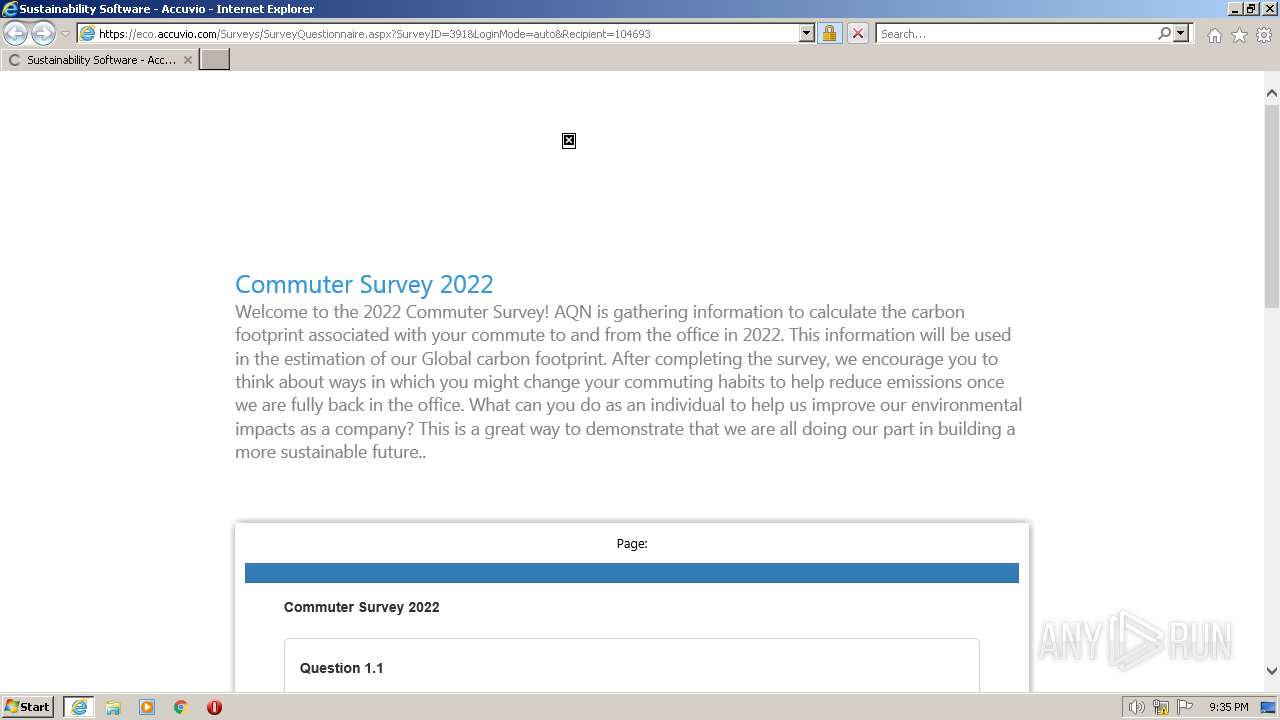
| URL: | https://urldefense.com/v3/__https://9hx1x32h.r.eu-west-1.awstrack.me/L0/https:*2F*2Feco.accuvio.com*2FSurveys*2FSurveyQuestionnaire.aspx*3FSurveyID=391*26Access=AutoLogin*26User=Yerzhan.Ospanov@libertyutilities.com*26Code=NEs050mO4Y/1/01020187b4658ace-cab8e617-6488-4b9e-9e36-d1b2d20280b5-000000/tR8ihP2mOxqTfJAGhi9-OM3GRJY=318__;JSUlJSUlJSU!!LKENFgF4IMmSVg!snC36rHAnOZR2s4LlM870Y8PxmZPT0CRXyHnlN0zMIIDXlcGrEVzfI7d9f66Vkk6TpoOxdiQXy1hRldKC9OA2i4Cmwuzbw$ |
| Full analysis: | https://app.any.run/tasks/88ddccfc-8169-4cbf-abd5-deb5daefb478 |
| Verdict: | No threats detected |
| Analysis date: | April 26, 2023, 20:34:35 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 0E4FED3002244B31C3EDF66E59282CB4 |
| SHA1: | F14629C91FBEA9721300362F31779DAD99394F25 |
| SHA256: | CF31A7D6B12A4BE0A0FF1FC1B7C6B97F7155376FB1FBCCE58540FE794C720952 |
| SSDEEP: | 12:2U069WLAESY0tp3drg6U6voX/4mebfXZwAO4j5kXB:2hSWA3W6U6vScDGAO0kR |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Application launched itself
- iexplore.exe (PID: 3224)
Create files in a temporary directory
- iexplore.exe (PID: 3224)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
38
Monitored processes
2
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3224 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://urldefense.com/v3/__https://9hx1x32h.r.eu-west-1.awstrack.me/L0/https:*2F*2Feco.accuvio.com*2FSurveys*2FSurveyQuestionnaire.aspx*3FSurveyID=391*26Access=AutoLogin*26User=Yerzhan.Ospanov@libertyutilities.com*26Code=NEs050mO4Y/1/01020187b4658ace-cab8e617-6488-4b9e-9e36-d1b2d20280b5-000000/tR8ihP2mOxqTfJAGhi9-OM3GRJY=318__;JSUlJSUlJSU!!LKENFgF4IMmSVg!snC36rHAnOZR2s4LlM870Y8PxmZPT0CRXyHnlN0zMIIDXlcGrEVzfI7d9f66Vkk6TpoOxdiQXy1hRldKC9OA2i4Cmwuzbwf7f81a39-5f63-5b42-9efd-1f13b5431005quot; | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3792 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3224 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
22 038
Read events
21 828
Write events
206
Delete events
4
Modification events
| (PID) Process: | (3224) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 0 | |||
| (PID) Process: | (3224) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30847387 | |||
| (PID) Process: | (3224) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30847437 | |||
| (PID) Process: | (3224) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3224) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3224) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3224) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3224) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3224) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3224) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
