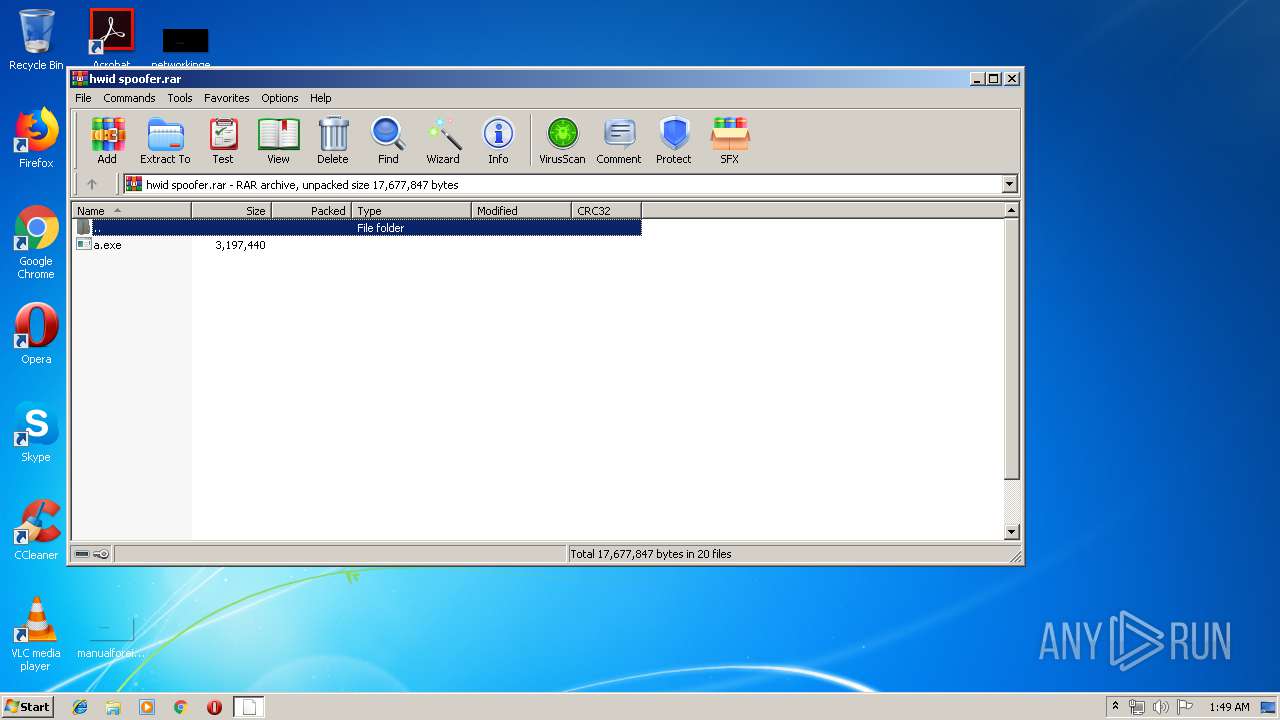
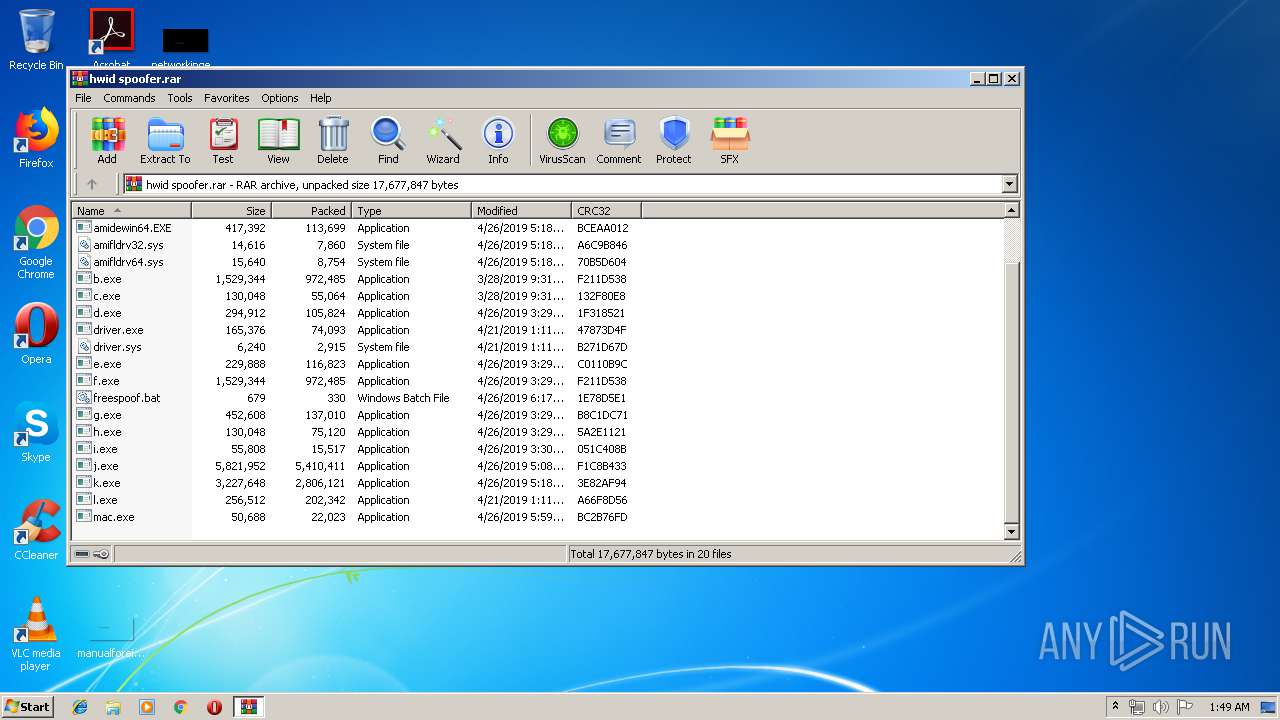
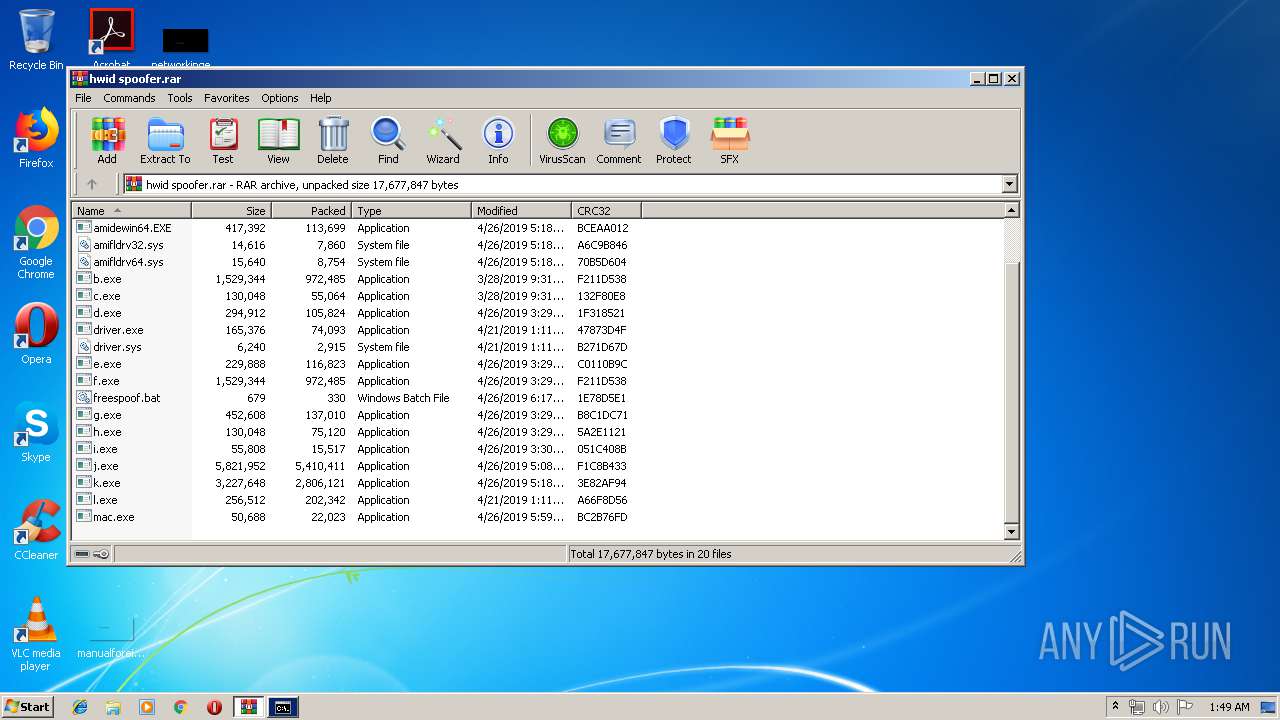
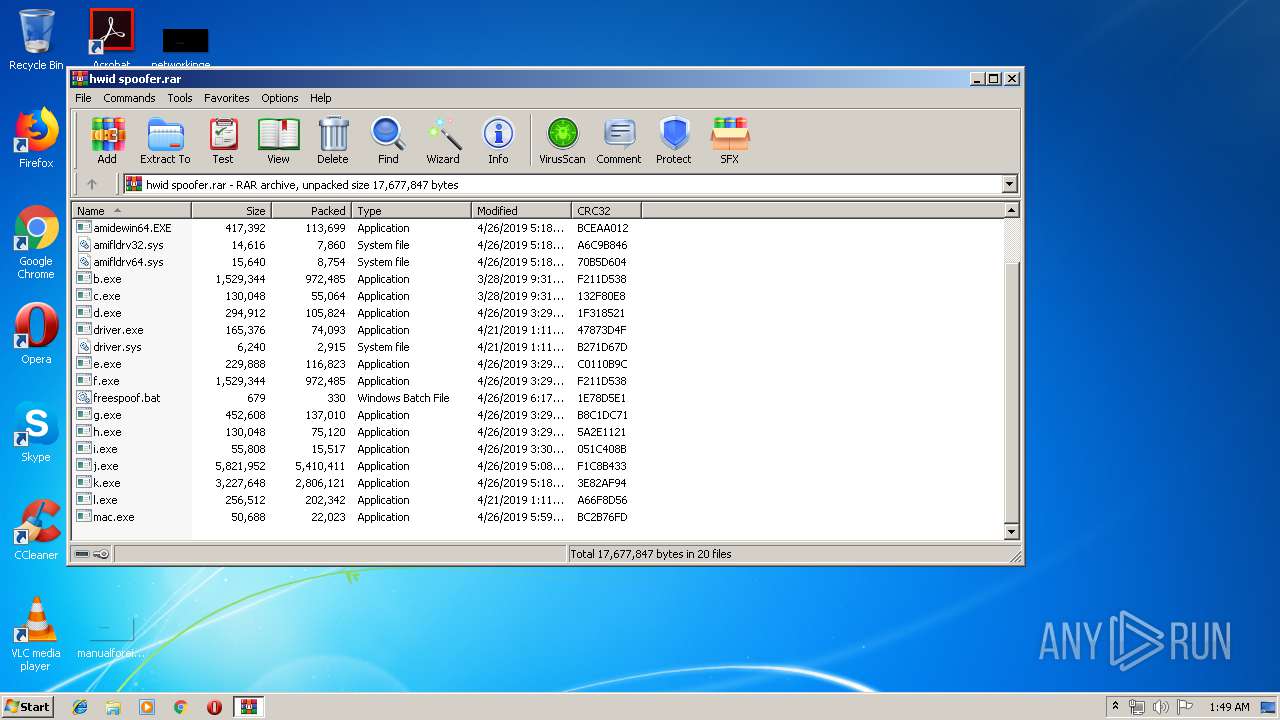
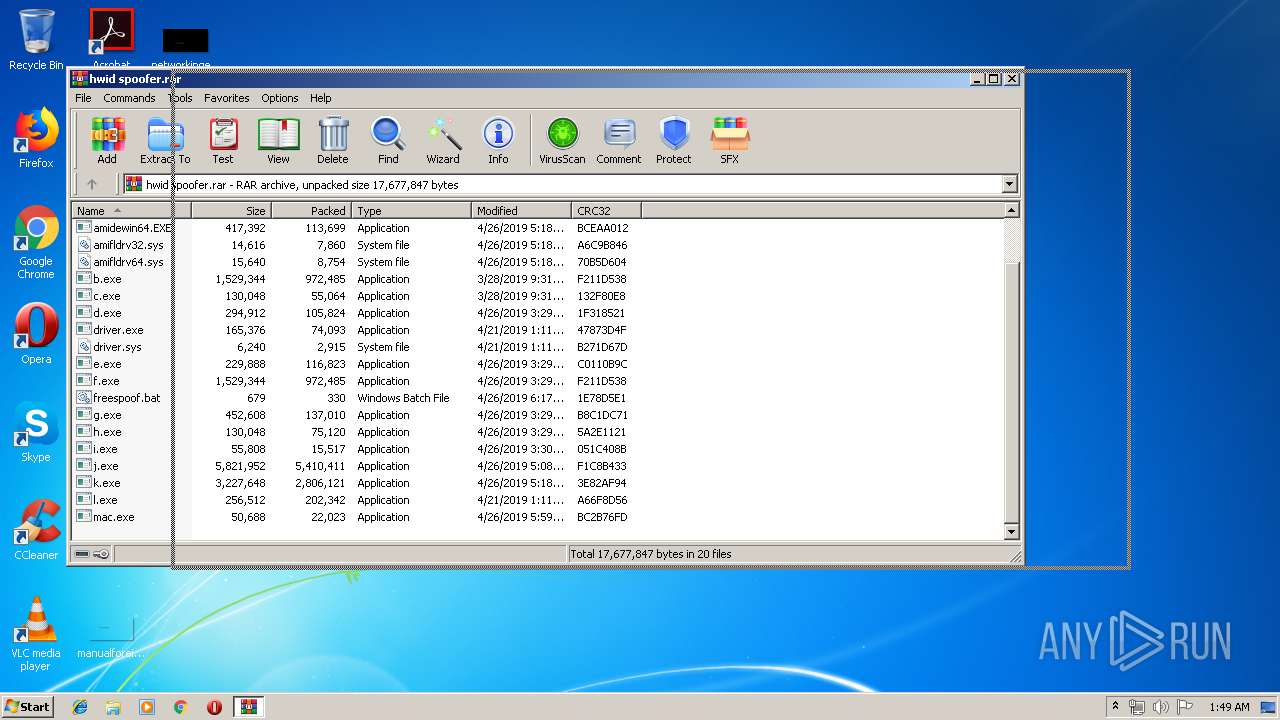
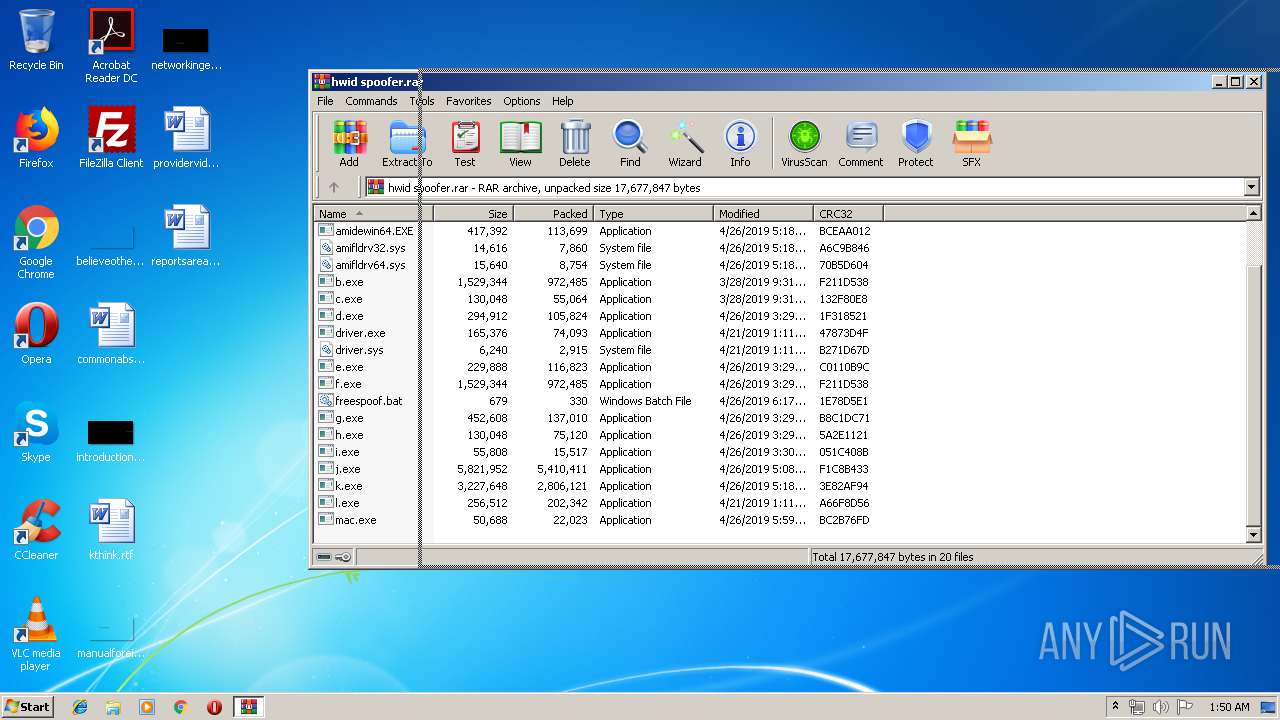
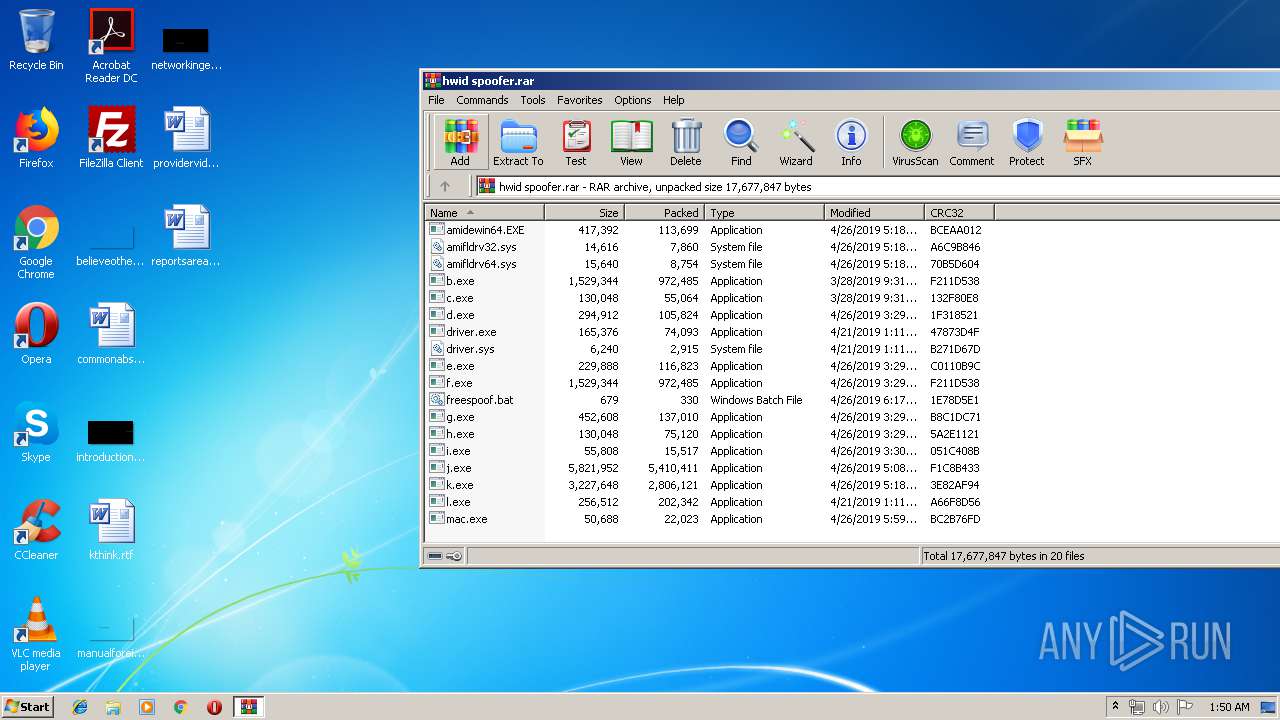
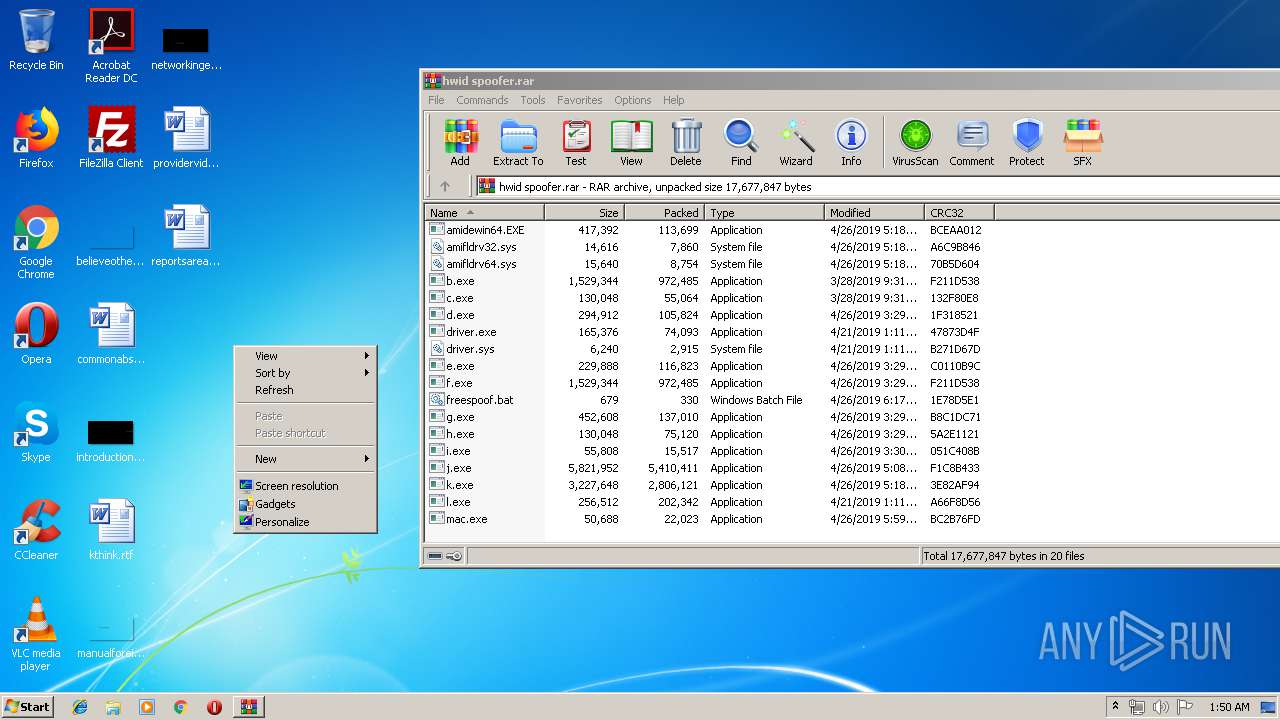
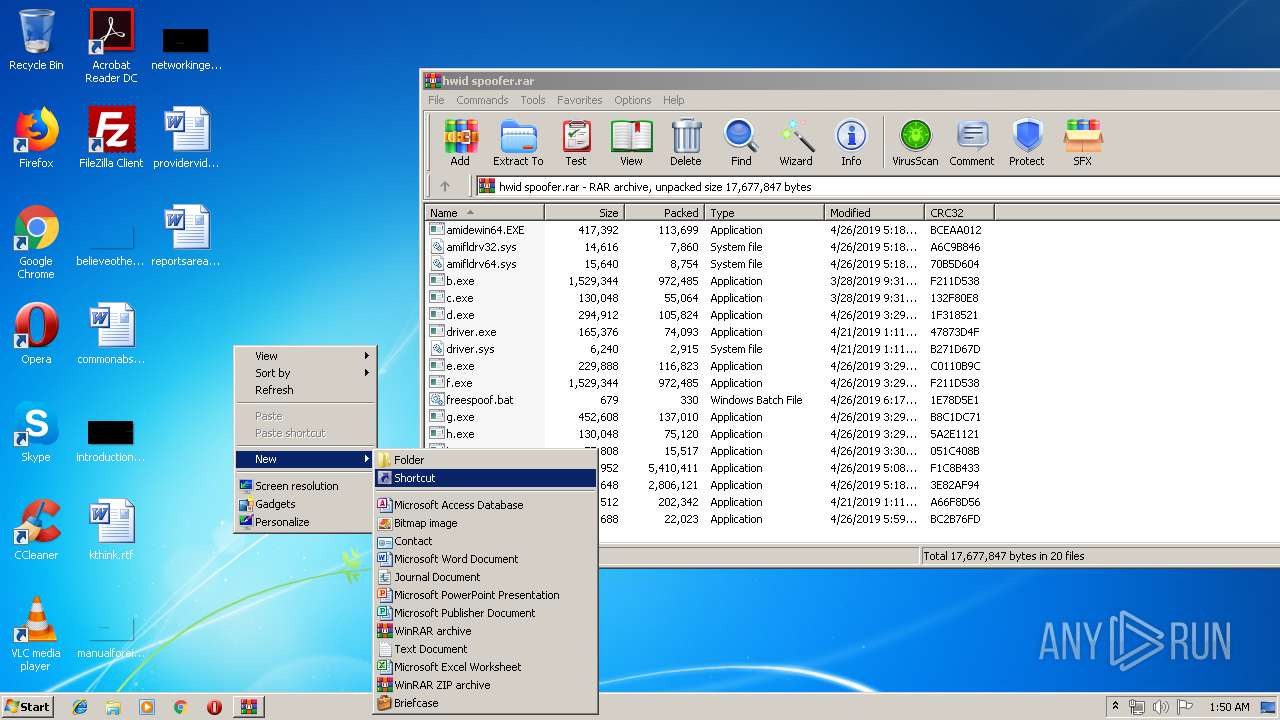
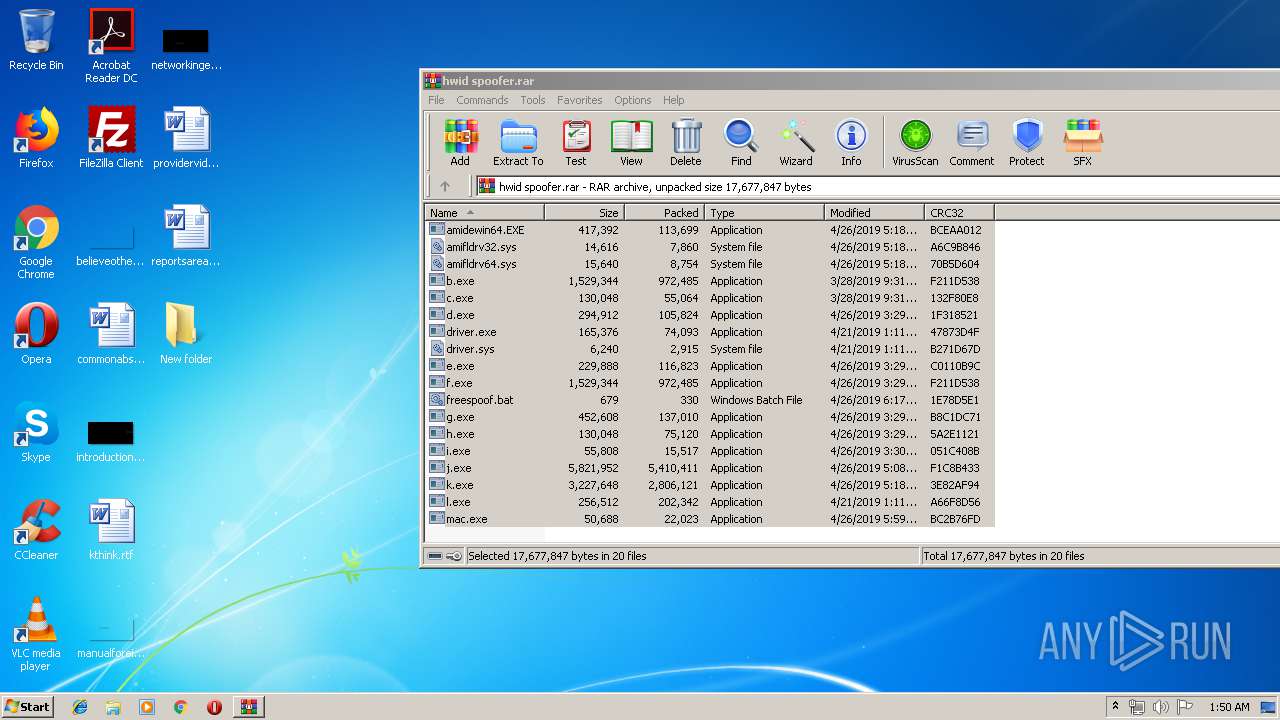
| File name: | hwid spoofer.rar |
| Full analysis: | https://app.any.run/tasks/7e6e3d1a-9871-4d37-9255-8c6e1e70af0e |
| Verdict: | Suspicious activity |
| Analysis date: | June 30, 2019, 00:49:05 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | E2135FDF994237959F9028138BC0D7B7 |
| SHA1: | F39345799ED05BFFDD56462D378293623B09EC0D |
| SHA256: | CF28ABDCF448E81D2FDE3CBF249E51EDACD1FA51B0EB3A687CDBD2AB42EAAEF0 |
