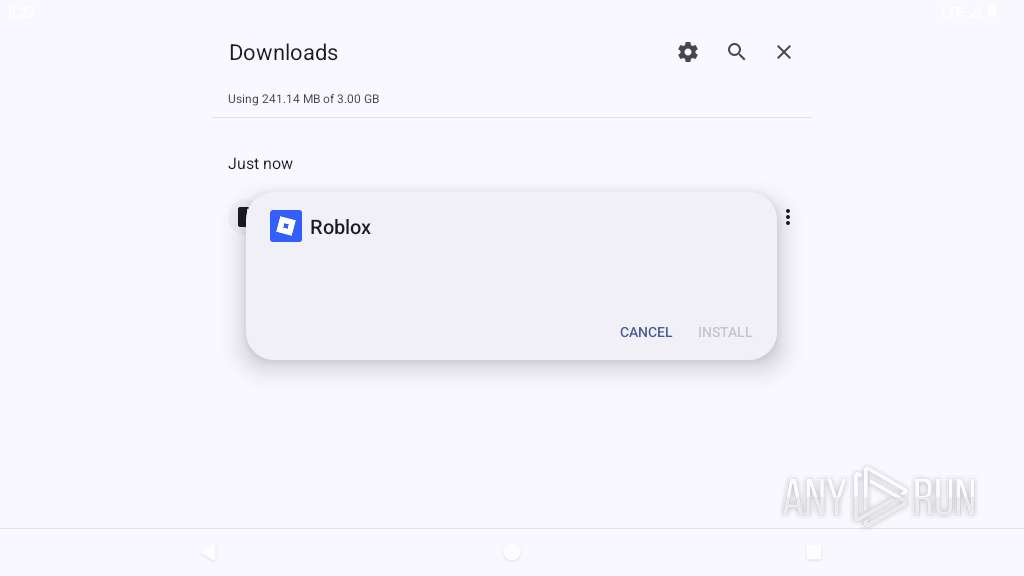
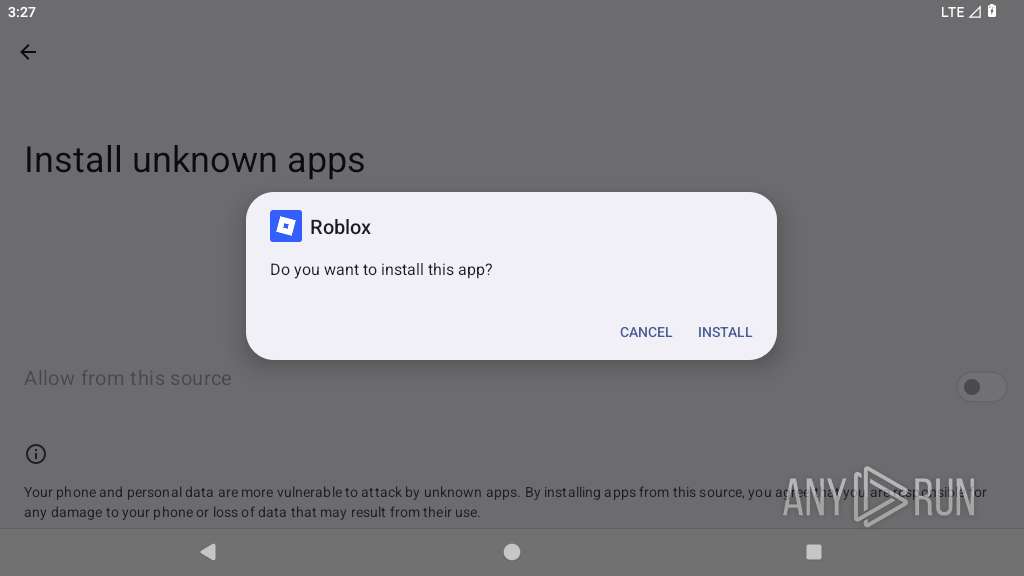
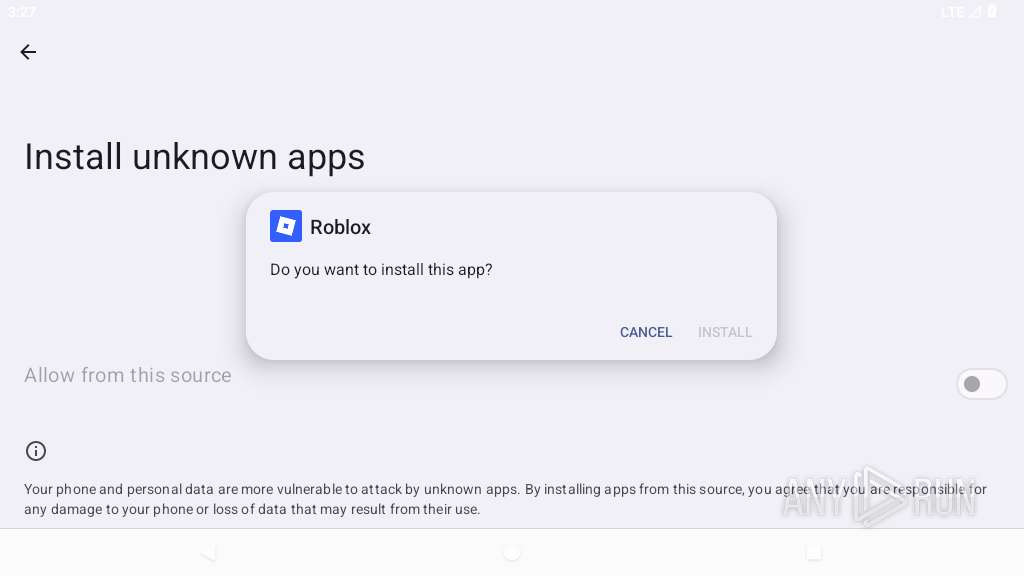
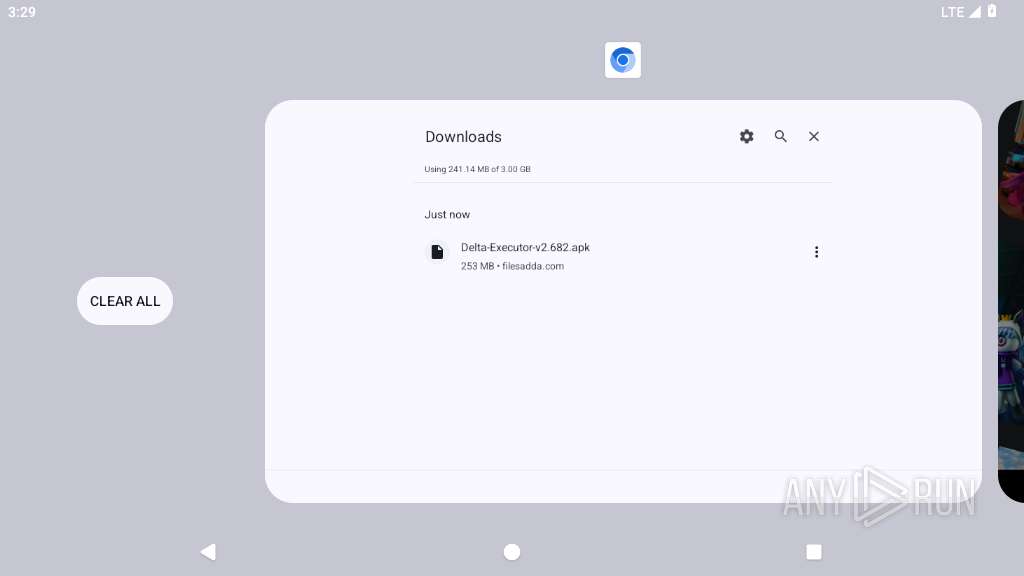
| URL: | delta-executor.com/download/ |
| Full analysis: | https://app.any.run/tasks/083231bd-badc-46ae-9b8c-33e6c349ee44 |
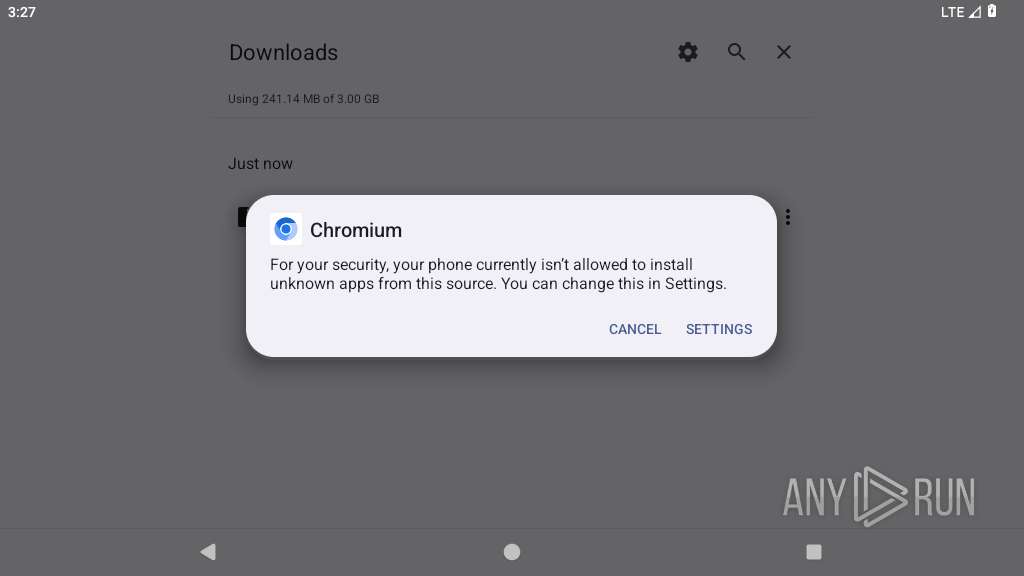
| Verdict: | Malicious activity |
| Analysis date: | July 24, 2025, 15:26:03 |
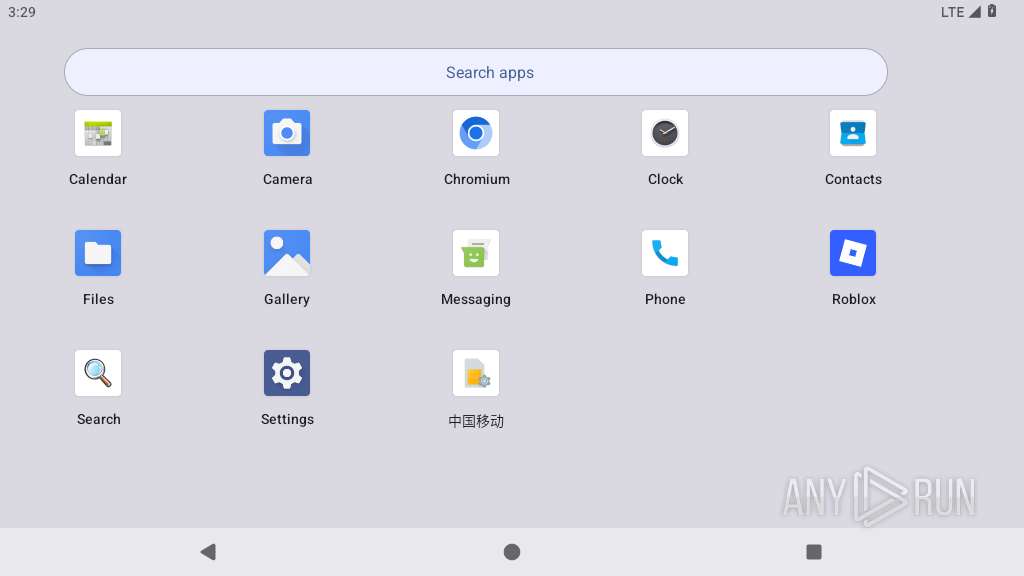
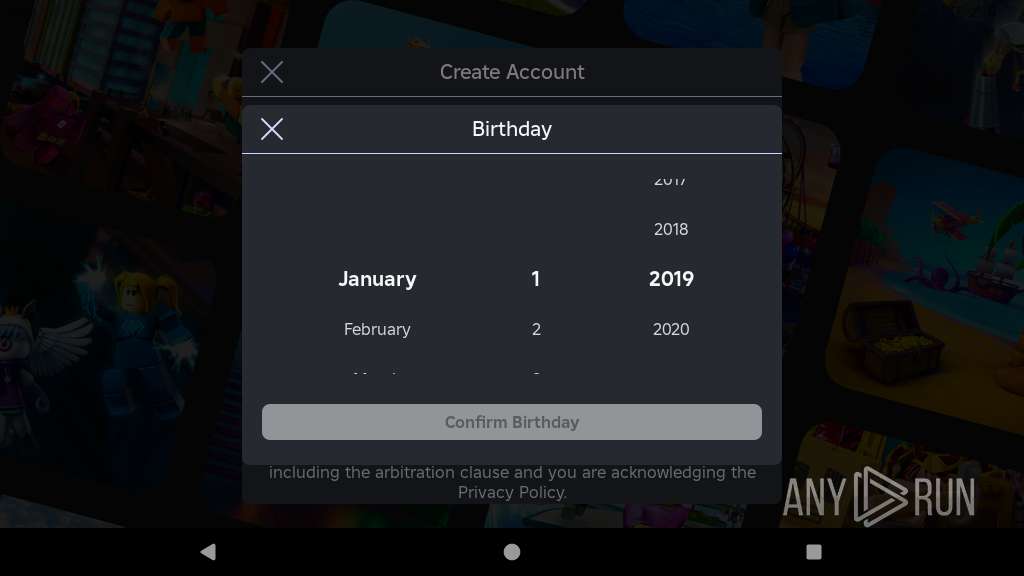
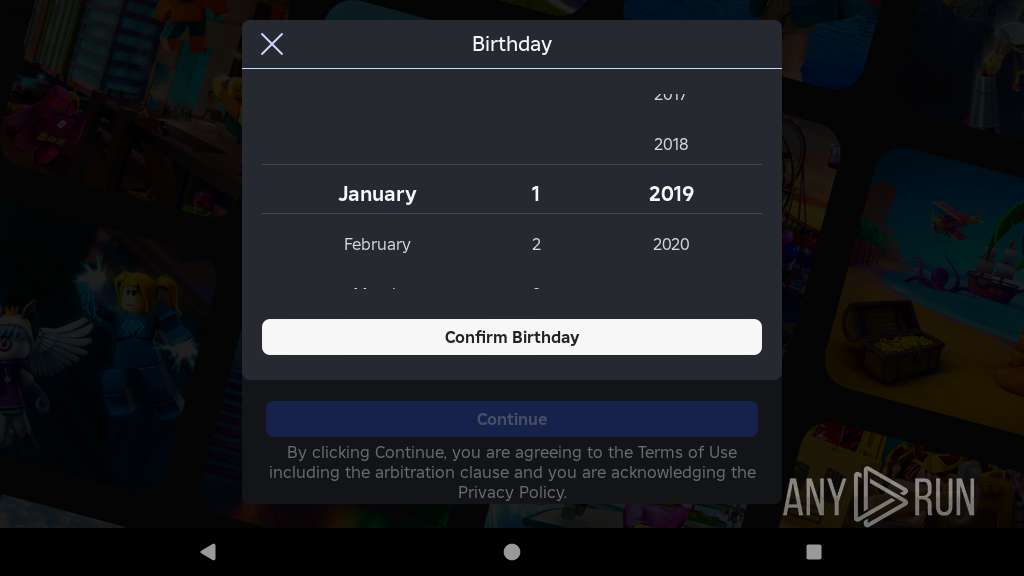
| OS: | Android 14 |
| Tags: | |
| Indicators: | |
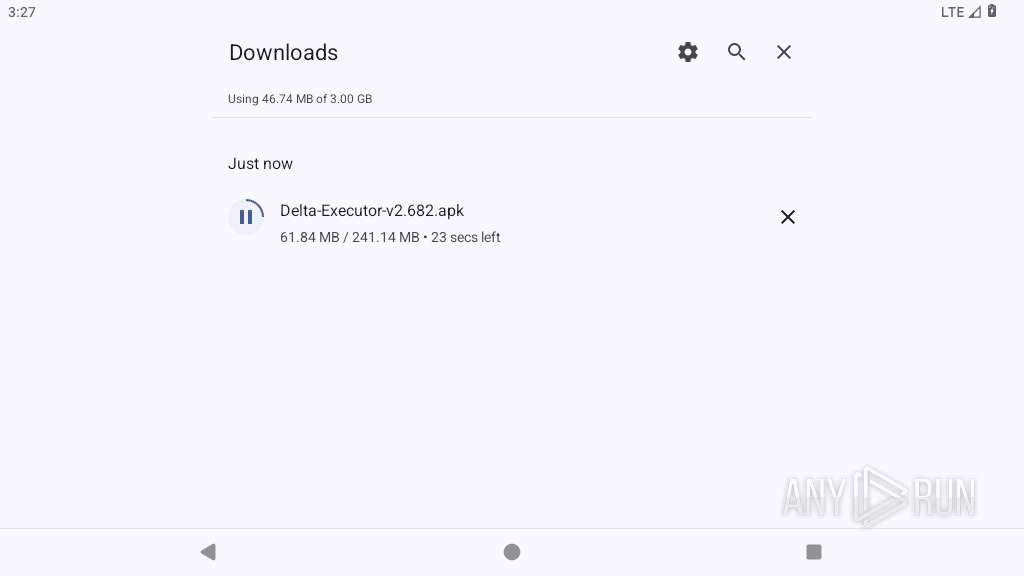
| MD5: | 1C0674CC51F55A7A9BC540C5EEEA813E |
| SHA1: | 3FF4FDA50DA095D431E35CE2D75B3E701A26784E |
| SHA256: | CF7E68B7B9024B871EC9645C9115EF76209A181B3DBDE32CF30373D851B2D6C5 |
| SSDEEP: | 3:sAqRDLn:hqRDL |
MALICIOUS
Executes system commands or scripts
- app_process64 (PID: 2983)
SUSPICIOUS
Updates data in the storage of application settings (SharedPreferences)
- app_process64 (PID: 2983)
Collects data about the device's environment (JVM version)
- app_process64 (PID: 2983)
Establishing a connection
- app_process64 (PID: 2983)
Accesses system-level resources
- app_process64 (PID: 2983)
Launches a new activity
- app_process64 (PID: 2983)
Retrieves a list of running application processes
- app_process64 (PID: 2983)
Accesses memory information
- app_process64 (PID: 2983)
