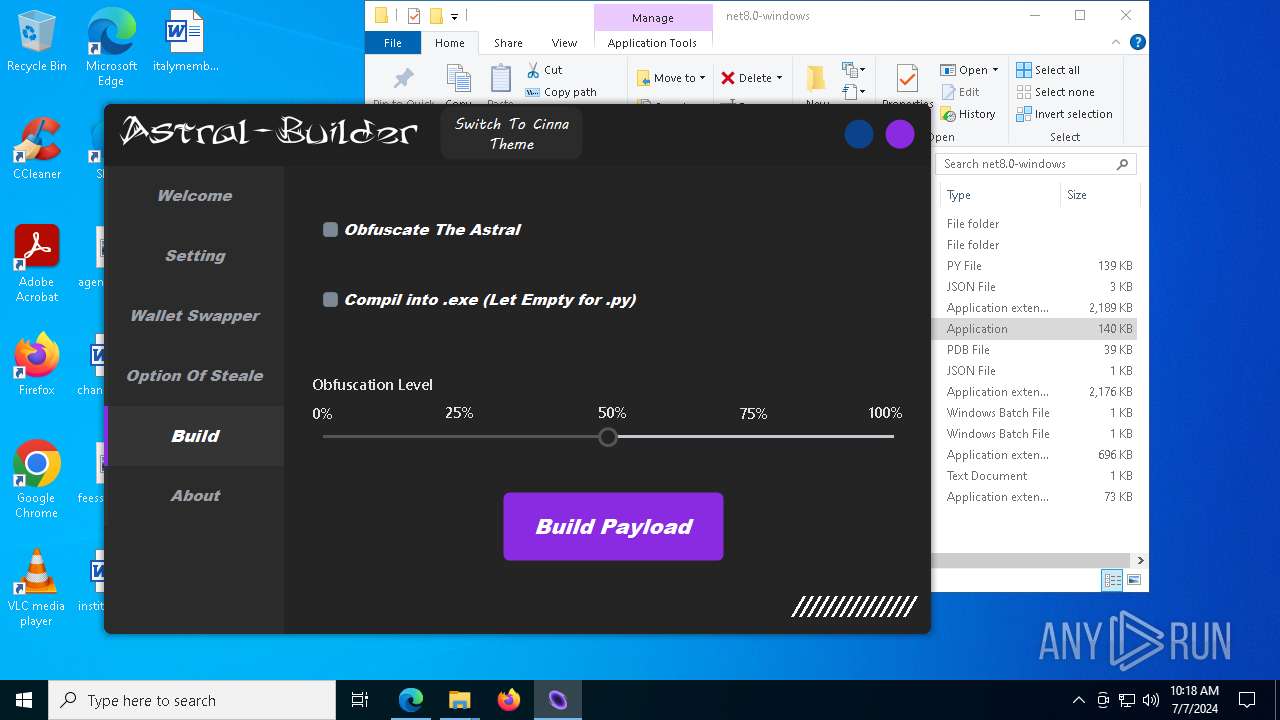
| download: | /freeman649/Astral-Stealer/releases/download/theme/Astral-Stealer-v1.8.zip |
| Full analysis: | https://app.any.run/tasks/7162bbaf-9736-4ecc-b6ad-a6a42ba819e1 |
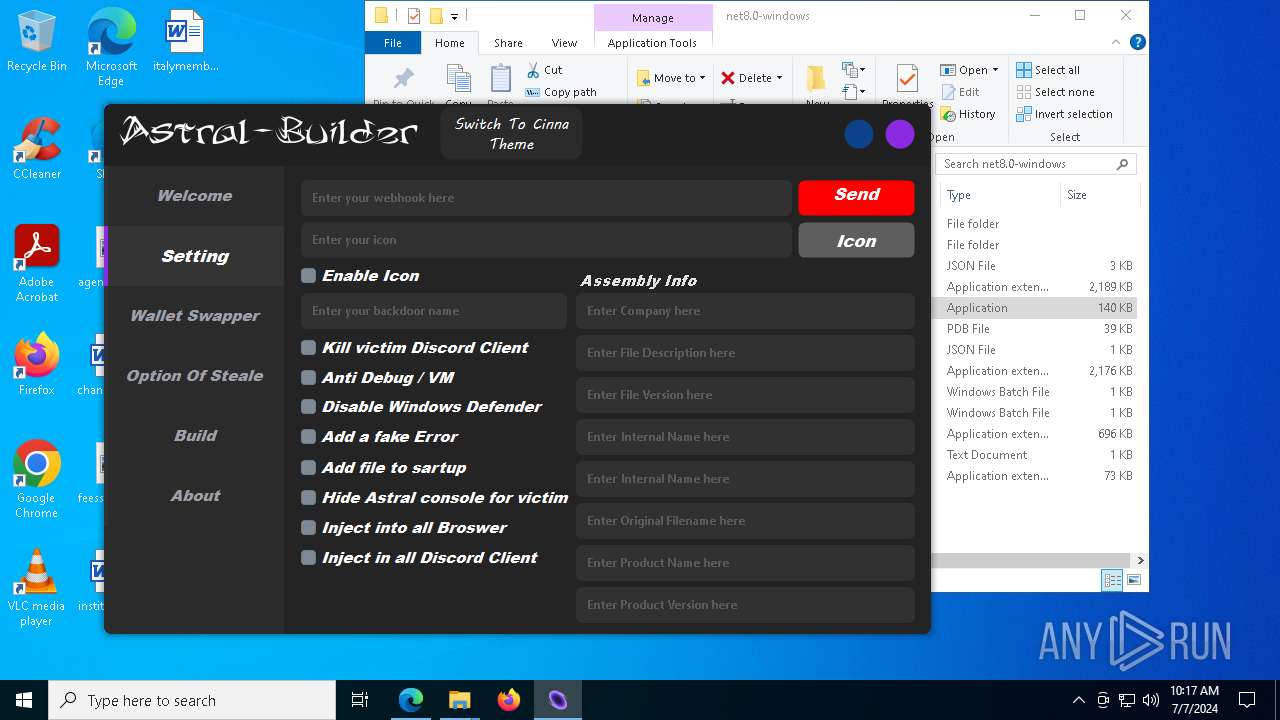
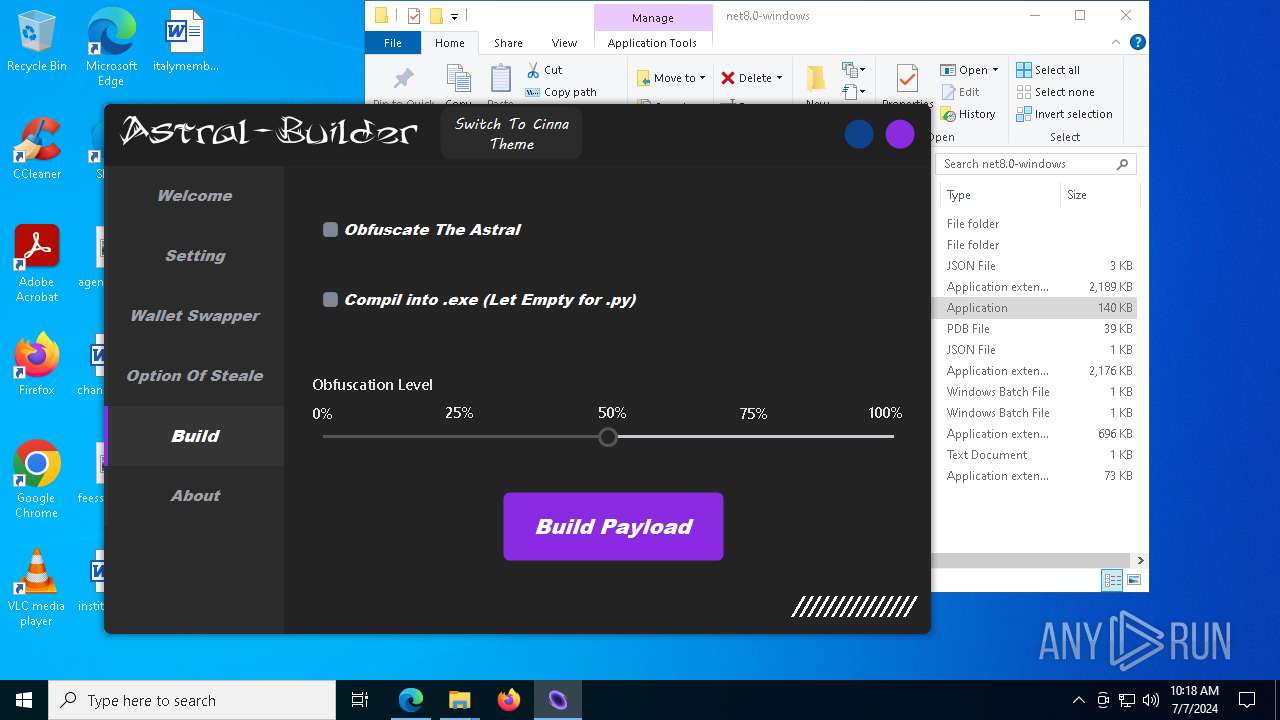
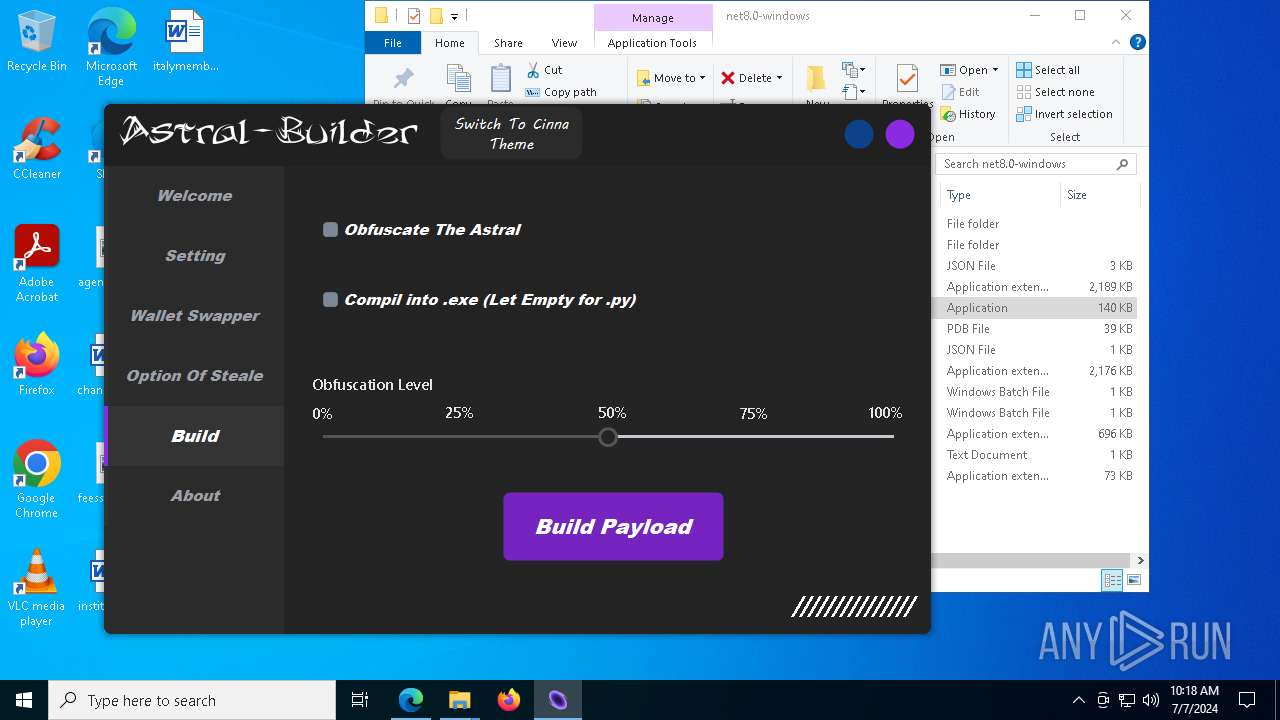
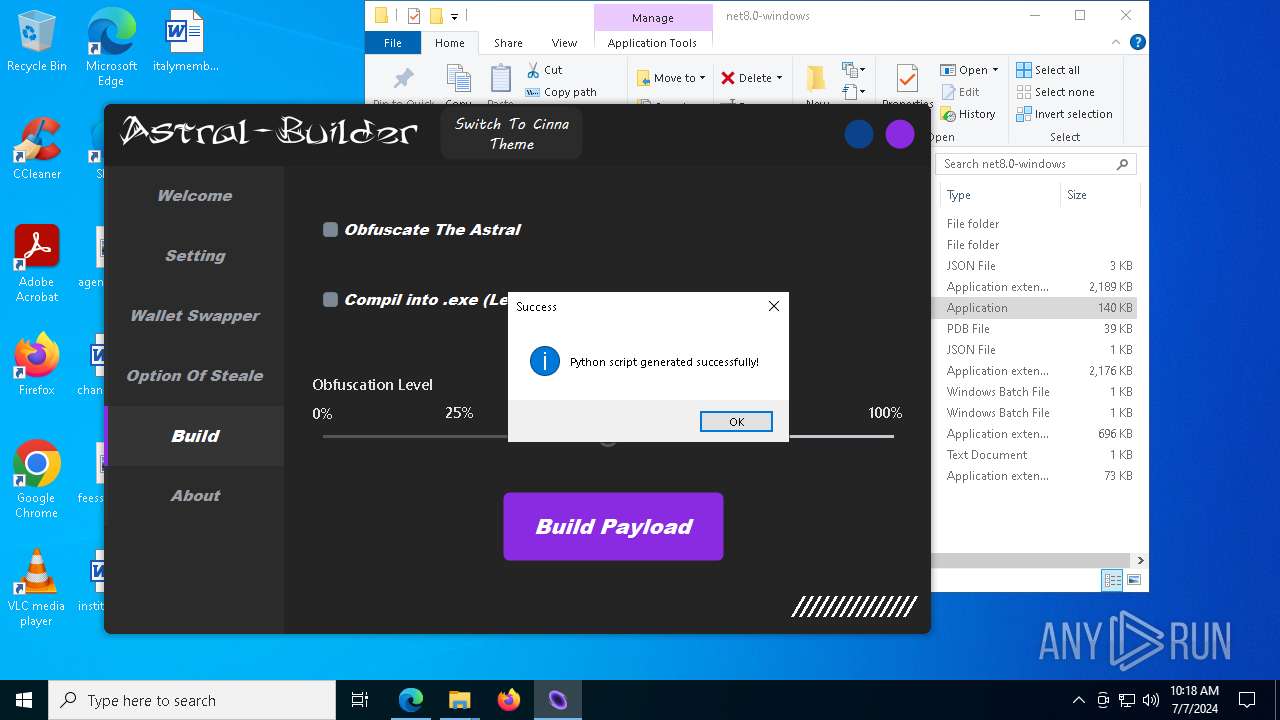
| Verdict: | Malicious activity |
| Analysis date: | July 07, 2024, 10:15:12 |
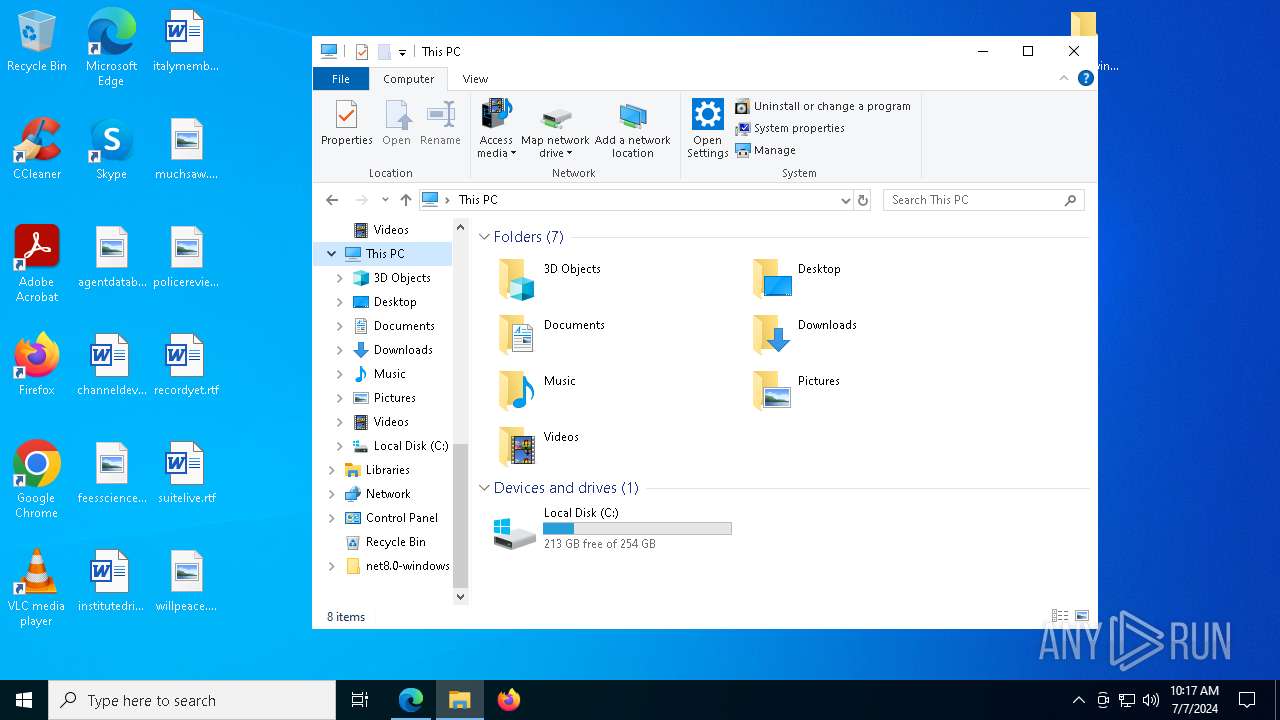
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
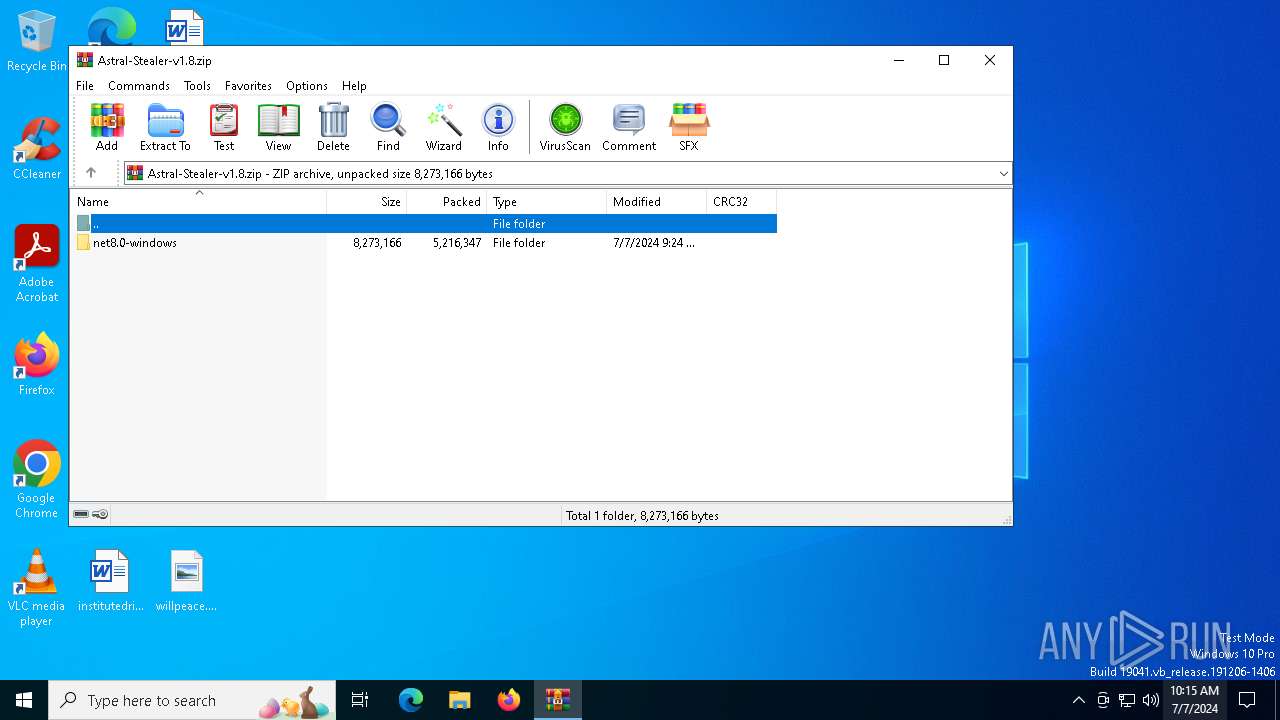
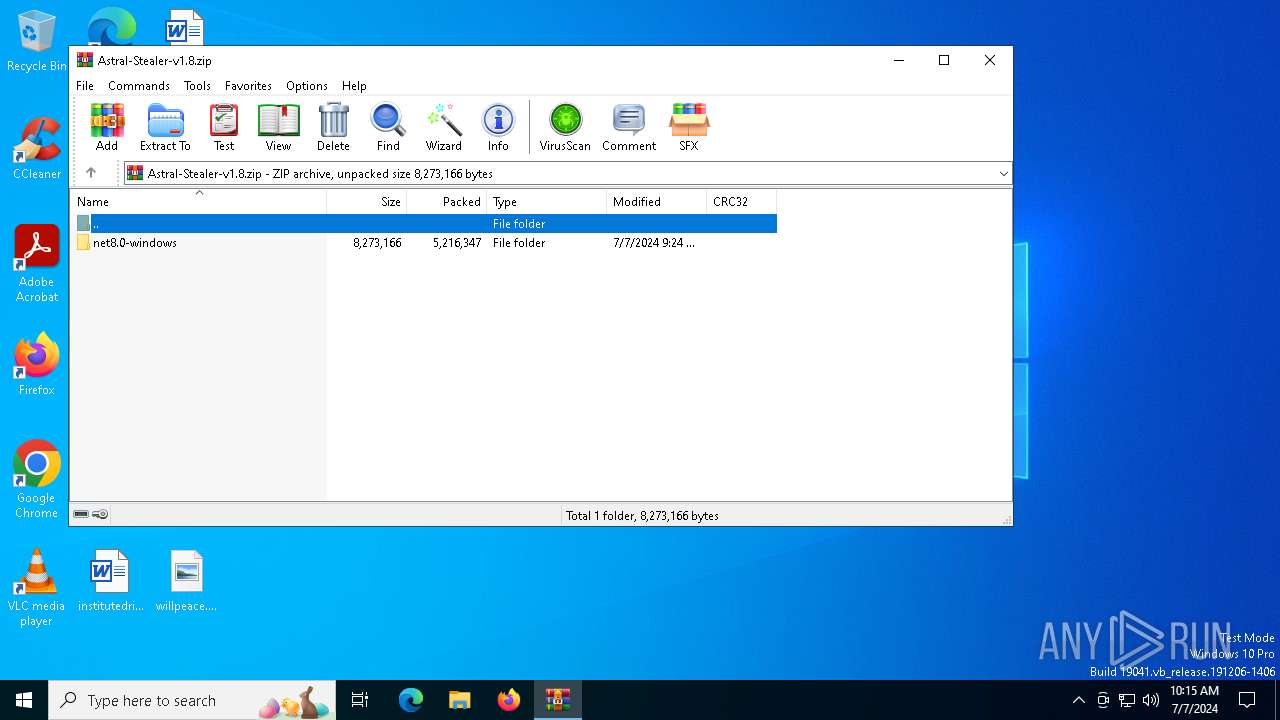
| MIME: | application/zip |
| File info: | Zip archive data, at least v1.0 to extract, compression method=store |
| MD5: | 99F1133043B27927628725CDEDAB82FC |
| SHA1: | 5C5EFF02B8CD8468638712CEF2F58DF38B678C8A |
| SHA256: | CF0B47EAFA7787A698BC8DBB62D18F1D16D0659FF7BD7E6312CCB50B08B754B6 |
| SSDEEP: | 98304:ExCjme2DRUaG8wayB15a0TpKa8LXxaaWPslabbda5VBbaAHqmjuD/PV+7L1CDs92:QpsENA |
MALICIOUS
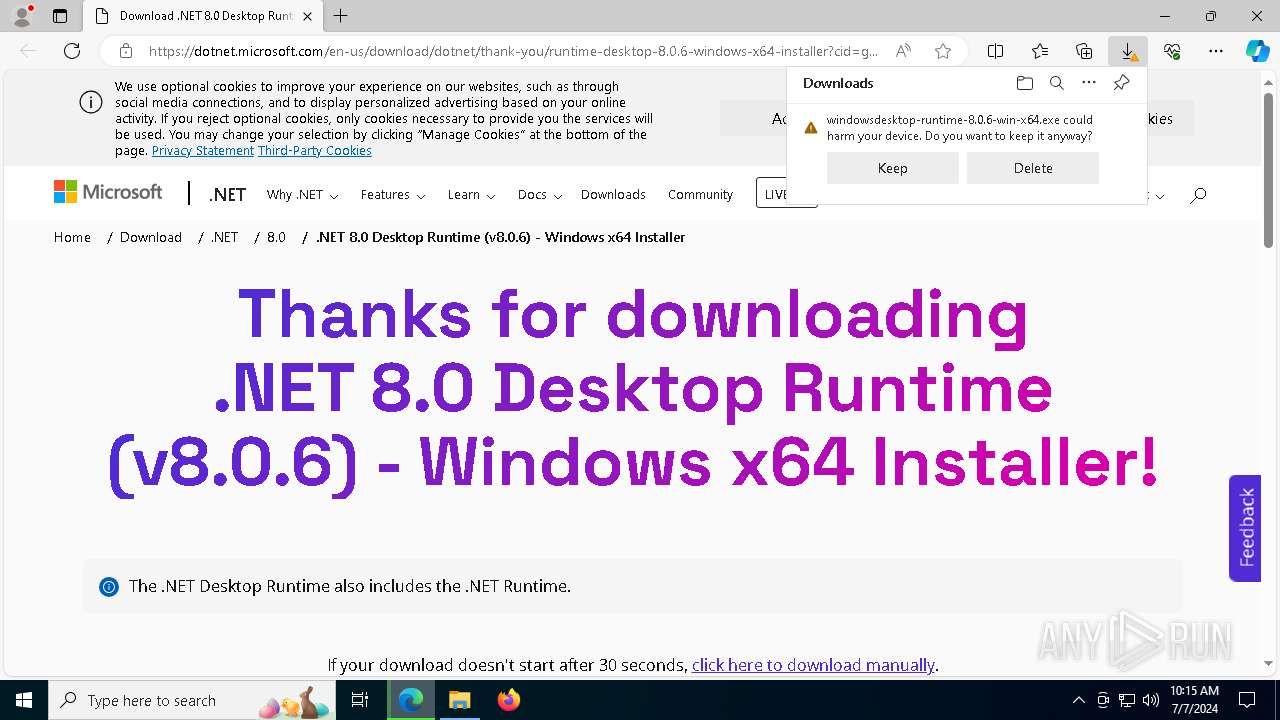
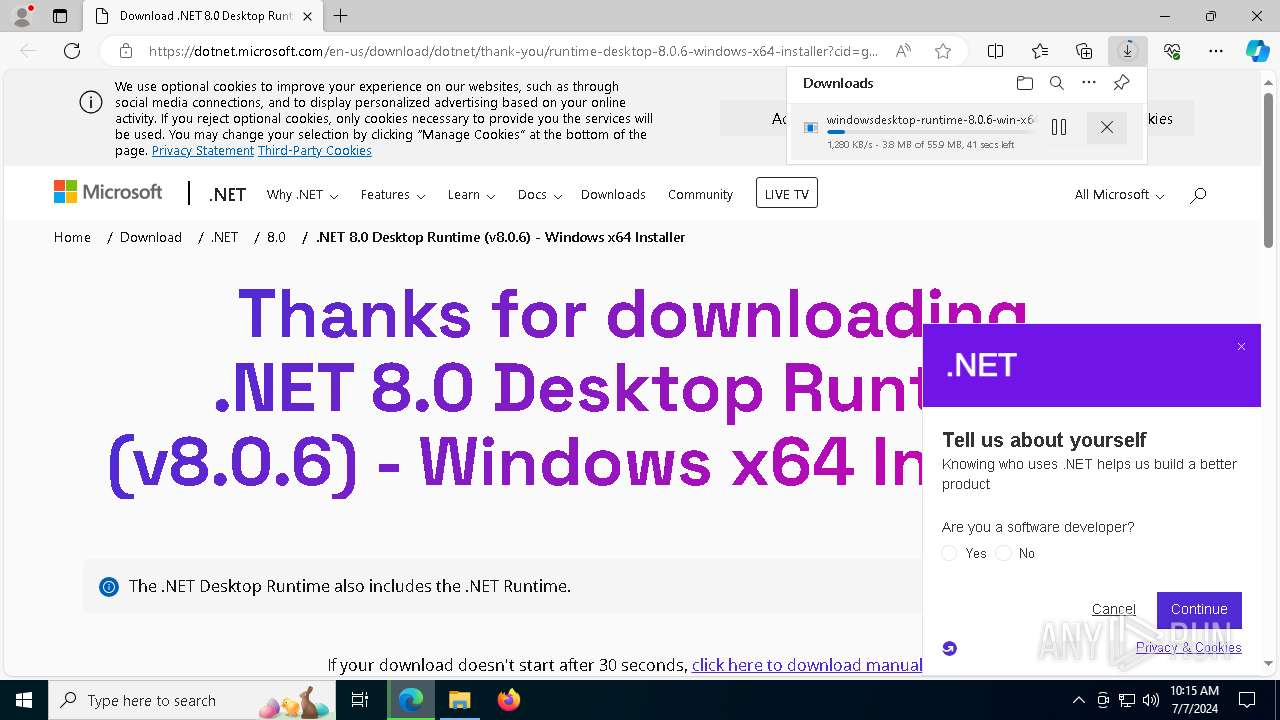
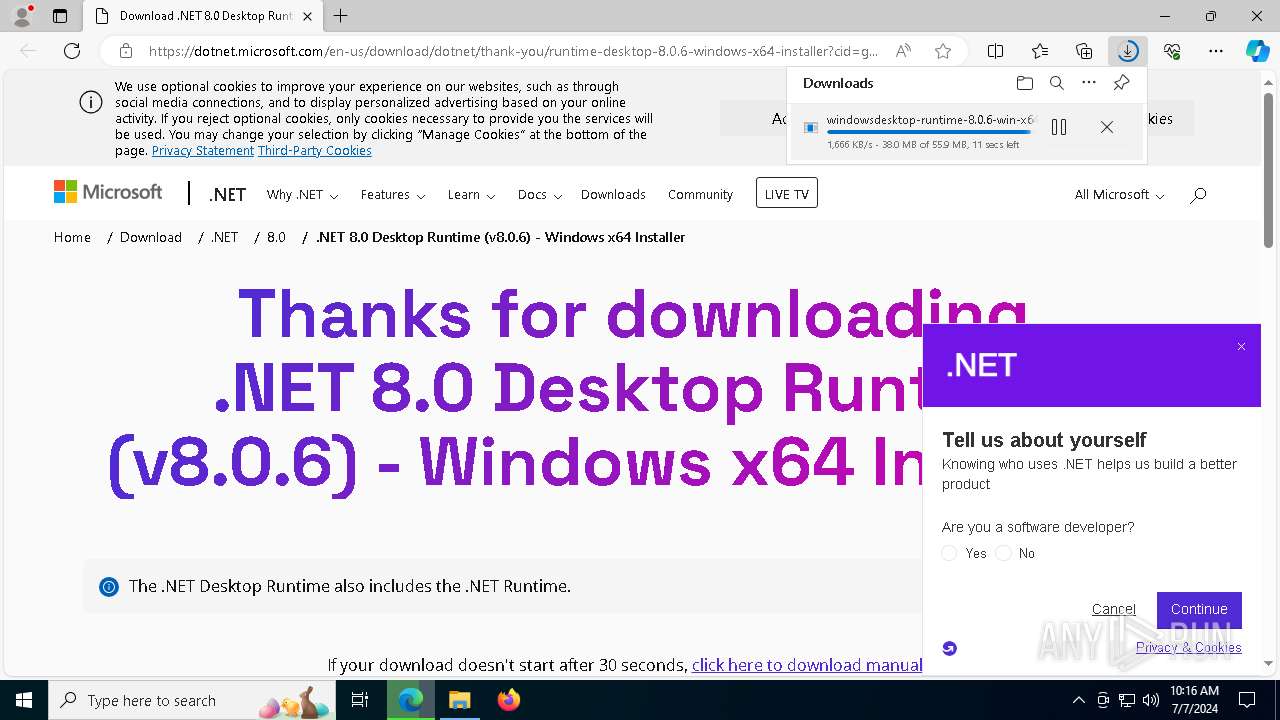
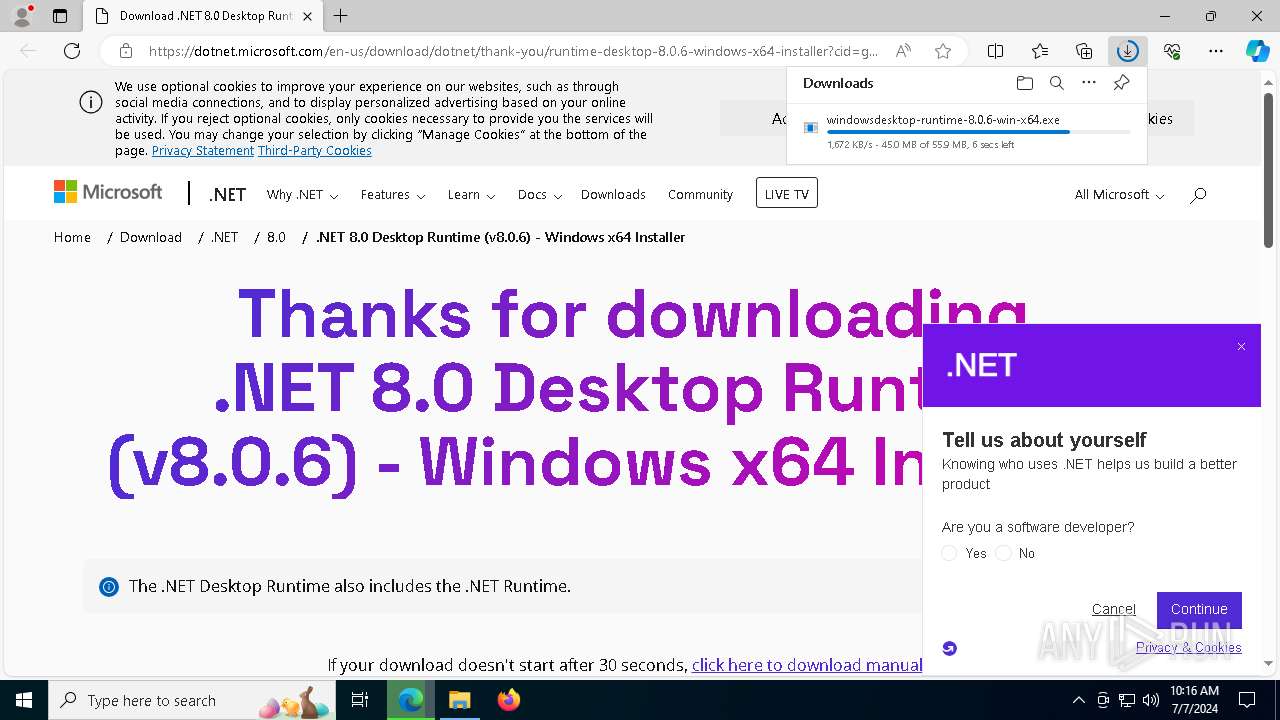
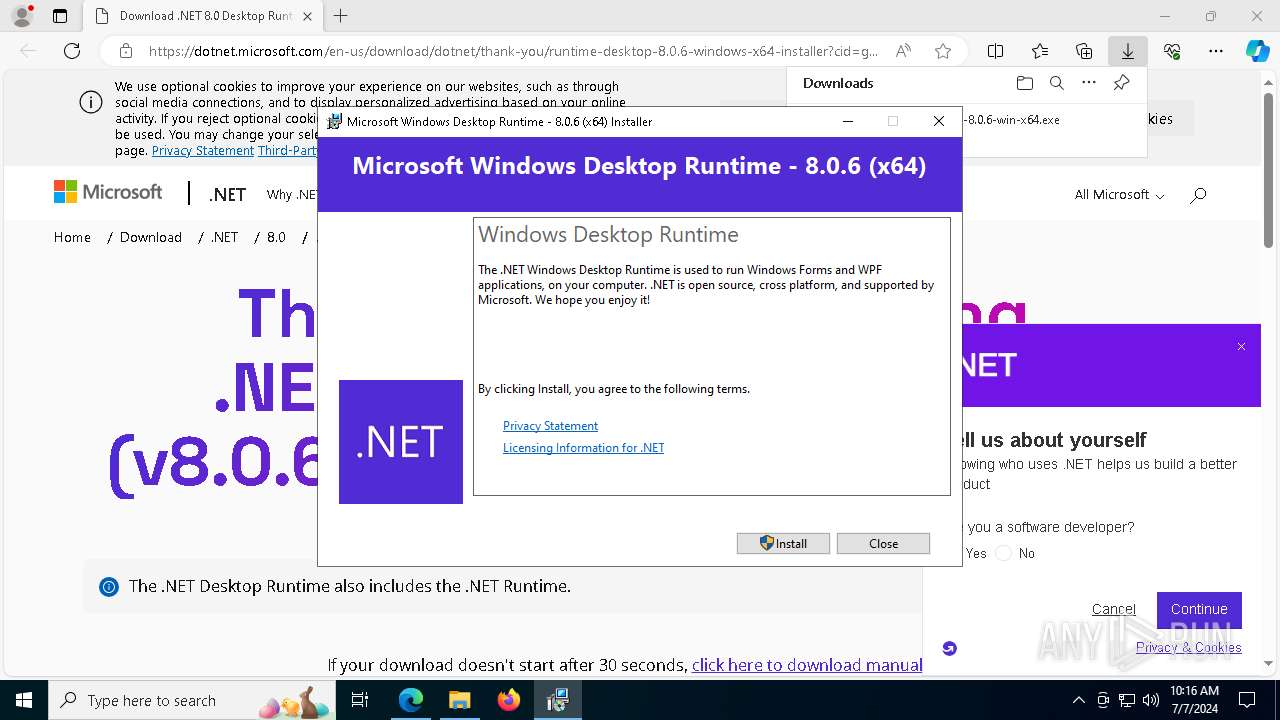
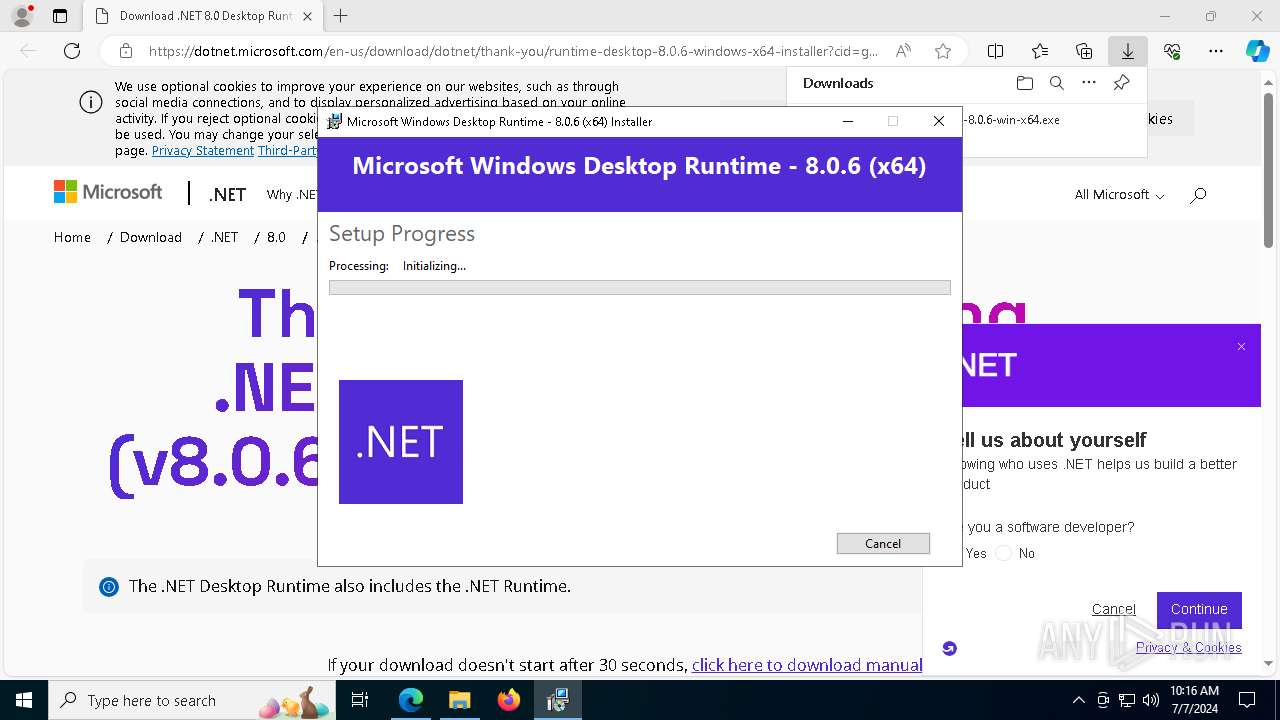
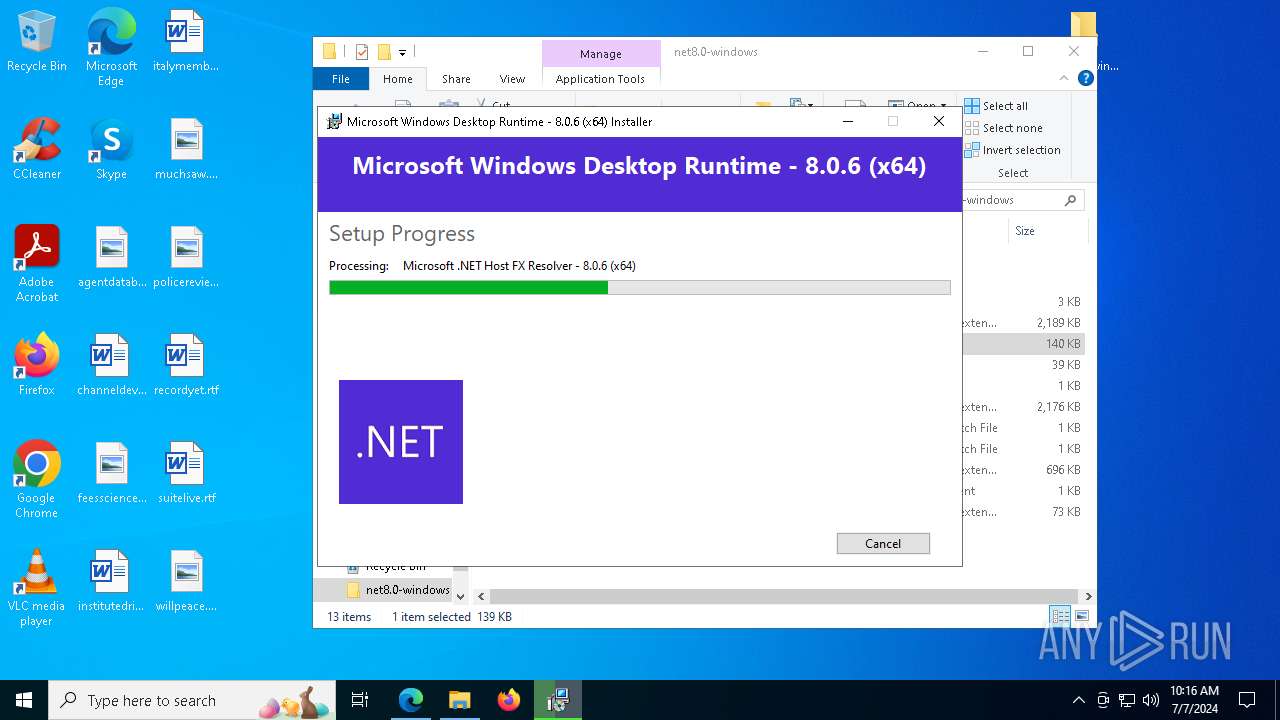
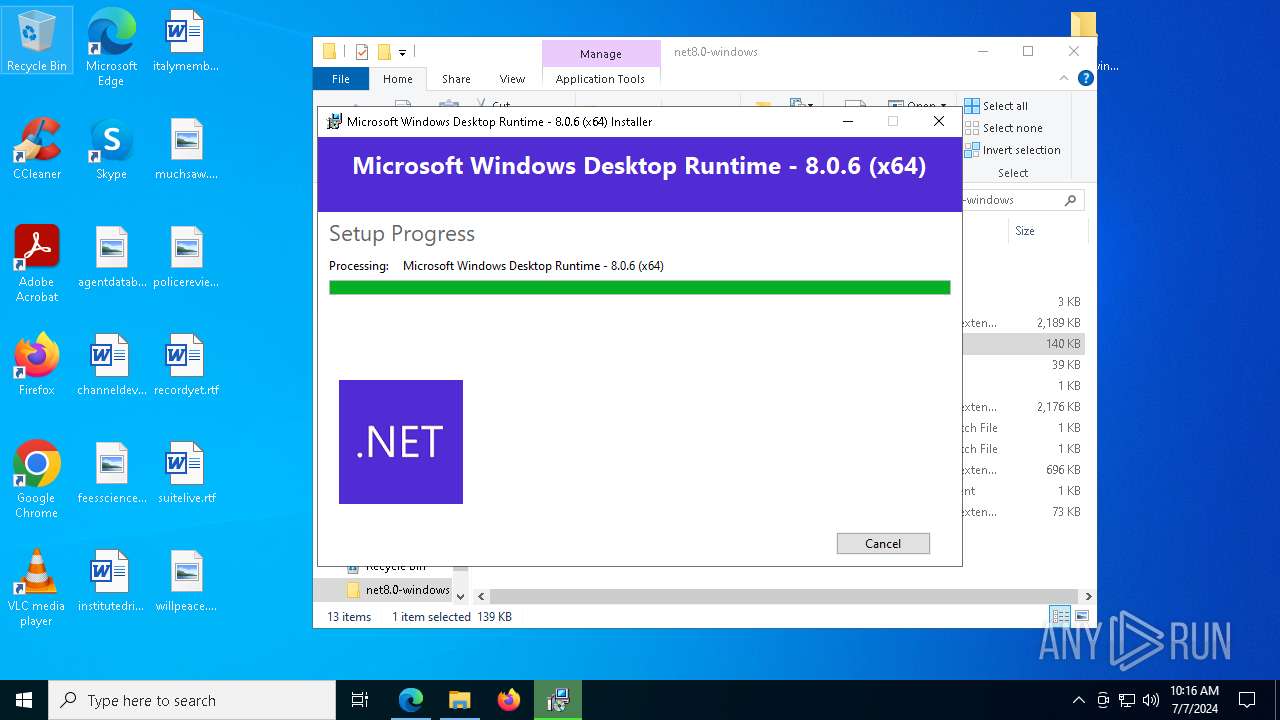
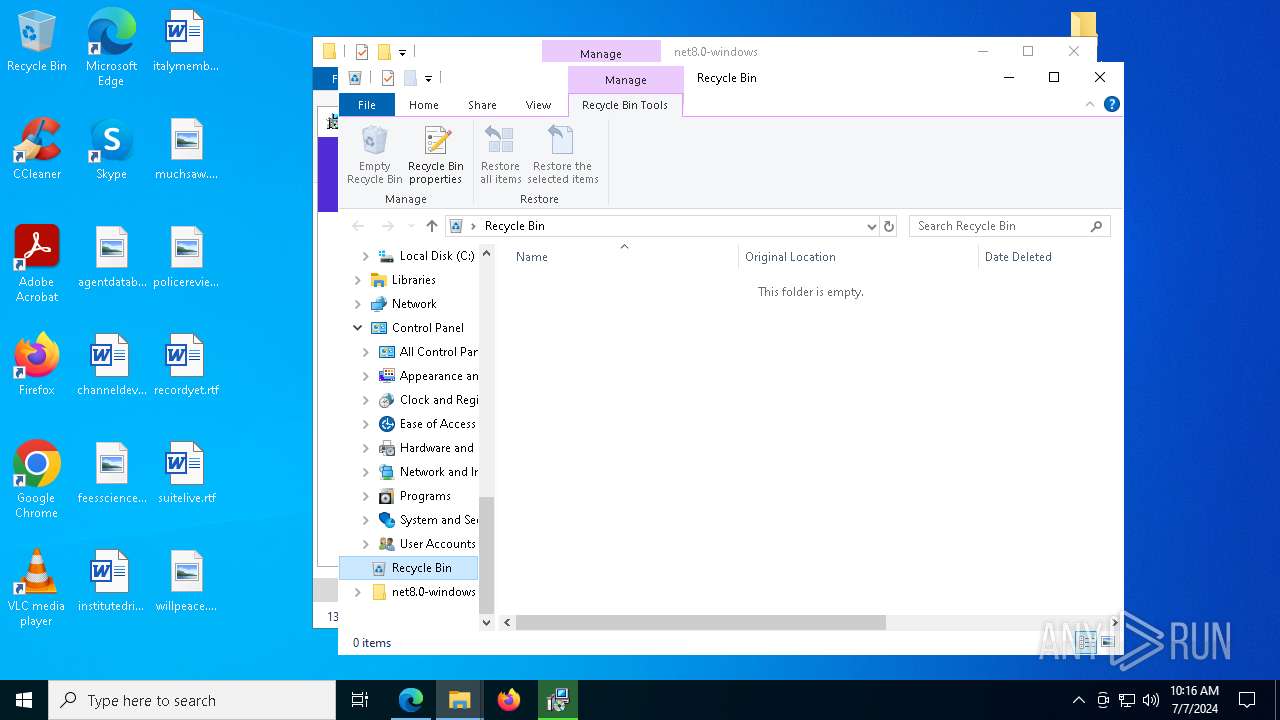
Drops the executable file immediately after the start
- WinRAR.exe (PID: 5872)
- windowsdesktop-runtime-8.0.6-win-x64.exe (PID: 8032)
- windowsdesktop-runtime-8.0.6-win-x64.exe (PID: 7888)
- windowsdesktop-runtime-8.0.6-win-x64.exe (PID: 8108)
- msiexec.exe (PID: 7680)
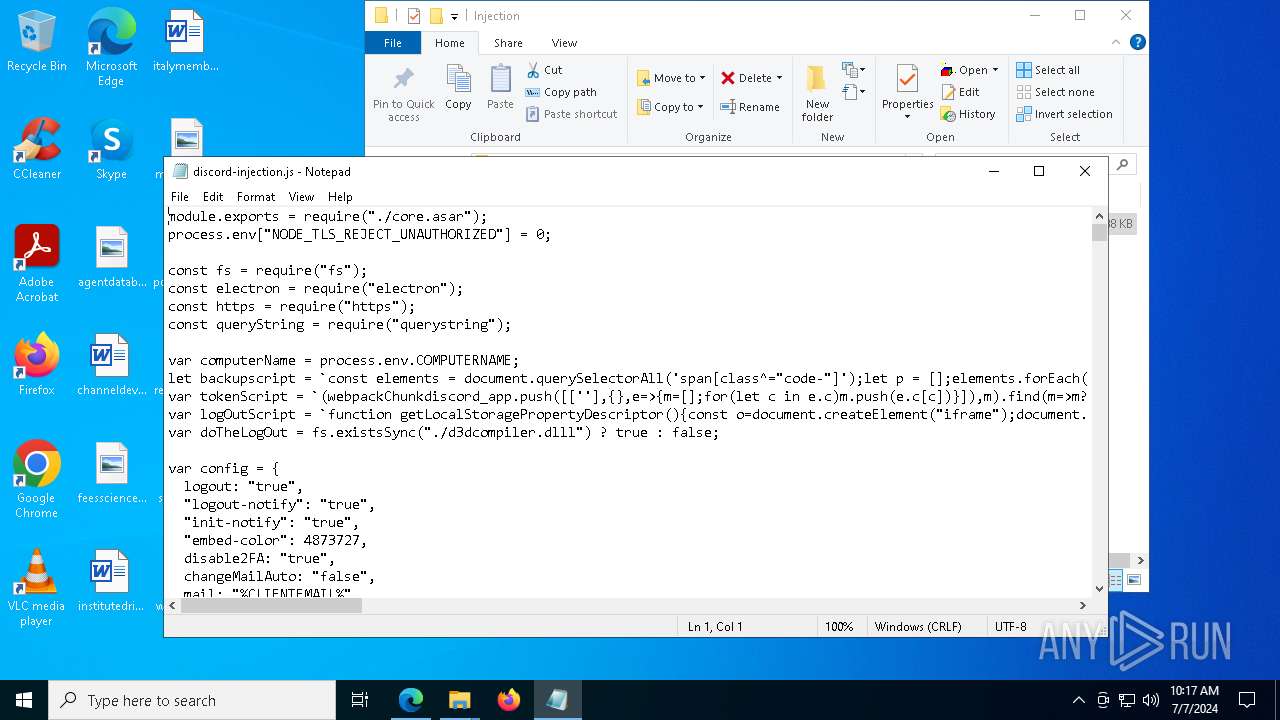
Actions looks like stealing of personal data
- WinRAR.exe (PID: 5872)
- notepad.exe (PID: 6388)
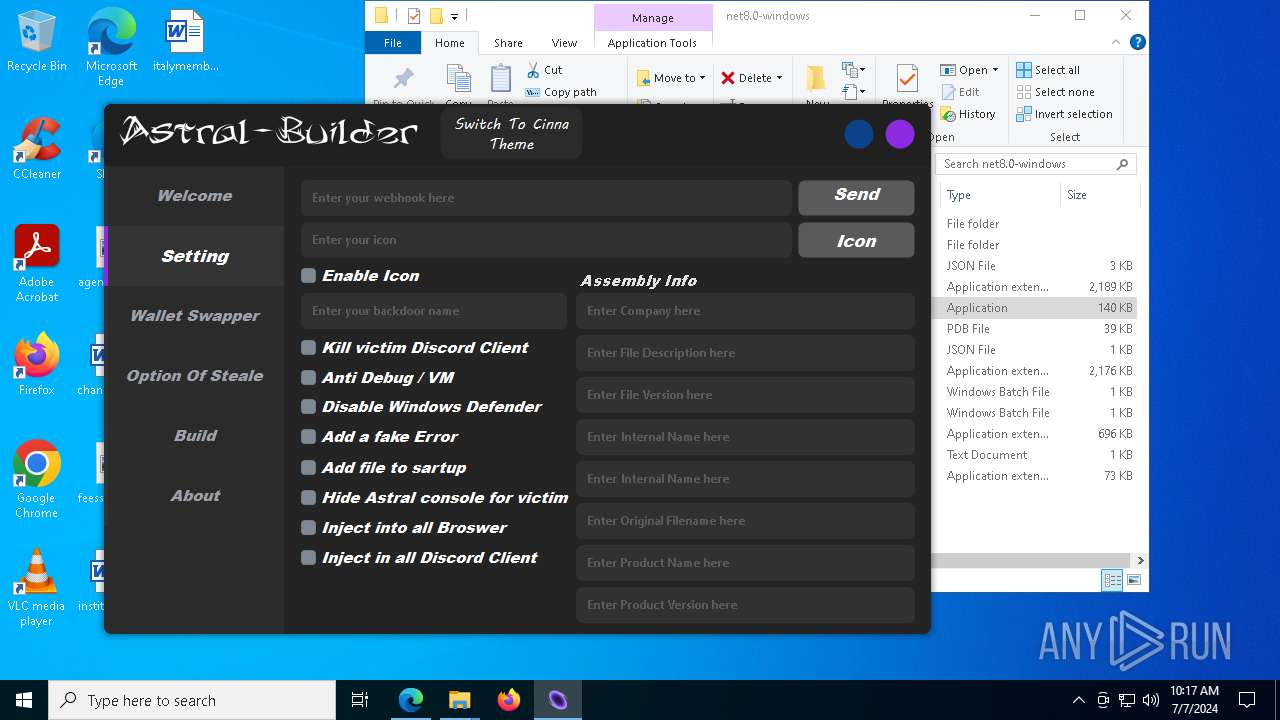
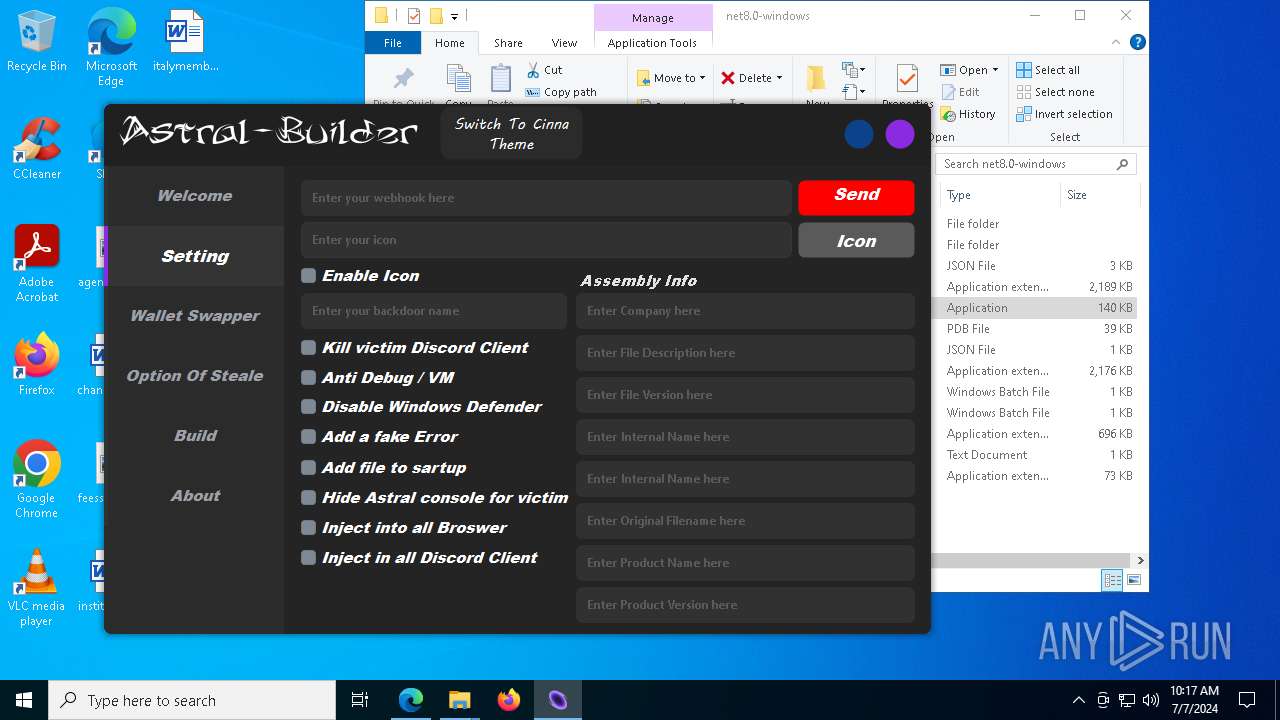
Changes the autorun value in the registry
- windowsdesktop-runtime-8.0.6-win-x64.exe (PID: 8108)
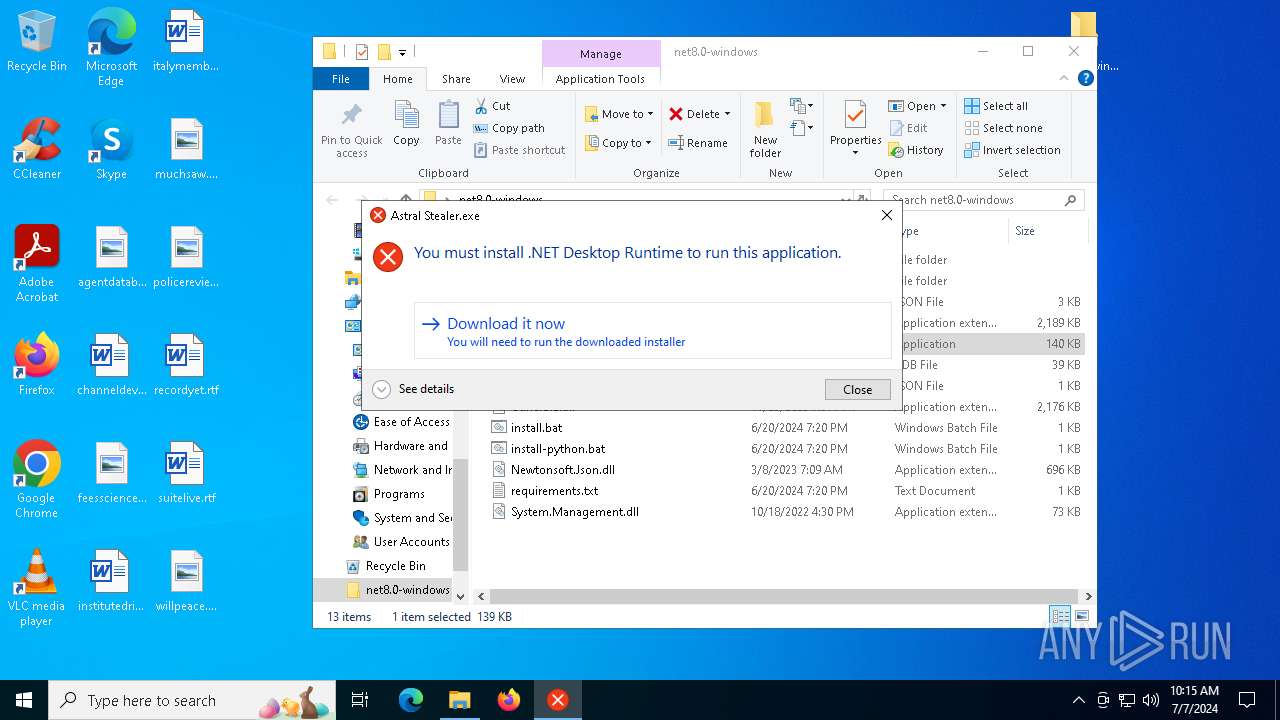
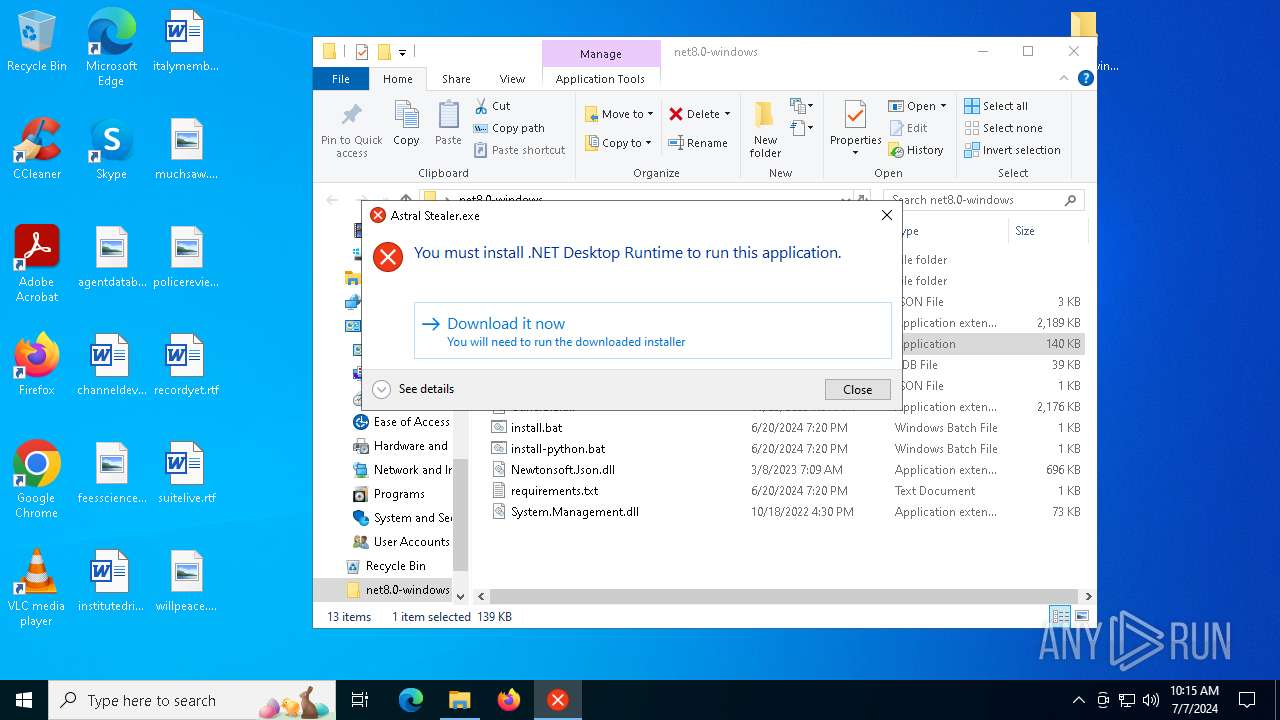