| SSDEEP: | 196608:j7xh5LehUnW+is86DEcl/HEox25tFia8aTPPORM49Y+Y1RPjQbHovBoM25i/PaVv:jDEajiFTcdkoQbFi1RkR1RkMvBt2U/qV |
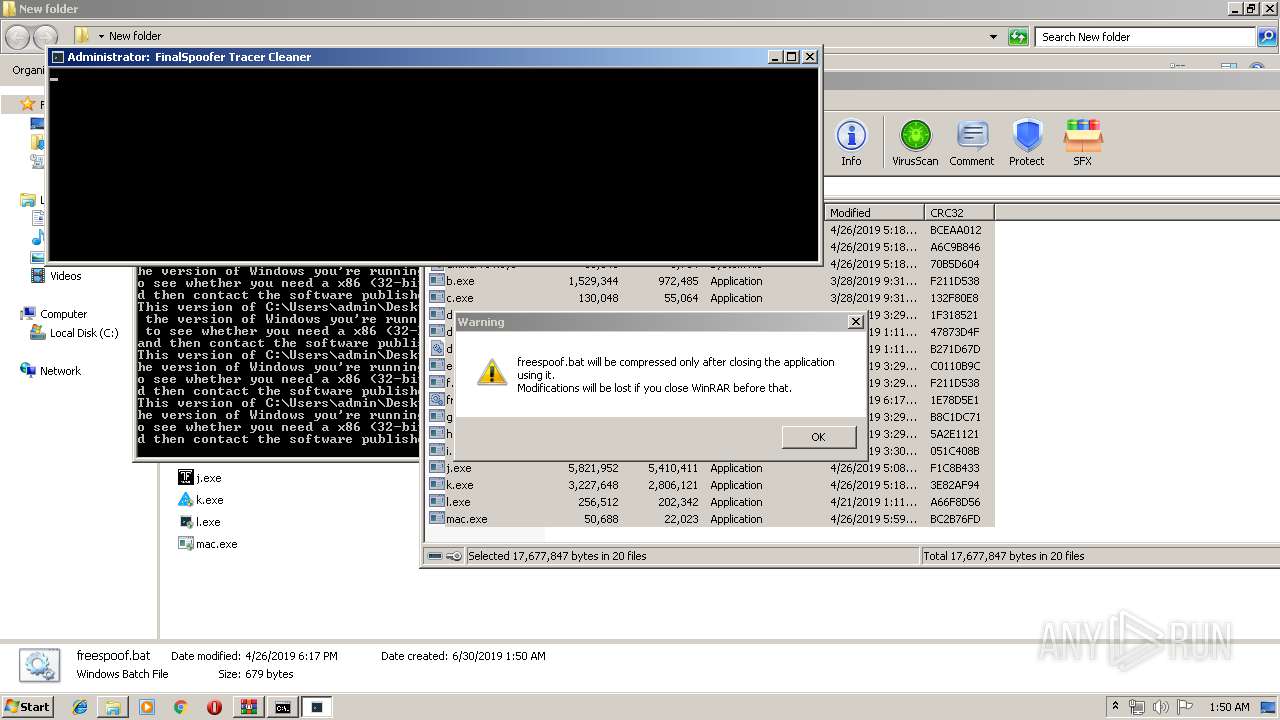
MALICIOUS
Application was dropped or rewritten from another process
- e.exe (PID: 3384)
- h.exe (PID: 3644)
- h.exe (PID: 3392)
- h.exe (PID: 3180)
SUSPICIOUS
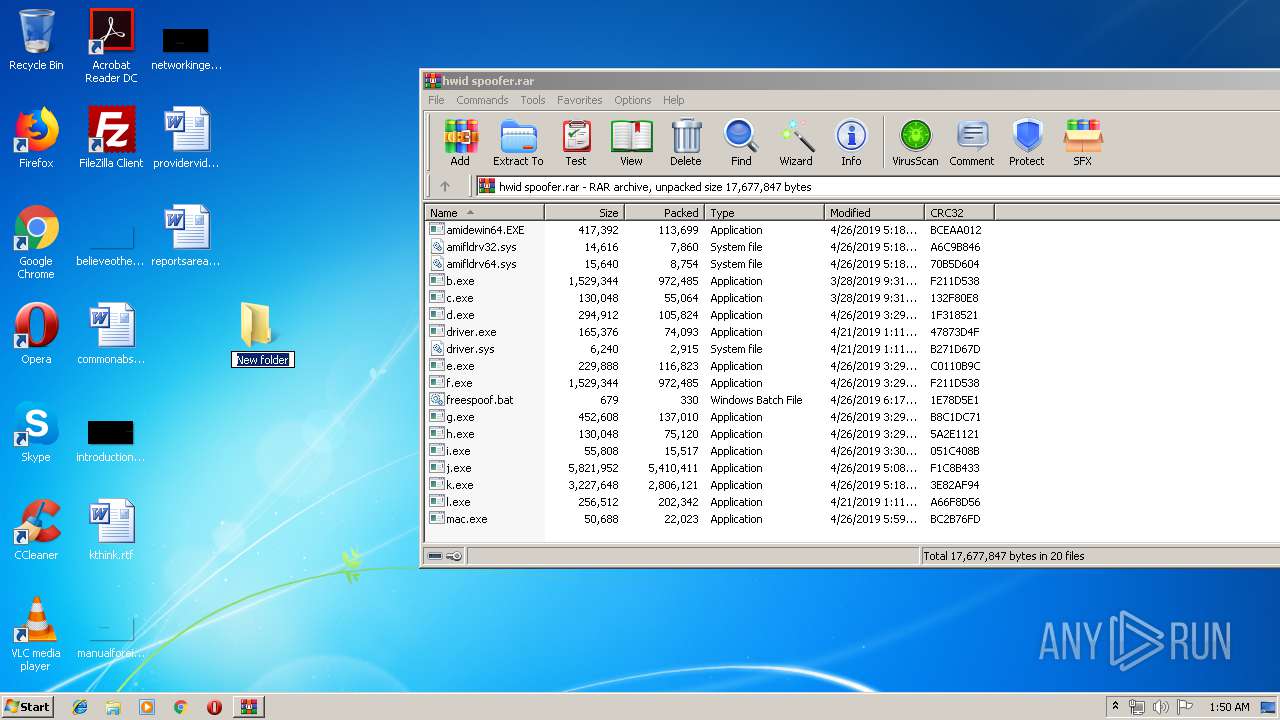
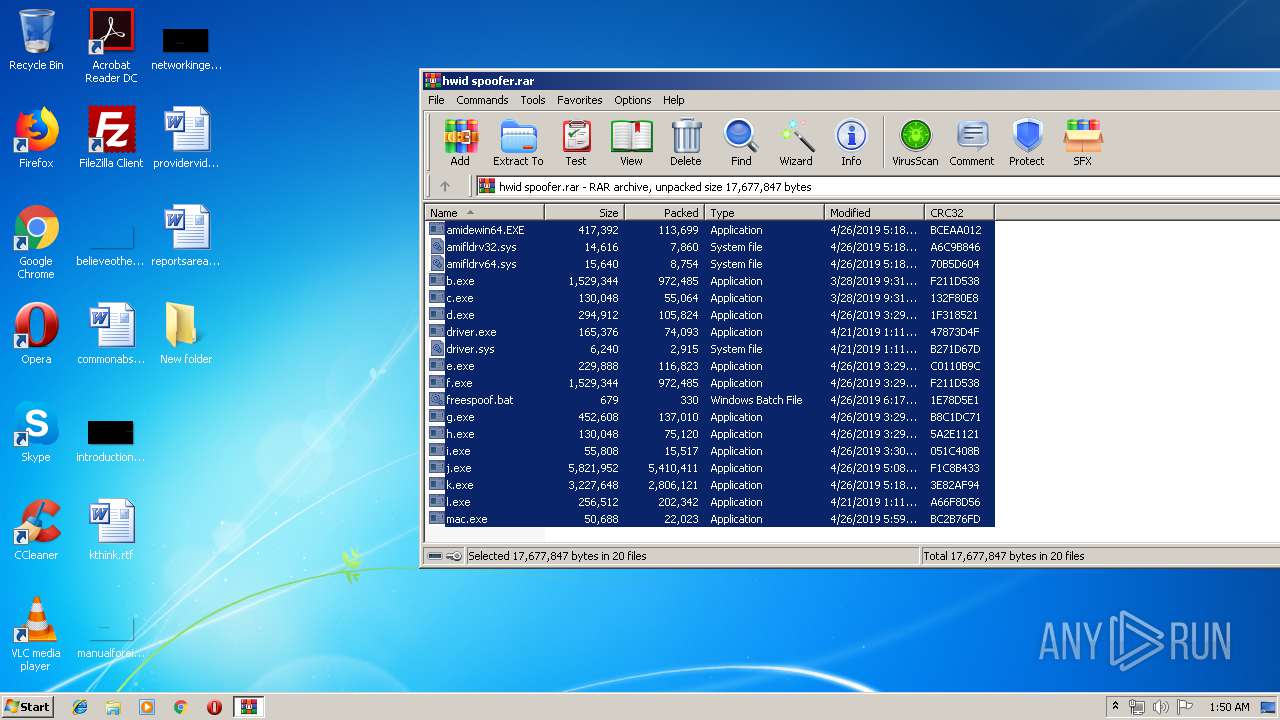
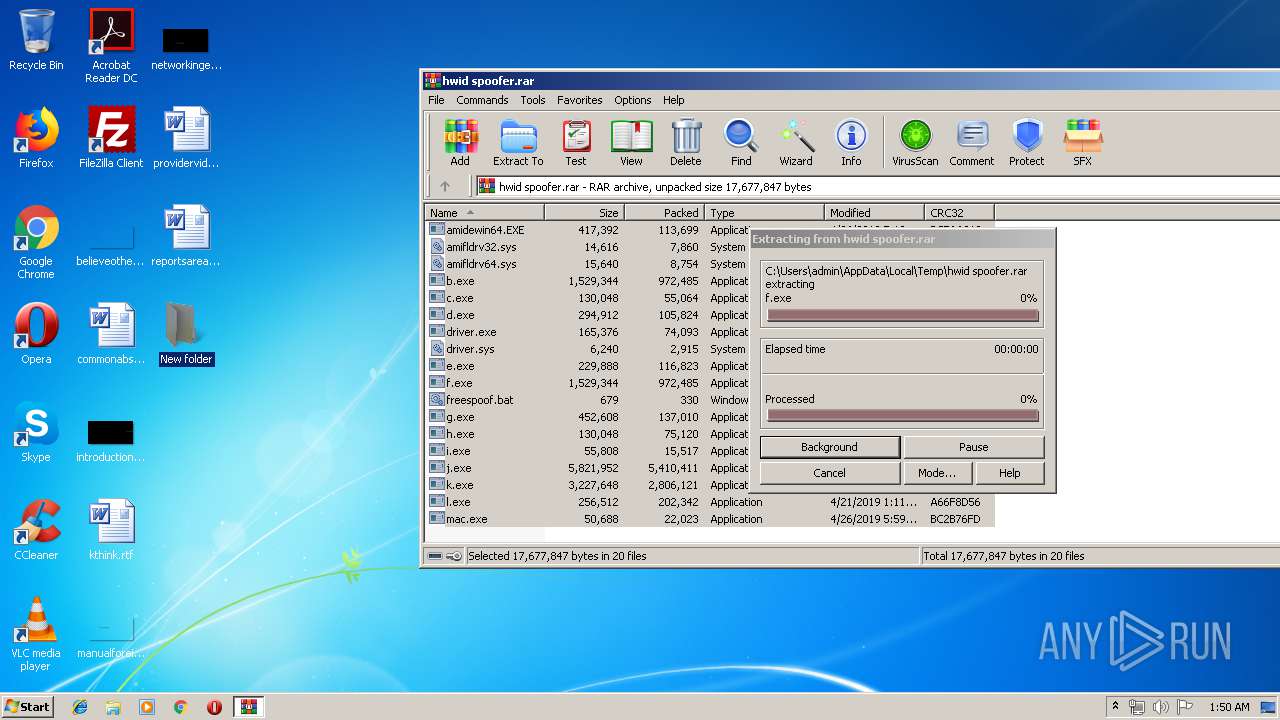
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2060)
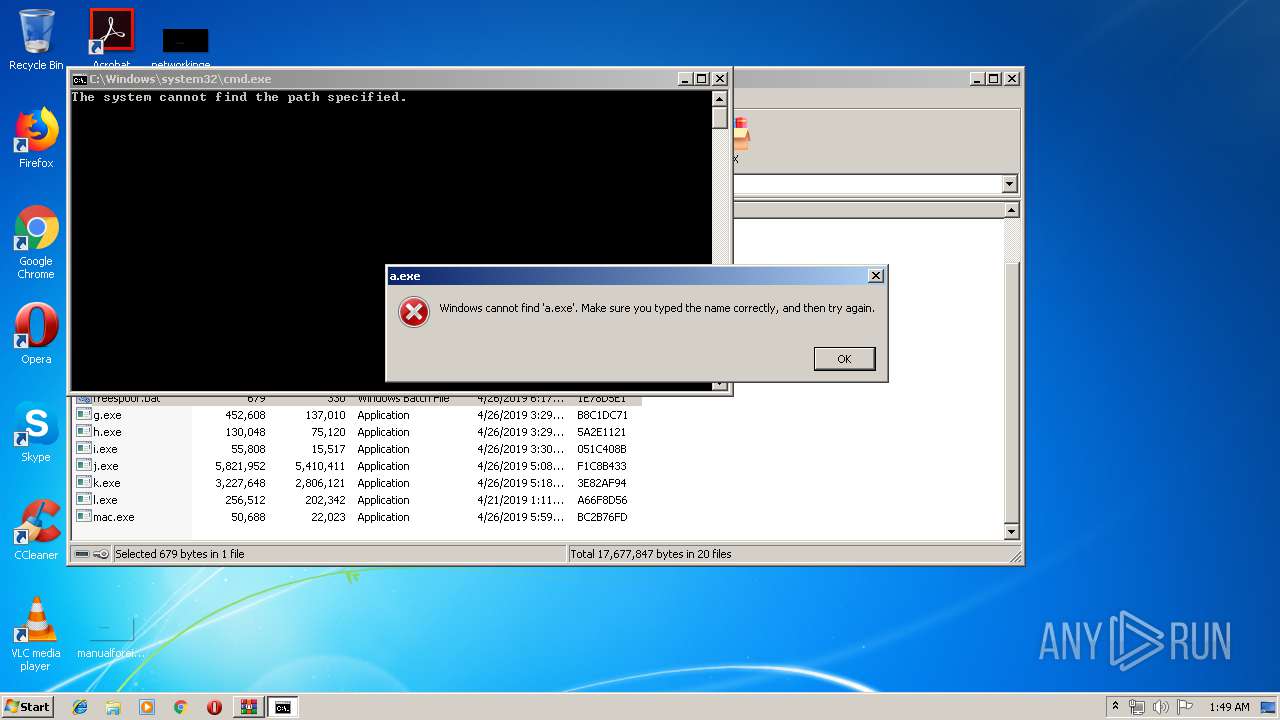
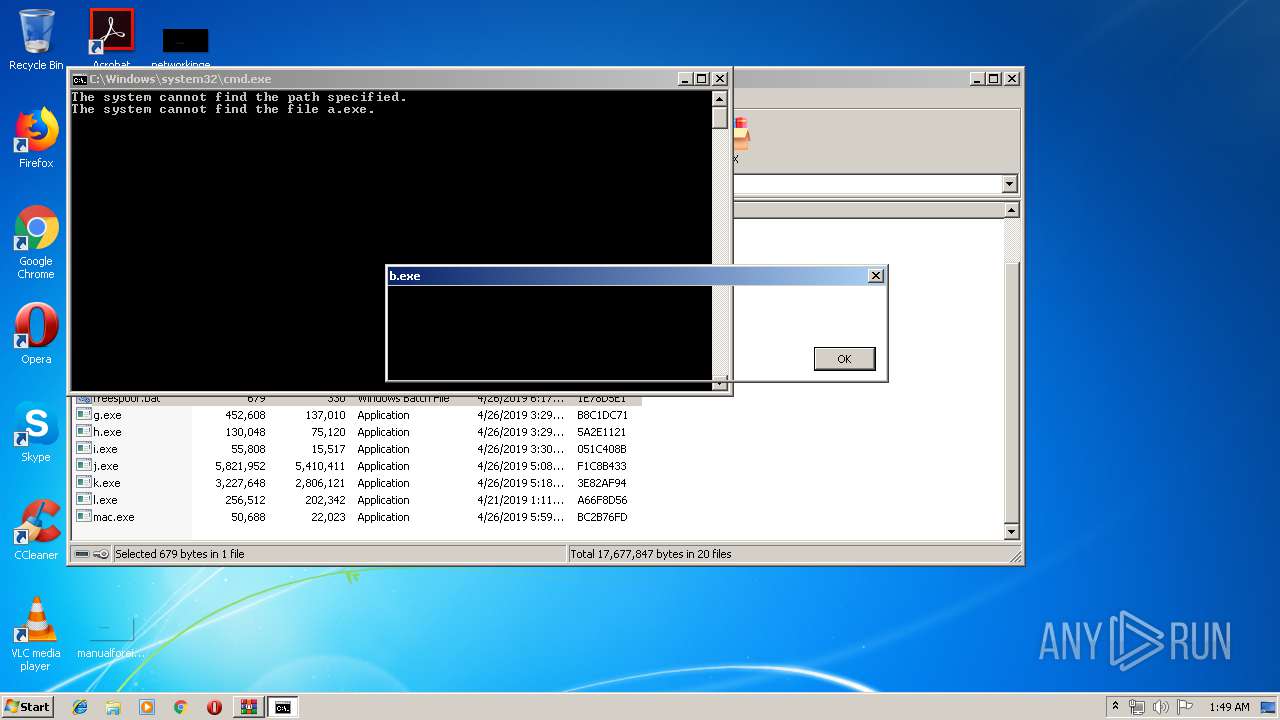
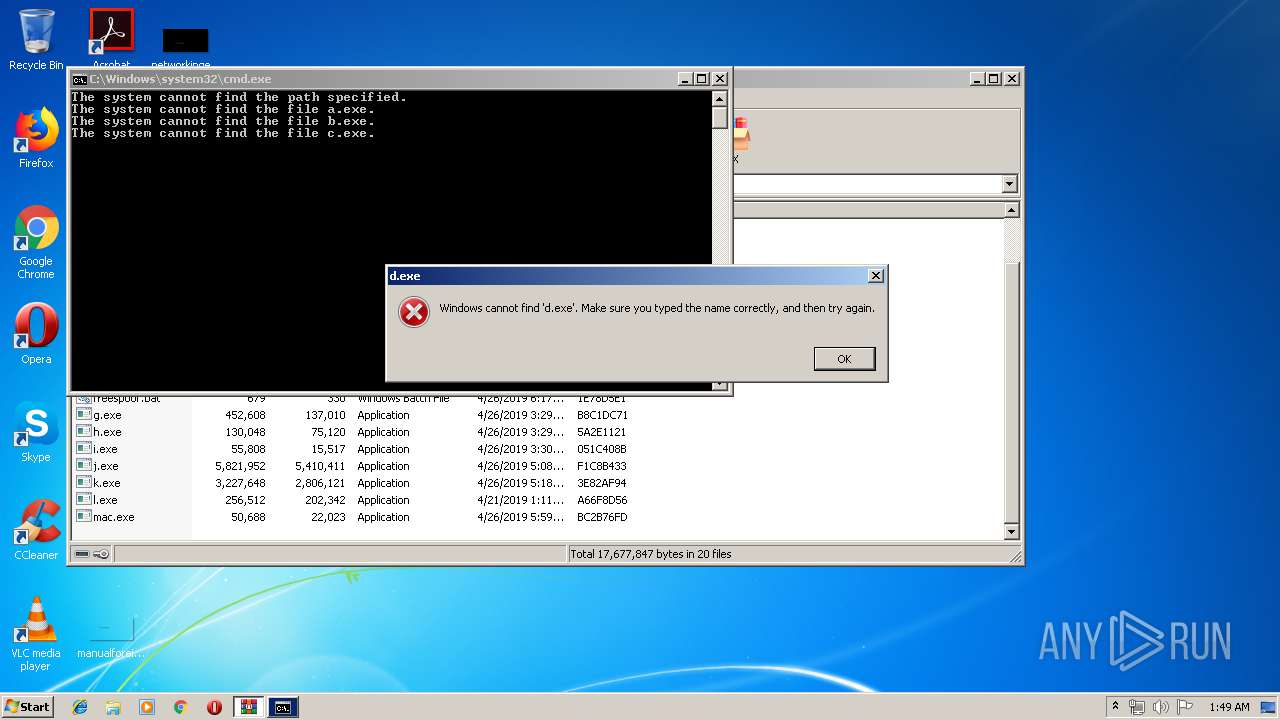
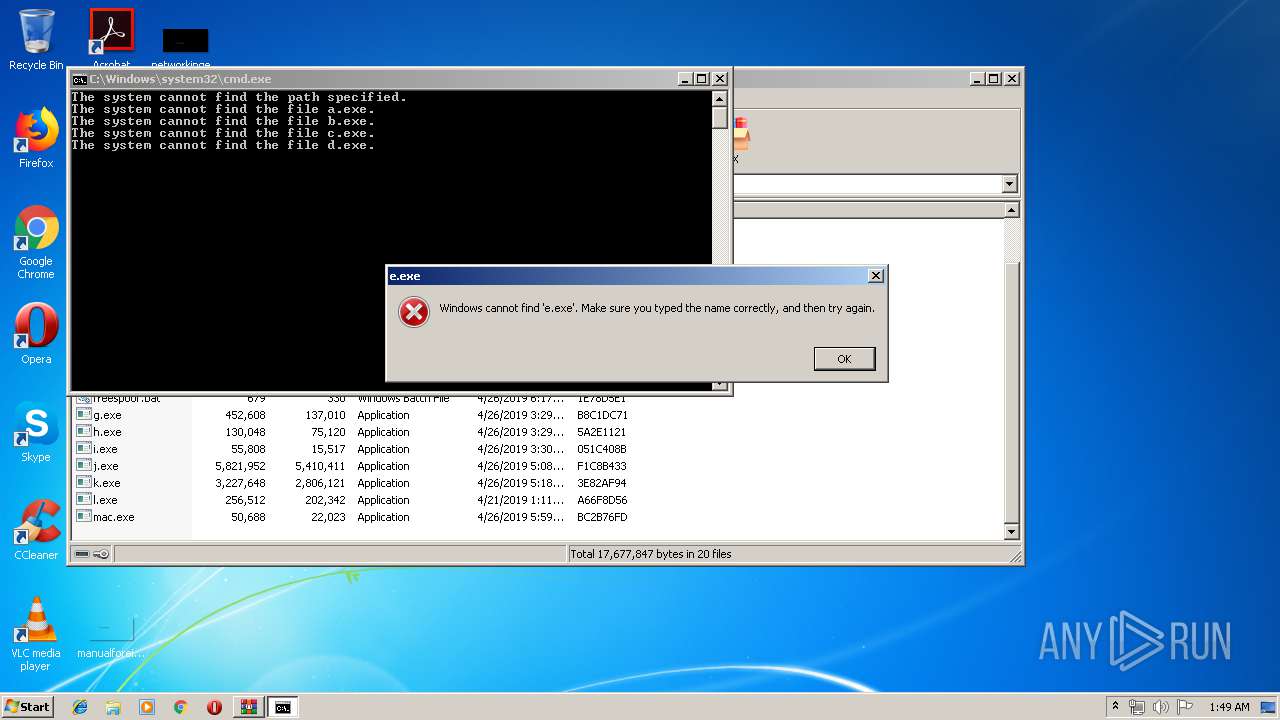
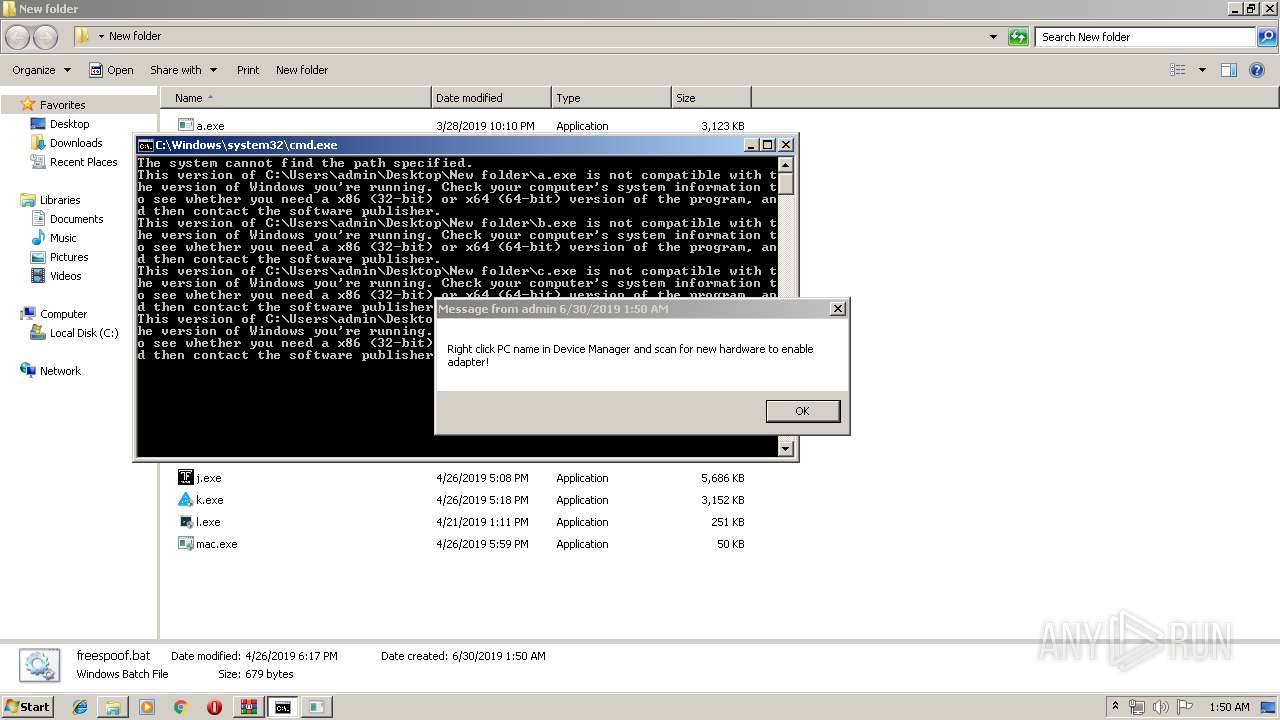
Starts CMD.EXE for commands execution
- WinRAR.exe (PID: 2060)
- h.exe (PID: 3180)
- e.exe (PID: 3384)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 2428)
INFO
Manual execution by user
- cmd.exe (PID: 292)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
Total processes
62
Monitored processes
17
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 292 | cmd /c ""C:\Users\admin\Desktop\New folder\freespoof.bat" " | C:\Windows\system32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
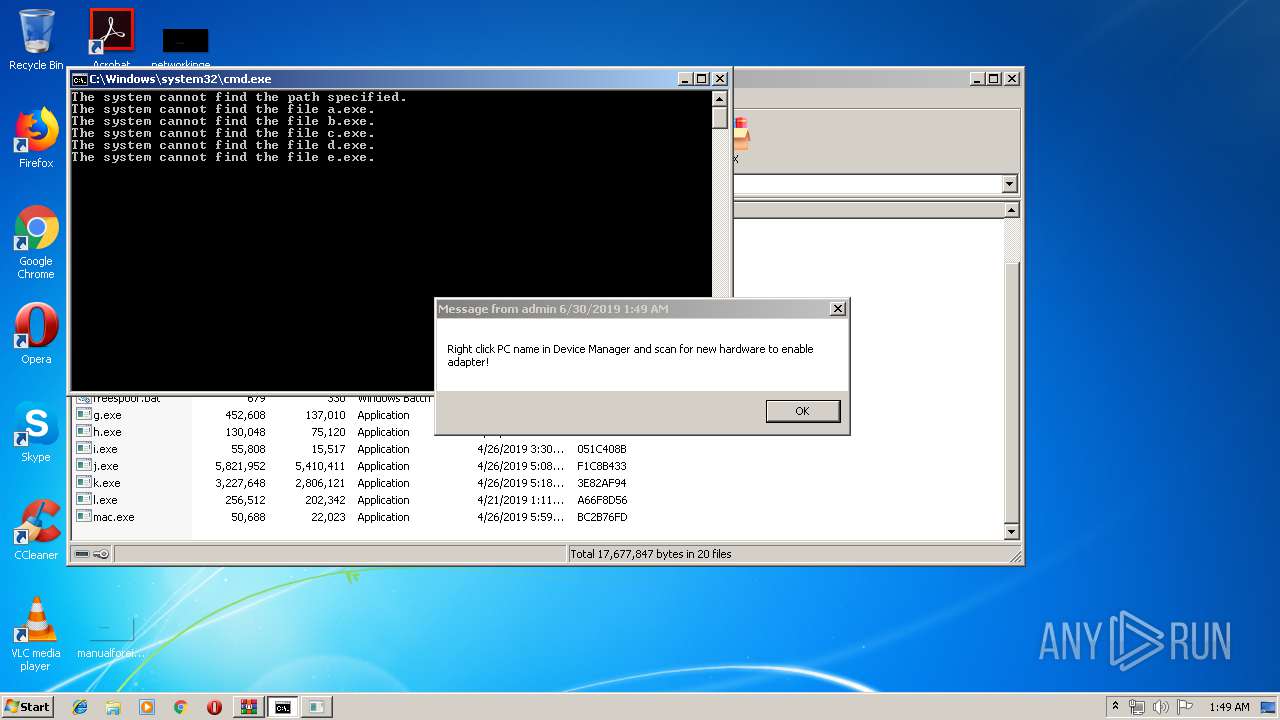
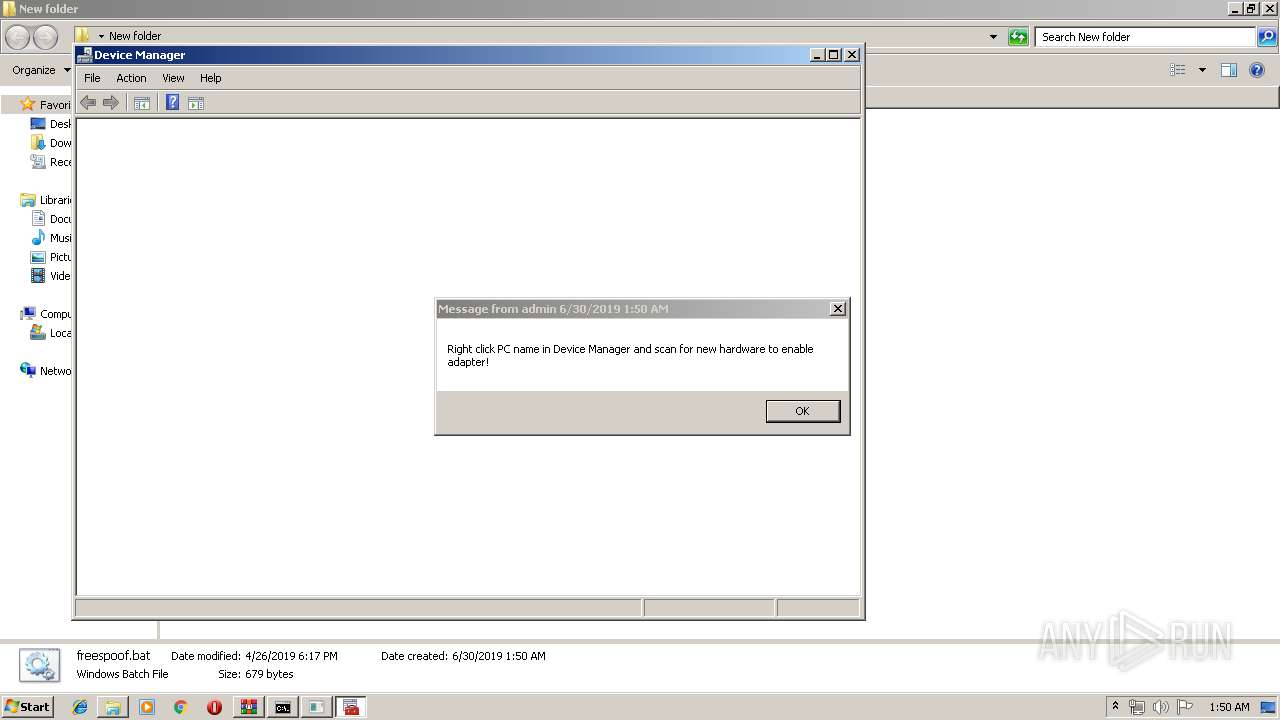
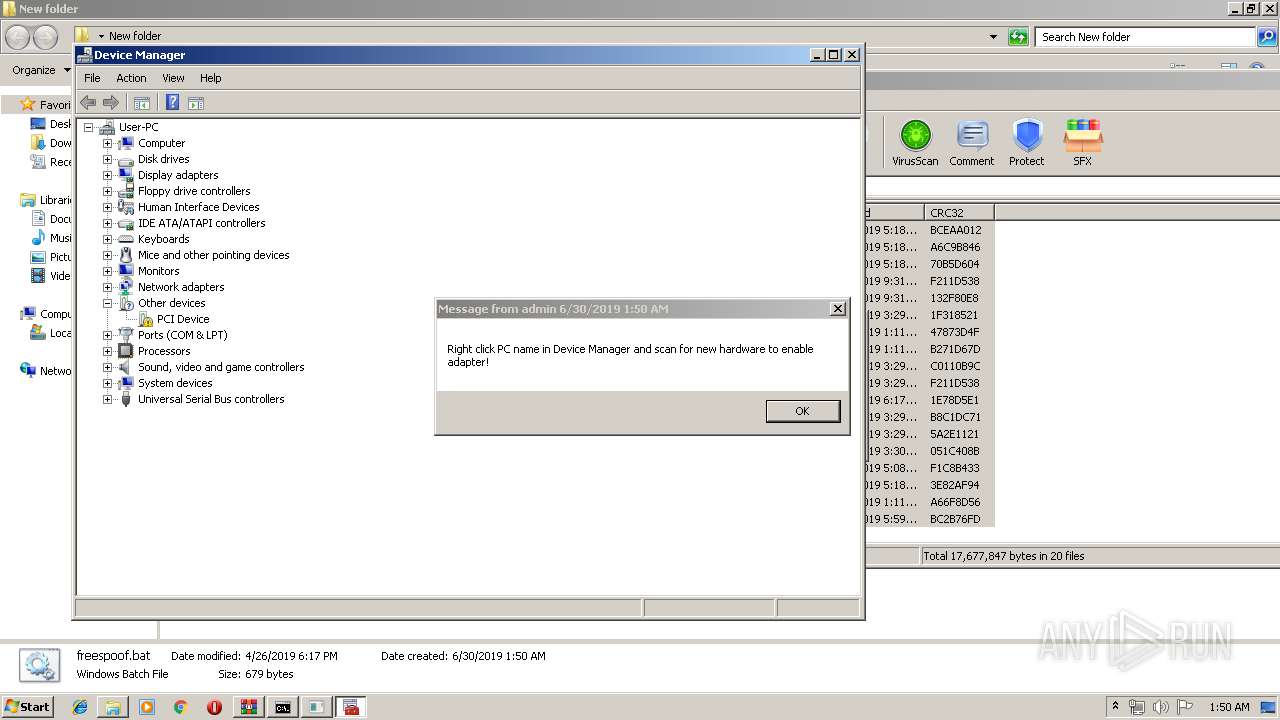
| 392 | msg *.* Right click PC name in Device Manager and scan for new hardware to enable adapter! | C:\Windows\system32\msg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Message Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
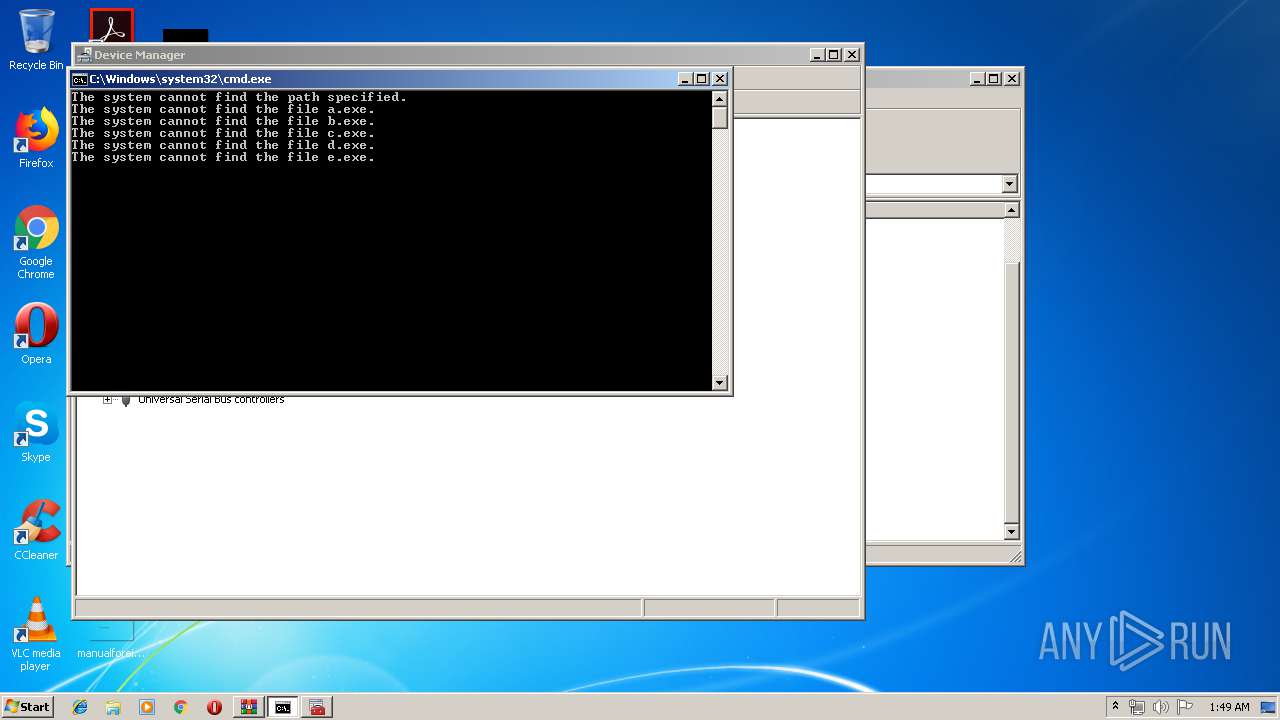
