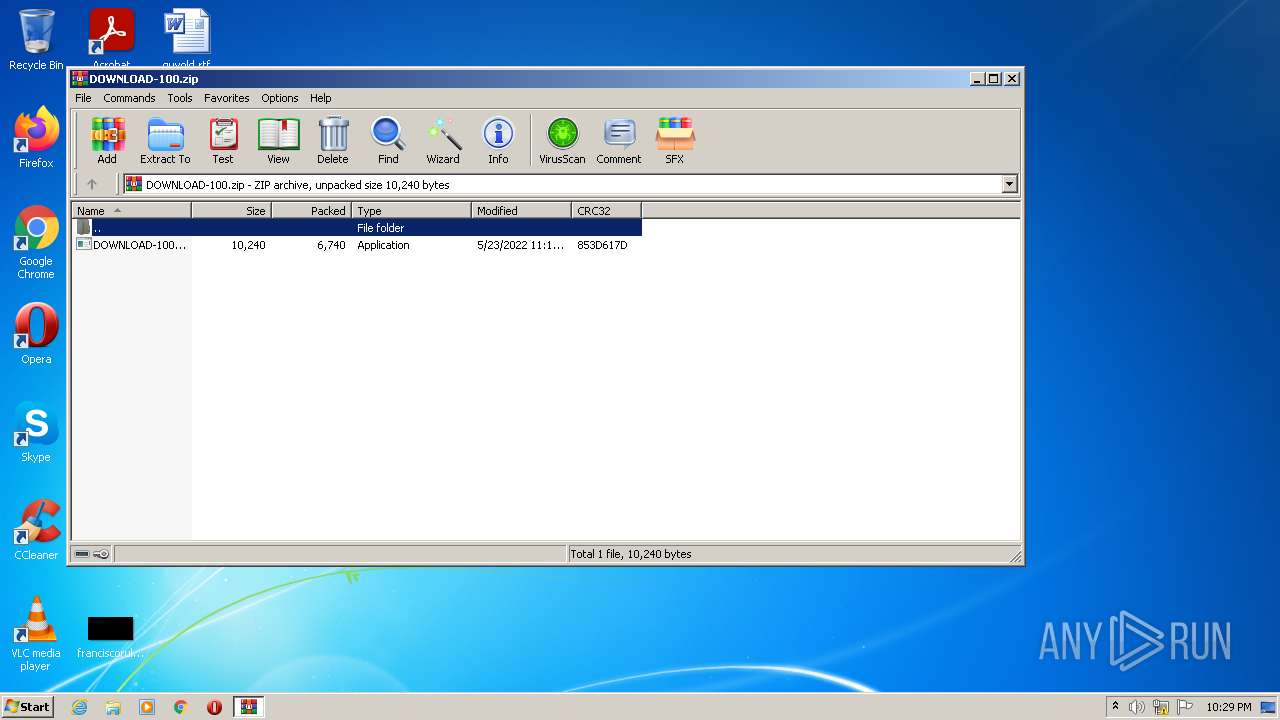
| File name: | DOWNLOAD-100.zip |
| Full analysis: | https://app.any.run/tasks/5fef0b0f-fb70-4786-8857-1515c1ef4b04 |
| Verdict: | Malicious activity |
| Analysis date: | August 12, 2022, 21:29:05 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 3A857A5178641E533F2381540E366B2B |
| SHA1: | 68DC53253FD79331C9D9920B6EBD160077C71F6F |
| SHA256: | CF8A0892A10B319CC7F82232FB4C2DFCF42FE27CEC9D15F7BD9DB576D83202BF |
| SSDEEP: | 96:lgZr0lBsI+KelaCgZGacCGDUd9w6FRuhpXeAc0ATa2Sh7ae1vtJJunW26BhaGGeD:+LJx+ZXcCGUw6yddvn2c1lzF26BFG4zr |
MALICIOUS
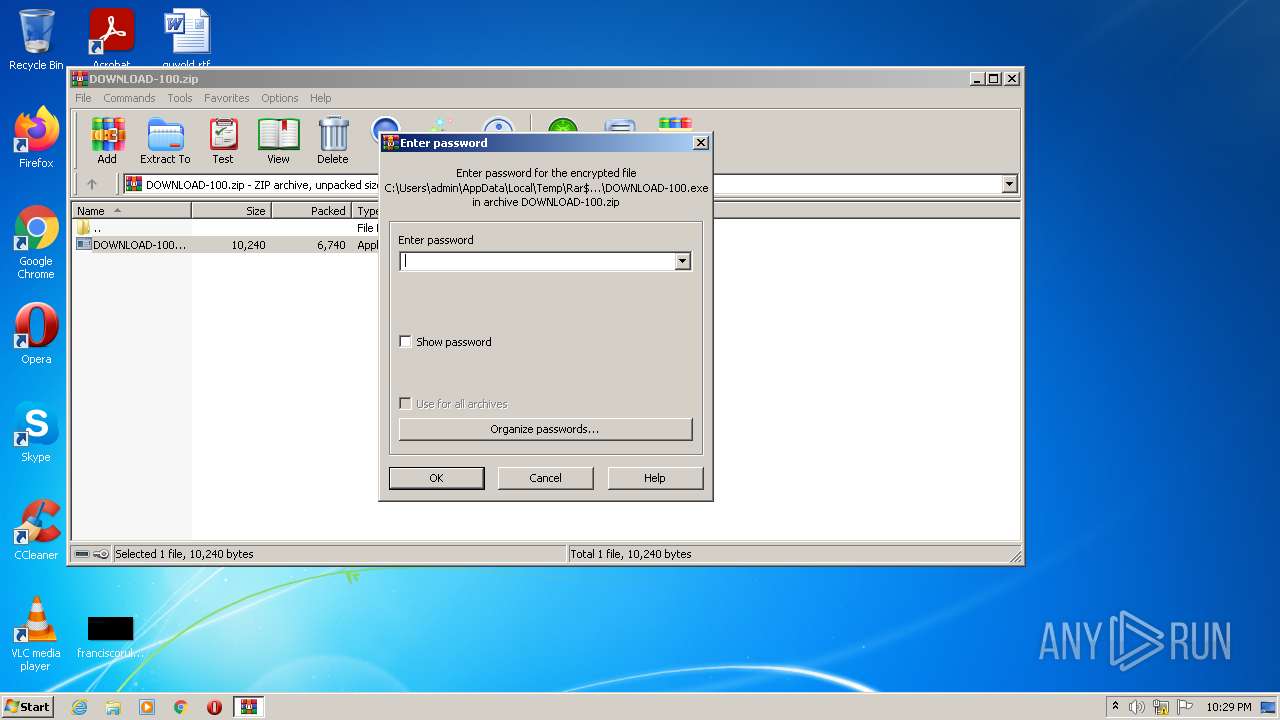
Drops executable file immediately after starts
- WinRAR.exe (PID: 2384)
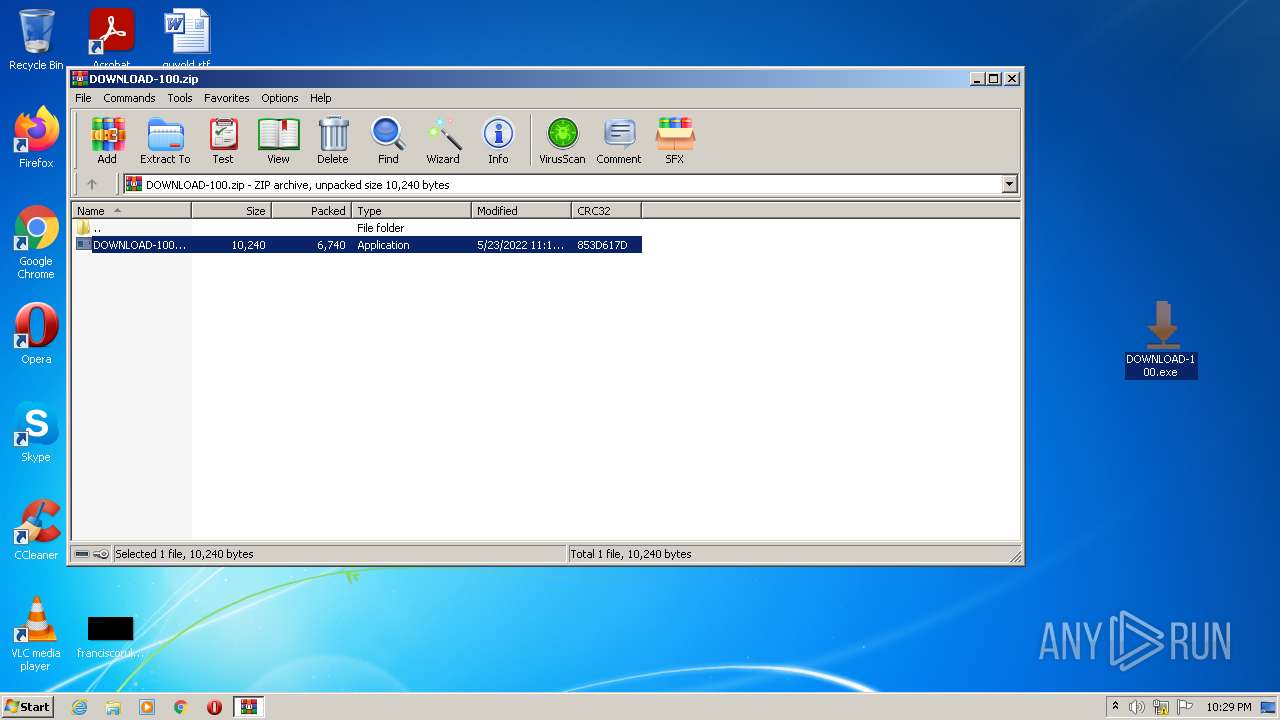
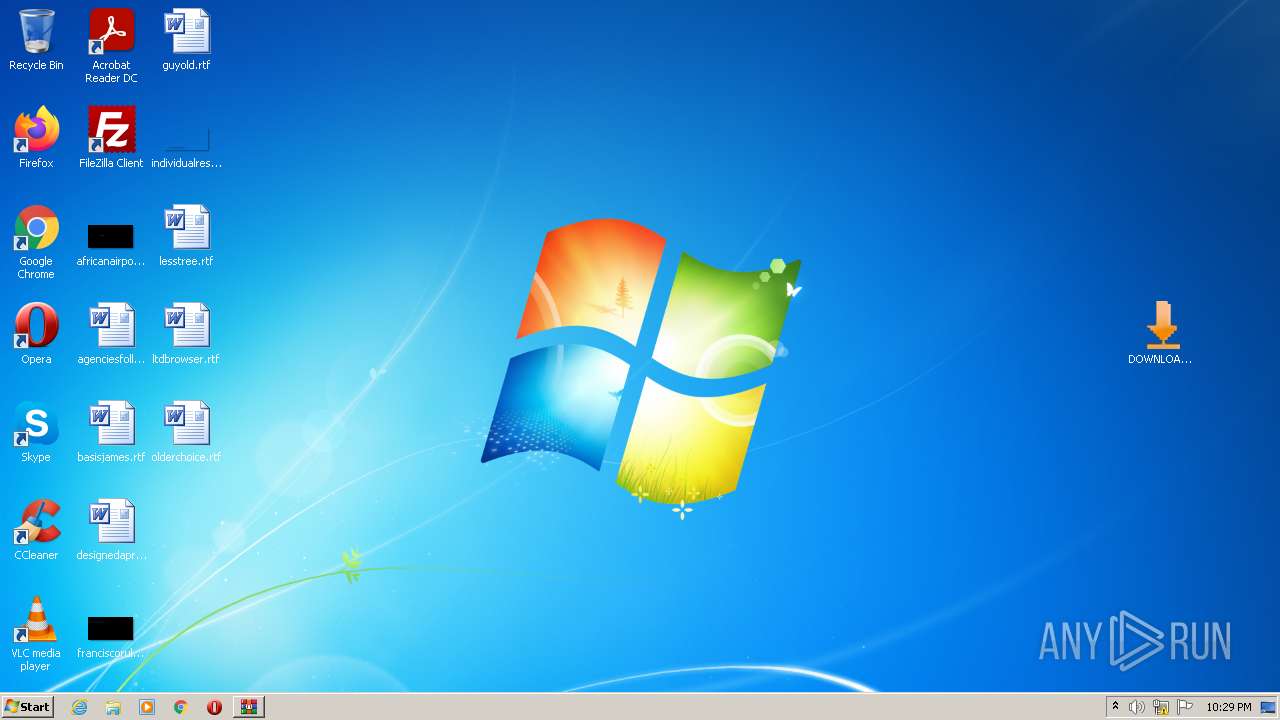
Application was dropped or rewritten from another process
- DOWNLOAD-100.exe (PID: 2496)
- DOWNLOAD-100.exe (PID: 2156)
Changes settings of System certificates
- DOWNLOAD-100.exe (PID: 2156)
SUSPICIOUS
Reads the computer name
- WinRAR.exe (PID: 2384)
- DOWNLOAD-100.exe (PID: 2496)
- DOWNLOAD-100.exe (PID: 2156)
Checks supported languages
- WinRAR.exe (PID: 2384)
- DOWNLOAD-100.exe (PID: 2496)
- DOWNLOAD-100.exe (PID: 2156)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2384)
Drops a file with a compile date too recent
- WinRAR.exe (PID: 2384)
Adds / modifies Windows certificates
- DOWNLOAD-100.exe (PID: 2156)
