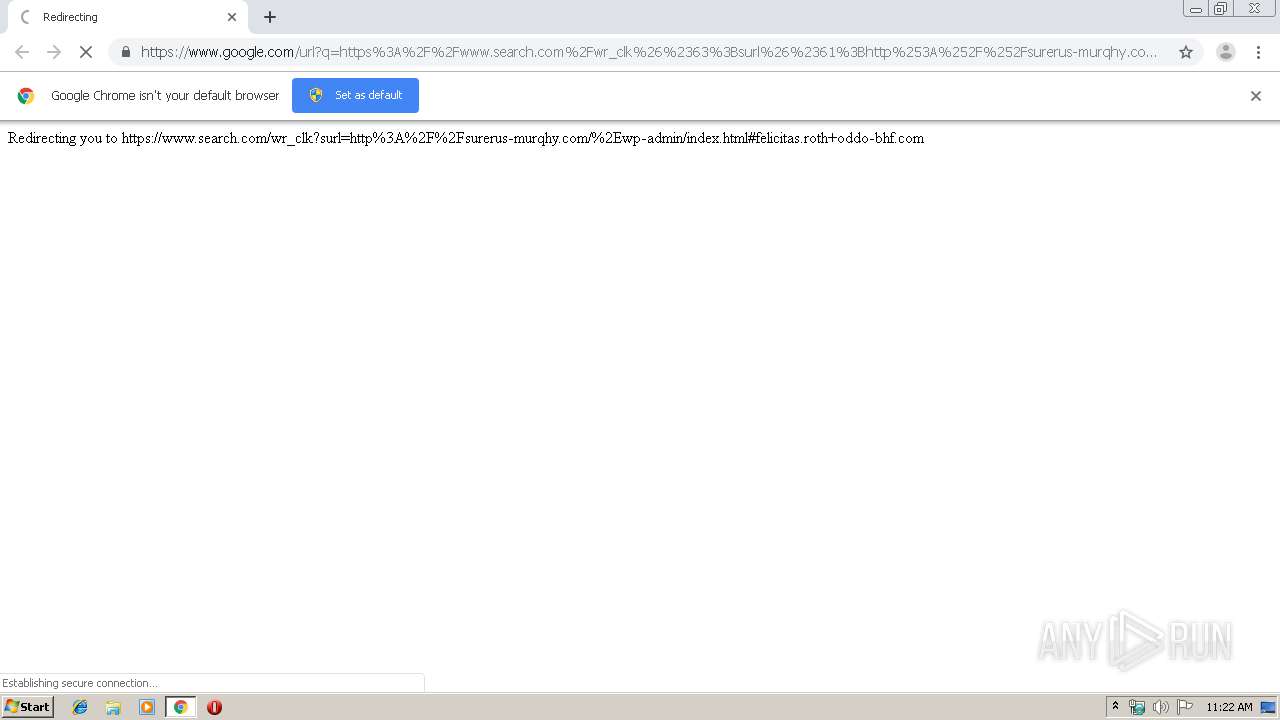
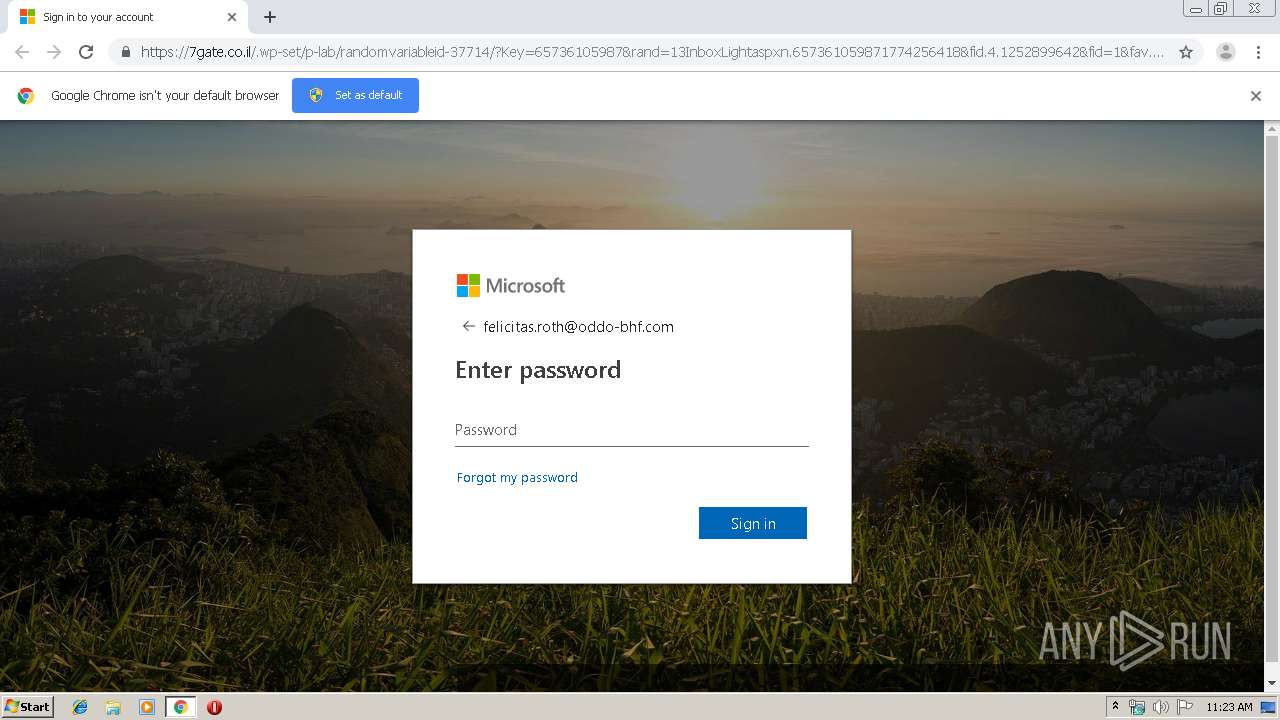
| URL: | https://www.google.com/url?q=https%3A%2F%2Fwww.search.com%2Fwr_clk%26%2363%3Bsurl%26%2361%3Bhttp%253A%252F%252Fsurerus-murqhy.com%2F%252Ewp-admin%2Findex.html%23felicitas.roth%2Boddo-bhf.com&sa=D&sntz=1&usg=AFQjCNEyfChq-psA1Z94qk9nYwdSjq0e7g |
| Full analysis: | https://app.any.run/tasks/d1cdeb2d-87e9-43f1-a1ad-d18fc0888735 |
| Verdict: | Malicious activity |
| Analysis date: | September 06, 2019, 10:22:37 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | C1738435E33B2B8FC2CFF17A6FE83FF9 |
| SHA1: | 6013D12E6C3E54A9C4719191B3F613CCE401E39C |
| SHA256: | CEC6021A3535364A6CA7B3868E82FC4756E0CC2AEA7CC99D93D035A74F8EB644 |
| SSDEEP: | 6:2OLI2Mz/v9AAJy9HAXDuzpkO5VBaXg8DizDCG0Ooa:2V2MBDy9HKYVINiiq |
MALICIOUS
No malicious indicators.SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 2900)
INFO
Reads the hosts file
- chrome.exe (PID: 2900)
- chrome.exe (PID: 2160)
Reads settings of System Certificates
- chrome.exe (PID: 2160)
Application launched itself
- chrome.exe (PID: 2900)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
56
Monitored processes
23
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 880 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1004,2808521579063662300,2381437257828957443,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=17181170986162811549 --mojo-platform-channel-handle=2512 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2160 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1004,2808521579063662300,2381437257828957443,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=8046269081765107333 --mojo-platform-channel-handle=1624 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2272 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1004,2808521579063662300,2381437257828957443,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=7471836903459390109 --mojo-platform-channel-handle=3944 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2316 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1004,2808521579063662300,2381437257828957443,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=15604595619004949872 --mojo-platform-channel-handle=3800 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2532 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1004,2808521579063662300,2381437257828957443,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=2060944783736408672 --renderer-client-id=7 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3136 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2540 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1004,2808521579063662300,2381437257828957443,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=11386127282828855156 --mojo-platform-channel-handle=3056 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2616 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1004,2808521579063662300,2381437257828957443,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=14471348722364201088 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2236 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2700 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1004,2808521579063662300,2381437257828957443,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=4315631171324292812 --mojo-platform-channel-handle=3648 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2712 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1004,2808521579063662300,2381437257828957443,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=13165497412258550639 --mojo-platform-channel-handle=2776 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2748 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2904 --on-initialized-event-handle=312 --parent-handle=316 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
613
Read events
526
Write events
82
Delete events
5
Modification events
| (PID) Process: | (2900) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2900) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2900) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2900) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2900) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2748) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2900-13212238973316875 |
Value: 259 | |||
| (PID) Process: | (2900) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2900) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2900) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1512-13197841398593750 |
Value: 0 | |||
| (PID) Process: | (2900) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 2900-13212238973316875 |
Value: 259 | |||
Executable files
0
Suspicious files
18
Text files
186
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2900 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2900 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\99e5bd3b-128b-48d3-baf6-fc626a3c7a89.tmp | — | |
MD5:— | SHA256:— | |||
| 2900 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2900 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF169e77.TMP | text | |
MD5:— | SHA256:— | |||
| 2900 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2900 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF169e67.TMP | text | |
MD5:— | SHA256:— | |||
| 2900 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old~RF169ef4.TMP | text | |
MD5:— | SHA256:— | |||
| 2900 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 2900 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Platform Notifications\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2900 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF169ea6.TMP | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
30
DNS requests
17
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
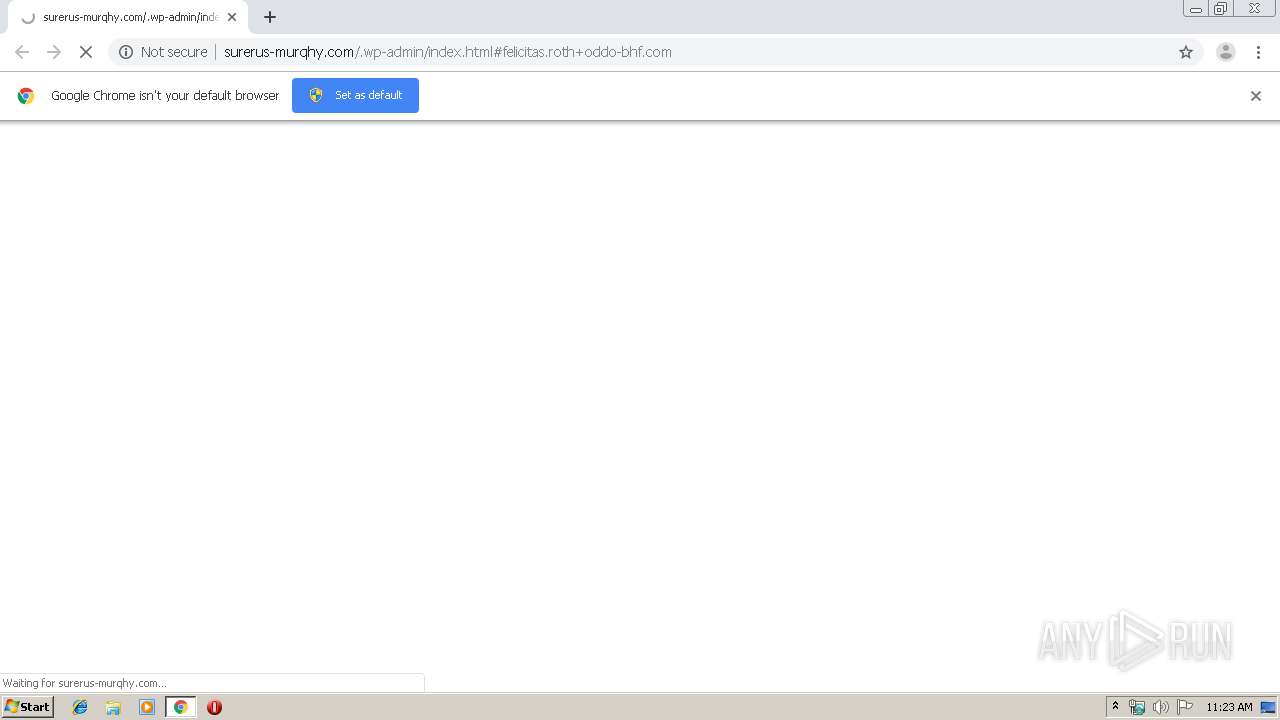
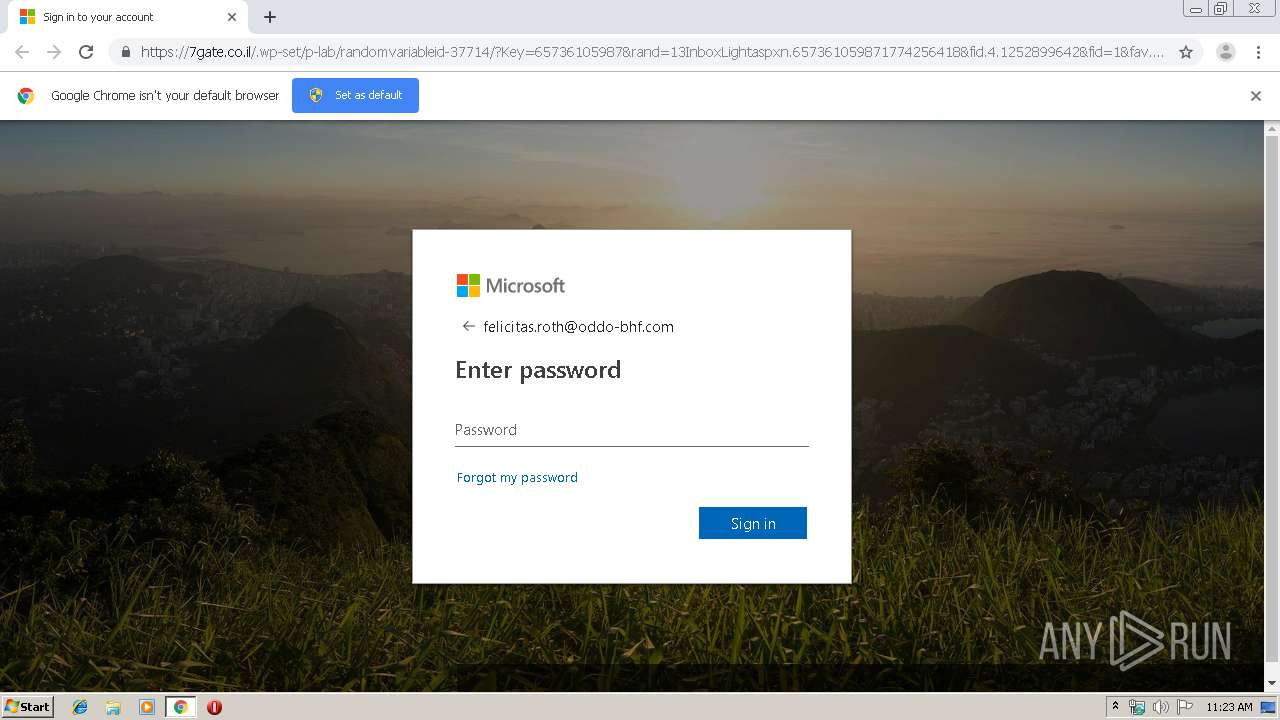
2160 | chrome.exe | GET | 302 | 162.241.157.164:80 | http://surerus-murqhy.com/.wp-admin/blocker.php?em=felicitas.roth+oddo-bhf.com | US | — | — | suspicious |
2160 | chrome.exe | GET | 200 | 162.241.157.164:80 | http://surerus-murqhy.com/.wp-admin/index.html | US | html | 4.39 Kb | suspicious |
2160 | chrome.exe | GET | 302 | 172.217.16.174:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 515 b | whitelisted |
2160 | chrome.exe | GET | 200 | 13.35.254.176:80 | http://x.ss2.us/x.cer | US | der | 1.27 Kb | whitelisted |
2160 | chrome.exe | GET | 200 | 93.184.221.240:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 57.0 Kb | whitelisted |
2160 | chrome.exe | GET | 404 | 162.241.157.164:80 | http://surerus-murqhy.com/favicon.ico | US | html | 315 b | suspicious |
2160 | chrome.exe | GET | 200 | 74.125.110.167:80 | http://r2---sn-5go7yner.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=82.103.130.125&mm=28&mn=sn-5go7yner&ms=nvh&mt=1567764906&mv=u&mvi=1&pl=26&shardbypass=yes | US | crx | 862 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2160 | chrome.exe | 162.241.157.164:80 | surerus-murqhy.com | CyrusOne LLC | US | suspicious |
2160 | chrome.exe | 172.217.18.10:443 | ajax.googleapis.com | Google Inc. | US | whitelisted |
2160 | chrome.exe | 172.217.22.1:443 | clients2.googleusercontent.com | Google Inc. | US | whitelisted |
2160 | chrome.exe | 216.58.210.14:443 | clients2.google.com | Google Inc. | US | whitelisted |
2160 | chrome.exe | 52.144.44.34:443 | 7gate.co.il | Kamatera, Inc. | US | unknown |
2160 | chrome.exe | 172.217.16.174:80 | redirector.gvt1.com | Google Inc. | US | whitelisted |
2160 | chrome.exe | 184.31.91.84:443 | secure.aadcdn.microsoftonline-p.com | Akamai International B.V. | NL | whitelisted |
2160 | chrome.exe | 172.217.21.227:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
2160 | chrome.exe | 172.217.22.42:443 | ajax.googleapis.com | Google Inc. | US | whitelisted |
2160 | chrome.exe | 172.217.23.138:443 | ajax.googleapis.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.google.com |
| malicious |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.search.com |
| whitelisted |
x.ss2.us |
| whitelisted |
www.download.windowsupdate.com |
| whitelisted |
surerus-murqhy.com |
| suspicious |
ajax.googleapis.com |
| whitelisted |
clients2.google.com |
| whitelisted |
clients2.googleusercontent.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2160 | chrome.exe | Potentially Bad Traffic | ET WEB_CLIENT Hex Obfuscation of String.fromCharCode % Encoding |
2160 | chrome.exe | Potentially Bad Traffic | ET WEB_CLIENT Hex Obfuscation of charCodeAt % Encoding |
2160 | chrome.exe | Potentially Bad Traffic | ET WEB_CLIENT Hex Obfuscation of document.write % Encoding |
2160 | chrome.exe | Potentially Bad Traffic | ET WEB_CLIENT Hex Obfuscation of parseInt % Encoding |
2160 | chrome.exe | Potentially Bad Traffic | ET WEB_CLIENT Hex Obfuscation of unescape % Encoding |
1 ETPRO signatures available at the full report