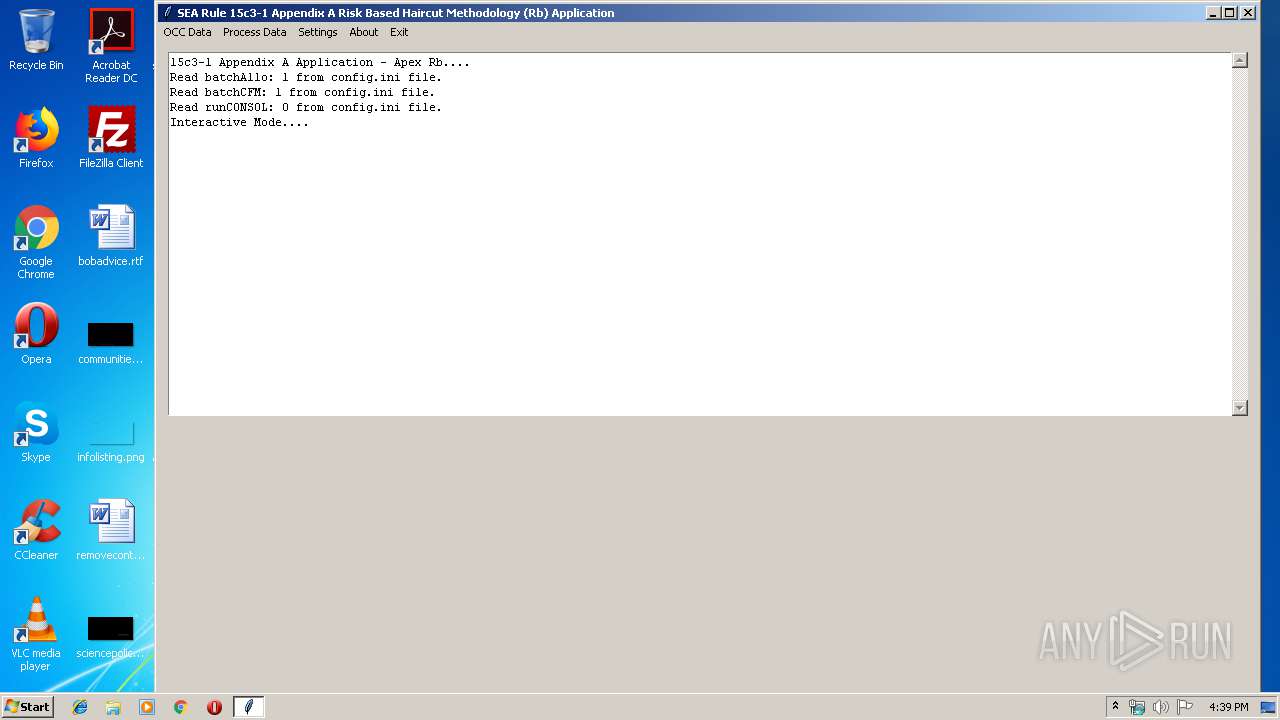
| File name: | Rb.exe |
| Full analysis: | https://app.any.run/tasks/3c677fa4-3592-49fe-9fdc-d3e6aaebc327 |
| Verdict: | Malicious activity |
| Analysis date: | January 17, 2020, 16:38:41 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | BBBEF216609000C3753A139FCA5B42FD |
| SHA1: | 57D11FEF5ACFC28457195C5917AB2F21EBEF4CD9 |
| SHA256: | CF73D5A1AB28866ECCB6794B55D589FA575FAC5E82553C02A3F4982CED6FA2BE |
| SSDEEP: | 196608:zjyLQM4Ik+i8I4GA81G+L9+3rkBwcrwaOme82giExmFDN:7M4Iz5G1NKrkBuaOm9y |
MALICIOUS
Loads dropped or rewritten executable
- Rb.exe (PID: 1028)
SUSPICIOUS
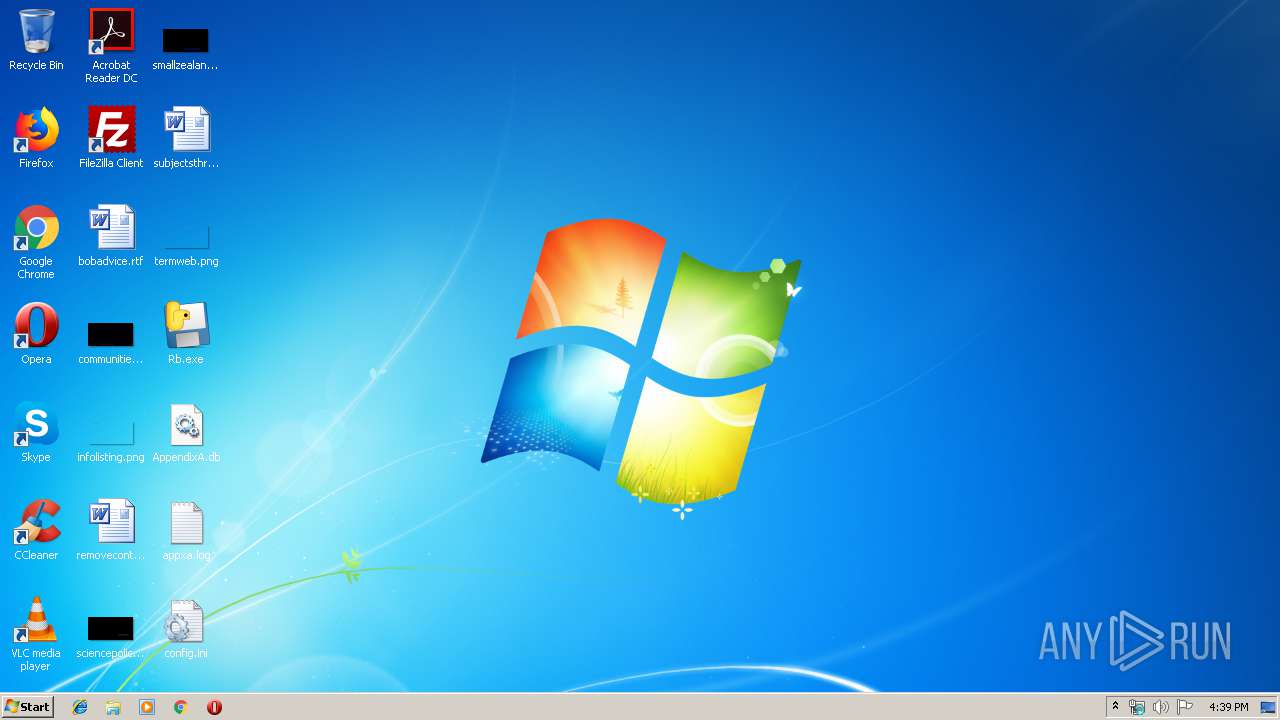
Executable content was dropped or overwritten
- Rb.exe (PID: 3944)
Application launched itself
- Rb.exe (PID: 3944)
Loads Python modules
- Rb.exe (PID: 1028)
INFO
Dropped object may contain Bitcoin addresses
- Rb.exe (PID: 3944)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | InstallShield setup (50.1) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (32.2) |
| .dll | | | Win32 Dynamic Link Library (generic) (7.6) |
| .exe | | | Win32 Executable (generic) (5.2) |
| .exe | | | Generic Win/DOS Executable (2.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:09:04 16:43:33+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 14 |
| CodeSize: | 125952 |
| InitializedDataSize: | 173056 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x79d3 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 04-Sep-2018 14:43:33 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000108 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 04-Sep-2018 14:43:33 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0001EB34 | 0x0001EC00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.64811 |
.rdata | 0x00020000 | 0x0000B164 | 0x0000B200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.09995 |
.data | 0x0002C000 | 0x0000E688 | 0x00000A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 1.92387 |
.gfids | 0x0003B000 | 0x000000B8 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 1.83952 |
.rsrc | 0x0003C000 | 0x0000EEC8 | 0x0000F000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.51705 |
.reloc | 0x0004B000 | 0x000017B4 | 0x00001800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.65332 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 6.15653 | 3752 | UNKNOWN | UNKNOWN | RT_ICON |
2 | 6.44895 | 2216 | UNKNOWN | UNKNOWN | RT_ICON |
3 | 5.77742 | 1384 | UNKNOWN | UNKNOWN | RT_ICON |
4 | 7.95095 | 38188 | UNKNOWN | UNKNOWN | RT_ICON |
5 | 6.0521 | 9640 | UNKNOWN | UNKNOWN | RT_ICON |
6 | 6.15081 | 4264 | UNKNOWN | UNKNOWN | RT_ICON |
7 | 6.39466 | 1128 | UNKNOWN | UNKNOWN | RT_ICON |
101 | 2.71858 | 104 | UNKNOWN | UNKNOWN | RT_GROUP_ICON |
Imports
KERNEL32.dll |
USER32.dll |
WS2_32.dll |
Total processes
37
Monitored processes
2
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1028 | "C:\Users\admin\Desktop\Rb.exe" | C:\Users\admin\Desktop\Rb.exe | — | Rb.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3944 | "C:\Users\admin\Desktop\Rb.exe" | C:\Users\admin\Desktop\Rb.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
0
Read events
0
Write events
0
Delete events
0
Modification events
Executable files
20
Suspicious files
1
Text files
913
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3944 | Rb.exe | C:\Users\admin\AppData\Local\Temp\_MEI39442\tk_appxa.exe.manifest | xml | |
MD5:— | SHA256:— | |||
| 3944 | Rb.exe | C:\Users\admin\AppData\Local\Temp\_MEI39442\_lzma.pyd | executable | |
MD5:D72665EA18965F103200CCC7AD072F85 | SHA256:AB20E63D14259A7DECA85A068796476C0EFCC236A11D53B1816FC6F8956424A8 | |||
| 3944 | Rb.exe | C:\Users\admin\AppData\Local\Temp\_MEI39442\_decimal.pyd | executable | |
MD5:942849B267A15E74C43BC298CF8EFCA3 | SHA256:749347C07F5DB9D5CD318313EBF120E541E12502710C27486047123E6E5D5AC4 | |||
| 3944 | Rb.exe | C:\Users\admin\AppData\Local\Temp\_MEI39442\_bz2.pyd | executable | |
MD5:055CFC5297933C338D8C04FD4E2462A2 | SHA256:BEFC81440BBC001BD7647ACA42962EE0B45B08435EE9F7140BF570AF636B7DD5 | |||
| 3944 | Rb.exe | C:\Users\admin\AppData\Local\Temp\_MEI39442\_contextvars.pyd | executable | |
MD5:4A525F91513ECE5FE180A5D1123D8337 | SHA256:6629835406814CD78D006A6080EFAF0E93E28B88B3FA2FEB00B7EF9C975E4A61 | |||
| 3944 | Rb.exe | C:\Users\admin\AppData\Local\Temp\_MEI39442\select.pyd | executable | |
MD5:CEFFF42D83A7DAFE76D22589978AA085 | SHA256:F8BF0C9909EE65038F5BFDB47C7EE037BF55C97D5BE259AA904D4E53A9B5CD34 | |||
| 3944 | Rb.exe | C:\Users\admin\AppData\Local\Temp\_MEI39442\sqlite3.dll | executable | |
MD5:373BC07173120B7839AD7DA9C7971B16 | SHA256:05901F8AF79A8186EBC013D6F41F22E53FD43DCCEEAD83265D74AEF0E3078A9C | |||
| 3944 | Rb.exe | C:\Users\admin\AppData\Local\Temp\_MEI39442\_socket.pyd | executable | |
MD5:51A38A6BF4C7E3D71B21A88B7A1DD555 | SHA256:B7829EC5C6DE17B30037E1B50F43E26B40FCD9ACDABCE0011D623F5C0CEBD70E | |||
| 3944 | Rb.exe | C:\Users\admin\AppData\Local\Temp\_MEI39442\_hashlib.pyd | executable | |
MD5:1280A084744EF726A673B757B9364335 | SHA256:C2B3DC92ABD96485032D1287941E405D56DF05FB5BA68199497D8594400163E5 | |||
| 3944 | Rb.exe | C:\Users\admin\AppData\Local\Temp\_MEI39442\_ssl.pyd | executable | |
MD5:E577403078DAF63CE6DDC07F195C45CE | SHA256:49559F96F659917C1C0E0D7CCB4FCF915BC1A00E51A5B25FE417262EF0F47774 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report