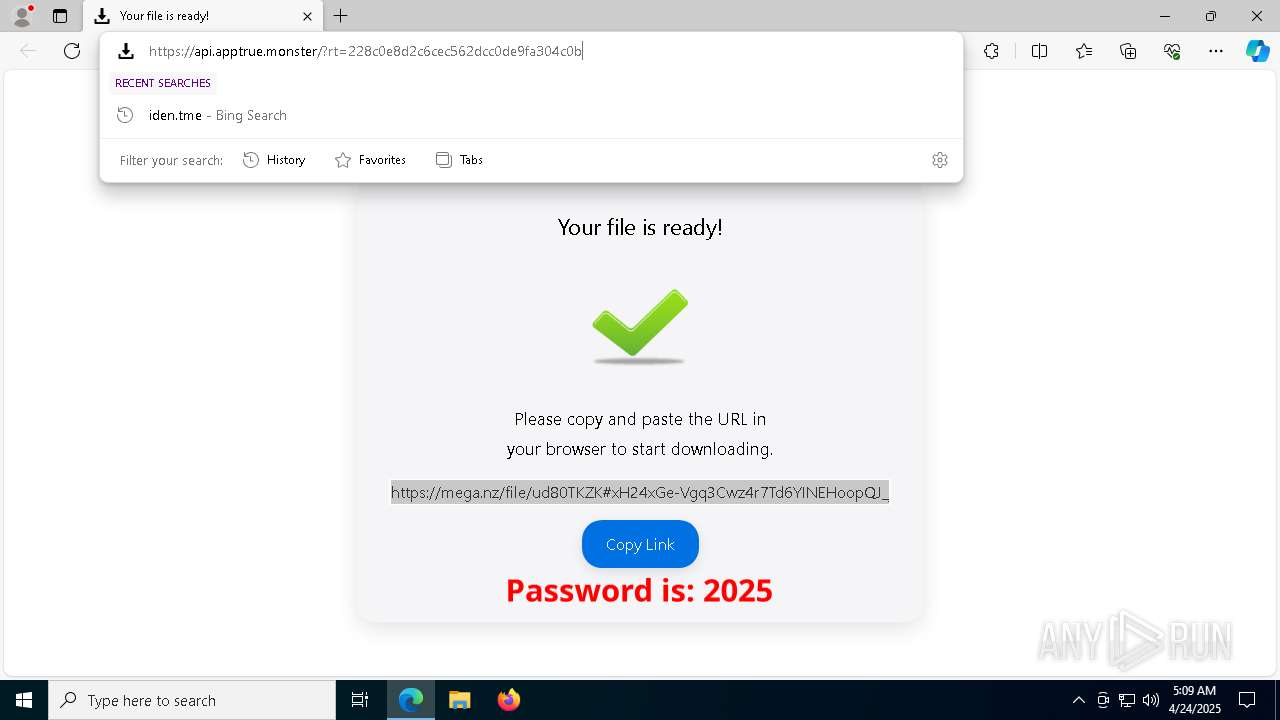
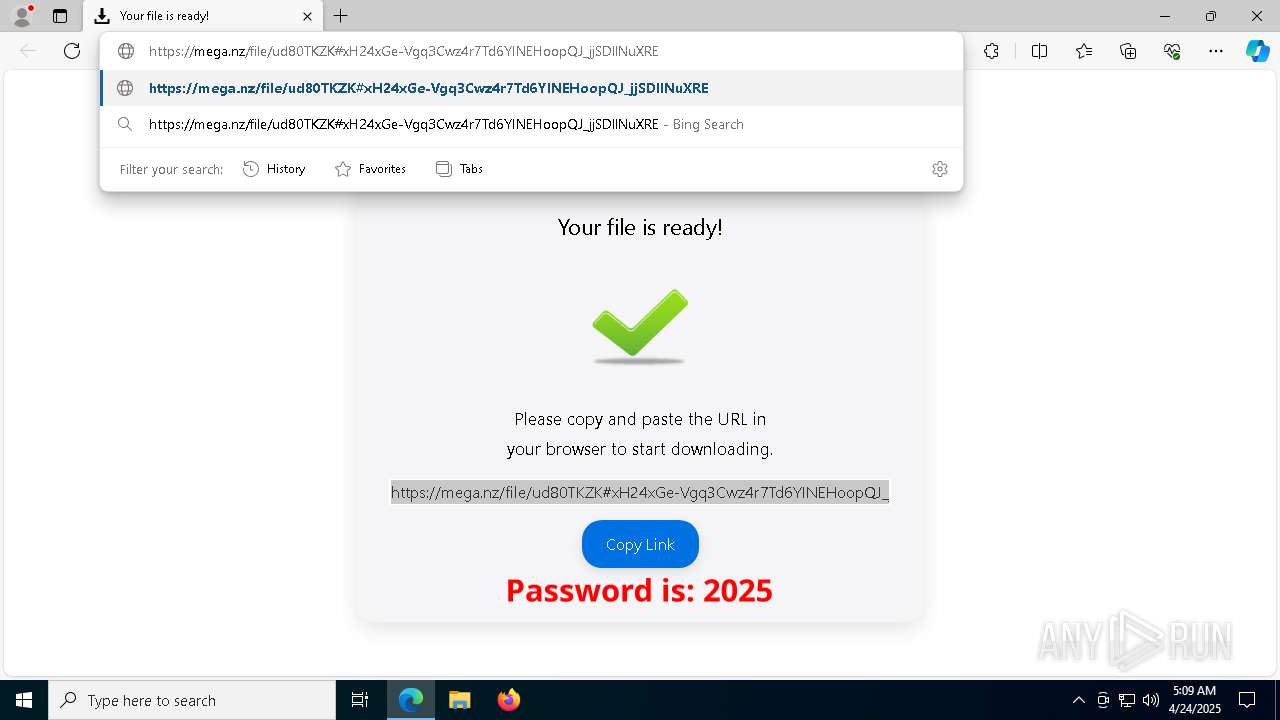
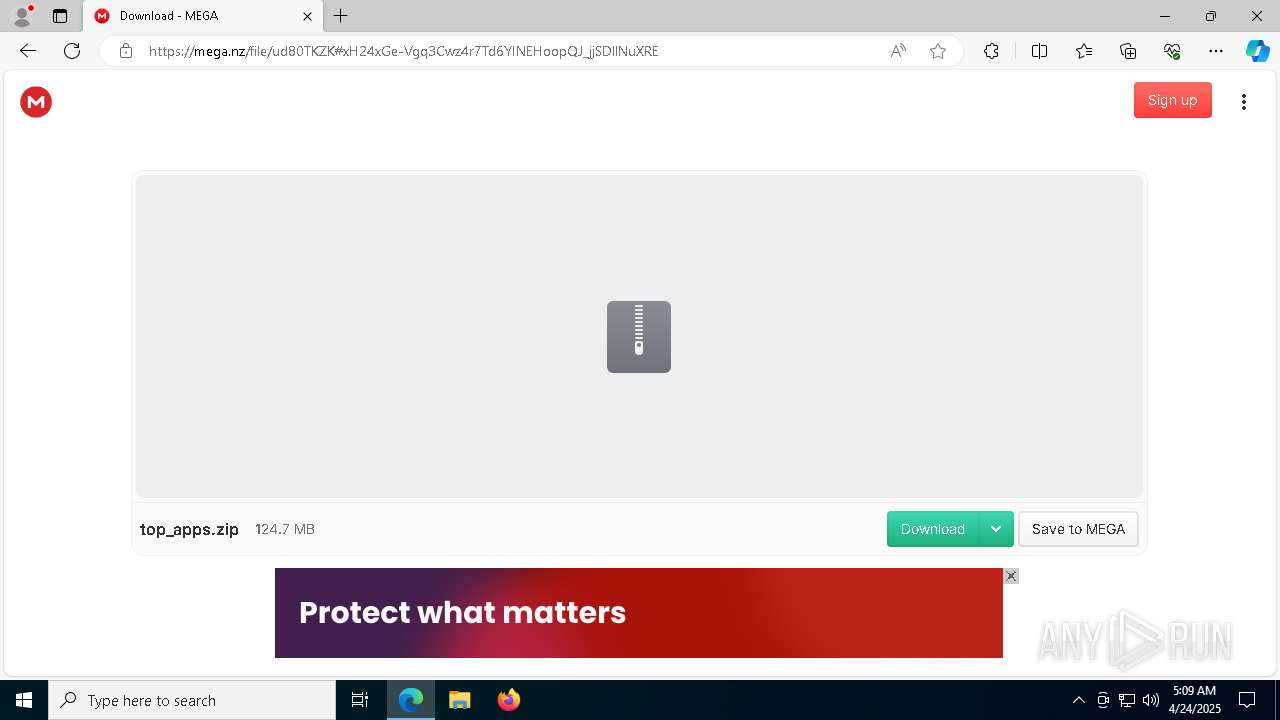
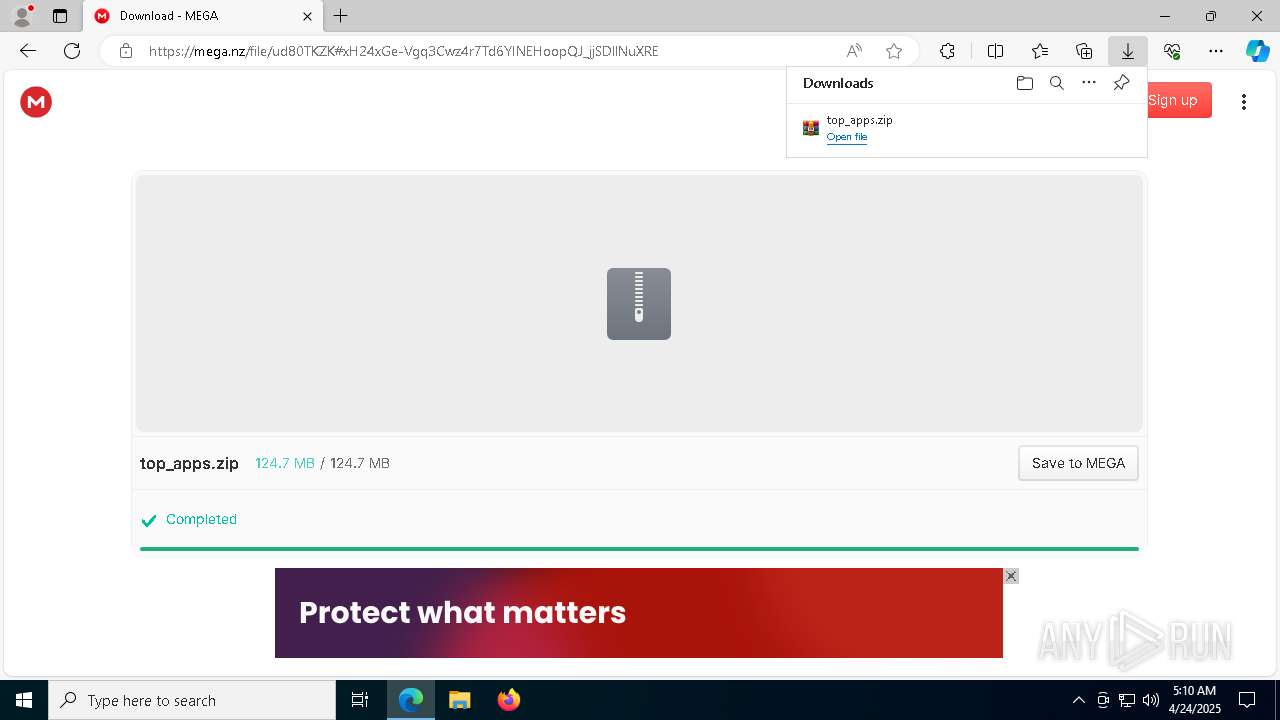
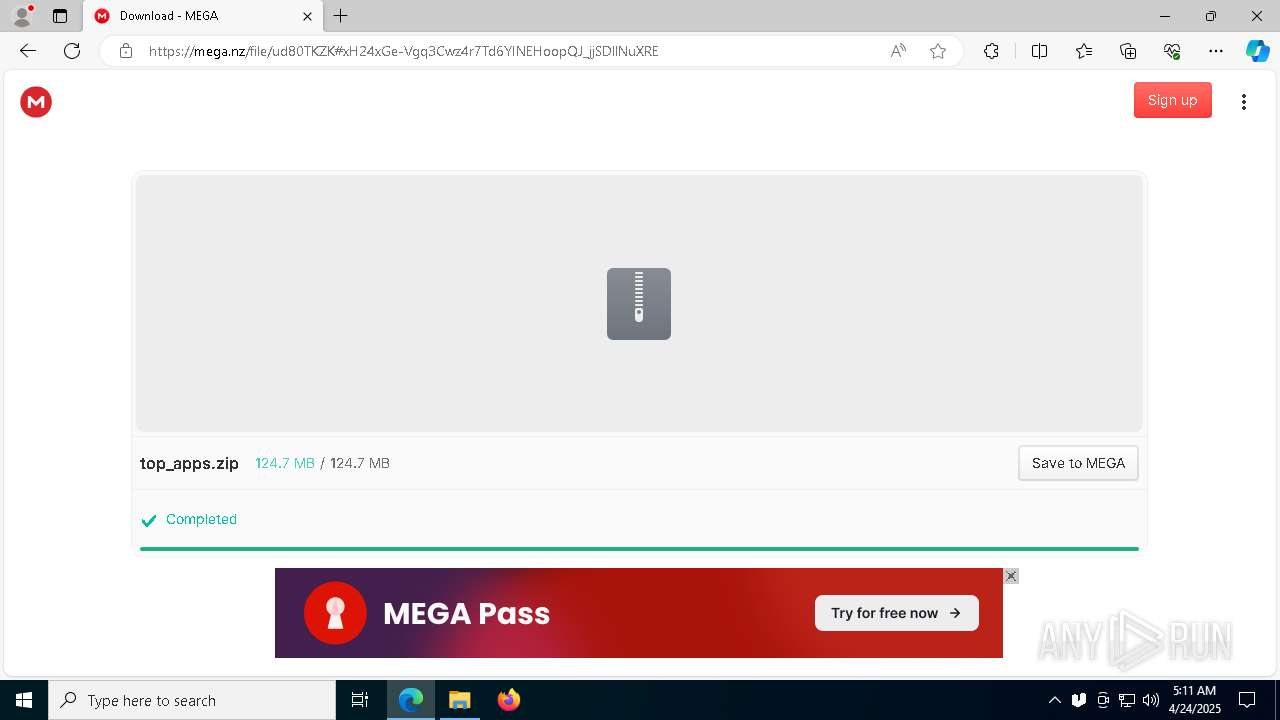
| URL: | https://apptrue.monster/indexk2.php?flow_id=104&click=1745721744778223366&source=1131696&keyword=Yourfile |
| Full analysis: | https://app.any.run/tasks/2463c986-eff5-471e-b738-fb604f6c2f34 |
| Verdict: | Malicious activity |
| Analysis date: | April 24, 2025, 05:08:47 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 5CFFDCAEBF8E36DCD778EB2EF7F07D4C |
| SHA1: | BB8B3966857BD90953E2AE3F69341352D6DE0027 |
| SHA256: | CF0842B3A02AFCDB364A99E180E7611F6A55896C97E43BFFEDAC7C645C66E2EB |
| SSDEEP: | 3:N8axQA8SVeJ0MB5m0QQkLR0SveXGAKqS55HDMO:2axe+MWQQxvnqS55wO |
MALICIOUS
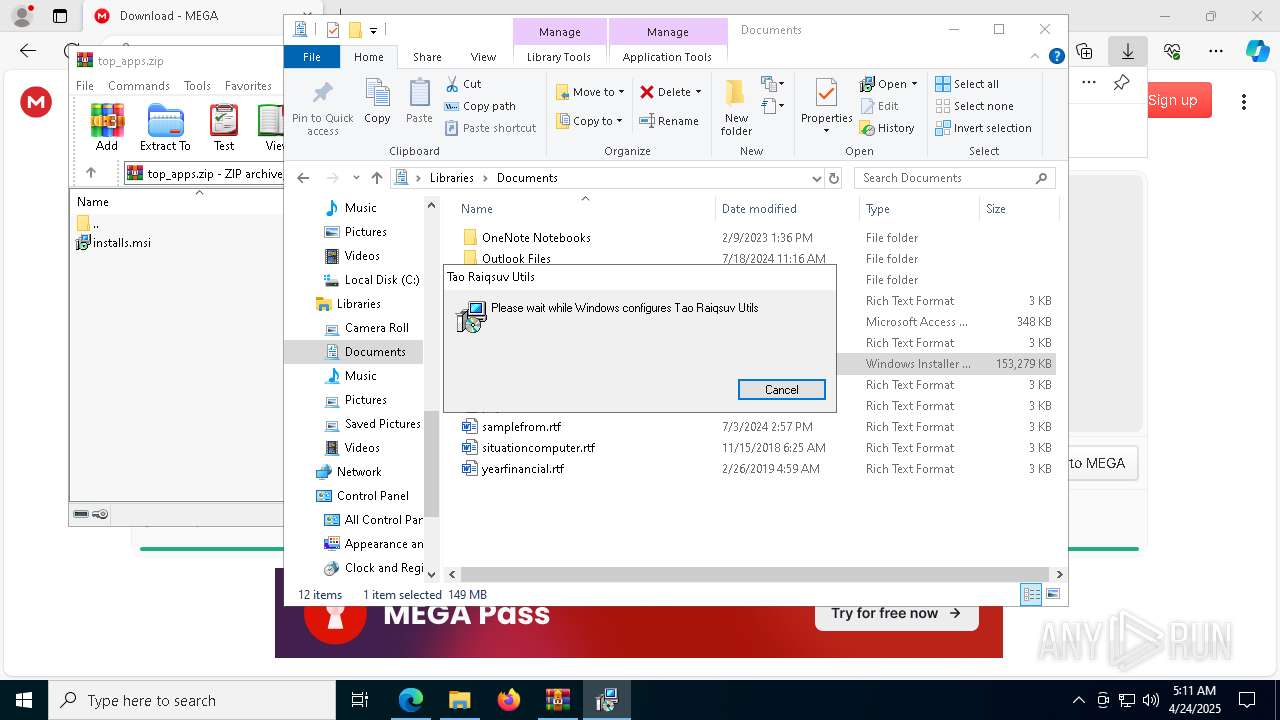
Changes the autorun value in the registry
- ueli.exe (PID: 1812)
Bypass execution policy to execute commands
- powershell.exe (PID: 6760)
Changes powershell execution policy (Bypass)
- ueli.exe (PID: 1812)
SUSPICIOUS
Checks for external IP
- svchost.exe (PID: 2196)
Reads the Windows owner or organization settings
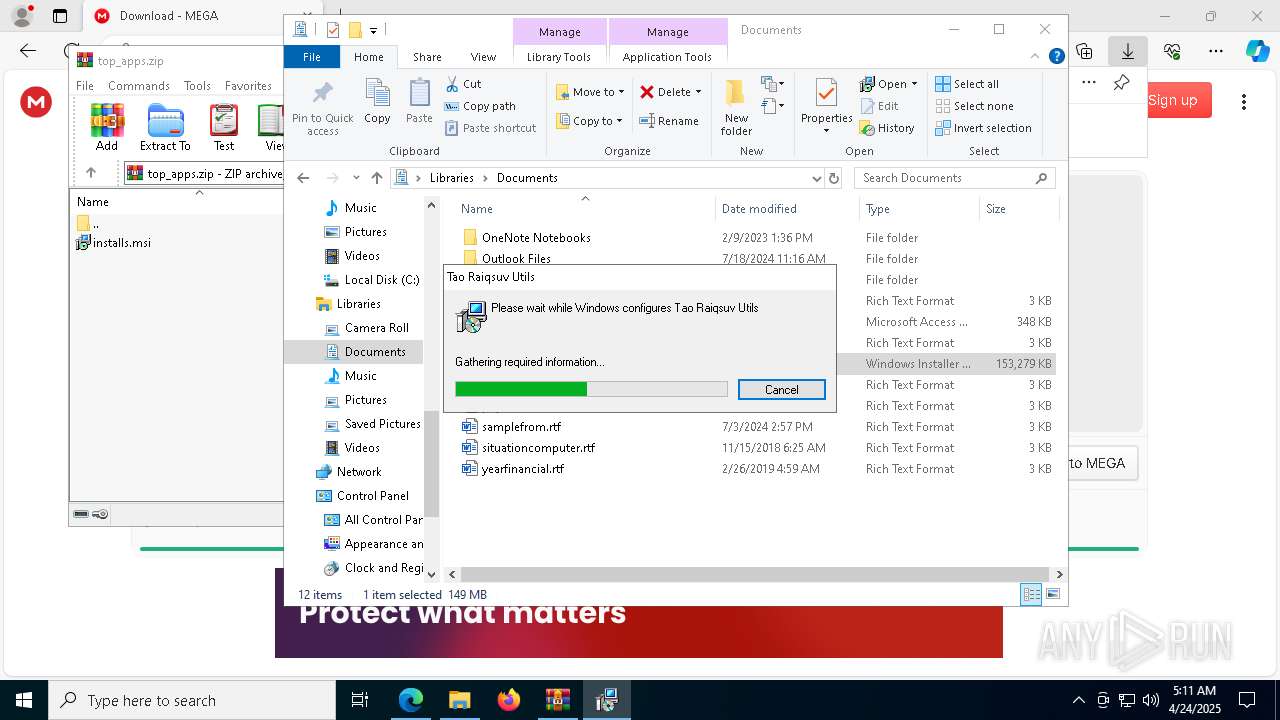
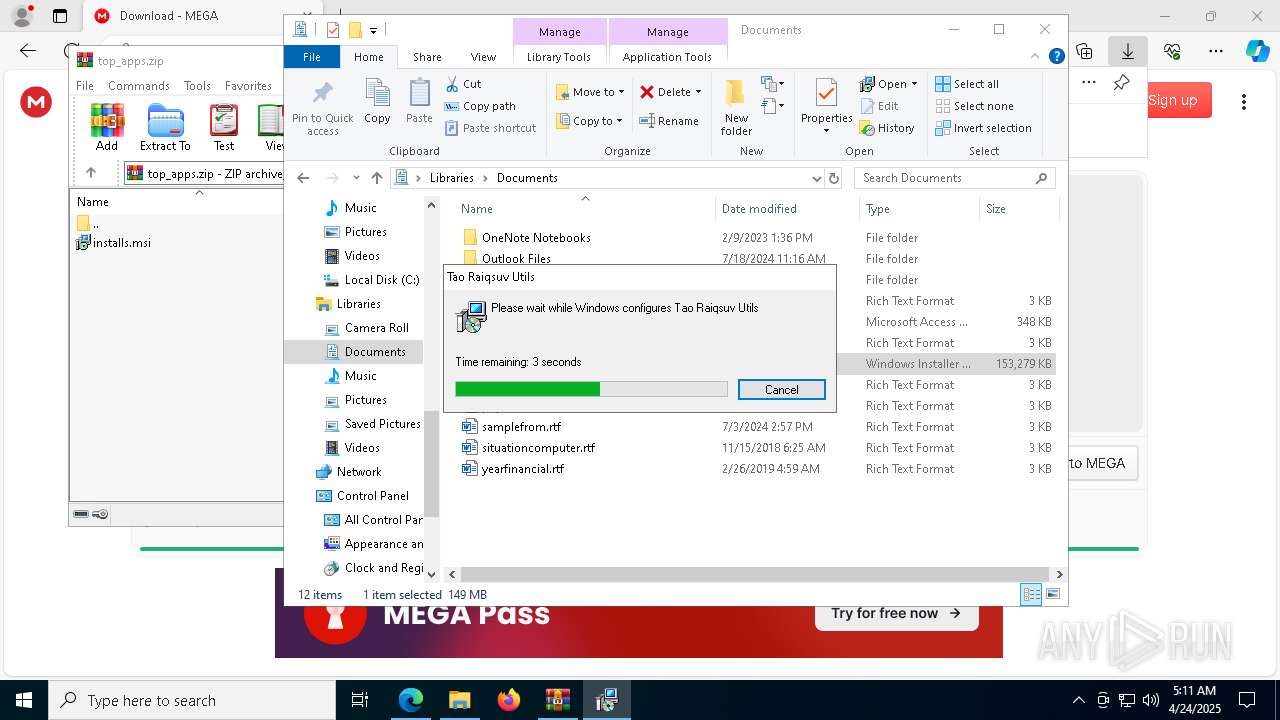
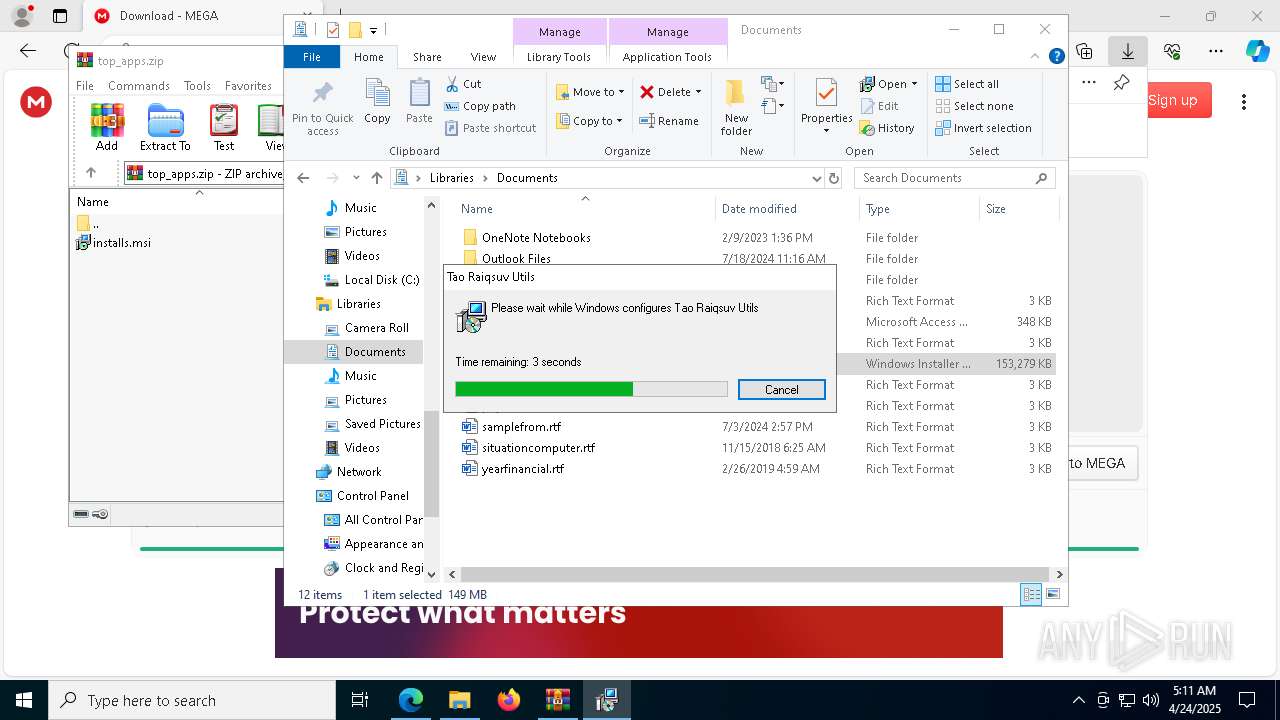
- msiexec.exe (PID: 4208)
Process drops legitimate windows executable
- msiexec.exe (PID: 4208)
Starts CMD.EXE for commands execution
- ueli.exe (PID: 1812)
Application launched itself
- ueli.exe (PID: 1812)
Starts POWERSHELL.EXE for commands execution
- ueli.exe (PID: 1812)
- cmd.exe (PID: 4844)
- cmd.exe (PID: 4620)
The process hide an interactive prompt from the user
- ueli.exe (PID: 1812)
- cmd.exe (PID: 4844)
- cmd.exe (PID: 4620)
