| File name: | ceace56b50080784e12d4a7a5e77cd23afa5589b492fd27d488a368346e4422c |
| Full analysis: | https://app.any.run/tasks/f8d3d14b-56dc-4713-8fb1-833aeb5853f3 |
| Verdict: | Malicious activity |
| Analysis date: | May 15, 2020, 13:16:54 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 378829AF72589E6DCAFE7F5FF288D7E7 |
| SHA1: | 06372565981D91978F573AA3152DCDE01B41081E |
| SHA256: | CEACE56B50080784E12D4A7A5E77CD23AFA5589B492FD27D488A368346E4422C |
| SSDEEP: | 24576:BylWUhEzahll/aHGB7Dh++nsbJ2yTmOpDOZjYSF76iSrAQopTi+BteknF:UAHIlP7DoTmYOZUSF2iSETJ |
MALICIOUS
No malicious indicators.SUSPICIOUS
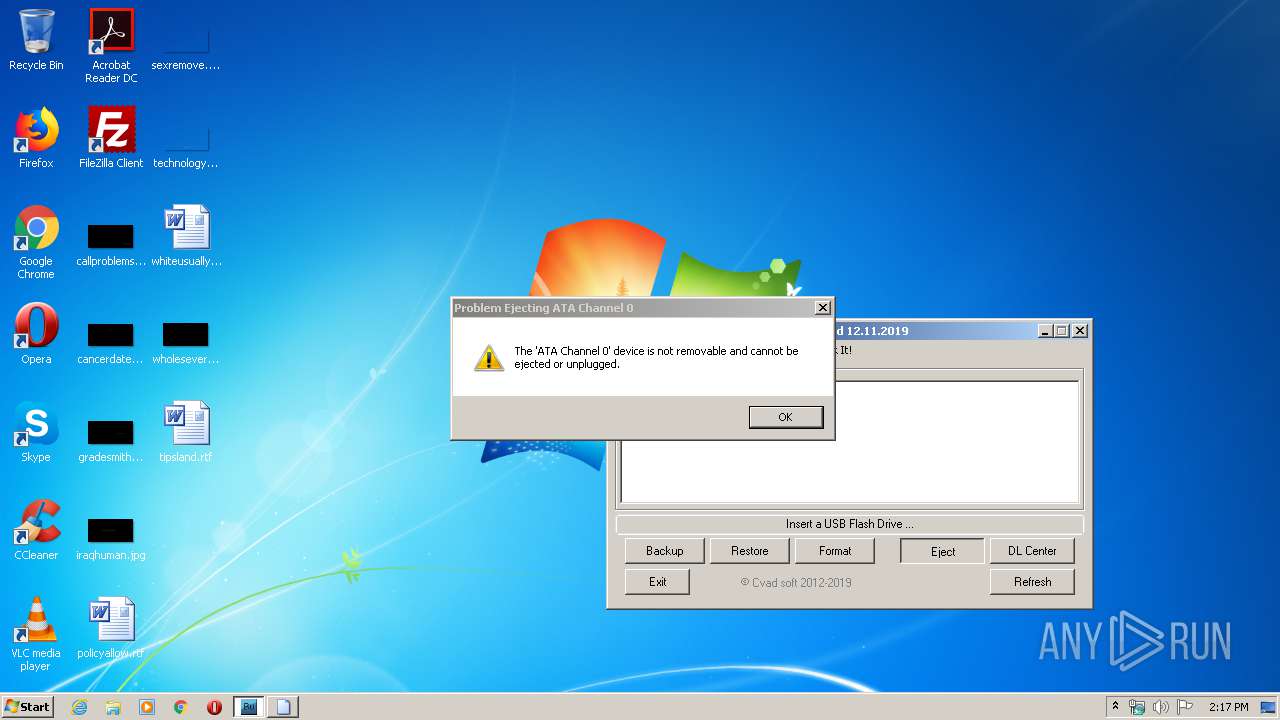
Low-level read access rights to disk partition
- ceace56b50080784e12d4a7a5e77cd23afa5589b492fd27d488a368346e4422c.exe (PID: 2068)
Starts CMD.EXE for commands execution
- ceace56b50080784e12d4a7a5e77cd23afa5589b492fd27d488a368346e4422c.exe (PID: 2068)
Executed via COM
- rundll32.exe (PID: 2432)
- rundll32.exe (PID: 3448)
- rundll32.exe (PID: 2548)
- rundll32.exe (PID: 1852)
- rundll32.exe (PID: 2300)
- rundll32.exe (PID: 3496)
- rundll32.exe (PID: 3980)
- rundll32.exe (PID: 3916)
- rundll32.exe (PID: 3840)
- rundll32.exe (PID: 3428)
- rundll32.exe (PID: 2512)
- rundll32.exe (PID: 3320)
- rundll32.exe (PID: 3584)
- rundll32.exe (PID: 2660)
- rundll32.exe (PID: 1840)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (41) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (36.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.6) |
| .exe | | | Win32 Executable (generic) (5.9) |
| .exe | | | Win16/32 Executable Delphi generic (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:11:12 14:12:25+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.5 |
| CodeSize: | 845824 |
| InitializedDataSize: | 1209344 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1000 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 2.1.2019.26 |
| ProductVersionNumber: | 2.1.2019.26 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
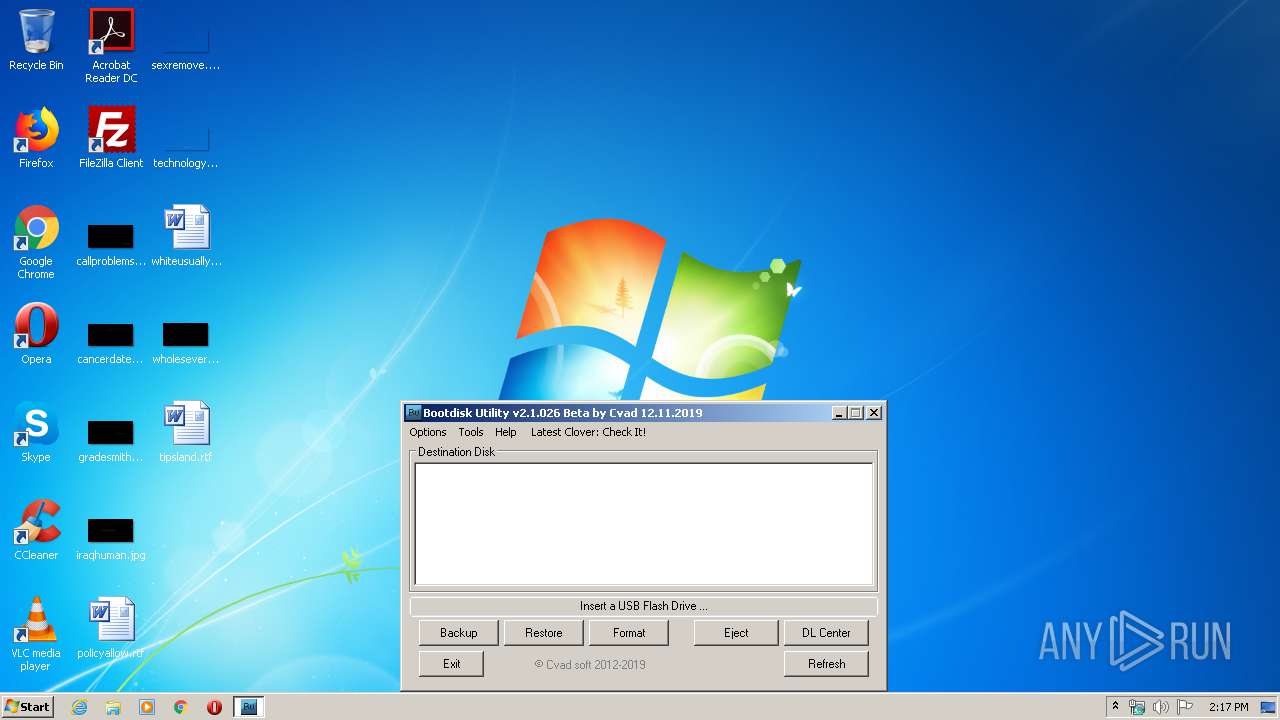
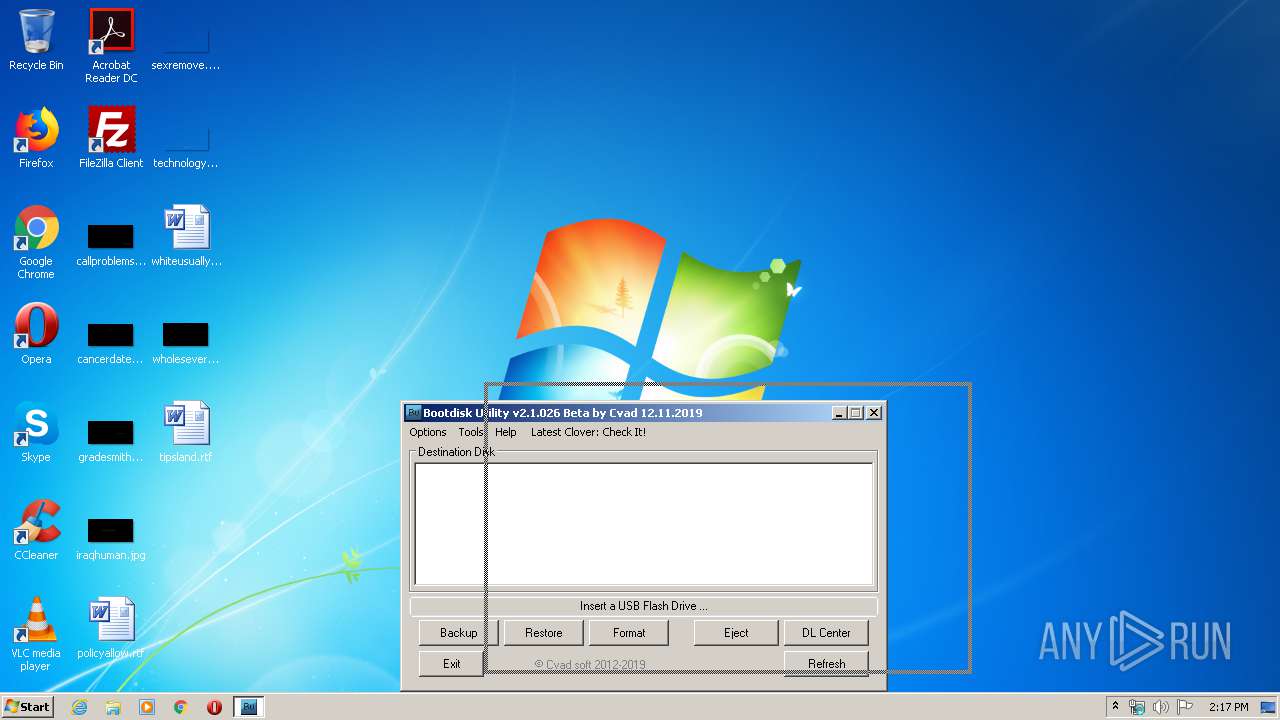
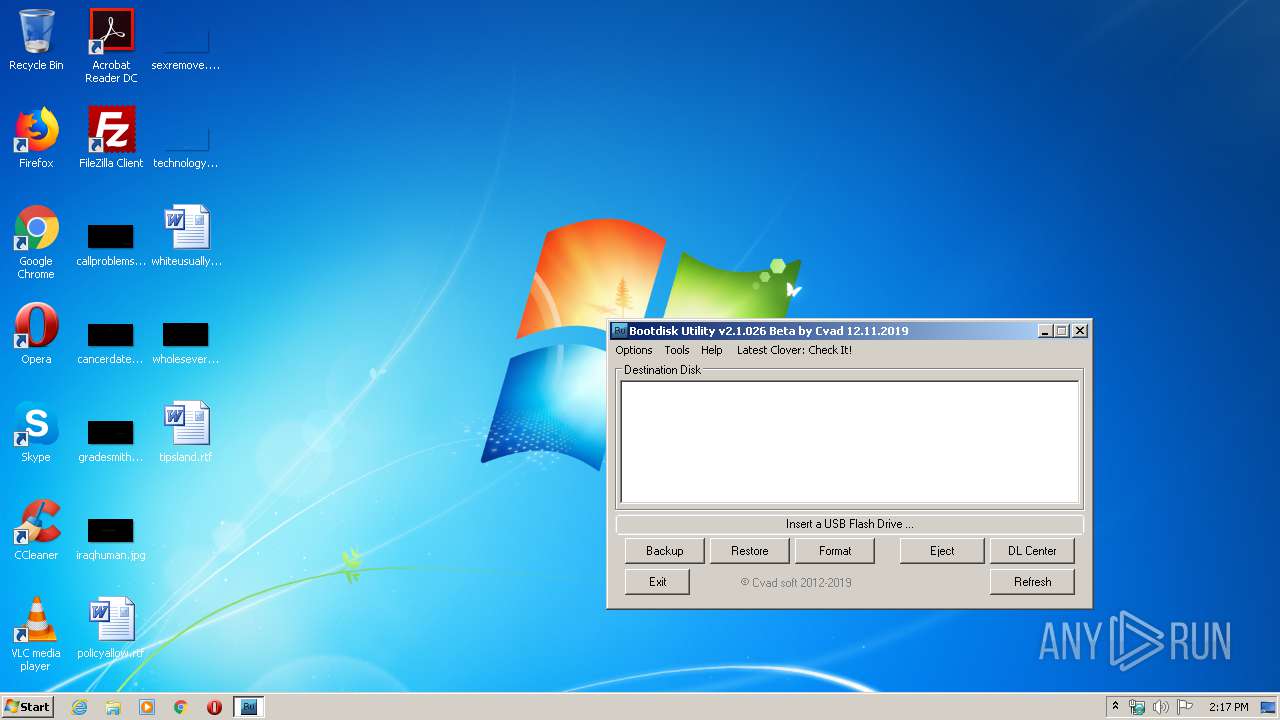
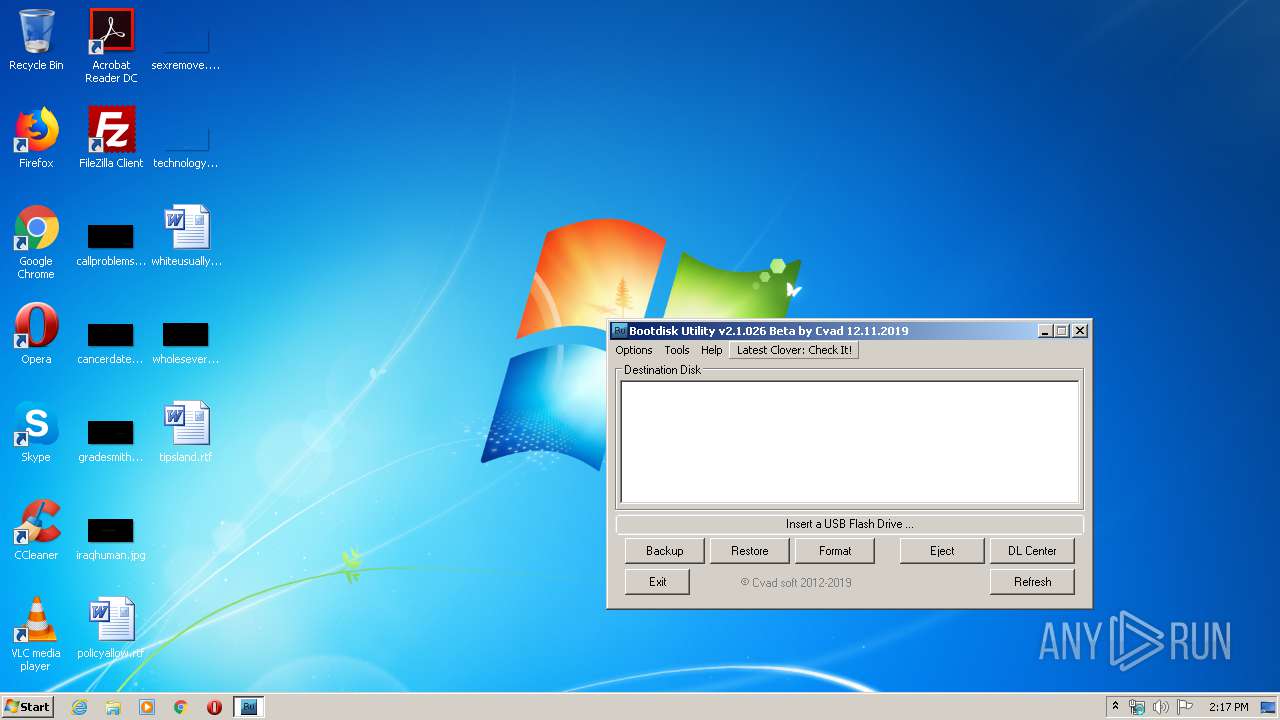
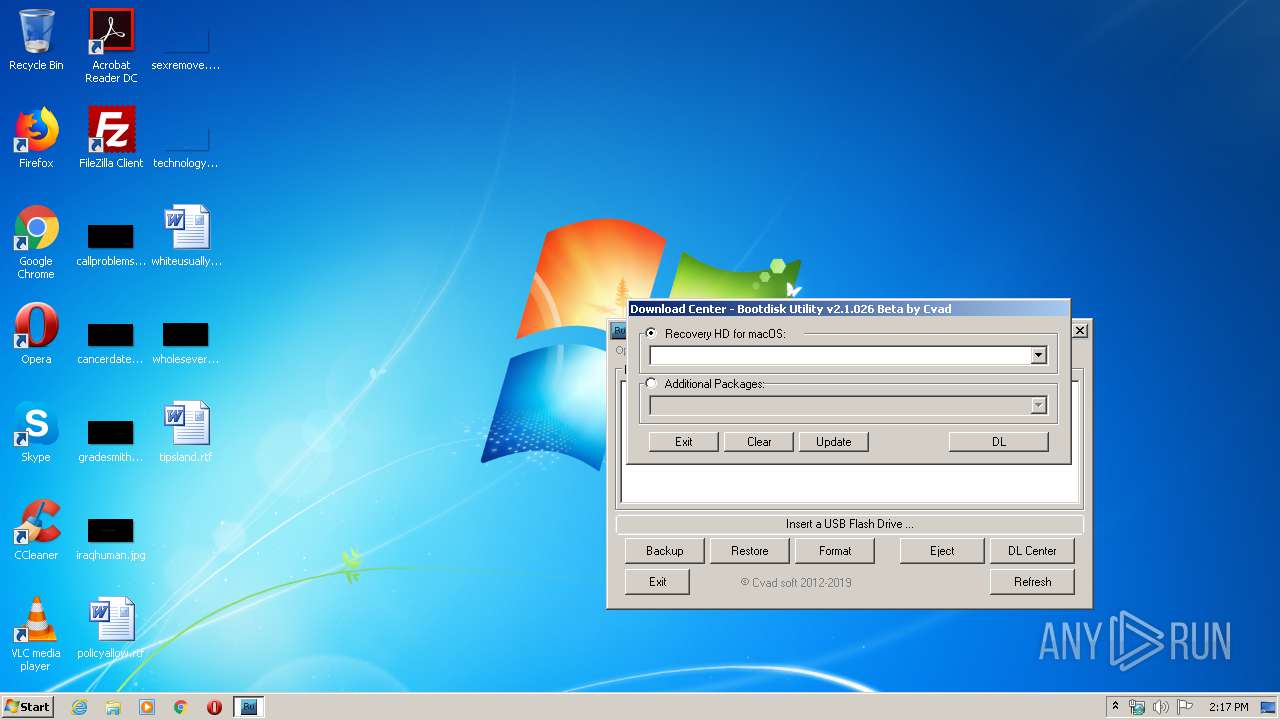
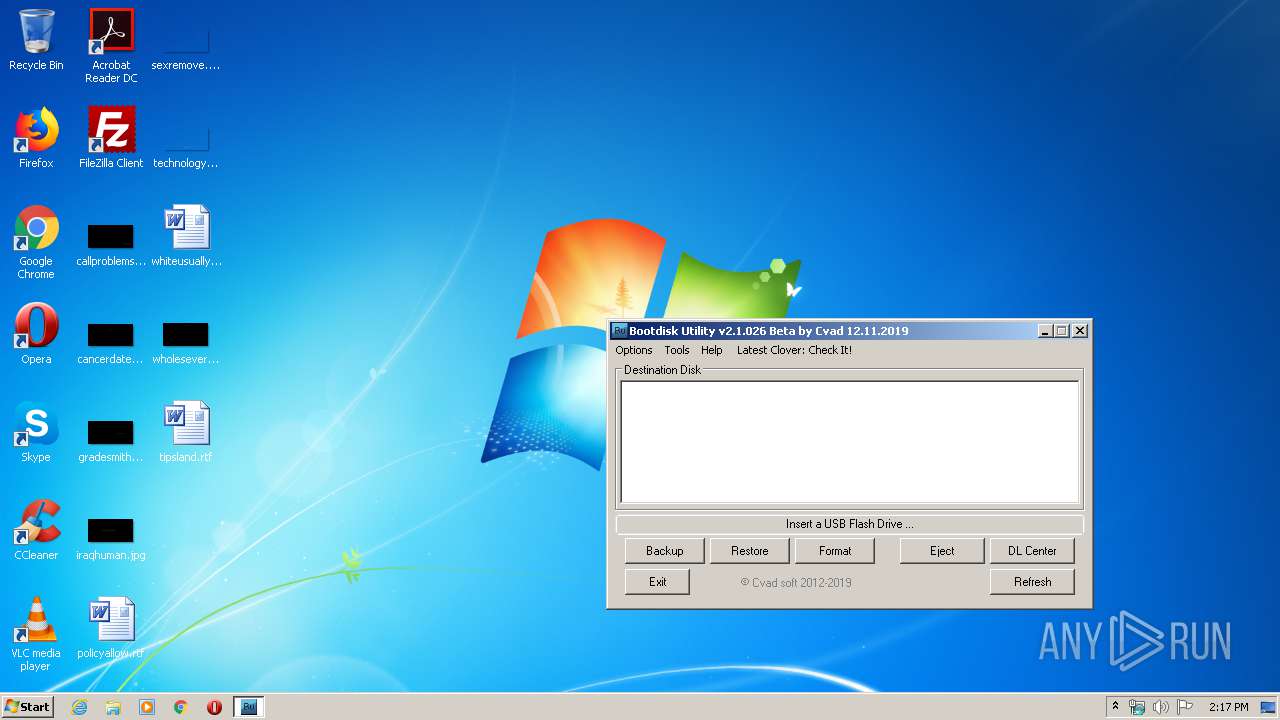
| CompanyName: | Cvad Software |
| ProductName: | Boot Disk Utility by Cvad |
| ProductVersion: | 2.1.2019.26 |
| FileVersion: | 2.1.2019.26 |
| FileDescription: | Utility to make bootable EFI USB Flash Drive |
| InternalName: | BDUtility.exe |
| OriginalFileName: | BDUtility.exe |
| LegalCopyright: | Copyright (c) 2019 Cvad |
| LegalTrademarks: | Cvad Software |
| Website: | http://cvad-mac.narod.ru |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 12-Nov-2019 13:12:25 |
| Detected languages: |
|
| CompanyName: | Cvad Software |
| ProductName: | Boot Disk Utility by Cvad |
| ProductVersion: | 2.1.2019.26 |
| FileVersion: | 2.1.2019.26 |
| FileDescription: | Utility to make bootable EFI USB Flash Drive |
| InternalName: | BDUtility.exe |
| OriginalFilename: | BDUtility.exe |
| LegalCopyright: | Copyright (c) 2019 Cvad |
| LegalTrademarks: | Cvad Software |
| Website: | http://cvad-mac.narod.ru |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 12-Nov-2019 13:12:25 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.code | 0x00001000 | 0x0003AA50 | 0x0003AC00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.67295 |
.text | 0x0003C000 | 0x00093B80 | 0x00093C00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.58507 |
.rdata | 0x000D0000 | 0x00021AA4 | 0x00021C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.34588 |
.data | 0x000F2000 | 0x00100CE0 | 0x000FDE00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.8737 |
.rsrc | 0x001F3000 | 0x000048C0 | 0x00004A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.55147 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.8674 | 874 | UNKNOWN | English - United States | RT_MANIFEST |
Imports
ADVAPI32.DLL |
COMCTL32.DLL |
COMDLG32.DLL |
GDI32.DLL |
KERNEL32.dll |
MSVCRT.dll |
NTDLL.DLL |
OLE32.DLL |
SETUPAPI.DLL |
SHELL32.DLL |
Total processes
62
Monitored processes
18
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
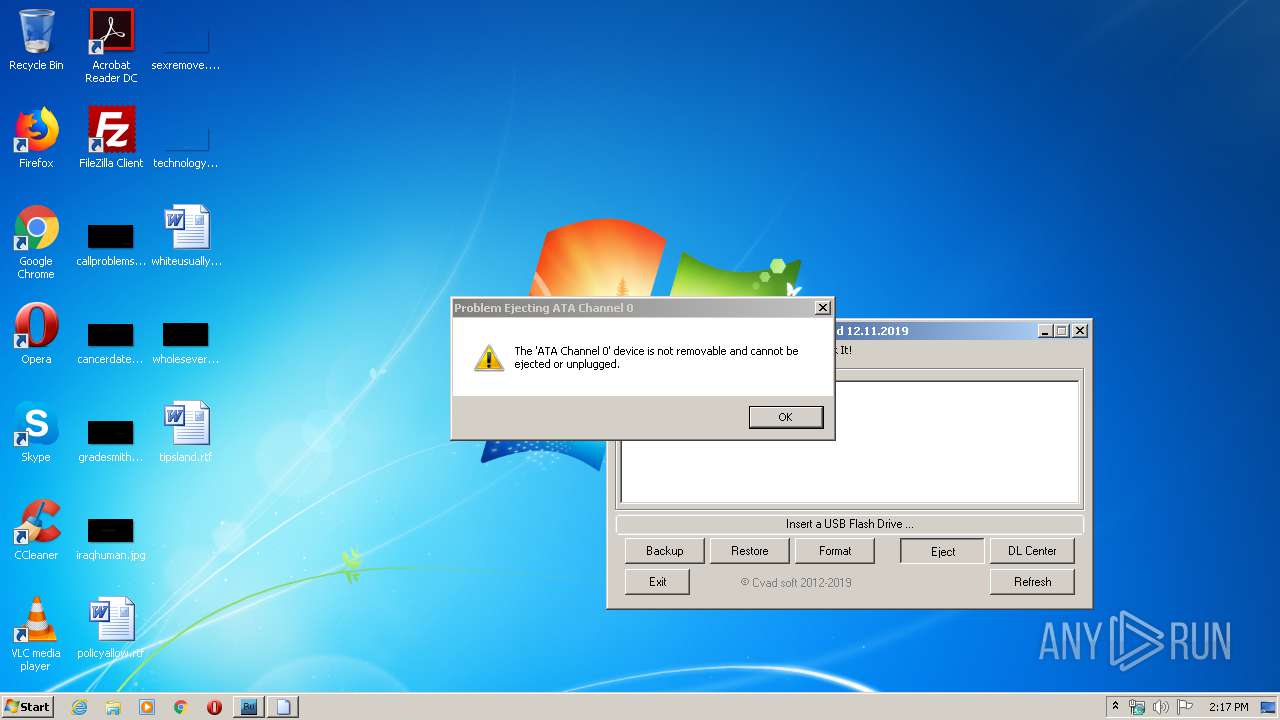
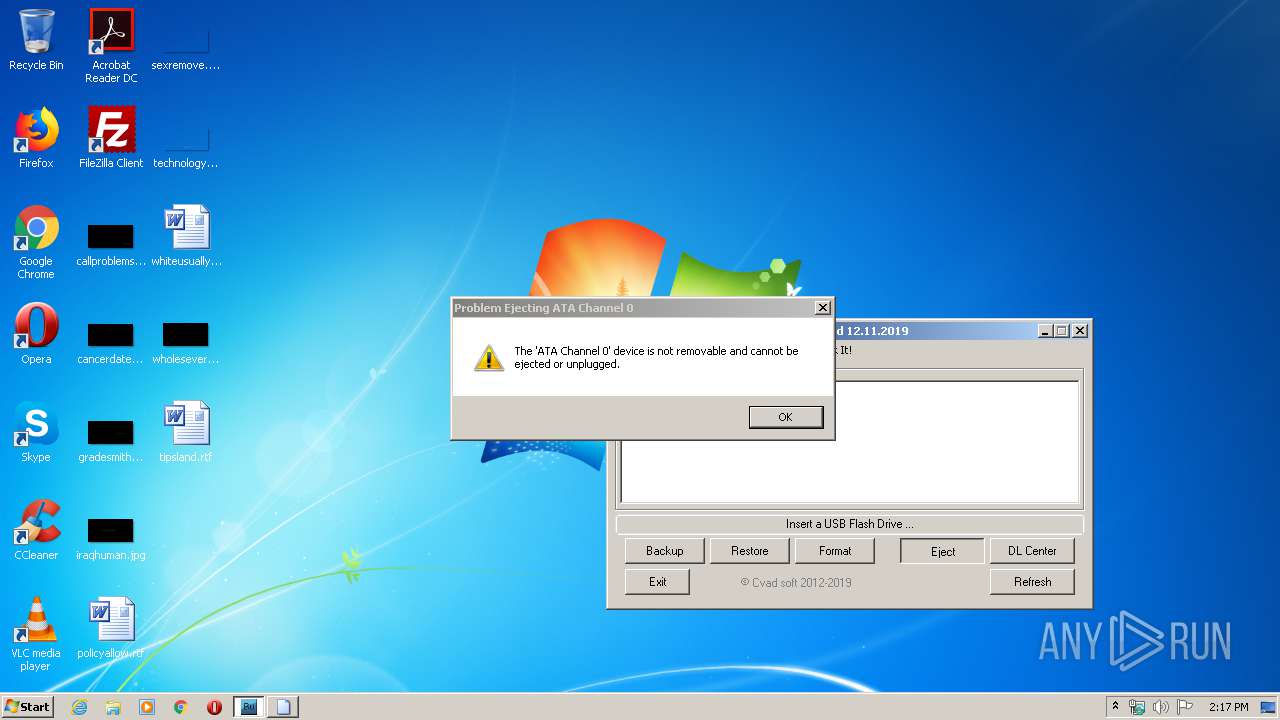
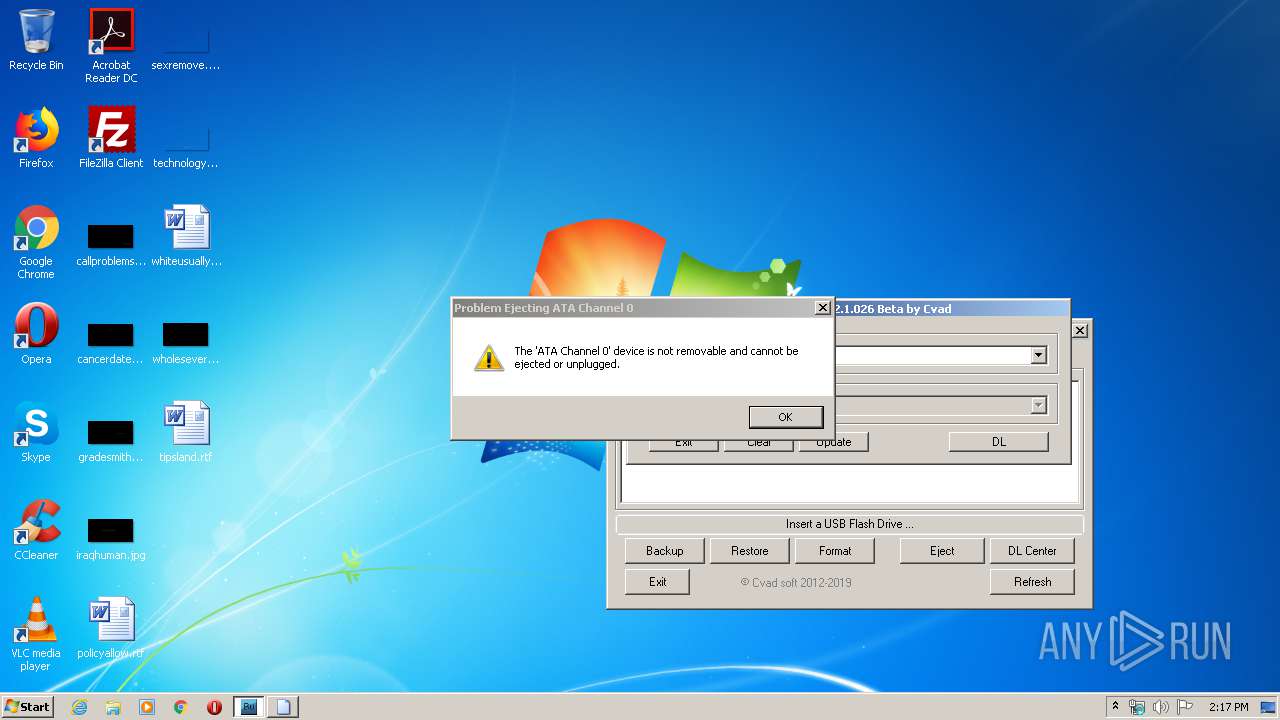
| 1840 | rundll32.exe C:\Windows\system32\hotplug.dll,HotPlugEjectVetoed \\.\pipe\PNP_HotPlug_Pipe_1.{64d5e8d0-8326-46b2-bbd4-8590da209aa6} | C:\Windows\system32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1852 | rundll32.exe C:\Windows\system32\hotplug.dll,HotPlugEjectVetoed \\.\pipe\PNP_HotPlug_Pipe_1.{5ea00cfc-90a6-41f0-bdcb-00377e02136c} | C:\Windows\system32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2068 | "C:\Users\admin\AppData\Local\Temp\ceace56b50080784e12d4a7a5e77cd23afa5589b492fd27d488a368346e4422c.exe" | C:\Users\admin\AppData\Local\Temp\ceace56b50080784e12d4a7a5e77cd23afa5589b492fd27d488a368346e4422c.exe | explorer.exe | ||||||||||||
User: admin Company: Cvad Software Integrity Level: HIGH Description: Utility to make bootable EFI USB Flash Drive Exit code: 0 Version: 2.1.2019.26 Modules
| |||||||||||||||
| 2300 | rundll32.exe C:\Windows\system32\hotplug.dll,HotPlugEjectVetoed \\.\pipe\PNP_HotPlug_Pipe_1.{b782f33a-34db-48d9-85f2-4e8a70ae37fc} | C:\Windows\system32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2432 | rundll32.exe C:\Windows\system32\hotplug.dll,HotPlugEjectVetoed \\.\pipe\PNP_HotPlug_Pipe_1.{45dadd77-2c1c-464d-aece-6c2680237765} | C:\Windows\system32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2512 | rundll32.exe C:\Windows\system32\hotplug.dll,HotPlugEjectVetoed \\.\pipe\PNP_HotPlug_Pipe_1.{fd14ffb7-7ad2-42f1-92c6-9be035266b7d} | C:\Windows\system32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2548 | rundll32.exe C:\Windows\system32\hotplug.dll,HotPlugEjectVetoed \\.\pipe\PNP_HotPlug_Pipe_1.{3e973be9-ff26-47fd-8a09-f42bbf306fd2} | C:\Windows\system32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2660 | rundll32.exe C:\Windows\system32\hotplug.dll,HotPlugEjectVetoed \\.\pipe\PNP_HotPlug_Pipe_1.{e4e4e5b1-42e8-4e0a-89d3-ea8f60bc0bd5} | C:\Windows\system32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2860 | "C:\Users\admin\AppData\Local\Temp\ceace56b50080784e12d4a7a5e77cd23afa5589b492fd27d488a368346e4422c.exe" | C:\Users\admin\AppData\Local\Temp\ceace56b50080784e12d4a7a5e77cd23afa5589b492fd27d488a368346e4422c.exe | — | explorer.exe | |||||||||||
User: admin Company: Cvad Software Integrity Level: MEDIUM Description: Utility to make bootable EFI USB Flash Drive Exit code: 3221226540 Version: 2.1.2019.26 Modules
| |||||||||||||||
| 3120 | "cmd" /c ver | C:\Windows\system32\cmd.exe | — | ceace56b50080784e12d4a7a5e77cd23afa5589b492fd27d488a368346e4422c.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
9
Read events
7
Write events
2
Delete events
0
Modification events
| (PID) Process: | (2068) ceace56b50080784e12d4a7a5e77cd23afa5589b492fd27d488a368346e4422c.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\Explorer |
| Operation: | write | Name: | NoDriveTypeAutoRun |
Value: 255 | |||
| (PID) Process: | (2068) ceace56b50080784e12d4a7a5e77cd23afa5589b492fd27d488a368346e4422c.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\Explorer |
| Operation: | write | Name: | NoDriveTypeAutoRun |
Value: 0 | |||
Executable files
0
Suspicious files
0
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2068 | ceace56b50080784e12d4a7a5e77cd23afa5589b492fd27d488a368346e4422c.exe | C:\Users\admin\AppData\Local\Temp\UserDL.ini | text | |
MD5:— | SHA256:— | |||
| 2068 | ceace56b50080784e12d4a7a5e77cd23afa5589b492fd27d488a368346e4422c.exe | C:\Users\admin\AppData\Local\Temp\ceace56b50080784e12d4a7a5e77cd23afa5589b492fd27d488a368346e4422c.ini | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report