0
Suspicious files
60
Text files
64
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3792 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\72BA427A91F50409B9EAC87F2B59B951_F0B960C3B1E522BB9772662759982F90 | binary | |
MD5:065AF10B7FFFAA712187F88ADCA1AE87 | SHA256:EA021EF1B045C8F3066C1166FDF4083B4BE1321651979E54E6342B4B1EFF3FC7 | |||
| 3792 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:274A4BF89D38CFA8687D54FF2CFFF440 | SHA256:33D5DF9A4C9B6A6CD0B5D8422AC2D09CBB876C97A55398BF5A443F7FFA8358BE | |||
| 3224 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_711ED44619924BA6DC33E69F97E7FF63 | der | |
MD5:98686643C5DCA95B188A5D182C113DDD | SHA256:F7219172CF2769337B3B4B8010B671A4383A0AFB108E8288C9F5D4D54F8C6186 | |||
| 3792 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\72BA427A91F50409B9EAC87F2B59B951_F0B960C3B1E522BB9772662759982F90 | binary | |
MD5:3F15A9BA2670568A62BA8A8948BF5D25 | SHA256:F8B5F31D3140230CF5A319CF24C5C3F459480C82498A8155ECC7AEED2DE38A86 | |||
| 3224 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\7423F88C7F265F0DEFC08EA88C3BDE45_AA1E8580D4EBC816148CE81268683776 | der | |
MD5:0D3A327012D745BE5460B16B2AD84A14 | SHA256:CE02F3C64F276F89F05554BD0E91388B26E2107C5C7C658C7A09A2F0937156FA | |||
| 3224 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_711ED44619924BA6DC33E69F97E7FF63 | binary | |
MD5:D027719B2B6ED8F52C12D2F8515C90C5 | SHA256:E9C2C159A630DA46183E39BF3375A8A2D819D7525380AF110C80830EA7596B95 | |||
| 3224 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\PO2HN1X2\urlblockindex[1].bin | binary | |
MD5:FA518E3DFAE8CA3A0E495460FD60C791 | SHA256:775853600060162C4B4E5F883F9FD5A278E61C471B3EE1826396B6D129499AA7 | |||
| 3224 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\VersionManager\versionlist.xml | xml | |
MD5:CBD0581678FA40F0EDCBC7C59E0CAD10 | SHA256:159BD4343F344A08F6AF3B716B6FA679859C1BD1D7030D26FF5EF0255B86E1D9 | |||
| 3792 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | compressed | |
MD5:F7DCB24540769805E5BB30D193944DCE | SHA256:6B88C6AC55BBD6FEA0EBE5A760D1AD2CFCE251C59D0151A1400701CB927E36EA | |||
| 3224 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\VersionManager\verFBE6.tmp | xml | |
MD5:CBD0581678FA40F0EDCBC7C59E0CAD10 | SHA256:159BD4343F344A08F6AF3B716B6FA679859C1BD1D7030D26FF5EF0255B86E1D9 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
15
TCP/UDP connections
48
DNS requests
25
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3792 | iexplore.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?5bd9e92495a37f72 | US | compressed | 4.70 Kb | whitelisted |
3792 | iexplore.exe | GET | 200 | 18.165.185.120:80 | http://o.ss2.us//MEowSDBGMEQwQjAJBgUrDgMCGgUABBSLwZ6EW5gdYc9UaSEaaLjjETNtkAQUv1%2B30c7dH4b0W1Ws3NcQwg6piOcCCQCnDkpMNIK3fw%3D%3D | US | binary | 1.70 Kb | whitelisted |
3792 | iexplore.exe | GET | 200 | 104.18.32.68:80 | http://crl.comodoca.com/AAACertificateServices.crl | US | der | 506 b | whitelisted |
3224 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8Ull8gIGmZT9XHrHiJQeI%3D | US | der | 1.47 Kb | whitelisted |
3792 | iexplore.exe | GET | 200 | 104.18.32.68:80 | http://crl.usertrust.com/USERTrustRSACertificationAuthority.crl | US | der | 929 b | whitelisted |
3792 | iexplore.exe | GET | 200 | 18.66.200.130:80 | http://ocsp.rootg2.amazontrust.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBSIfaREXmfqfJR3TkMYnD7O5MhzEgQUnF8A36oB1zArOIiiuG1KnPIRkYMCEwZ%2FlEoqJ83z%2BsKuKwH5CO65xMY%3D | US | der | 1.51 Kb | whitelisted |
3224 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | der | 471 b | whitelisted |
3792 | iexplore.exe | GET | 200 | 18.66.200.39:80 | http://ocsp.rootca1.amazontrust.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBRPWaOUU8%2B5VZ5%2Fa9jFTaU9pkK3FAQUhBjMhTTsvAyUlC4IWZzHshBOCggCEwdzEkpLy9ROx7U76vGUhC06D6E%3D | US | der | 1.39 Kb | shared |
3792 | iexplore.exe | GET | 200 | 192.124.249.23:80 | http://ocsp.starfieldtech.com//MEQwQjBAMD4wPDAJBgUrDgMCGgUABBSLwZ6EW5gdYc9UaSEaaLjjETNtkAQUv1%2B30c7dH4b0W1Ws3NcQwg6piOcCAzkUhA%3D%3D | US | der | 1.70 Kb | whitelisted |
3792 | iexplore.exe | GET | 200 | 52.222.226.205:80 | http://ocsp.r2m02.amazontrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRmbQtwnInkvkvr7BNFR%2BS2lTYPjAQUwDFSzVpQw4J8dHHOy%2Bmc%2BXrrguICEAufowGc7G1h1SSOonC0Xpc%3D | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3792 | iexplore.exe | 52.6.56.188:443 | — | AMAZON-AES | US | suspicious |
3792 | iexplore.exe | 104.18.32.68:80 | ocsp.comodoca.com | CLOUDFLARENET | — | suspicious |
3224 | iexplore.exe | 2.23.209.187:443 | www.bing.com | Akamai International B.V. | GB | suspicious |
3792 | iexplore.exe | 93.184.221.240:80 | ctldl.windowsupdate.com | EDGECAST | GB | whitelisted |
— | — | 172.64.155.188:80 | ocsp.comodoca.com | CLOUDFLARENET | US | suspicious |
— | — | 104.18.32.68:80 | ocsp.comodoca.com | CLOUDFLARENET | — | suspicious |
3792 | iexplore.exe | 172.64.155.188:80 | ocsp.comodoca.com | CLOUDFLARENET | US | suspicious |
— | — | 34.247.154.58:443 | 9hx1x32h.r.eu-west-1.awstrack.me | AMAZON-02 | IE | unknown |
— | — | 52.71.28.102:443 | — | AMAZON-AES | US | suspicious |
3224 | iexplore.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
ctldl.windowsupdate.com |
| whitelisted |
ocsp.comodoca.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
crl.comodoca.com |
| whitelisted |
ocsp.usertrust.com |
| whitelisted |
crl.usertrust.com |
| whitelisted |
ocsp.sectigo.com |
| whitelisted |
9hx1x32h.r.eu-west-1.awstrack.me |
| unknown |
ocsp.digicert.com |
| whitelisted |