| download: | flashplayer27pp_xa_install.exe |
| Full analysis: | https://app.any.run/tasks/434aa119-88e0-4f78-b694-3ad696719c4f |
| Verdict: | Malicious activity |
| Analysis date: | May 24, 2019, 21:28:50 |
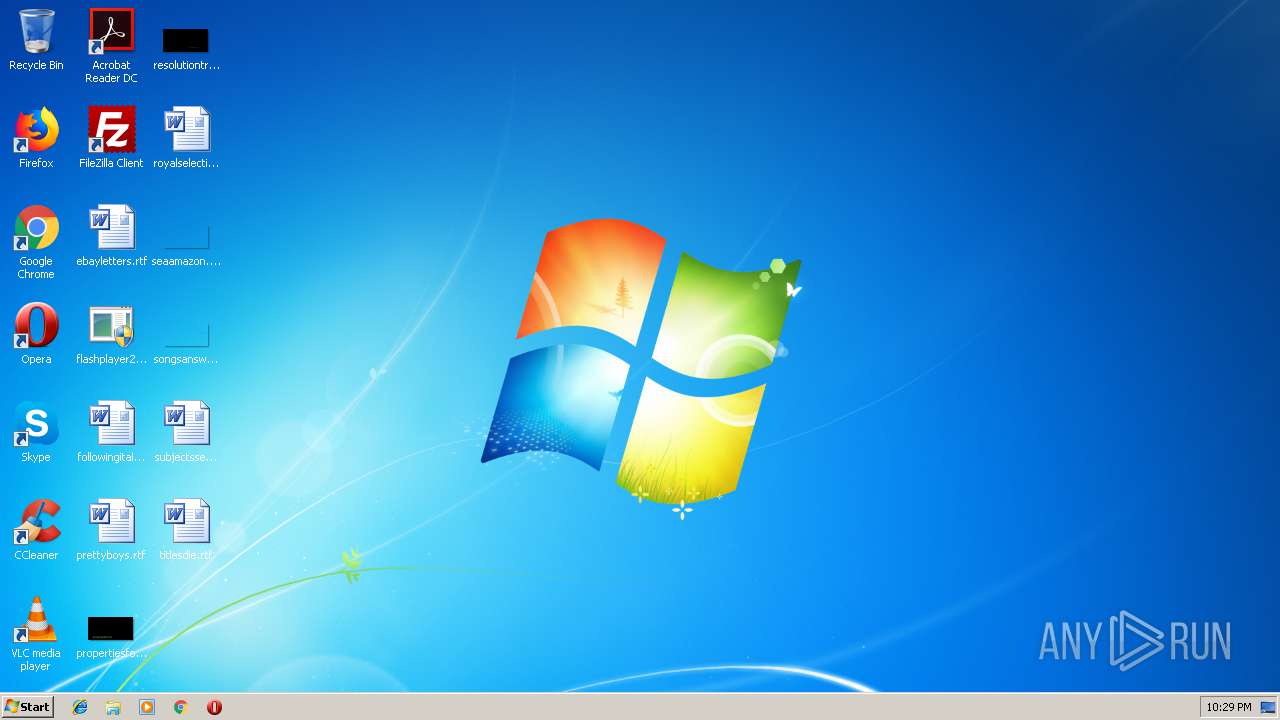
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 (stripped to external PDB), for MS Windows |
| MD5: | 1010DFCDFF7E04EA1BA40C4CB3AD9925 |
| SHA1: | B31FD6C36837D73020205D75E3F070DB8EE001DA |
| SHA256: | CF0A219F0132CD02CE35F6FE4CDE24DE14A564CD6C9A4F19CBF9F9F6FCB60F5E |
| SSDEEP: | 1536:sHtTu8U/b1/utgI06tnIcvldn38ZAuSU8NbLXc5kt4G+:itSv/b1/uiILFMKRUqXc5kGG+ |
MALICIOUS
Runs injected code in another process
- flashplayer27pp_xa_install.exe (PID: 2864)
Application was injected by another process
- explorer.exe (PID: 116)
SUSPICIOUS
Executable content was dropped or overwritten
- flashplayer27pp_xa_install.exe (PID: 2864)
INFO
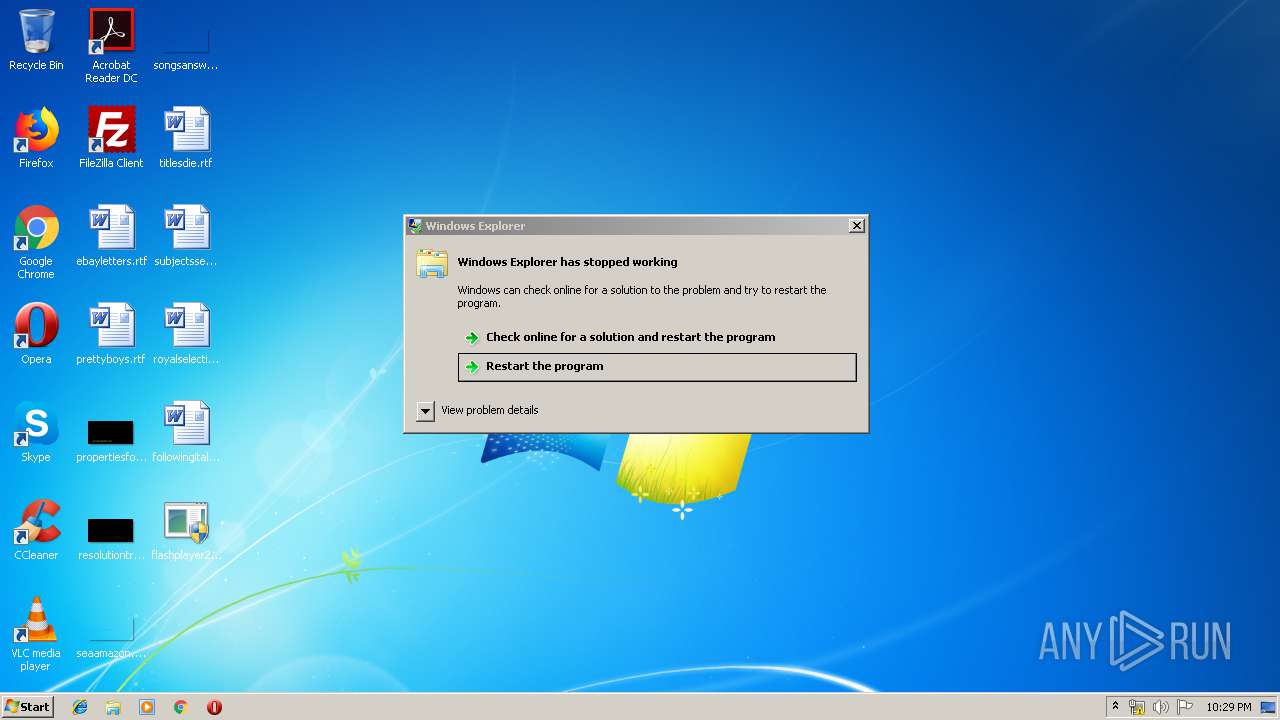
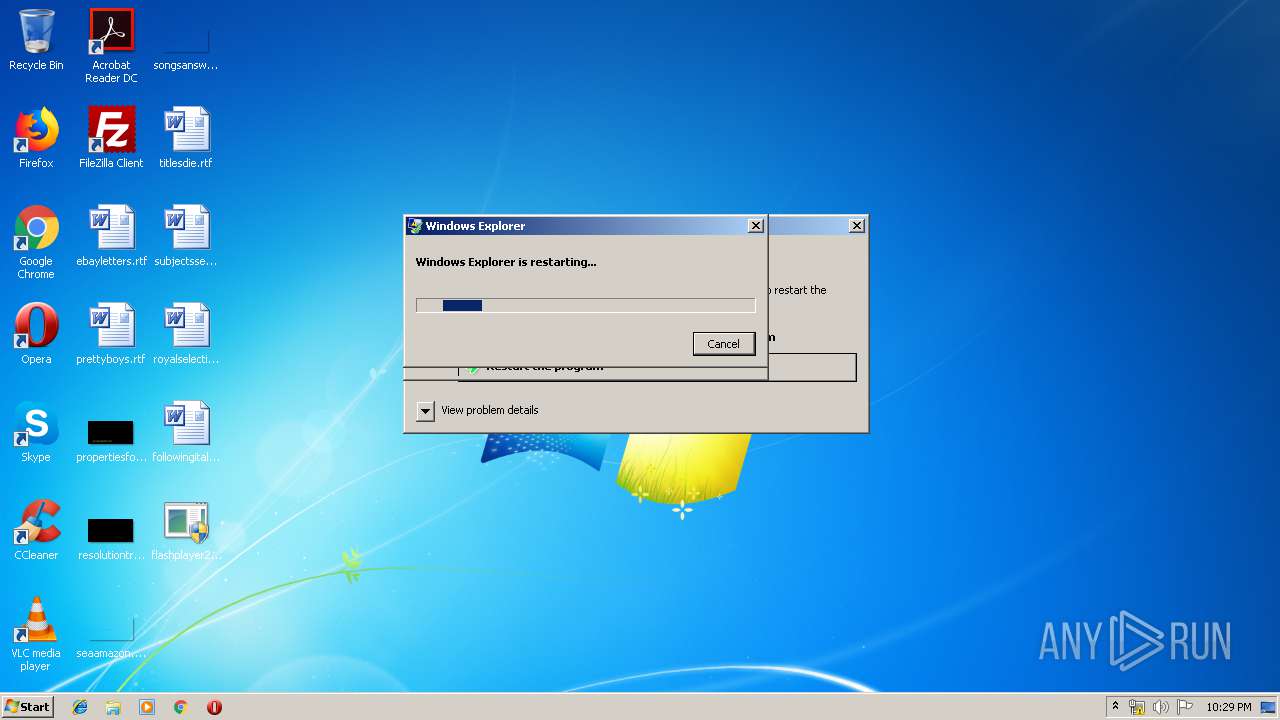
Application was crashed
- explorer.exe (PID: 116)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable PowerBASIC (generic) (87.5) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (4.7) |
| .exe | | | Win32 Executable (generic) (3.2) |
| .exe | | | Win16/32 Executable Delphi generic (1.4) |
| .exe | | | Generic Win/DOS Executable (1.4) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1970:01:01 04:25:45+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.52 |
| CodeSize: | 67072 |
| InitializedDataSize: | 14848 |
| UninitializedDataSize: | 104632 |
| EntryPoint: | 0xaf40 |
| OSVersion: | 1 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 01-Jan-1970 03:25:45 |
| Detected languages: |
|
| CompanyName: | Microsoft Corporation |
| FileDescription: | Microsoft Software Protection Platform Service |
| FileVersion: | 6.1.7600.16385 (win7_rtm.090713-1255) |
| InternalName: | sppsvc |
| OriginalFilename: | sppsvc.exe |
| LegalCopyright: | © Microsoft Corporation. All rights reserved. |
| ProductName: | Microsoft® Windows® Operating System |
| ProductVersion: | 6.1.7600.16385 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x000A |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00C0 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 01-Jan-1970 03:25:45 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00010600 | 0x00010600 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.32855 |
.data | 0x00012000 | 0x0001AEB8 | 0x00001600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.50426 |
.link | 0x0002D000 | 0x000010D0 | 0x00001200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.83071 |
.rloc | 0x0002F000 | 0x00000A80 | 0x00000C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.31035 |
.rsrc | 0x00030000 | 0x00000414 | 0x00000600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.03861 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.48916 | 956 | Latin 1 / Western European | English - United States | RT_VERSION |
Imports
ADVAPI32.DLL |
COMCTL32.DLL |
GDI32.DLL |
KERNEL32.DLL |
NTDLL.DLL |
OLE32.DLL |
OLEAUT32.DLL |
SHELL32.DLL |
SHLWAPI.DLL |
URLMON.DLL |
Total processes
42
Monitored processes
3
Malicious processes
0
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 116 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 255 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2128 | "C:\Users\admin\Desktop\flashplayer27pp_xa_install.exe" | C:\Users\admin\Desktop\flashplayer27pp_xa_install.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Software Protection Platform Service Exit code: 3221226540 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2864 | "C:\Users\admin\Desktop\flashplayer27pp_xa_install.exe" | C:\Users\admin\Desktop\flashplayer27pp_xa_install.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Software Protection Platform Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
895
Read events
895
Write events
0
Delete events
0
Modification events
Executable files
