| File name: | PCHunter32.exe |
| Full analysis: | https://app.any.run/tasks/bc1836aa-a9ff-4685-9db6-9a564c339c05 |
| Verdict: | Malicious activity |
| Analysis date: | December 07, 2018, 03:07:58 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 02C7DF0E0734208AFEF41EB4F7D359FA |
| SHA1: | C4E2953509E9A47D9EE0ECFA8C886328D700ED7E |
| SHA256: | CE90F3E0C2B13ECF22C2251810BDEAB9739EF18BE52B485877B5D521089EE024 |
| SSDEEP: | 98304:nveNx8SaUF0NwHS1cUlGZCVLdXg7Coa+QVB9RBgJSggMPbtlaqg6Iw9pkI6ISvbi:nveNx8SgpfBHfvKact |
MALICIOUS
No malicious indicators.SUSPICIOUS
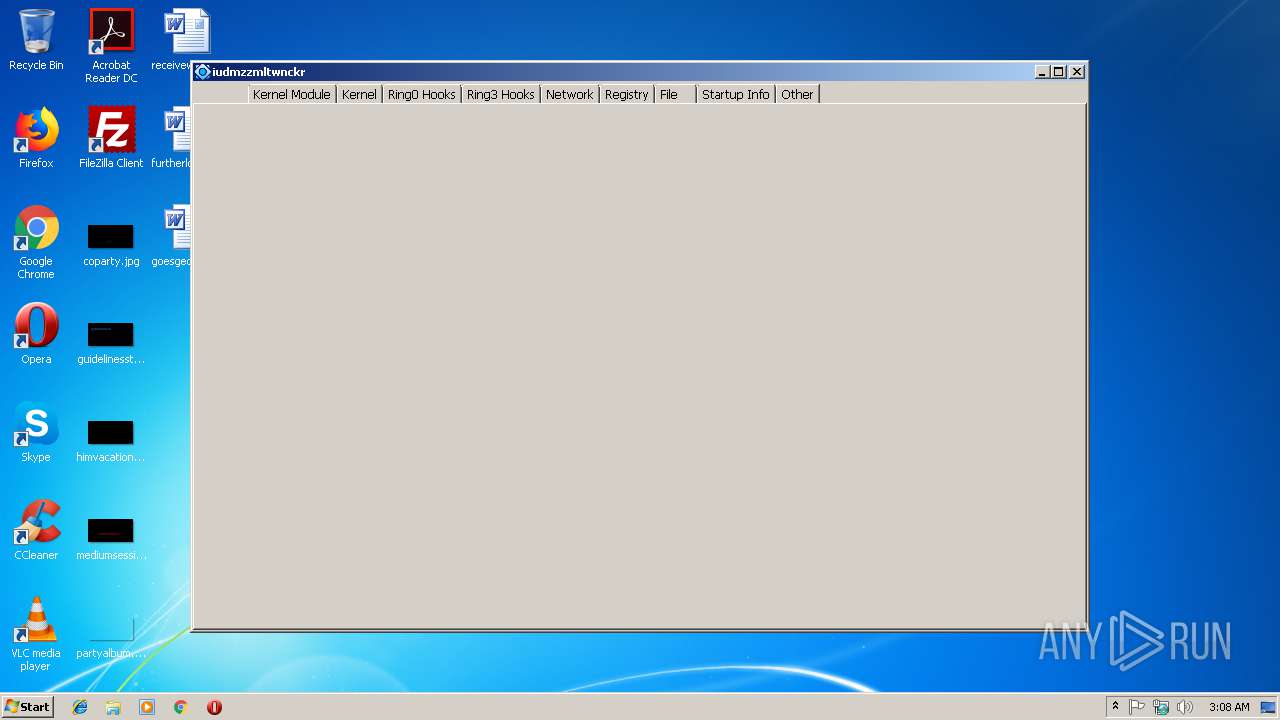
Creates or modifies windows services
- PCHunter32.exe (PID: 3956)
Executable content was dropped or overwritten
- PCHunter32.exe (PID: 3956)
Low-level read access rights to disk partition
- PCHunter32.exe (PID: 3956)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (52.9) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.5) |
| .exe | | | DOS Executable Generic (23.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:08:14 11:44:14+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 9 |
| CodeSize: | 3043840 |
| InitializedDataSize: | 3771392 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x280bb9 |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.5 |
| ProductVersionNumber: | 1.0.0.5 |
| FileFlagsMask: | 0x003f |
| FileFlags: | Special build |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| Comments: | 一普明为Windows系统信息查看工具(安全类) |
| CompanyName: | 一普明为(北京)信息技术有限公司 |
| FileDescription: | Epoolsoft Windows Information View Tools |
| FileVersion: | 1.0.0.5 |
| InternalName: | PCHunter |
| LegalCopyright: | (C) 2013-2020 Epoolsoft Corporation. All Rights Reserved. |
| OriginalFileName: | PCHunter.exe |
| ProductName: | PC Hunter |
| ProductVersion: | 1.0.0.5 |
| SpecialBuild: | 2018-04-29 Build |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 14-Aug-2018 09:44:14 |
| Detected languages: |
|
| Debug artifacts: |
|
| Comments: | 一普明为Windows系统信息查看工具(安全类) |
| CompanyName: | 一普明为(北京)信息技术有限公司 |
| FileDescription: | Epoolsoft Windows Information View Tools |
| FileVersion: | 1.0.0.5 |
| InternalName: | PCHunter |
| LegalCopyright: | (C) 2013-2020 Epoolsoft Corporation. All Rights Reserved. |
| OriginalFilename: | PCHunter.exe |
| ProductName: | PC Hunter |
| ProductVersion: | 1.0.0.5 |
| SpecialBuild: | 2018-04-29 Build |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0xC276 |
| Initial IP value: | 0x374D |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000108 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 14-Aug-2018 09:44:14 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x002E707A | 0x002E7200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.59389 |
.rdata | 0x002E9000 | 0x00133914 | 0x00133A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.24374 |
.data | 0x0041D000 | 0x000C0558 | 0x00073A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.42609 |
.rsrc | 0x004DE000 | 0x001F1788 | 0x001F1800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.43486 |
.vmp0 | 0x006D0000 | 0x0002A4C9 | 0x0002A600 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.99858 |
.reloc | 0x006FB000 | 0x00000018 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 0.236539 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.77792 | 357 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 2.6906 | 296 | Latin 1 / Western European | Chinese - PRC | RT_ICON |
3 | 2.52047 | 296 | Latin 1 / Western European | Chinese - PRC | RT_ICON |
4 | 2.60217 | 296 | Latin 1 / Western European | Chinese - PRC | RT_ICON |
5 | 2.8139 | 296 | Latin 1 / Western European | Chinese - PRC | RT_ICON |
6 | 2.73517 | 296 | Latin 1 / Western European | Chinese - PRC | RT_ICON |
7 | 2.08563 | 76 | Latin 1 / Western European | Chinese - PRC | RT_STRING |
8 | 4.03806 | 1128 | Latin 1 / Western European | Chinese - PRC | RT_ICON |
9 | 4.4558 | 1384 | Latin 1 / Western European | Chinese - PRC | RT_ICON |
10 | 3.16973 | 1384 | Latin 1 / Western European | Chinese - PRC | RT_ICON |
Imports
ADVAPI32.dll |
COMCTL32.dll |
COMDLG32.dll |
CRYPT32.dll |
GDI32.dll |
IMM32.dll |
IPHLPAPI.DLL |
KERNEL32.dll |
MSIMG32.dll |
NETAPI32.dll |
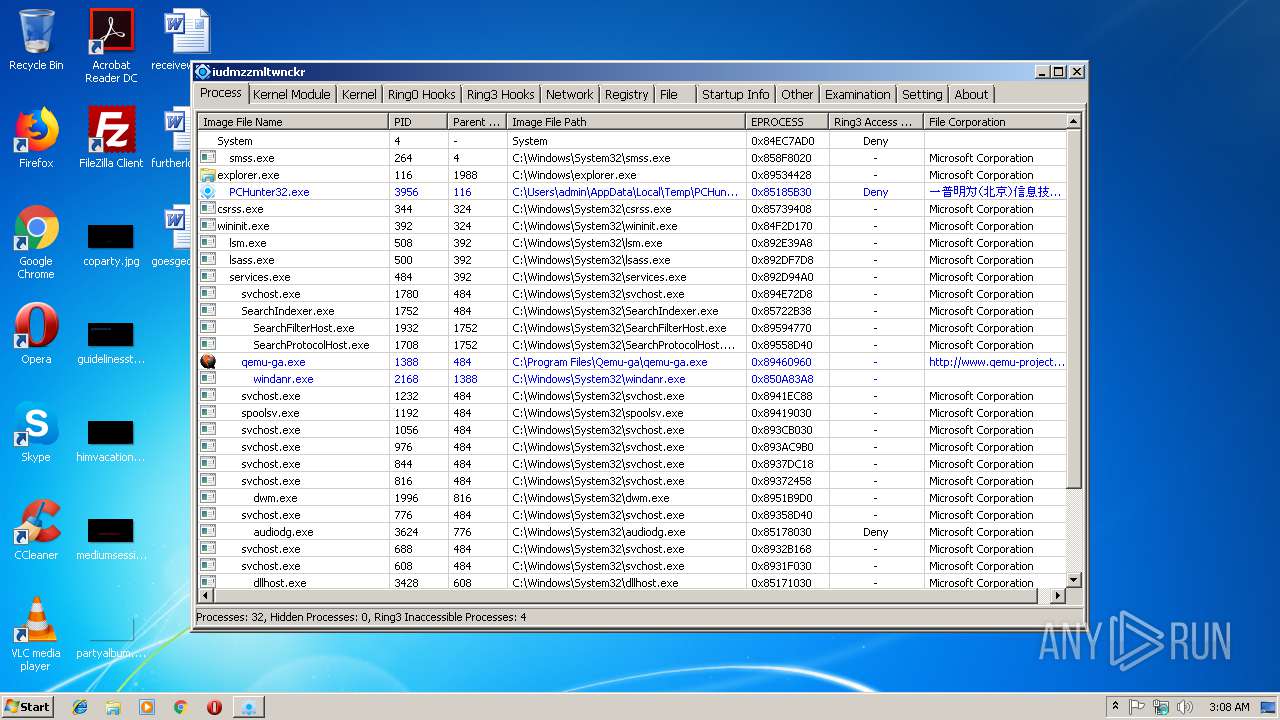
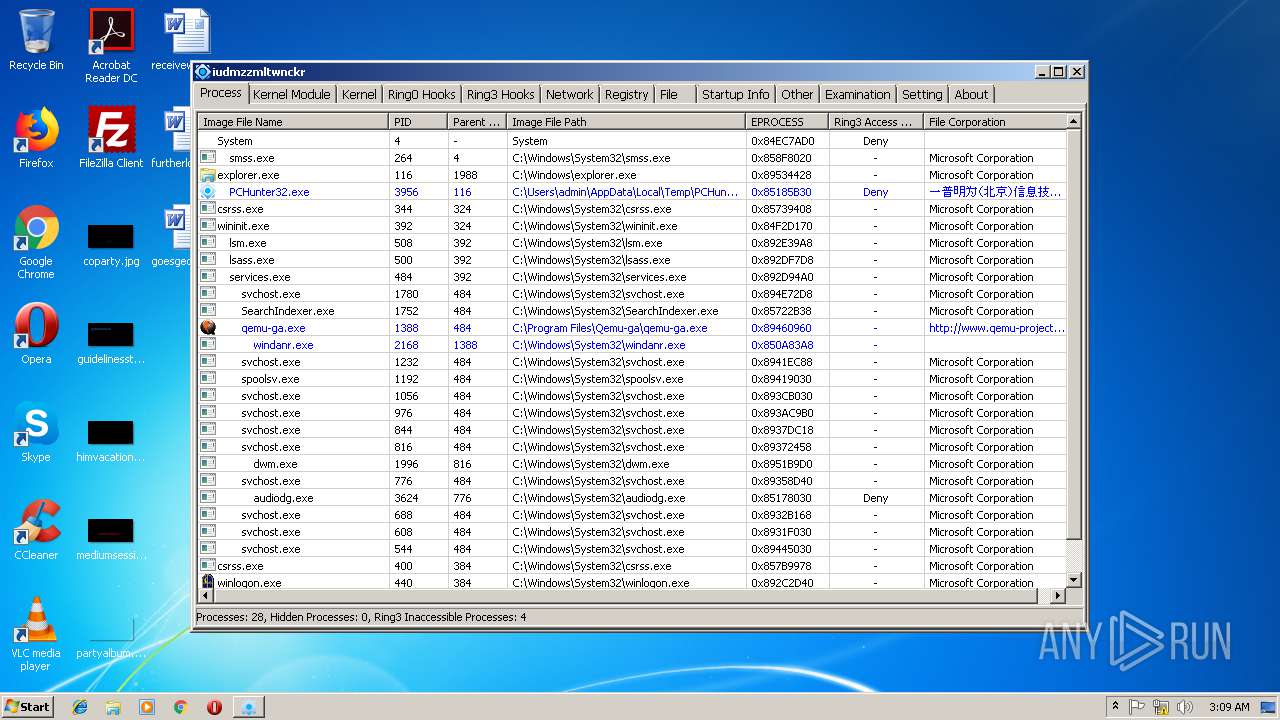
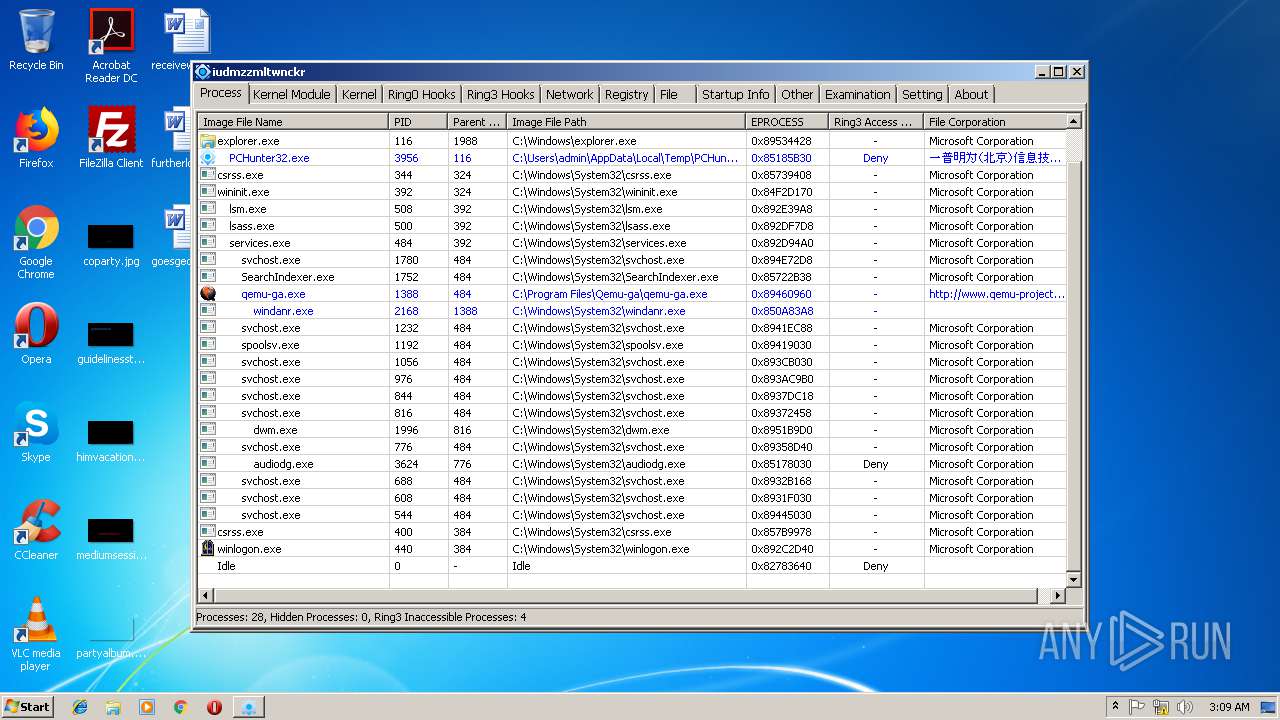
Total processes
34
Monitored processes
2
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
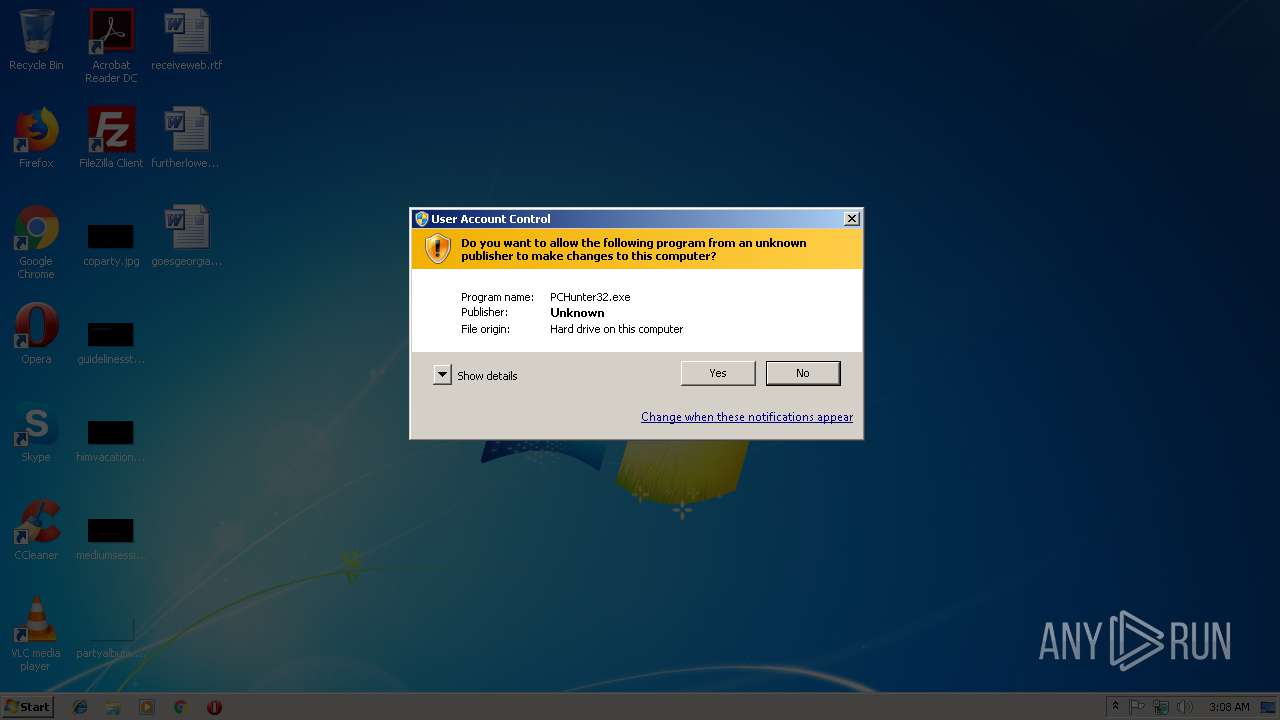
| 2968 | "C:\Users\admin\AppData\Local\Temp\PCHunter32.exe" | C:\Users\admin\AppData\Local\Temp\PCHunter32.exe | — | explorer.exe | |||||||||||
User: admin Company: 一普明为(北京)信息技术有限公司 Integrity Level: MEDIUM Description: Epoolsoft Windows Information View Tools Exit code: 3221226540 Version: 1.0.0.5 Modules
| |||||||||||||||
| 3956 | "C:\Users\admin\AppData\Local\Temp\PCHunter32.exe" | C:\Users\admin\AppData\Local\Temp\PCHunter32.exe | explorer.exe | ||||||||||||
User: admin Company: 一普明为(北京)信息技术有限公司 Integrity Level: HIGH Description: Epoolsoft Windows Information View Tools Exit code: 0 Version: 1.0.0.5 Modules
| |||||||||||||||
Total events
60
Read events
36
Write events
22
Delete events
2
Modification events
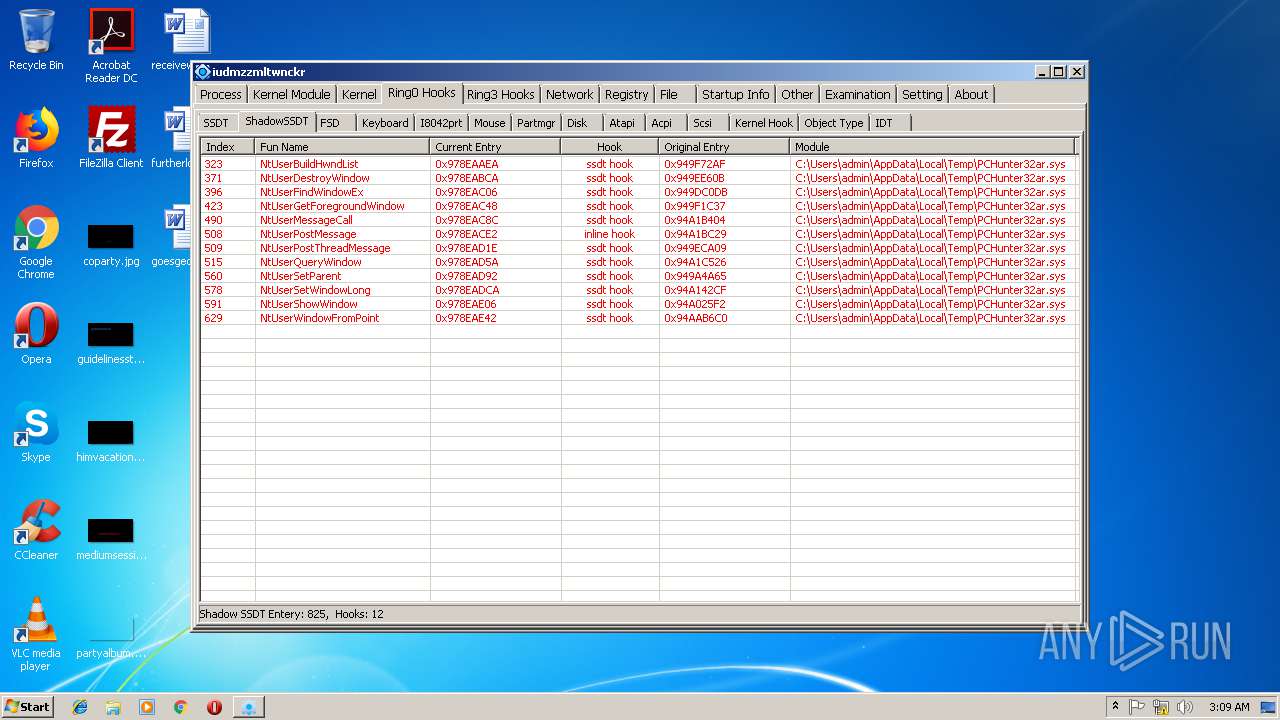
| (PID) Process: | (3956) PCHunter32.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\PCHunter32ar |
| Operation: | write | Name: | Type |
Value: 1 | |||
| (PID) Process: | (3956) PCHunter32.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\PCHunter32ar |
| Operation: | write | Name: | ErrorControl |
Value: 1 | |||
| (PID) Process: | (3956) PCHunter32.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\PCHunter32ar |
| Operation: | write | Name: | Start |
Value: 1 | |||
| (PID) Process: | (3956) PCHunter32.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\PCHunter32ar |
| Operation: | write | Name: | ImagePath |
Value: \??\C:\Users\admin\AppData\Local\Temp\PCHunter32ar.sys | |||
| (PID) Process: | (3956) PCHunter32.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\PCHunter32ar\Enum |
| Operation: | delete key | Name: | |
Value: | |||
| (PID) Process: | (3956) PCHunter32.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\PCHunter32ar |
| Operation: | delete key | Name: | |
Value: | |||
| (PID) Process: | (3956) PCHunter32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\PCHunter32_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3956) PCHunter32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\PCHunter32_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (3956) PCHunter32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\PCHunter32_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3956) PCHunter32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\PCHunter32_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
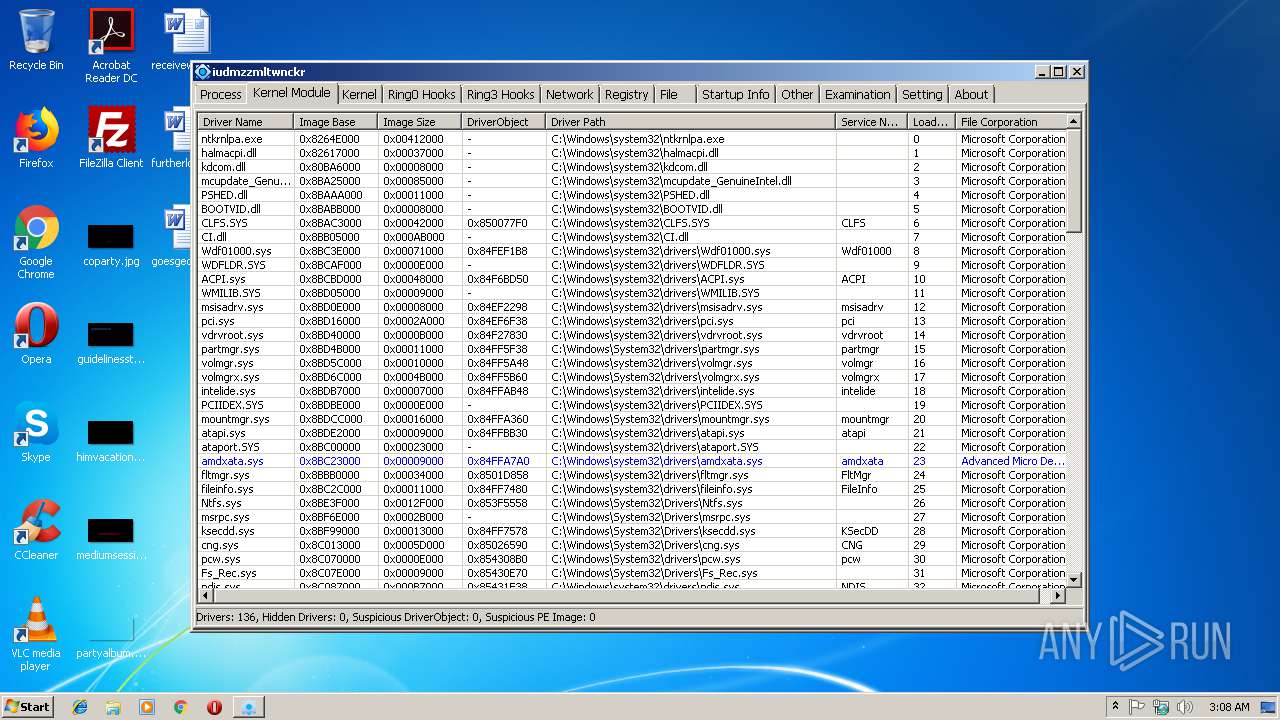
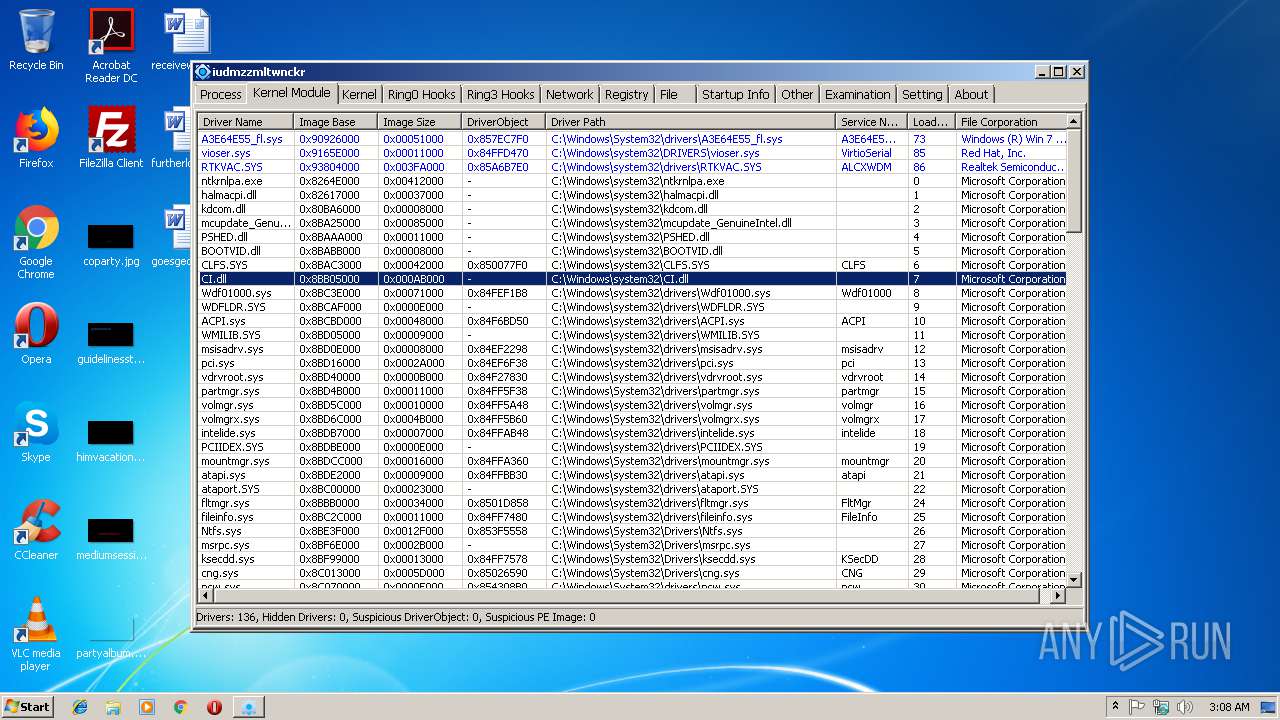
Executable files
1
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3956 | PCHunter32.exe | C:\Users\admin\AppData\Local\Temp\PCHunter32ar.sys | executable | |
MD5:9B3C23898430562D952BBC116D8ADA87 | SHA256:692E3CDB7178BEA1CD83D40CD869A77832A2642E9E2A0236AB0C73643654500C | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
1
DNS requests
1
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3956 | PCHunter32.exe | GET | 404 | 120.133.5.200:80 | http://www.epoolsoft.com/PCHunter_StandardV1.55=A4C2B0AE1B16D62545410189102FC1ED9FBD918D447169B141FB79AE219533EA01CB197252D11B86A40CE8C2735449AC | CN | html | 317 b | malicious |
3956 | PCHunter32.exe | GET | 404 | 120.133.5.200:80 | http://www.epoolsoft.com/pchunter/pchunter_free | CN | html | 187 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3956 | PCHunter32.exe | 120.133.5.200:80 | www.epoolsoft.com | CHINA UNICOM China169 Backbone | CN | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.epoolsoft.com |
| malicious |