The process bypasses the loading of PowerShell profile settings
- ueli.exe (PID: 1812)
- cmd.exe (PID: 4844)
- cmd.exe (PID: 4620)
Probably obfuscated PowerShell command line is found
- ueli.exe (PID: 1812)
Hides errors and continues executing the command without stopping
- powershell.exe (PID: 7752)
- powershell.exe (PID: 5044)
Returns all items found within a container (POWERSHELL)
- powershell.exe (PID: 7752)
- powershell.exe (PID: 7252)
- powershell.exe (PID: 5044)
Reads security settings of Internet Explorer
- msiexec.exe (PID: 5596)
- ueli.exe (PID: 5680)
The process hides Powershell's copyright startup banner
- ueli.exe (PID: 1812)
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 7752)
- powershell.exe (PID: 6760)
INFO
Application launched itself
- msedge.exe (PID: 7284)
- msedge.exe (PID: 3024)
Checks supported languages
- identity_helper.exe (PID: 5380)
- msiexec.exe (PID: 4208)
- msiexec.exe (PID: 5596)
- ueli.exe (PID: 1812)
- ueli.exe (PID: 8028)
- ueli.exe (PID: 6384)
- ueli.exe (PID: 1328)
- identity_helper.exe (PID: 8132)
- msiexec.exe (PID: 7672)
- ueli.exe (PID: 5680)
Reads the software policy settings
- slui.exe (PID: 780)
- slui.exe (PID: 5020)
- ueli.exe (PID: 5680)
Reads Environment values
- identity_helper.exe (PID: 5380)
- msiexec.exe (PID: 5596)
- ueli.exe (PID: 1812)
- ueli.exe (PID: 1328)
- identity_helper.exe (PID: 8132)
- msiexec.exe (PID: 7672)
- ueli.exe (PID: 5680)
Reads the computer name
- identity_helper.exe (PID: 5380)
- msiexec.exe (PID: 4208)
- msiexec.exe (PID: 5596)
- ueli.exe (PID: 1812)
- ueli.exe (PID: 8028)
- ueli.exe (PID: 6384)
- msiexec.exe (PID: 7672)
- identity_helper.exe (PID: 8132)
- ueli.exe (PID: 5680)
Reads Microsoft Office registry keys
- msedge.exe (PID: 7284)
Checks proxy server information