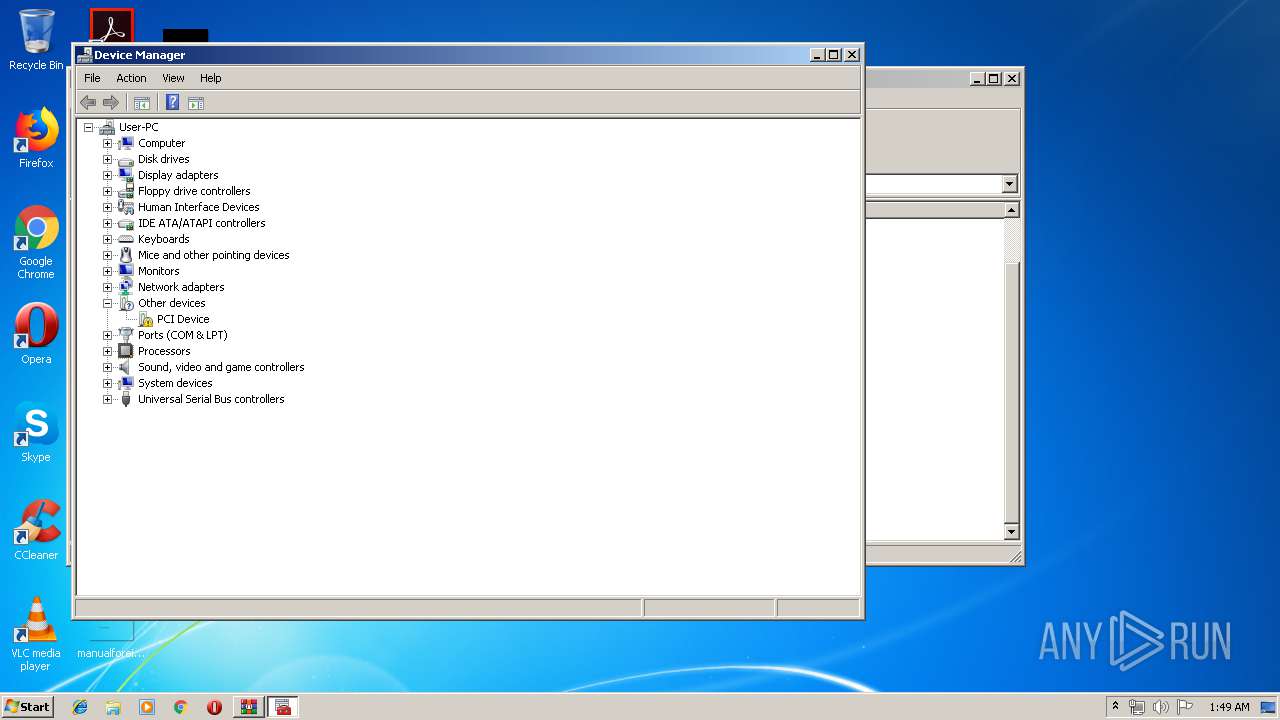
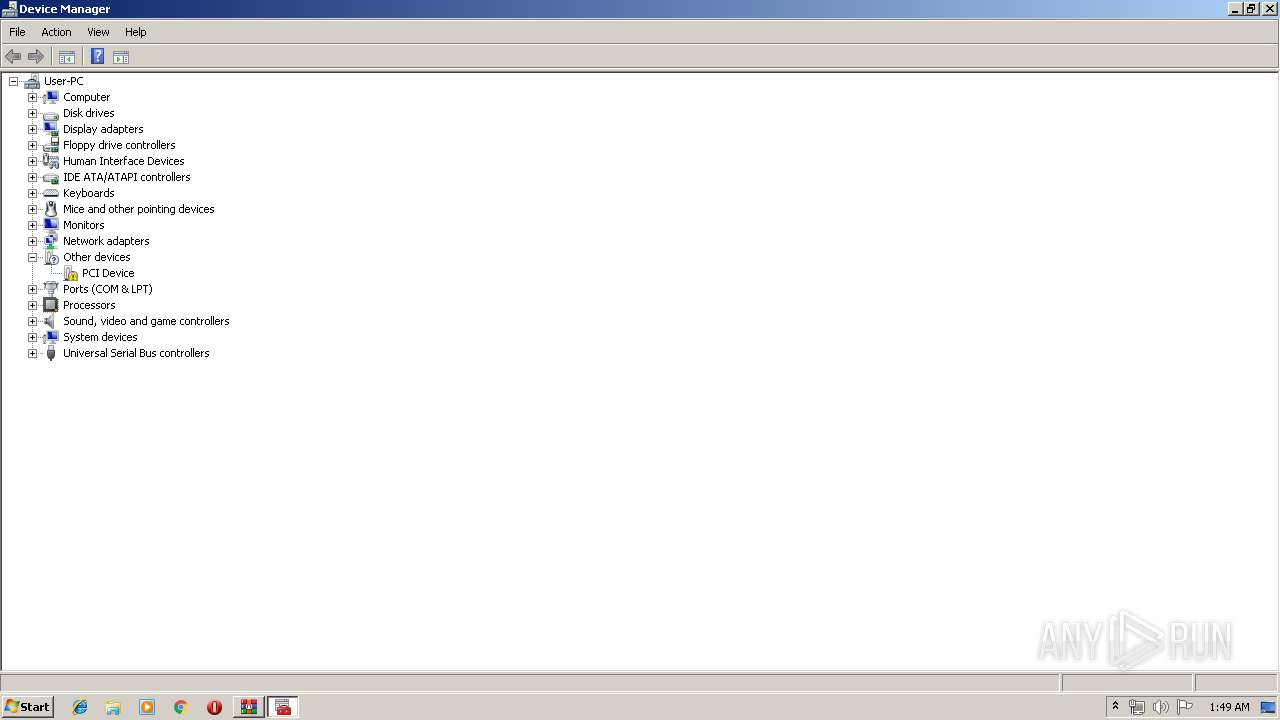
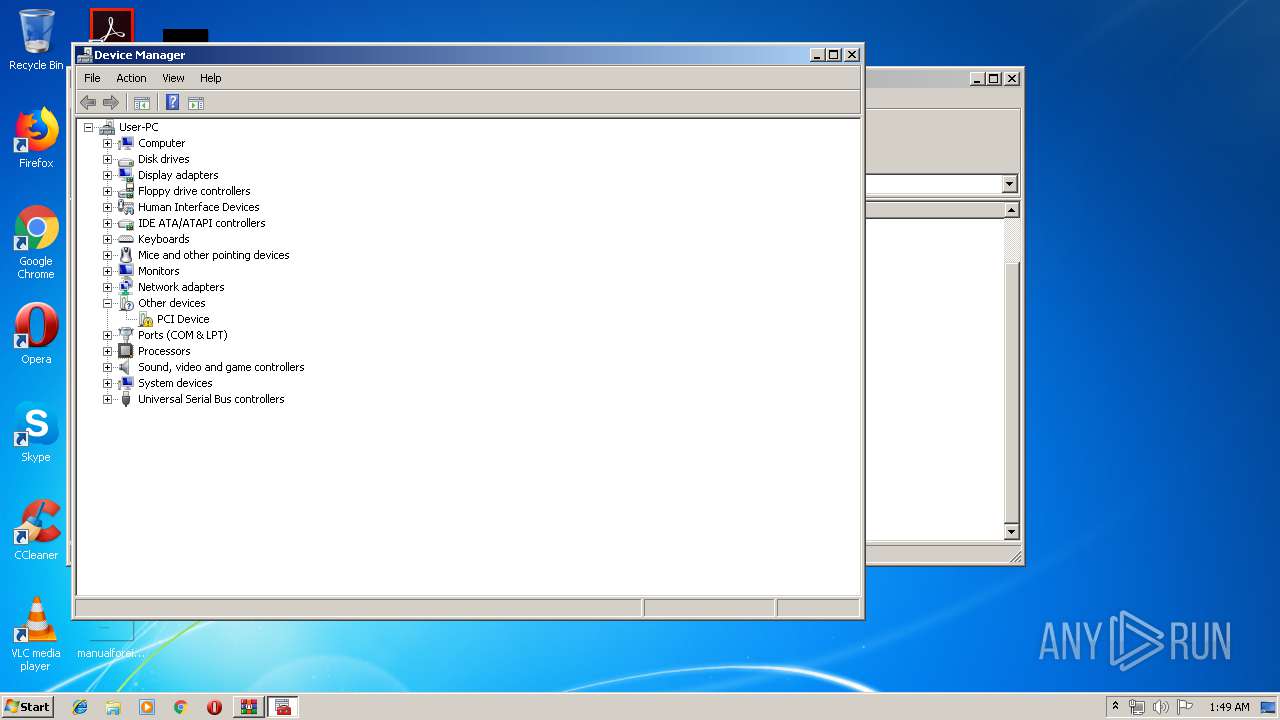
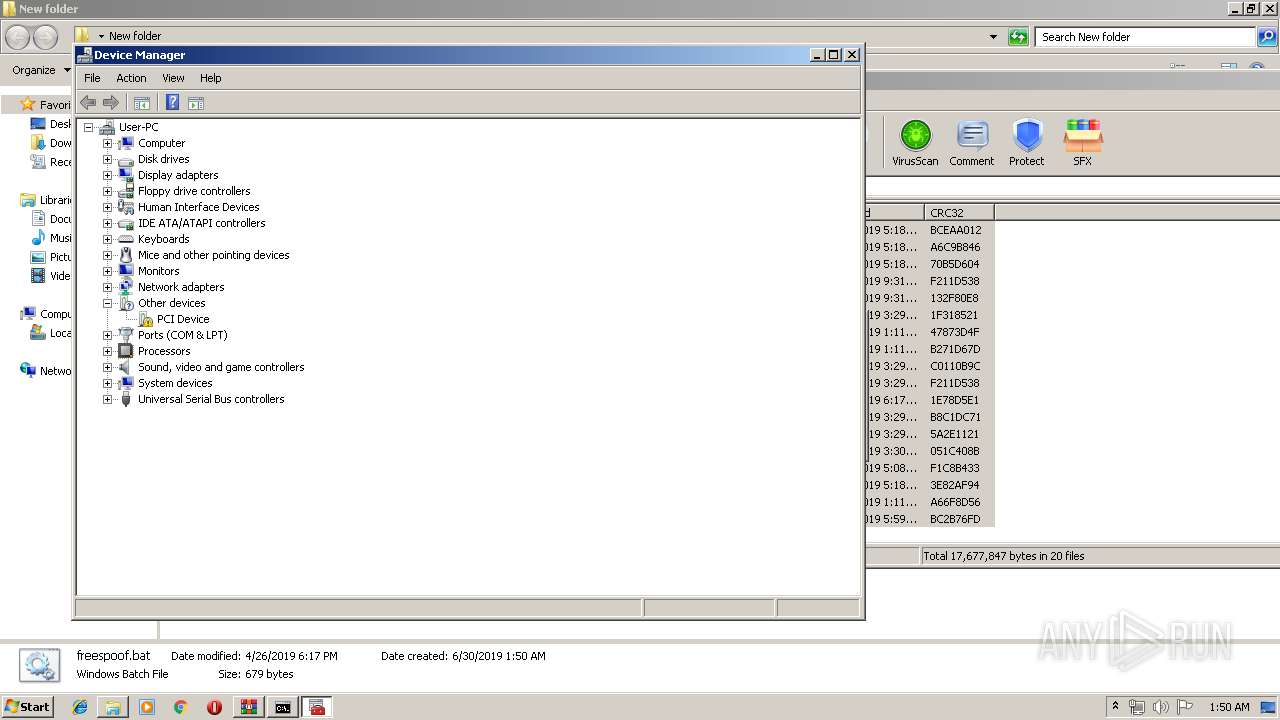
| 1844 | "C:\Windows\system32\mmc.exe" "C:\Windows\system32\devmgmt.msc" | C:\Windows\system32\mmc.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Management Console Exit code: 3221226540 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1868 | cmd /c ""C:\Users\admin\AppData\Local\Temp\Rar$DIa2060.27922\freespoof.bat" " | C:\Windows\system32\cmd.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 3221225786 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2060 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\hwid spoofer.rar" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 2104 | "C:\Windows\system32\mmc.exe" "C:\Windows\system32\devmgmt.msc" | C:\Windows\system32\mmc.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Management Console Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2228 | cmd /c ""C:\Users\admin\AppData\Local\Temp\2588.tmp\delet.bat"" | C:\Windows\system32\cmd.exe | — | e.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2304 | "C:\Windows\system32\mmc.exe" "C:\Windows\system32\devmgmt.msc" | C:\Windows\system32\mmc.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Management Console Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2428 | "C:\Windows\system32\cmd" /c "C:\Users\admin\AppData\Local\Temp\3D27.tmp\3D28.tmp\3D29.bat "C:\Users\admin\Desktop\New folder\h.exe"" | C:\Windows\system32\cmd.exe | — | h.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) | |||||||||||||||
| 2484 | taskkill /f /im "BEService.exe" /t /fi "status eq running" | C:\Windows\system32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) | |||||||||||||||
Total events
718
Read events
672
Write events
44
Delete events
2
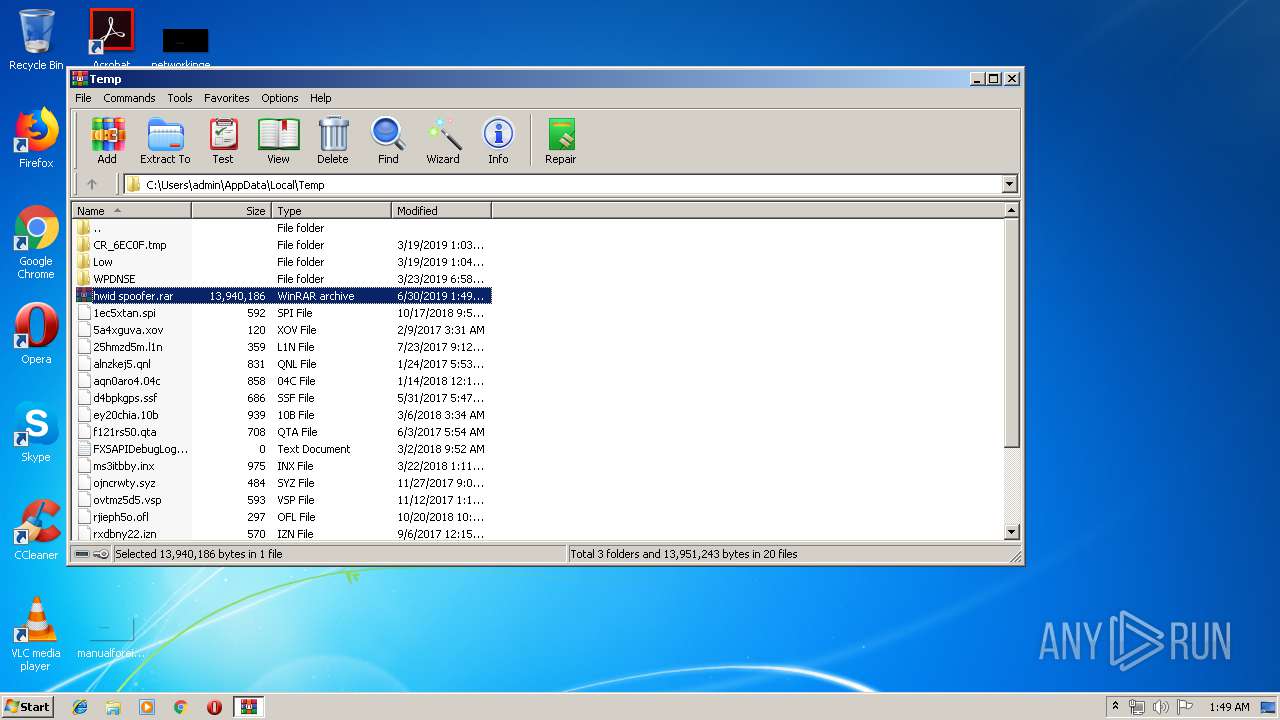
Modification events
| (PID) Process: | (2060) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2060) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2060) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2060) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\hwid spoofer.rar | |||
| (PID) Process: | (2060) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2060) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2060) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2060) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2060) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | @C:\Windows\System32\acppage.dll,-6002 |
Value: Windows Batch File | |||
| (PID) Process: | (2060) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\ArcColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
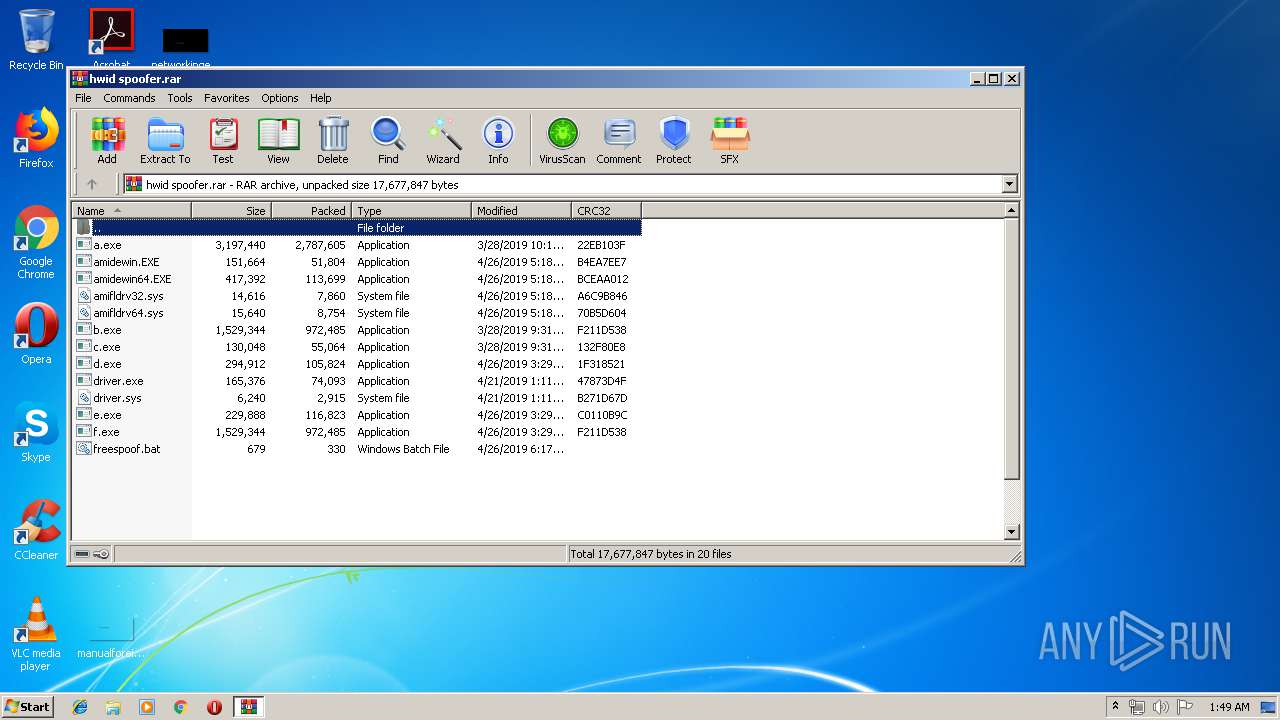
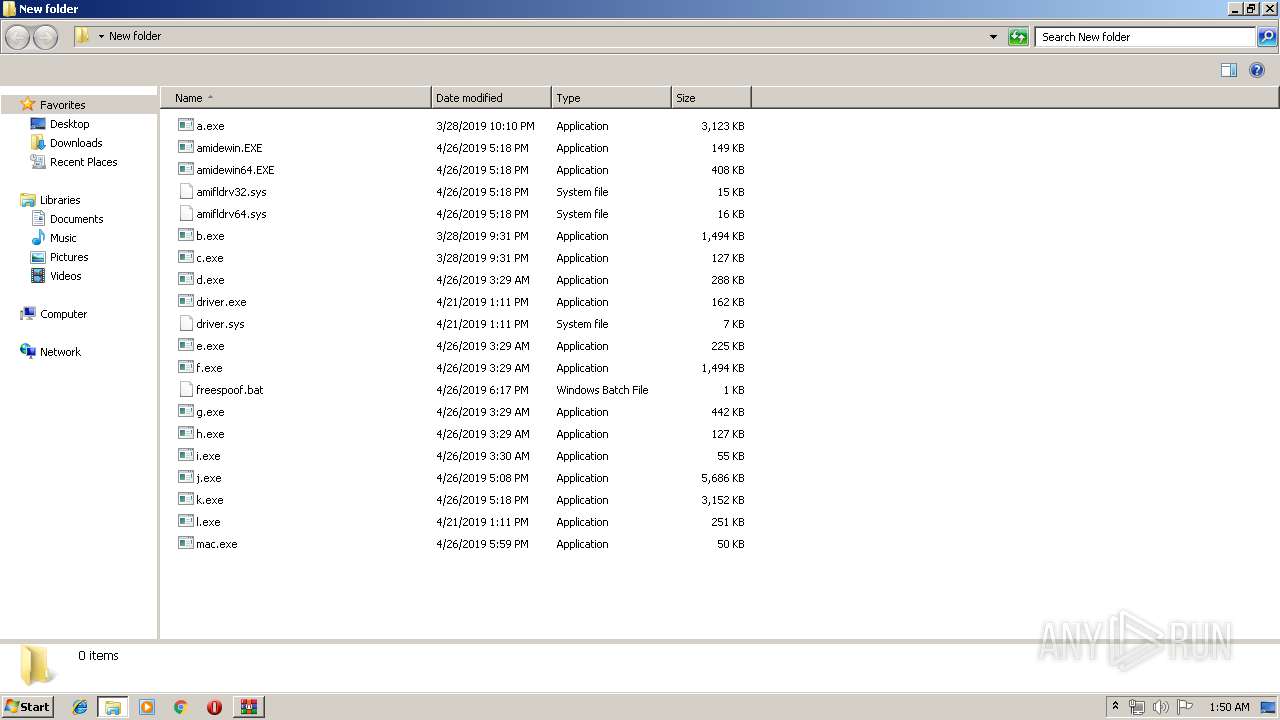
Executable files
17
Suspicious files
0
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2060 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2060.31698\k.exe | — | |
MD5:— | SHA256:— | |||
| 2060 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2060.31698\l.exe | — | |
MD5:— | SHA256:— | |||
| 3384 | e.exe | C:\Users\admin\AppData\Local\Temp\2588.tmp\delet.bat | — | |
MD5:— | SHA256:— | |||
| 3180 | h.exe | C:\Users\admin\AppData\Local\Temp\3D27.tmp\3D28.tmp\3D29.bat | — | |
MD5:— | SHA256:— | |||
| 2060 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2060.31698\c.exe | executable | |
MD5:— | SHA256:— | |||
| 2060 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2060.31698\driver.exe | executable | |
MD5:— | SHA256:— | |||
| 2060 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2060.31698\e.exe | executable | |
MD5:— | SHA256:— | |||
| 2060 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2060.31698\freespoof.bat | text | |
MD5:— | SHA256:— | |||
| 2060 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2060.31698\g.exe | executable | |
MD5:— | SHA256:— | |||
| 2060 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2060.31698\f.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report