Reads device serial number identifier
- app_process64 (PID: 2983)
Connects to unusual port
- app_process64 (PID: 2983)
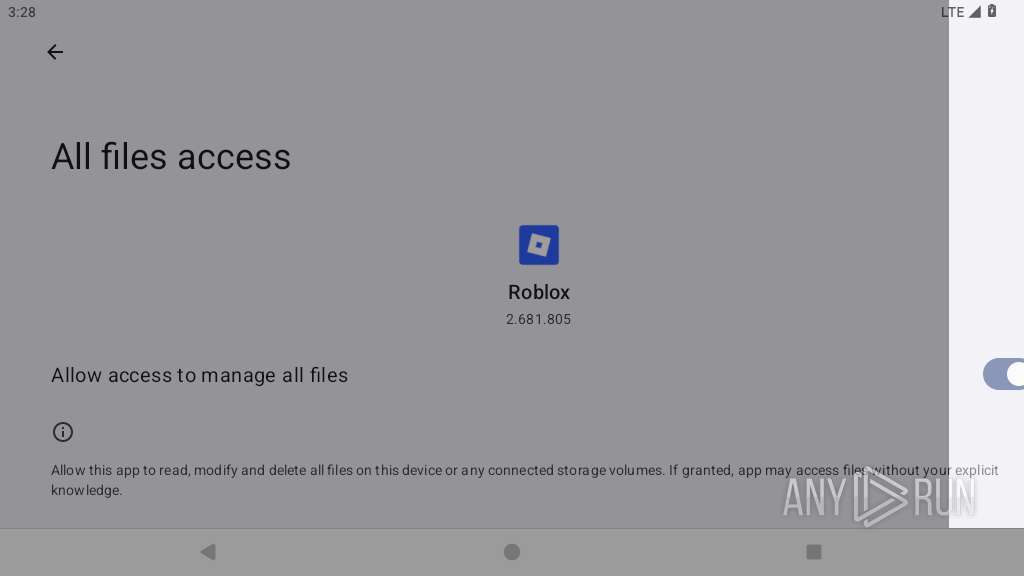
Accesses external device storage files
- app_process64 (PID: 2983)
INFO
Retrieves data from storage of application settings (SharedPreferences)
- app_process64 (PID: 2983)
Dynamically inspects or modifies classes, methods, and fields at runtime
- app_process64 (PID: 2983)
Loads a native library into the application
- app_process64 (PID: 2983)
Gets the display metrics associated with the device's screen
- app_process64 (PID: 2983)
Returns elapsed time since boot
- app_process64 (PID: 2983)
Dynamically registers broadcast event listeners
- app_process64 (PID: 2983)
Verifies whether the device is connected to the internet
- app_process64 (PID: 2983)
Stores data using SQLite database
- app_process64 (PID: 2983)
Retrieves the value of a secure system setting
- app_process64 (PID: 2983)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
172
Monitored processes
51
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
| 1793 | com.android.statementservice | /system/bin/app_process64 | app_process64 | |
User: u0_a34 Integrity Level: UNKNOWN Exit code: 0 | ||||