- slui.exe (PID: 5020)
- ueli.exe (PID: 1812)
- msiexec.exe (PID: 5596)
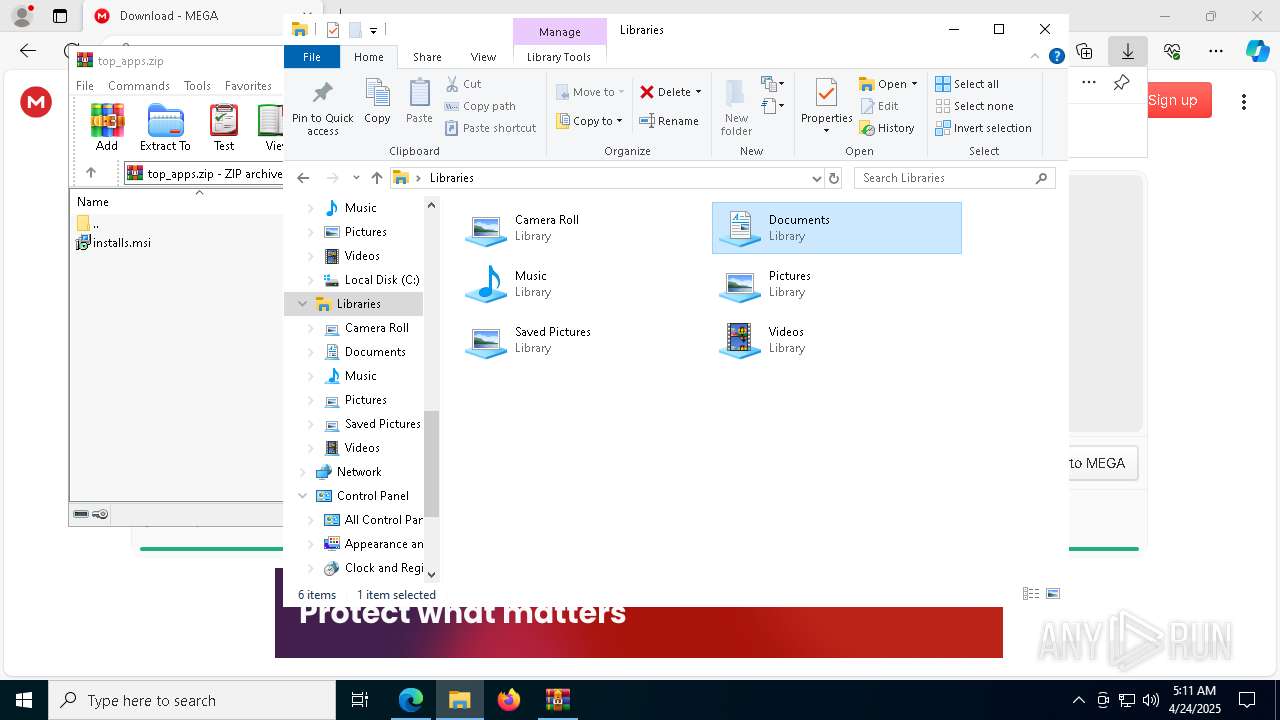
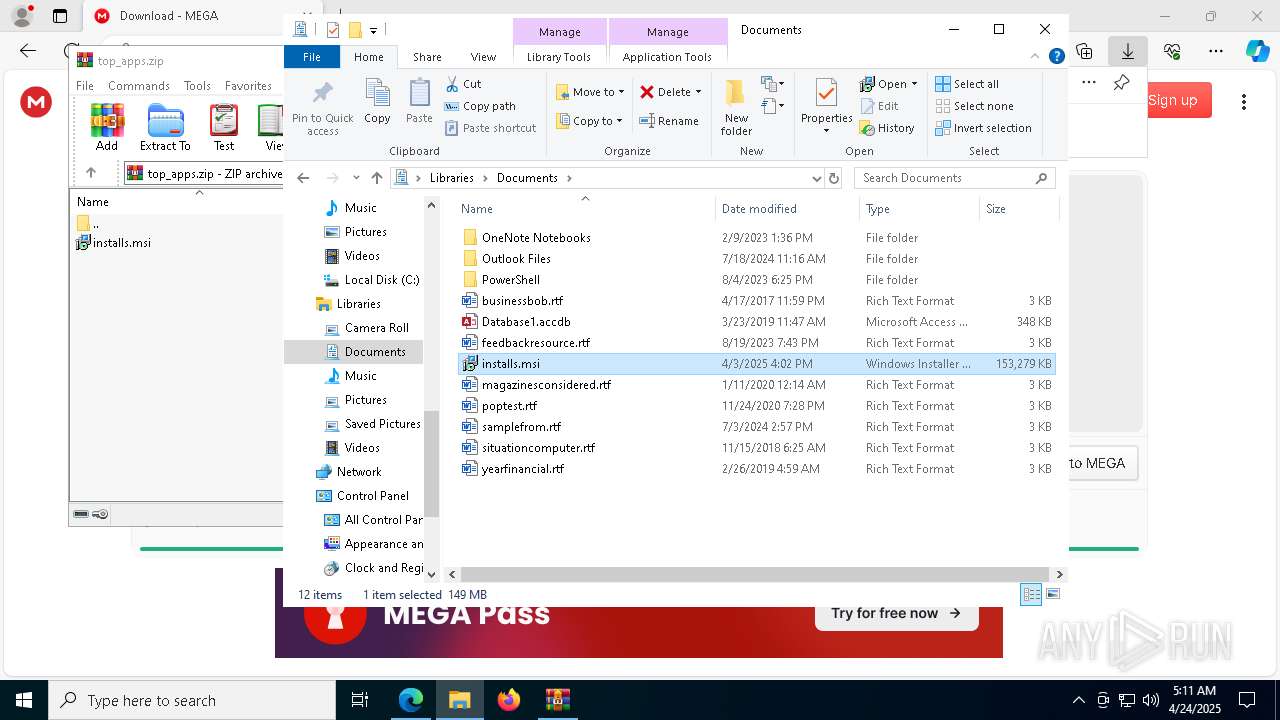
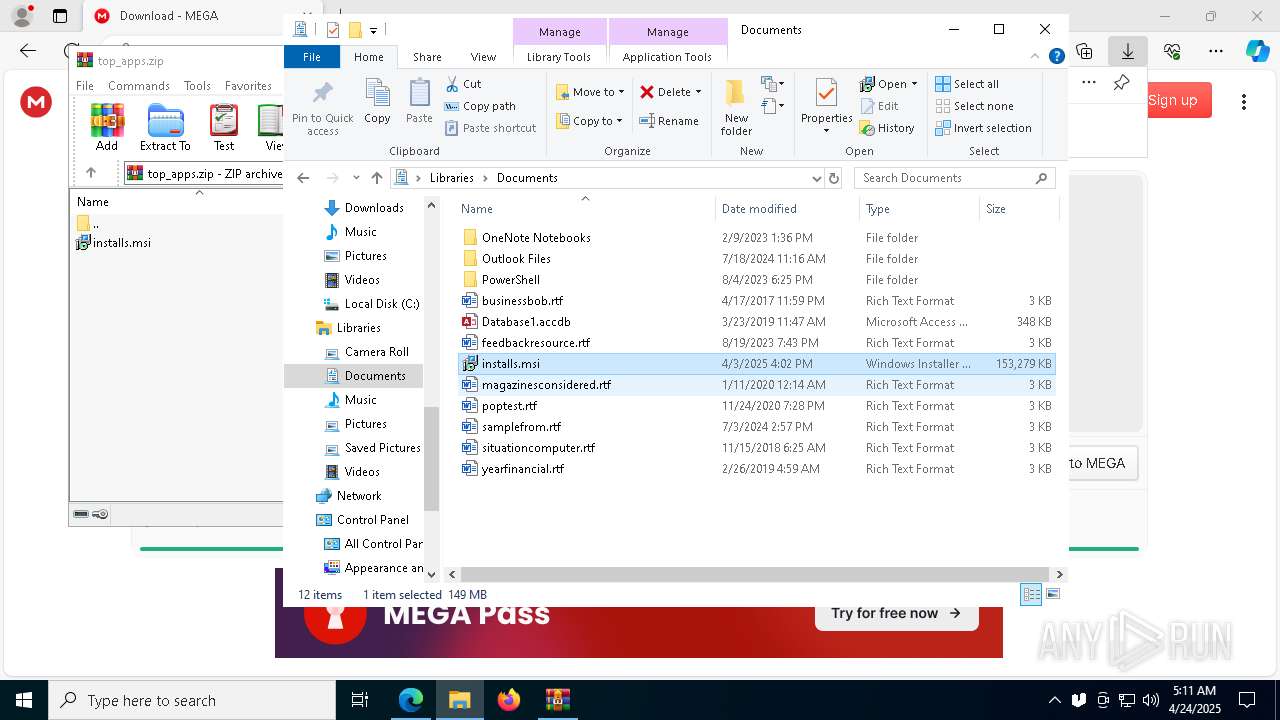
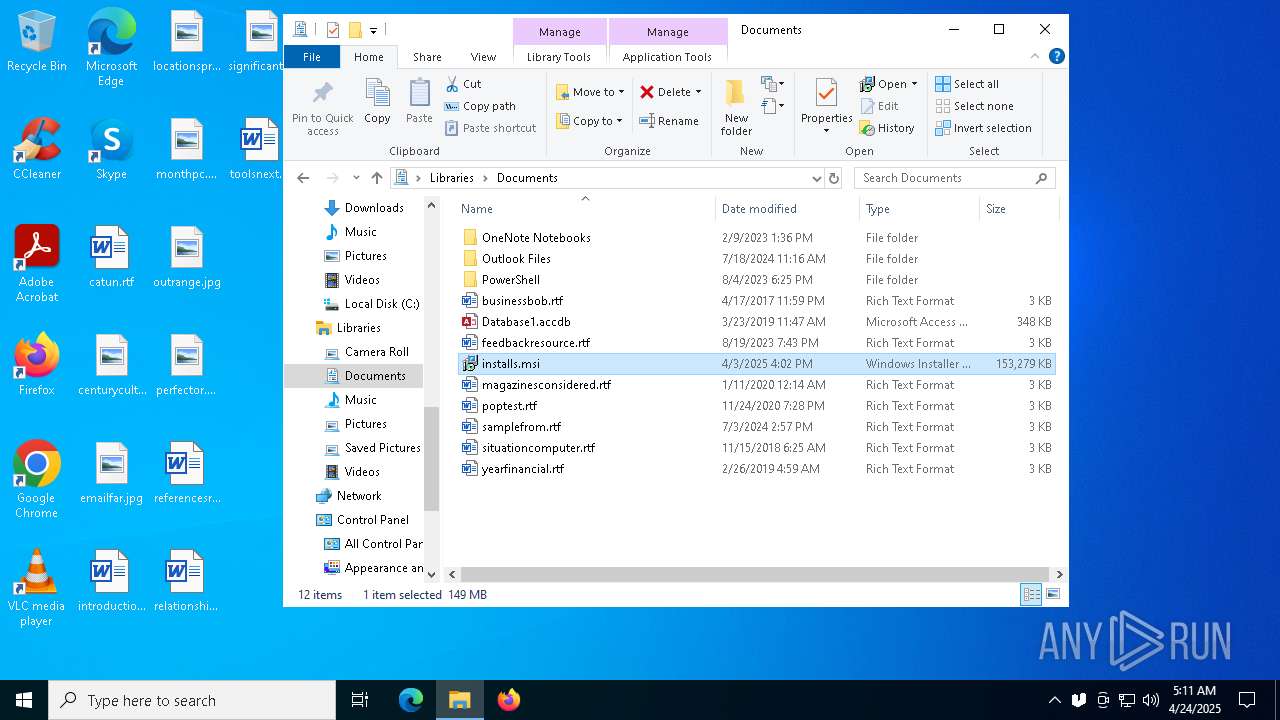
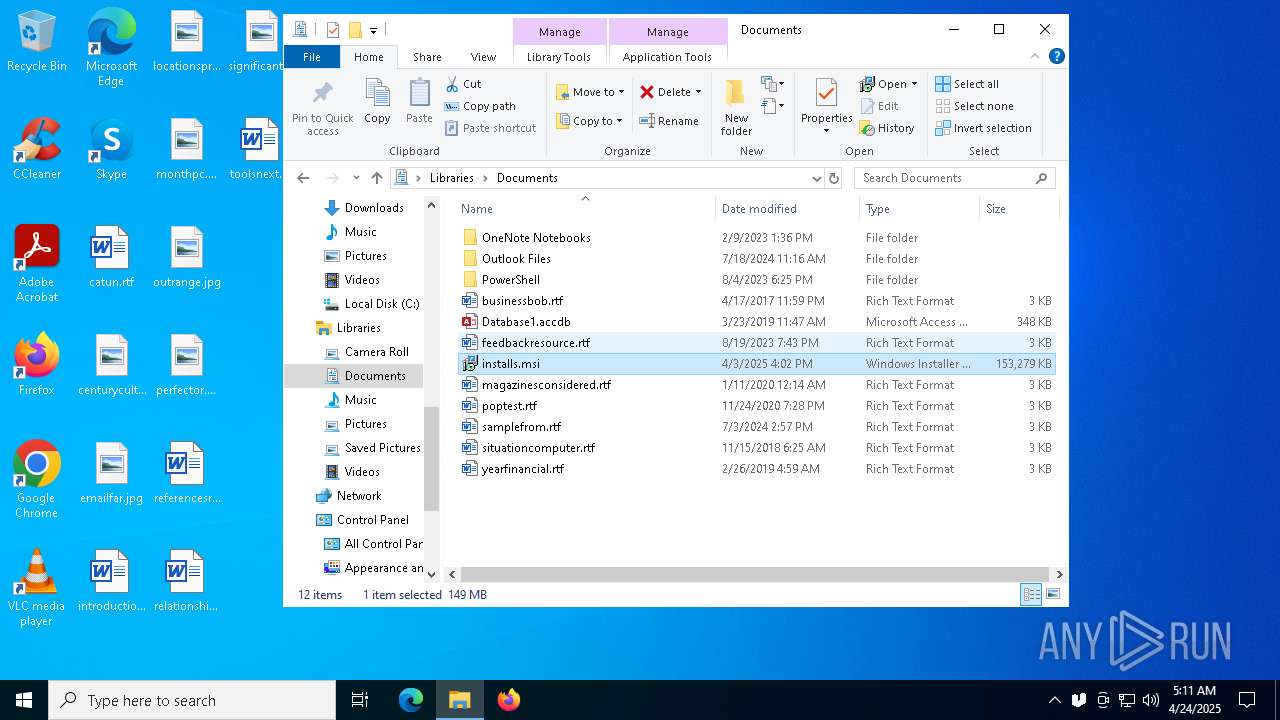
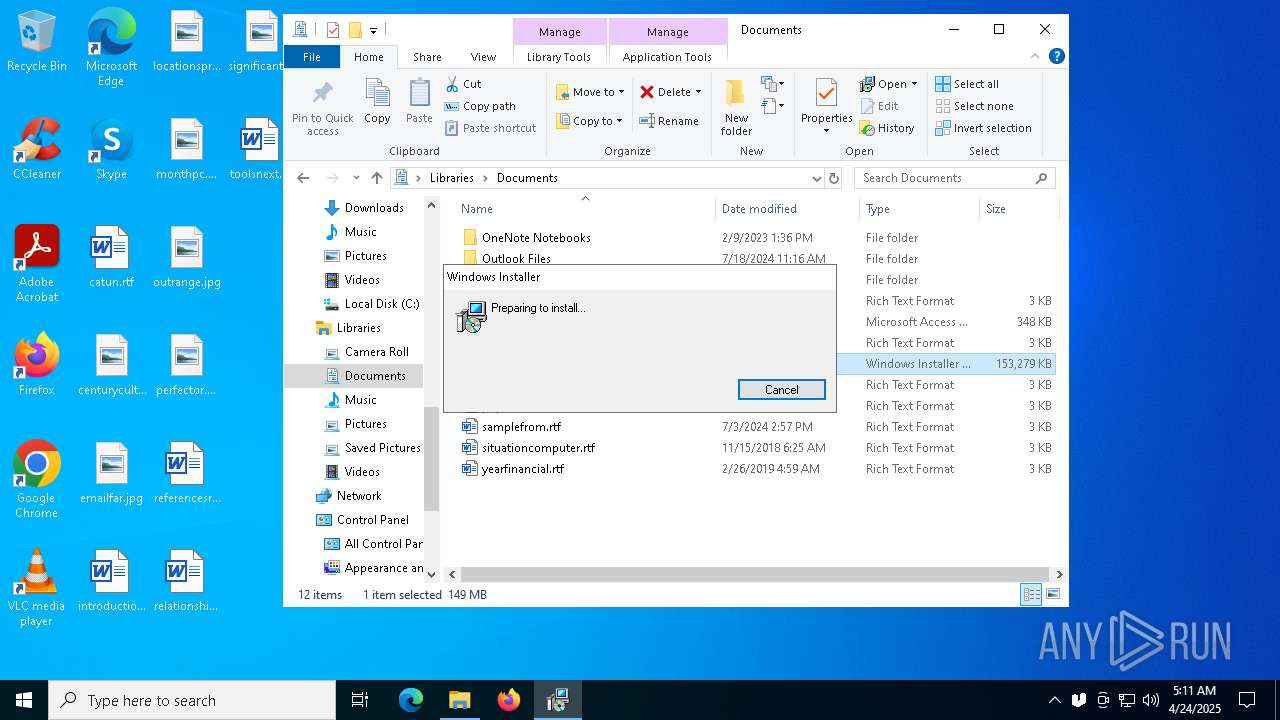
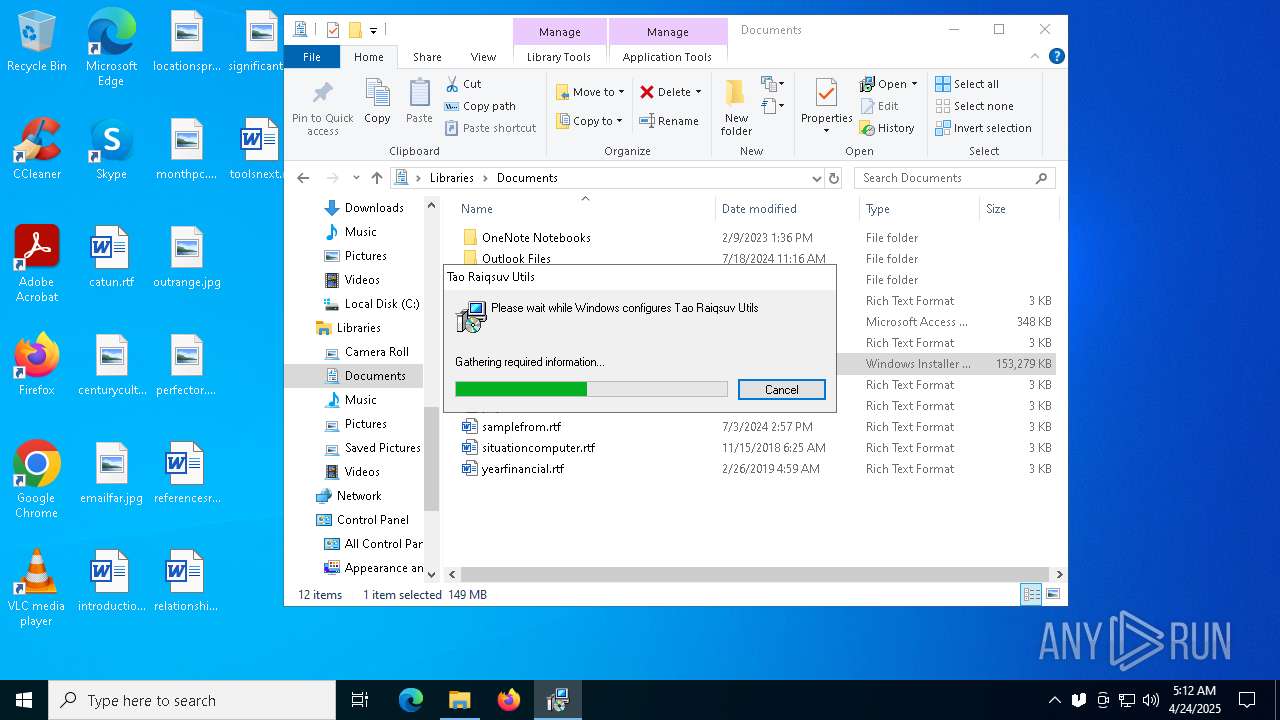
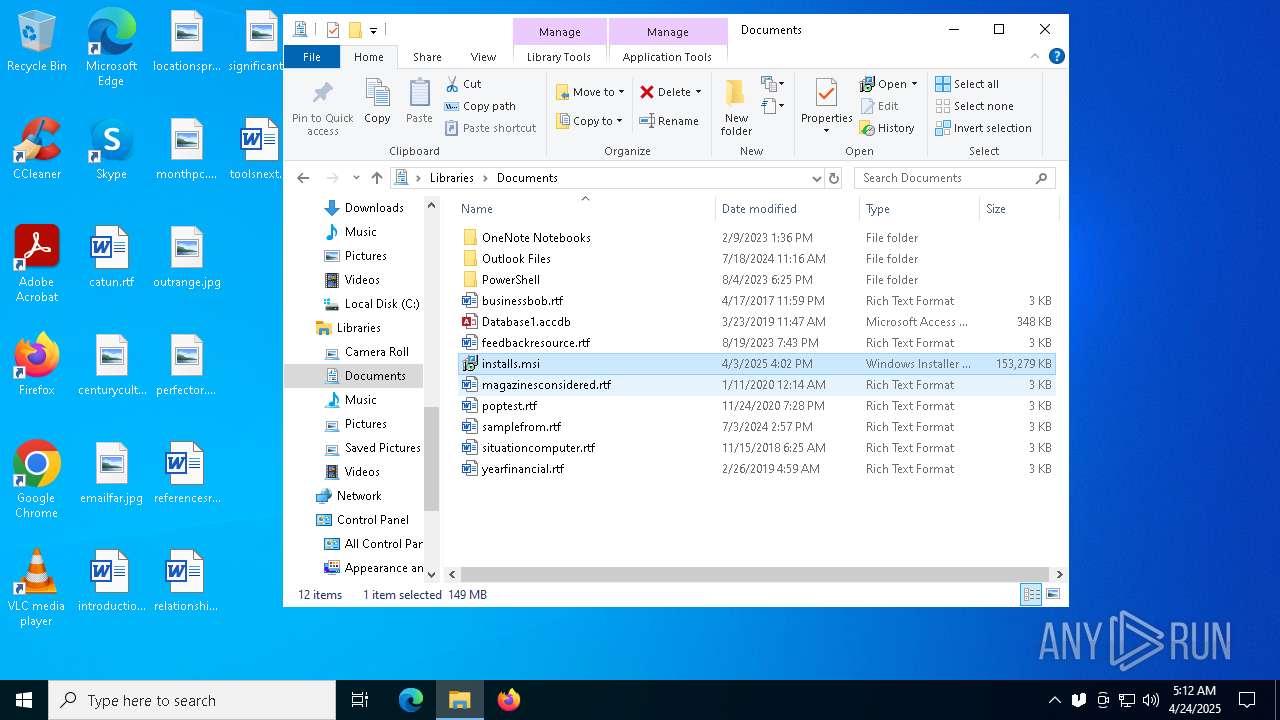
Manual execution by a user
- msiexec.exe (PID: 6824)
- msiexec.exe (PID: 7564)
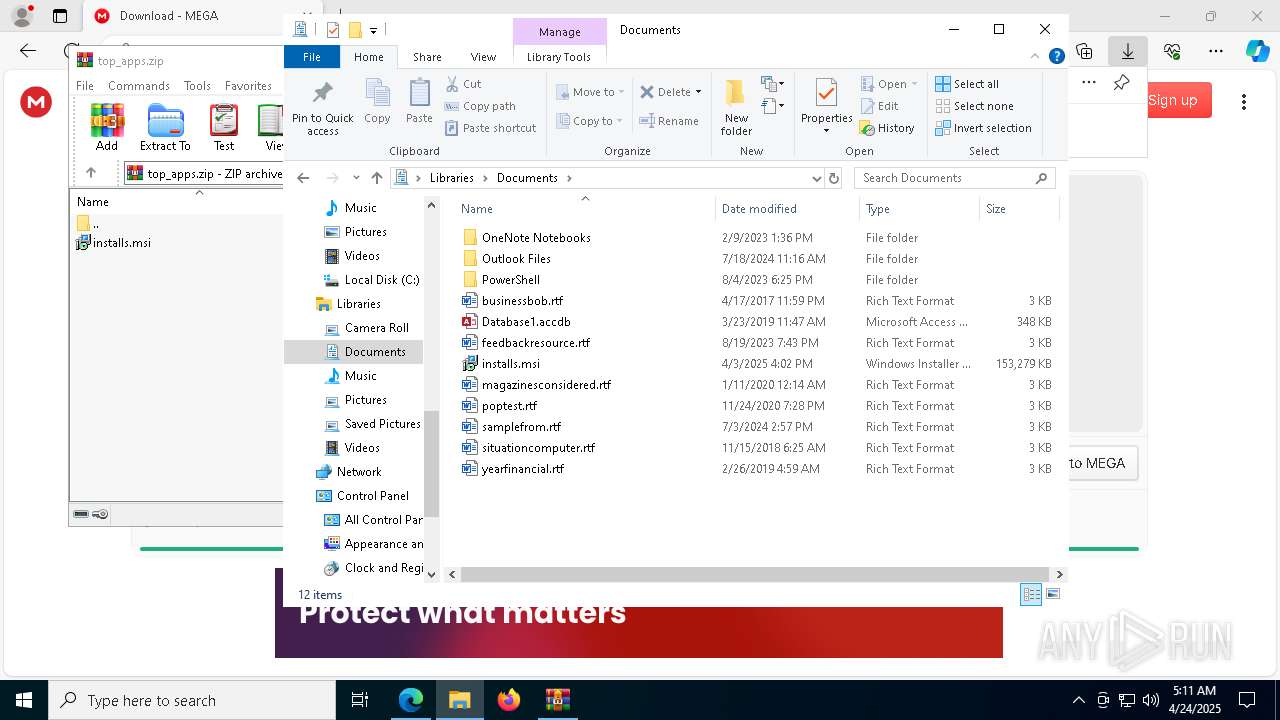
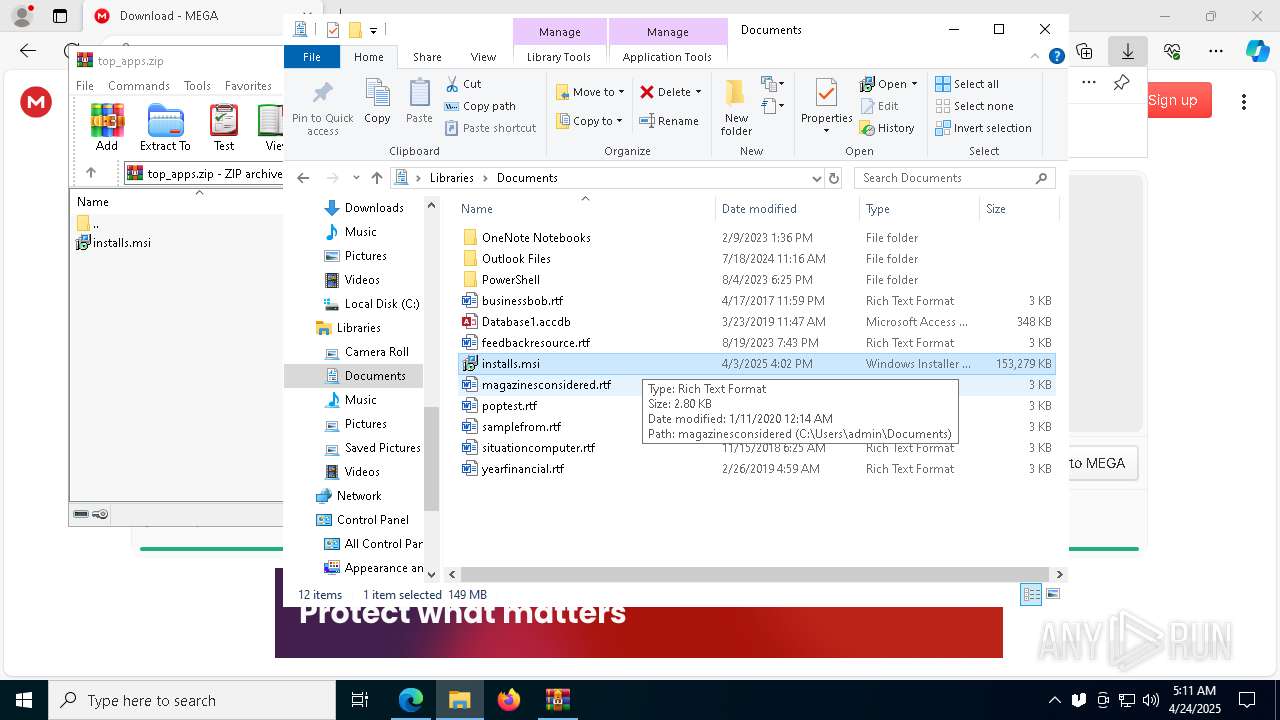
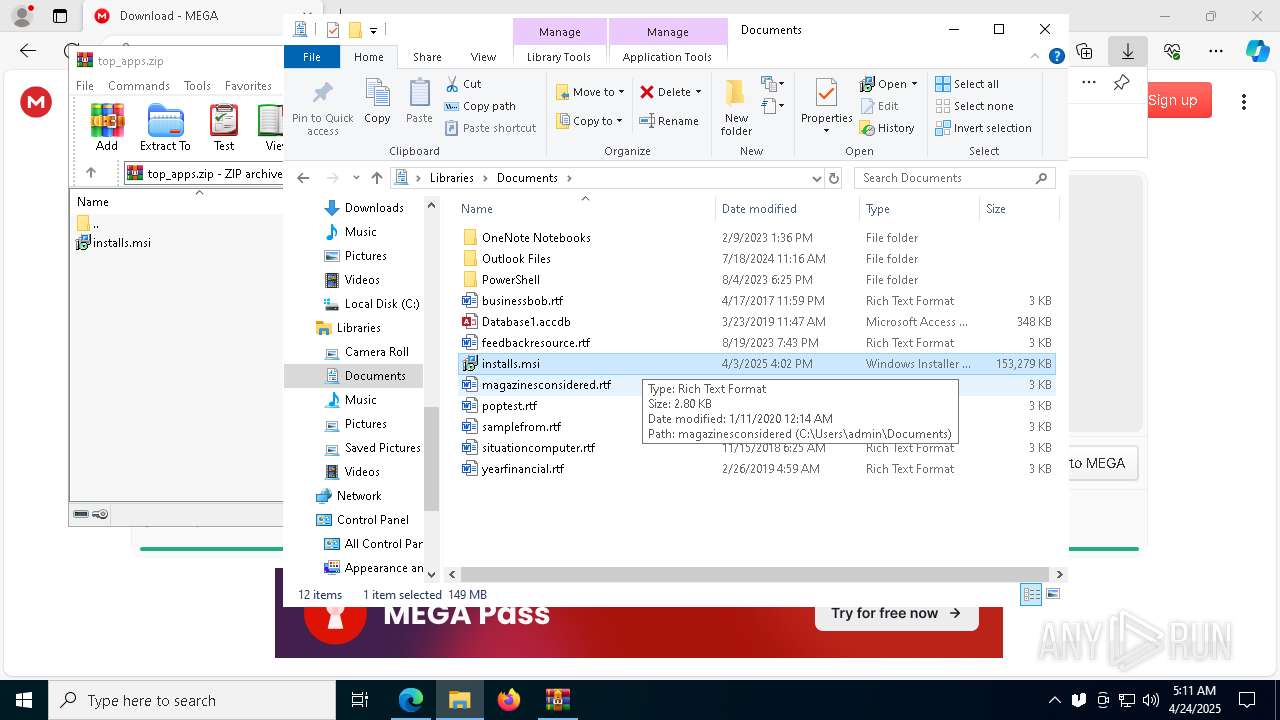
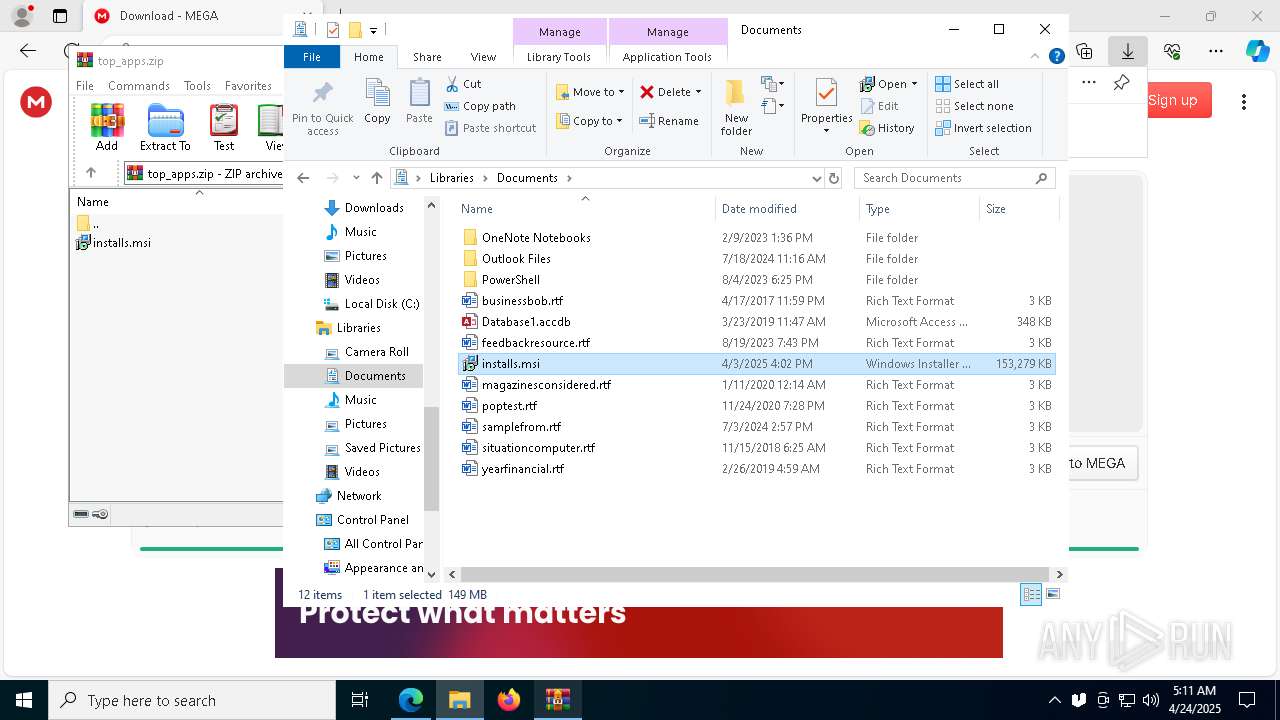
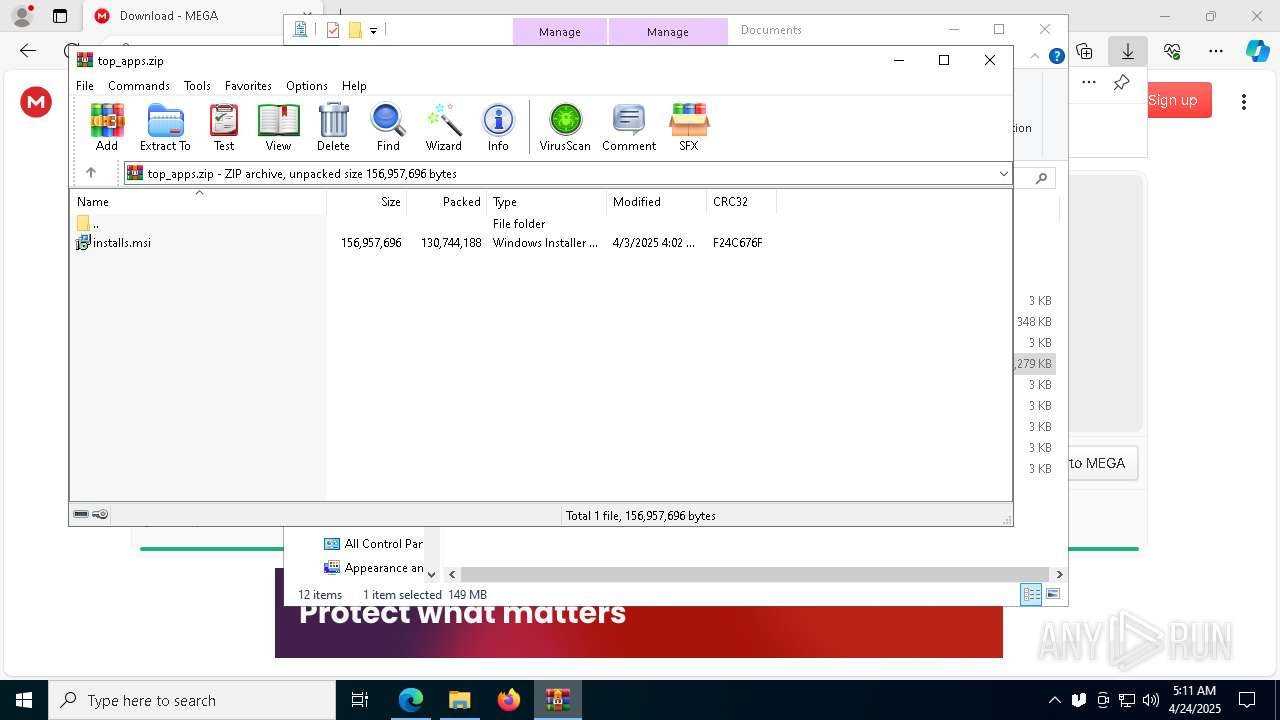
Executable content was dropped or overwritten
- msiexec.exe (PID: 4208)
Creates files or folders in the user directory
- msiexec.exe (PID: 4208)
- ueli.exe (PID: 1812)
- ueli.exe (PID: 6384)
- ueli.exe (PID: 5680)
Create files in a temporary directory
- ueli.exe (PID: 1812)
Creates a software uninstall entry
- msiexec.exe (PID: 4208)
Reads product name
- ueli.exe (PID: 1812)
- ueli.exe (PID: 1328)
Process checks computer location settings
- ueli.exe (PID: 1812)
- ueli.exe (PID: 1328)
The sample compiled with english language support
- msiexec.exe (PID: 4208)
Returns hidden items found within a container (POWERSHELL)
- ueli.exe (PID: 1328)
- conhost.exe (PID: 7800)
- conhost.exe (PID: 2064)
- conhost.exe (PID: 4784)
- conhost.exe (PID: 6416)
Returns all items recursively from all subfolders (POWERSHELL)
- cmd.exe (PID: 4620)
- powershell.exe (PID: 5044)
Reads the machine GUID from the registry
- ueli.exe (PID: 1812)
- ueli.exe (PID: 5680)
Checks whether the specified file exists (POWERSHELL)
- powershell.exe (PID: 7752)