INFO
Manual execution by user
- DOWNLOAD-100.exe (PID: 2496)
- DOWNLOAD-100.exe (PID: 2156)
Reads settings of System Certificates
- DOWNLOAD-100.exe (PID: 2496)
- DOWNLOAD-100.exe (PID: 2156)
Checks Windows Trust Settings
- DOWNLOAD-100.exe (PID: 2496)
- DOWNLOAD-100.exe (PID: 2156)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipFileName: | DOWNLOAD-100.exe |
|---|---|
| ZipUncompressedSize: | 10240 |
| ZipCompressedSize: | 6740 |
| ZipCRC: | 0x853d617d |
| ZipModifyDate: | 2022:05:23 17:16:04 |
| ZipCompression: | Deflated |
| ZipBitFlag: | 0x0001 |
| ZipRequiredVersion: | 20 |
Total processes
39
Monitored processes
3
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2156 | "C:\Users\admin\Desktop\DOWNLOAD-100.exe" | C:\Users\admin\Desktop\DOWNLOAD-100.exe | Explorer.EXE | ||||||||||||
User: admin Company: PoC-BootCamp Integrity Level: MEDIUM Exit code: 0 Version: 1 Modules
| |||||||||||||||
| 2384 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\DOWNLOAD-100.zip" | C:\Program Files\WinRAR\WinRAR.exe | Explorer.EXE | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 2496 | "C:\Users\admin\Desktop\DOWNLOAD-100.exe" | C:\Users\admin\Desktop\DOWNLOAD-100.exe | Explorer.EXE | ||||||||||||
User: admin Company: PoC-BootCamp Integrity Level: MEDIUM Exit code: 0 Version: 1 Modules
| |||||||||||||||
Total events
8 803
Read events
8 700
Write events
100
Delete events
