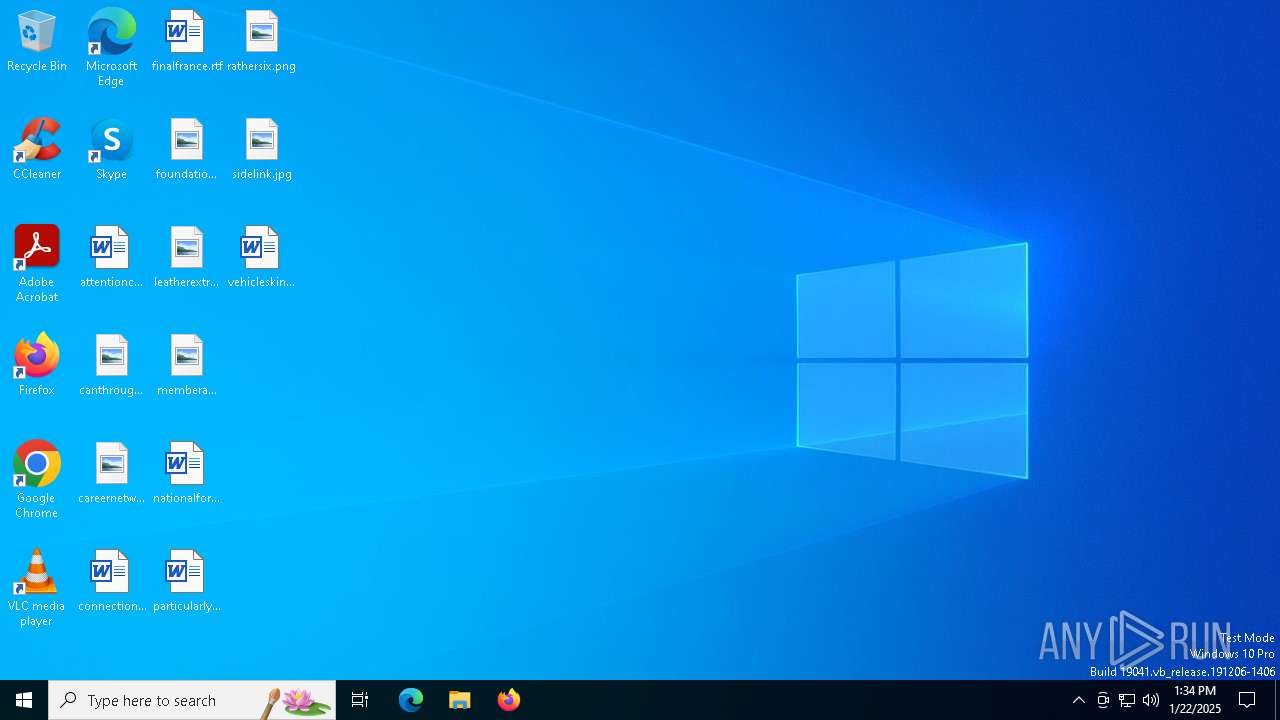
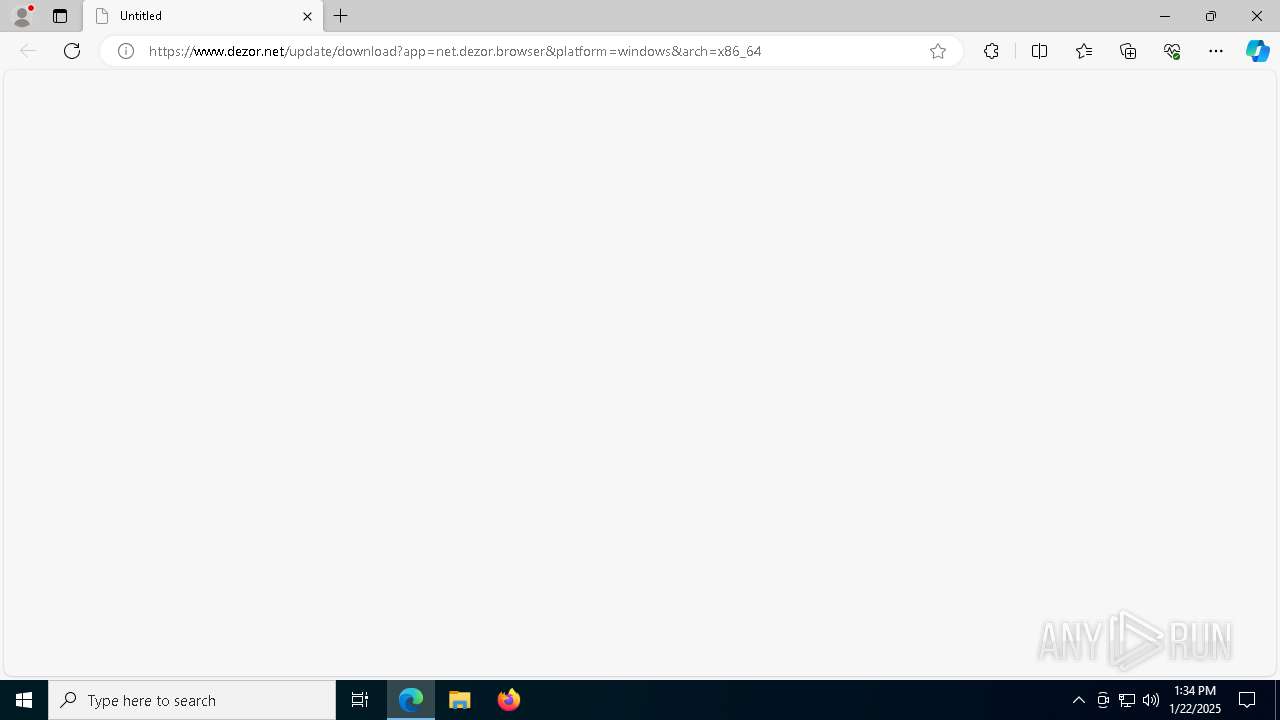
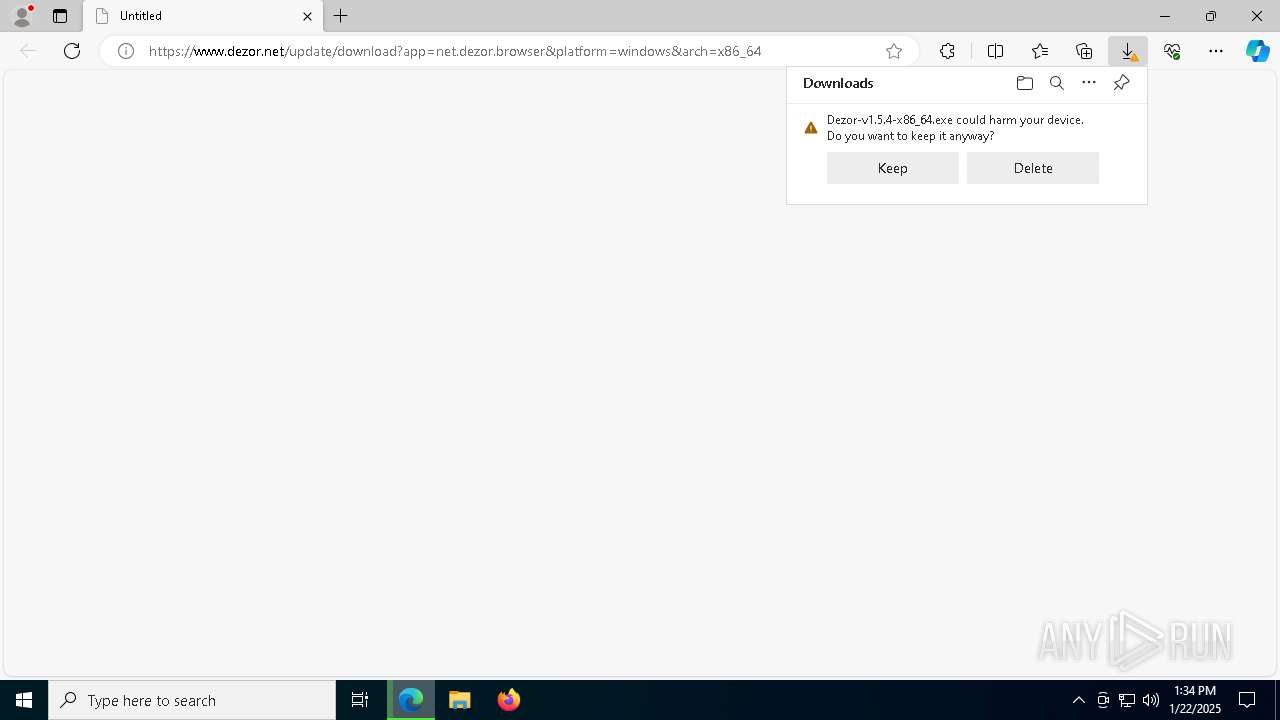
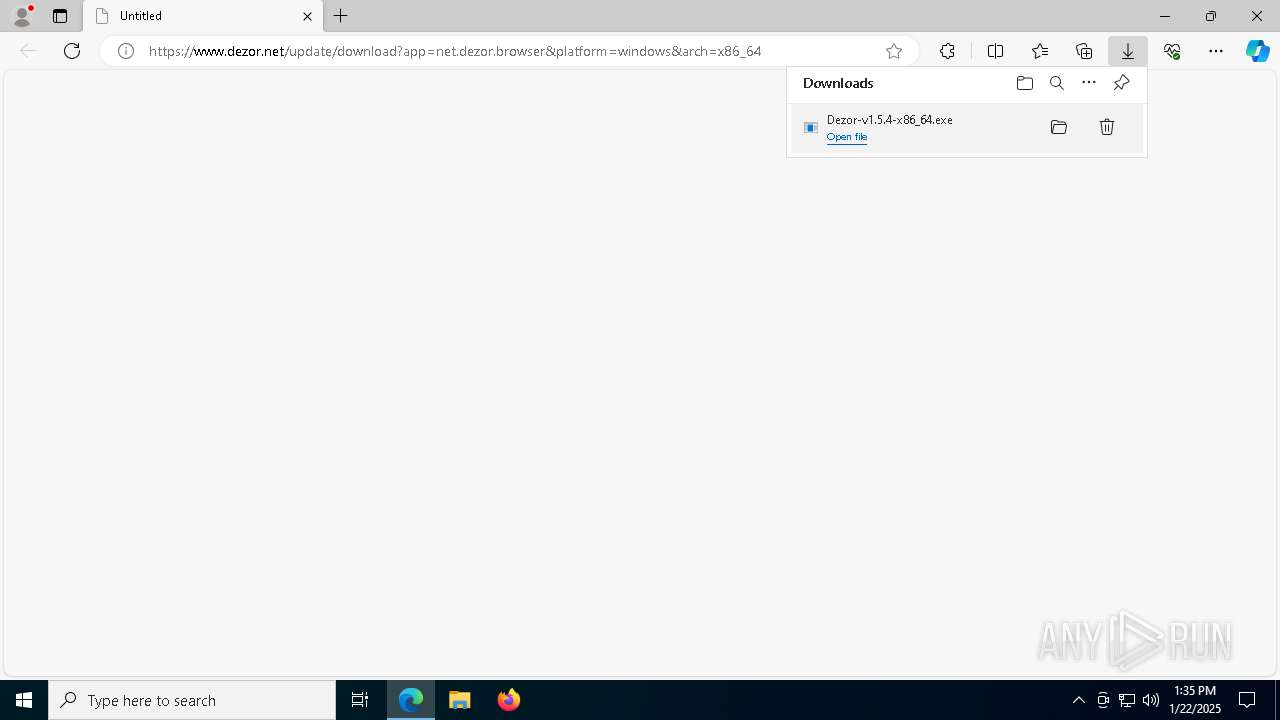
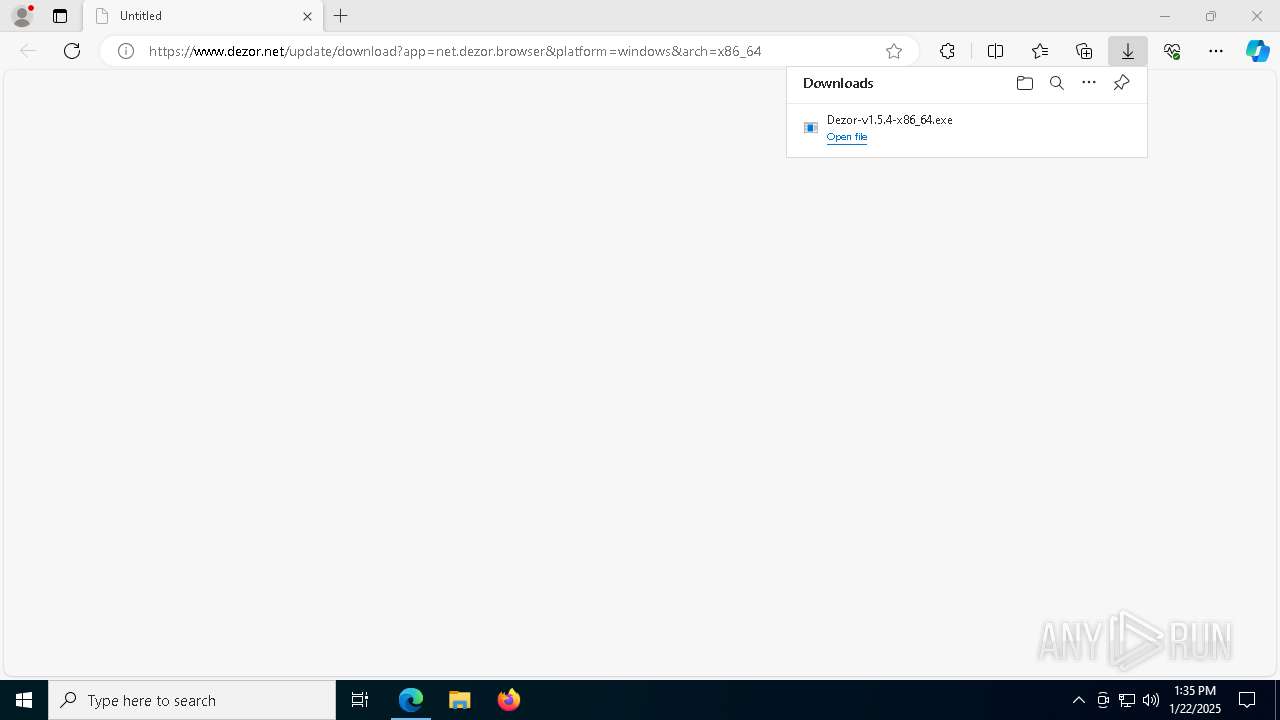
| URL: | https://www.dezor.net/update/download?app=net.dezor.browser&platform=windows&arch=x86_64 |
| Full analysis: | https://app.any.run/tasks/a8038797-0d44-492d-be36-aea8eb1127e2 |
| Verdict: | Malicious activity |
| Analysis date: | January 22, 2025, 13:34:43 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 7C814579A75C32511895C231BAD4B230 |
| SHA1: | 864880B6E7E8980A1B028E83CD011954A7F7F920 |
| SHA256: | CEA24853A2FEEE8AC697FD2774A47B47B50B4D6436D844ECA4F0D2BE461FB159 |
| SSDEEP: | 3:N8DSLUQm5EhEMJJYW/LZ4R:2OLUcO |
MALICIOUS
No malicious indicators.SUSPICIOUS
Get information on the list of running processes
- Dezor-v1.5.4-x86_64.exe (PID: 4128)
- cmd.exe (PID: 7992)
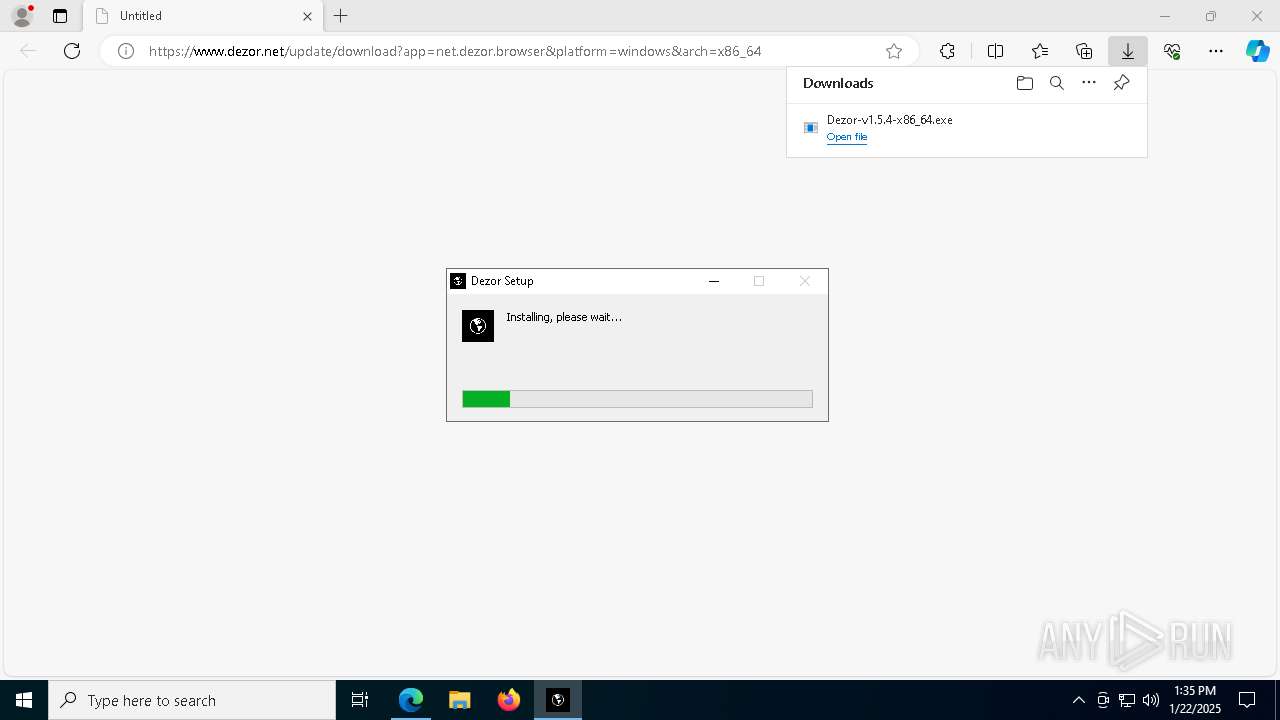
The process creates files with name similar to system file names
- Dezor-v1.5.4-x86_64.exe (PID: 4128)
Process drops legitimate windows executable
- Dezor-v1.5.4-x86_64.exe (PID: 4128)
Malware-specific behavior (creating "System.dll" in Temp)
- Dezor-v1.5.4-x86_64.exe (PID: 4128)
Drops 7-zip archiver for unpacking
- Dezor-v1.5.4-x86_64.exe (PID: 4128)
There is functionality for taking screenshot (YARA)
- Dezor-v1.5.4-x86_64.exe (PID: 4128)
Application launched itself
- Dezor.exe (PID: 5540)
Executable content was dropped or overwritten
- Dezor.exe (PID: 5540)
- Dezor-v1.5.4-x86_64.exe (PID: 4128)
Starts CMD.EXE for commands execution
- Dezor.exe (PID: 5540)
- Dezor-v1.5.4-x86_64.exe (PID: 4128)
Connects to unusual port
- sslocal.exe (PID: 7404)
INFO
Application launched itself
- msedge.exe (PID: 6648)
Executable content was dropped or overwritten
- msedge.exe (PID: 6648)
The sample compiled with english language support
- msedge.exe (PID: 6648)
- Dezor-v1.5.4-x86_64.exe (PID: 4128)
The process uses the downloaded file
- msedge.exe (PID: 6184)
- msedge.exe (PID: 6648)
- Dezor-v1.5.4-x86_64.exe (PID: 4128)
Checks supported languages
- Dezor-v1.5.4-x86_64.exe (PID: 4128)
- identity_helper.exe (PID: 7928)
- Dezor.exe (PID: 7956)
Reads the computer name
- identity_helper.exe (PID: 7928)
- Dezor.exe (PID: 6160)
Creates files or folders in the user directory
- Dezor-v1.5.4-x86_64.exe (PID: 4128)
- Dezor.exe (PID: 5540)
- Dezor.exe (PID: 6160)
Checks proxy server information
- Dezor.exe (PID: 5540)
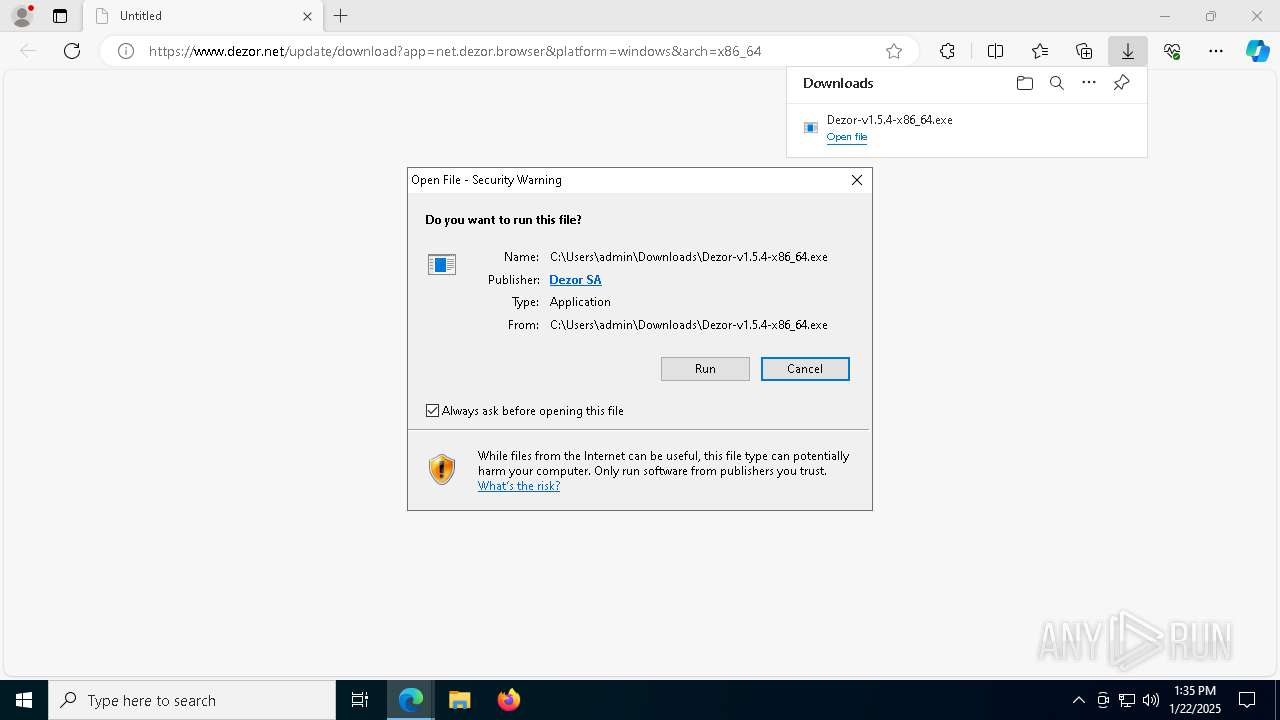
Manual execution by a user
- Dezor.exe (PID: 5540)
Create files in a temporary directory
- Dezor.exe (PID: 5540)
- Dezor-v1.5.4-x86_64.exe (PID: 4128)
Reads Environment values
- identity_helper.exe (PID: 7928)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
184
Monitored processes
52
Malicious processes
2
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 432 | "C:\Users\admin\AppData\Local\Programs\Dezor\Dezor.exe" --type=renderer --user-data-dir="C:\Users\admin\AppData\Roaming\Dezor" --standard-schemes=mhub,mediaurl --secure-schemes --bypasscsp-schemes --cors-schemes --fetch-schemes --service-worker-schemes --streaming-schemes --app-path="C:\Users\admin\AppData\Local\Programs\Dezor\resources\app.asar" --enable-sandbox --enable-blink-features --disable-blink-features --no-sandbox --register-pepper-plugins=mpvjs.node;application/x-mpvjs --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=9 --mojo-platform-channel-handle=2080 --field-trial-handle=1864,i,2165481107309334788,14782887986364319405,131072 --enable-features=PlatformHEVCDecoderSupport --disable-features=SpareRendererForSitePerProcess,WinRetrieveSuggestionsOnlyOnDemand /prefetch:1 | C:\Users\admin\AppData\Local\Programs\Dezor\Dezor.exe | — | Dezor.exe | |||||||||||
User: admin Company: GitHub, Inc. Integrity Level: MEDIUM Description: Dezor Version: 1.5.4 Modules
| |||||||||||||||
| 2092 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=edge_search_indexer.mojom.SearchIndexerInterfaceBroker --lang=en-US --service-sandbox-type=search_indexer --message-loop-type-ui --no-appcompat-clear --mojo-platform-channel-handle=1580 --field-trial-handle=2332,i,16515248052568852143,7056003562781464664,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2132 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --mojo-platform-channel-handle=3496 --field-trial-handle=2332,i,16515248052568852143,7056003562781464664,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 3128 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=7564 --field-trial-handle=2332,i,16515248052568852143,7056003562781464664,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 3224 | "C:\Users\admin\AppData\Local\Programs\Dezor\Dezor.exe" --type=gpu-process --no-sandbox --use-gpu-in-tests --user-data-dir="C:\Users\admin\AppData\Roaming\Dezor" --gpu-preferences=UAAAAAAAAADgAAAYAAAAAAAAAAAAAAAAAABgAAAAAAAwAAAAAAAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAEgAAAAAAAAASAAAAAAAAAAYAAAAAgAAABAAAAAAAAAAGAAAAAAAAAAQAAAAAAAAAAAAAAAOAAAAEAAAAAAAAAABAAAADgAAAAgAAAAAAAAACAAAAAAAAAA= --mojo-platform-channel-handle=1700 --field-trial-handle=1864,i,2165481107309334788,14782887986364319405,131072 --enable-features=PlatformHEVCDecoderSupport --disable-features=SpareRendererForSitePerProcess,WinRetrieveSuggestionsOnlyOnDemand /prefetch:2 | C:\Users\admin\AppData\Local\Programs\Dezor\Dezor.exe | — | Dezor.exe | |||||||||||
User: admin Company: GitHub, Inc. Integrity Level: MEDIUM Description: Dezor Version: 1.5.4 Modules
| |||||||||||||||
| 3280 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3296 | "C:\Users\admin\AppData\Local\Programs\Dezor\Dezor.exe" --type=renderer --user-data-dir="C:\Users\admin\AppData\Roaming\Dezor" --standard-schemes=mhub,mediaurl --secure-schemes --bypasscsp-schemes --cors-schemes --fetch-schemes --service-worker-schemes --streaming-schemes --app-path="C:\Users\admin\AppData\Local\Programs\Dezor\resources\app.asar" --no-sandbox --no-zygote --enable-blink-features --disable-blink-features --no-sandbox --register-pepper-plugins=mpvjs.node;application/x-mpvjs --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --mojo-platform-channel-handle=3668 --field-trial-handle=1864,i,2165481107309334788,14782887986364319405,131072 --enable-features=PlatformHEVCDecoderSupport --disable-features=SpareRendererForSitePerProcess,WinRetrieveSuggestionsOnlyOnDemand /prefetch:1 | C:\Users\admin\AppData\Local\Programs\Dezor\Dezor.exe | — | Dezor.exe | |||||||||||
User: admin Company: GitHub, Inc. Integrity Level: MEDIUM Description: Dezor Exit code: 0 Version: 1.5.4 Modules
| |||||||||||||||
| 4128 | "C:\Users\admin\Downloads\Dezor-v1.5.4-x86_64.exe" | C:\Users\admin\Downloads\Dezor-v1.5.4-x86_64.exe | msedge.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Version: 1.5.4 Modules
| |||||||||||||||
| 4164 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=7188 --field-trial-handle=2332,i,16515248052568852143,7056003562781464664,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 4740 | C:\WINDOWS\system32\cmd.exe /d /s /c "%windir%\System32\REG.exe QUERY HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Cryptography /v MachineGuid" | C:\Windows\System32\cmd.exe | — | Dezor.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
16 642
Read events
16 595
Write events
29
Delete events
18
Modification events
| (PID) Process: | (6648) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 9AD755D7E18A2F00 | |||
| (PID) Process: | (6648) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328530 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {7328D11E-83A2-4A84-BE6E-AF3C4A8CB862} | |||
| (PID) Process: | (6648) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328530 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {E56F46C9-00BC-45F5-A6E0-8511BD58E58B} | |||
| (PID) Process: | (6648) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6648) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6648) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6648) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (6648) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: CE6240D7E18A2F00 | |||
| (PID) Process: | (6648) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: DC1BAED7E18A2F00 | |||
| (PID) Process: | (6648) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | MicrosoftEdgeAutoLaunch_29EBC4579851B72EE312C449CF839B1A |
Value: "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --no-startup-window --win-session-start | |||
Executable files
41
Suspicious files
529
Text files
65
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6648 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF135b33.TMP | — | |
MD5:— | SHA256:— | |||
| 6648 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6648 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF135b33.TMP | — | |
MD5:— | SHA256:— | |||
| 6648 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6648 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF135b42.TMP | — | |
MD5:— | SHA256:— | |||
| 6648 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6648 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF135b42.TMP | — | |
MD5:— | SHA256:— | |||
| 6648 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6648 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF135b42.TMP | — | |
MD5:— | SHA256:— | |||
| 6648 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
21
TCP/UDP connections
81
DNS requests
64
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6648 | msedge.exe | GET | 200 | 104.18.38.233:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEEj8k7RgVZSNNqfJionWlBY%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6648 | msedge.exe | GET | 200 | 172.64.149.23:80 | http://ocsp.sectigo.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSdE3gf41WAic8Uh9lF92%2BIJqh5qwQUMuuSmv81lkgvKEBCcCA2kVwXheYCEGIdbQxSAZ47kHkVIIkhHAo%3D | unknown | — | — | whitelisted |
6648 | msedge.exe | GET | 200 | 172.64.149.23:80 | http://ocsp.sectigo.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQVD%2BnGf79Hpedv3mhy6uKMVZkPCQQUDyrLIIcouOxvSK4rVKYpqhekzQwCECGPqH3Sb%2BwIVOBFwrwKM70%3D | unknown | — | — | whitelisted |
6472 | backgroundTaskHost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
6592 | svchost.exe | GET | 206 | 23.48.23.44:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/6ca9004c-2afd-40c0-a9b1-4fec460952e5?P1=1738129079&P2=404&P3=2&P4=YyoE0uFWK61fToNb9ZsdYPG%2bawKFBehfZt60x3YS0Yo3F%2f%2bnrLzZmUF4v958aKpuRDy5qW%2fHvDmpkN9FHXeQcA%3d%3d | unknown | — | — | whitelisted |
6592 | svchost.exe | GET | 206 | 23.48.23.44:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/6ca9004c-2afd-40c0-a9b1-4fec460952e5?P1=1738129079&P2=404&P3=2&P4=YyoE0uFWK61fToNb9ZsdYPG%2bawKFBehfZt60x3YS0Yo3F%2f%2bnrLzZmUF4v958aKpuRDy5qW%2fHvDmpkN9FHXeQcA%3d%3d | unknown | — | — | whitelisted |
6592 | svchost.exe | HEAD | 200 | 23.48.23.44:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/6ca9004c-2afd-40c0-a9b1-4fec460952e5?P1=1738129079&P2=404&P3=2&P4=YyoE0uFWK61fToNb9ZsdYPG%2bawKFBehfZt60x3YS0Yo3F%2f%2bnrLzZmUF4v958aKpuRDy5qW%2fHvDmpkN9FHXeQcA%3d%3d | unknown | — | — | whitelisted |
6592 | svchost.exe | GET | 206 | 23.48.23.44:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/6ca9004c-2afd-40c0-a9b1-4fec460952e5?P1=1738129079&P2=404&P3=2&P4=YyoE0uFWK61fToNb9ZsdYPG%2bawKFBehfZt60x3YS0Yo3F%2f%2bnrLzZmUF4v958aKpuRDy5qW%2fHvDmpkN9FHXeQcA%3d%3d | unknown | — | — | whitelisted |
6592 | svchost.exe | GET | 206 | 23.48.23.44:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/6ca9004c-2afd-40c0-a9b1-4fec460952e5?P1=1738129079&P2=404&P3=2&P4=YyoE0uFWK61fToNb9ZsdYPG%2bawKFBehfZt60x3YS0Yo3F%2f%2bnrLzZmUF4v958aKpuRDy5qW%2fHvDmpkN9FHXeQcA%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1176 | svchost.exe | 40.126.31.67:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 2.17.190.73:80 | — | AKAMAI-AS | DE | unknown |
4712 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6984 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6984 | msedge.exe | 104.21.51.210:443 | cdn.dezor.net | — | — | unknown |
6648 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
6984 | msedge.exe | 142.250.186.65:443 | clients2.googleusercontent.com | GOOGLE | US | whitelisted |
1076 | svchost.exe | 23.218.210.69:443 | go.microsoft.com | AKAMAI-AS | DE | whitelisted |
6984 | msedge.exe | 13.107.21.239:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
login.live.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
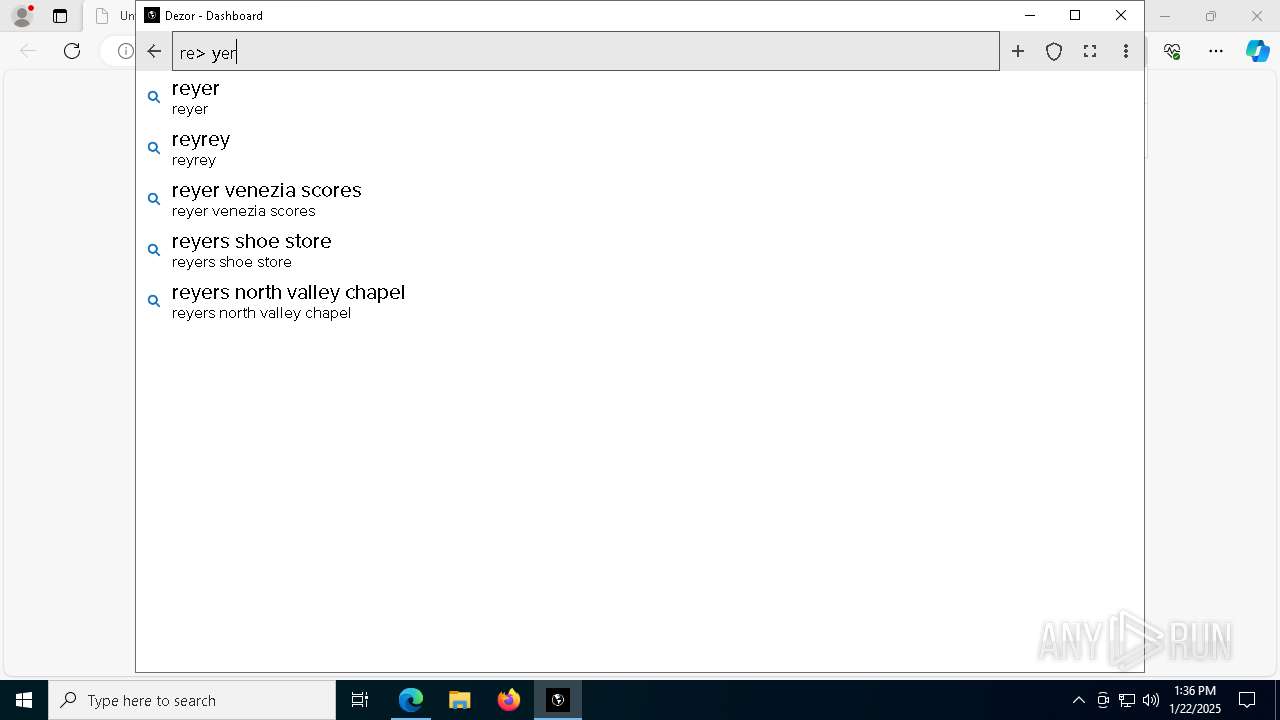
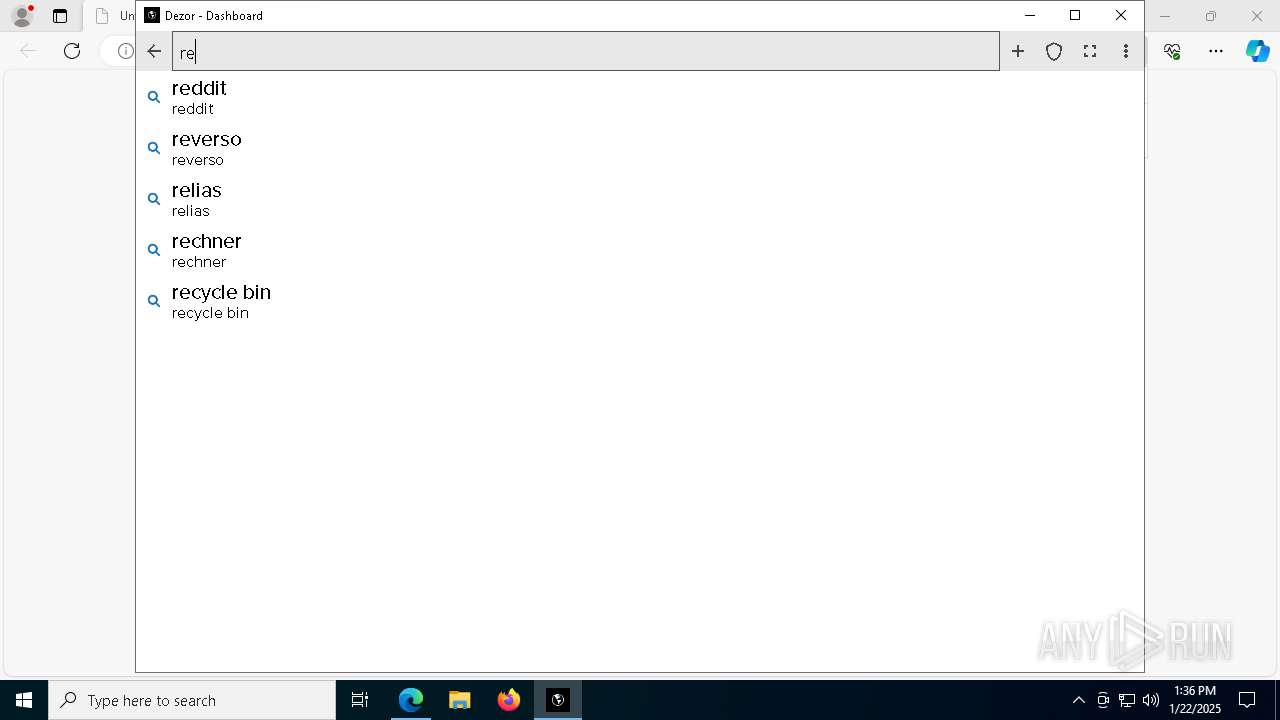
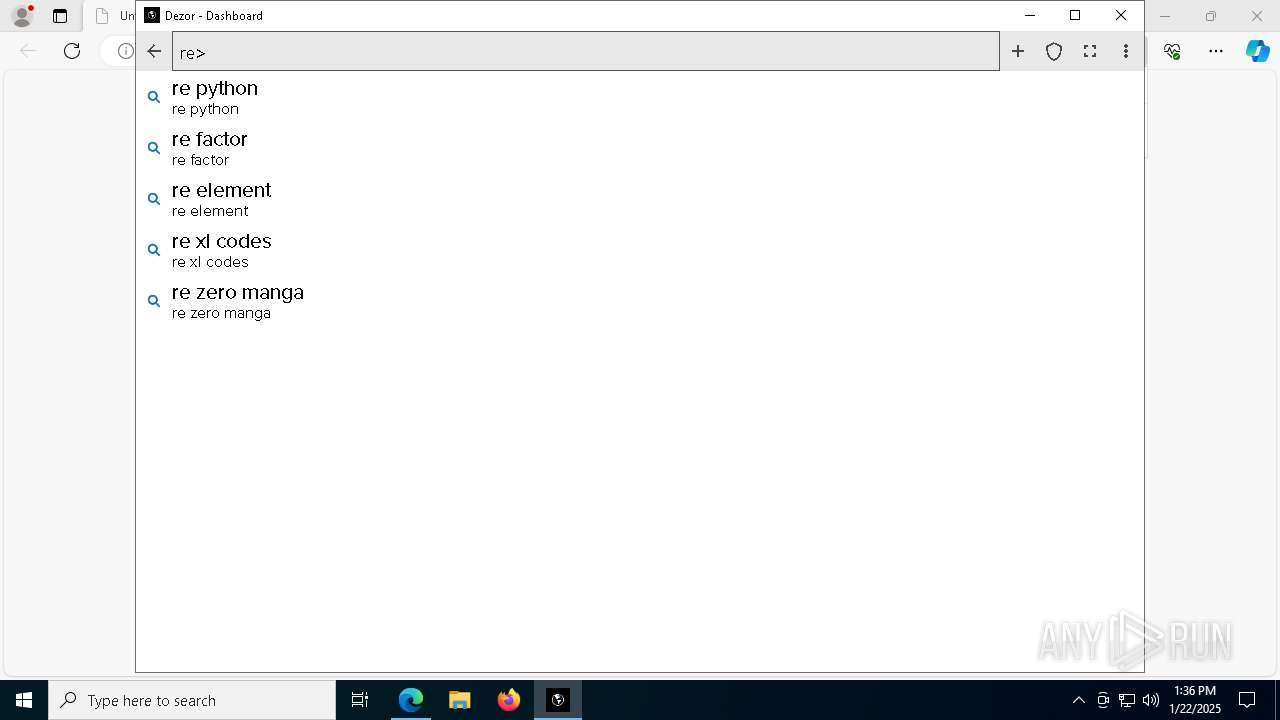
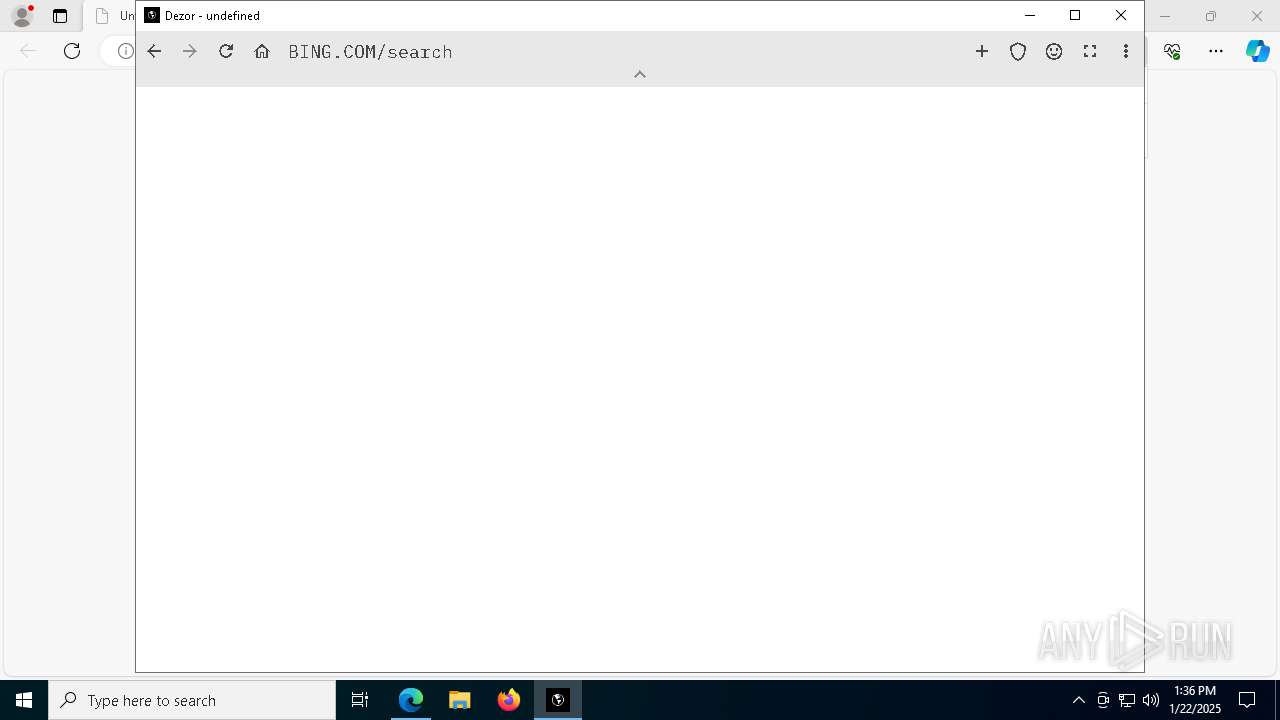
www.dezor.net |
| unknown |
go.microsoft.com |
| whitelisted |
business.bing.com |
| whitelisted |
bzib.nelreports.net |
| whitelisted |
cdn.dezor.net |
| unknown |
edgeservices.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2192 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |