| download: | /client/FileZilla_3.69.0_win64_sponsored2-setup.exe |
| Full analysis: | https://app.any.run/tasks/ece94b08-acfd-4773-9677-89b22c92fb1d |
| Verdict: | Malicious activity |
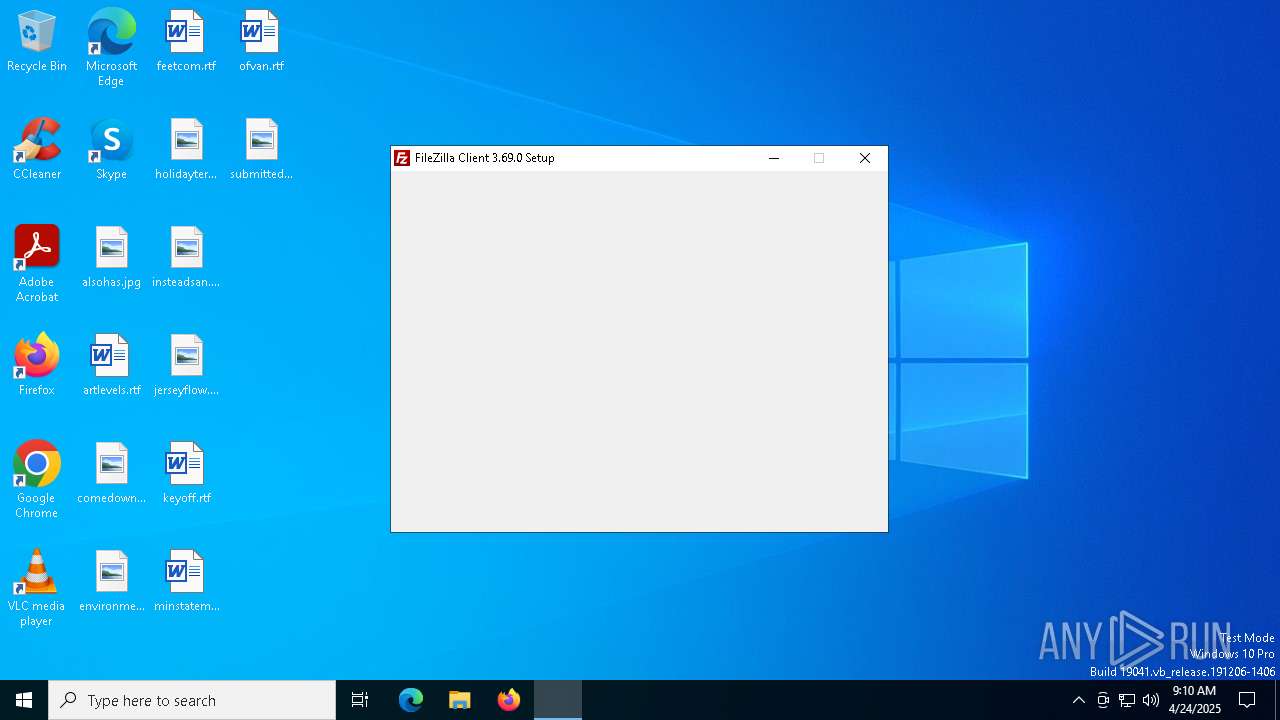
| Analysis date: | April 24, 2025, 09:10:08 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive, 5 sections |
| MD5: | D3C985FD7F82EEC589C0FB9AE9E3D7A1 |
| SHA1: | 50BA6E67312650AFB3E4D92A095F19B7F70628CC |
| SHA256: | CEB72A80FCD320148C1C3D45FB64EC77B9877657A26C4873323974EB6758D4BE |
| SSDEEP: | 98304:RxouhKFrEIdj6f6K7rKd3S3yayFkfvfRA2N3OeQG0fjGizYvgu4yICIimMiwR5cL:HYV0z48JIHrhuhdx0JoV6Qs/zMg |
MALICIOUS
Executing a file with an untrusted certificate
- FileZilla_3.69.0_win64_sponsored2-setup.exe (PID: 7352)
SUSPICIOUS
The process creates files with name similar to system file names
- FileZilla_3.69.0_win64_sponsored2-setup.exe (PID: 7352)
- FileZilla_3.69.0_win64_sponsored2-setup.exe (PID: 7480)
Malware-specific behavior (creating "System.dll" in Temp)
- FileZilla_3.69.0_win64_sponsored2-setup.exe (PID: 7352)
- FileZilla_3.69.0_win64_sponsored2-setup.exe (PID: 7480)
Executable content was dropped or overwritten
- FileZilla_3.69.0_win64_sponsored2-setup.exe (PID: 7352)
- FileZilla_3.69.0_win64_sponsored2-setup.exe (PID: 7480)
Application launched itself
- FileZilla_3.69.0_win64_sponsored2-setup.exe (PID: 7352)
Reads security settings of Internet Explorer
- FileZilla_3.69.0_win64_sponsored2-setup.exe (PID: 7352)
- FileZilla_3.69.0_win64_sponsored2-setup.exe (PID: 7480)
There is functionality for taking screenshot (YARA)
- FileZilla_3.69.0_win64_sponsored2-setup.exe (PID: 7480)
- FileZilla_3.69.0_win64_sponsored2-setup.exe (PID: 7352)
INFO
Checks supported languages
- FileZilla_3.69.0_win64_sponsored2-setup.exe (PID: 7352)
- FileZilla_3.69.0_win64_sponsored2-setup.exe (PID: 7480)
The sample compiled with english language support
- FileZilla_3.69.0_win64_sponsored2-setup.exe (PID: 7352)
- FileZilla_3.69.0_win64_sponsored2-setup.exe (PID: 7480)
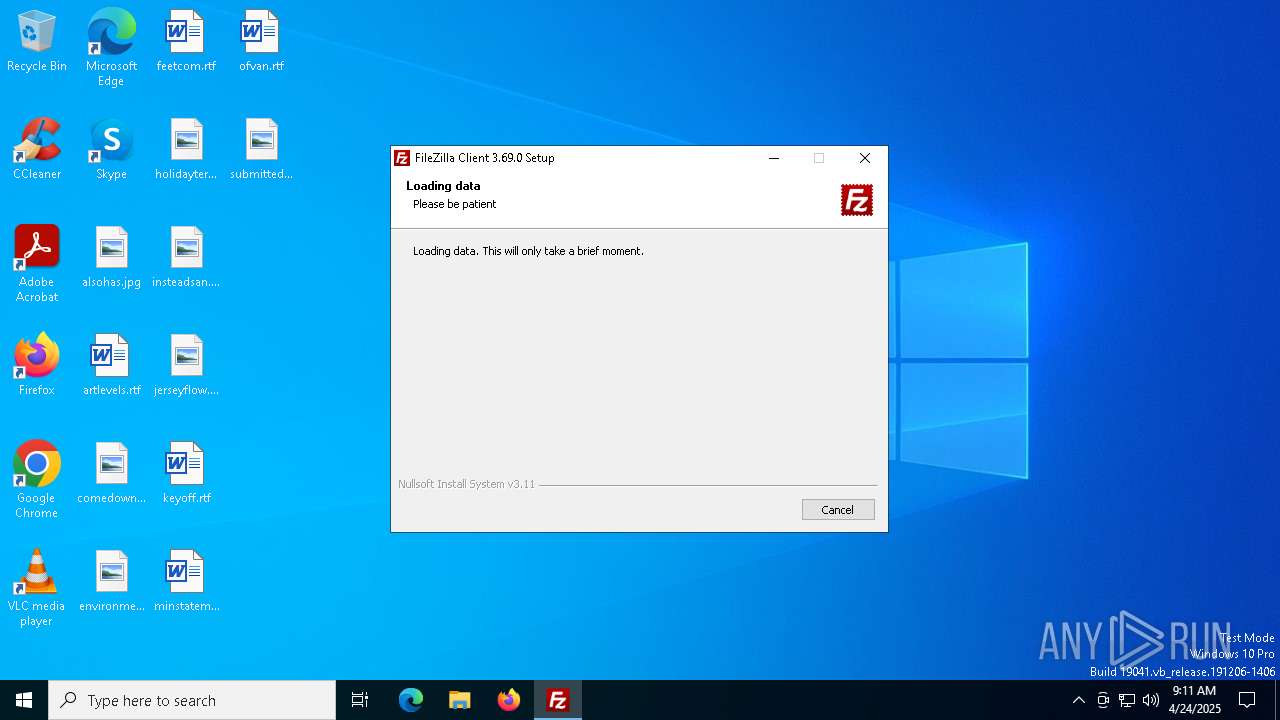
Create files in a temporary directory
- FileZilla_3.69.0_win64_sponsored2-setup.exe (PID: 7352)
- FileZilla_3.69.0_win64_sponsored2-setup.exe (PID: 7480)
Reads the computer name
- FileZilla_3.69.0_win64_sponsored2-setup.exe (PID: 7352)
- FileZilla_3.69.0_win64_sponsored2-setup.exe (PID: 7480)
Process checks computer location settings
- FileZilla_3.69.0_win64_sponsored2-setup.exe (PID: 7352)
FileZilla executable
- FileZilla_3.69.0_win64_sponsored2-setup.exe (PID: 7352)
Reads the software policy settings
- FileZilla_3.69.0_win64_sponsored2-setup.exe (PID: 7480)
Checks proxy server information
- FileZilla_3.69.0_win64_sponsored2-setup.exe (PID: 7480)
Reads the machine GUID from the registry
- FileZilla_3.69.0_win64_sponsored2-setup.exe (PID: 7480)
Creates files or folders in the user directory
- FileZilla_3.69.0_win64_sponsored2-setup.exe (PID: 7480)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2025:03:08 23:05:20+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 26624 |
| InitializedDataSize: | 139776 |
| UninitializedDataSize: | 2048 |
| EntryPoint: | 0x369f |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 3.69.0.0 |
| ProductVersionNumber: | 3.69.0.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
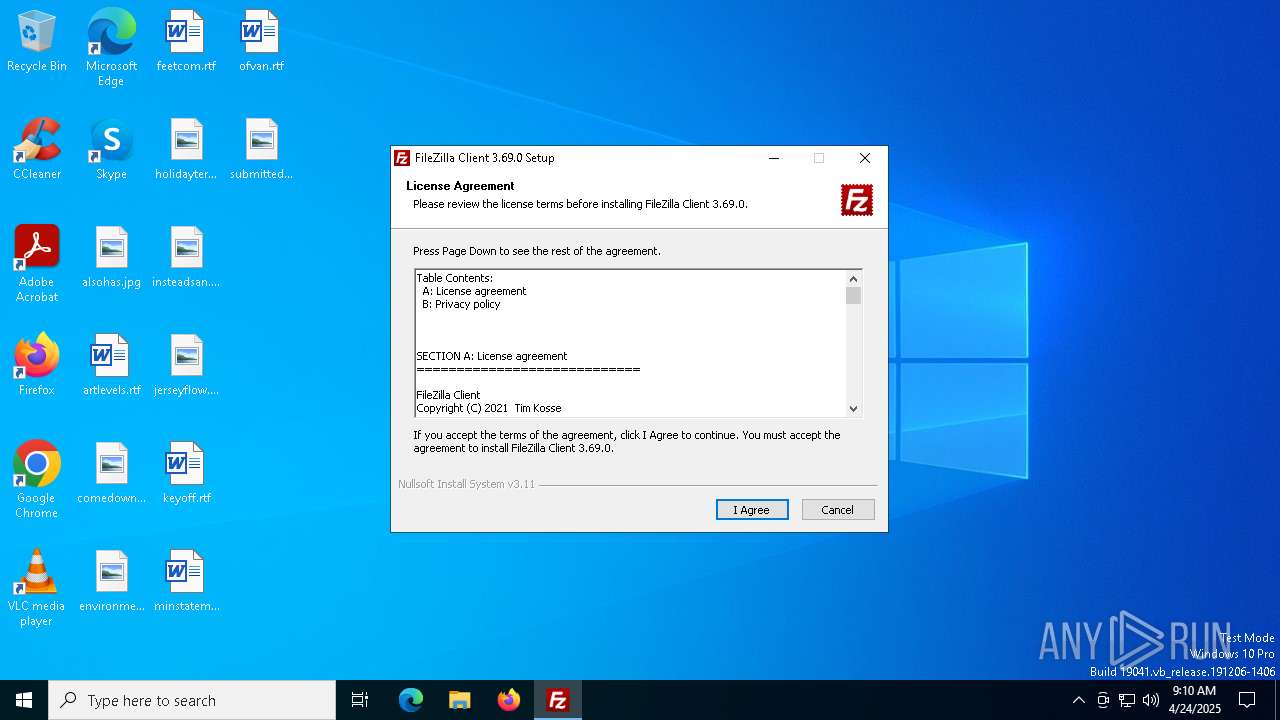
| CompanyName: | Tim Kosse |
| FileDescription: | FileZilla FTP Client |
| FileVersion: | 3.69.0 |
| LegalCopyright: | Tim Kosse |
| OriginalFileName: | FileZilla_3.69.0_win32-setup.exe |
| ProductName: | FileZilla |
| ProductVersion: | 3.69.0 |
Total processes
135
Monitored processes
4
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 7352 | "C:\Users\admin\AppData\Local\Temp\FileZilla_3.69.0_win64_sponsored2-setup.exe" | C:\Users\admin\AppData\Local\Temp\FileZilla_3.69.0_win64_sponsored2-setup.exe | explorer.exe | ||||||||||||
User: admin Company: Tim Kosse Integrity Level: MEDIUM Description: FileZilla FTP Client Version: 3.69.0 Modules
| |||||||||||||||
| 7480 | "C:\Users\admin\AppData\Local\Temp\FileZilla_3.69.0_win64_sponsored2-setup.exe" /UAC:40312 /NCRC | C:\Users\admin\AppData\Local\Temp\FileZilla_3.69.0_win64_sponsored2-setup.exe | FileZilla_3.69.0_win64_sponsored2-setup.exe | ||||||||||||
User: admin Company: Tim Kosse Integrity Level: HIGH Description: FileZilla FTP Client Version: 3.69.0 Modules
| |||||||||||||||
| 7488 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7520 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | — | SppExtComObj.Exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
1 078
Read events
1 072
Write events
4
Delete events
2
Modification events
| (PID) Process: | (7480) FileZilla_3.69.0_win64_sponsored2-setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\GCAPITemp |
| Operation: | write | Name: | test |
Value: te | |||
| (PID) Process: | (7480) FileZilla_3.69.0_win64_sponsored2-setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\GCAPITemp |
| Operation: | delete value | Name: | test |
Value: te | |||
| (PID) Process: | (7480) FileZilla_3.69.0_win64_sponsored2-setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\GCAPITemp |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (7480) FileZilla_3.69.0_win64_sponsored2-setup.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (7480) FileZilla_3.69.0_win64_sponsored2-setup.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (7480) FileZilla_3.69.0_win64_sponsored2-setup.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
Executable files
9
Suspicious files
2
Text files
5
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7480 | FileZilla_3.69.0_win64_sponsored2-setup.exe | C:\Users\admin\AppData\Local\Temp\nsnCA49.tmp\System.dll | executable | |
MD5:9B38A1B07A0EBC5C7E59E63346ECC2DB | SHA256:C881253DAFCF1322A771139B1A429EC1E78C507CA81A218A20DC1A4B25ABBFE7 | |||
| 7352 | FileZilla_3.69.0_win64_sponsored2-setup.exe | C:\Users\admin\AppData\Local\Temp\nslC519.tmp\UAC.dll | executable | |
MD5:ADB29E6B186DAA765DC750128649B63D | SHA256:2F7F8FC05DC4FD0D5CDA501B47E4433357E887BBFED7292C028D99C73B52DC08 | |||
| 7480 | FileZilla_3.69.0_win64_sponsored2-setup.exe | C:\Users\admin\AppData\Local\Temp\nsnCA49.tmp\INetC.dll | executable | |
MD5:640BFF73A5F8E37B202D911E4749B2E9 | SHA256:C1E568E25EC111184DEB1B87CFDA4BFEC529B1ABEAB39B66539D998012F33502 | |||
| 7480 | FileZilla_3.69.0_win64_sponsored2-setup.exe | C:\Users\admin\AppData\Local\Temp\nsnCA49.tmp\UAC.dll | executable | |
MD5:ADB29E6B186DAA765DC750128649B63D | SHA256:2F7F8FC05DC4FD0D5CDA501B47E4433357E887BBFED7292C028D99C73B52DC08 | |||
| 7480 | FileZilla_3.69.0_win64_sponsored2-setup.exe | C:\Users\admin\AppData\Local\Temp\nsnCA49.tmp\nsDialogs.dll | executable | |
MD5:8F0E7415F33843431DF308BB8E06AF81 | SHA256:BB49F15FA83452370047A7801E39FC7F64E70C7545B8999BB85AA4749EAA048B | |||
| 7480 | FileZilla_3.69.0_win64_sponsored2-setup.exe | C:\Users\admin\AppData\Local\Temp\nsq9C21.tmp | executable | |
MD5:F03205B2487FBDA78C05FE108B8D672E | SHA256:03617EF6705ECD575F209B1023C85E9F5E3AC174E2E2DE088553A4536CB930AE | |||
| 7480 | FileZilla_3.69.0_win64_sponsored2-setup.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\83D863F495E7D991917B3ABB3E1EB382_691FAAC5472BBA0ABBD4299D570E051A | binary | |
MD5:42C3860BF8351D16789799417FDB8C40 | SHA256:20EF2BE68FDF0A2966BA109492ED1EF446D53106ED4190C08D0DF2C39F463C3B | |||
| 7480 | FileZilla_3.69.0_win64_sponsored2-setup.exe | C:\Users\admin\AppData\Local\Temp\nszA6A2.tmp | image | |
MD5:3944AC469603D2D37D4D07D2A4461E03 | SHA256:99F62EAB1E884811C056FD7441249C4D0A41B34386D8B8B03F20CA0113F9FA48 | |||
| 7480 | FileZilla_3.69.0_win64_sponsored2-setup.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\IE\RR3E01RZ\AvastImage[1].bmp | image | |
MD5:1D3412FB6A97AF76D06C5A3A8155325B | SHA256:018BDCA28E7DA0D2B7CF8FFFE5833355D6BC653DAF4D5821C78AB68B1639CB9E | |||
| 7480 | FileZilla_3.69.0_win64_sponsored2-setup.exe | C:\Users\admin\AppData\Local\Temp\nsjA559.tmp | image | |
MD5:1D3412FB6A97AF76D06C5A3A8155325B | SHA256:018BDCA28E7DA0D2B7CF8FFFE5833355D6BC653DAF4D5821C78AB68B1639CB9E | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
14
TCP/UDP connections
30
DNS requests
19
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
7480 | FileZilla_3.69.0_win64_sponsored2-setup.exe | POST | 200 | 18.245.86.26:80 | http://api.playanext.com/httpapi | unknown | — | — | whitelisted |
7480 | FileZilla_3.69.0_win64_sponsored2-setup.exe | POST | 200 | 18.245.86.26:80 | http://api.playanext.com/httpapi | unknown | — | — | whitelisted |
7480 | FileZilla_3.69.0_win64_sponsored2-setup.exe | POST | 200 | 18.245.86.26:80 | http://api.playanext.com/httpapi | unknown | — | — | whitelisted |
7480 | FileZilla_3.69.0_win64_sponsored2-setup.exe | POST | 200 | 18.245.86.26:80 | http://api.playanext.com/httpapi | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.19.11.120:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7304 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7480 | FileZilla_3.69.0_win64_sponsored2-setup.exe | POST | 200 | 18.245.86.26:80 | http://api.playanext.com/httpapi | unknown | — | — | whitelisted |
7480 | FileZilla_3.69.0_win64_sponsored2-setup.exe | GET | 200 | 18.245.65.219:80 | http://ocsp.r2m03.amazontrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQqHI%2BsdmapawQncL1rpCEZZ8gTSAQUVdkYX9IczAHhWLS%2Bq9lVQgHXLgICEAcMPK7%2B7NwWI1AE5%2BRymUw%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.19.11.120:80 | crl.microsoft.com | Elisa Oyj | NL | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.219.150.101:80 | www.microsoft.com | AKAMAI-AS | CL | whitelisted |
3216 | svchost.exe | 172.211.123.249:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6544 | svchost.exe | 20.190.160.14:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 2.23.77.188:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
536 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2104 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
api.playanext.com |
| whitelisted |