| 2199 | org.chromium.chrome | /system/bin/app_process64 | app_process64 | |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 2238 | com.android.settings | /system/bin/app_process64 | — | app_process64 |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 2286 | org.chromium.chrome_zygote | /system/bin/app_process64 | — | app_process64 |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 2296 | org.chromium.chrome_zygote | /system/bin/app_process64 | — | app_process64 |
User: u0_a72 Integrity Level: UNKNOWN Exit code: 9 | ||||
| 2338 | org.chromium.chrome:privileged_process0 | /system/bin/app_process64 | — | app_process64 |
User: root Integrity Level: UNKNOWN Exit code: 6 | ||||
| 2358 | com.android.adservices.api | /system/bin/app_process64 | — | app_process64 |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 2417 | org.chromium.chrome_zygote | /system/bin/app_process64 | — | app_process64 |
User: u0_a72 Integrity Level: UNKNOWN Exit code: 9 | ||||
| 2446 | org.chromium.chrome_zygote | /system/bin/app_process64 | — | app_process64 |
User: u0_a72 Integrity Level: UNKNOWN Exit code: 6 | ||||
| 2470 | com.android.providers.partnerbookmarks | /system/bin/app_process64 | — | app_process64 |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
Total events
0
Read events
0
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
65
Text files
71
Unknown types
18
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2558 | app_process64 | /data/data/org.chromium.chrome/cache/.org.chromium.Chromium.dXKBJB/decoded_xz | binary | |
MD5:— | SHA256:— | |||
| 2558 | app_process64 | /data/data/org.chromium.chrome/cache/.org.chromium.Chromium.dXKBJB/284970dba1157444cf24e06eabcc032caacc9db8d2874ba5928165482c55e3f1 | xz | |
MD5:— | SHA256:— | |||
| 2578 | app_process64 | /data/data/org.chromium.chrome/cache/.org.chromium.Chromium.QGLe4F/LICENSE.txt | text | |
MD5:— | SHA256:— | |||
| 2578 | app_process64 | /data/data/org.chromium.chrome/cache/.org.chromium.Chromium.QGLe4F/Filtering Rules | binary | |
MD5:— | SHA256:— | |||
| 2578 | app_process64 | /data/data/org.chromium.chrome/cache/.org.chromium.Chromium.QGLe4F/manifest.json | binary | |
MD5:— | SHA256:— | |||
| 2578 | app_process64 | /data/data/org.chromium.chrome/cache/.org.chromium.Chromium.QGLe4F/_metadata/verified_contents.json | ini | |
MD5:— | SHA256:— | |||
| 2578 | app_process64 | /data/data/org.chromium.chrome/app_chrome/component_crx_cache/15335e5e45db72828ff3226e84eccf2e71a4f7f51da7392fb2e3e24348ecff28 | binary | |
MD5:— | SHA256:— | |||
| 2617 | app_process64 | /data/data/org.chromium.chrome/cache/.org.chromium.Chromium.hjlgRj/manifest.json | binary | |
MD5:— | SHA256:— | |||
| 2617 | app_process64 | /data/data/org.chromium.chrome/cache/.org.chromium.Chromium.hjlgRj/_metadata/verified_contents.json | ini | |
MD5:— | SHA256:— | |||
| 2638 | app_process64 | /data/data/org.chromium.chrome/cache/.org.chromium.Chromium.OWsxYO/optimization-hints.pb | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
15
TCP/UDP connections
145
DNS requests
167
Threats
188
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 204 | 142.250.186.131:80 | http://connectivitycheck.gstatic.com/generate_204 | unknown | — | — | whitelisted |
2199 | app_process64 | GET | 200 | 142.250.185.238:80 | http://clients2.google.com/time/1/current?cup2key=9:aJ1S29A3y32jvnnCIB2FrPDQEH1duBz4H4x-QSKV2NM&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
2199 | app_process64 | GET | 301 | 162.159.136.54:80 | http://delta-executor.com/download/ | unknown | — | — | unknown |
2199 | app_process64 | GET | 301 | 162.159.136.54:80 | http://delta-executor.com/download/ | unknown | — | — | unknown |
2199 | app_process64 | GET | — | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/diffgen-puffin/obedbbhbpmojnkanicioggnmelmoomoc/9afe3368bc864fb80e494232fb6250ced25bbb312d83b4890ebabc5eef20c455 | unknown | — | — | whitelisted |
2199 | app_process64 | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/diffgen-puffin/gcmjkmgdlgnkkcocmoeiminaijmmjnii/284970dba1157444cf24e06eabcc032caacc9db8d2874ba5928165482c55e3f1 | unknown | — | — | whitelisted |
2199 | app_process64 | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/lbesfpxkiqwpv2vyqakempzgly_526/lmelglejhemejginpboagddgdfbepgmp_526_all_ZZ_o4icitdmqtcvxlkq6f6okokkn4.crx3 | unknown | — | — | whitelisted |
2199 | app_process64 | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acmmwq7dser4xm5sepzjv74g65vq_2023.7.28.10/cffplpkejcbdpfnfabnjikeicbedmifn_2023.07.28.10_all_acgbwixmcanakp2bkoppyszsbkrq.crx3 | unknown | — | — | whitelisted |
2199 | app_process64 | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acdvcifl2ztime6bsz3eijtcfeaq_2025.5.15.1/kiabhabjdbkjdpjbpigfodbdjmbglcoo_2025.05.15.01_all_ehum5zzx5qnqq3vyyhyi6ytrfq.crx3 | unknown | — | — | whitelisted |
2199 | app_process64 | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/diffgen-puffin/niikhdgajlphfehepabhhblakbdgeefj/97b4e68a7a79ae5be44033dbc869b57b36884d4ba50887521547c98b08363638 | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
445 | mdnsd | 224.0.0.251:5353 | — | — | — | unknown |
— | — | 142.250.185.68:443 | www.google.com | GOOGLE | US | whitelisted |
— | — | 142.250.186.131:80 | connectivitycheck.gstatic.com | GOOGLE | US | whitelisted |
1760 | app_process64 | 108.177.15.81:443 | staging-remoteprovisioning.sandbox.googleapis.com | GOOGLE | US | whitelisted |
574 | app_process64 | 216.239.35.0:123 | time.android.com | — | — | whitelisted |
2199 | app_process64 | 142.250.185.238:80 | clients2.google.com | GOOGLE | US | whitelisted |
2199 | app_process64 | 142.250.185.68:443 | www.google.com | — | — | whitelisted |
2199 | app_process64 | 162.159.136.54:80 | delta-executor.com | CLOUDFLARENET | — | unknown |
2199 | app_process64 | 74.125.133.84:443 | accounts.google.com | GOOGLE | US | whitelisted |
2199 | app_process64 | 162.159.137.54:443 | delta-executor.com | CLOUDFLARENET | — | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.google.com |
| whitelisted |
connectivitycheck.gstatic.com |
| whitelisted |
google.com |
| whitelisted |
staging-remoteprovisioning.sandbox.googleapis.com |
| whitelisted |
time.android.com |
| whitelisted |
clients2.google.com |
| whitelisted |
delta-executor.com |
| unknown |
accounts.google.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
securepubads.g.doubleclick.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Misc activity | ET INFO Android Device Connectivity Check |
2199 | app_process64 | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
2199 | app_process64 | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
2199 | app_process64 | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
2199 | app_process64 | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
2199 | app_process64 | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
2199 | app_process64 | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
2199 | app_process64 | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
2199 | app_process64 | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
2199 | app_process64 | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |