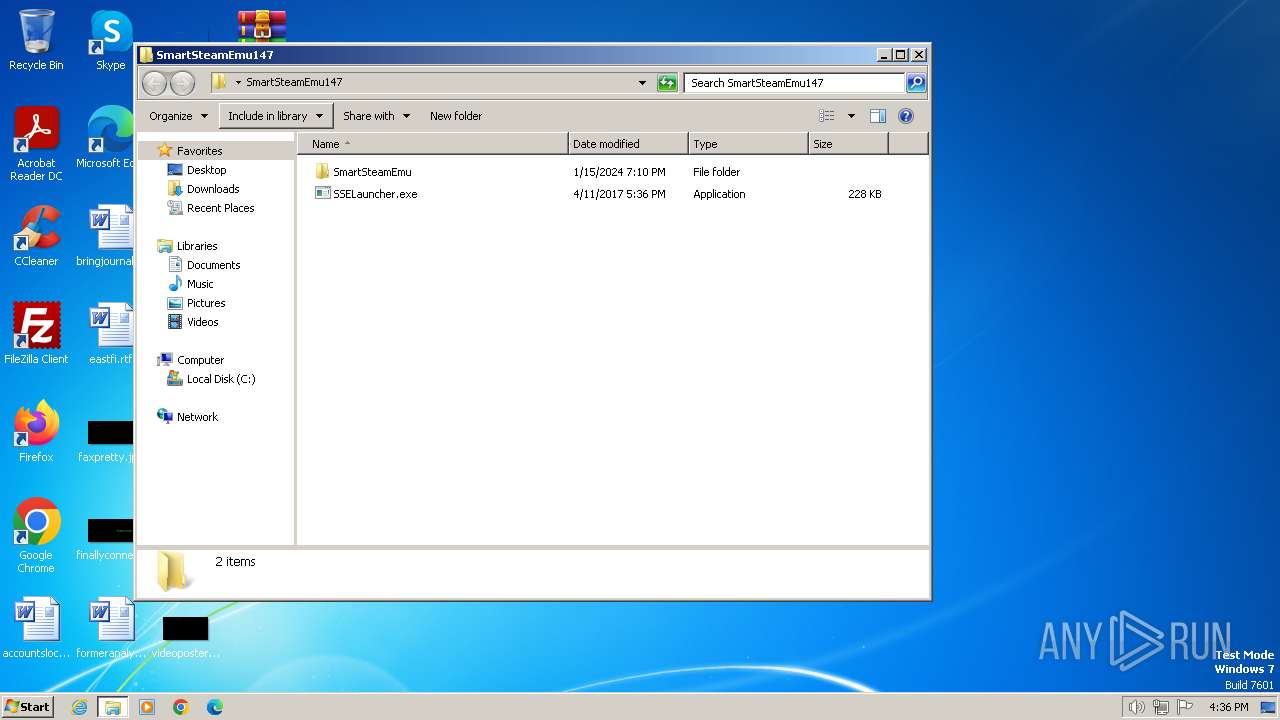
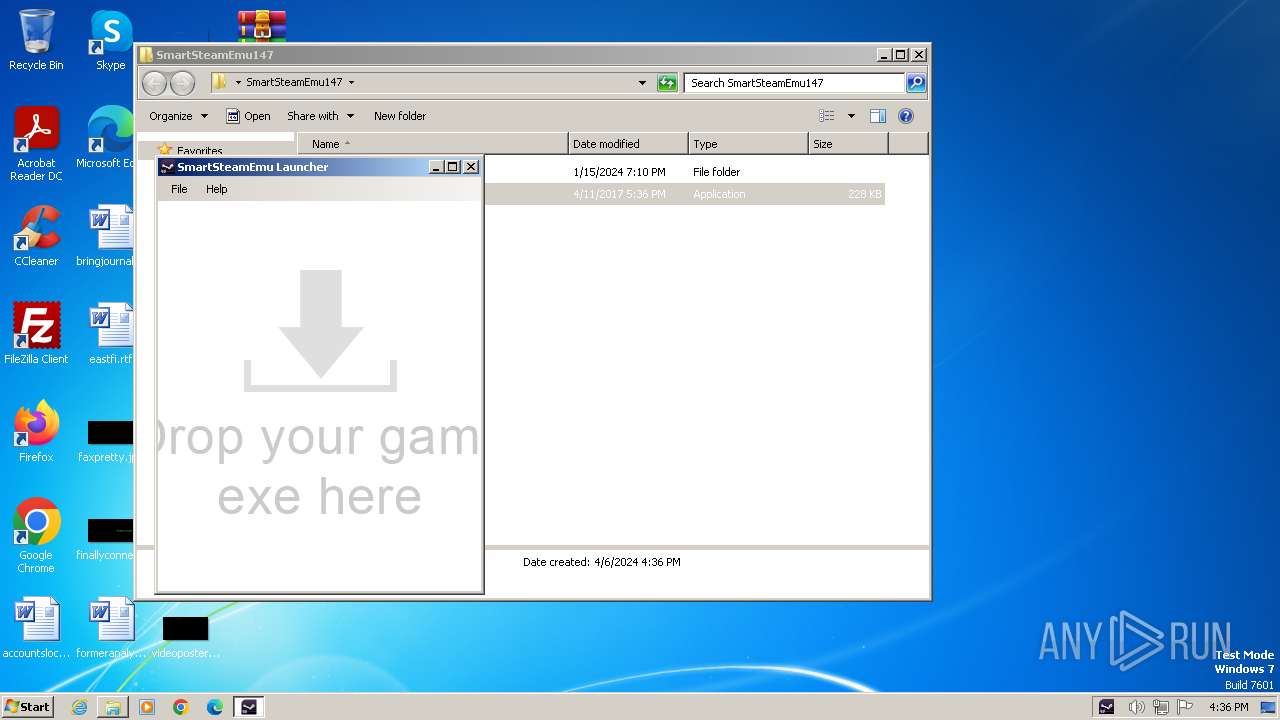
| File name: | SmartSteamEmu147.7z |
| Full analysis: | https://app.any.run/tasks/77949a3d-609d-49e2-870a-b60b2979a46b |
| Verdict: | Malicious activity |
| Analysis date: | April 06, 2024, 15:35:36 |
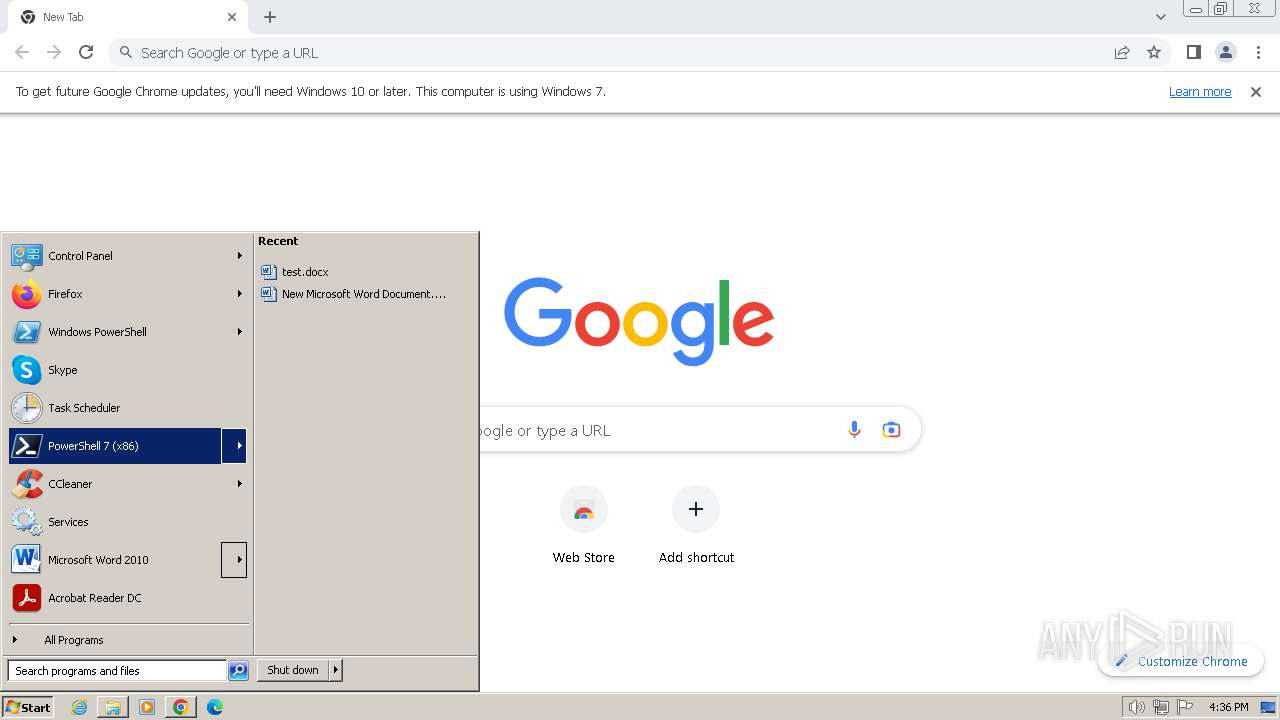
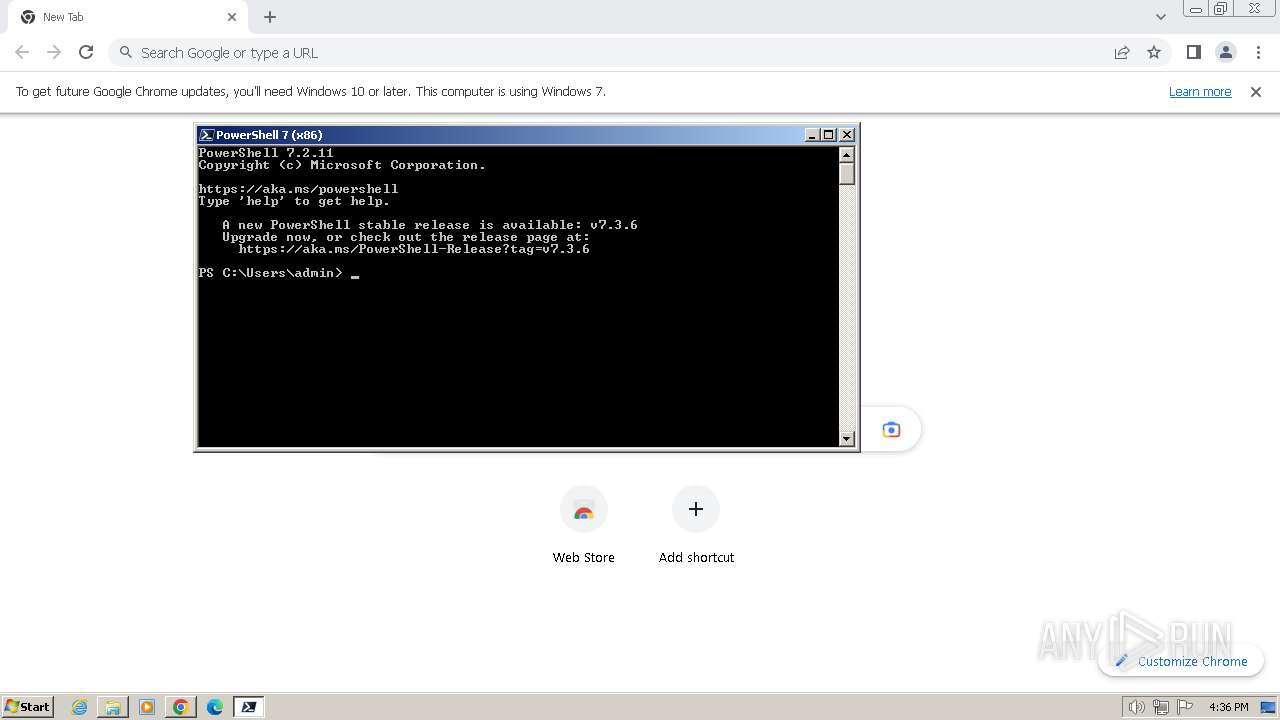
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
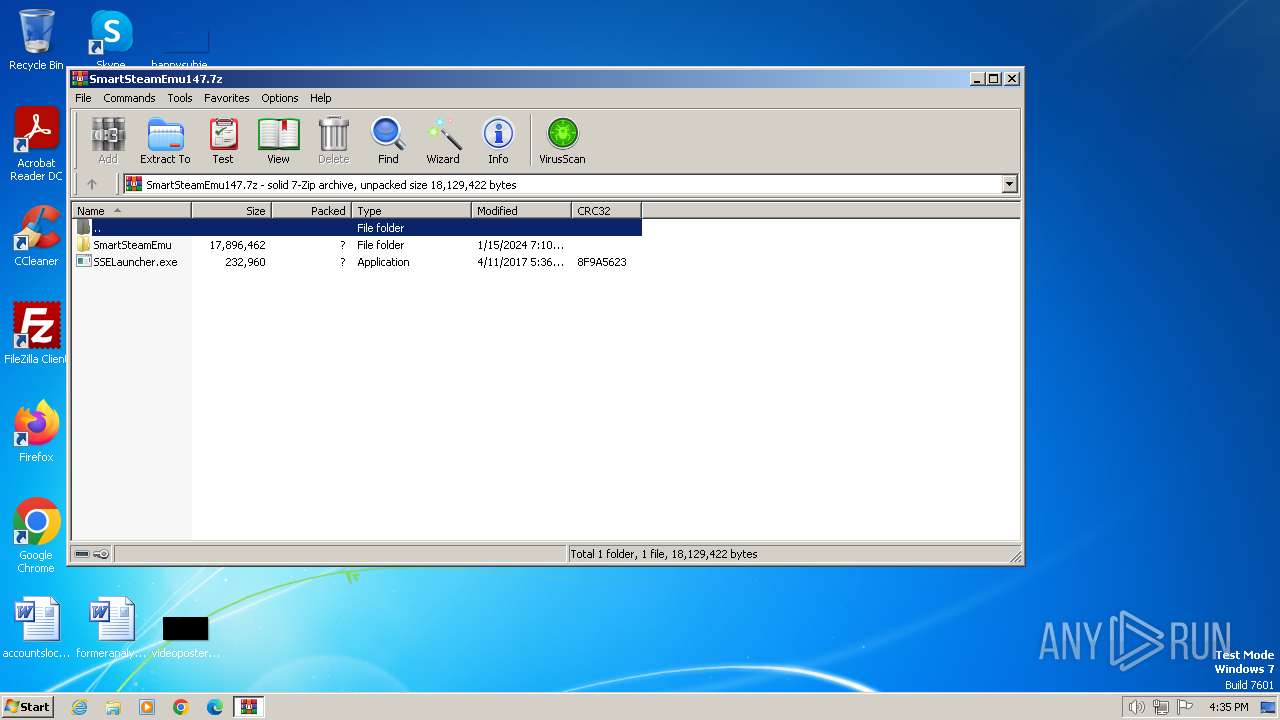
| MIME: | application/x-7z-compressed |
| File info: | 7-zip archive data, version 0.4 |
| MD5: | B7969A4A6F7B14A4825F730582E2D07B |
| SHA1: | 6033BAD4C5271DFF1025E864EAB5F6BB7677D49F |
| SHA256: | CEBB06642902082315B6BC4224A224429C34A6C1FACB7F296897A0799ABCB3DA |
| SSDEEP: | 98304:VGP9qRQUiebZ/flQH3bDELMc+Rq4FIbvFmK76dksnFwPQ/QHY8xwZm2z51GRE7oe:jWzEXS3 |
MALICIOUS
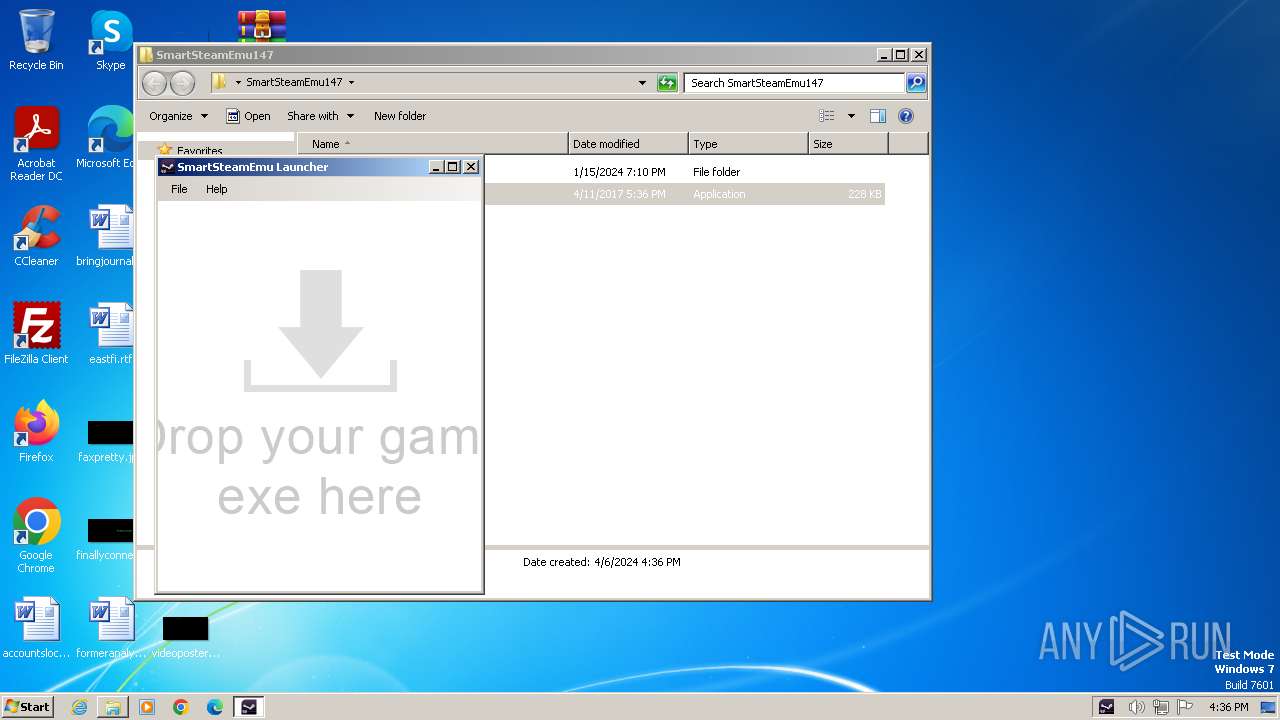
Drops the executable file immediately after the start
- WinRAR.exe (PID: 1836)
SUSPICIOUS
Reads the date of Windows installation
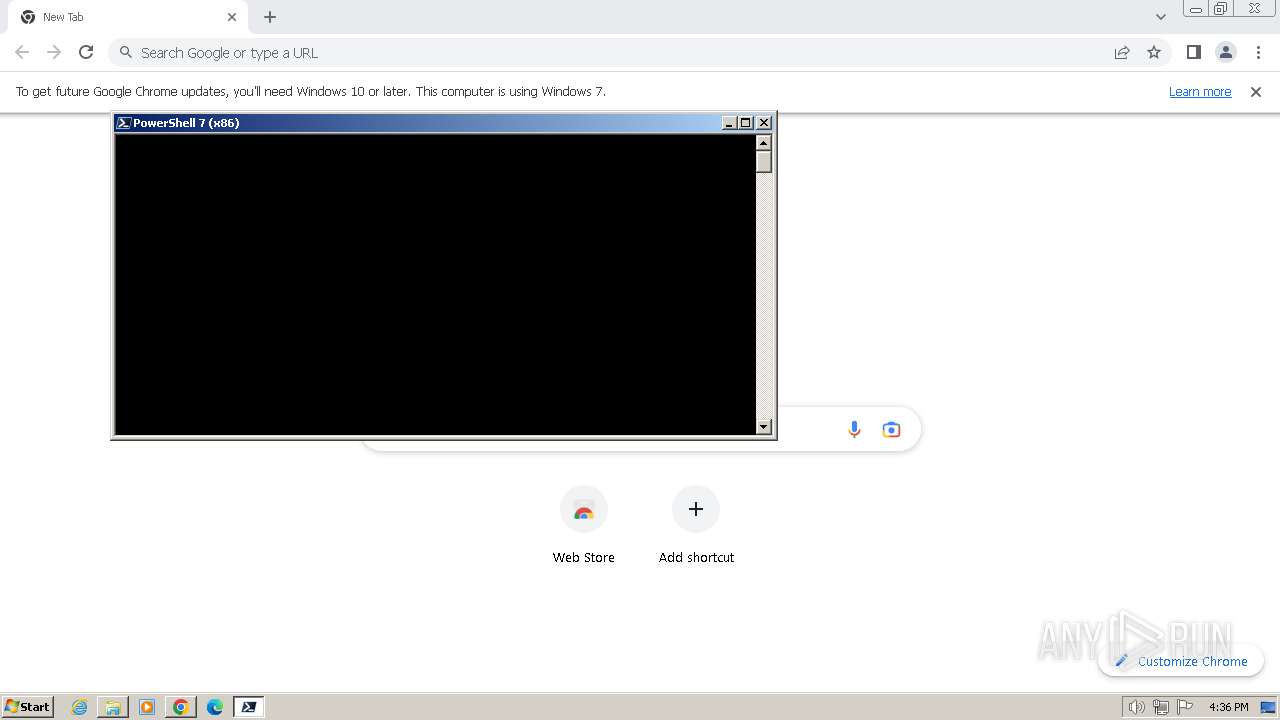
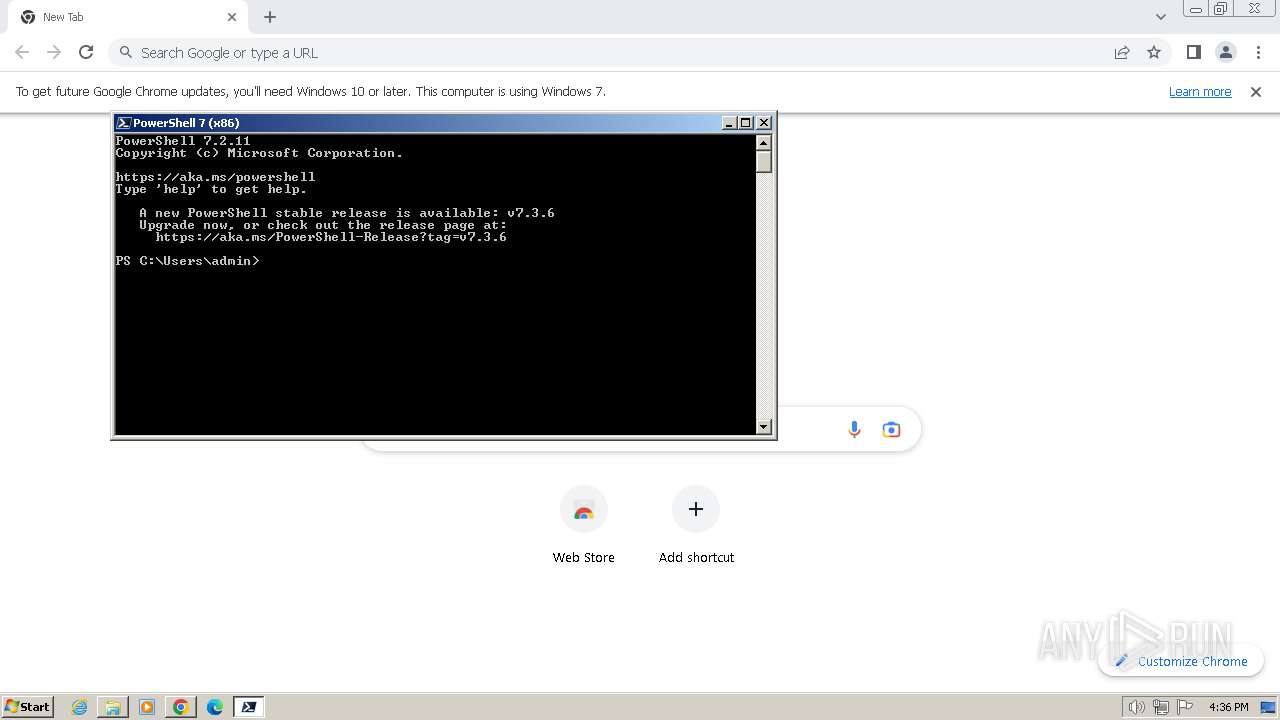
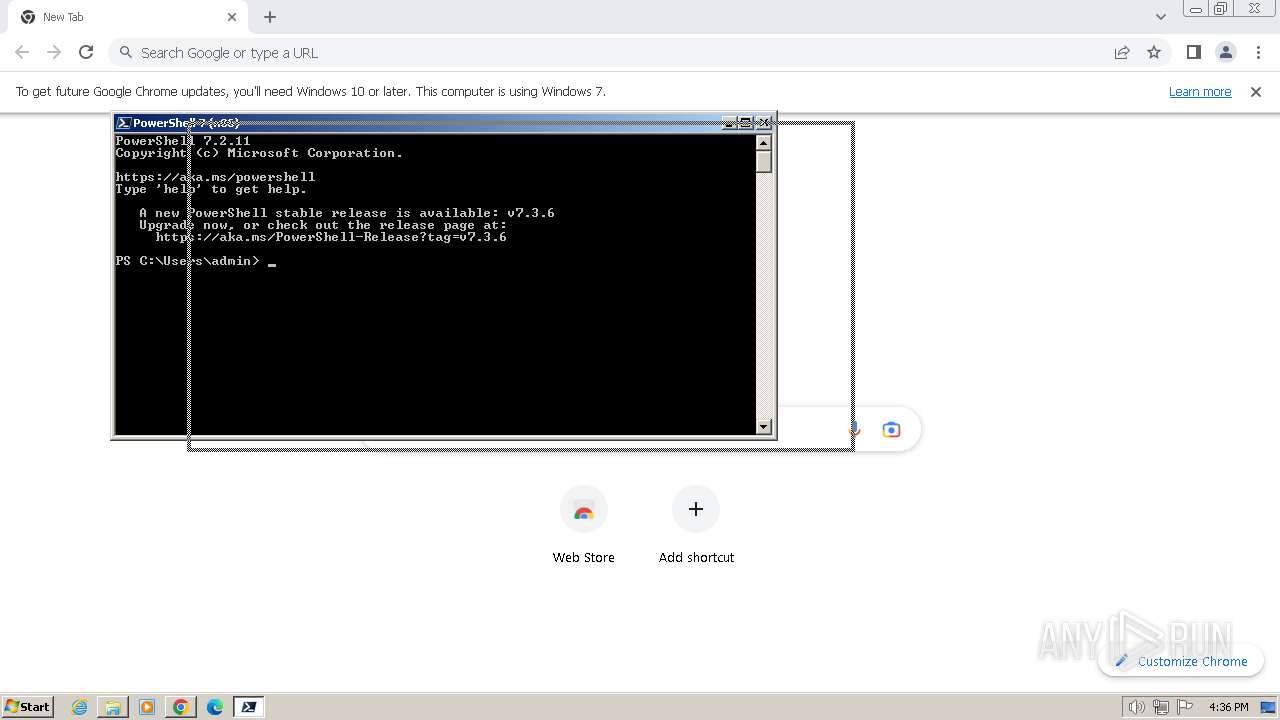
- pwsh.exe (PID: 3456)
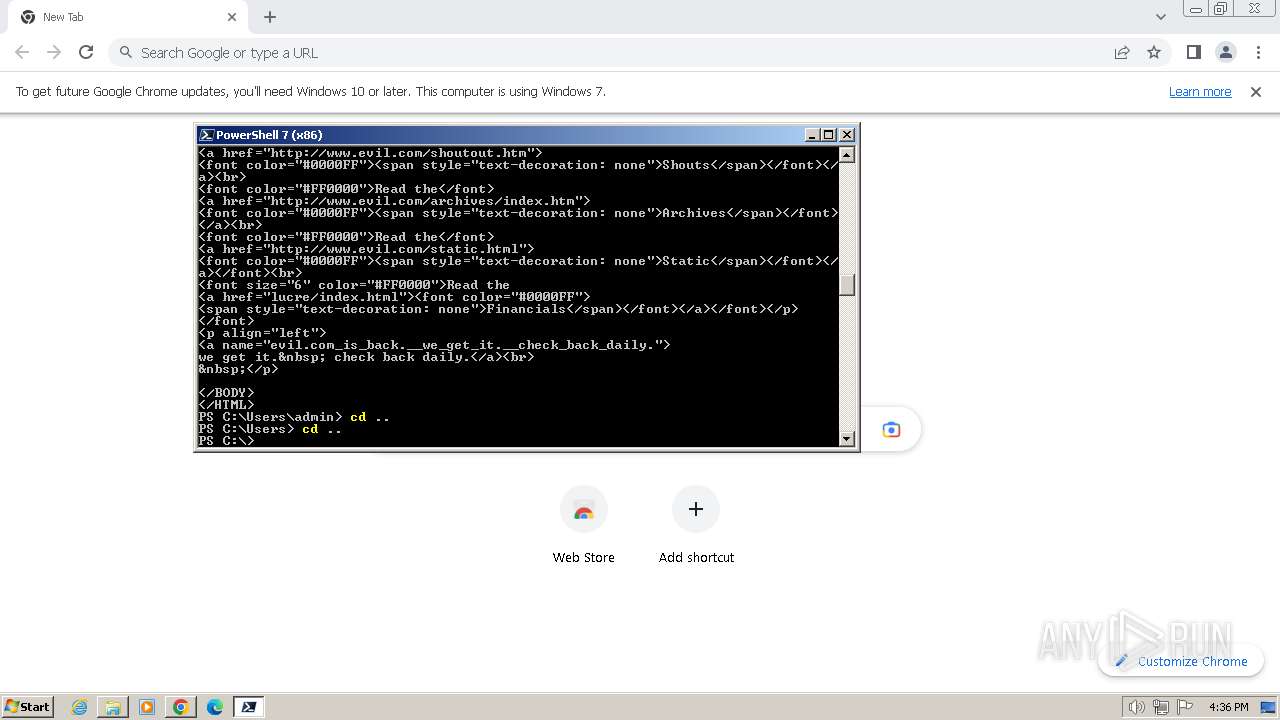
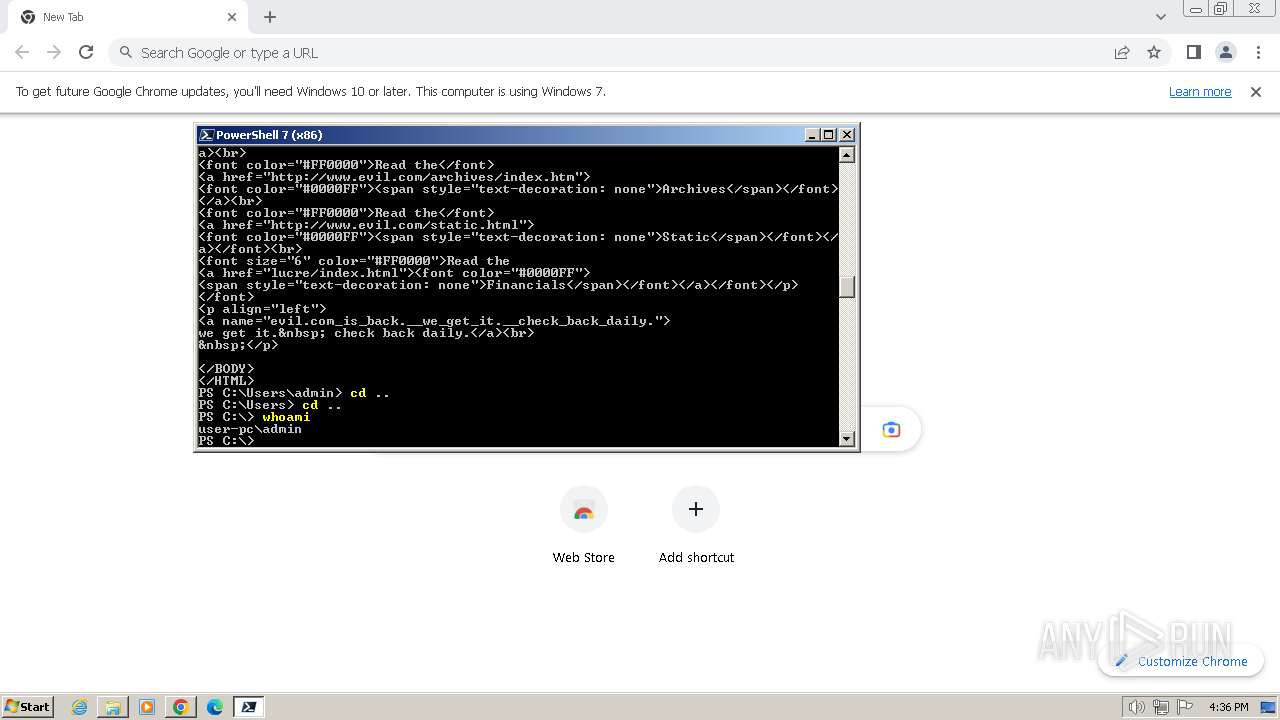
Identifying current user with WHOAMI command
- pwsh.exe (PID: 3456)
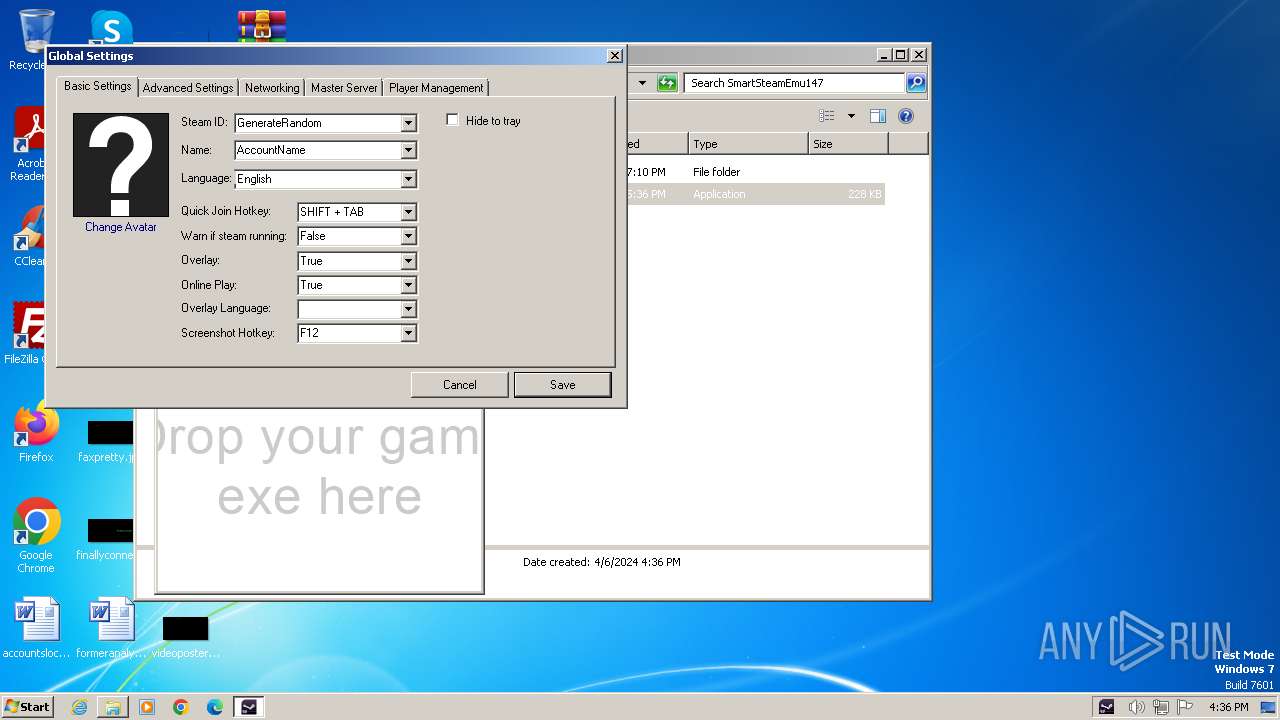
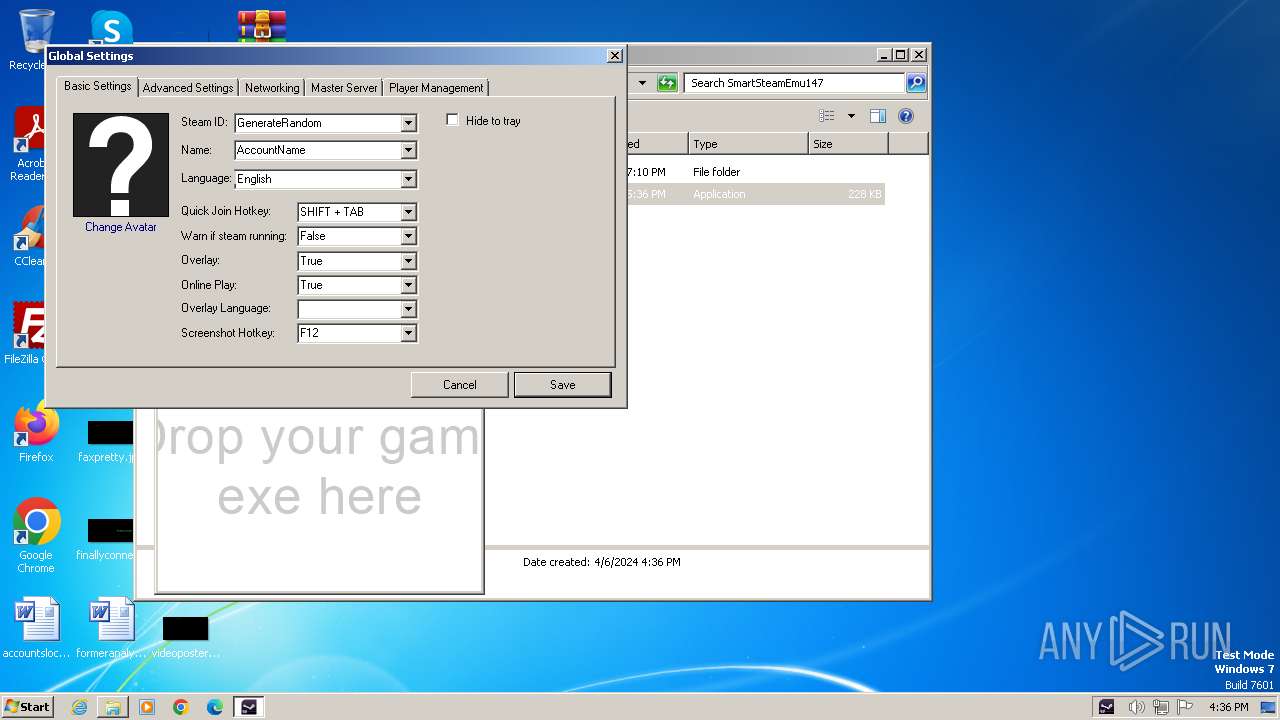
INFO
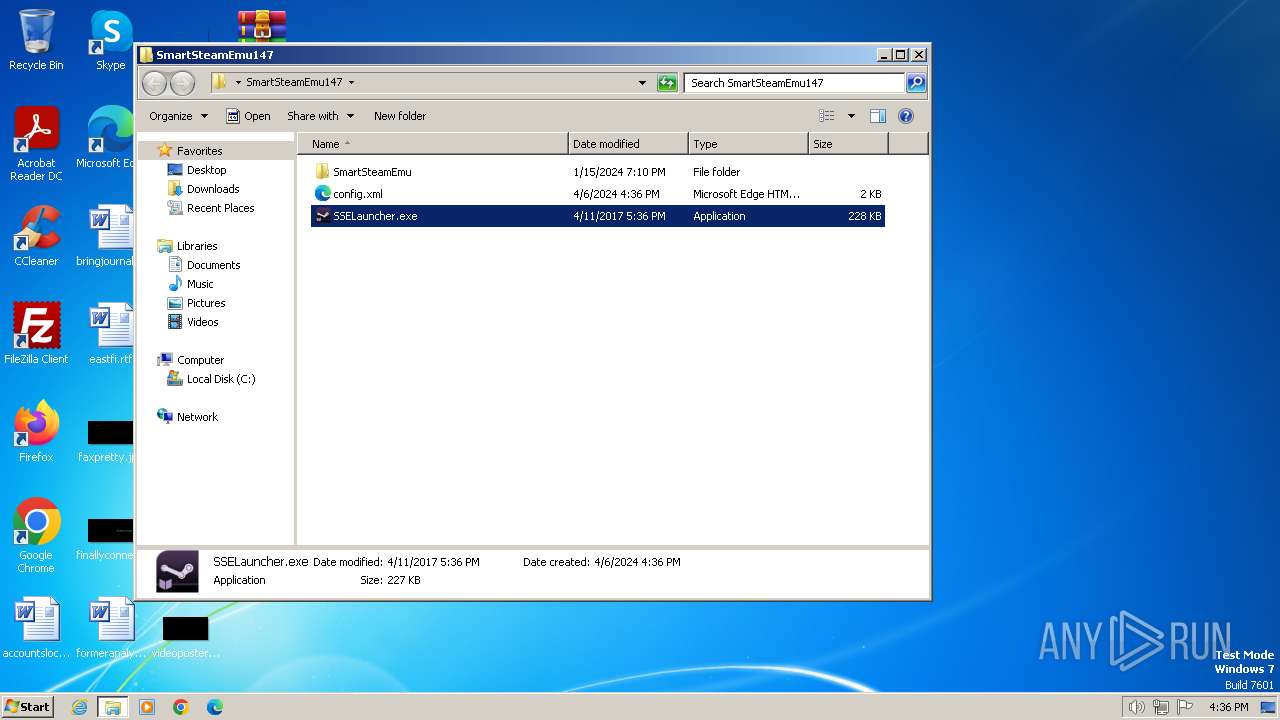
Reads the machine GUID from the registry
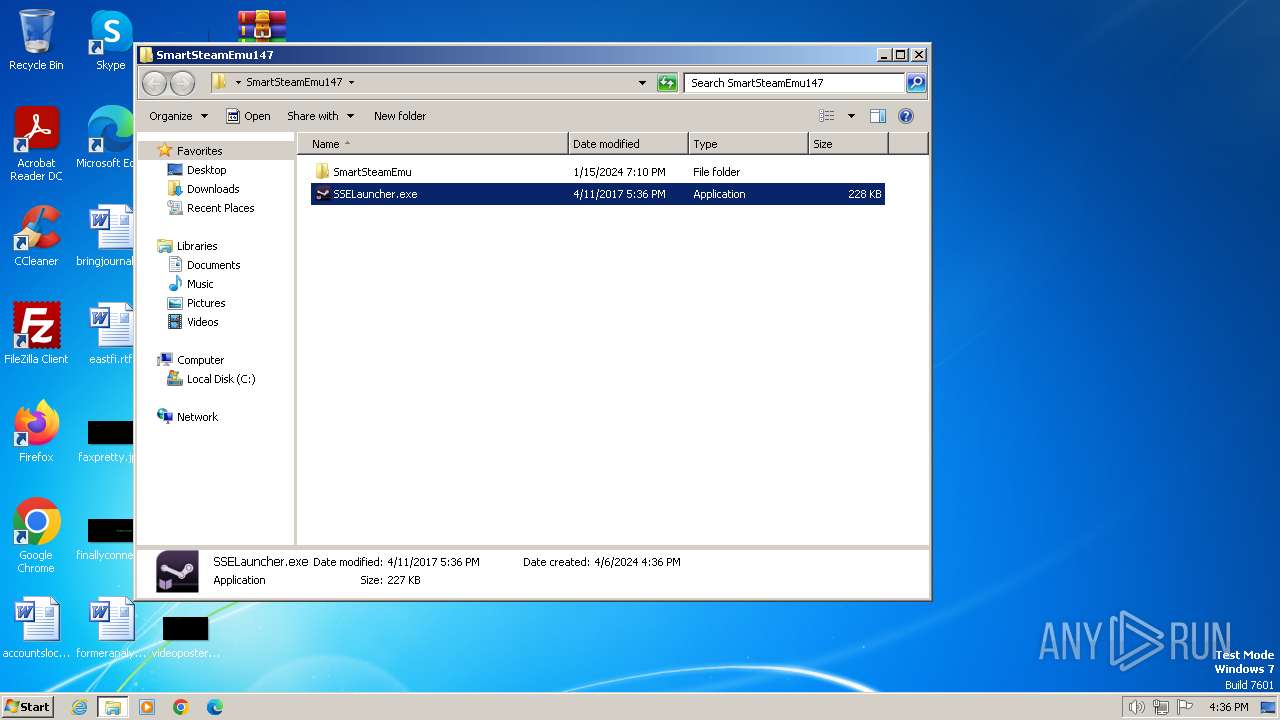
- SSELauncher.exe (PID: 1888)
Reads the computer name
- SSELauncher.exe (PID: 1888)
- pwsh.exe (PID: 3456)
- curl.exe (PID: 3084)
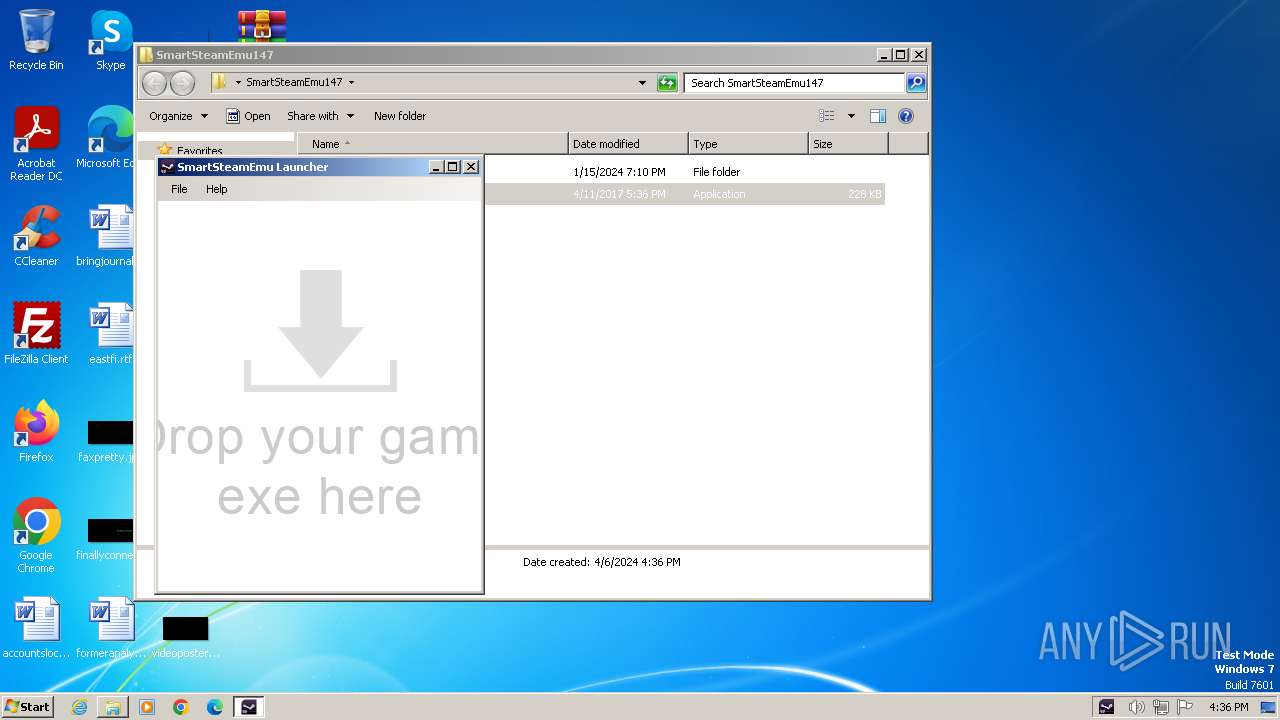
Manual execution by a user
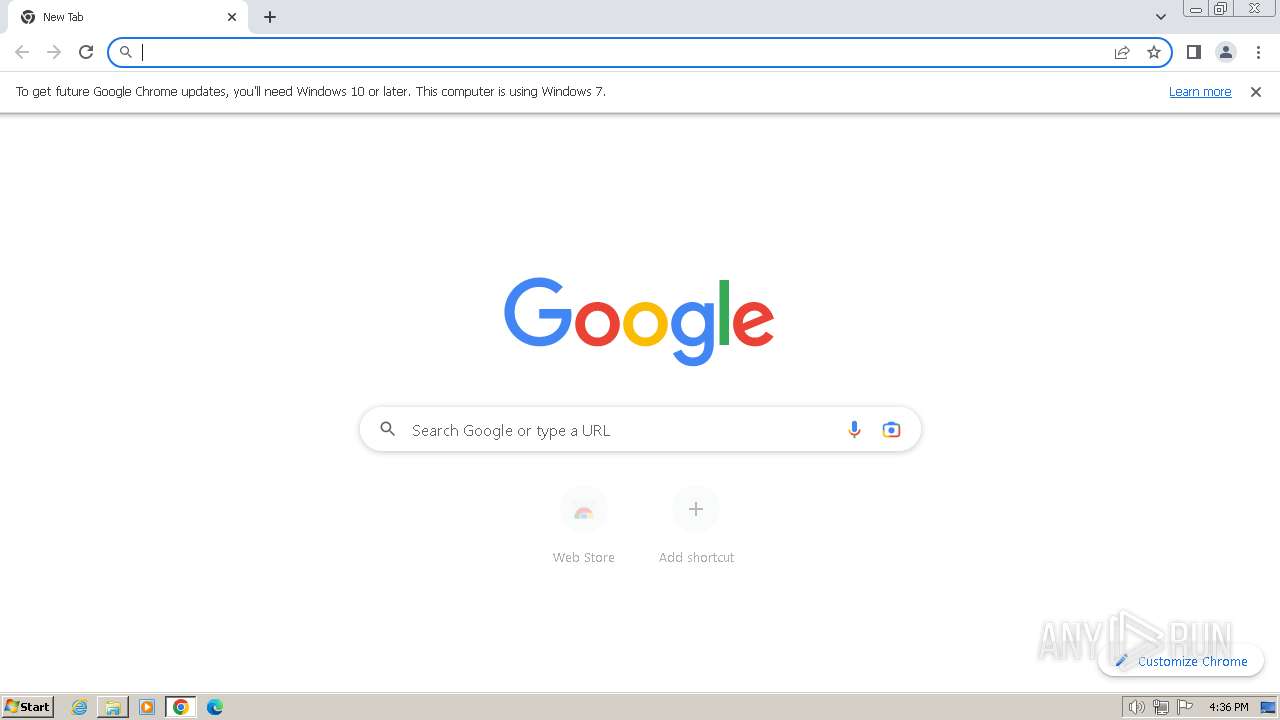
- chrome.exe (PID: 2484)
- pwsh.exe (PID: 3456)
- SSELauncher.exe (PID: 1888)
Checks supported languages
- pwsh.exe (PID: 3456)
- curl.exe (PID: 3084)
- SSELauncher.exe (PID: 1888)
Drops the executable file immediately after the start
- chrome.exe (PID: 2820)
- chrome.exe (PID: 3408)
Application launched itself
- chrome.exe (PID: 2484)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .7z | | | 7-Zip compressed archive (v0.4) (57.1) |
|---|---|---|
| .7z | | | 7-Zip compressed archive (gen) (42.8) |
Total processes
67
Monitored processes
24
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 572 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --mojo-platform-channel-handle=3636 --field-trial-handle=1168,i,9610512206371427143,13419056760584964019,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 840 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --disable-quic --mojo-platform-channel-handle=1412 --field-trial-handle=1168,i,9610512206371427143,13419056760584964019,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1768 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --mojo-platform-channel-handle=2056 --field-trial-handle=1168,i,9610512206371427143,13419056760584964019,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
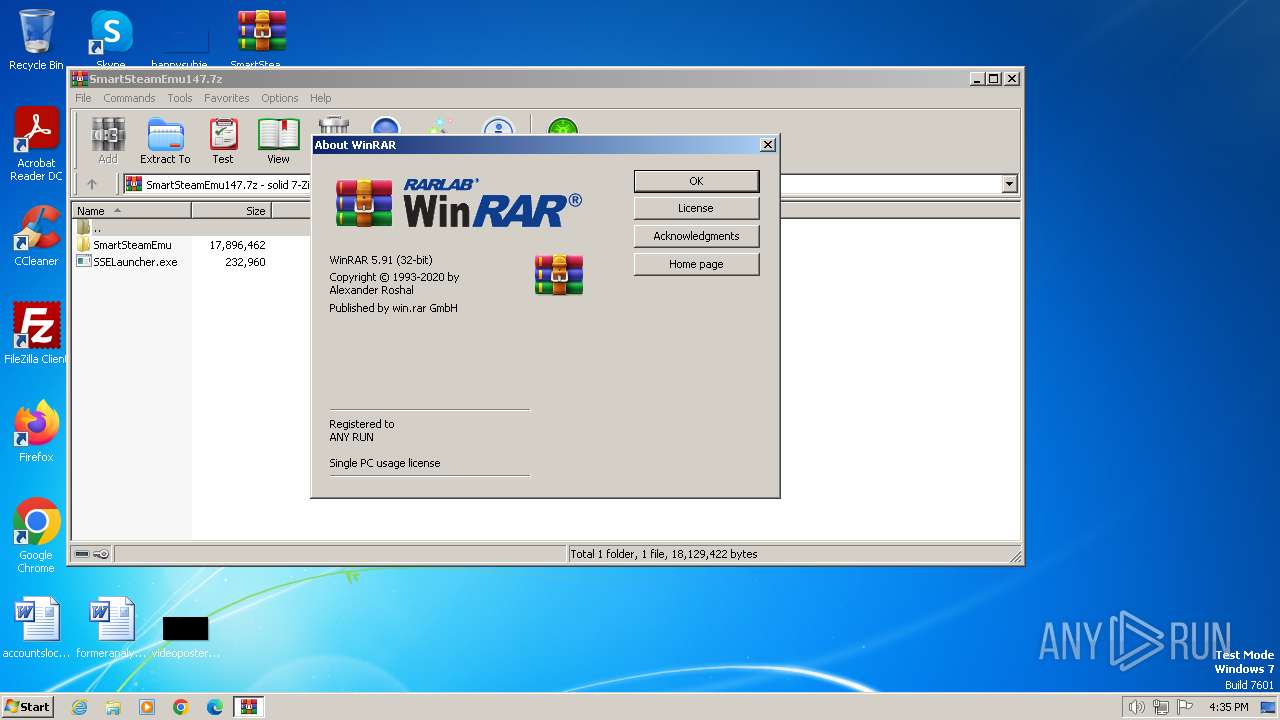
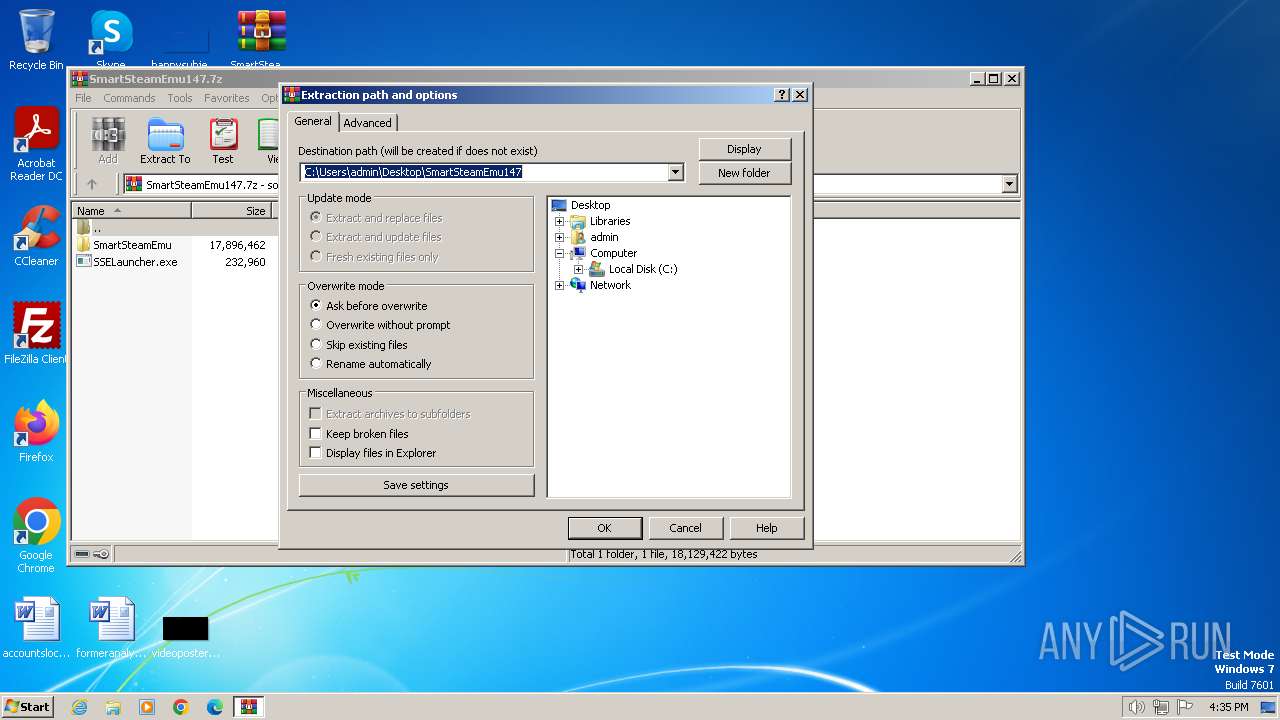
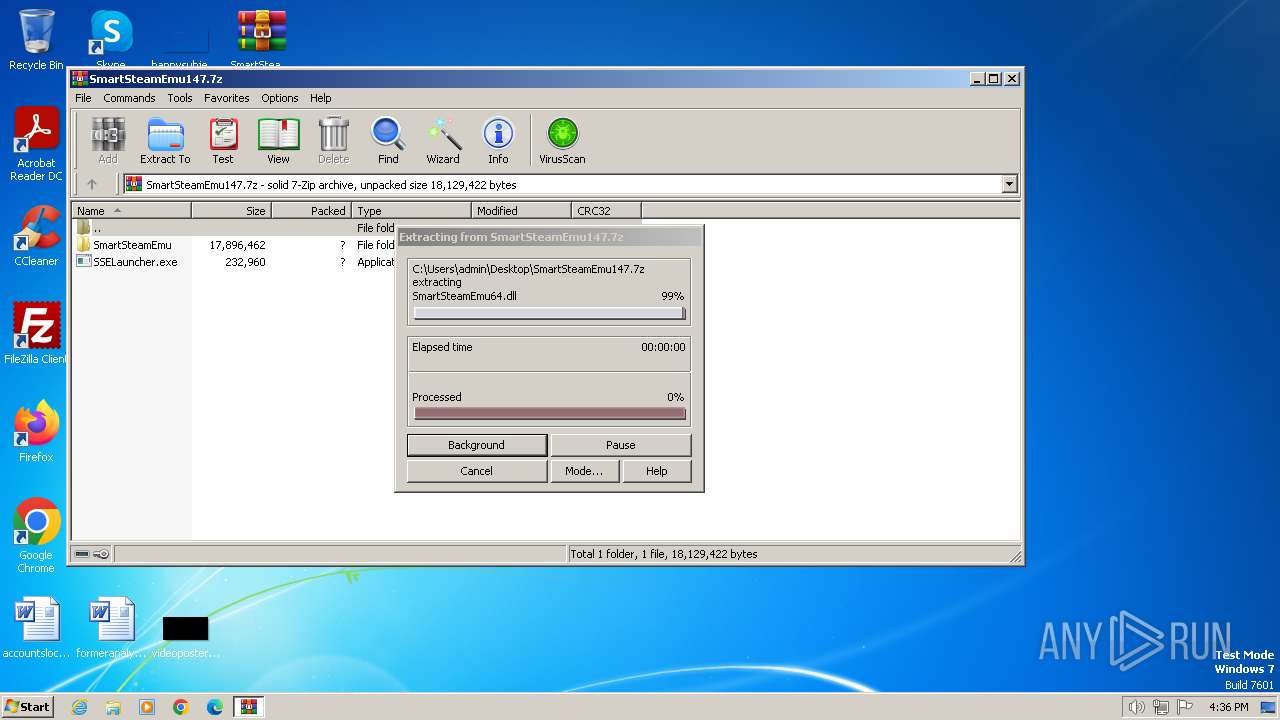
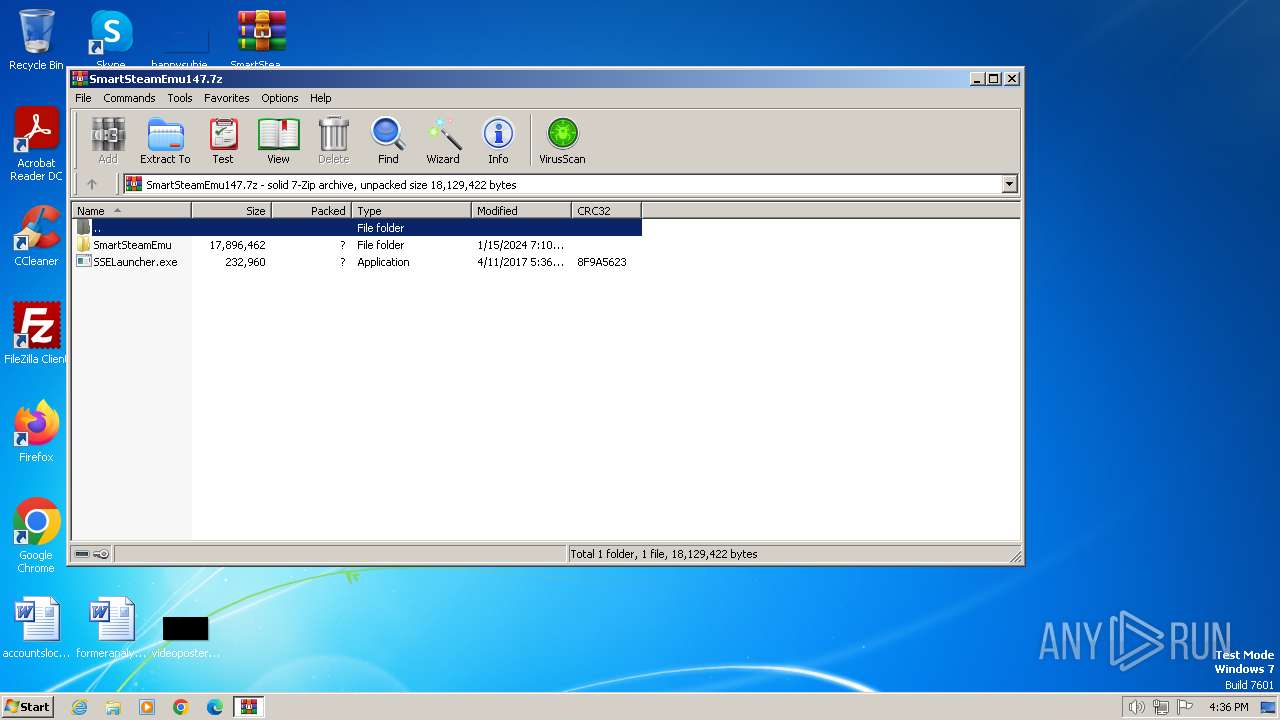
| 1836 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Desktop\SmartSteamEmu147.7z" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
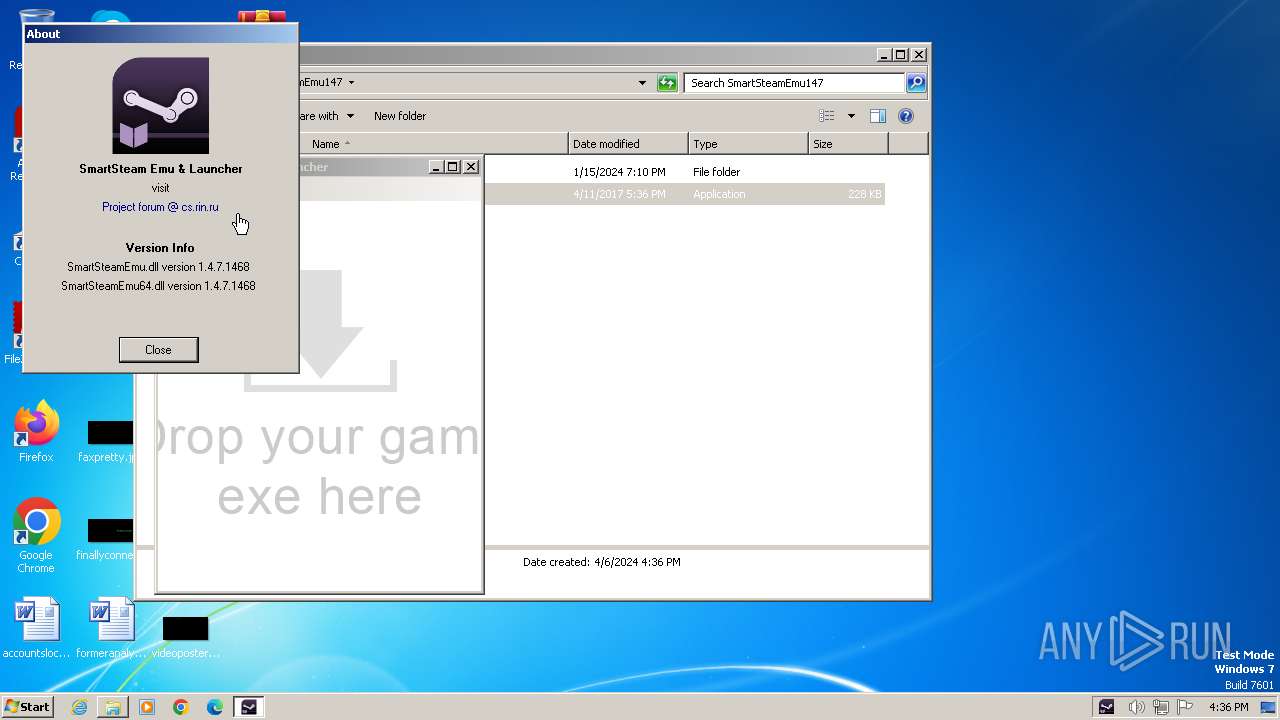
| 1888 | "C:\Users\admin\Desktop\SmartSteamEmu147\SSELauncher.exe" | C:\Users\admin\Desktop\SmartSteamEmu147\SSELauncher.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: SSELauncher Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 1892 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --gpu-preferences=UAAAAAAAAADgAAAYAAAAAAAAAAAAAAAAAABgAAAAAAAwAAAAAAAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAEgAAAAAAAAASAAAAAAAAAAYAAAAAgAAABAAAAAAAAAAGAAAAAAAAAAQAAAAAAAAAAAAAAAOAAAAEAAAAAAAAAABAAAADgAAAAgAAAAAAAAACAAAAAAAAAA= --mojo-platform-channel-handle=1116 --field-trial-handle=1168,i,9610512206371427143,13419056760584964019,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 2020 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --first-renderer-process --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --mojo-platform-channel-handle=2136 --field-trial-handle=1168,i,9610512206371427143,13419056760584964019,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 109.0.5414.120 Modules
| |||||||||||||||
| 2484 | "C:\Program Files\Google\Chrome\Application\chrome.exe" "--disable-features=OptimizationGuideModelDownloading,OptimizationHintsFetching,OptimizationTargetPrediction,OptimizationHints" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Version: 109.0.5414.120 Modules
| |||||||||||||||
| 2772 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --disable-quic --mojo-platform-channel-handle=1612 --field-trial-handle=1168,i,9610512206371427143,13419056760584964019,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 109.0.5414.120 Modules
| |||||||||||||||
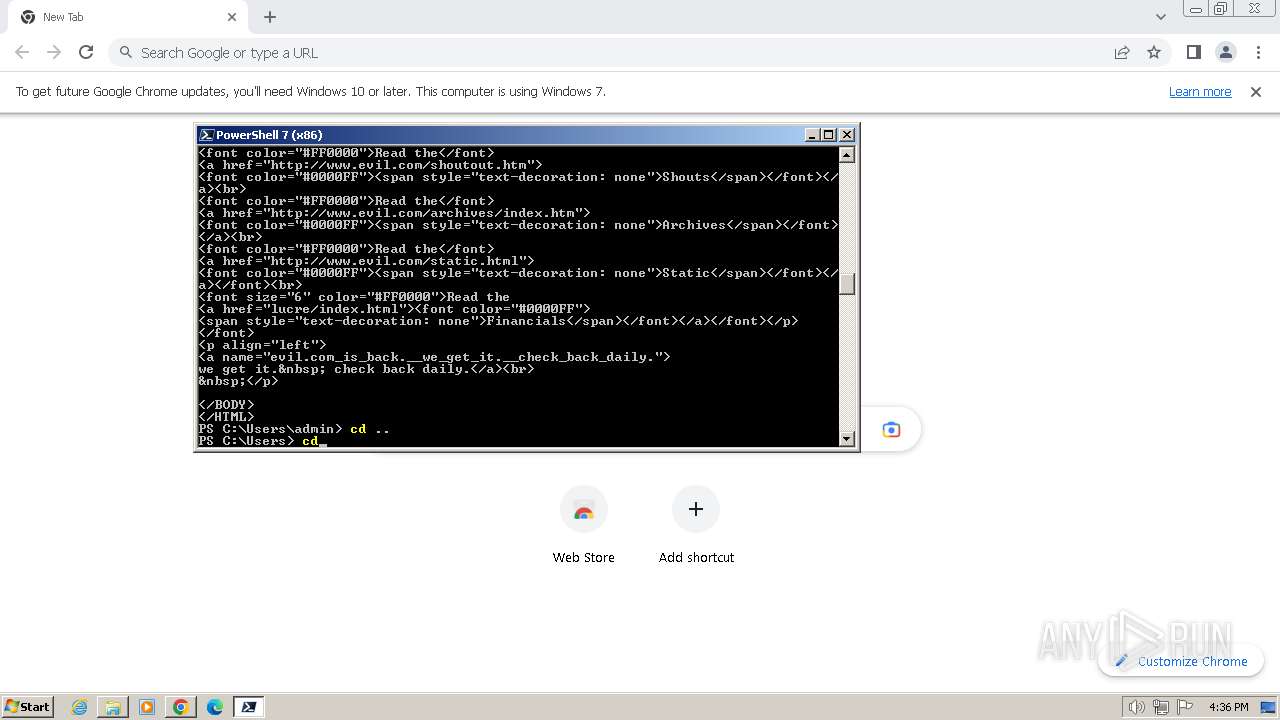
| 2784 | "C:\Windows\system32\whoami.exe" | C:\Windows\System32\whoami.exe | — | pwsh.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: whoami - displays logged on user information Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
16 776
Read events
16 607
Write events
167
Delete events
2
Modification events
| (PID) Process: | (1836) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (1836) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (1836) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1836) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\phacker.zip | |||
| (PID) Process: | (1836) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (1836) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\curl-8.5.0_1-win32-mingw.zip | |||
| (PID) Process: | (1836) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\SmartSteamEmu147.7z | |||
| (PID) Process: | (1836) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (1836) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (1836) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
Executable files
19
Suspicious files
233
Text files
44
Unknown types
114
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1836 | WinRAR.exe | C:\Users\admin\Desktop\SmartSteamEmu147\SmartSteamEmu\SmartSteamEmu\Common\218620\inventory.bin | binary | |
MD5:— | SHA256:— | |||
| 1836 | WinRAR.exe | C:\Users\admin\Desktop\SmartSteamEmu147\SmartSteamEmu\SmartSteamEmu\Common\218620\item_schema.bin | binary | |
MD5:— | SHA256:— | |||
| 1836 | WinRAR.exe | C:\Users\admin\Desktop\SmartSteamEmu147\SmartSteamEmu\SmartSteamEmu\Common\620\items.bin | binary | |
MD5:— | SHA256:— | |||
| 1836 | WinRAR.exe | C:\Users\admin\Desktop\SmartSteamEmu147\SmartSteamEmu\SmartSteamEmu\Common\730\items.bin | binary | |
MD5:— | SHA256:— | |||
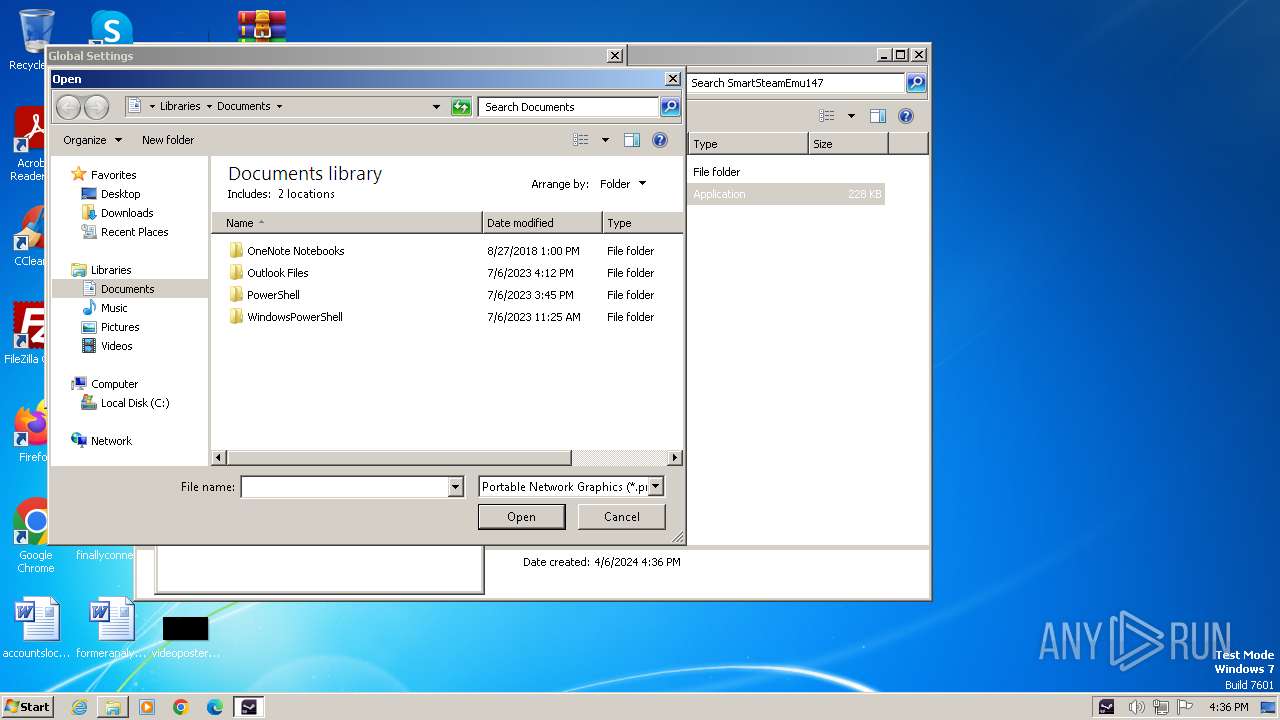
| 1836 | WinRAR.exe | C:\Users\admin\Desktop\SmartSteamEmu147\SmartSteamEmu\SmartSteamEmu\Common\avatar.png | image | |
MD5:— | SHA256:— | |||
| 1836 | WinRAR.exe | C:\Users\admin\Desktop\SmartSteamEmu147\SmartSteamEmu\SmartSteamEmu\Common\Readme.txt | text | |
MD5:— | SHA256:— | |||
| 1836 | WinRAR.exe | C:\Users\admin\Desktop\SmartSteamEmu147\SmartSteamEmu\SmartSteamEmu\Plugins\SSEFirewall.ini | text | |
MD5:— | SHA256:— | |||
| 1836 | WinRAR.exe | C:\Users\admin\Desktop\SmartSteamEmu147\SmartSteamEmu\SmartSteamEmu\Plugins\SSEOverlay\Language.ini | text | |
MD5:— | SHA256:— | |||
| 1836 | WinRAR.exe | C:\Users\admin\Desktop\SmartSteamEmu147\SmartSteamEmu\SmartSteamEmu.ini | text | |
MD5:— | SHA256:— | |||
| 1836 | WinRAR.exe | C:\Users\admin\Desktop\SmartSteamEmu147\SmartSteamEmu\SmartSteamEmu.txt | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
42
TCP/UDP connections
22
DNS requests
21
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
856 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | unknown | — | — | unknown |
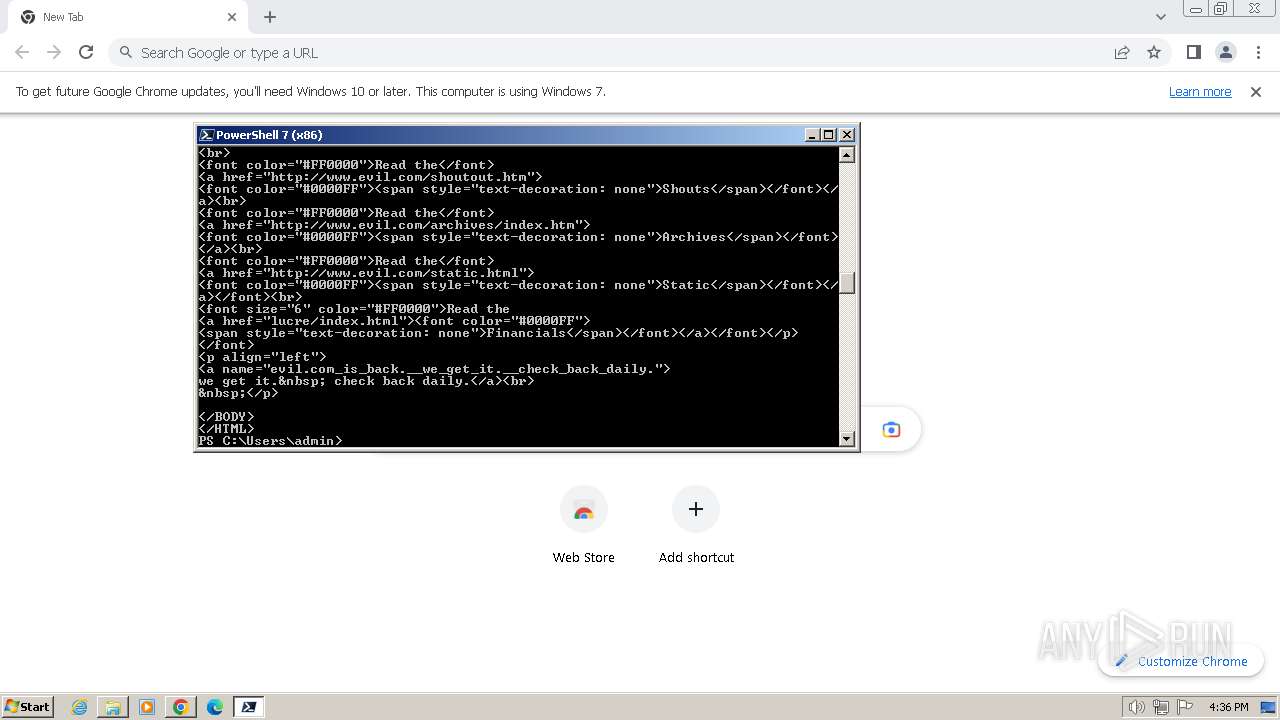
3084 | curl.exe | GET | 200 | 66.96.146.129:80 | http://evil.com/ | unknown | — | — | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | unknown | — | — | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | unknown | — | — | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | unknown | — | — | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | unknown | — | — | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | unknown | — | — | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | unknown | — | — | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | unknown | — | — | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 224.0.0.252:5355 | — | — | — | unknown |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
2484 | chrome.exe | 239.255.255.250:1900 | — | — | — | unknown |
840 | chrome.exe | 142.250.186.99:443 | clientservices.googleapis.com | GOOGLE | US | whitelisted |
840 | chrome.exe | 64.233.167.84:443 | accounts.google.com | GOOGLE | US | unknown |
840 | chrome.exe | 142.250.185.196:443 | www.google.com | GOOGLE | US | whitelisted |
2484 | chrome.exe | 224.0.0.251:5353 | — | — | — | unknown |
840 | chrome.exe | 142.250.181.227:443 | update.googleapis.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com |
| whitelisted |
update.googleapis.com |
| whitelisted |
aka.ms |
| whitelisted |
pscoretestdata.blob.core.windows.net |
| unknown |
evil.com |
| malicious |
www.googleapis.com |
| whitelisted |
dc.services.visualstudio.com |
| whitelisted |
edgedl.me.gvt1.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3084 | curl.exe | Attempted Information Leak | ET POLICY curl User-Agent Outbound |
Process | Message |
|---|---|
pwsh.exe | Profiler was prevented from loading notification profiler due to app settings.
Process ID (decimal): 3456. Message ID: [0x2509].
|