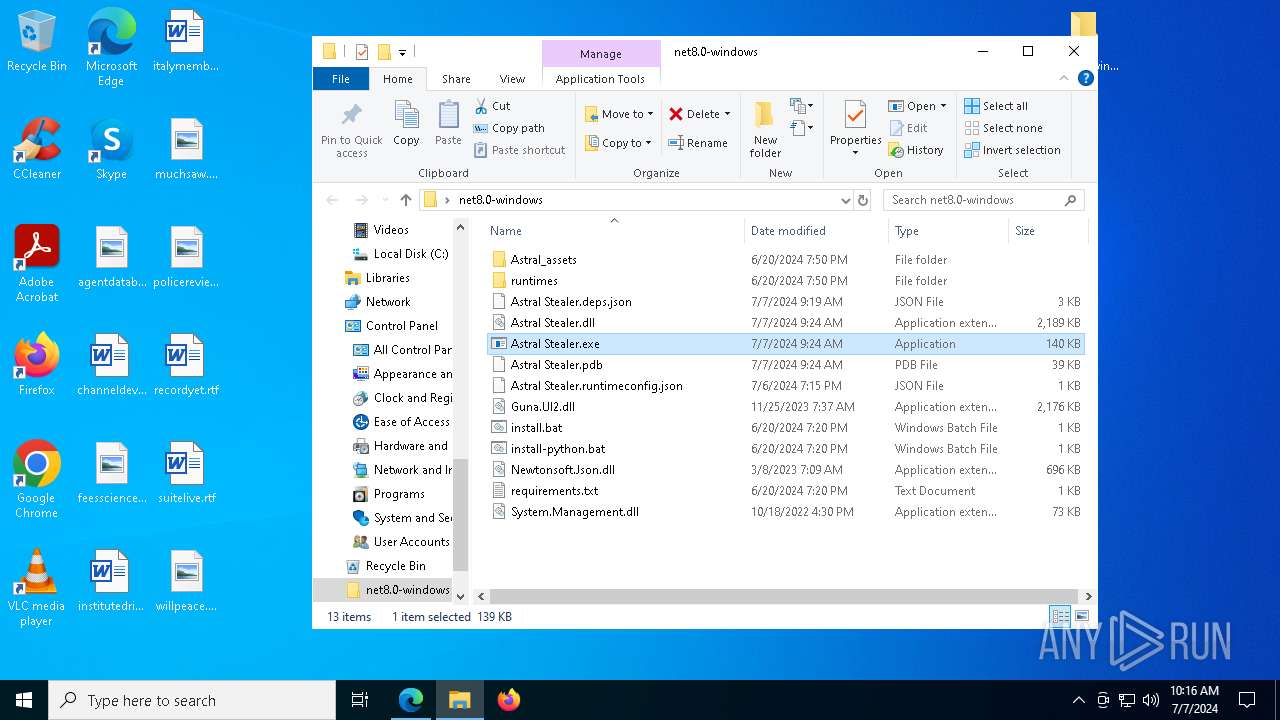
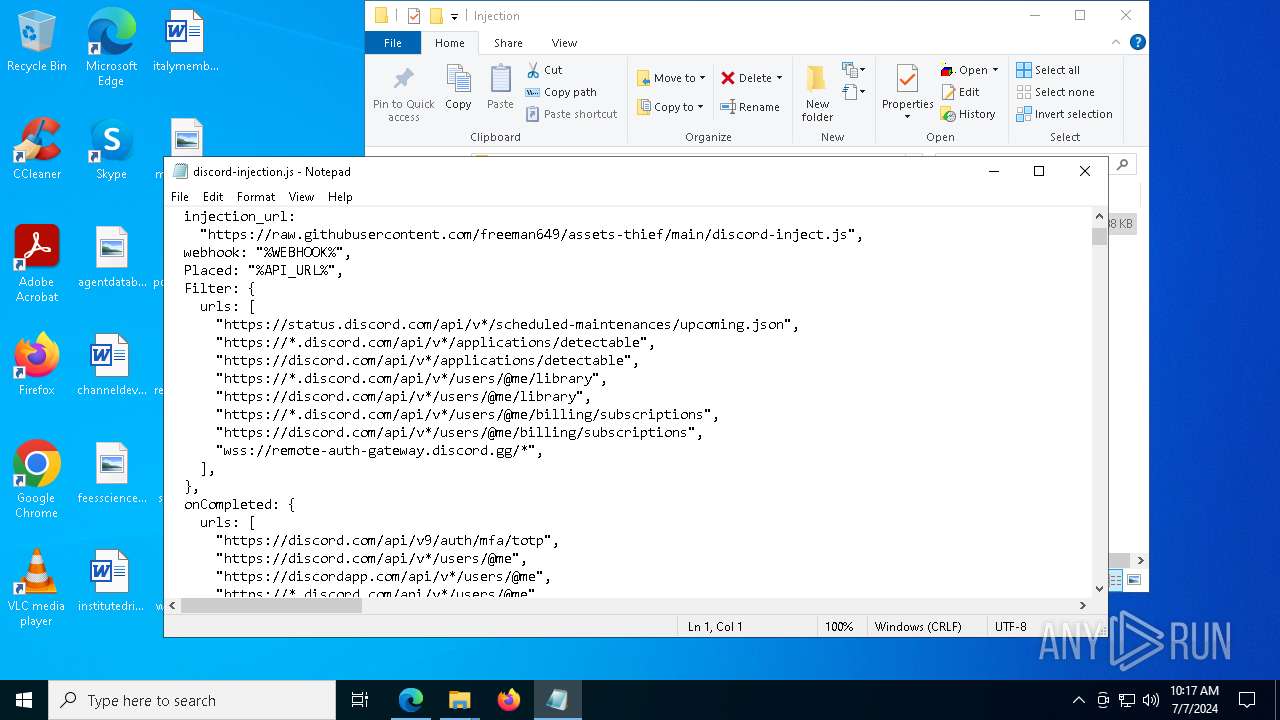
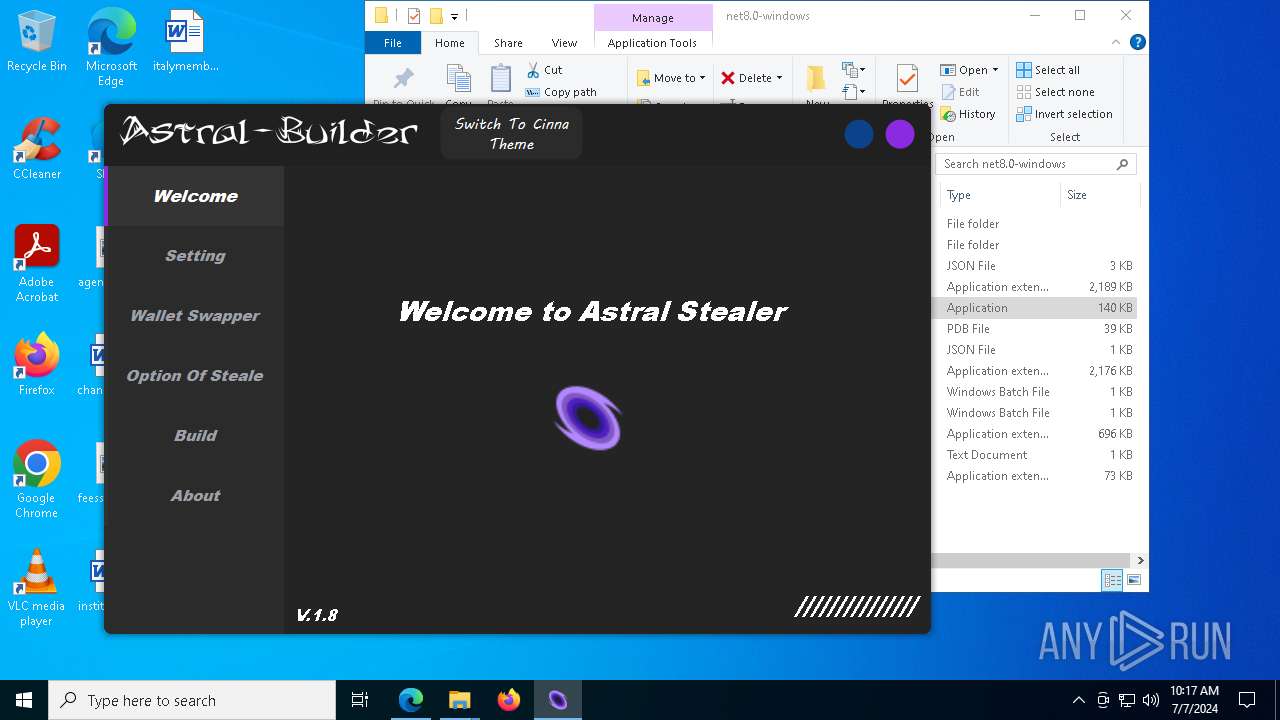
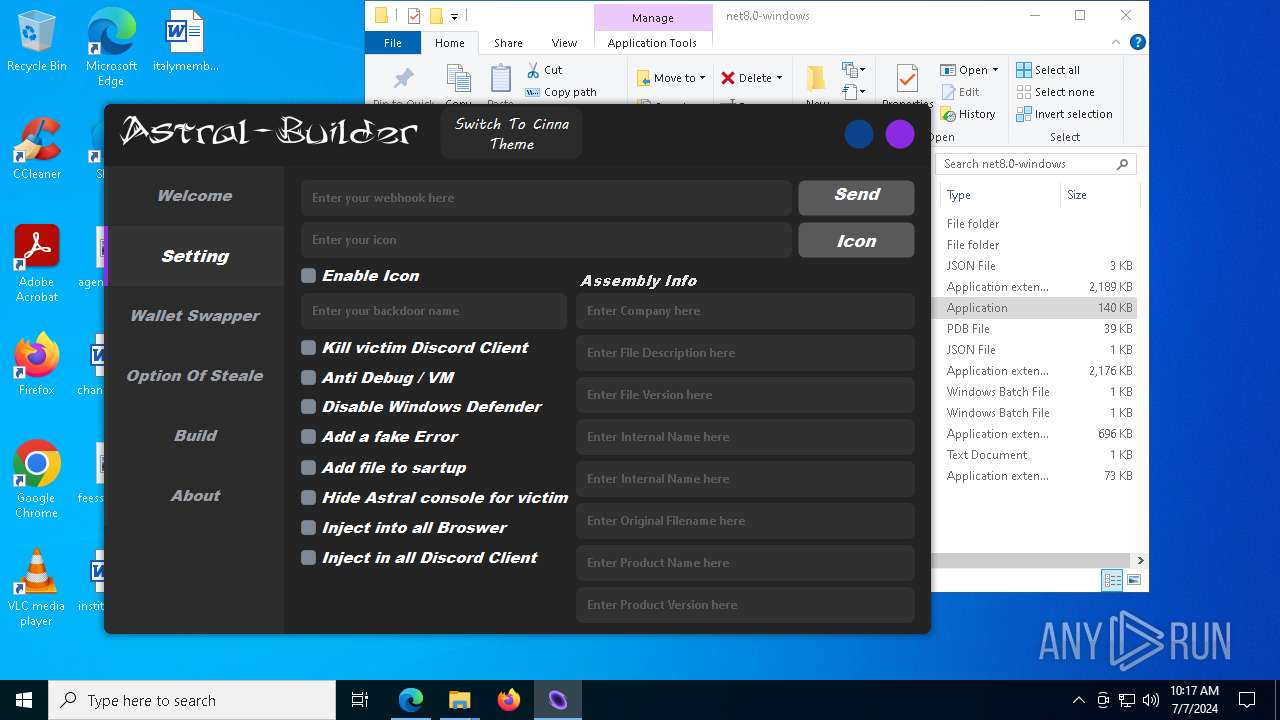
UMBRALSTEALER has been detected (YARA)
- Astral Stealer.exe (PID: 7228)
SUSPICIOUS
Process drops legitimate windows executable
- WinRAR.exe (PID: 5872)
- windowsdesktop-runtime-8.0.6-win-x64.exe (PID: 8032)
- windowsdesktop-runtime-8.0.6-win-x64.exe (PID: 7888)
- windowsdesktop-runtime-8.0.6-win-x64.exe (PID: 8108)
- msiexec.exe (PID: 7680)
Reads security settings of Internet Explorer
- Astral Stealer.exe (PID: 5112)
- windowsdesktop-runtime-8.0.6-win-x64.exe (PID: 7888)
Starts a Microsoft application from unusual location
- windowsdesktop-runtime-8.0.6-win-x64.exe (PID: 7888)
- windowsdesktop-runtime-8.0.6-win-x64.exe (PID: 8108)
Executable content was dropped or overwritten
- windowsdesktop-runtime-8.0.6-win-x64.exe (PID: 7888)
- windowsdesktop-runtime-8.0.6-win-x64.exe (PID: 8032)
- windowsdesktop-runtime-8.0.6-win-x64.exe (PID: 8108)
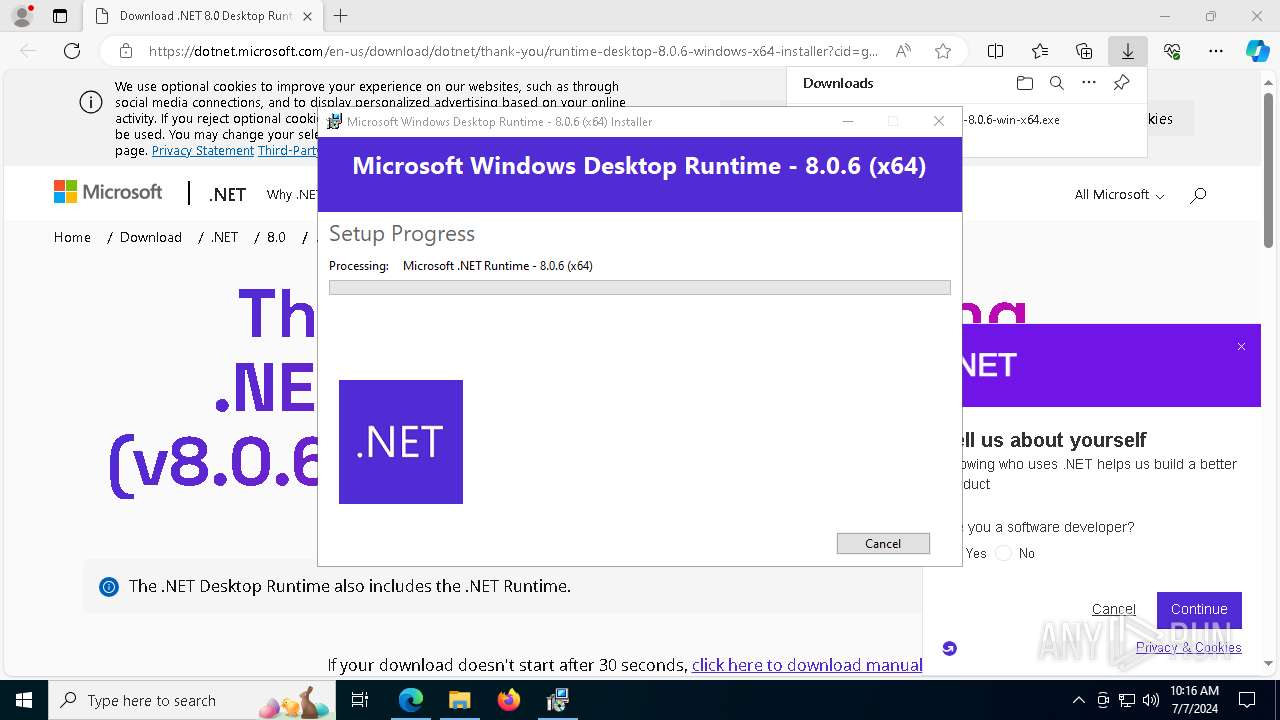
Searches for installed software
- windowsdesktop-runtime-8.0.6-win-x64.exe (PID: 7888)
- windowsdesktop-runtime-8.0.6-win-x64.exe (PID: 8108)
Reads the date of Windows installation
- windowsdesktop-runtime-8.0.6-win-x64.exe (PID: 7888)
Starts itself from another location
- windowsdesktop-runtime-8.0.6-win-x64.exe (PID: 7888)
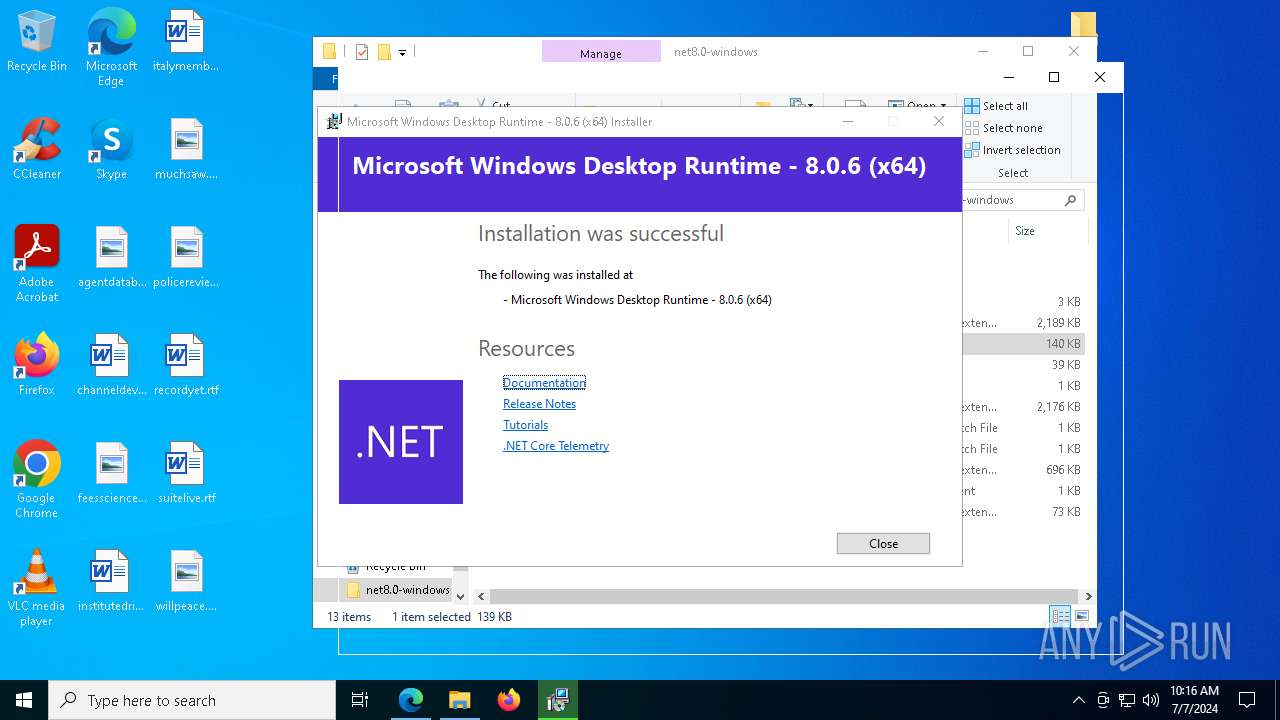
Creates a software uninstall entry
- windowsdesktop-runtime-8.0.6-win-x64.exe (PID: 8108)
Reads the Windows owner or organization settings
- msiexec.exe (PID: 7680)
Checks Windows Trust Settings
- msiexec.exe (PID: 7680)
The process creates files with name similar to system file names
- msiexec.exe (PID: 7680)
The process drops C-runtime libraries
- msiexec.exe (PID: 7680)
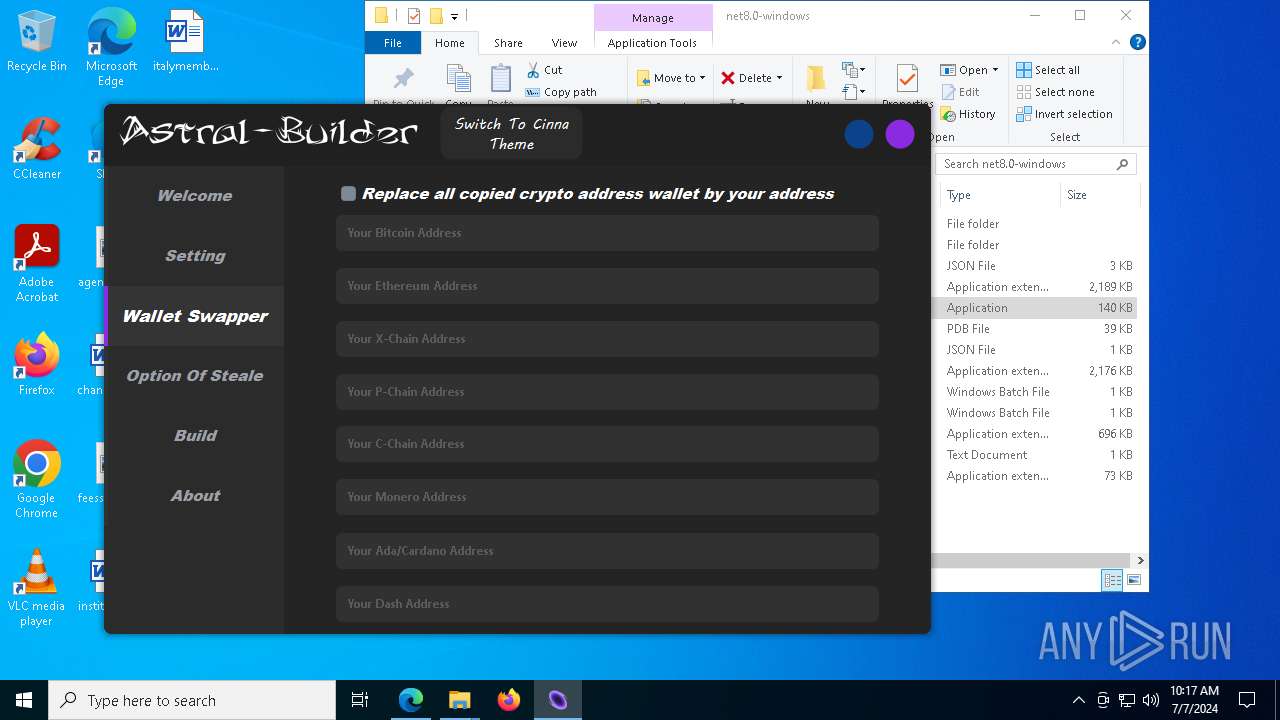
Found regular expressions for crypto-addresses (YARA)
- Astral Stealer.exe (PID: 7228)
There is functionality for taking screenshot (YARA)
- Astral Stealer.exe (PID: 7228)
INFO
Checks supported languages
- Astral Stealer.exe (PID: 5112)
- identity_helper.exe (PID: 7636)
- windowsdesktop-runtime-8.0.6-win-x64.exe (PID: 8032)
- windowsdesktop-runtime-8.0.6-win-x64.exe (PID: 7888)
- windowsdesktop-runtime-8.0.6-win-x64.exe (PID: 8108)
- msiexec.exe (PID: 7680)
- msiexec.exe (PID: 3932)
- msiexec.exe (PID: 4756)
- Astral Stealer.exe (PID: 7228)
- msiexec.exe (PID: 6792)
- msiexec.exe (PID: 7236)
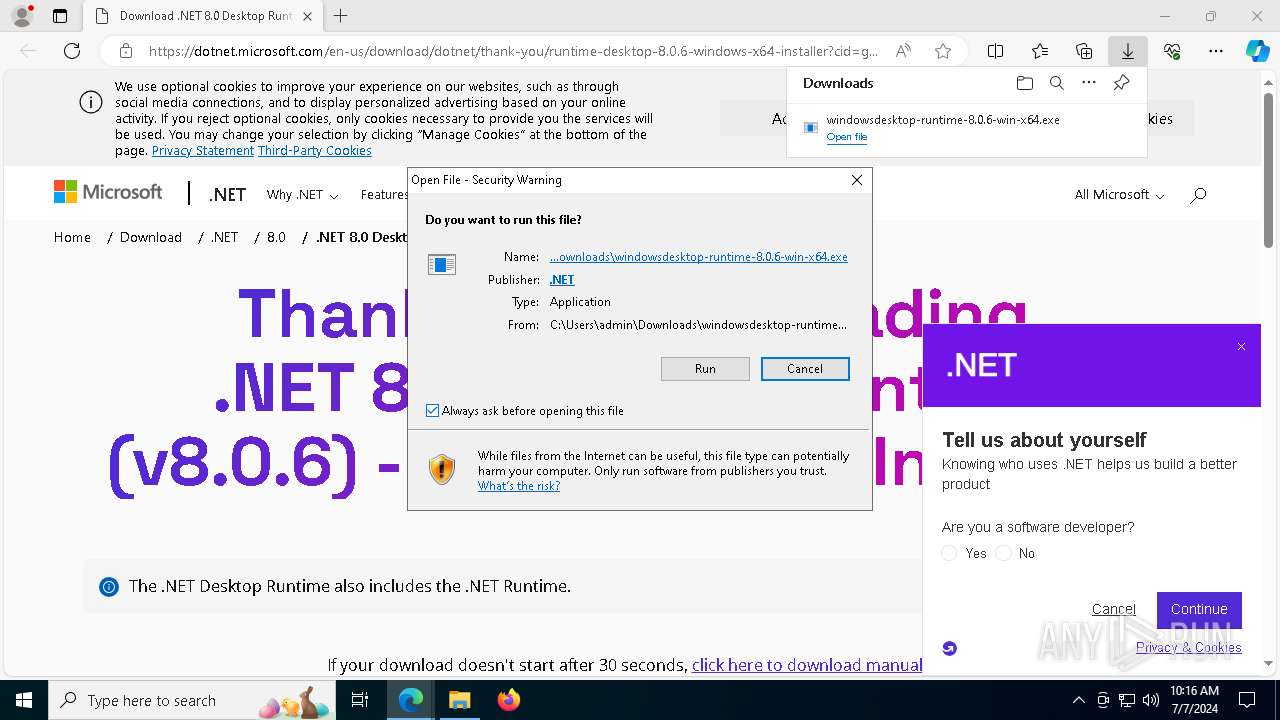
Manual execution by a user
- Astral Stealer.exe (PID: 5112)
- notepad.exe (PID: 6388)
- Astral Stealer.exe (PID: 7228)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 5872)
- msedge.exe (PID: 6320)
- msiexec.exe (PID: 7680)
Reads the computer name
- Astral Stealer.exe (PID: 5112)
- identity_helper.exe (PID: 7636)
- windowsdesktop-runtime-8.0.6-win-x64.exe (PID: 7888)
- windowsdesktop-runtime-8.0.6-win-x64.exe (PID: 8108)
- msiexec.exe (PID: 7680)
- msiexec.exe (PID: 3932)
- msiexec.exe (PID: 6792)
- msiexec.exe (PID: 7236)
- msiexec.exe (PID: 4756)
- Astral Stealer.exe (PID: 7228)
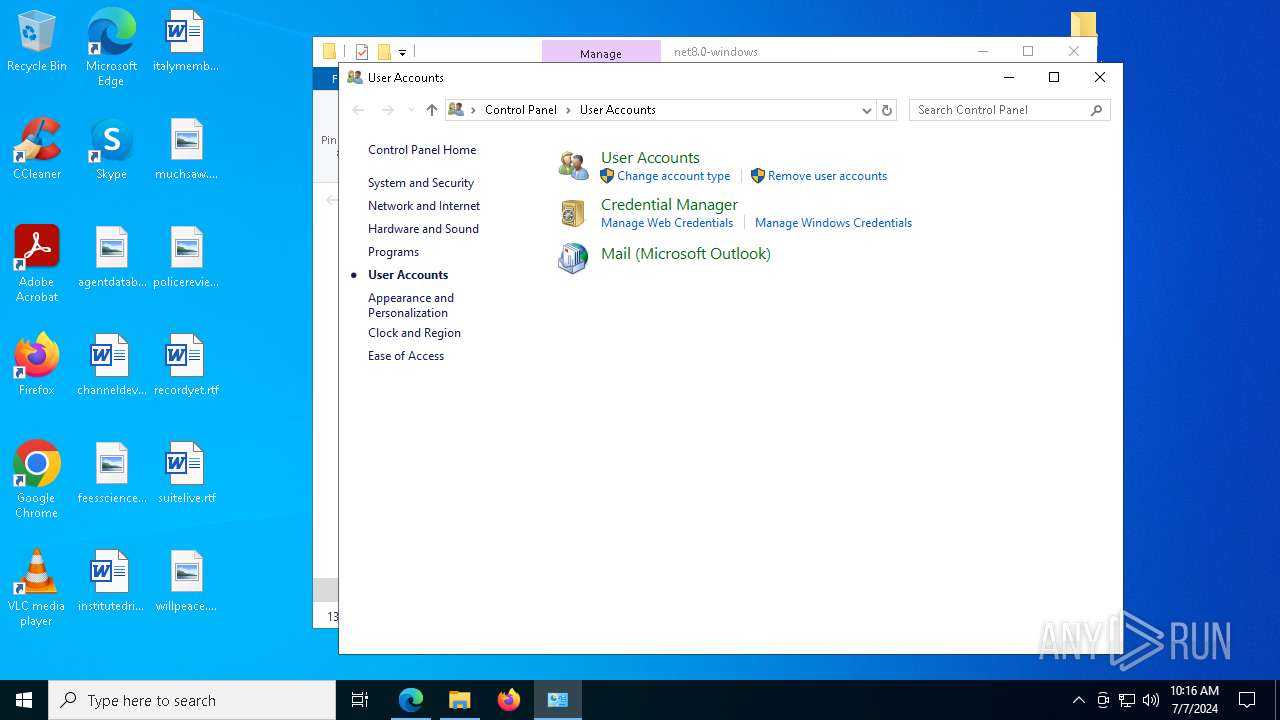
Reads Microsoft Office registry keys
- Astral Stealer.exe (PID: 5112)
- msedge.exe (PID: 6320)
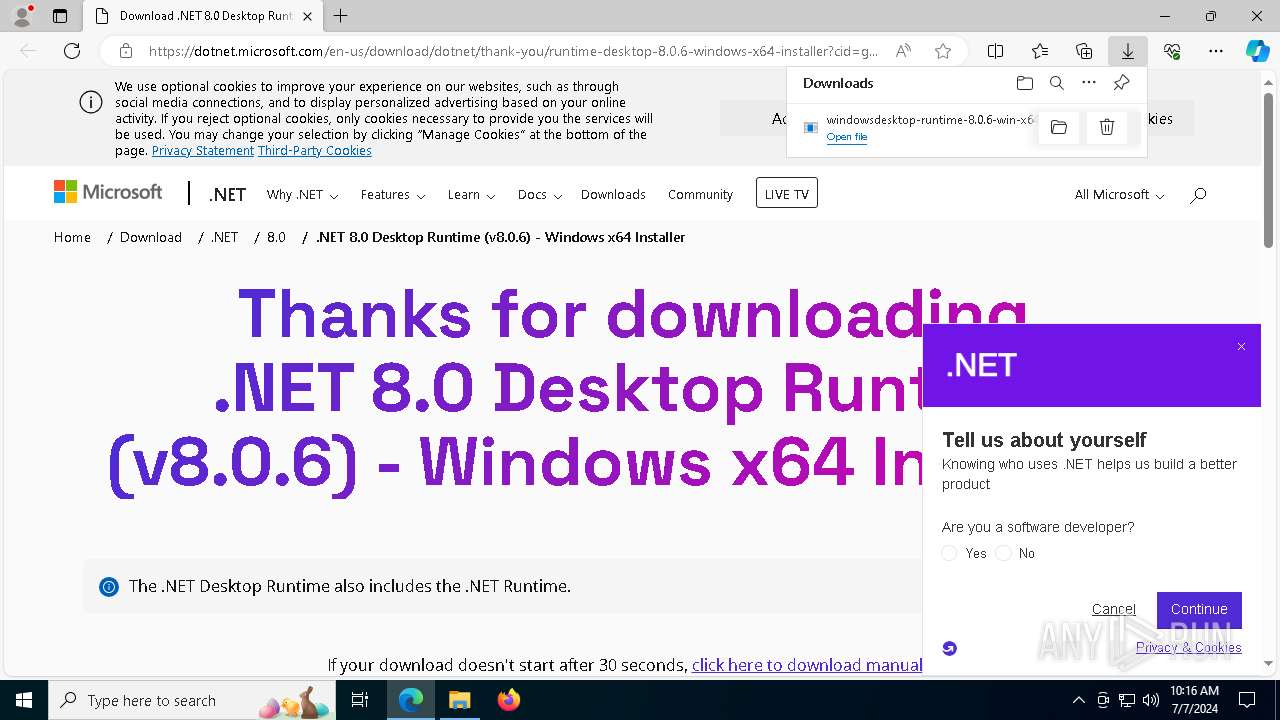
Drops the executable file immediately after the start
- msedge.exe (PID: 6320)
- msedge.exe (PID: 7712)
Application launched itself
- msedge.exe (PID: 6320)
The process uses the downloaded file
- msedge.exe (PID: 7956)
- msedge.exe (PID: 6320)
Create files in a temporary directory
- windowsdesktop-runtime-8.0.6-win-x64.exe (PID: 8032)
- windowsdesktop-runtime-8.0.6-win-x64.exe (PID: 7888)
- windowsdesktop-runtime-8.0.6-win-x64.exe (PID: 8108)
Process checks computer location settings
- windowsdesktop-runtime-8.0.6-win-x64.exe (PID: 7888)
- Astral Stealer.exe (PID: 7228)
Creates files in the program directory
- windowsdesktop-runtime-8.0.6-win-x64.exe (PID: 8108)
- Astral Stealer.exe (PID: 7228)
Reads the machine GUID from the registry
- windowsdesktop-runtime-8.0.6-win-x64.exe (PID: 8108)
- msiexec.exe (PID: 7680)
Reads the software policy settings
- msiexec.exe (PID: 7680)
Reads security settings of Internet Explorer
- notepad.exe (PID: 6388)
Creates a software uninstall entry
- msiexec.exe (PID: 7680)
Found Base64 encoded access to Windows Defender via PowerShell (YARA)
- Astral Stealer.exe (PID: 7228)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .xpi | | | Mozilla Firefox browser extension (66.6) |
|---|---|---|
| .zip | | | ZIP compressed archive (33.3) |
EXIF
ZIP
| ZipRequiredVersion: | 10 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2024:07:07 11:24:16 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
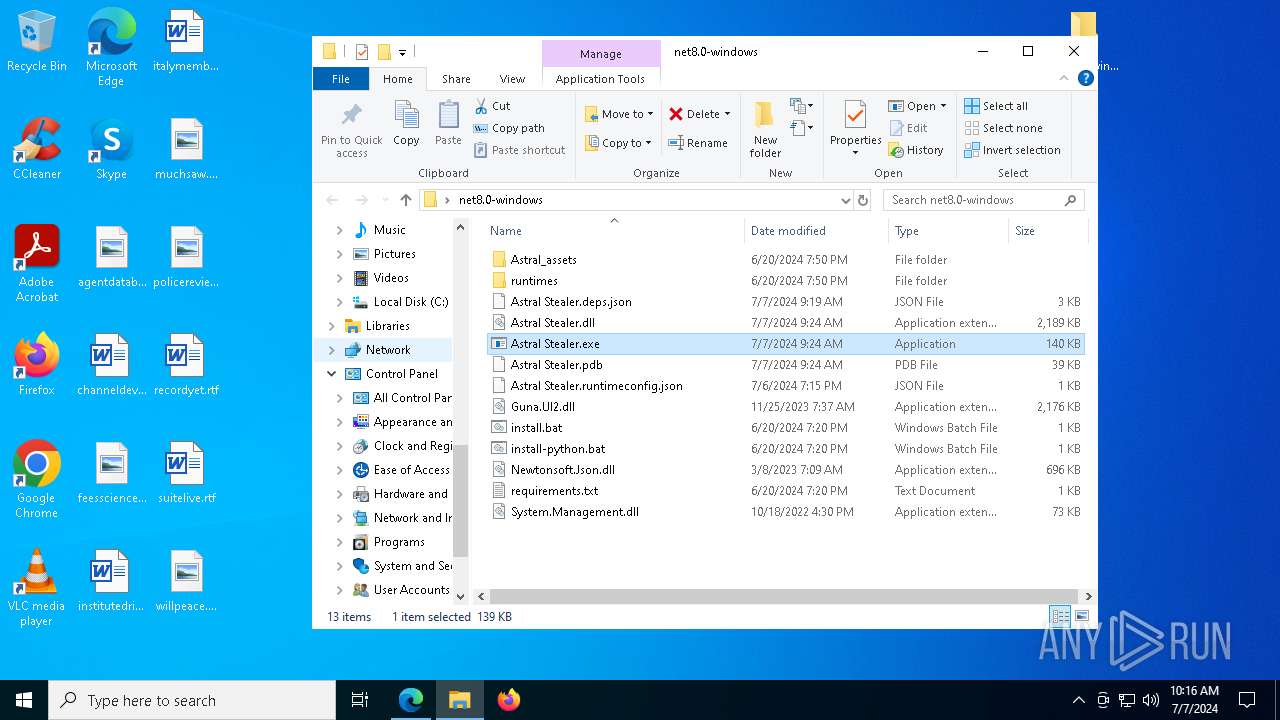
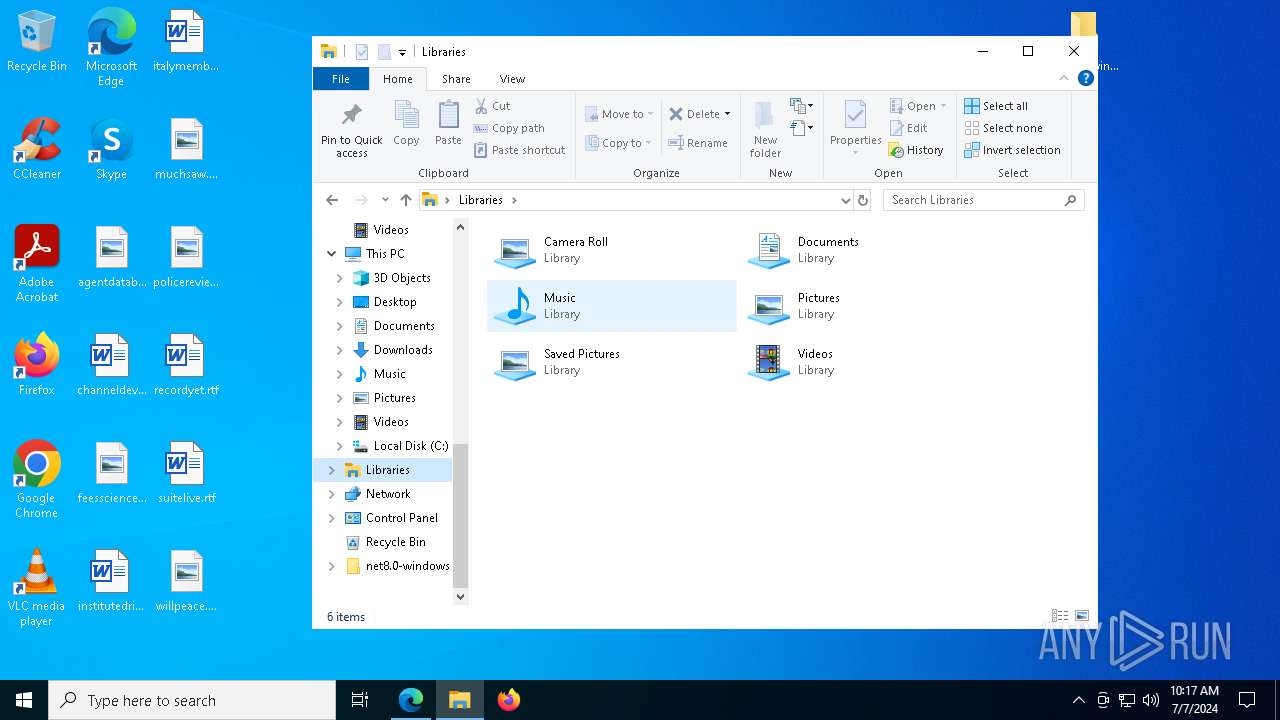
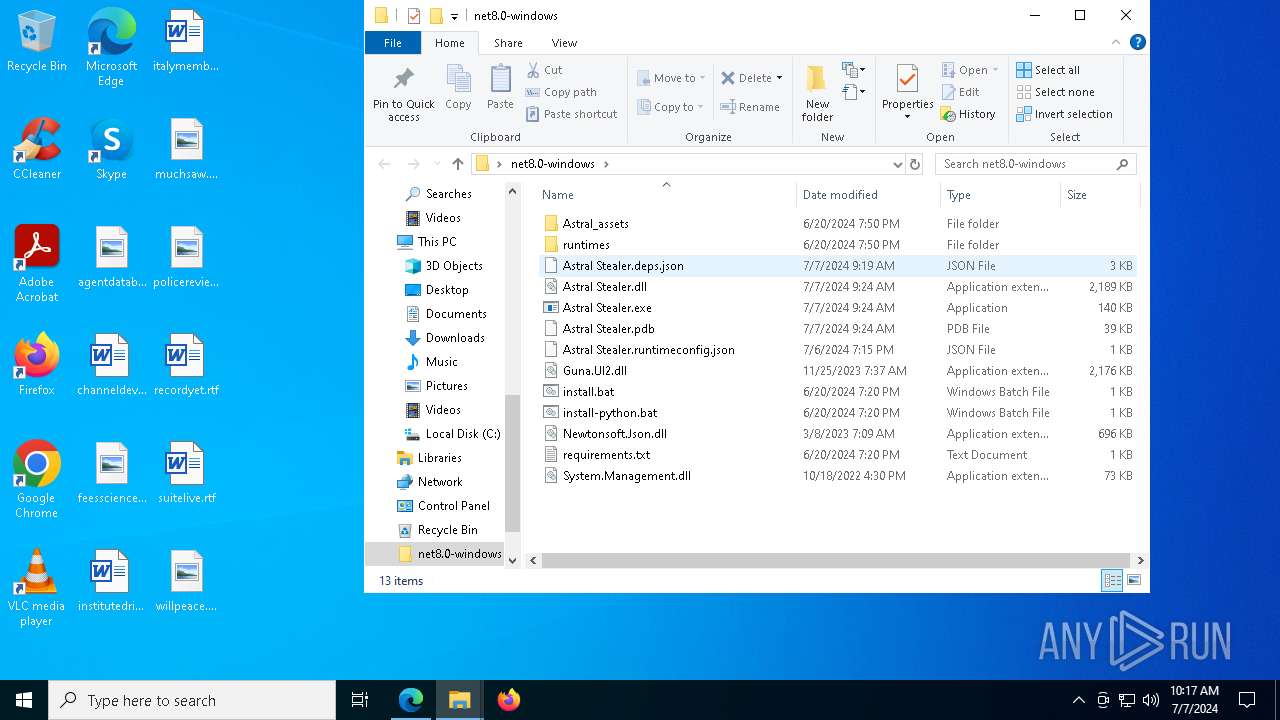
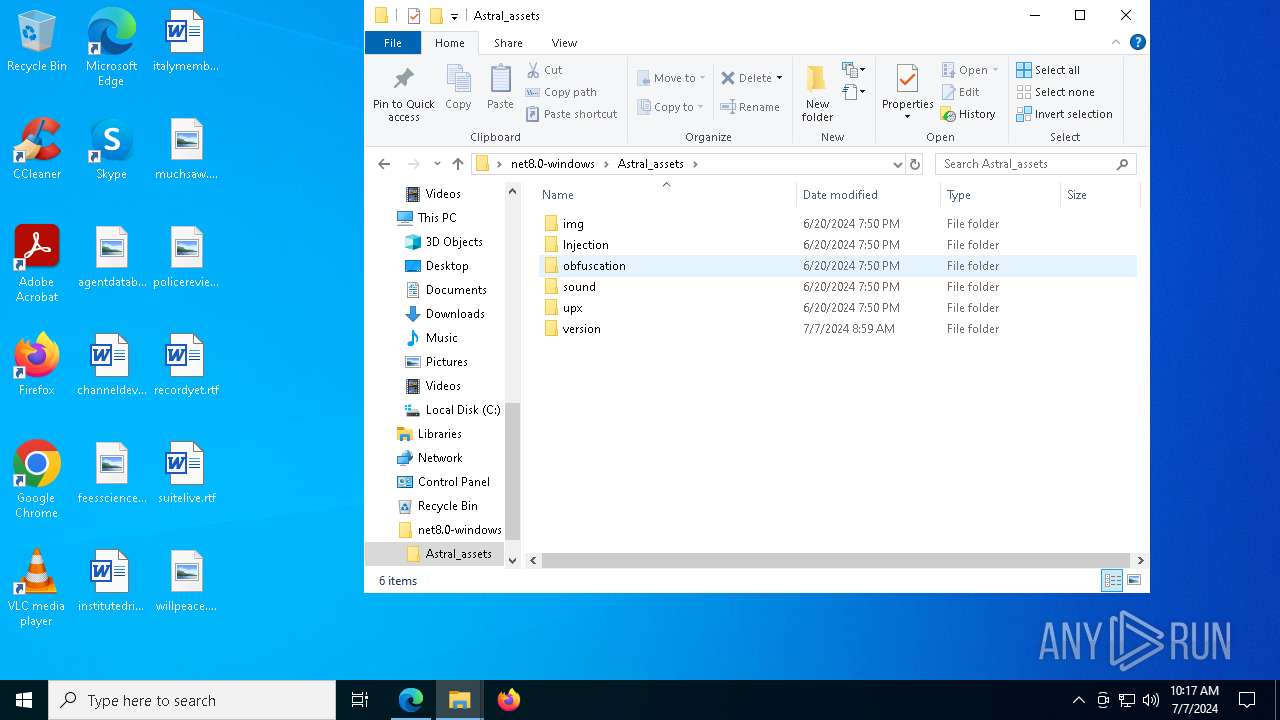
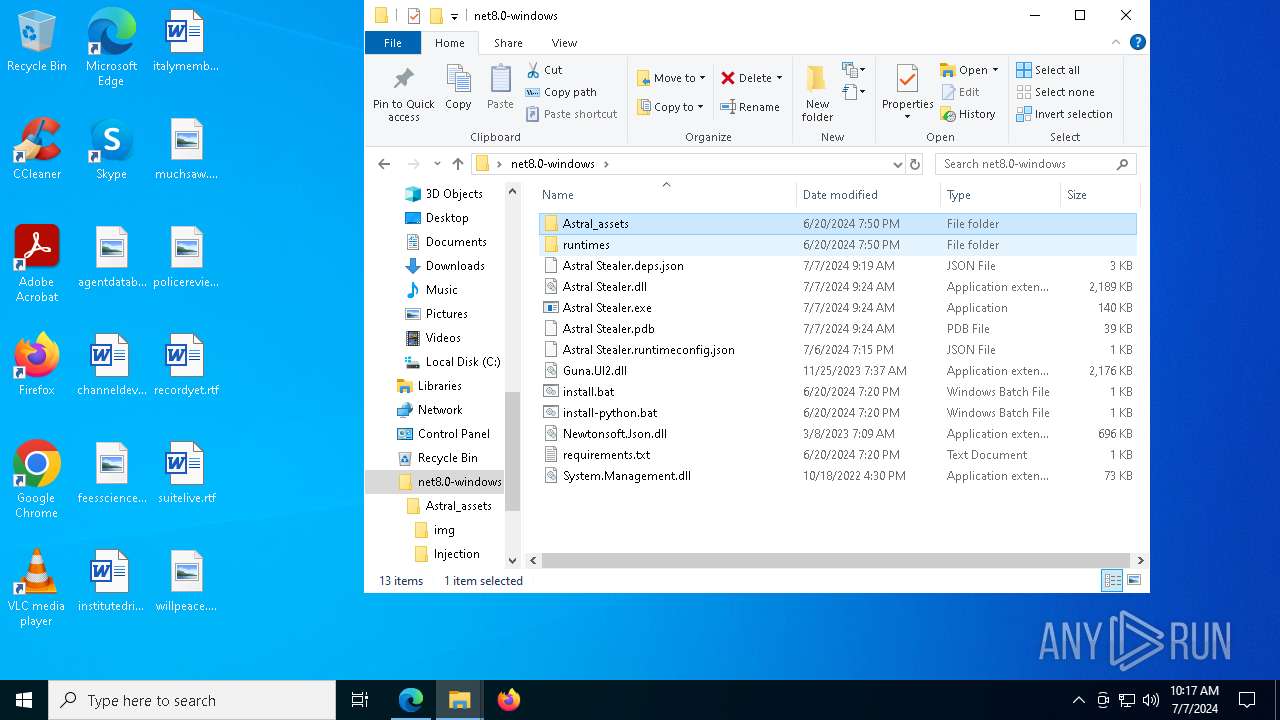
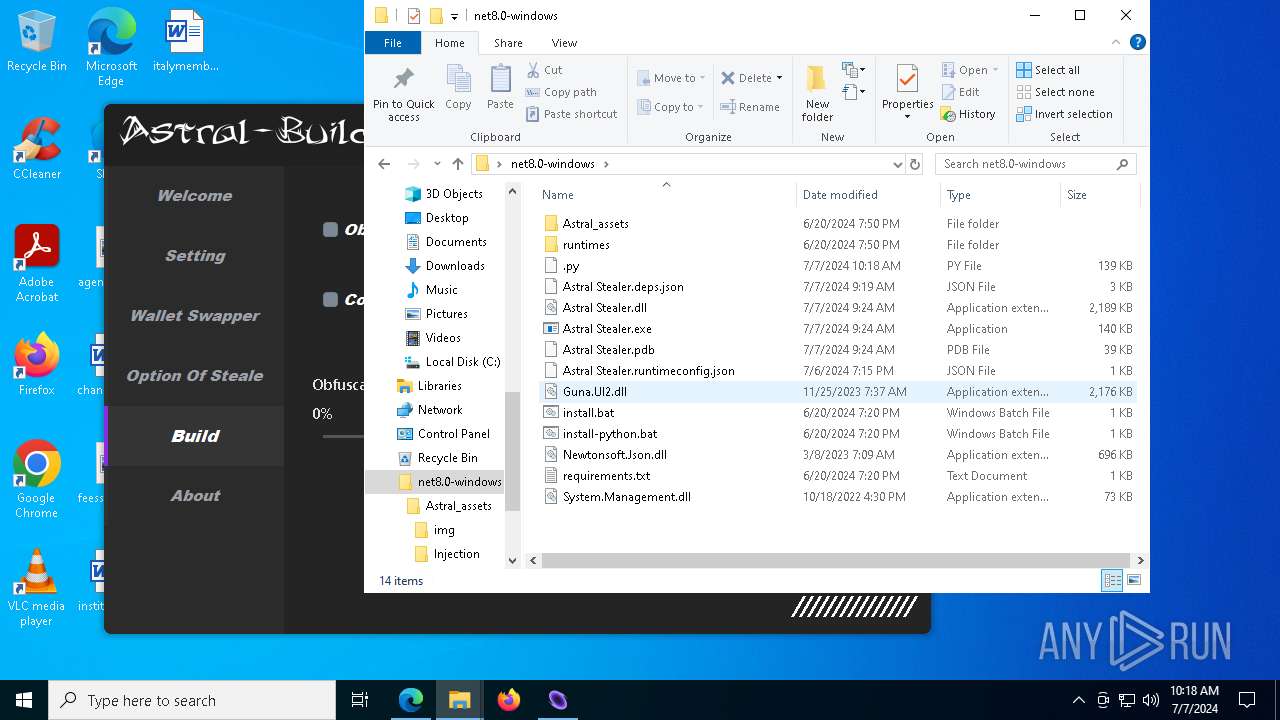
| ZipFileName: | net8.0-windows/ |
Total processes
204
Monitored processes
64
Malicious processes
8
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 376 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --disable-gpu-sandbox --use-gl=disabled --gpu-vendor-id=5140 --gpu-device-id=140 --gpu-sub-system-id=0 --gpu-revision=0 --gpu-driver-version=10.0.19041.3636 --no-appcompat-clear --gpu-preferences=WAAAAAAAAADoAAAMAAAAAAAAAAAAAAAAAABgAAAAAAA4AAAAAAAAAAAAAABEAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAGAAAAAAAAAAYAAAAAAAAAAgAAAAAAAAACAAAAAAAAAAIAAAAAAAAAA== --mojo-platform-channel-handle=6576 --field-trial-handle=2368,i,12752881730215851703,7689843112686011042,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1052 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1292 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=2560 --field-trial-handle=2368,i,12752881730215851703,7689843112686011042,262144 --variations-seed-version /prefetch:3 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2140 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=2752 --field-trial-handle=2368,i,12752881730215851703,7689843112686011042,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 3652 | C:\WINDOWS\explorer.exe /factory,{5BD95610-9434-43C2-886C-57852CC8A120} -Embedding | C:\Windows\explorer.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 10.0.19041.3758 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3932 | C:\Windows\syswow64\MsiExec.exe -Embedding 399E4A530181C236F6CB181F67D6991D | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4092 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5580 --field-trial-handle=2368,i,12752881730215851703,7689843112686011042,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 4600 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=8 --mojo-platform-channel-handle=5000 --field-trial-handle=2368,i,12752881730215851703,7689843112686011042,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 4756 | C:\Windows\syswow64\MsiExec.exe -Embedding 960CBE644B029703133B0A05ABFCEB9E | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
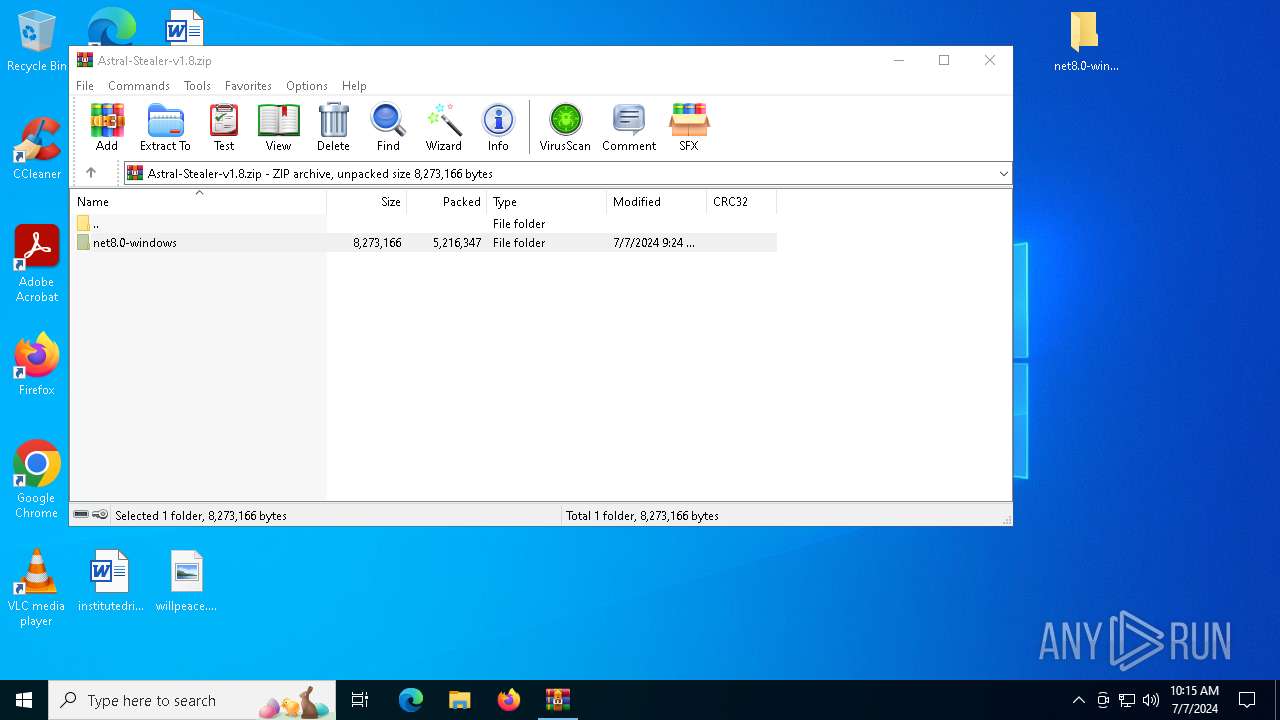
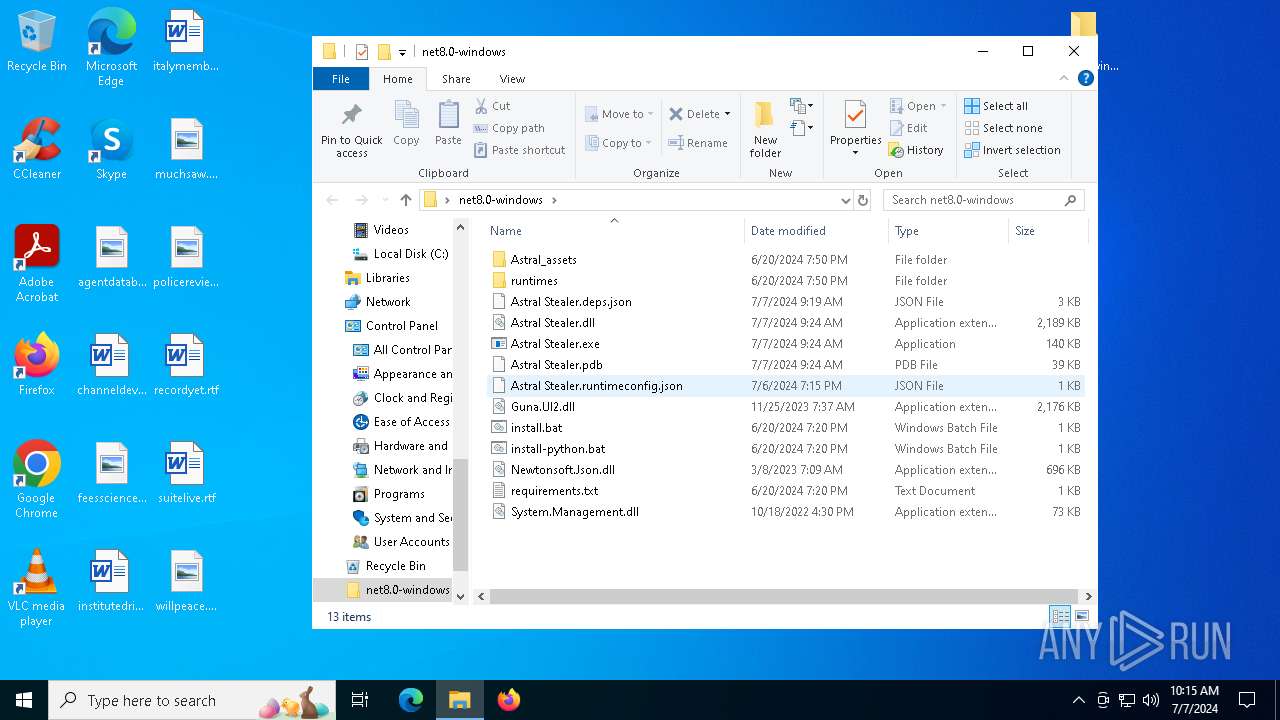
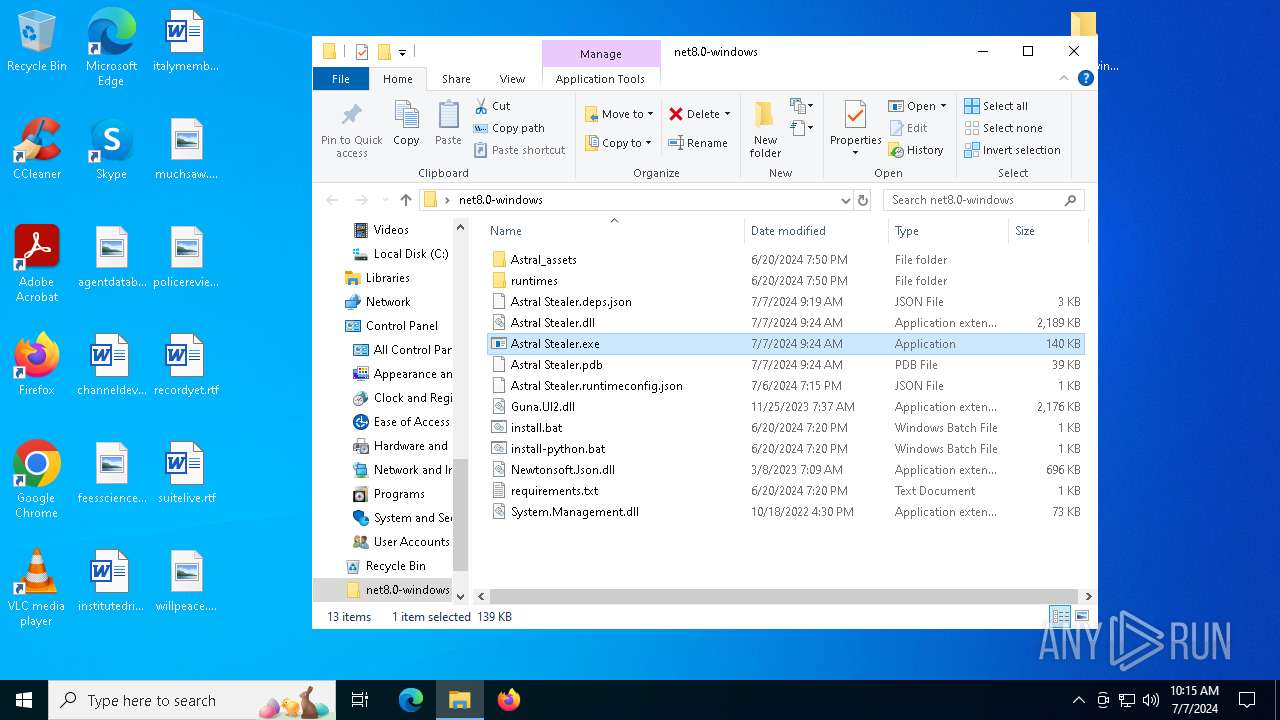
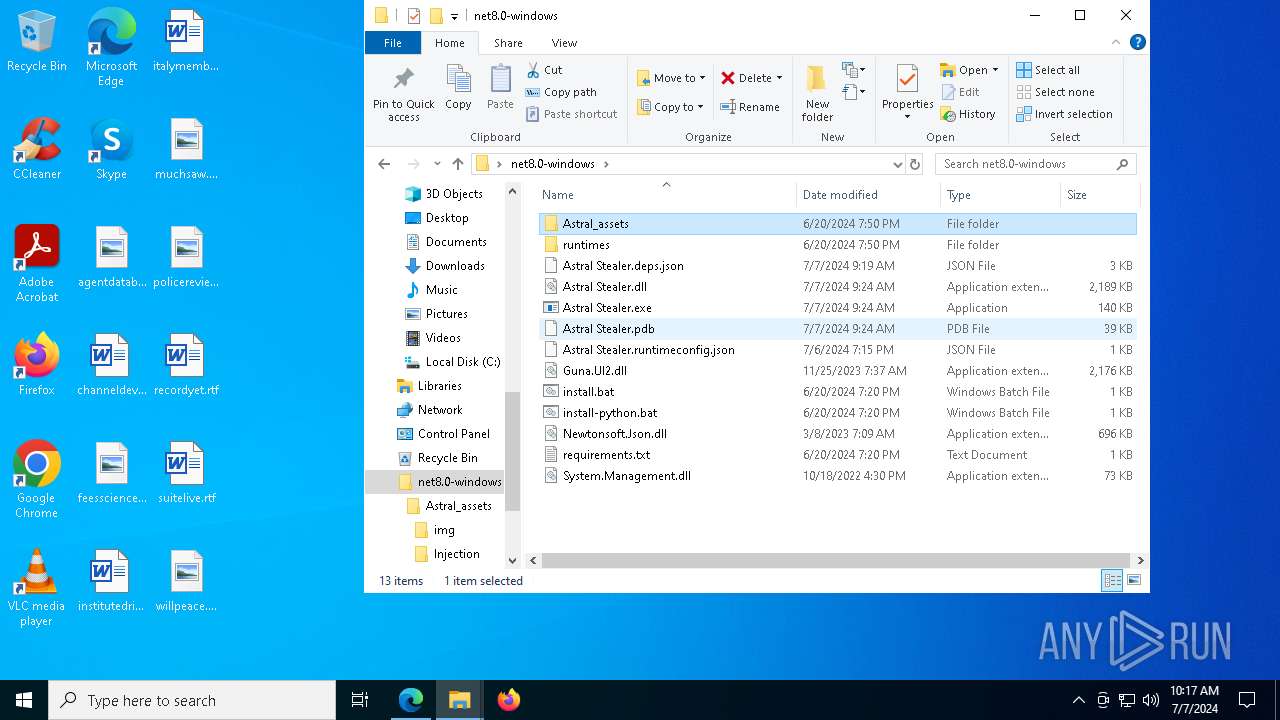
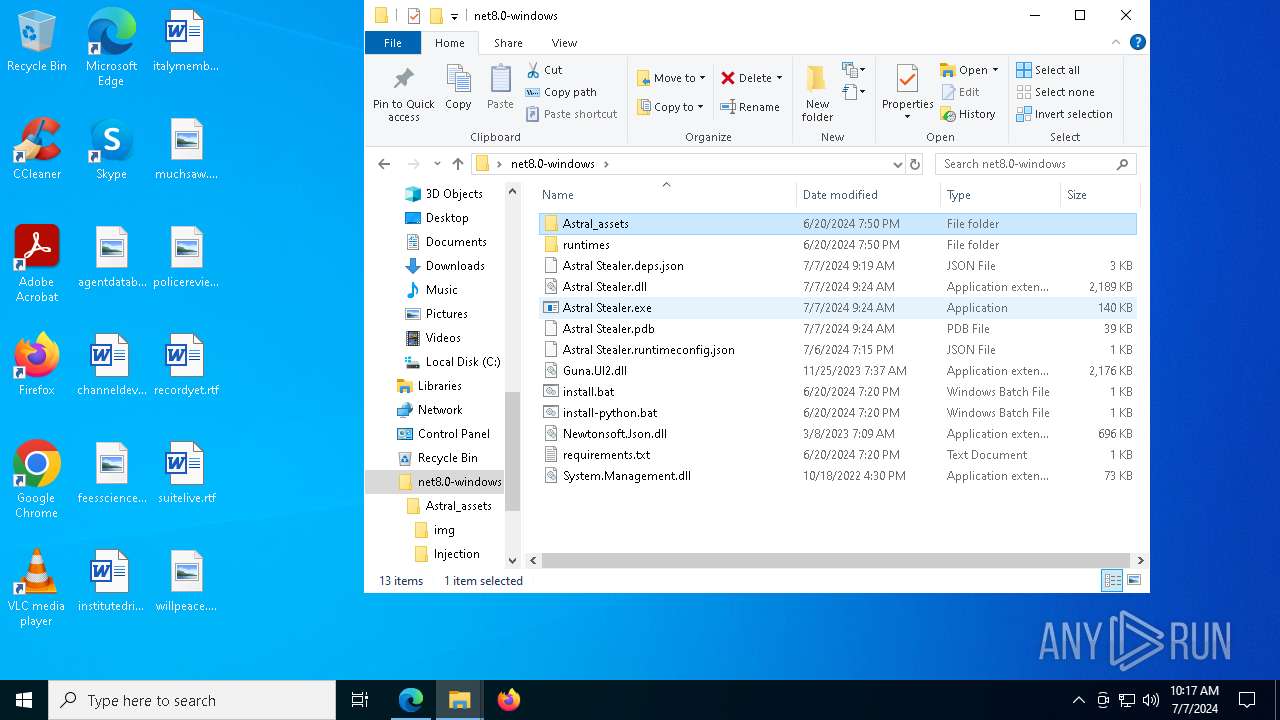
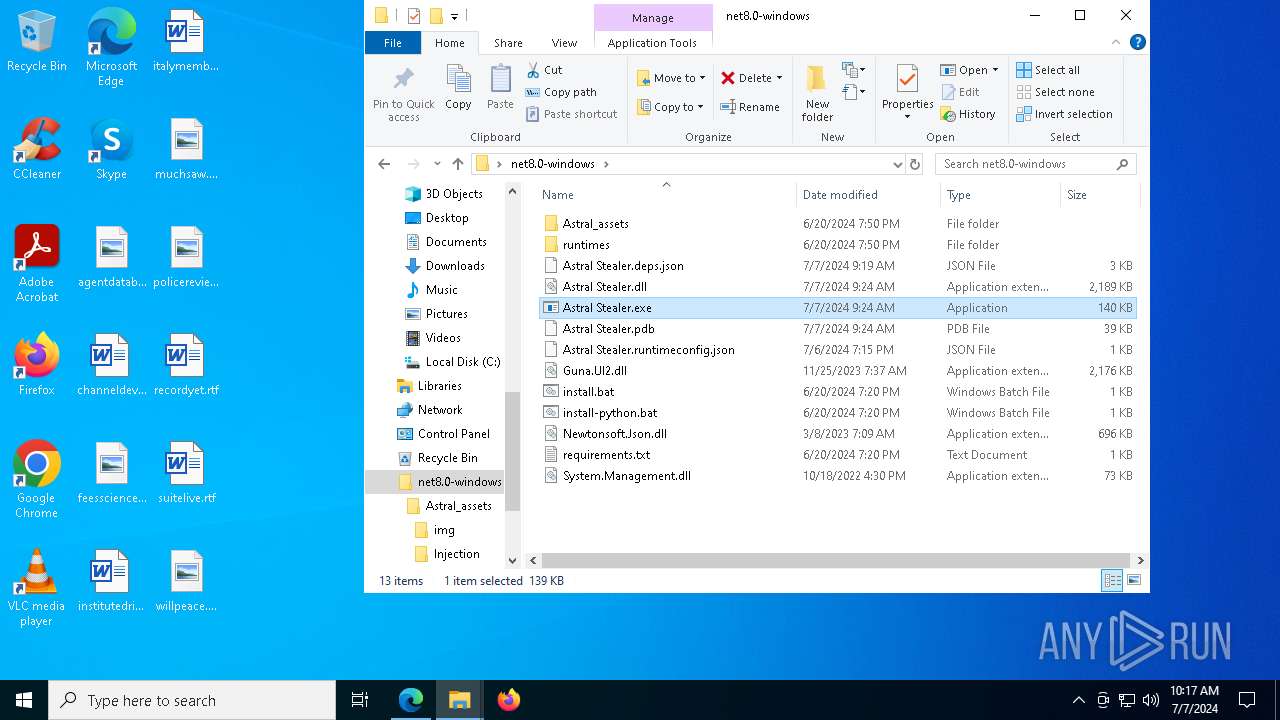
| 5112 | "C:\Users\admin\Desktop\net8.0-windows\Astral Stealer.exe" | C:\Users\admin\Desktop\net8.0-windows\Astral Stealer.exe | explorer.exe | ||||||||||||
User: admin Company: Astral Stealer Integrity Level: MEDIUM Description: Astral Stealer Exit code: 2147516547 Version: 1.0.0.0 Modules
| |||||||||||||||
Total events
38 547
Read events
37 466
Write events
1 031
Delete events
50
Modification events
| (PID) Process: | (5872) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (5872) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (5872) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\GoogleChromeEnterpriseBundle64.zip | |||
| (PID) Process: | (5872) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Astral-Stealer-v1.8.zip | |||
| (PID) Process: | (5872) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (5872) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (5872) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (5872) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (5872) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF3D0000002D000000FD03000016020000 | |||
| (PID) Process: | (5872) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\General |
| Operation: | write | Name: | LastFolder |
Value: C:\Users\admin\AppData\Local\Temp | |||
Executable files
497
Suspicious files
209
Text files
148
Unknown types
12
Dropped files
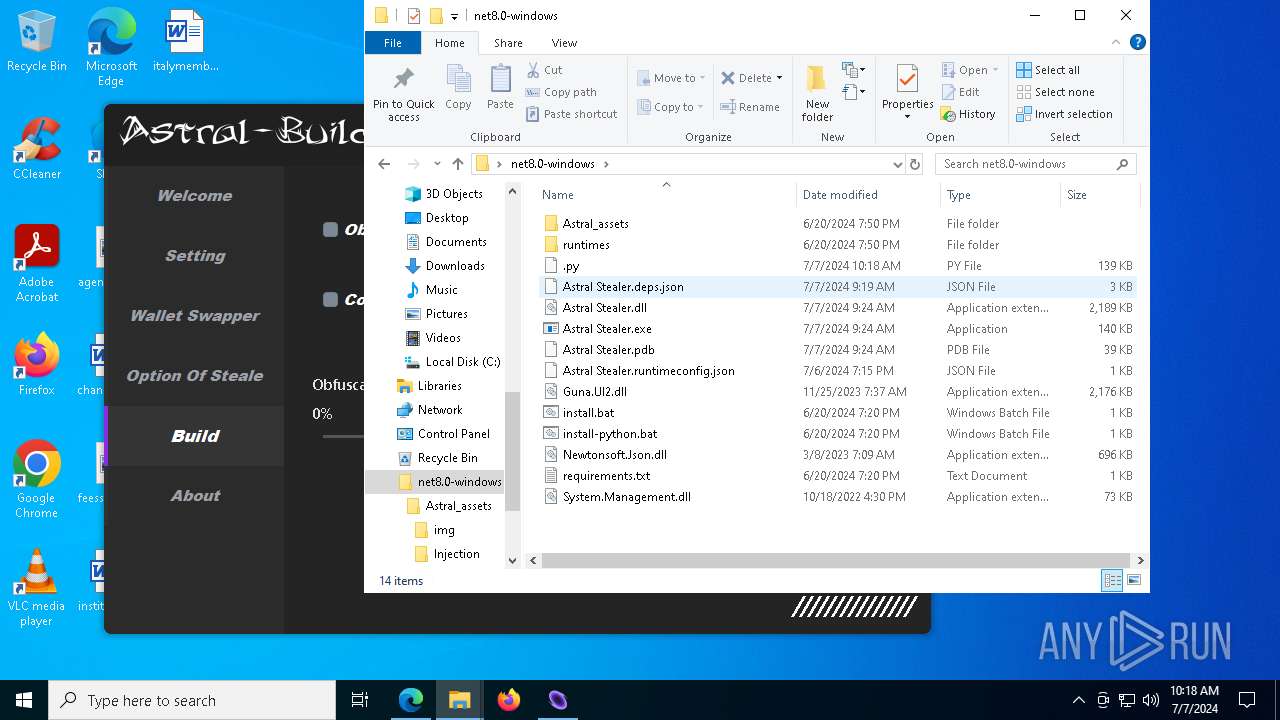
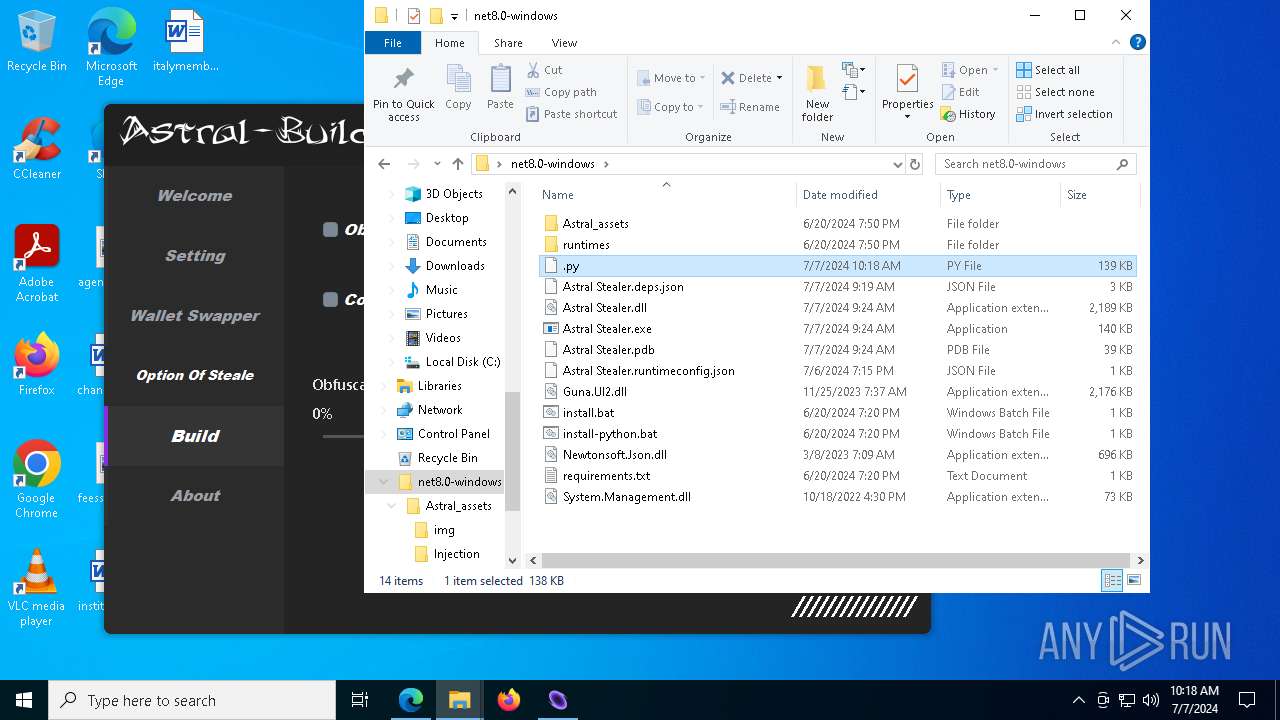
PID | Process | Filename | Type | |
|---|---|---|---|---|
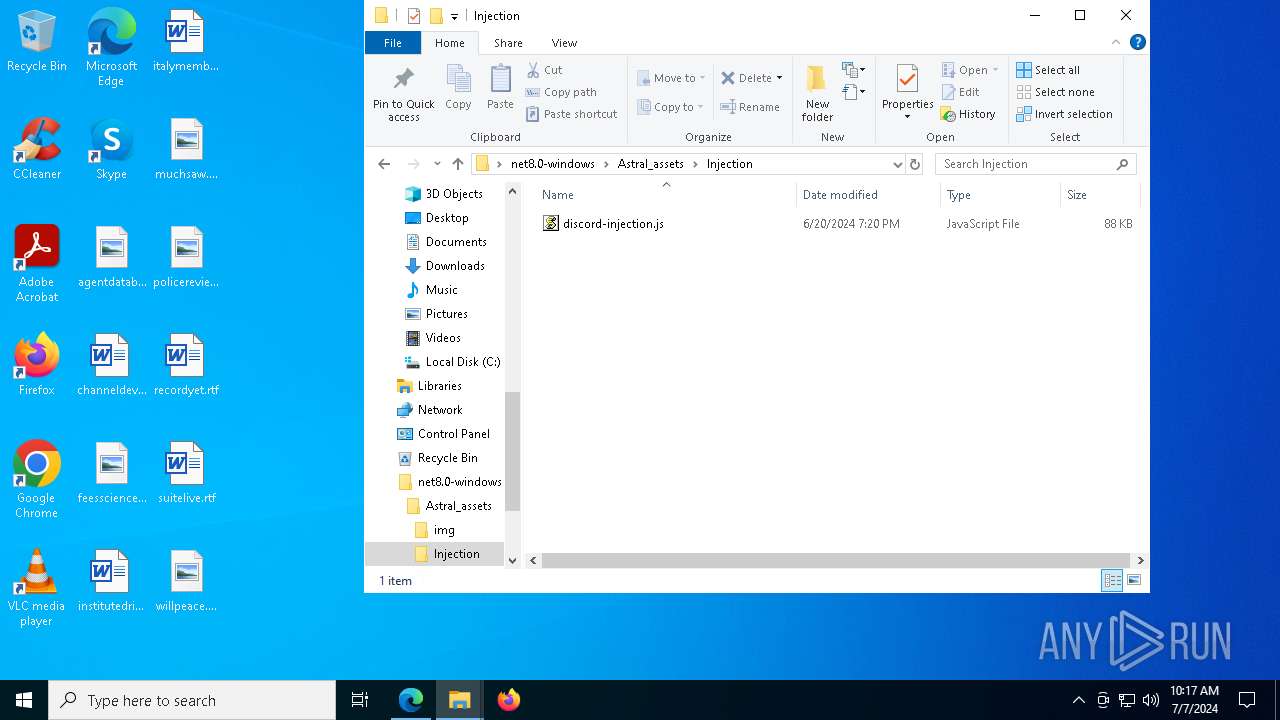
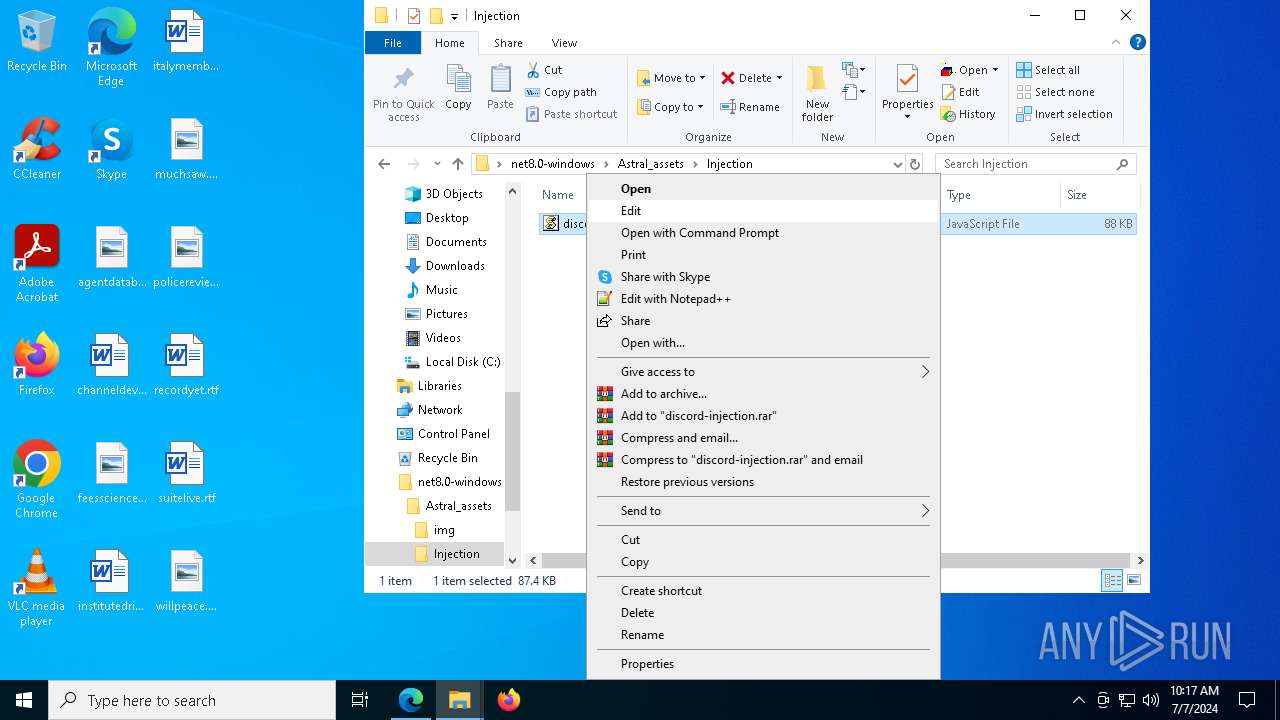
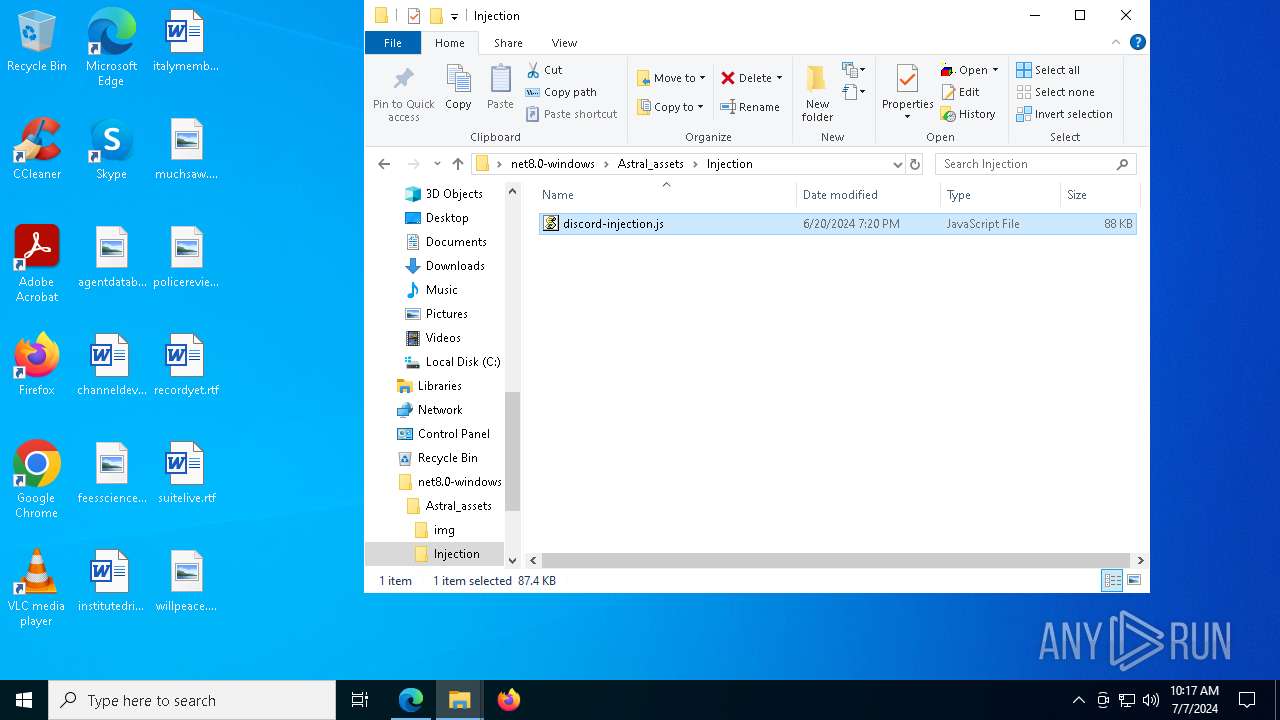
| 5872 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa5872.14134\net8.0-windows\Astral Stealer.deps.json | binary | |
MD5:AD3899242747075A58AD9E39E902E572 | SHA256:E065D74B80C7C33FF71F58641CC8F5B999AF72248E360C913B9E171074ECA9E7 | |||
| 5872 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa5872.14134\net8.0-windows\Astral_assets\img\arrow_w.png | image | |
MD5:2AA9FB89F507C2C1984E980E2071BB4A | SHA256:C879A67F58F2B5519EC14674821F688374B836CD674BAD39508473CE72227E60 | |||
| 5872 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa5872.14134\net8.0-windows\Astral_assets\img\build_d.png | image | |
MD5:25BF42F9EF458447BE831BBB05911CA3 | SHA256:889B85BB4D8FF9EE03FA812419920451093840A57A8CA1735DE653C5D8BCF7A8 | |||
| 5872 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa5872.14134\net8.0-windows\Astral_assets\img\logo.png | image | |
MD5:1751C2A5022ACF8B8B8C4C1CD2BF81A3 | SHA256:B7FF5AFACEE4665FE44D3ADB0D5AB059F8310B9C06D77722C191678F5CB61623 | |||
| 5872 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa5872.14134\net8.0-windows\Astral_assets\img\logo.ico | image | |
MD5:76CC56ED36875BCE61E0BBE4DD9BF6E8 | SHA256:EAB8C8E0B63F9C7E36BEC88095BE0454B83E0EF4EA050801FF621411EC16D9D4 | |||
| 5872 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa5872.14134\net8.0-windows\Astral_assets\img\options_w.png | image | |
MD5:CEDC30F87B27F7BA298C5BF5B7BC9F09 | SHA256:8A5319FDBCC6AEFD47BB3FE0138BDA7355C84CF0D5C6D9F7503756D5A86A81F2 | |||
| 5872 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa5872.14134\net8.0-windows\Astral_assets\img\options_d.png | image | |
MD5:F99BD429D4A98AD8FDE284D387329A9E | SHA256:0D26C8710E401C4428B4C5214DF2B6FDEA0DABEED0D6005CBEA46771034319B0 | |||
| 5872 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa5872.14134\net8.0-windows\Astral_assets\img\thiefcat.ico | image | |
MD5:76CC56ED36875BCE61E0BBE4DD9BF6E8 | SHA256:EAB8C8E0B63F9C7E36BEC88095BE0454B83E0EF4EA050801FF621411EC16D9D4 | |||
| 5872 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa5872.14134\net8.0-windows\Astral Stealer.dll | executable | |
MD5:AAE3DB3D79052FBDD65728644D0B778B | SHA256:9E2E1E1392CBD5097033CFD40A1D496F9BB31003D7C80CBA53EB8CDD100531F4 | |||
| 5872 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa5872.14134\net8.0-windows\Astral Stealer.exe | executable | |
MD5:726C717D3E26F216B316F169AE4BEFD2 | SHA256:1E7A930303762A3A1F8678DA099225D9276D1A9FA16CED07A9FB4F14E0201BD9 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
35
TCP/UDP connections
97
DNS requests
74
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2456 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | binary | 471 b | unknown |
6428 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | US | binary | 471 b | unknown |
6440 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | US | binary | 471 b | unknown |
7596 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | DE | binary | 419 b | unknown |
7596 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | DE | binary | 408 b | unknown |
2108 | svchost.exe | HEAD | 200 | 23.48.23.53:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/6e6d05a2-47e8-42b8-85a0-e8b7ee48333a?P1=1720572211&P2=404&P3=2&P4=eO1vkFBZLeP28EmdxGvs9M2A9592%2bqIyRuctg%2bVfIH8OYFRuKg55APFmKYwCWEx%2fmM%2f%2b8MDuSzIVvtrPb0qALw%3d%3d | DE | — | — | unknown |
6320 | msedge.exe | GET | 200 | 23.48.23.143:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | binary | 1.01 Kb | unknown |
6320 | msedge.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicCodSigPCA2011_2011-07-08.crl | DE | binary | 1.05 Kb | unknown |
3040 | OfficeClickToRun.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | US | binary | 471 b | unknown |
2108 | svchost.exe | GET | 206 | 23.48.23.53:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/6e6d05a2-47e8-42b8-85a0-e8b7ee48333a?P1=1720572211&P2=404&P3=2&P4=eO1vkFBZLeP28EmdxGvs9M2A9592%2bqIyRuctg%2bVfIH8OYFRuKg55APFmKYwCWEx%2fmM%2f%2b8MDuSzIVvtrPb0qALw%3d%3d | DE | binary | 1.09 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
444 | svchost.exe | 51.104.136.2:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2124 | RUXIMICS.exe | 51.104.136.2:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4032 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4656 | SearchApp.exe | 92.123.104.61:443 | www.bing.com | Akamai International B.V. | DE | unknown |
2456 | svchost.exe | 40.126.32.140:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | unknown |
2456 | svchost.exe | 192.229.221.95:80 | — | EDGECAST | US | whitelisted |
1060 | svchost.exe | 23.35.238.131:443 | go.microsoft.com | AKAMAI-AS | DE | unknown |
3040 | OfficeClickToRun.exe | 52.111.236.21:443 | nexusrules.officeapps.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
login.live.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
nexusrules.officeapps.live.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
arc.msn.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
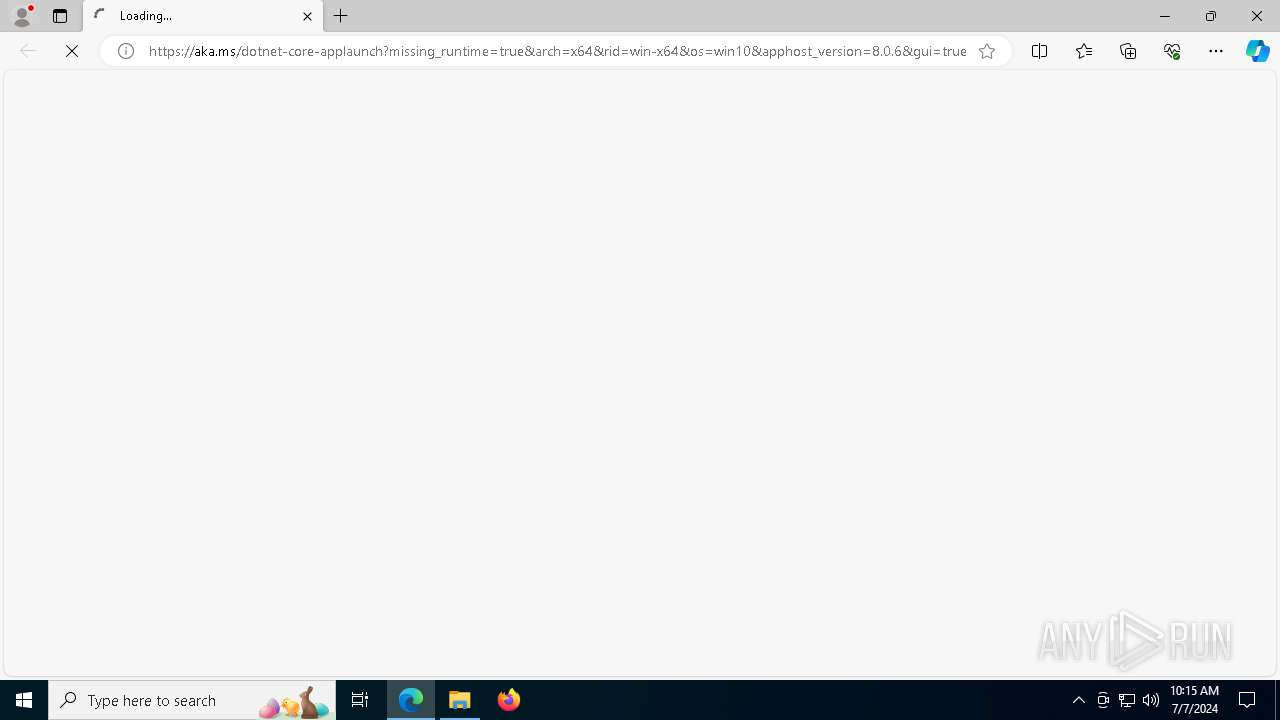
aka.ms |
| whitelisted |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| unknown |
Threats
Process | Message |
|---|---|
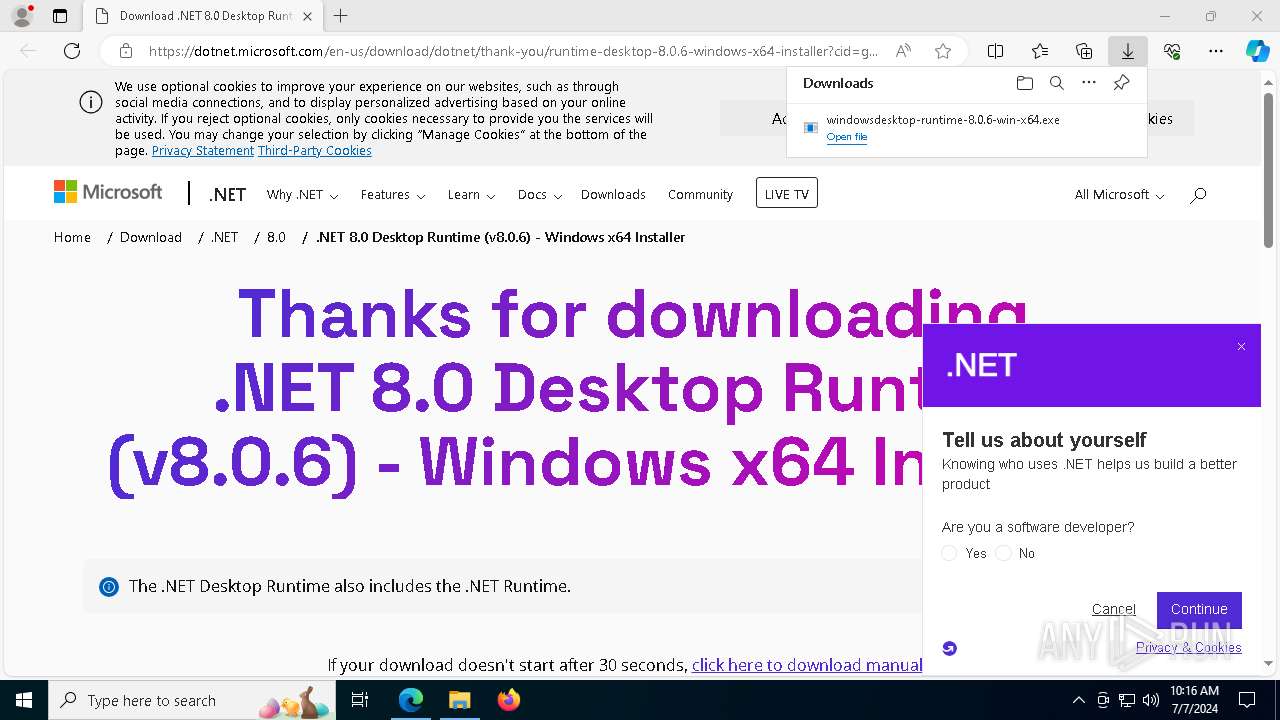
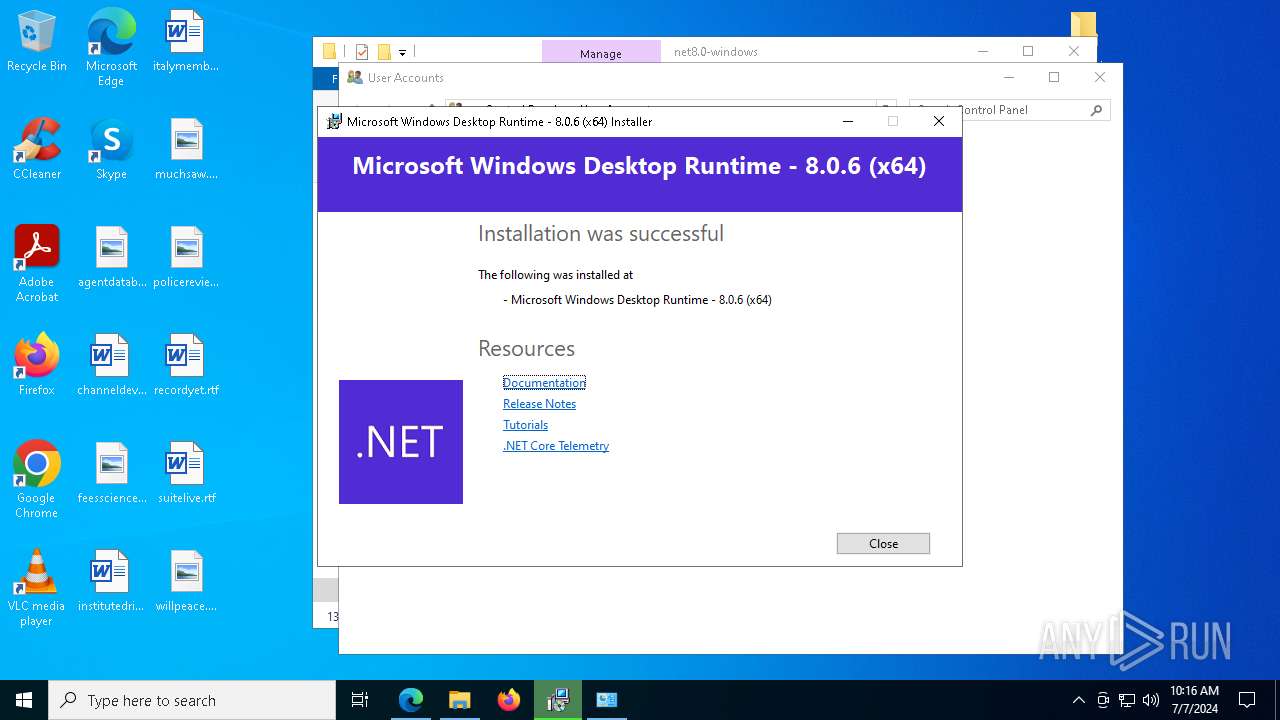
Astral Stealer.exe | You must install .NET to run this application.
App: C:\Users\admin\Desktop\net8.0-windows\Astral Stealer.exe
Architecture: x64
App host version: 8.0.6
.NET location: Not found
Learn more:
https://aka.ms/dotnet/app-launch-failed
Download the .NET runtime:
https://aka.ms/dotnet-core-applaunch?missing_runtime=true&arch=x64&rid=win-x64&os=win10&apphost_version=8.0.6 |