3
Modification events
| (PID) Process: | (2384) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2384) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2384) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2384) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\virtio_ivshmem_master_build.zip | |||
| (PID) Process: | (2384) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (2384) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\DOWNLOAD-100.zip | |||
| (PID) Process: | (2384) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2384) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2384) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2384) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
Executable files
1
Suspicious files
5
Text files
1
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2496 | DOWNLOAD-100.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_28DEA62A0AE77228DD387E155AD0BA27 | binary | |
MD5:— | SHA256:— | |||
| 2496 | DOWNLOAD-100.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_28DEA62A0AE77228DD387E155AD0BA27 | der | |
MD5:— | SHA256:— | |||
| 2156 | DOWNLOAD-100.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\24BD96D5497F70B3F510A6B53CD43F3E_3A89246FB90C5EE6620004F1AE0EB0EA | der | |
MD5:— | SHA256:— | |||
| 2156 | DOWNLOAD-100.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\24BD96D5497F70B3F510A6B53CD43F3E_3A89246FB90C5EE6620004F1AE0EB0EA | binary | |
MD5:— | SHA256:— | |||
| 2156 | DOWNLOAD-100.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\CAF4703619713E3F18D8A9D5D88D6288_A7725538C46DE2D0088EE44974E2CEBA | der | |
MD5:— | SHA256:— | |||
| 2156 | DOWNLOAD-100.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\PO2HN1X2\dfirsena[1].htm | html | |
MD5:— | SHA256:— | |||
| 2496 | DOWNLOAD-100.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 2156 | DOWNLOAD-100.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\CAF4703619713E3F18D8A9D5D88D6288_A7725538C46DE2D0088EE44974E2CEBA | binary | |
MD5:— | SHA256:— | |||
| 2496 | DOWNLOAD-100.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | compressed | |
MD5:F7DCB24540769805E5BB30D193944DCE | SHA256:6B88C6AC55BBD6FEA0EBE5A760D1AD2CFCE251C59D0151A1400701CB927E36EA | |||
| 2384 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb2384.41302\DOWNLOAD-100.exe | executable | |
MD5:95801AF084F016C65FE03CA79EB1B996 | SHA256:603488E403F45E7EECC5B738057C255533AE704450B00F94CCB03F6C714042BF | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
7
DNS requests
6
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2156 | DOWNLOAD-100.exe | GET | — | 142.250.186.67:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQCJ0LMUWb9%2FFgo%2FwIbO2Mkq | US | — | — | whitelisted |
2156 | DOWNLOAD-100.exe | GET | 200 | 142.250.186.67:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | US | der | 1.41 Kb | whitelisted |
2496 | DOWNLOAD-100.exe | GET | 200 | 8.253.95.121:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?7d388210155f3d20 | US | compressed | 4.70 Kb | whitelisted |
2496 | DOWNLOAD-100.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAo3h2ReX7SMIk79G%2B0UDDw%3D | US | der | 1.47 Kb | whitelisted |
2156 | DOWNLOAD-100.exe | GET | 200 | 142.250.186.67:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIDvFNZazTHGPUBUGY%3D | US | der | 724 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2496 | DOWNLOAD-100.exe | 104.20.139.65:443 | tinyurl.com | Cloudflare Inc | US | suspicious |
2496 | DOWNLOAD-100.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
— | — | 104.20.139.65:443 | tinyurl.com | Cloudflare Inc | US | suspicious |
2156 | DOWNLOAD-100.exe | 104.20.138.65:443 | tinyurl.com | Cloudflare Inc | US | suspicious |
2496 | DOWNLOAD-100.exe | 8.253.95.121:80 | ctldl.windowsupdate.com | Global Crossing | US | suspicious |
2156 | DOWNLOAD-100.exe | 142.250.185.129:443 | c.tenor.com | Google Inc. | US | whitelisted |
2156 | DOWNLOAD-100.exe | 142.250.186.67:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
tinyurl.com |
| shared |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
dns.msftncsi.com |
| shared |
c.tenor.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |