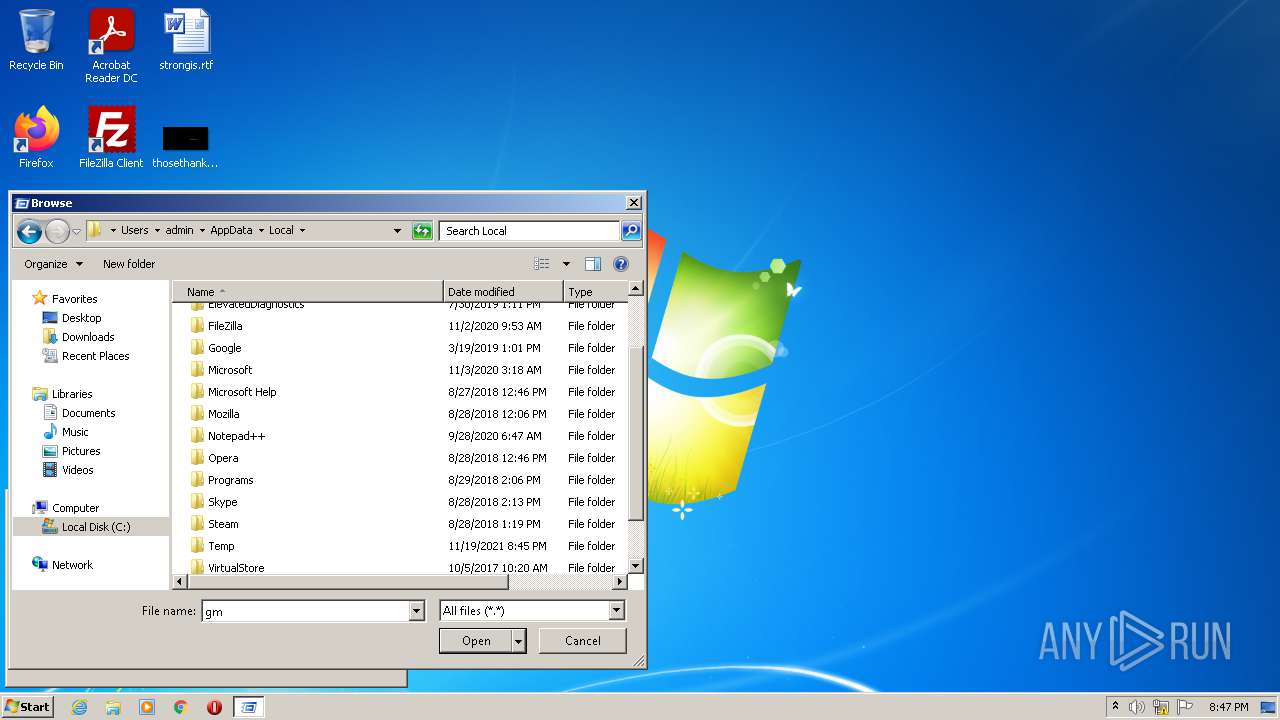
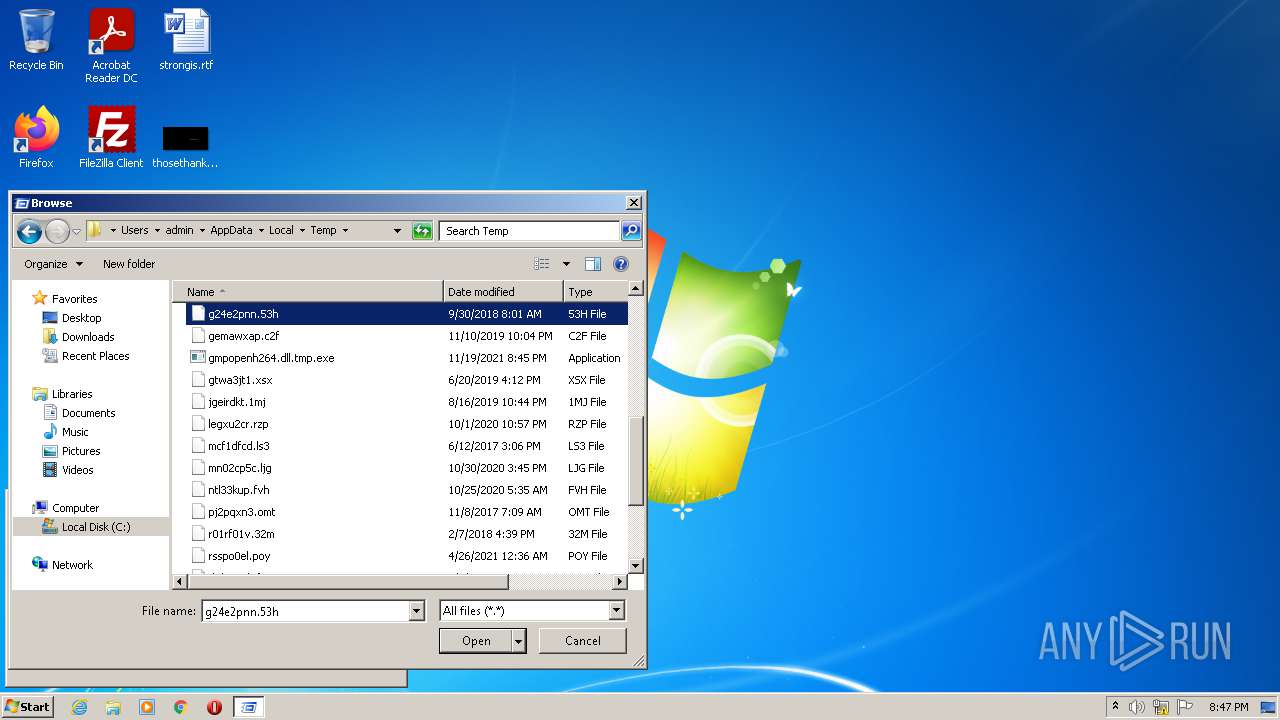
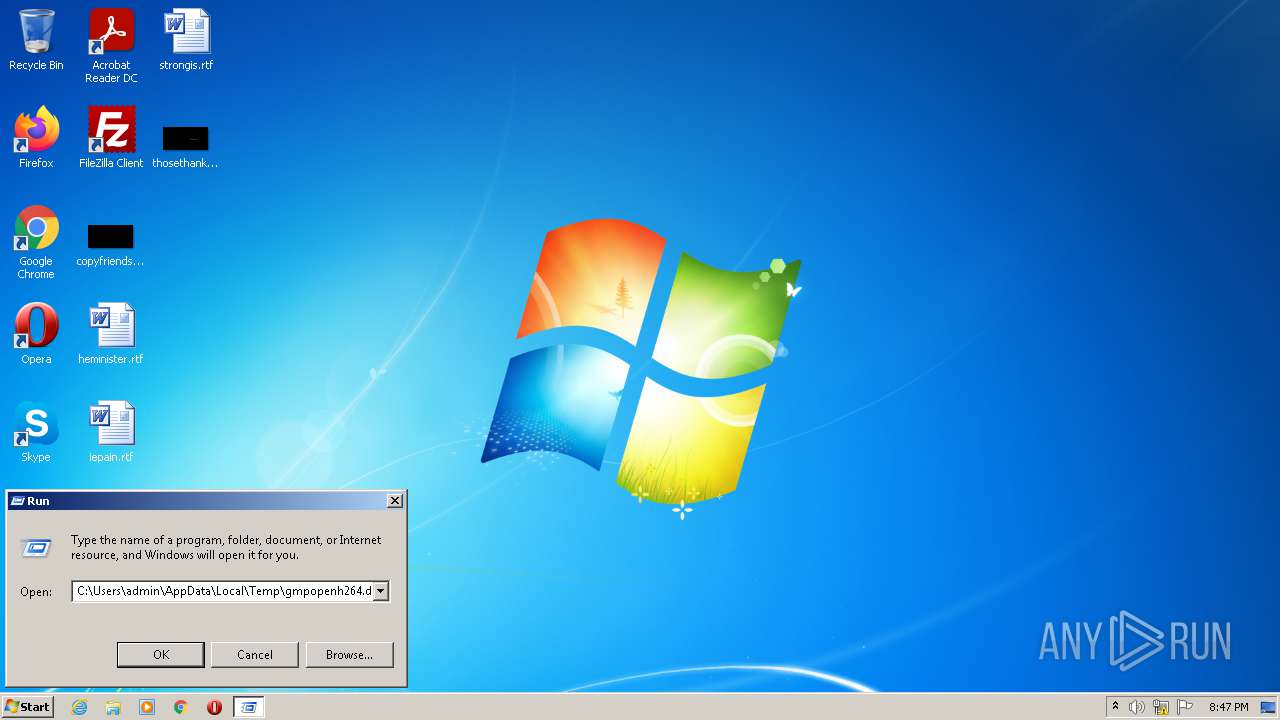
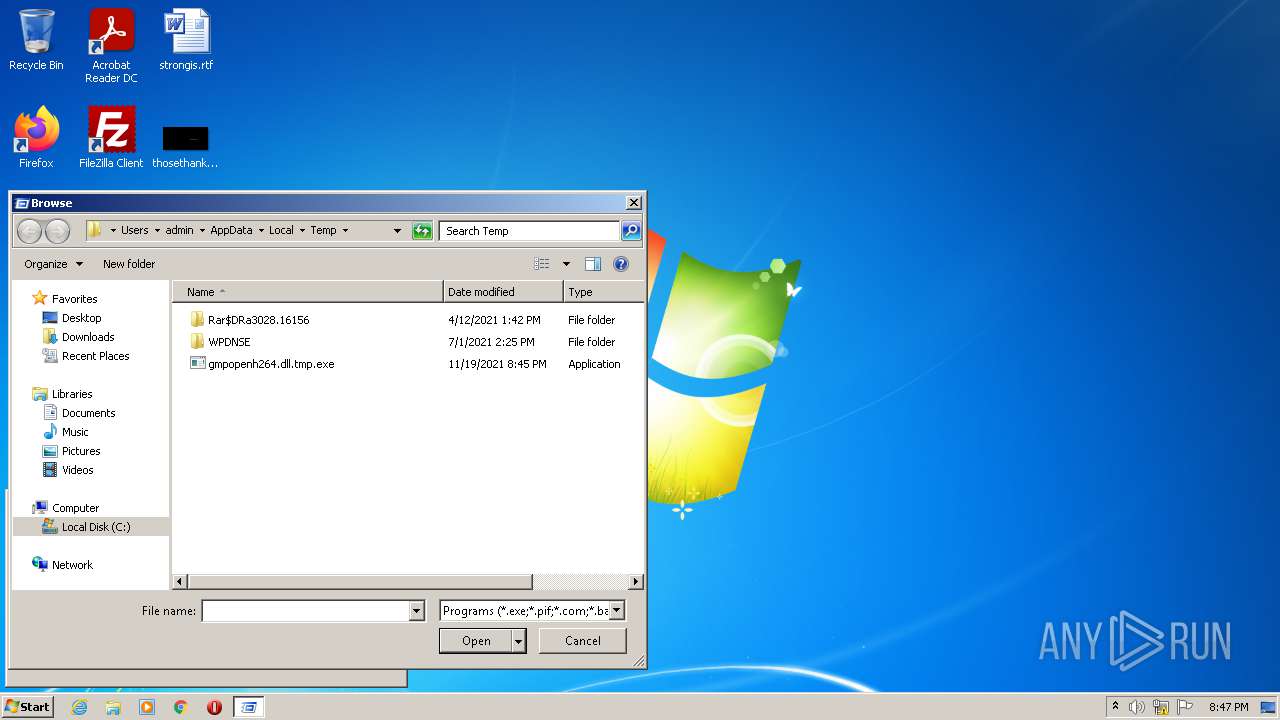
| File name: | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\gmp-gmpopenh264\1.8.1.1\gmpopenh264.dll.tmp |
| Full analysis: | https://app.any.run/tasks/b88a1309-cb83-4ef8-a1b1-ed817e66378c |
| Verdict: | Malicious activity |
| Analysis date: | November 19, 2021, 20:45:01 |
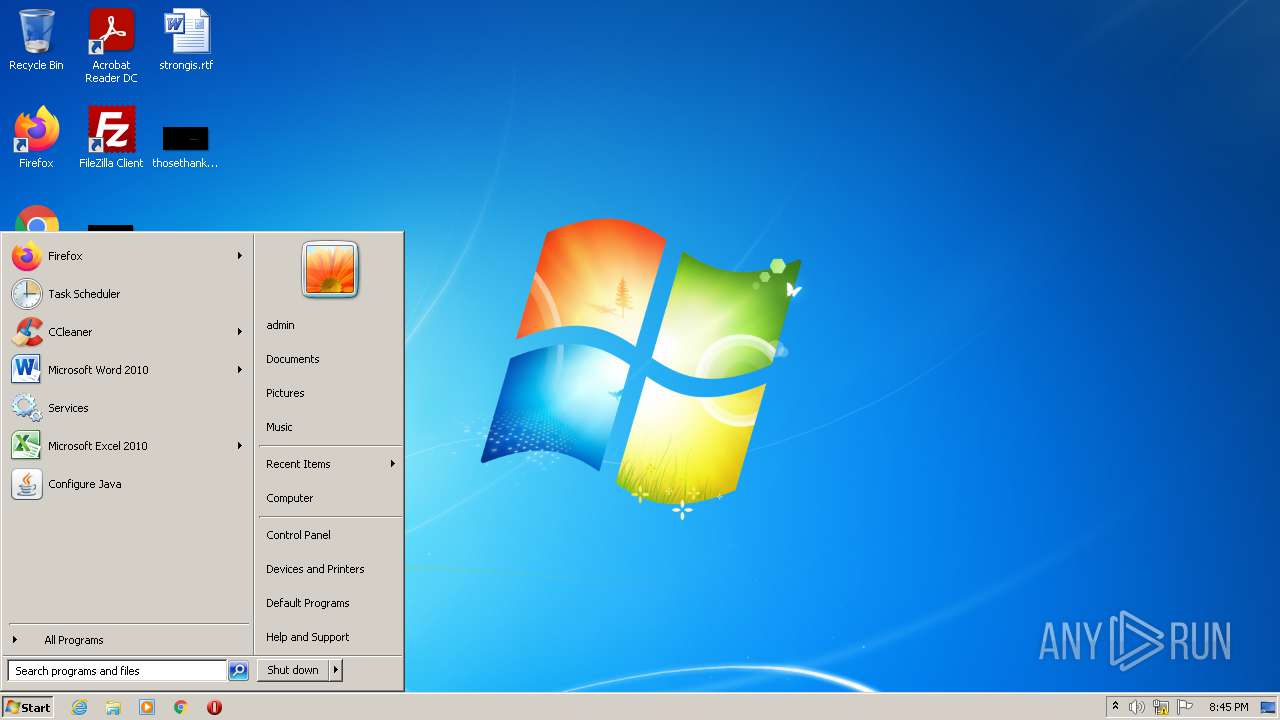
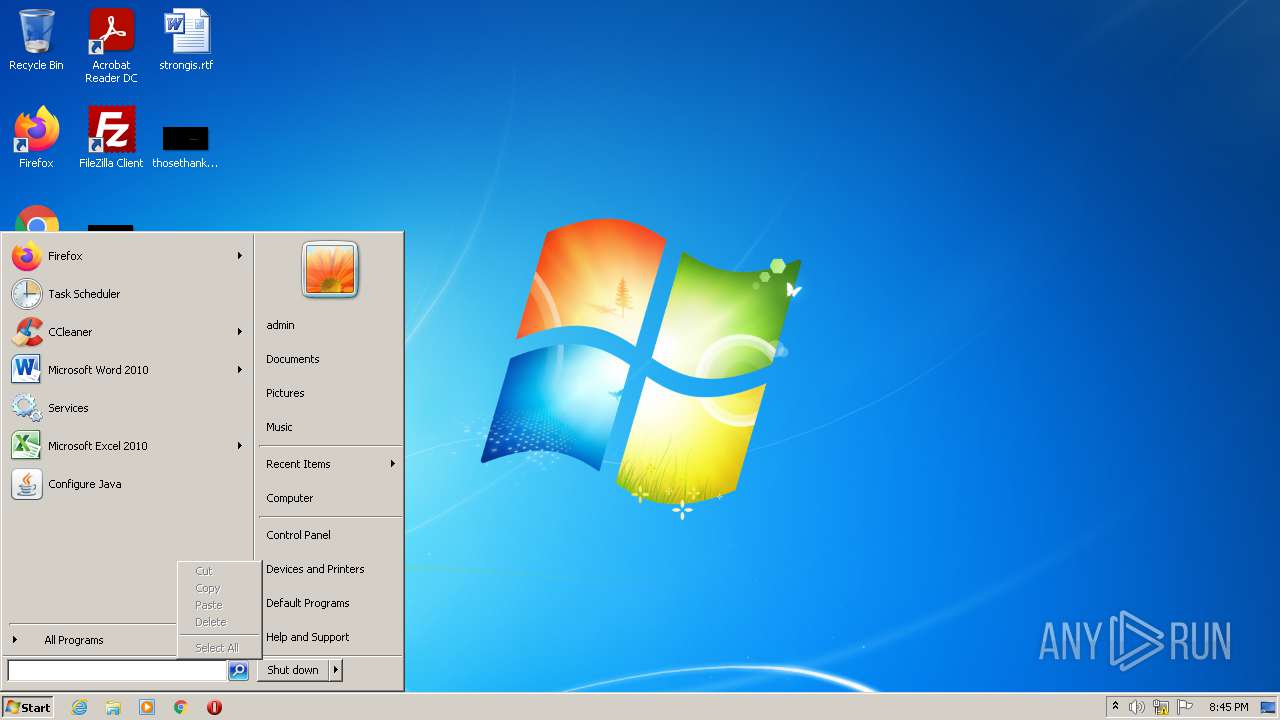
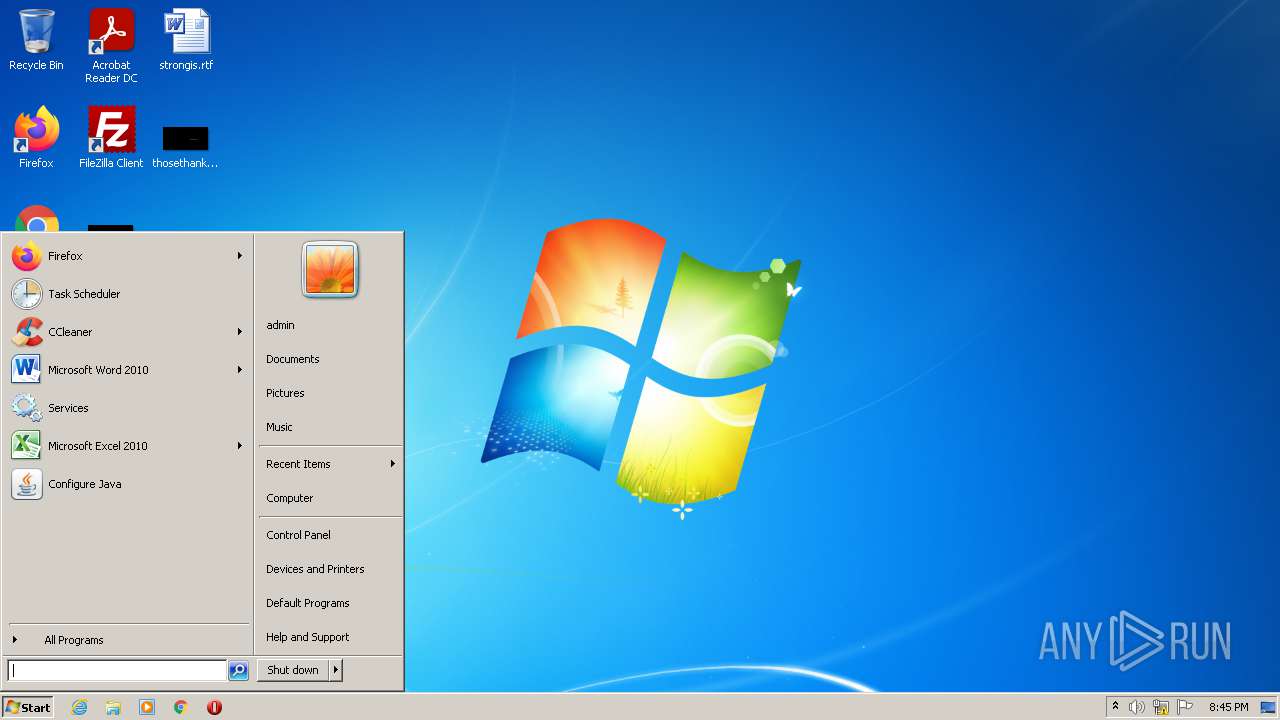
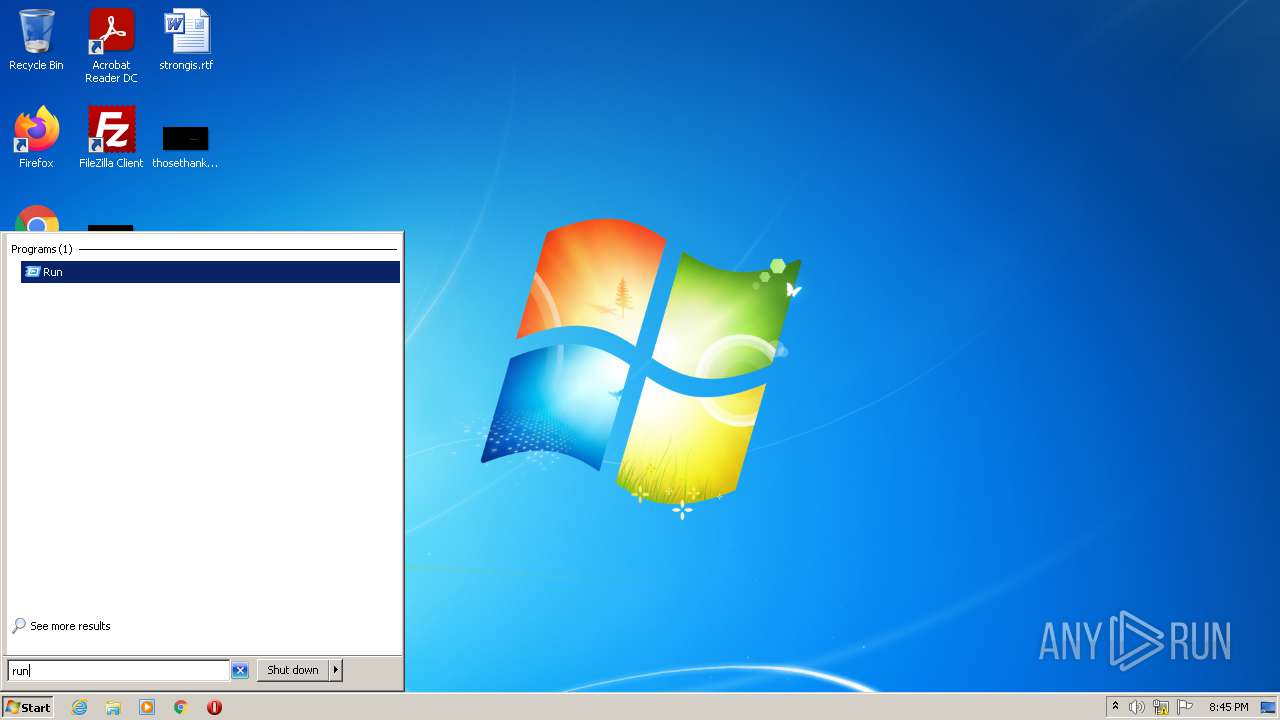
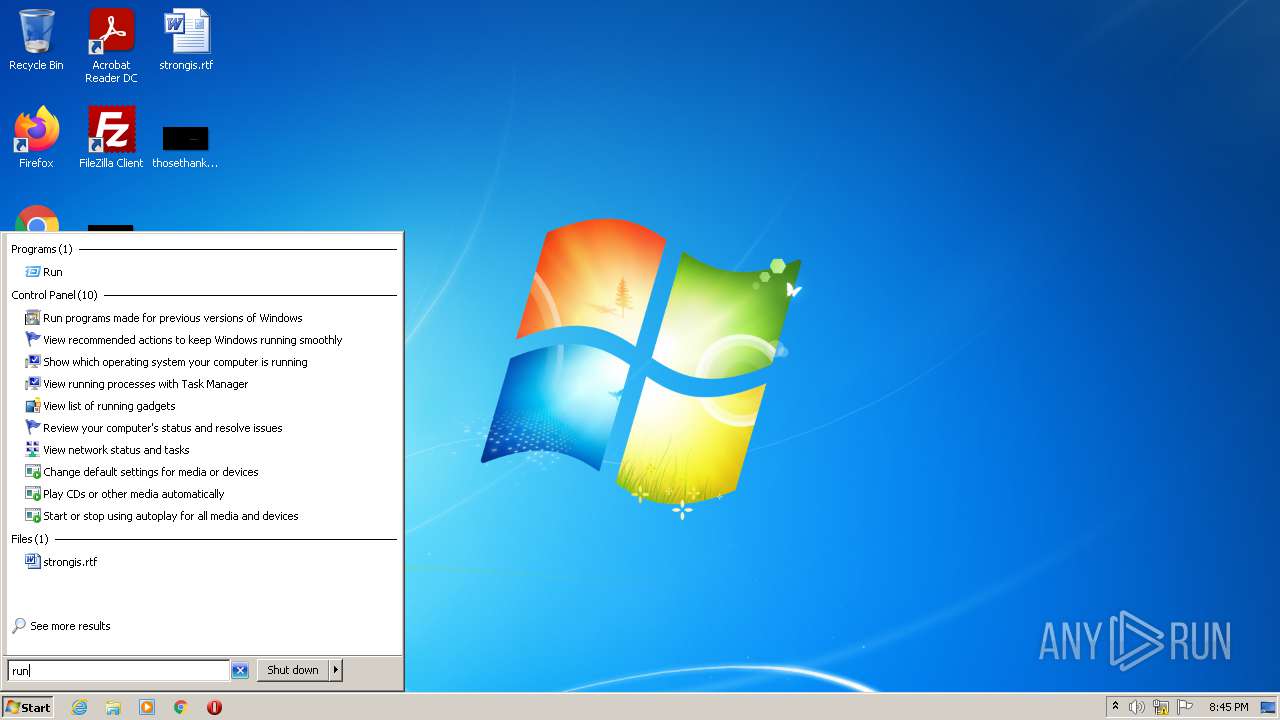
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
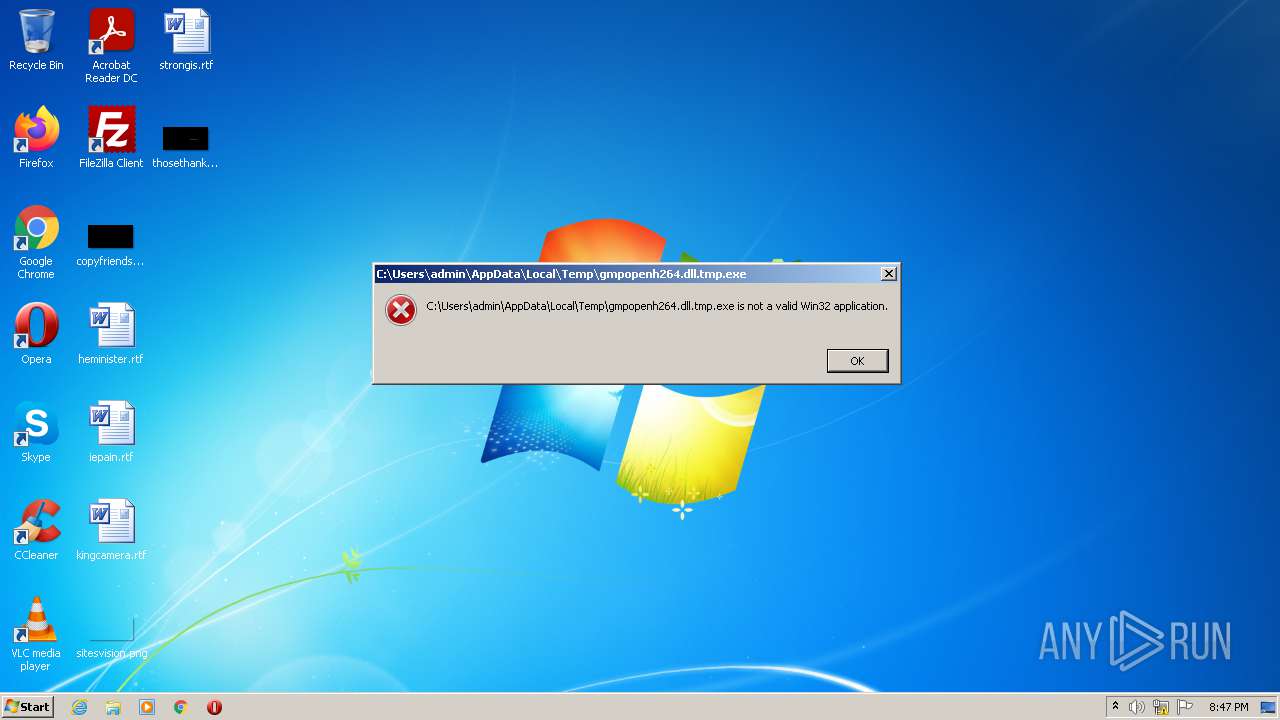
| MIME: | application/x-dosexec |
| File info: | PE32 executable (DLL) (GUI) Intel 80386, for MS Windows |
| MD5: | D23F706F2EACC190F2D4B75B041670D5 |
| SHA1: | 7DED6EE7912BAAD38A0D70E979E21A97DE8FD665 |
| SHA256: | CED08CE5BC45DBE505FA94B3A4268C0830CCDA016A23C0ACB16DD7268CFA7A65 |
| SSDEEP: | 24576:sAOHCYPulBi8knduE5vif0hexELM4zs+3pMepbsVj9XXfedmRi:zOlkCdrgxEY4zs2ij9XXfgmRi |
MALICIOUS
Loads dropped or rewritten executable
- Explorer.EXE (PID: 636)
- rundll32.exe (PID: 2648)
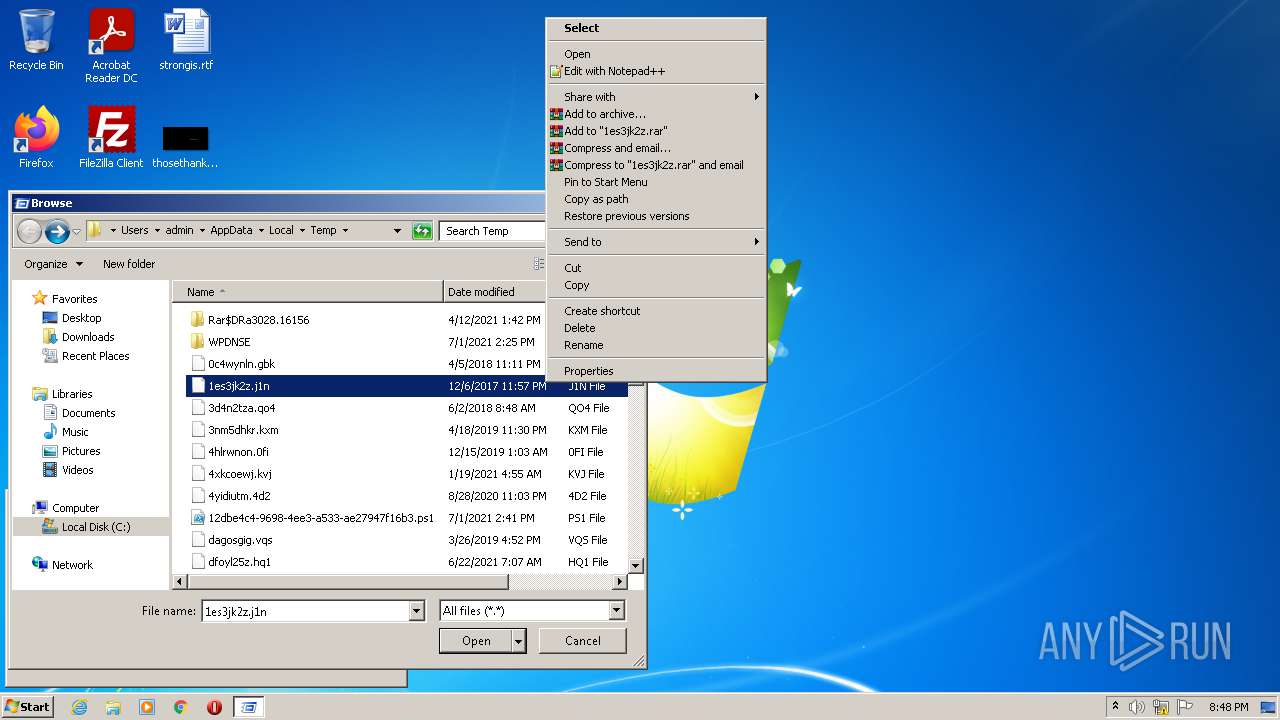
SUSPICIOUS
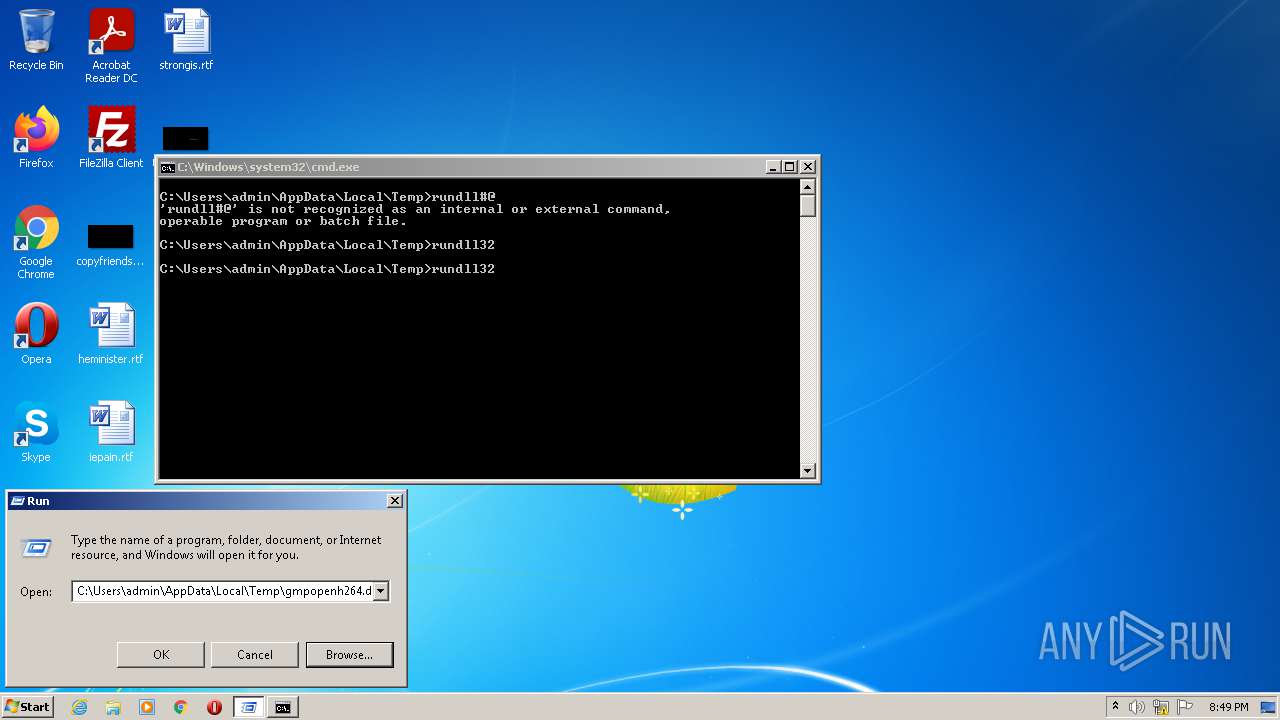
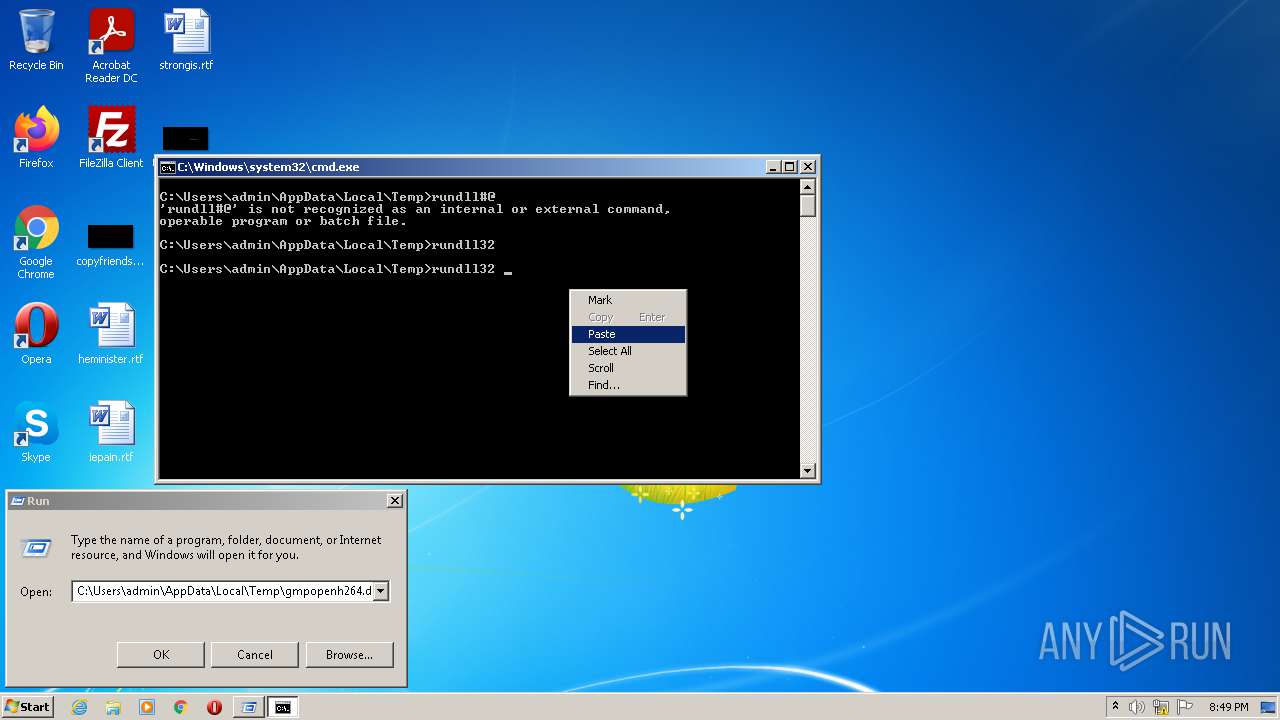
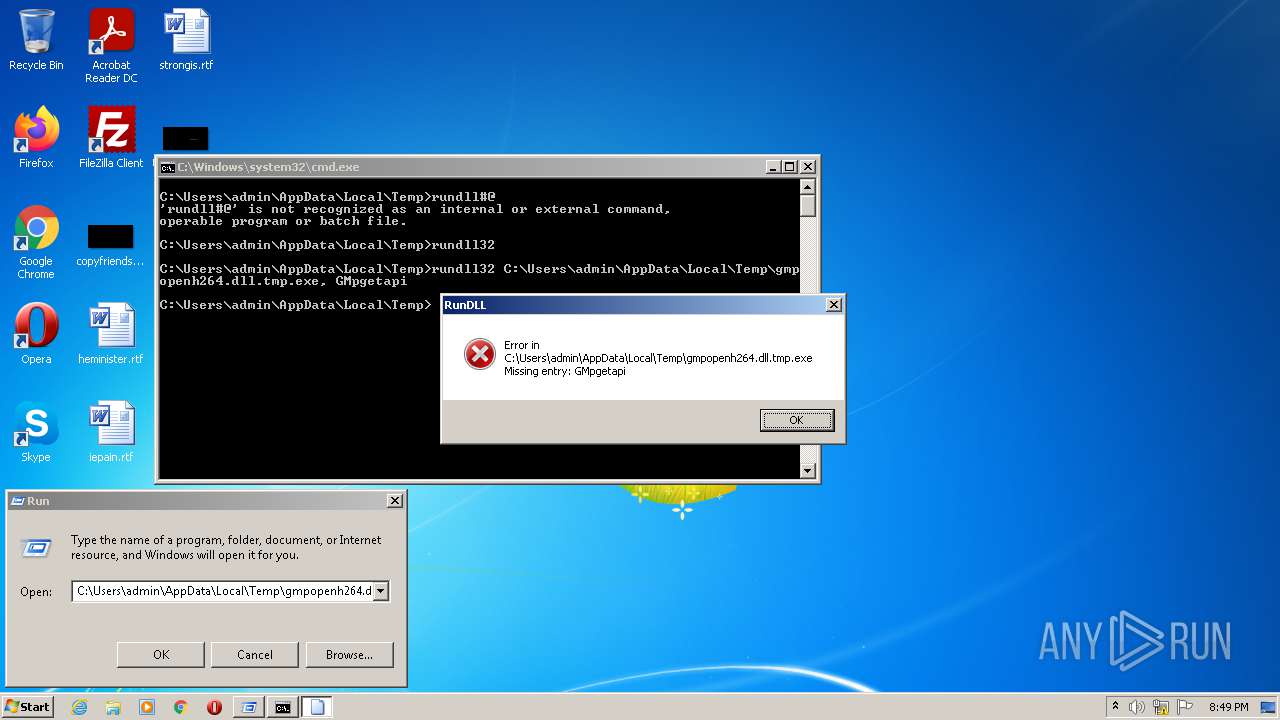
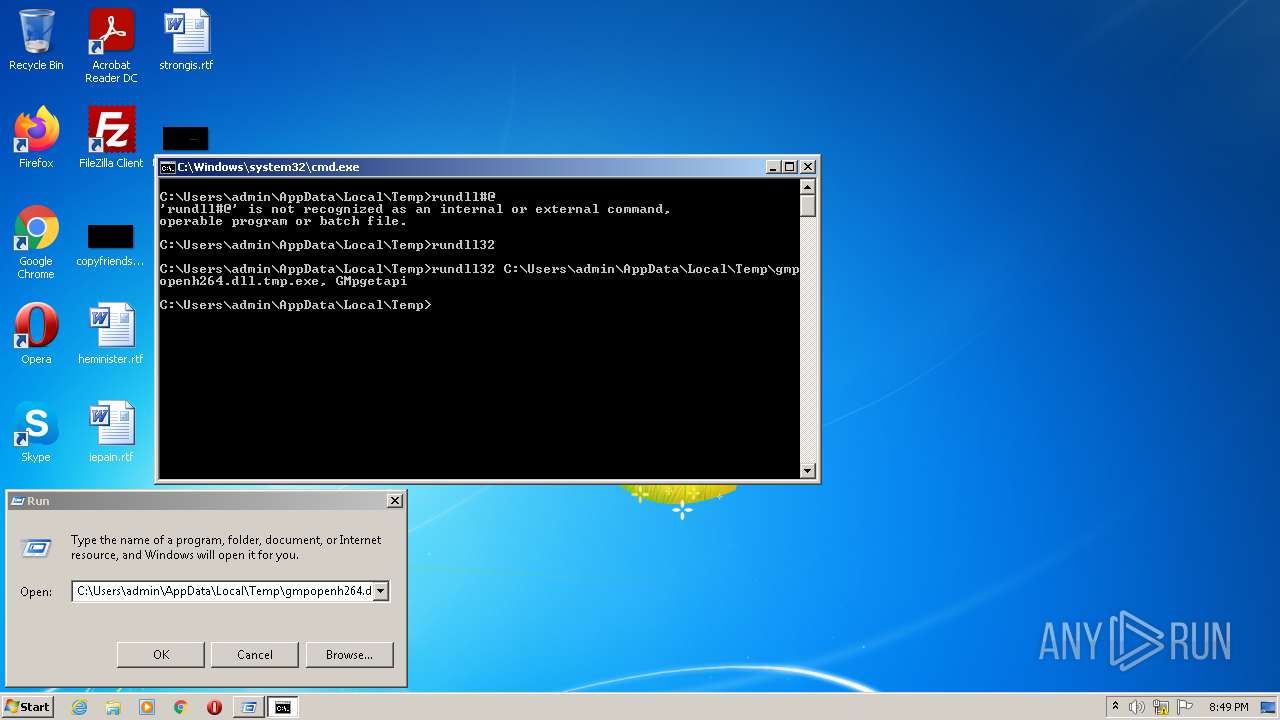
Uses RUNDLL32.EXE to load library
- Explorer.EXE (PID: 636)
- cmd.exe (PID: 3340)
Checks supported languages
- cmd.exe (PID: 3340)
Starts CMD.EXE for commands execution
- Explorer.EXE (PID: 636)
INFO
Checks supported languages
- rundll32.exe (PID: 3180)
- Explorer.EXE (PID: 636)
- rundll32.exe (PID: 604)
- rundll32.exe (PID: 2648)
Loads main object executable
- rundll32.exe (PID: 3180)
Reads Microsoft Office registry keys
- Explorer.EXE (PID: 636)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:03:02 17:54:21+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 14.15 |
| CodeSize: | 1042944 |
| InitializedDataSize: | 187392 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xdb450 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 02-Mar-2019 16:54:21 |
| Debug artifacts: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000F8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 02-Mar-2019 16:54:21 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000FE9DE | 0x000FEA00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.31443 |
.rdata | 0x00100000 | 0x000246C6 | 0x00024800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.93117 |
.data | 0x00125000 | 0x00002C18 | 0x00001E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.26644 |
.rodata | 0x00128000 | 0x00001320 | 0x00001400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.64432 |
.reloc | 0x0012A000 | 0x000051C4 | 0x00005200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.57661 |
Imports
KERNEL32.dll |
Exports
Title | Ordinal | Address |
|---|---|---|
GMPGetAPI | 1 | 0x00001130 |
GMPInit | 2 | 0x00001110 |
GMPShutdown | 3 | 0x00001210 |
WelsCreateDecoder | 4 | 0x000AF170 |
WelsCreateSVCEncoder | 5 | 0x0006ABD0 |
WelsDestroyDecoder | 6 | 0x000AF1E0 |
WelsDestroySVCEncoder | 7 | 0x0006AC30 |
WelsGetCodecVersion | 8 | 0x0006AC90 |
WelsGetCodecVersionEx | 9 | 0x0006ACC0 |
Total processes
39
Monitored processes
5
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 604 | rundll32 | C:\Windows\system32\rundll32.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 636 | C:\Windows\Explorer.EXE | C:\Windows\Explorer.EXE | — | — | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
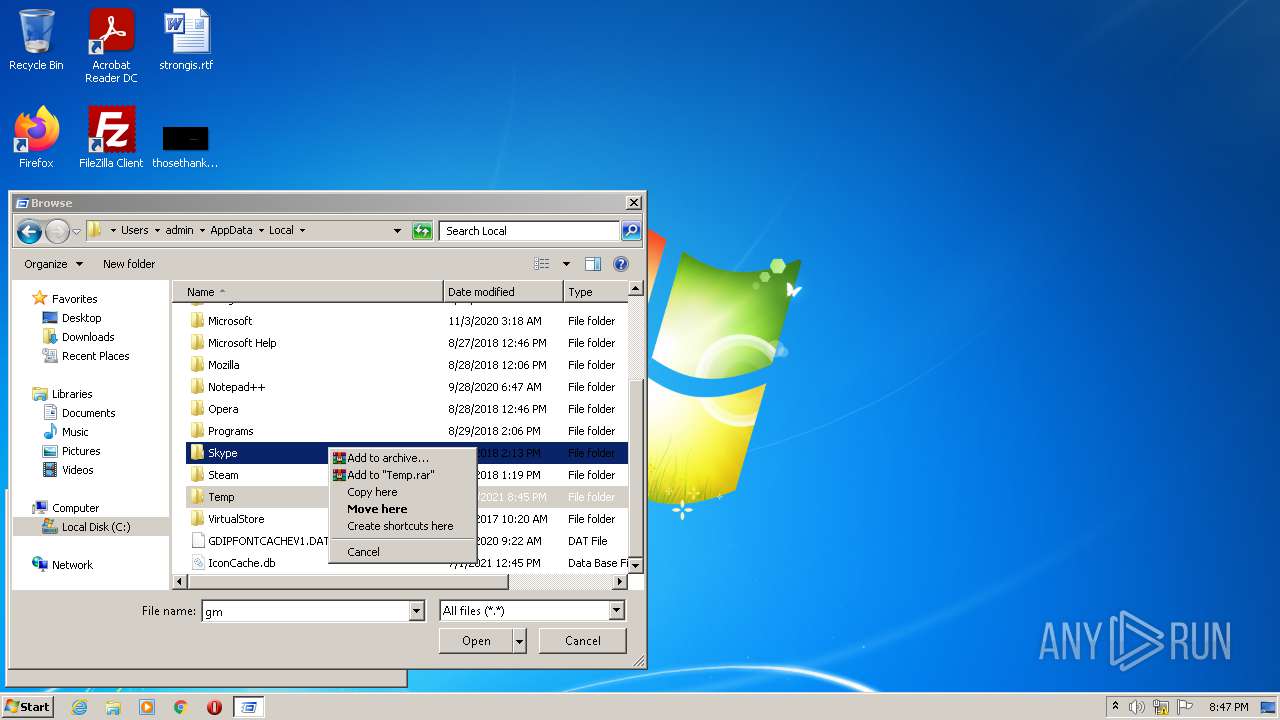
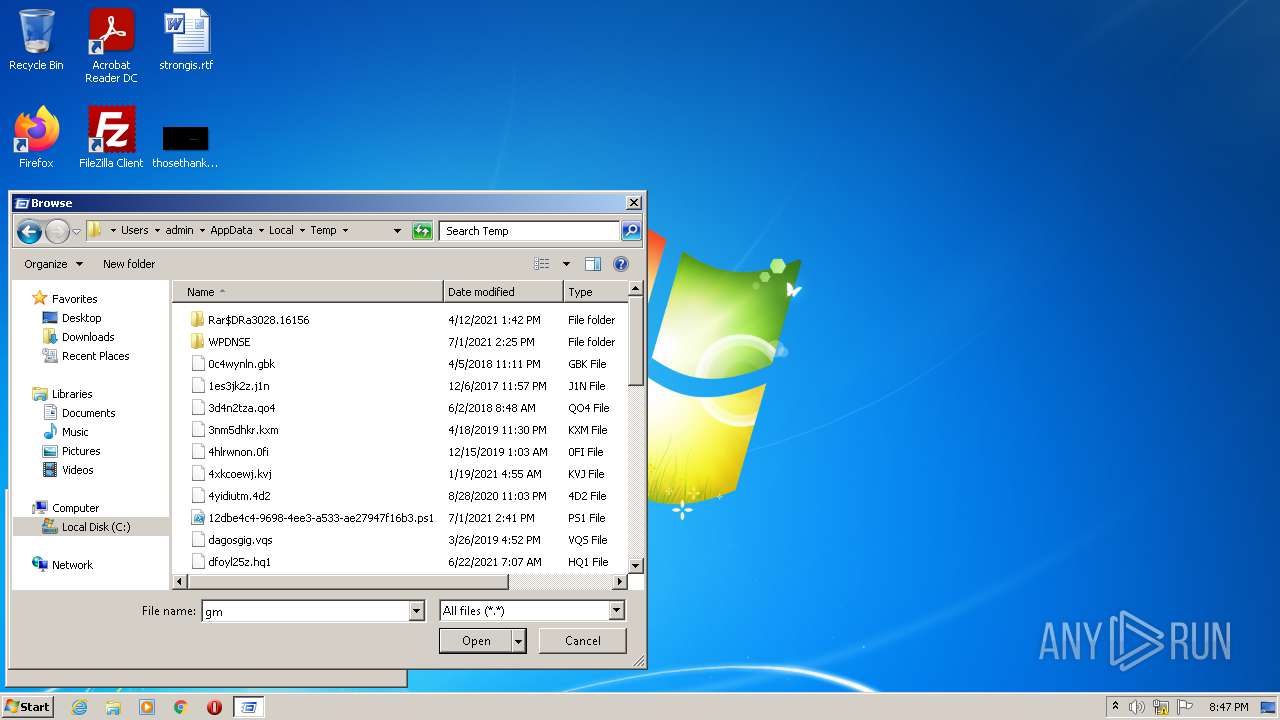
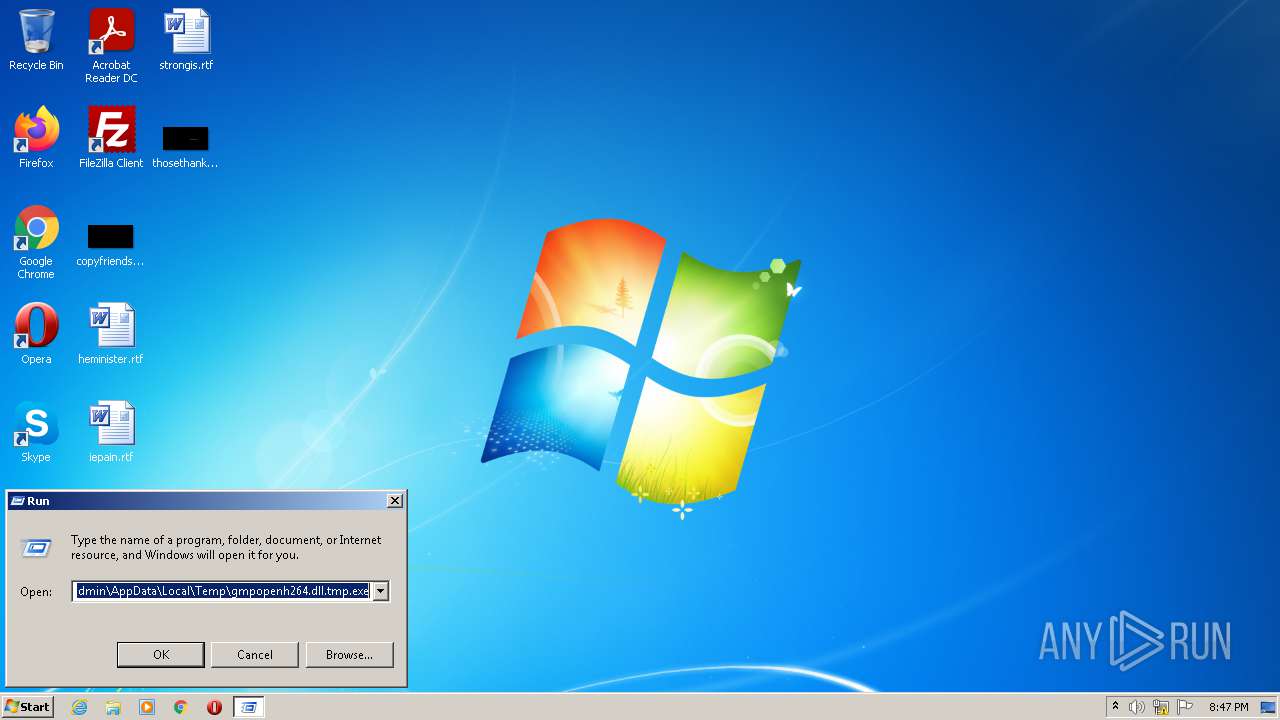
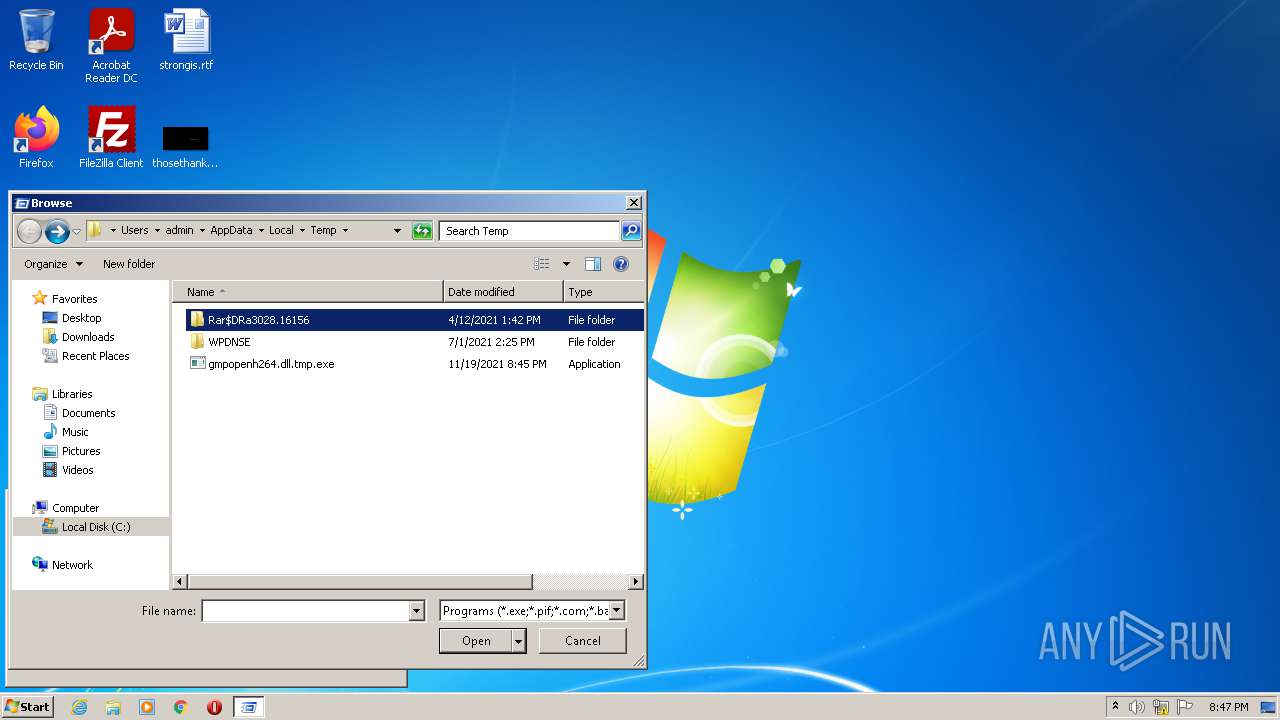
| 2648 | rundll32 C:\Users\admin\AppData\Local\Temp\gmpopenh264.dll.tmp.exe, GMpgetapi | C:\Windows\system32\rundll32.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3180 | "C:\Windows\System32\rundll32.exe" "C:\Users\admin\AppData\Local\Temp\gmpopenh264.dll.tmp.exe", GMPGetAPI | C:\Windows\System32\rundll32.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
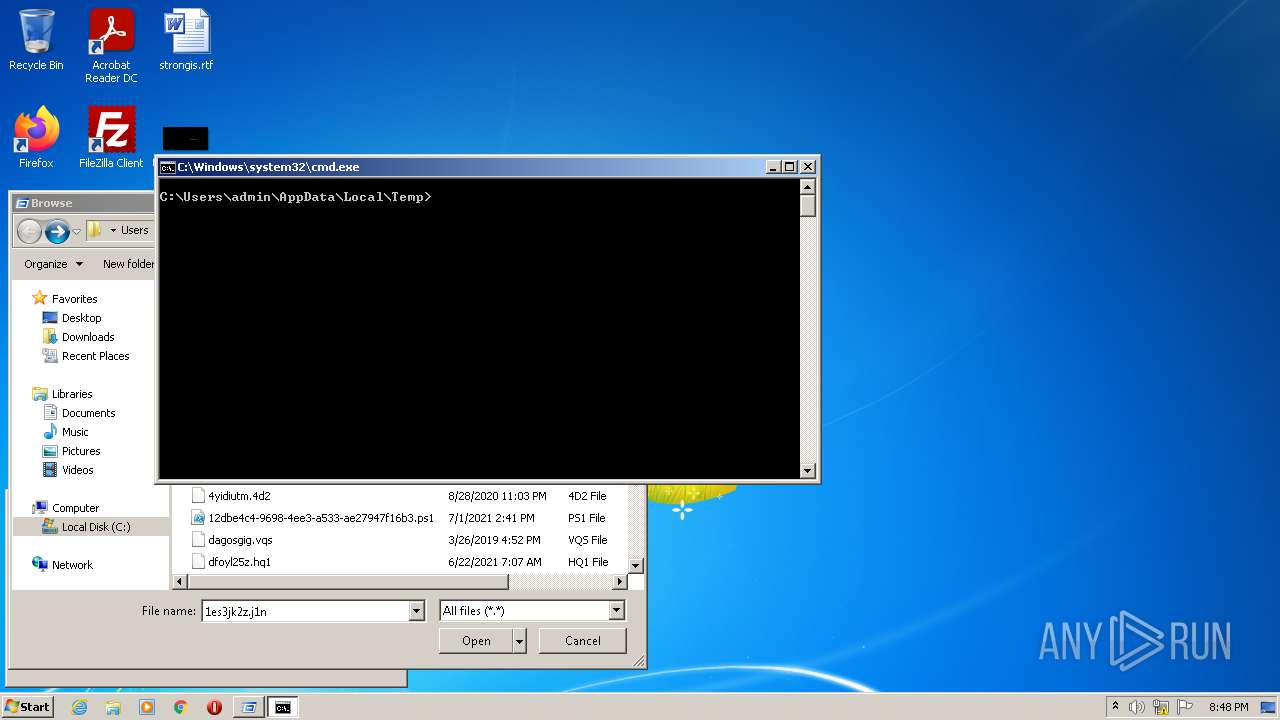
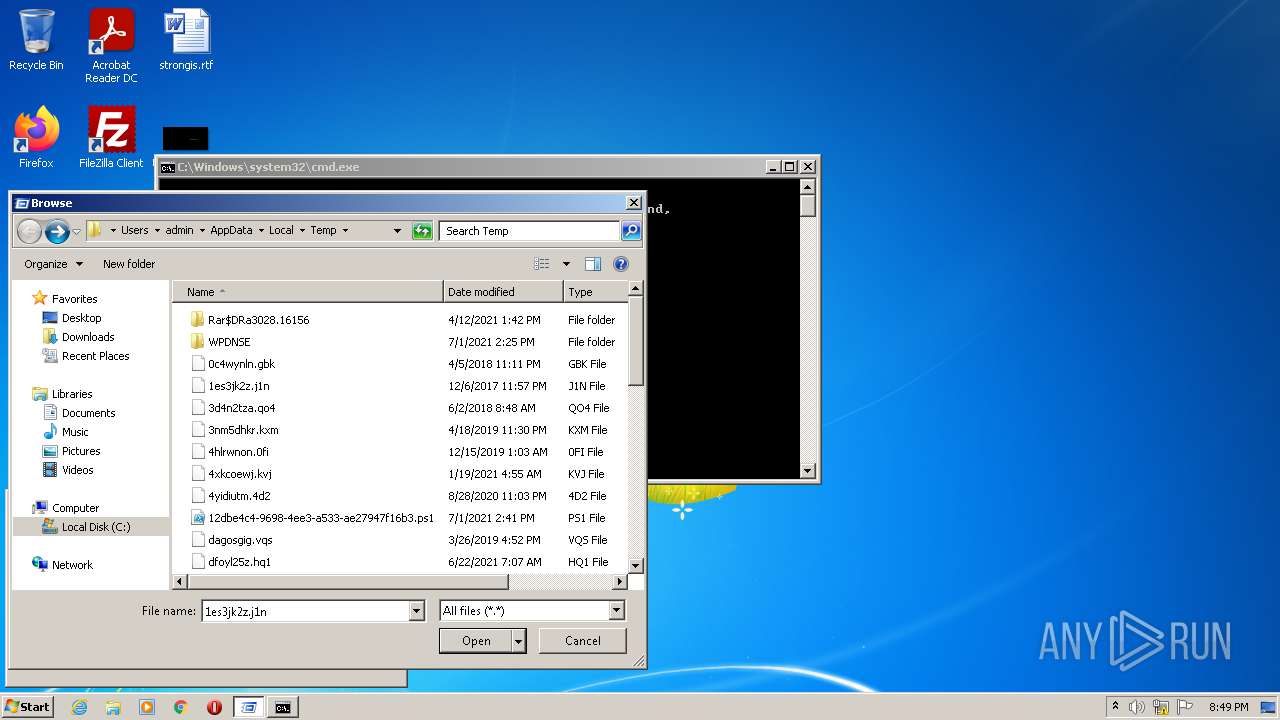
| 3340 | "cmd.exe" /s /k pushd "C:\Users\admin\AppData\Local\Temp" | C:\Windows\system32\cmd.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
12 092
Read events
11 022
Write events
1 067
Delete events
3
Modification events
| (PID) Process: | (636) Explorer.EXE | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (636) Explorer.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\ApplicationDestinations |
| Operation: | write | Name: | MaxEntries |
Value: 15 | |||
| (PID) Process: | (636) Explorer.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\StartPage |
| Operation: | write | Name: | StartMenu_Balloon_Time |
Value: 2E6ECB6486DDD701 | |||
| (PID) Process: | (636) Explorer.EXE | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | @%systemroot%\system32\recdisc.exe,-2001 |
Value: Creates a disc you can use to access system recovery options. | |||
| (PID) Process: | (636) Explorer.EXE | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | @%windir%\system32\speech\speechux\sapi.cpl,-5556 |
Value: Dictate text and control your computer by voice. | |||
| (PID) Process: | (636) Explorer.EXE | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | @%systemroot%\system32\sdcpl.dll,-100 |
Value: Backup and restore your files and system. Monitor latest backup status and configuration. | |||
| (PID) Process: | (636) Explorer.EXE | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | @%windir%\system32\msra.exe,-635 |
Value: Invite a friend or technical support person to connect to your computer and help you, or offer to help someone else. | |||
| (PID) Process: | (636) Explorer.EXE | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\SoundRecorder.exe,-32790 |
Value: Record sound and save it on your computer. | |||
| (PID) Process: | (636) Explorer.EXE | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | @%windir%\system32\migwiz\wet.dll,-601 |
Value: View reports from transfers you've performed | |||
| (PID) Process: | (636) Explorer.EXE | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | @%systemroot%\system32\rstrui.exe,-102 |
Value: Restore system to a chosen restore point. | |||
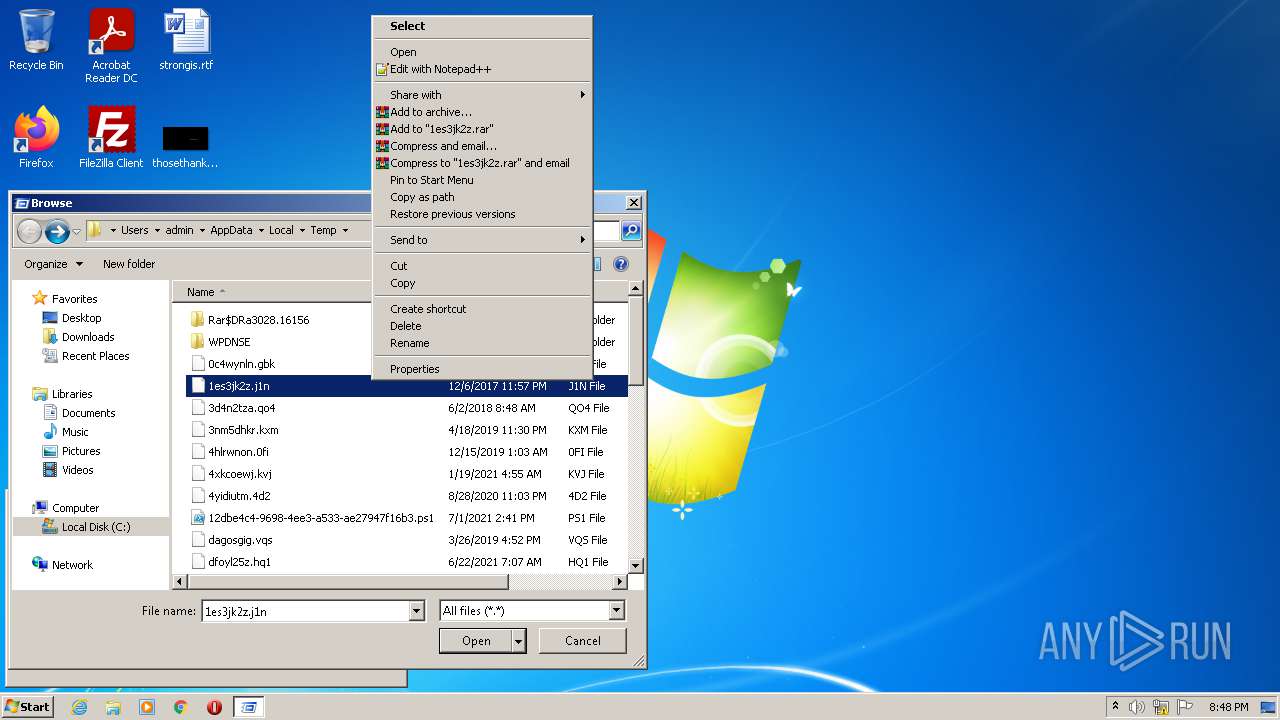
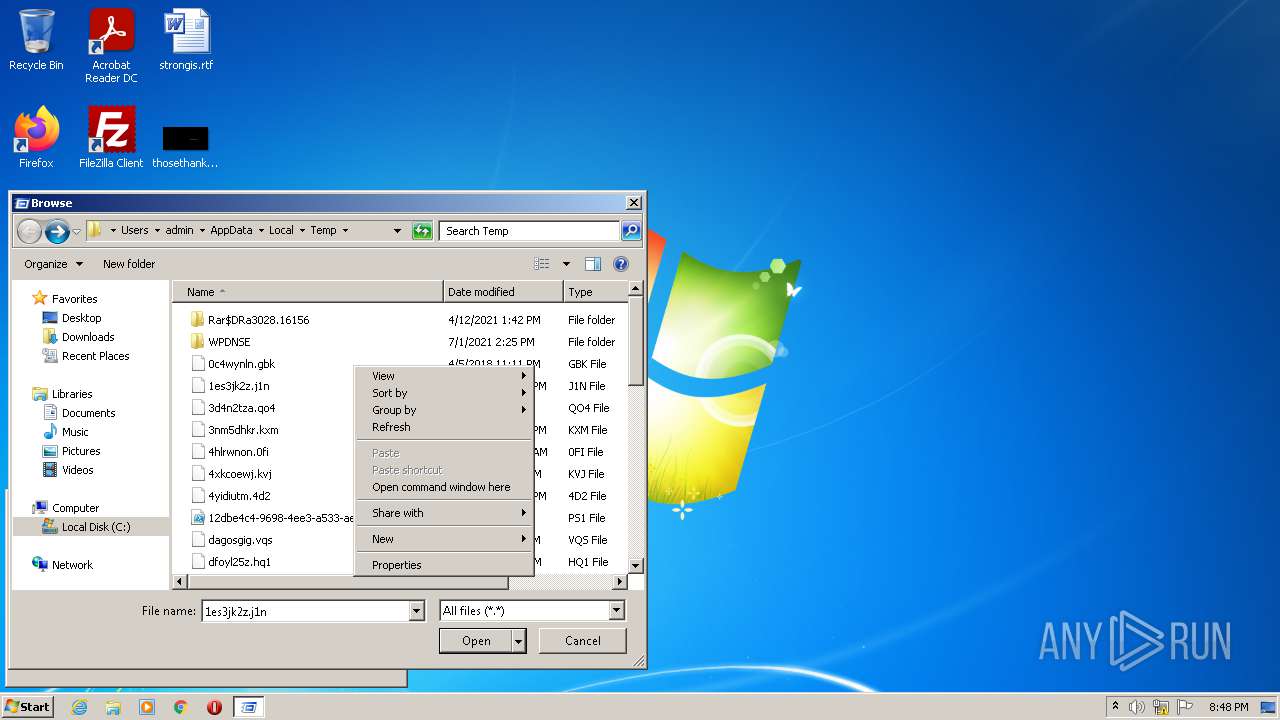
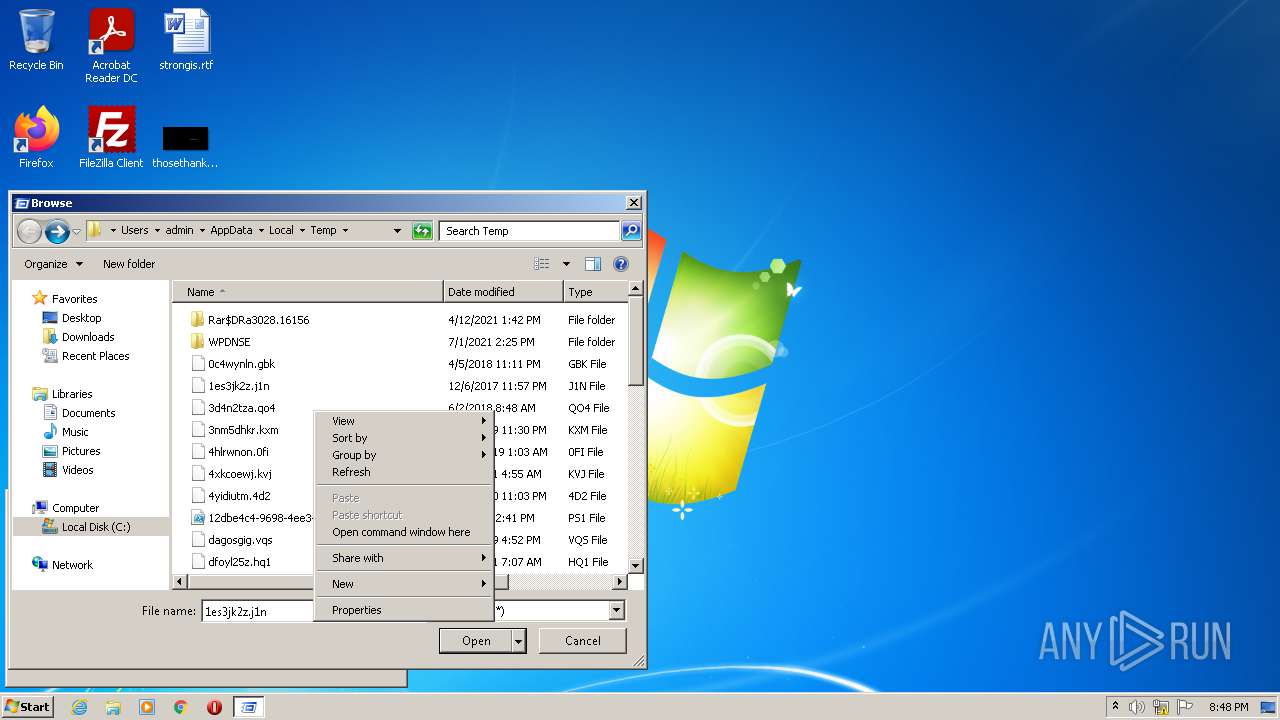
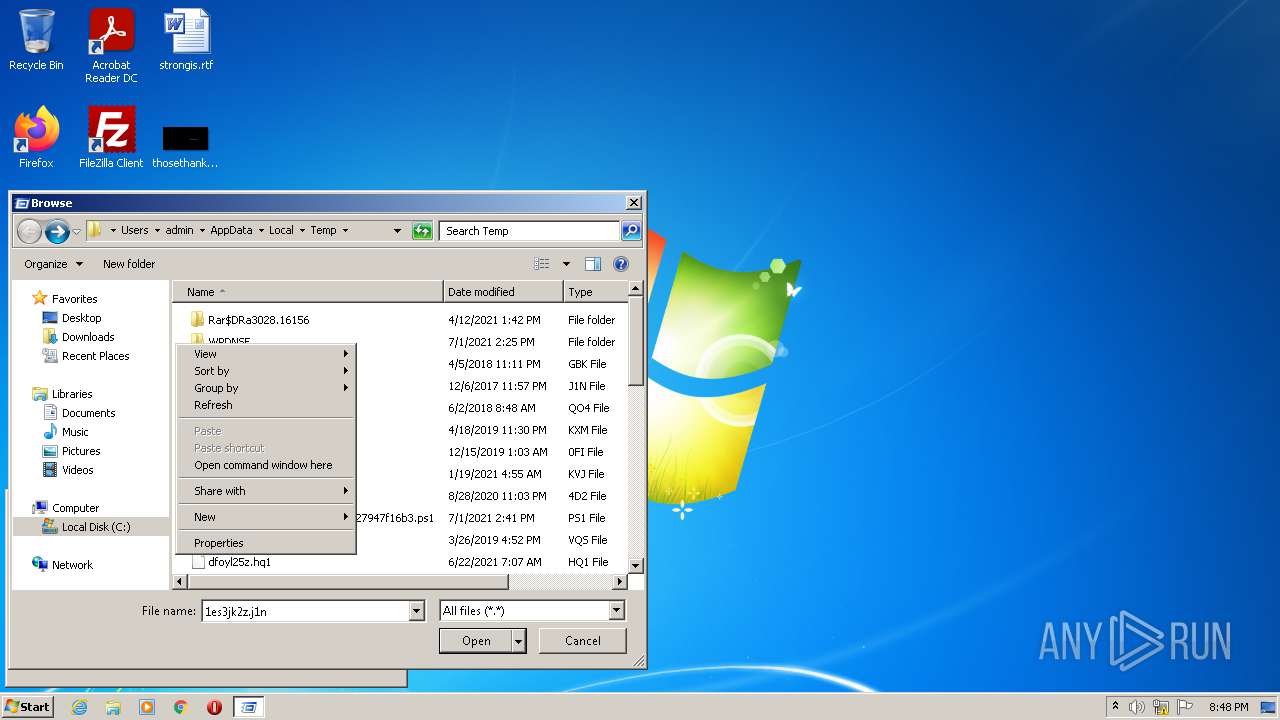
Executable files
0
Suspicious files
0
Text files
0
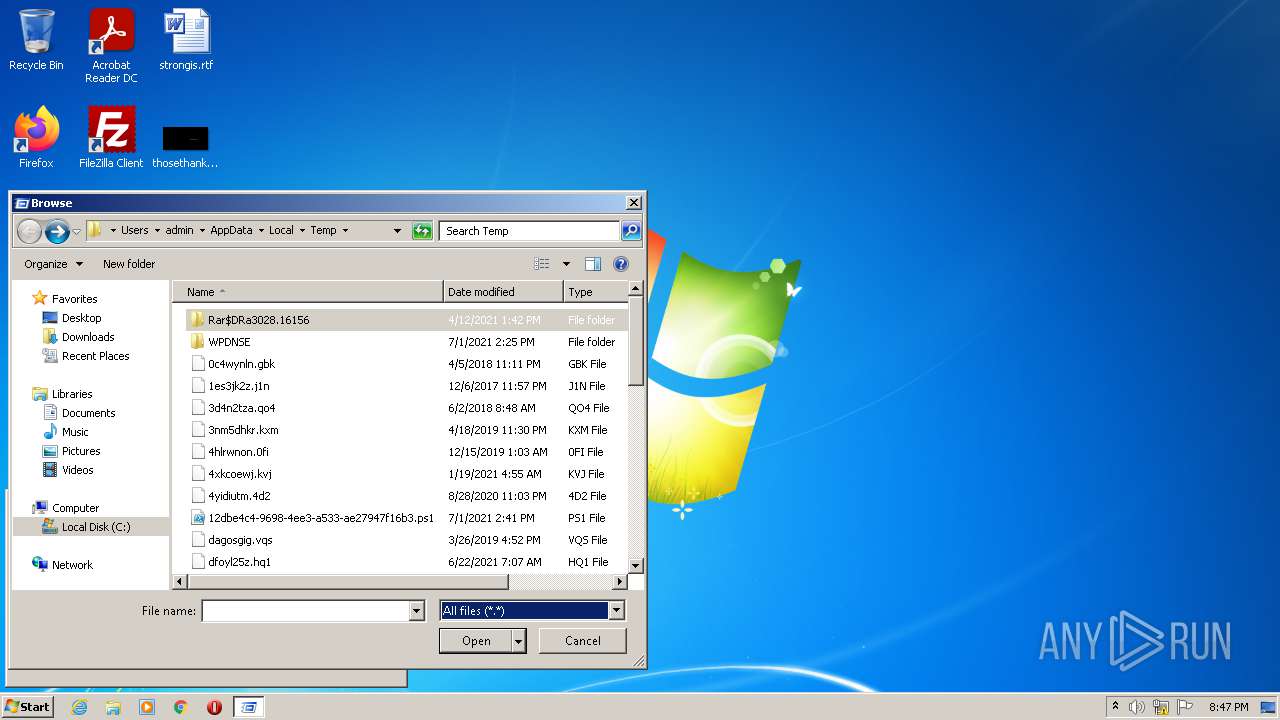
Unknown types
1
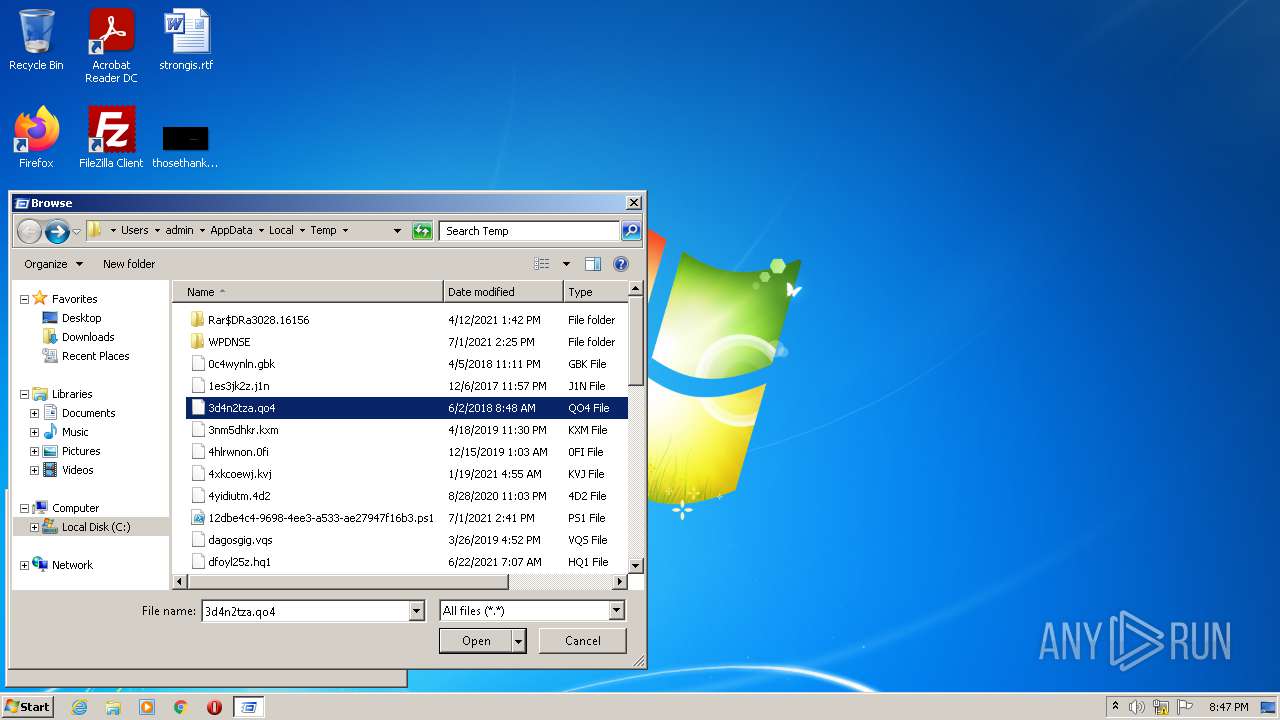
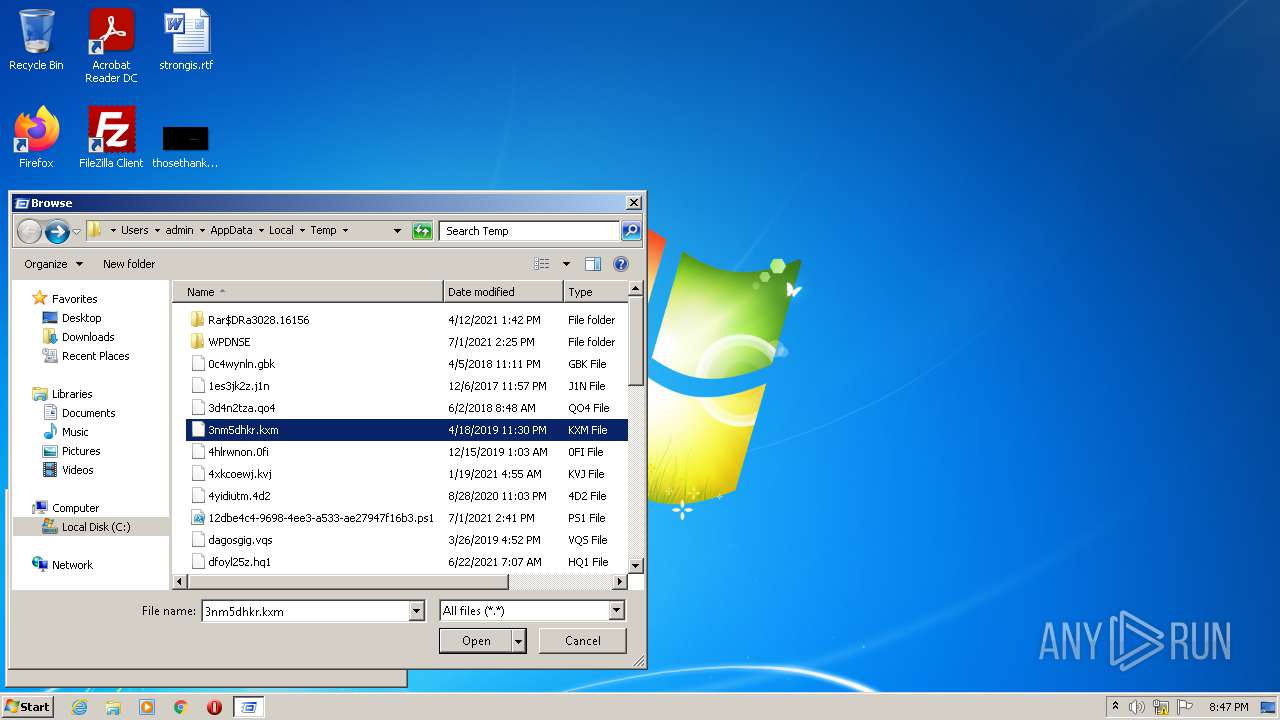
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 636 | Explorer.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\AutomaticDestinations\1b4dd67f29cb1962.automaticDestinations-ms | automaticdestinations-ms | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report