1
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2864 | flashplayer27pp_xa_install.exe | C:\Users\admin\AppData\Local\cpiresu.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
9
DNS requests
8
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2864 | flashplayer27pp_xa_install.exe | GET | — | 145.14.145.230:80 | http://bbzsvr02.000webhostapp.com/ | US | — | — | shared |
2864 | flashplayer27pp_xa_install.exe | GET | 200 | 216.146.43.71:80 | http://checkip.dyndns.com/myip | US | html | 105 b | shared |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2864 | flashplayer27pp_xa_install.exe | 172.217.23.132:80 | www.google.com | Google Inc. | US | whitelisted |
— | — | 172.217.23.132:80 | www.google.com | Google Inc. | US | whitelisted |
2864 | flashplayer27pp_xa_install.exe | 145.14.145.230:80 | bbzsvr02.000webhostapp.com | Hostinger International Limited | US | shared |
2864 | flashplayer27pp_xa_install.exe | 216.146.43.71:80 | checkip.dyndns.com | Dynamic Network Services, Inc. | US | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.google.com |
| malicious |
checkip.dyndns.com |
| shared |
bbzsvr01.ga |
| unknown |
bbzsvr02.000webhostapp.com |
| shared |
mdutmjqtmjaxoq.ga |
| unknown |
mdutmjqtmjaxoq.tk |
| unknown |
mdutmjqtmjaxoq.cf |
| unknown |
mdutmjqtmjaxoq.ml |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1056 | svchost.exe | Misc activity | ET INFO DYNAMIC_DNS Query to *.dyndns. Domain |
2864 | flashplayer27pp_xa_install.exe | Potentially Bad Traffic | ET POLICY DynDNS CheckIp External IP Address Server Response |
1056 | svchost.exe | Potentially Bad Traffic | ET INFO DNS Query for Suspicious .ga Domain |
1056 | svchost.exe | Not Suspicious Traffic | ET INFO Observed Free Hosting Domain (*.000webhostapp .com in DNS Lookup) |
1056 | svchost.exe | Potentially Bad Traffic | ET INFO DNS Query for Suspicious .cf Domain |
1056 | svchost.exe | Potentially Bad Traffic | ET INFO DNS Query for Suspicious .ml Domain |