Gets data length (POWERSHELL)
- powershell.exe (PID: 7252)
Uses string replace method (POWERSHELL)
- powershell.exe (PID: 7752)
Local mutex for internet shortcut management
- powershell.exe (PID: 6760)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
237
Monitored processes
98
Malicious processes
2
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 780 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | SppExtComObj.Exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 780 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=1304 --field-trial-handle=2236,i,5960564746738444555,8510589191855625567,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 812 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=asset_store.mojom.AssetStoreService --lang=en-US --service-sandbox-type=asset_store_service --no-appcompat-clear --mojo-platform-channel-handle=5824 --field-trial-handle=2196,i,10270894464828684092,385200930755738918,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 872 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=4968 --field-trial-handle=2236,i,5960564746738444555,8510589191855625567,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1012 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=4728 --field-trial-handle=2236,i,5960564746738444555,8510589191855625567,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1180 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5096 --field-trial-handle=2236,i,5960564746738444555,8510589191855625567,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1272 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) | |||||||||||||||
| 1328 | "C:\Users\admin\AppData\Roaming\RepairCang\Tao Raiqsuv Utils\ueli.exe" --type=renderer --user-data-dir="C:\Users\admin\AppData\Roaming\ueli" --app-path="C:\Users\admin\AppData\Roaming\RepairCang\Tao Raiqsuv Utils\resources\app.asar" --no-sandbox --no-zygote --first-renderer-process --force-color-profile=srgb --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=4 --mojo-platform-channel-handle=2400 --field-trial-handle=1728,i,6829312226487693572,17215137031775782071,262144 --enable-features=kWebSQLAccess --disable-features=SpareRendererForSitePerProcess,WinDelaySpellcheckServiceInit,WinRetrieveSuggestionsOnlyOnDemand --variations-seed-version /prefetch:1 | C:\Users\admin\AppData\Roaming\RepairCang\Tao Raiqsuv Utils\ueli.exe | — | ueli.exe | |||||||||||
User: admin Company: Oliver Schwendener Integrity Level: MEDIUM Description: ueli Version: 8.29.1 Modules
| |||||||||||||||
| 1600 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=788 --field-trial-handle=2196,i,10270894464828684092,385200930755738918,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1812 | "C:\Users\admin\AppData\Roaming\RepairCang\Tao Raiqsuv Utils\ueli.exe" | C:\Users\admin\AppData\Roaming\RepairCang\Tao Raiqsuv Utils\ueli.exe | msiexec.exe | ||||||||||||
User: admin Company: Oliver Schwendener Integrity Level: MEDIUM Description: ueli Version: 8.29.1 Modules
| |||||||||||||||
Total events
45 032
Read events
44 680
Write events
270
Delete events
82
Modification events
| (PID) Process: | (6040) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (6040) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (6040) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (6040) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (6040) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (6040) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | DisableFirstRunCustomize |
Value: 1 | |||
| (PID) Process: | (7284) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (7284) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (7284) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (7284) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
Executable files
29
Suspicious files
650
Text files
261
Unknown types
2
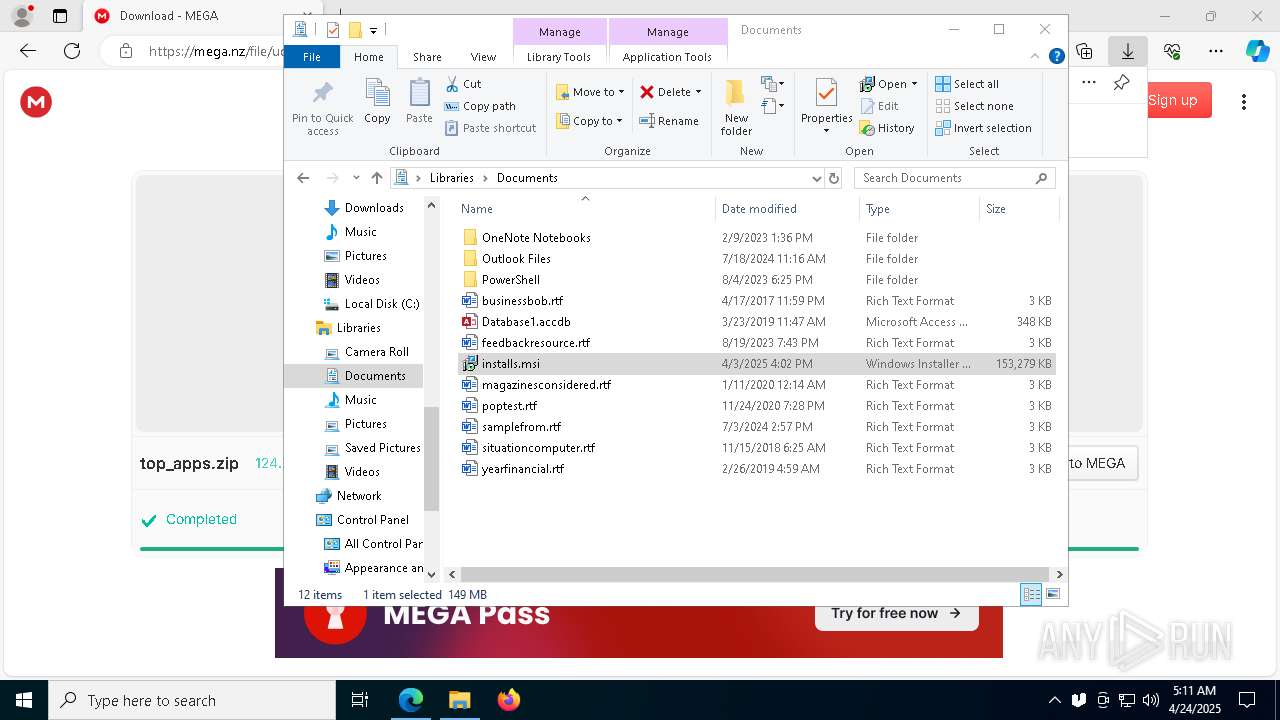
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7284 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10b836.TMP | — | |
MD5:— | SHA256:— | |||
| 7284 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7284 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10b836.TMP | — | |
MD5:— | SHA256:— | |||
| 7284 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7284 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10b846.TMP | — | |
MD5:— | SHA256:— | |||
| 7284 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10b846.TMP | — | |
MD5:— | SHA256:— | |||
| 7284 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7284 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7284 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10b846.TMP | — | |
MD5:— | SHA256:— | |||
| 7284 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
47
TCP/UDP connections
117
DNS requests
162
Threats
36
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3140 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
3140 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7420 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/a575cead-e662-4f4d-b0c3-81f1438d0388?P1=1746054379&P2=404&P3=2&P4=AjqRpMZUud%2f8N%2fwCTpcF%2bfpNImPgn9YW4nJNaAYADnNKIAmlTYAgI54KKhQ1kOFJ0wUWGAJ65o5QGgmBzUKrBg%3d%3d | unknown | — | — | whitelisted |
7420 | svchost.exe | HEAD | 200 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/a575cead-e662-4f4d-b0c3-81f1438d0388?P1=1746054379&P2=404&P3=2&P4=AjqRpMZUud%2f8N%2fwCTpcF%2bfpNImPgn9YW4nJNaAYADnNKIAmlTYAgI54KKhQ1kOFJ0wUWGAJ65o5QGgmBzUKrBg%3d%3d | unknown | — | — | whitelisted |
7420 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/a575cead-e662-4f4d-b0c3-81f1438d0388?P1=1746054379&P2=404&P3=2&P4=AjqRpMZUud%2f8N%2fwCTpcF%2bfpNImPgn9YW4nJNaAYADnNKIAmlTYAgI54KKhQ1kOFJ0wUWGAJ65o5QGgmBzUKrBg%3d%3d | unknown | — | — | whitelisted |
7420 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/a575cead-e662-4f4d-b0c3-81f1438d0388?P1=1746054379&P2=404&P3=2&P4=AjqRpMZUud%2f8N%2fwCTpcF%2bfpNImPgn9YW4nJNaAYADnNKIAmlTYAgI54KKhQ1kOFJ0wUWGAJ65o5QGgmBzUKrBg%3d%3d | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
7420 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/a575cead-e662-4f4d-b0c3-81f1438d0388?P1=1746054379&P2=404&P3=2&P4=AjqRpMZUud%2f8N%2fwCTpcF%2bfpNImPgn9YW4nJNaAYADnNKIAmlTYAgI54KKhQ1kOFJ0wUWGAJ65o5QGgmBzUKrBg%3d%3d | unknown | — | — | whitelisted |
7420 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/a575cead-e662-4f4d-b0c3-81f1438d0388?P1=1746054379&P2=404&P3=2&P4=AjqRpMZUud%2f8N%2fwCTpcF%2bfpNImPgn9YW4nJNaAYADnNKIAmlTYAgI54KKhQ1kOFJ0wUWGAJ65o5QGgmBzUKrBg%3d%3d | unknown | — | — | whitelisted |
7420 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/a575cead-e662-4f4d-b0c3-81f1438d0388?P1=1746054379&P2=404&P3=2&P4=AjqRpMZUud%2f8N%2fwCTpcF%2bfpNImPgn9YW4nJNaAYADnNKIAmlTYAgI54KKhQ1kOFJ0wUWGAJ65o5QGgmBzUKrBg%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2104 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.16.164.106:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.23.246.101:80 | www.microsoft.com | Ooredoo Q.S.C. | QA | whitelisted |
— | — | 2.23.246.101:80 | www.microsoft.com | Ooredoo Q.S.C. | QA | whitelisted |
5496 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 239.255.255.250:1900 | — | — | — | whitelisted |
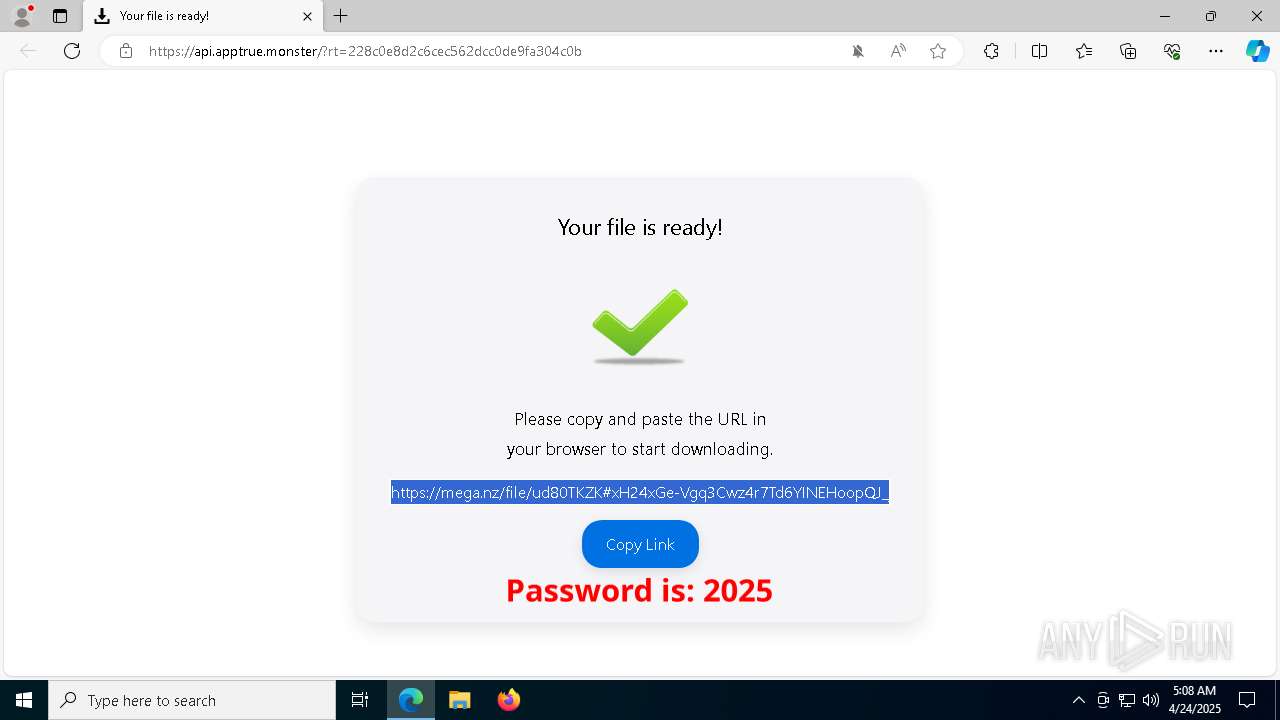
7520 | msedge.exe | 188.114.96.3:443 | apptrue.monster | — | — | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
apptrue.monster |
| unknown |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
business.bing.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
bzib.nelreports.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7520 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] jQuery JavaScript Library Code Loaded (code .jquery .com) |
7520 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] jQuery JavaScript Library Code Loaded (code .jquery .com) |
7520 | msedge.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup Domain in DNS Lookup (ident .me) |
7520 | msedge.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup Domain in DNS Lookup (ident .me) |
7520 | msedge.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup Domain in DNS Lookup (ident .me) |
7520 | msedge.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup Domain in DNS Lookup (ident .me) |
7520 | msedge.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup Domain in DNS Lookup (ident .me) |
7520 | msedge.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup Domain in DNS Lookup (ident .me) |
2196 | svchost.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup Domain in DNS Lookup (ident .me) |
7520 | msedge.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup Domain in DNS Lookup (ident .me) |