| File name: | com-happymod-apk-225-66584197-d3a335299a9c321986473a108f1deaeb.apk |
| Full analysis: | https://app.any.run/tasks/afab4221-9c7f-4eea-88f4-b5708ff1fc1e |
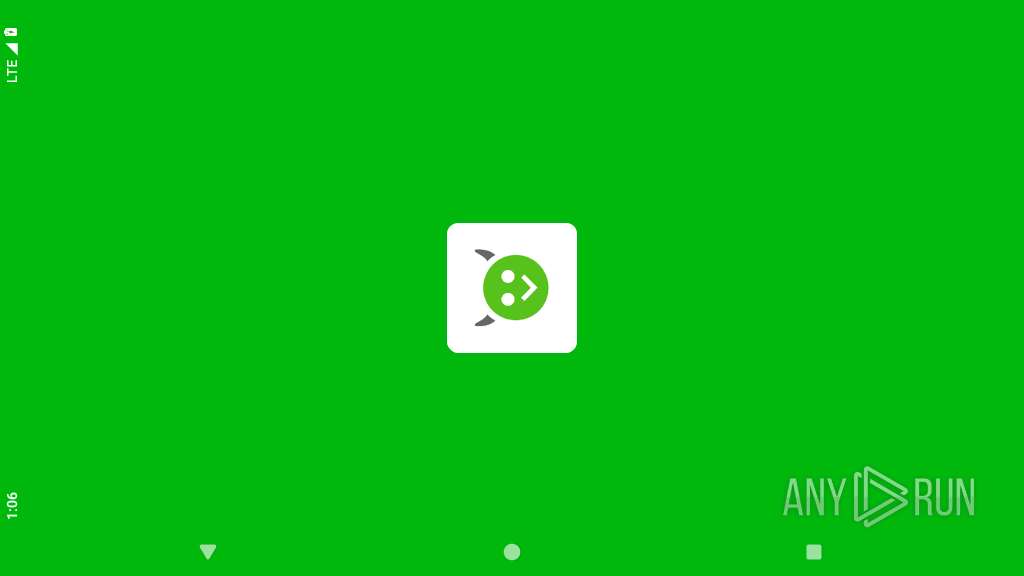
| Verdict: | Malicious activity |
| Analysis date: | July 19, 2025, 13:06:35 |
| OS: | Android 14 |
| MIME: | application/vnd.android.package-archive |
| File info: | Android package (APK), with gradle app-metadata.properties |
| MD5: | D3A335299A9C321986473A108F1DEAEB |
| SHA1: | 5A3D836B6AA9DF8AED47B06AE128B2CD74FA9166 |
| SHA256: | CEFD05599ADF739D010FD39224AD59868A6E6E04AB0D46D01D89E36FDE9C0A3D |
| SSDEEP: | 98304:+Dh9RqCFPZ4peTl7bAhNSJrOrvVJagy7mu3eGbAdVsz1BErCSB1OrclvxCDsOazP:KLtLiPO5W96qJ4FmQ5usu |
MALICIOUS
Checks whether the screen is currently on
- app_process32 (PID: 2475)
SUSPICIOUS
Updates data in the storage of application settings (SharedPreferences)
- app_process32 (PID: 2285)
- app_process32 (PID: 2475)
- app_process32 (PID: 2382)
Retrieves a list of running application processes
- app_process32 (PID: 2285)
- app_process32 (PID: 2475)
- app_process32 (PID: 2382)
Accesses external device storage files
- app_process32 (PID: 2285)
- app_process32 (PID: 2382)
- app_process32 (PID: 2475)
Collects data about the device's environment (JVM version)
- app_process32 (PID: 2285)
- app_process32 (PID: 2382)
- app_process32 (PID: 2475)
Abuses foreground service for persistence
- app_process32 (PID: 2382)
- app_process32 (PID: 2475)
INFO
Loads a native library into the application
- app_process32 (PID: 2285)
- app_process32 (PID: 2382)
- app_process32 (PID: 2475)
Dynamically inspects or modifies classes, methods, and fields at runtime
- app_process32 (PID: 2285)
- app_process32 (PID: 2382)
- app_process32 (PID: 2475)
Dynamically registers broadcast event listeners
- app_process32 (PID: 2285)
- app_process32 (PID: 2475)
- app_process32 (PID: 2382)
Gets the display metrics associated with the device's screen
- app_process32 (PID: 2285)
- app_process32 (PID: 2382)
- app_process32 (PID: 2475)
Retrieves data from storage of application settings (SharedPreferences)
- app_process32 (PID: 2285)
- app_process32 (PID: 2382)
- app_process32 (PID: 2475)
Verifies whether the device is connected to the internet
- app_process32 (PID: 2285)
- app_process32 (PID: 2475)
- app_process32 (PID: 2382)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .apk | | | Android Package (60.3) |
|---|---|---|
| .jar | | | Java Archive (16.6) |
| .widget | | | Konfabulator widget (9.1) |
| .xpi | | | Mozilla Firefox browser extension (9.1) |
| .zip | | | ZIP compressed archive (4.5) |
EXIF
ZIP
| ZipRequiredVersion: | - |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 1981:01:01 01:01:02 |
| ZipCRC: | 0xd1f06b7f |
| ZipCompressedSize: | 52 |
| ZipUncompressedSize: | 56 |
| ZipFileName: | META-INF/com/android/build/gradle/app-metadata.properties |
Total processes
136
Monitored processes
11
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
| 2285 | <pre-initialized> | /system/bin/app_process32 | app_process32 | |
User: root Integrity Level: UNKNOWN Exit code: 11 | ||||
| 2359 | crash_dump32 2305 2358 4 | /apex/com.android.runtime/bin/crash_dump32 | — | app_process32 |
User: u0_a108 Integrity Level: UNKNOWN Exit code: 0 | ||||
| 2360 | crash_dump32 2305 2358 4 | /apex/com.android.runtime/bin/crash_dump32 | — | crash_dump32 |
User: u0_a108 Integrity Level: UNKNOWN Exit code: 0 | ||||
| 2372 | com.happymod.apk | /system/bin/app_process32 | — | app_process32 |
User: u0_a108 Integrity Level: UNKNOWN Exit code: 0 | ||||
| 2373 | com.happymod.apk | /system/bin/app_process32 | — | app_process32 |
User: u0_a108 Integrity Level: UNKNOWN Exit code: 0 | ||||
| 2382 | com.happymod.apk | /system/bin/app_process32 | app_process32 | |
User: root Integrity Level: UNKNOWN Exit code: 11 | ||||
| 2447 | crash_dump32 2402 2446 4 | /apex/com.android.runtime/bin/crash_dump32 | — | app_process32 |
User: u0_a108 Integrity Level: UNKNOWN Exit code: 0 | ||||
| 2451 | crash_dump32 2402 2446 4 | /apex/com.android.runtime/bin/crash_dump32 | — | crash_dump32 |
User: u0_a108 Integrity Level: UNKNOWN Exit code: 0 | ||||
| 2463 | com.happymod.apk | /system/bin/app_process32 | — | app_process32 |
User: u0_a108 Integrity Level: UNKNOWN Exit code: 0 | ||||
| 2464 | com.happymod.apk | /system/bin/app_process32 | — | app_process32 |
User: u0_a108 Integrity Level: UNKNOWN Exit code: 0 | ||||
Total events
0
Read events
0
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
44
Text files
18
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2285 | app_process32 | /data/data/com.happymod.apk/files/prodexdir/o0oooOO0ooOo.dat | binary | |
MD5:— | SHA256:— | |||
| 2285 | app_process32 | /data/data/com.happymod.apk/files/prodexdir/tosversion | binary | |
MD5:— | SHA256:— | |||
| 2285 | app_process32 | /data/data/com.happymod.apk/no_backup/.flurryNoBackup/installationNum | compressed | |
MD5:— | SHA256:— | |||
| 2285 | app_process32 | /data/data/com.happymod.apk/shared_prefs/com.happymod.apk.v2.playerprefs.xml | xml | |
MD5:— | SHA256:— | |||
| 2285 | app_process32 | /data/data/com.happymod.apk/shared_prefs/unityads-installinfo.xml | xml | |
MD5:— | SHA256:— | |||
| 2285 | app_process32 | /data/data/com.happymod.apk/no_backup/androidx.work.workdb-journal | binary | |
MD5:— | SHA256:— | |||
| 2285 | app_process32 | /data/data/com.happymod.apk/no_backup/androidx.work.workdb-wal | binary | |
MD5:— | SHA256:— | |||
| 2285 | app_process32 | /data/data/com.happymod.apk/no_backup/androidx.work.workdb | binary | |
MD5:— | SHA256:— | |||
| 2285 | app_process32 | /data/data/com.happymod.apk/no_backup/androidx.work.workdb-shm | binary | |
MD5:— | SHA256:— | |||
| 2285 | app_process32 | /storage/emulated/0/Android/data/com.happymod.apk/files/mb/res/.mbridge700/mb/config/share_date.kva | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
40
DNS requests
12
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 204 | 216.58.206.68:443 | https://www.google.com/generate_204 | US | — | — | unknown |
— | — | GET | 204 | 216.58.206.68:80 | http://www.google.com/gen_204 | US | — | — | whitelisted |
— | — | GET | 204 | 216.58.206.67:80 | http://connectivitycheck.gstatic.com/generate_204 | US | — | — | whitelisted |
— | — | GET | 204 | 216.58.206.67:80 | http://connectivitycheck.gstatic.com/generate_204 | US | — | — | whitelisted |
— | — | GET | 200 | 18.245.86.74:443 | https://configure.rayjump.com/setting?app_id=107909&sign=144dd95958835a2925357b1decc09114&vtag=&open=0&channel=&band_width=0&platform=1&os_version=14&package_name=com.happymod.apk&app_version_name=3.0.7&app_version_code=225&orientation=2&model=Xperia_1&brand=sony&gaid=&gaid2=&network_type=0&network_str=&language=en-US&timezone=UTC&useragent=Mozilla%2F5.0+%28Linux%3B+Android+14%3B+Xperia_1+Build%2F%29+AppleWebKit%2F535.19+%28KHTML%2C+like+Gecko%29+Chrome%2F18.0.1025.133+Mobile+Safari%2F535.19&sdk_version=MAL_16.4.11&screen_size=1024x576&withGP=0&has_wx=0&integrated_wx=0&opensdk_ver=0&wx_api_ver=0&f=Cq%2FHvEgYIxbJ1wDxDn%2Fz0lWualRTPDjMKRHa%2FkUDEawp63sWuZgaQCcdbZ888uznuEDwxCdLzoUX%0A%2Bn1zm0TSqw%3D%3D%0A&ts=1752930411370&st=ab1076eb07842478b64052c6f62f587e | US | binary | 6.48 Kb | unknown |
— | — | POST | 200 | 66.102.1.81:443 | https://staging-remoteprovisioning.sandbox.googleapis.com/v1:fetchEekChain | US | binary | 699 b | whitelisted |
— | — | GET | 200 | 18.245.86.74:443 | https://configure.rayjump.com/setting?app_id=107909&sign=144dd95958835a2925357b1decc09114&vtag=&open=0&channel=&band_width=0&platform=1&os_version=14&package_name=com.happymod.apk&app_version_name=3.0.7&app_version_code=225&orientation=2&model=Xperia_1&brand=sony&gaid=&gaid2=&network_type=0&network_str=&language=en-US&timezone=UTC&useragent=Mozilla%2F5.0+%28Linux%3B+Android+14%3B+Xperia_1+Build%2F%29+AppleWebKit%2F535.19+%28KHTML%2C+like+Gecko%29+Chrome%2F18.0.1025.133+Mobile+Safari%2F535.19&sdk_version=MAL_16.4.11&screen_size=1024x576&withGP=0&has_wx=0&integrated_wx=0&opensdk_ver=0&wx_api_ver=0&f=Cq%2FHvEgYIxbJ1wDxDn%2Fz0lWualRTPDjMKRHa%2FkUDEawp63sWuZgaQCcdbZ888uznuEDwxCdLzoUX%0A%2Bn1zm0TSqw%3D%3D%0A&ts=1752930416363&st=6c5130a5e5ceaabe59dff08045eef16d | US | binary | 6.48 Kb | unknown |
— | — | GET | — | 13.32.121.89:443 | https://hybird.mtgglobals.com/lib/mraid_20220816.js?open=0&channel=&band_width=6110&ts=1752930417415&st=091081103326740a8514876d8a1aa015 | US | — | — | unknown |
— | — | GET | — | 3.160.150.75:443 | https://cdn-adn-https.mtgglobals.com/cdn-adn/v2/portal/21/08/31/14/23/612dcaeadd4b8.js?open=0&channel=&band_width=6110&ts=1752930417419&st=b1212b96e477aeb16db0dd9fee61d607 | US | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
445 | mdnsd | 224.0.0.251:5353 | — | — | — | unknown |
— | — | 216.58.206.68:443 | www.google.com | GOOGLE | US | whitelisted |
— | — | 216.58.206.67:80 | connectivitycheck.gstatic.com | GOOGLE | US | whitelisted |
— | — | 216.58.206.68:80 | www.google.com | GOOGLE | US | whitelisted |
1760 | app_process64 | 66.102.1.81:443 | staging-remoteprovisioning.sandbox.googleapis.com | GOOGLE | US | whitelisted |
574 | app_process64 | 216.239.35.4:123 | time.android.com | — | — | whitelisted |
2285 | app_process32 | 239.255.255.250:1900 | — | — | — | whitelisted |
2285 | app_process32 | 18.245.86.97:443 | configure.rayjump.com | — | US | unknown |
2285 | app_process32 | 67.215.246.10:6881 | router.bittorrent.com | — | — | whitelisted |
2285 | app_process32 | 185.157.221.247:25401 | dht.libtorrent.org | — | — | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.google.com |
| whitelisted |
connectivitycheck.gstatic.com |
| whitelisted |
google.com |
| whitelisted |
staging-remoteprovisioning.sandbox.googleapis.com |
| whitelisted |
time.android.com |
| whitelisted |
configure.rayjump.com |
| unknown |
dht.libtorrent.org |
| unknown |
router.bittorrent.com |
| whitelisted |
dht.transmissionbt.com |
| unknown |
router.silotis.us |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Misc activity | ET INFO Android Device Connectivity Check |
— | — | Misc activity | ET INFO Android Device Connectivity Check |