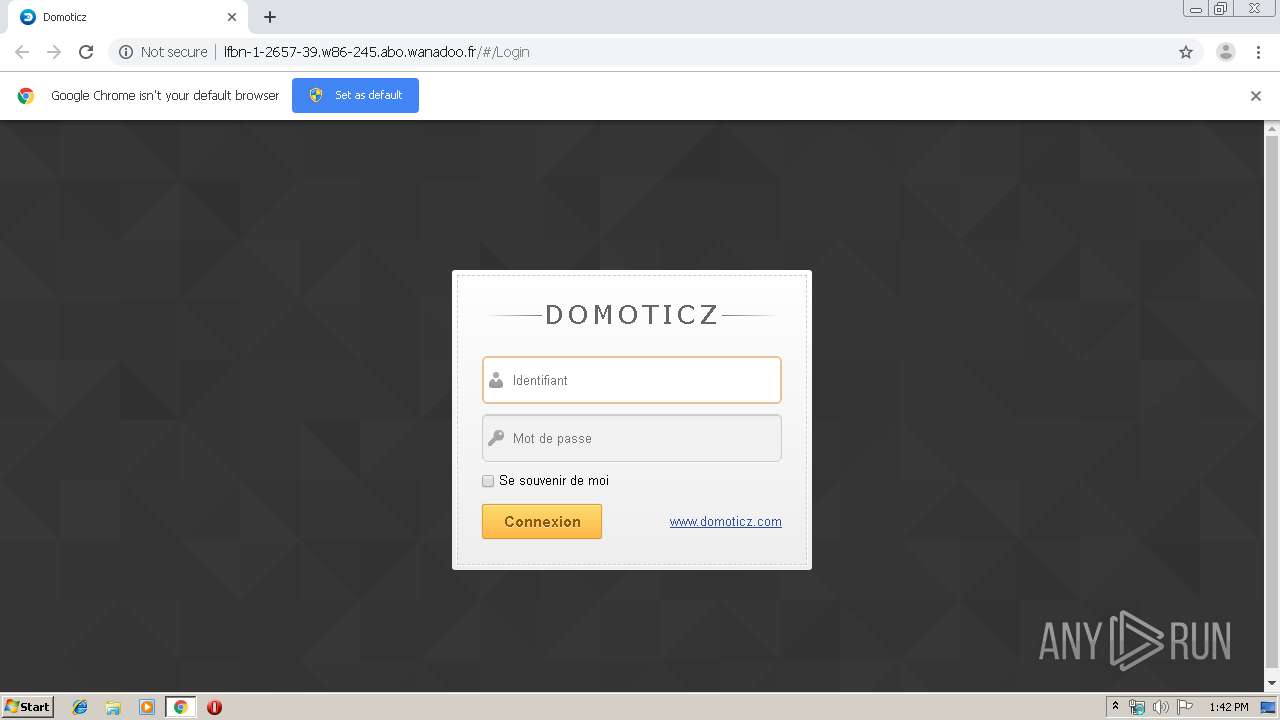
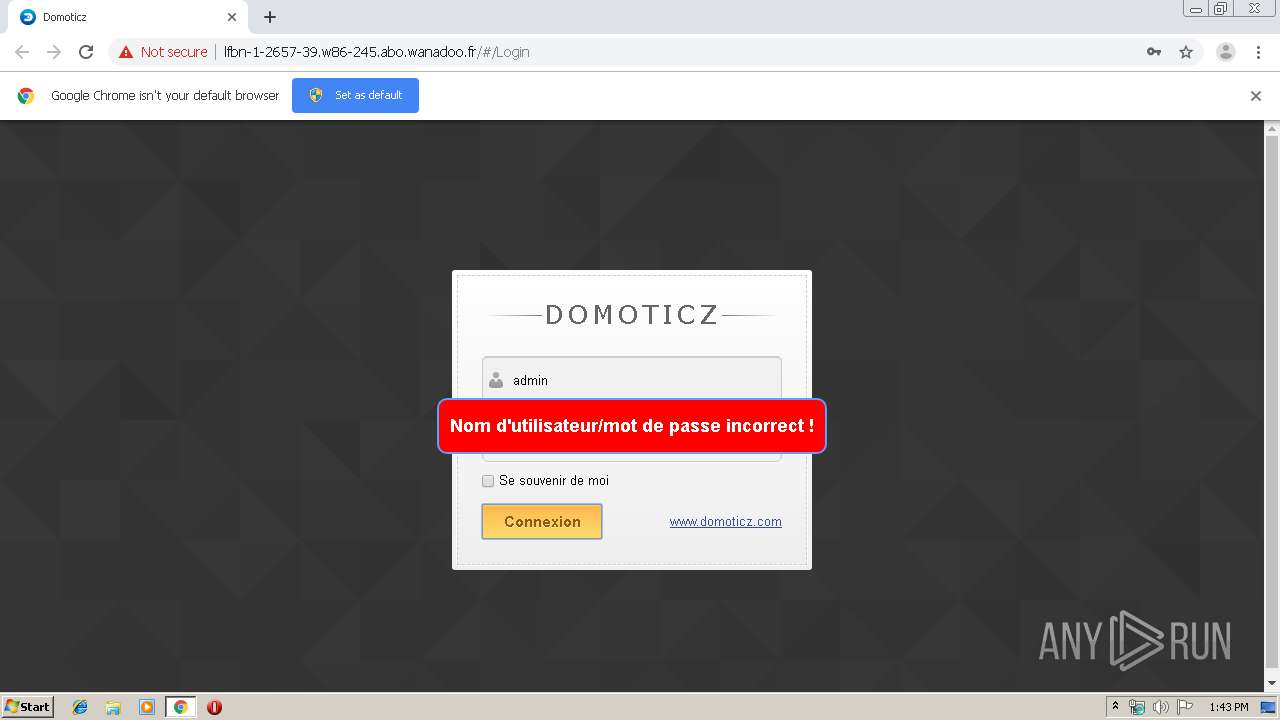
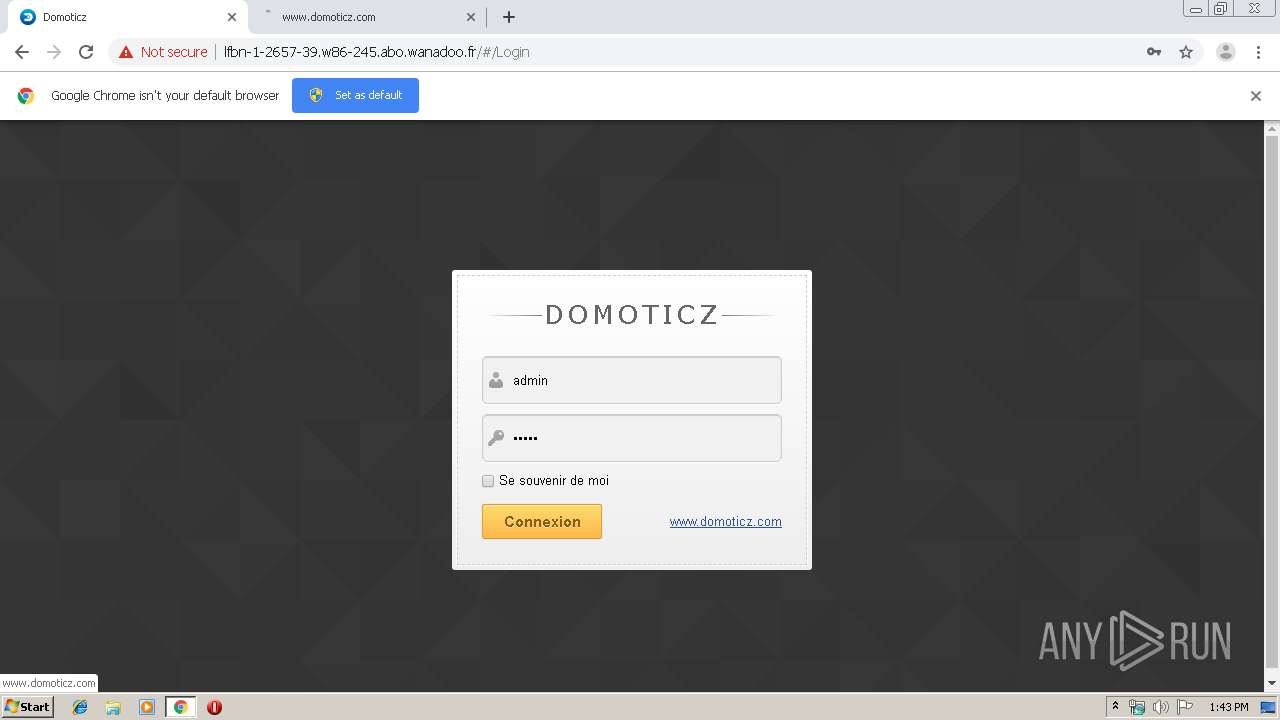
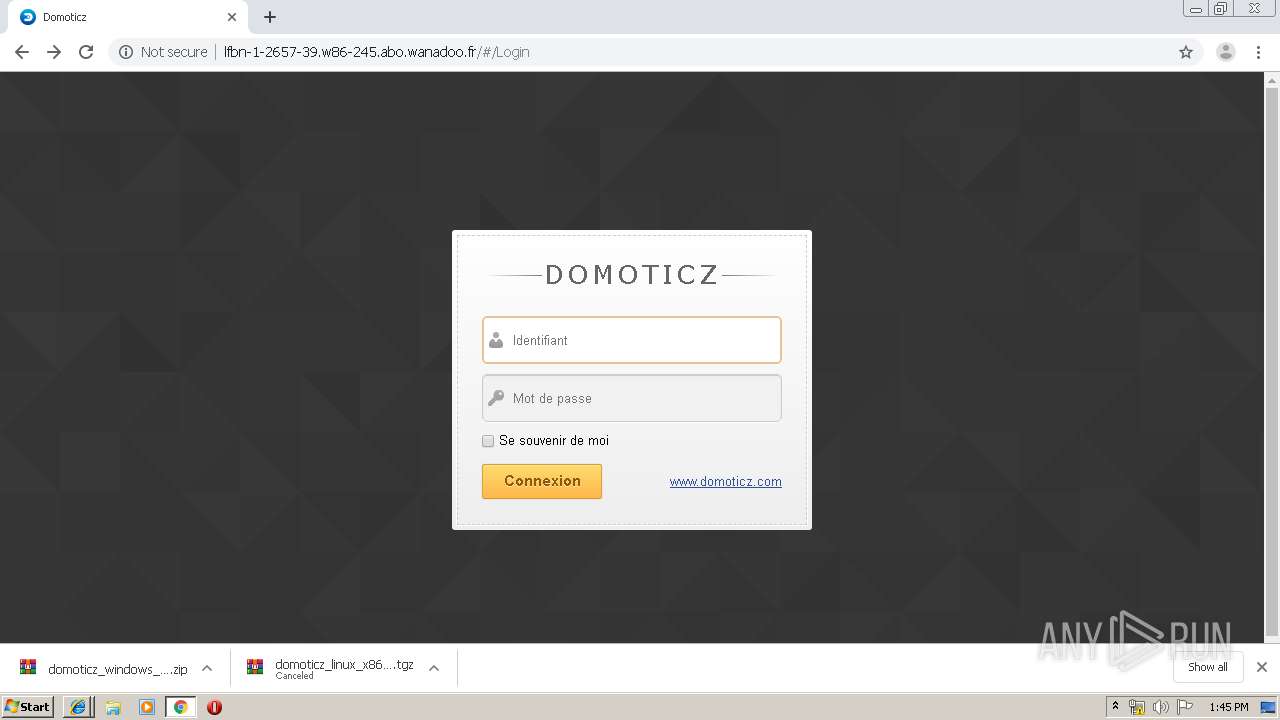
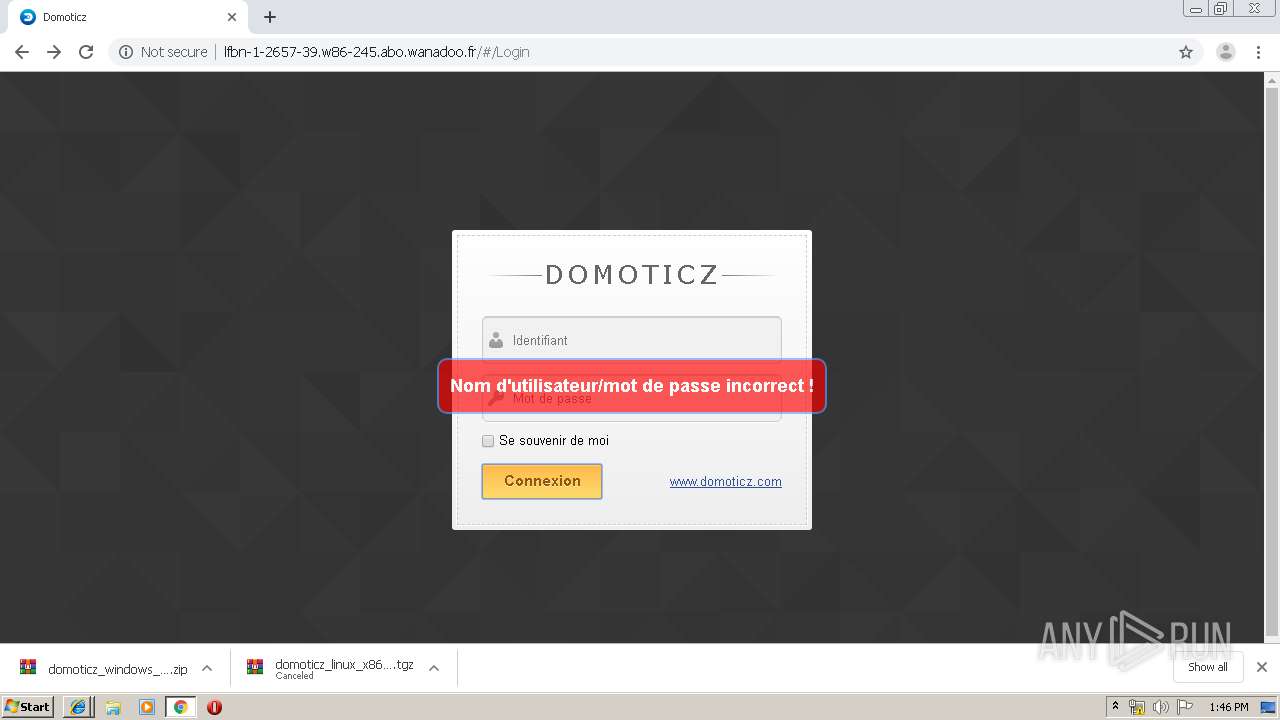
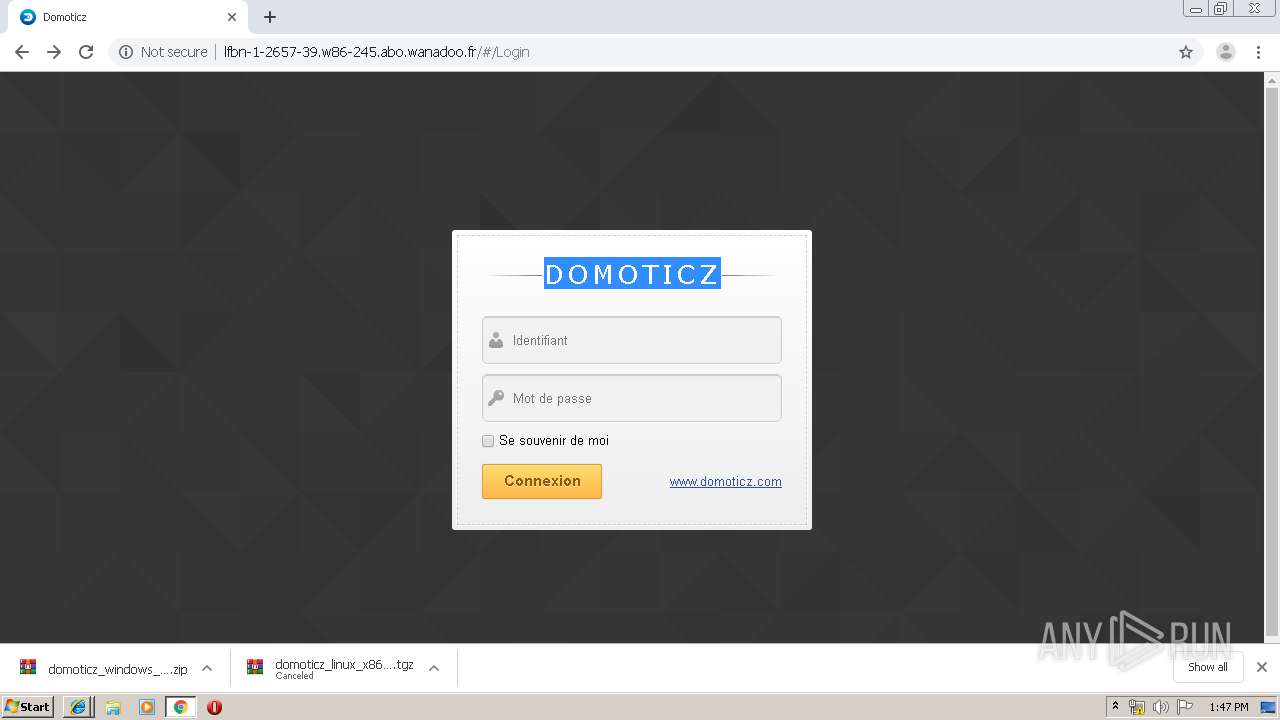
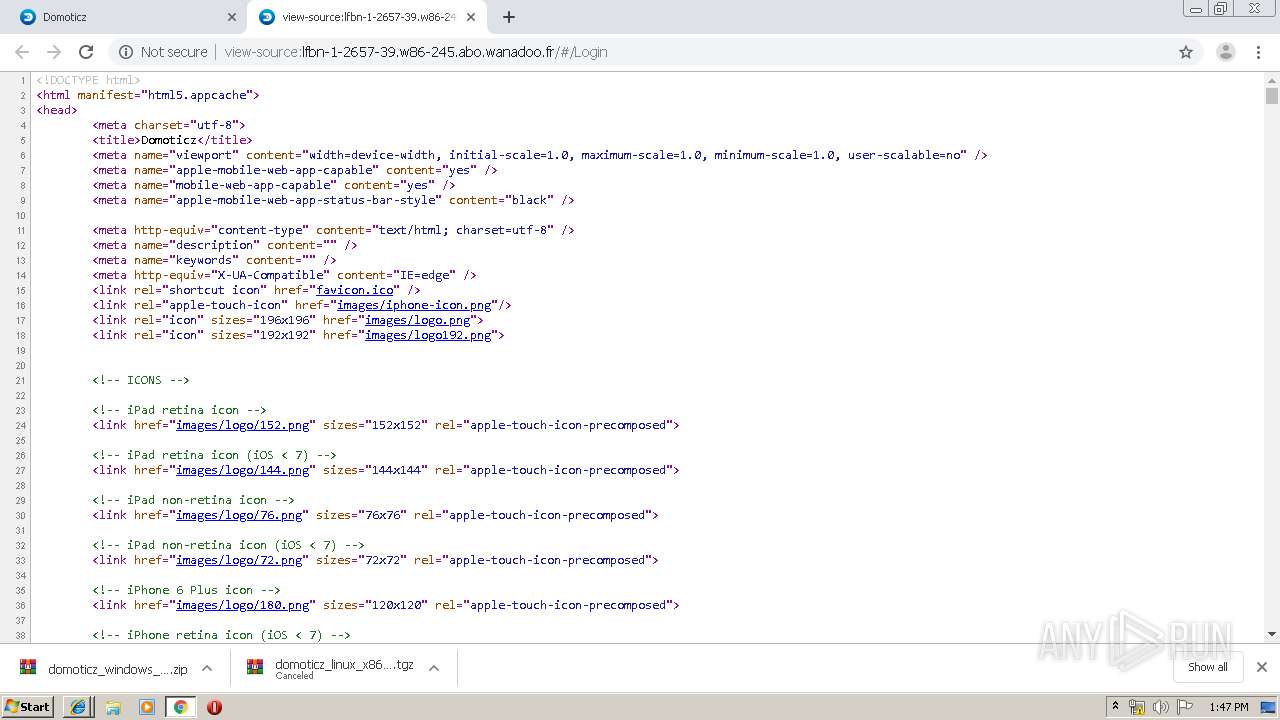
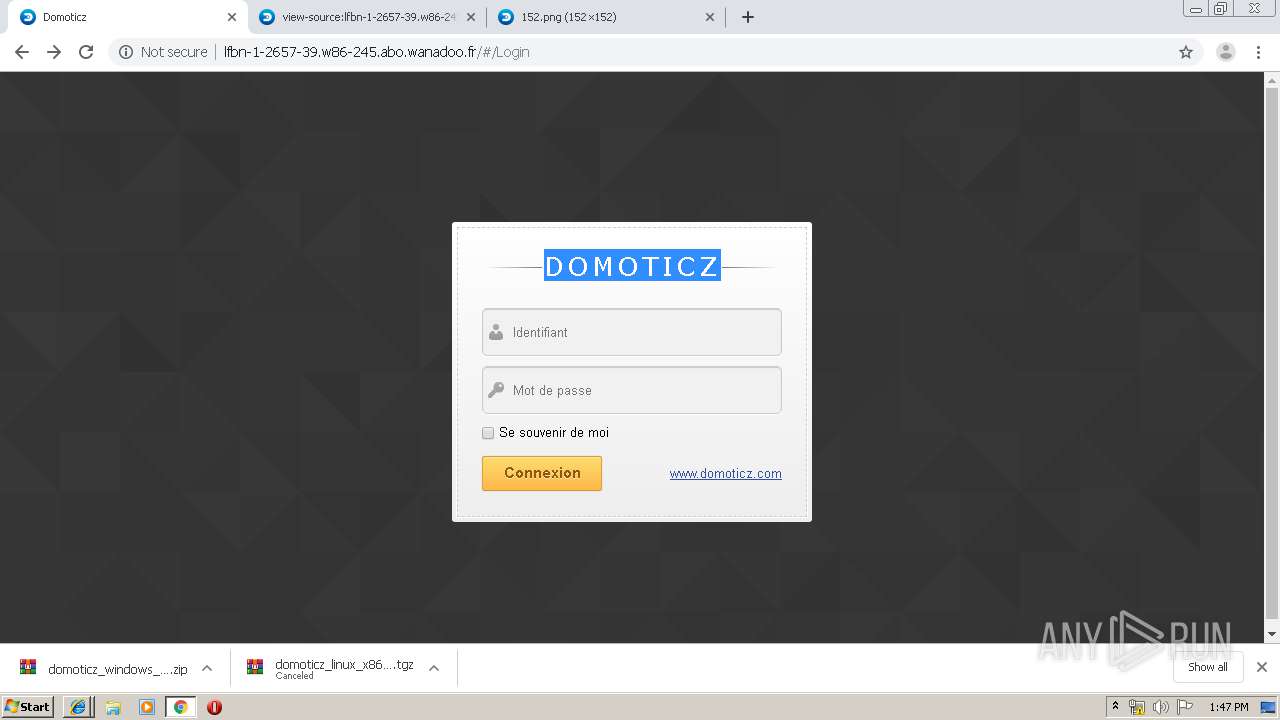
| URL: | http://lfbn-1-2657-39.w86-245.abo.wanadoo.fr |
| Full analysis: | https://app.any.run/tasks/3baa0c6a-9d86-41d7-8a50-25aa7539ffd4 |
| Verdict: | Malicious activity |
| Analysis date: | July 17, 2019, 12:42:37 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 5FCC00AF9EA0AA4A54B56F4D4DB12C0E |
| SHA1: | C88DE2A70D2F22E6B69FBA280EFA0A9C3170090D |
| SHA256: | CEB2FA94890ACD5880D4E49B70732EB33FF346D802A2357500B7709A8E7BB8B8 |
| SSDEEP: | 3:N1KSDrIVHrc9RjHBR:CSDrWHrc9Rzz |
MALICIOUS
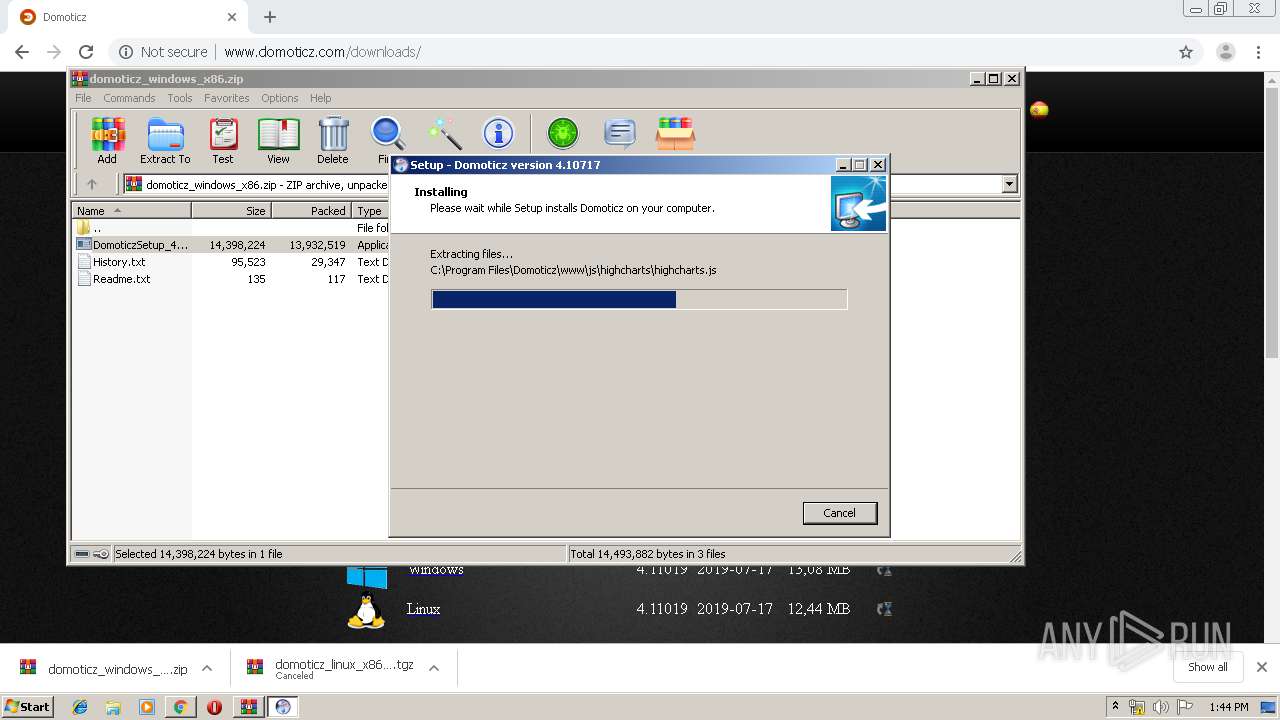
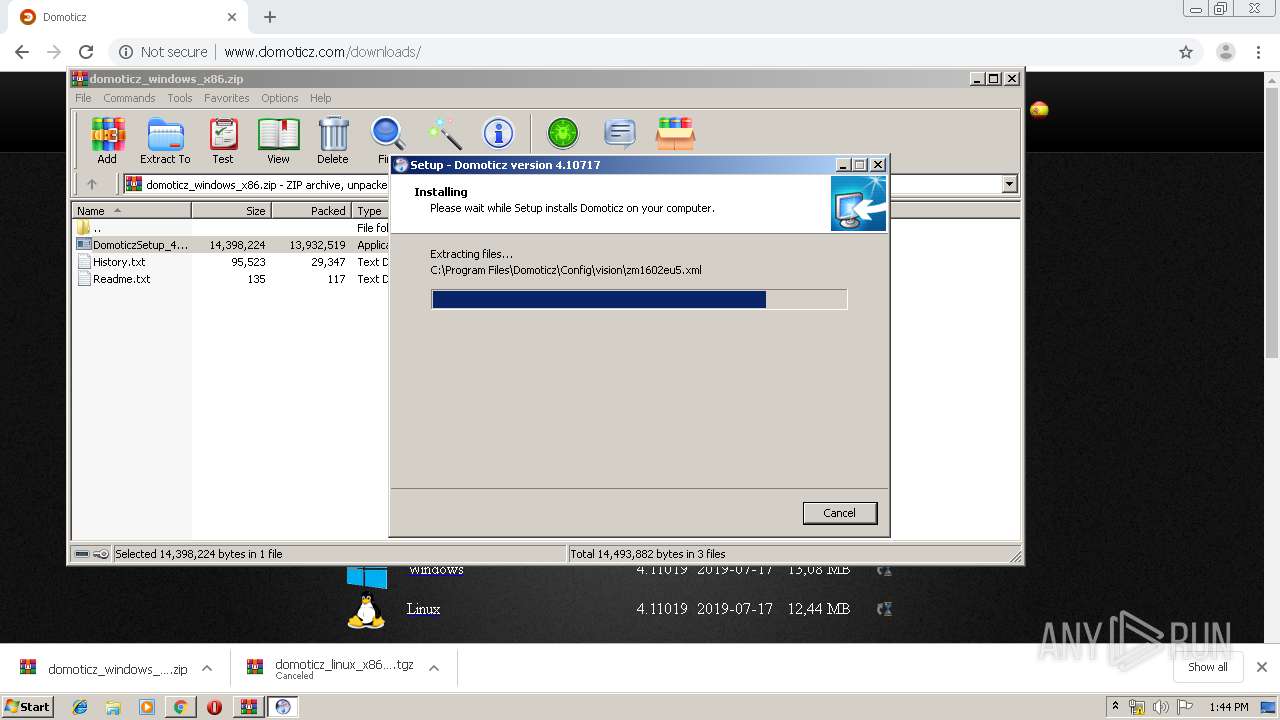
Application was dropped or rewritten from another process
- DomoticzSetup_4_10717.exe (PID: 3892)
- DomoticzSetup_4_10717.exe (PID: 2216)
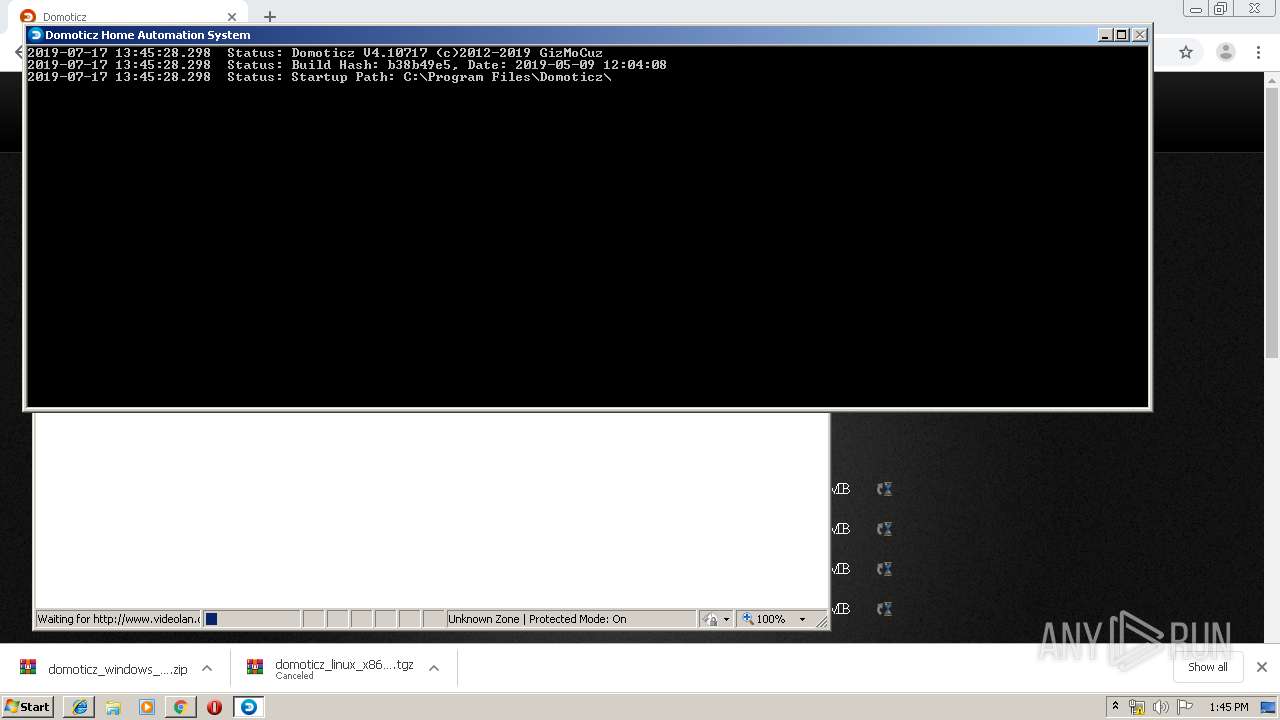
- domoticz.exe (PID: 3056)
Writes to a start menu file
- DomoticzSetup_4_10717.tmp (PID: 3656)
Loads dropped or rewritten executable
- domoticz.exe (PID: 3056)
SUSPICIOUS
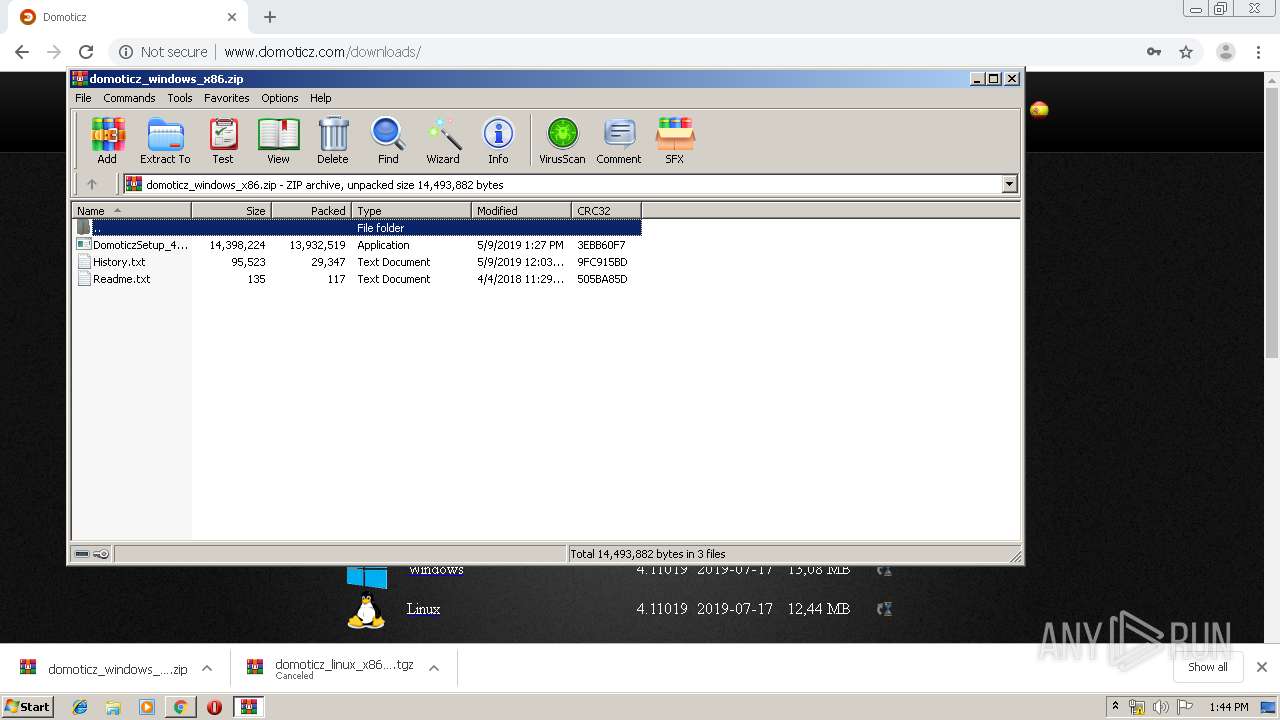
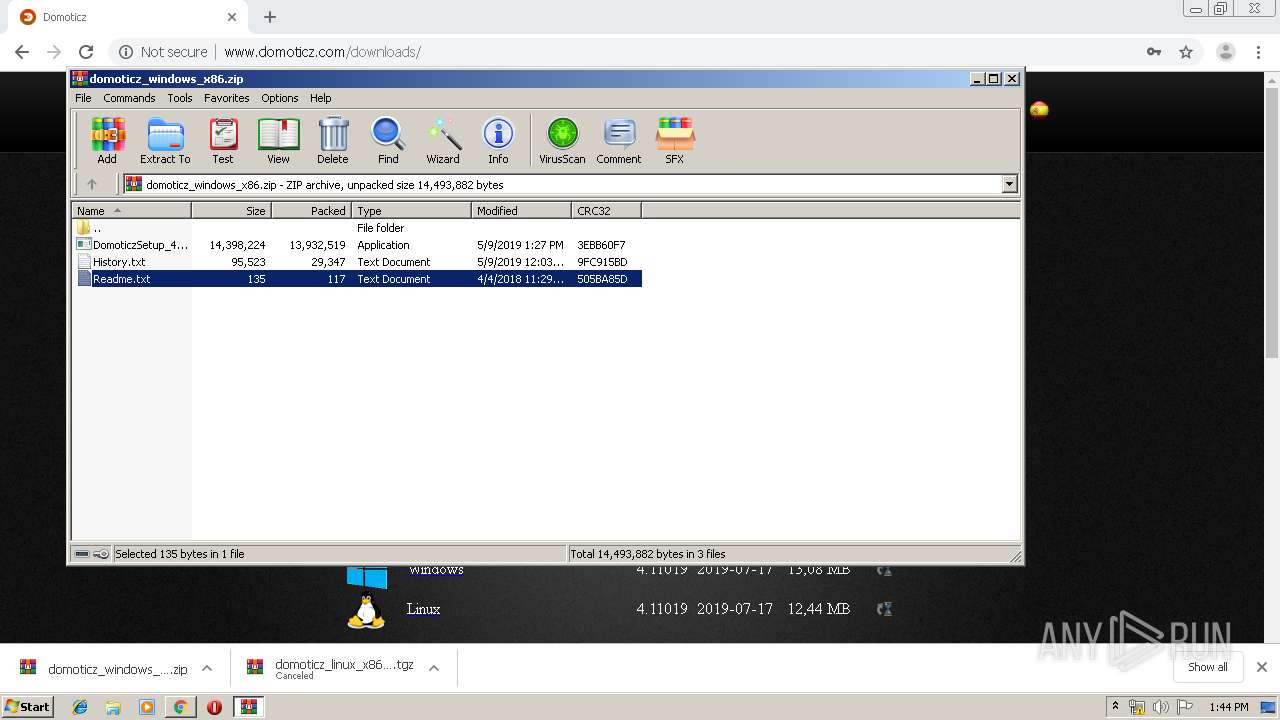
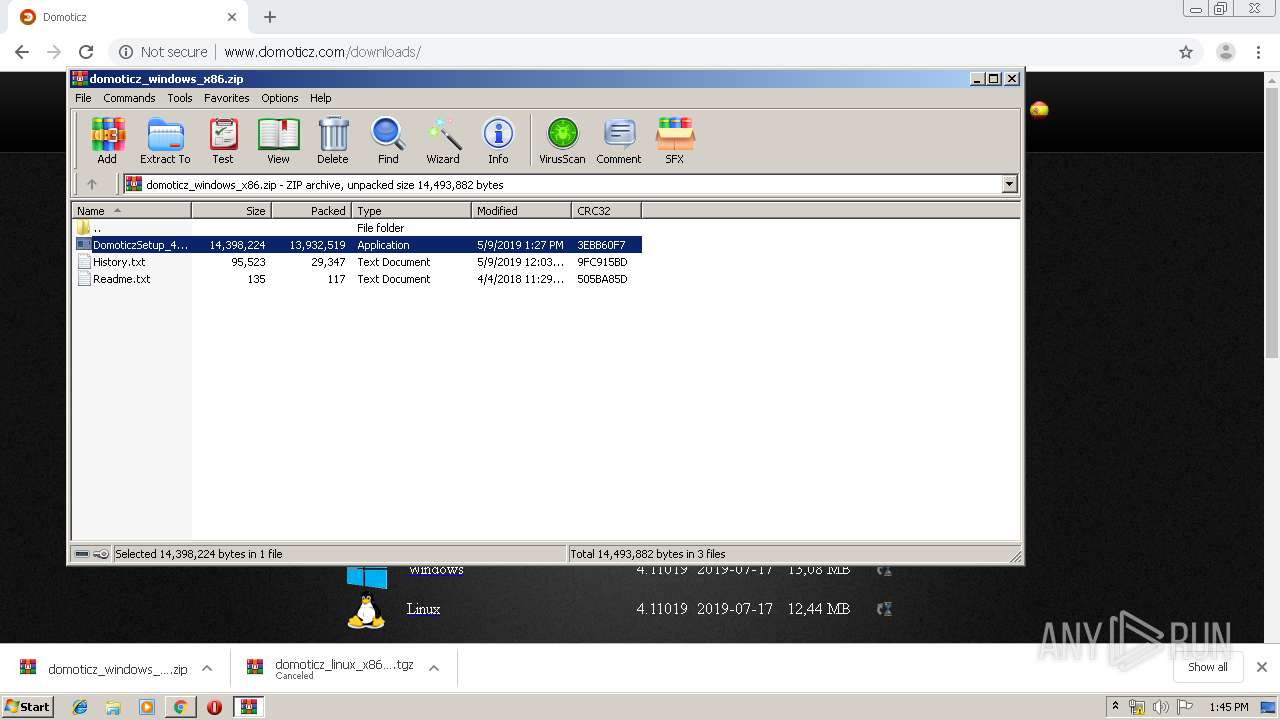
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2696)
- DomoticzSetup_4_10717.exe (PID: 3892)
- DomoticzSetup_4_10717.exe (PID: 2216)
- DomoticzSetup_4_10717.tmp (PID: 3656)
Reads the Windows organization settings
- DomoticzSetup_4_10717.tmp (PID: 3656)
Creates files in the user directory
- DomoticzSetup_4_10717.tmp (PID: 3656)
Executed via COM
- iexplore.exe (PID: 2868)
Modifies files in Chrome extension folder
- chrome.exe (PID: 3532)
Reads Windows owner or organization settings
- DomoticzSetup_4_10717.tmp (PID: 3656)
Creates files in the program directory
- domoticz.exe (PID: 3056)
Starts SC.EXE for service management
- DomoticzSetup_4_10717.tmp (PID: 3656)
INFO
Application launched itself
- chrome.exe (PID: 3532)
- iexplore.exe (PID: 2868)
Reads Internet Cache Settings
- chrome.exe (PID: 3532)
- iexplore.exe (PID: 3988)
- iexplore.exe (PID: 3212)
Application was dropped or rewritten from another process
- DomoticzSetup_4_10717.tmp (PID: 2236)
- DomoticzSetup_4_10717.tmp (PID: 3656)
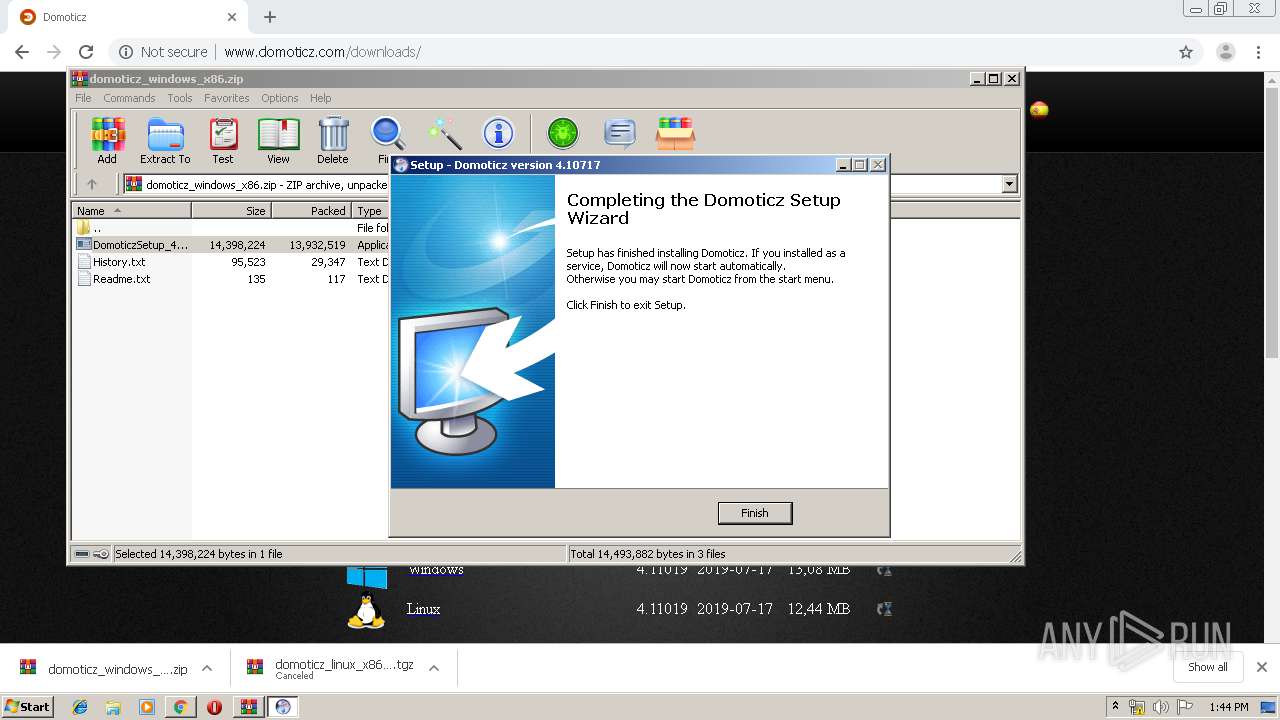
Creates a software uninstall entry
- DomoticzSetup_4_10717.tmp (PID: 3656)
Changes internet zones settings
- iexplore.exe (PID: 2868)
Creates files in the user directory
- iexplore.exe (PID: 3988)
Reads internet explorer settings
- iexplore.exe (PID: 3212)
- iexplore.exe (PID: 3988)
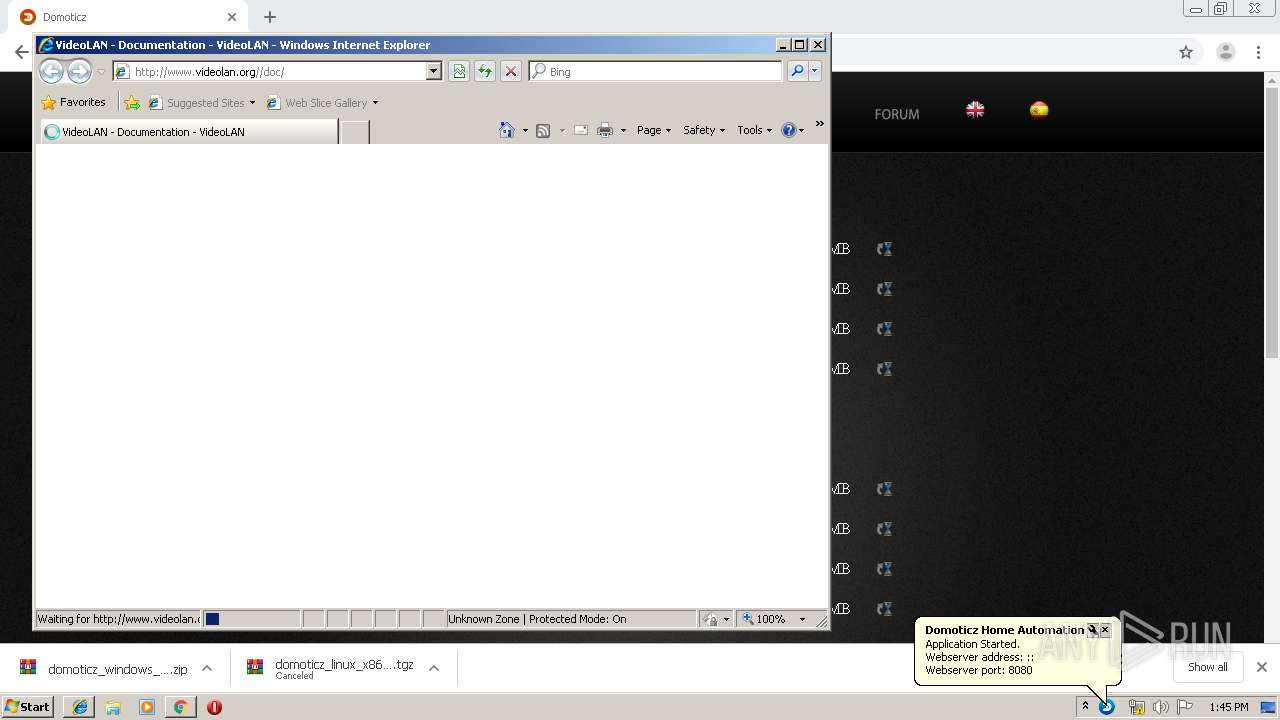
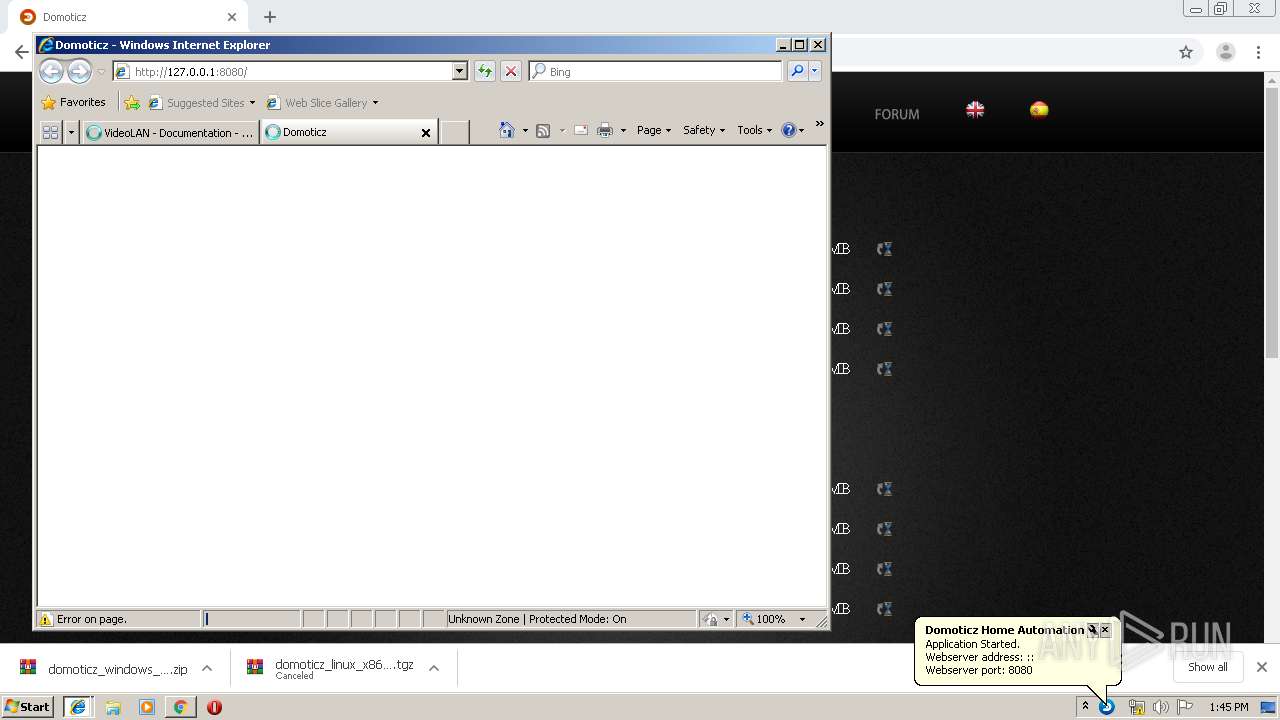
Manual execution by user
- domoticz.exe (PID: 3056)
Creates files in the program directory
- DomoticzSetup_4_10717.tmp (PID: 3656)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
87
Monitored processes
42
Malicious processes
2
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 872 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1012,16830080728677279432,8067339584116522813,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=3811545751490079025 --mojo-platform-channel-handle=1548 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 956 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1012,16830080728677279432,8067339584116522813,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=12640548816619903444 --mojo-platform-channel-handle=3900 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1148 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1012,16830080728677279432,8067339584116522813,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=7575075031812439362 --renderer-client-id=27 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3372 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1456 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=75.0.3770.100 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6efca9d0,0x6efca9e0,0x6efca9ec | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1492 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1012,16830080728677279432,8067339584116522813,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=14253329001230070588 --mojo-platform-channel-handle=2780 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1744 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1012,16830080728677279432,8067339584116522813,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=14113940961551448756 --renderer-client-id=26 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3580 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2036 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1012,16830080728677279432,8067339584116522813,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=898705061274671657 --mojo-platform-channel-handle=980 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2100 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1012,16830080728677279432,8067339584116522813,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=16059914320964820966 --mojo-platform-channel-handle=3024 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2164 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1012,16830080728677279432,8067339584116522813,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=17987059061315143982 --mojo-platform-channel-handle=3584 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2216 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa2696.46312\DomoticzSetup_4_10717.exe" /SPAWNWND=$8012C /NOTIFYWND=$701D6 | C:\Users\admin\AppData\Local\Temp\Rar$EXa2696.46312\DomoticzSetup_4_10717.exe | DomoticzSetup_4_10717.tmp | ||||||||||||
User: admin Company: Domoticz.com Integrity Level: HIGH Description: Domoticz Setup Exit code: 0 Version: Modules
| |||||||||||||||
Total events
2 662
Read events
2 430
Write events
220
Delete events
12
Modification events
| (PID) Process: | (3532) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3532) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3532) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3532) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3532) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3368) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 3532-13207840972438750 |
Value: 259 | |||
| (PID) Process: | (3532) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3532) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3532) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1512-13197841398593750 |
Value: 0 | |||
| (PID) Process: | (3532) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
8
Suspicious files
365
Text files
1 806
Unknown types
63
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3532 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3532 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3532 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3532 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\e91a7d5e-0b5f-47b0-bed4-94c5073f15c9.tmp | — | |
MD5:— | SHA256:— | |||
| 3532 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3532 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3532 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF17d12b.TMP | text | |
MD5:— | SHA256:— | |||
| 3532 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 3532 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old~RF17d1b7.TMP | text | |
MD5:— | SHA256:— | |||
| 3532 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF17d0fc.TMP | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
170
TCP/UDP connections
56
DNS requests
36
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
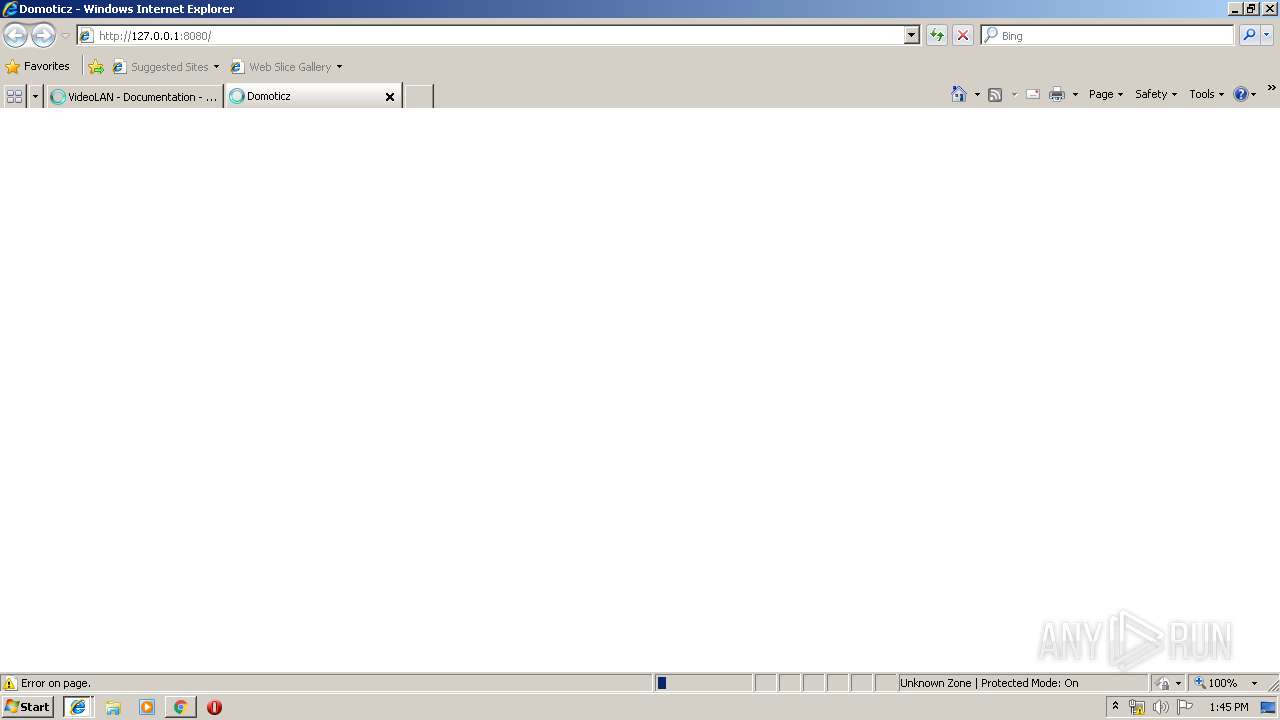
872 | chrome.exe | GET | 200 | 86.245.127.39:80 | http://lfbn-1-2657-39.w86-245.abo.wanadoo.fr/ | FR | html | 12.6 Kb | unknown |
872 | chrome.exe | GET | 200 | 86.245.127.39:80 | http://lfbn-1-2657-39.w86-245.abo.wanadoo.fr/js/babel-polyfill-6.26.0.js | FR | text | 62.2 Kb | unknown |
872 | chrome.exe | GET | 200 | 86.245.127.39:80 | http://lfbn-1-2657-39.w86-245.abo.wanadoo.fr/js/bootstrap.min.js | FR | text | 9.63 Kb | unknown |
872 | chrome.exe | GET | 200 | 86.245.127.39:80 | http://lfbn-1-2657-39.w86-245.abo.wanadoo.fr/js/bootbox.min.js | FR | text | 2.03 Kb | unknown |
872 | chrome.exe | GET | 200 | 86.245.127.39:80 | http://lfbn-1-2657-39.w86-245.abo.wanadoo.fr/css/legacy.css | FR | text | 2.11 Kb | unknown |
872 | chrome.exe | GET | 200 | 86.245.127.39:80 | http://lfbn-1-2657-39.w86-245.abo.wanadoo.fr/css/style.css | FR | text | 7.07 Kb | unknown |
872 | chrome.exe | GET | 200 | 86.245.127.39:80 | http://lfbn-1-2657-39.w86-245.abo.wanadoo.fr/js/jquery-ui.min.js | FR | text | 66.1 Kb | unknown |
872 | chrome.exe | GET | 200 | 86.245.127.39:80 | http://lfbn-1-2657-39.w86-245.abo.wanadoo.fr/css/jquery-ui-timepicker-addon.css | FR | text | 246 b | unknown |
872 | chrome.exe | GET | 200 | 86.245.127.39:80 | http://lfbn-1-2657-39.w86-245.abo.wanadoo.fr/css/colpick.css | FR | text | 1.97 Kb | unknown |
872 | chrome.exe | GET | 200 | 86.245.127.39:80 | http://lfbn-1-2657-39.w86-245.abo.wanadoo.fr/acttheme/custom.css | FR | text | 1.39 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
872 | chrome.exe | 172.217.18.109:443 | accounts.google.com | Google Inc. | US | suspicious |
872 | chrome.exe | 86.245.127.39:80 | lfbn-1-2657-39.w86-245.abo.wanadoo.fr | Orange | FR | unknown |
872 | chrome.exe | 172.217.18.110:443 | clients1.google.com | Google Inc. | US | whitelisted |
872 | chrome.exe | 216.58.208.46:443 | clients2.google.com | Google Inc. | US | whitelisted |
872 | chrome.exe | 172.217.23.129:443 | clients2.googleusercontent.com | Google Inc. | US | whitelisted |
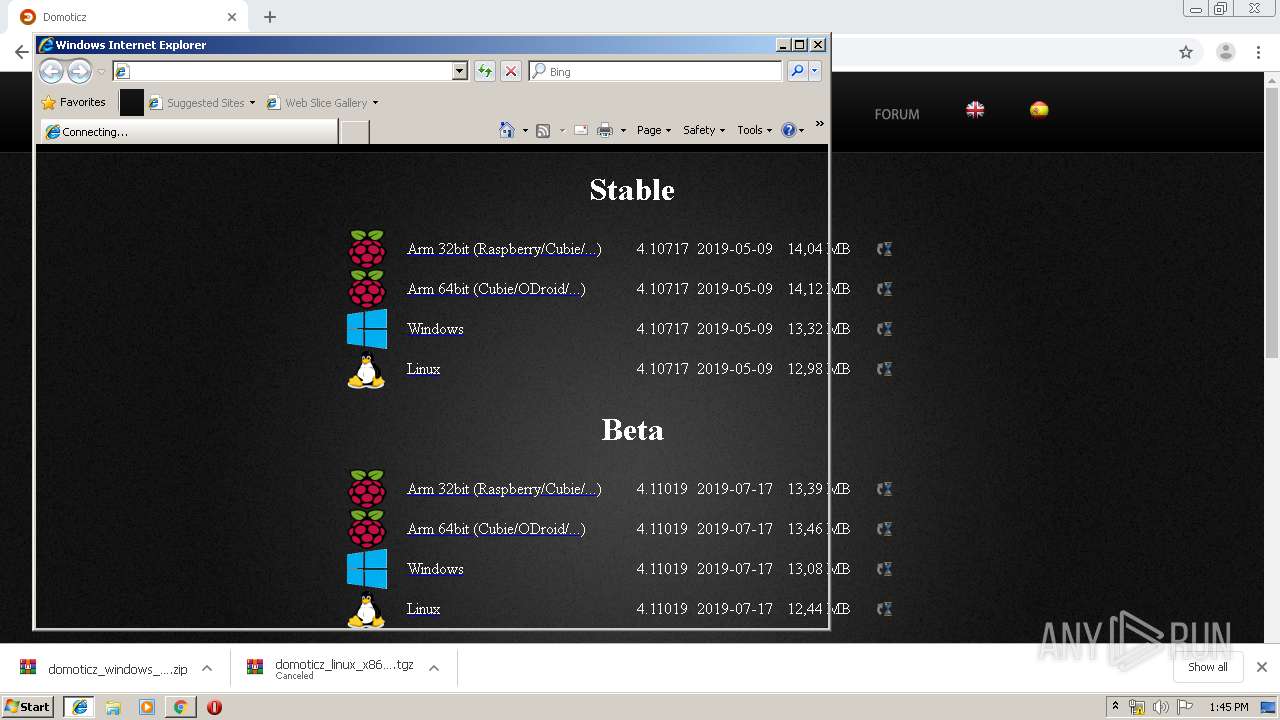
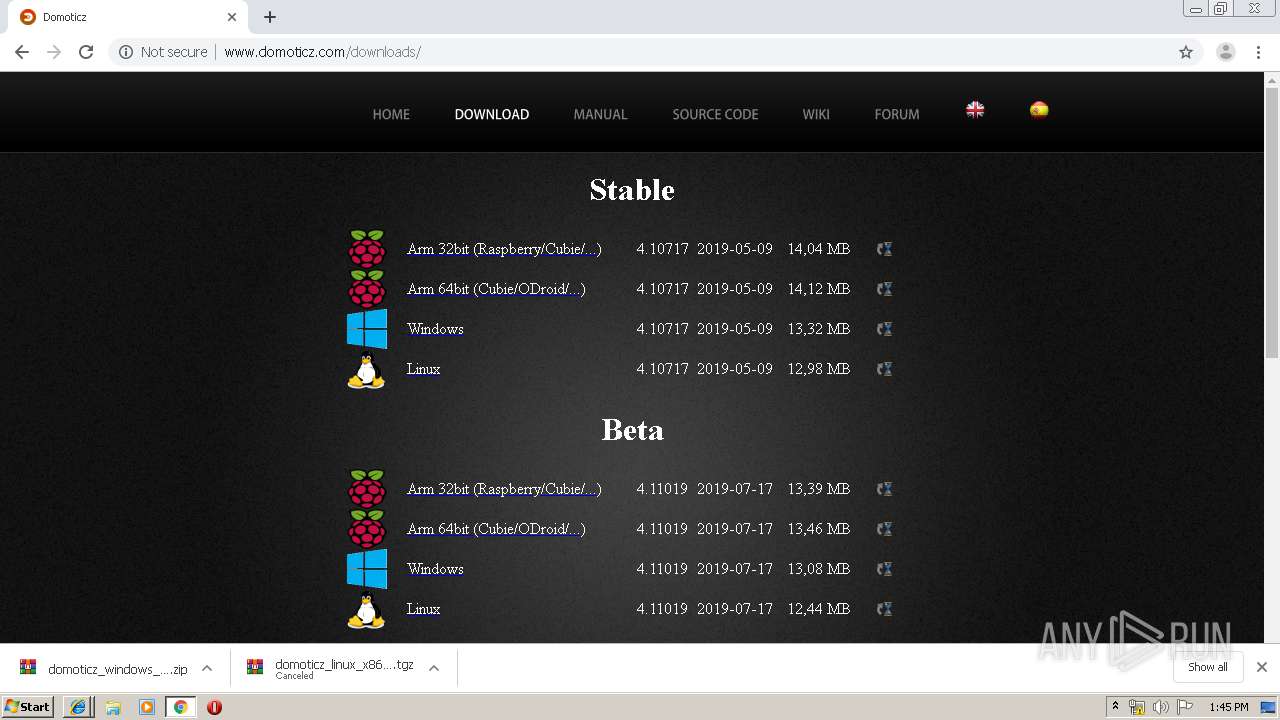
872 | chrome.exe | 146.185.159.228:80 | domoticz.com | Digital Ocean, Inc. | NL | unknown |
872 | chrome.exe | 74.125.8.60:80 | r6---sn-5hne6n7z.gvt1.com | Google Inc. | US | whitelisted |
872 | chrome.exe | 216.58.207.67:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
872 | chrome.exe | 23.210.248.226:443 | www.paypalobjects.com | Akamai International B.V. | NL | whitelisted |
872 | chrome.exe | 146.185.159.228:443 | domoticz.com | Digital Ocean, Inc. | NL | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
lfbn-1-2657-39.w86-245.abo.wanadoo.fr |
| unknown |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
clients1.google.com |
| whitelisted |
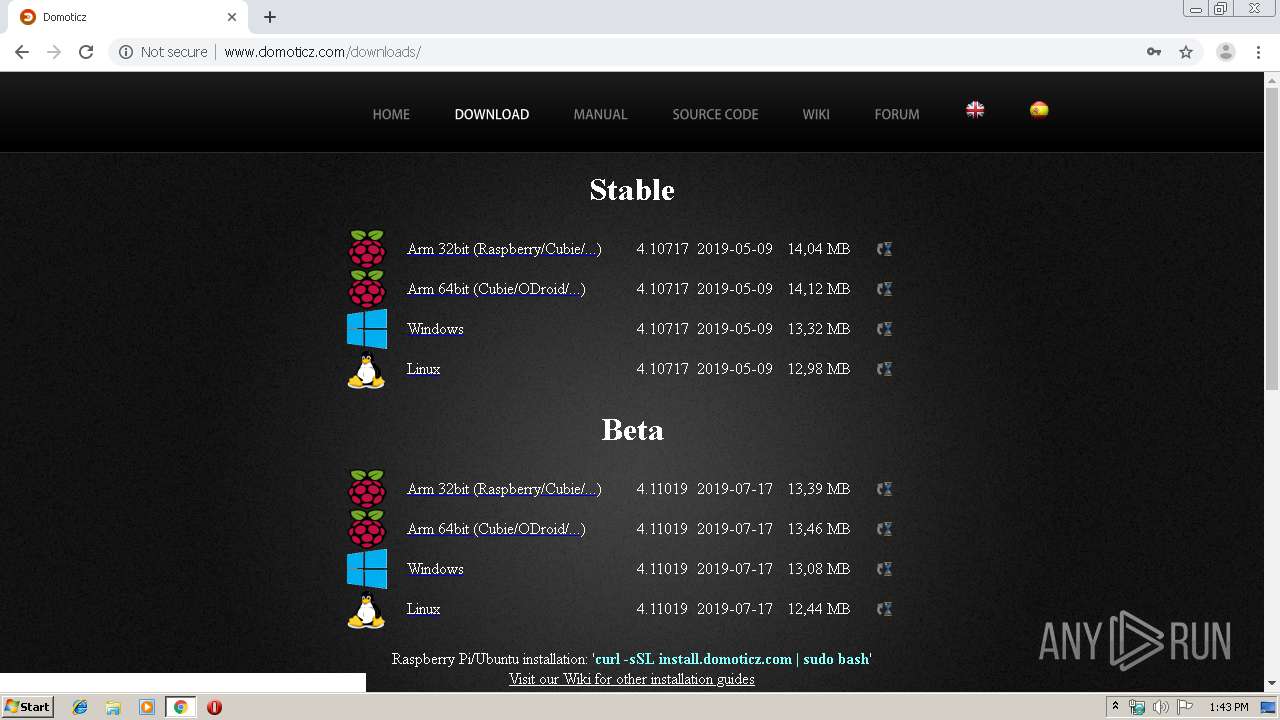
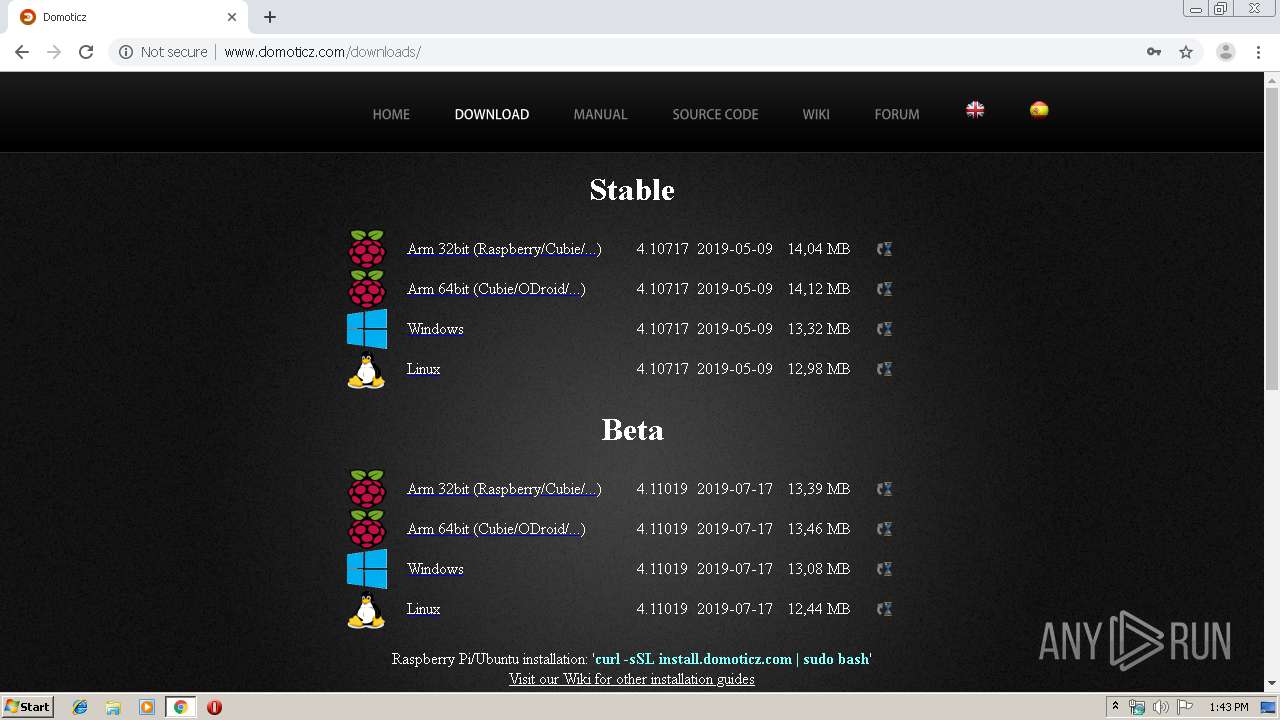
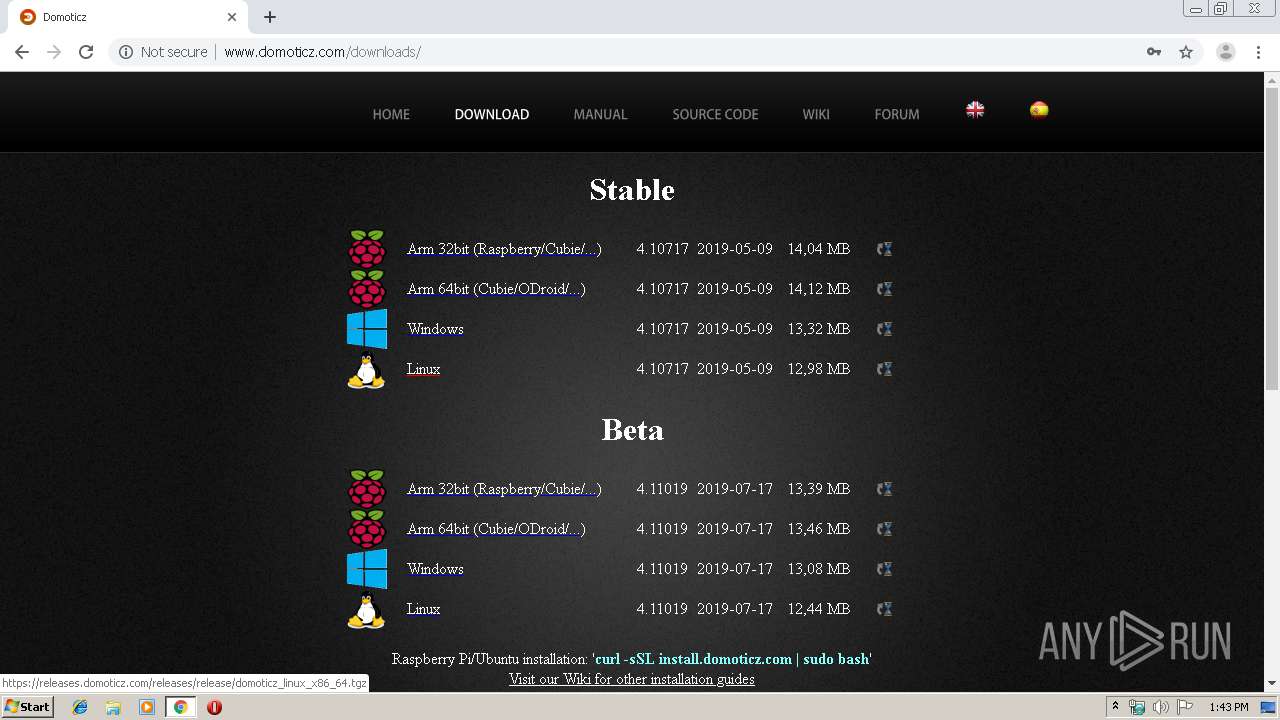
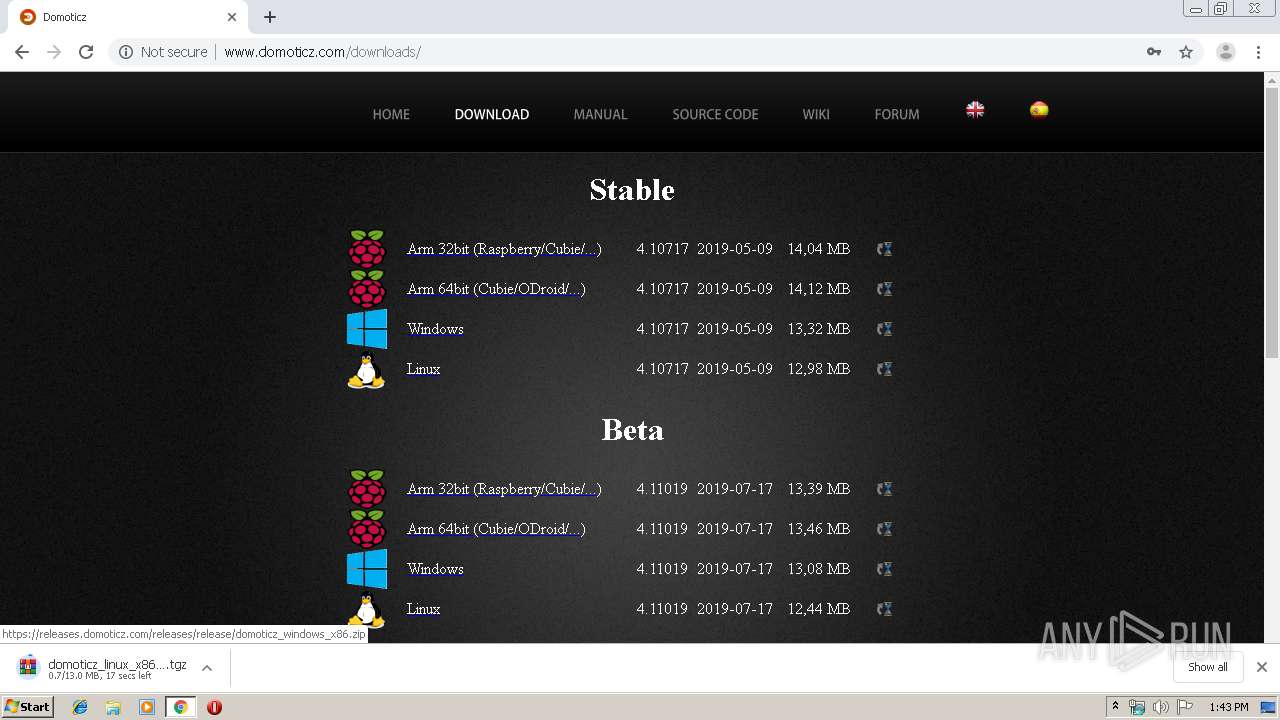
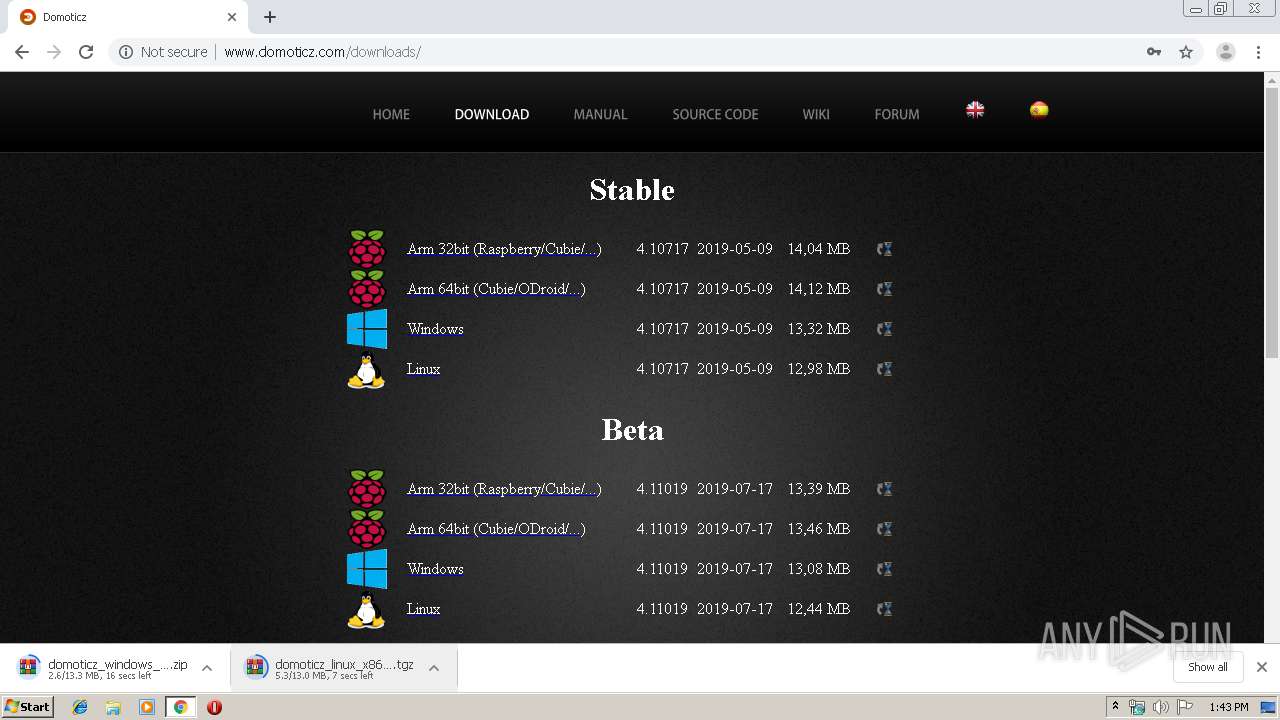
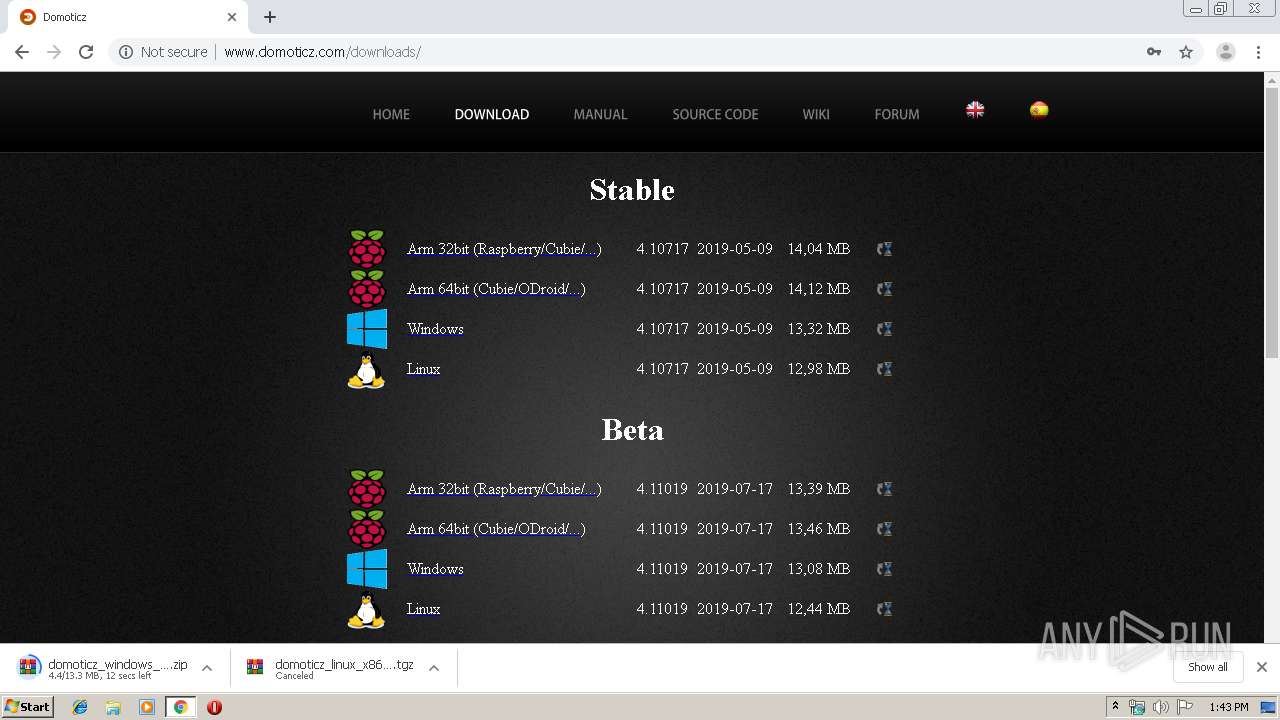
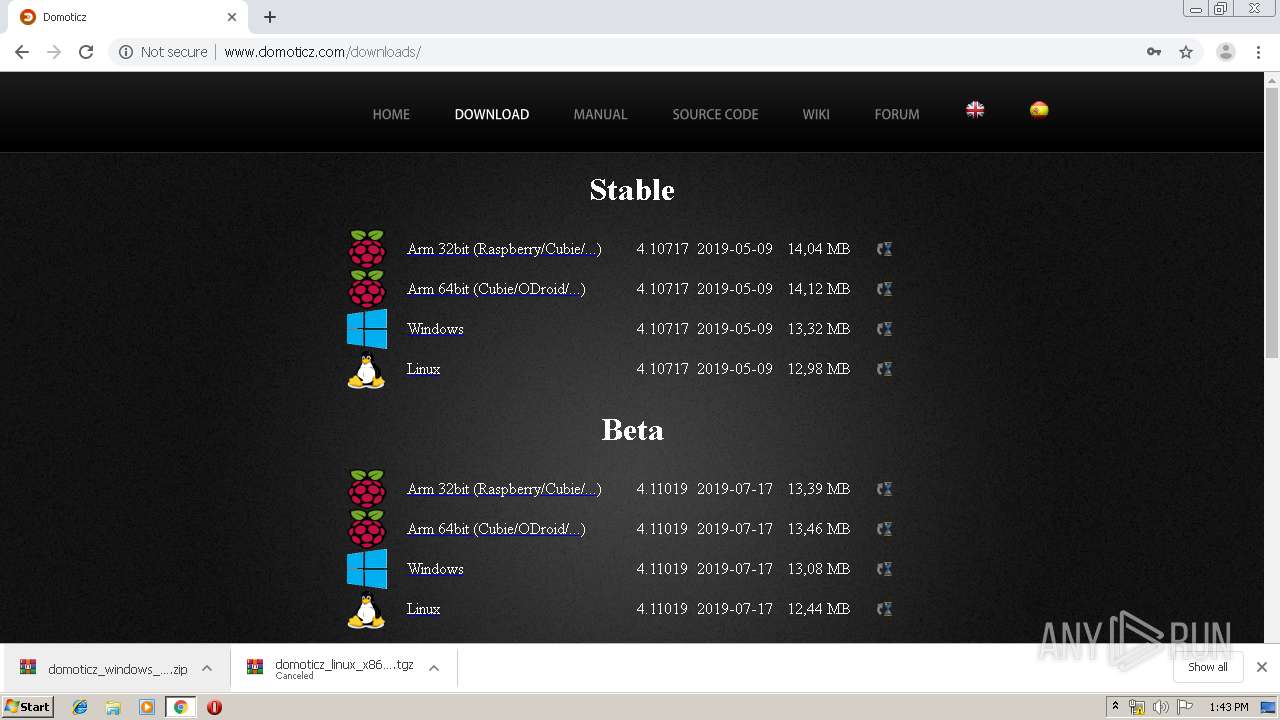
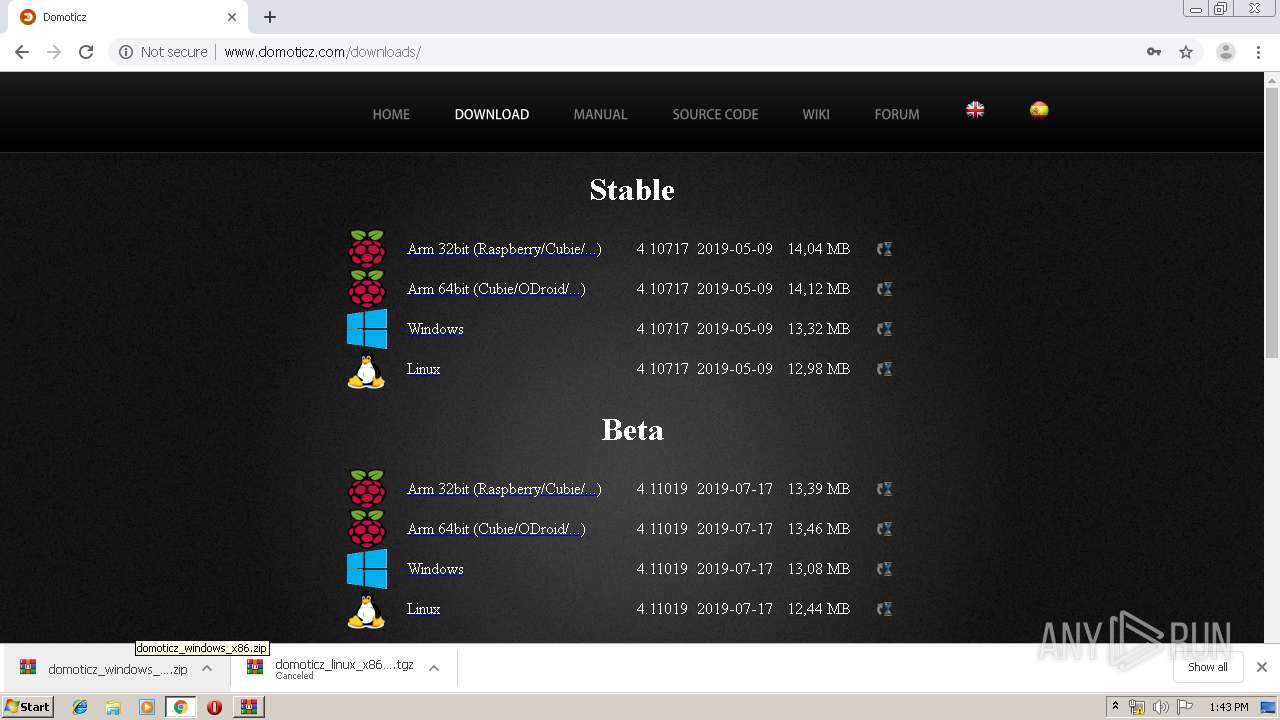
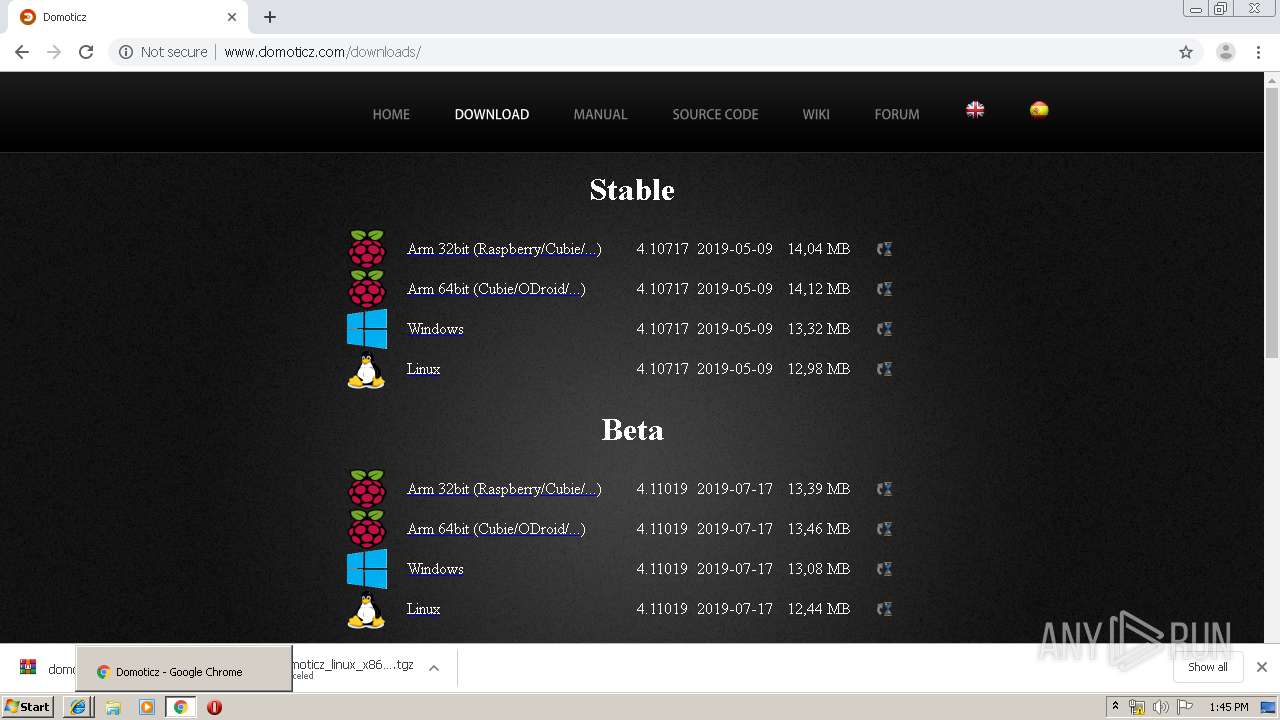
domoticz.com |
| whitelisted |
www.domoticz.com |
| malicious |
www.google.com |
| malicious |
ssl.gstatic.com |
| whitelisted |
clients2.google.com |
| whitelisted |
clients2.googleusercontent.com |
| whitelisted |