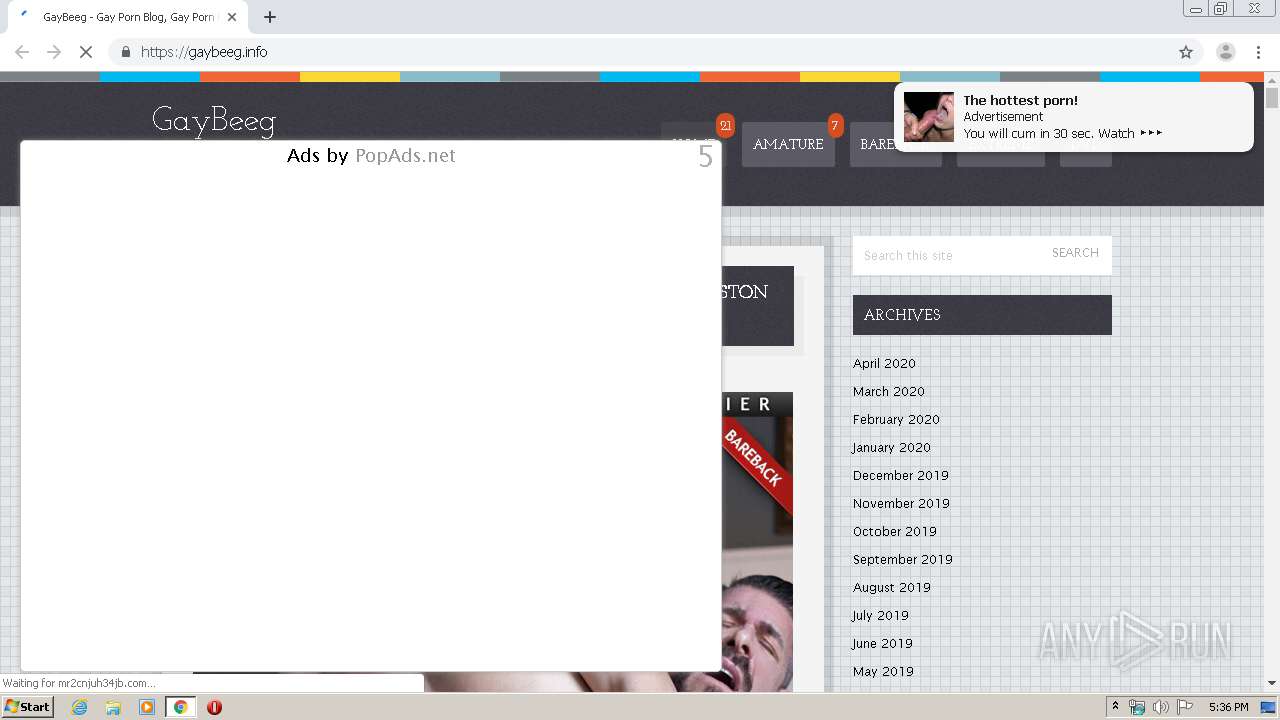
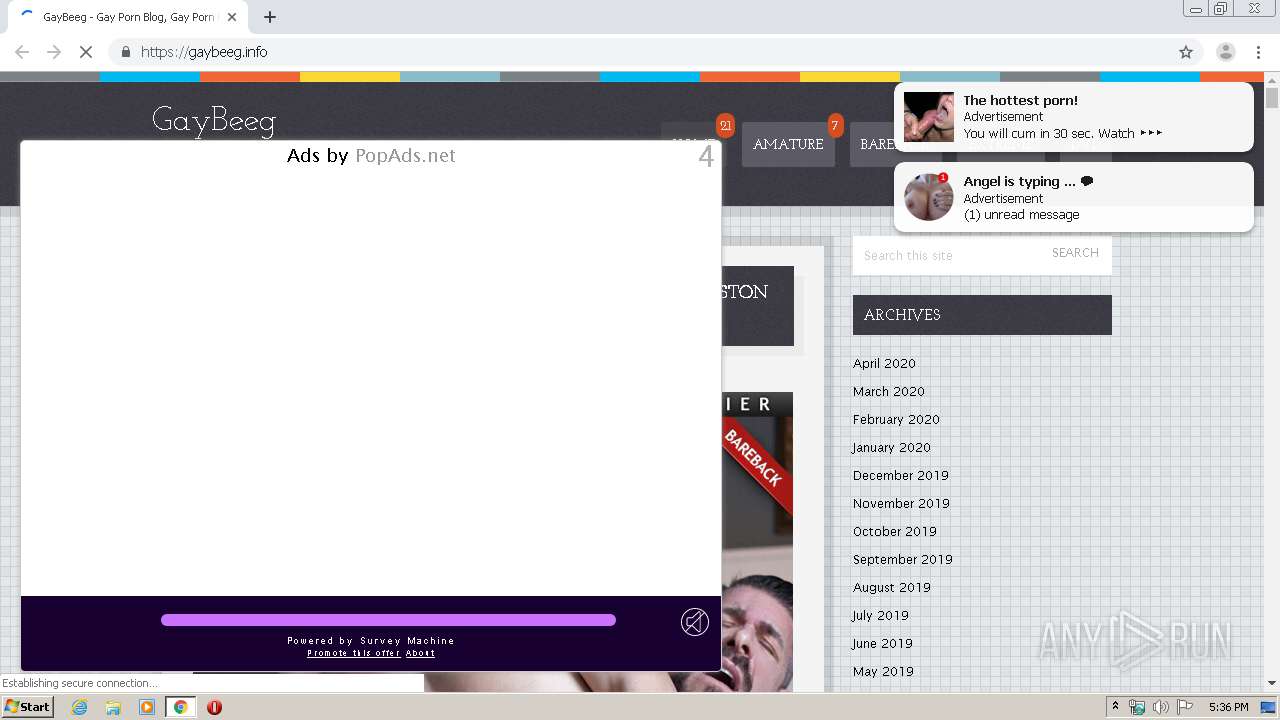
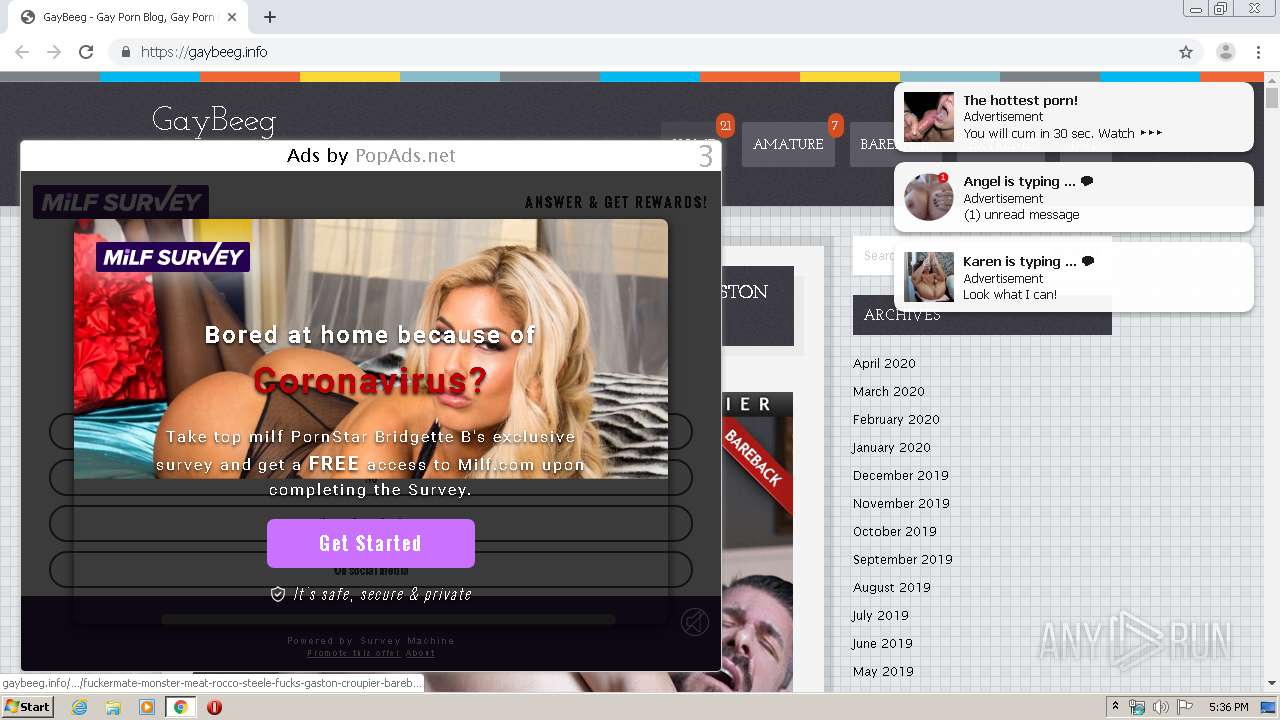
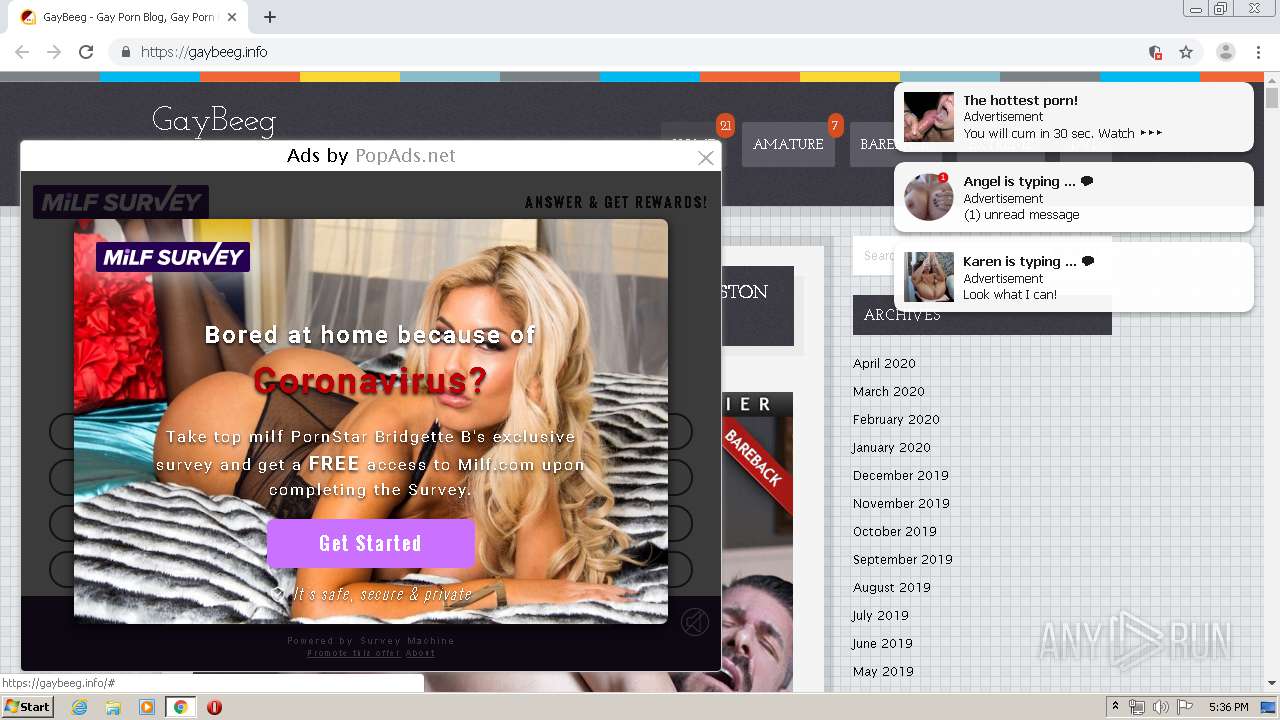
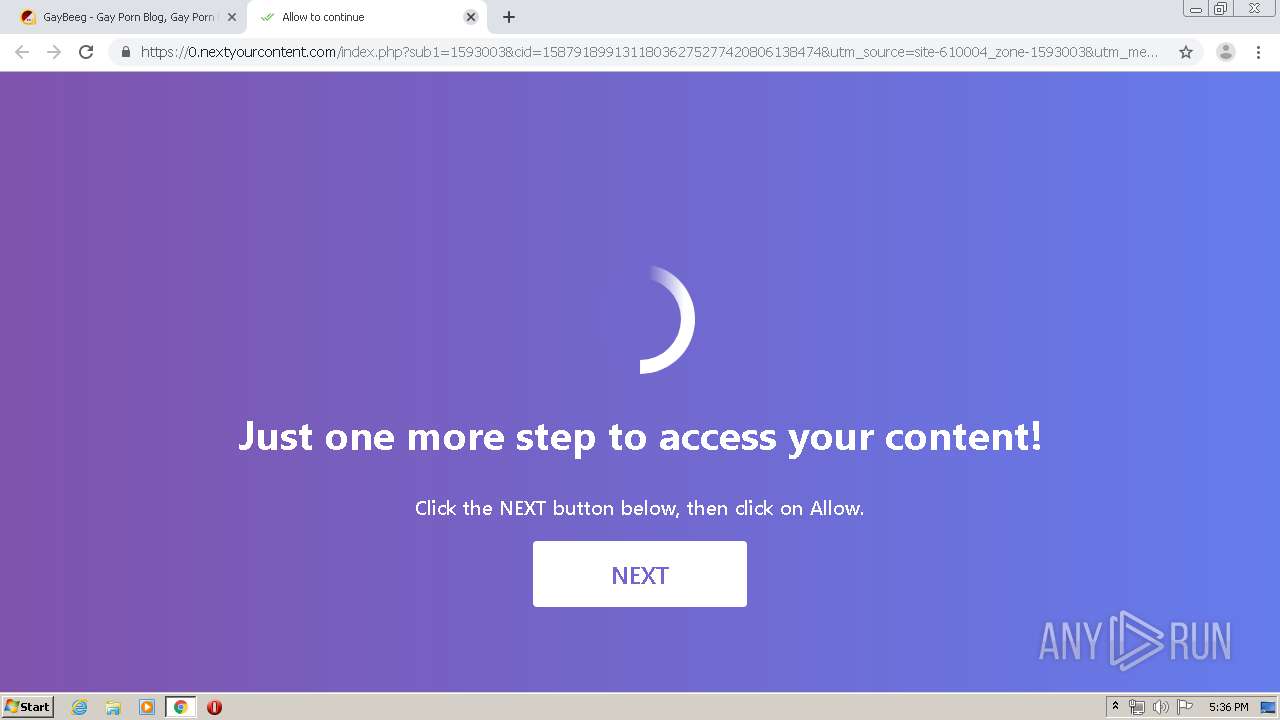
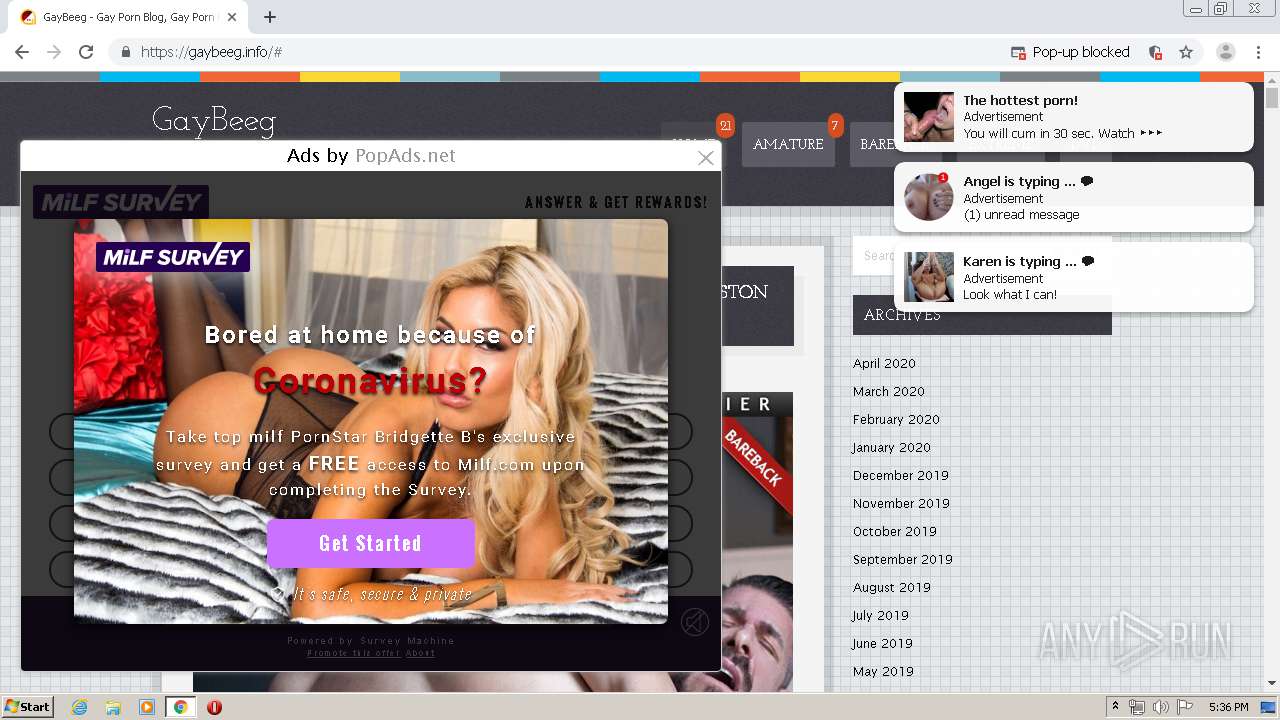
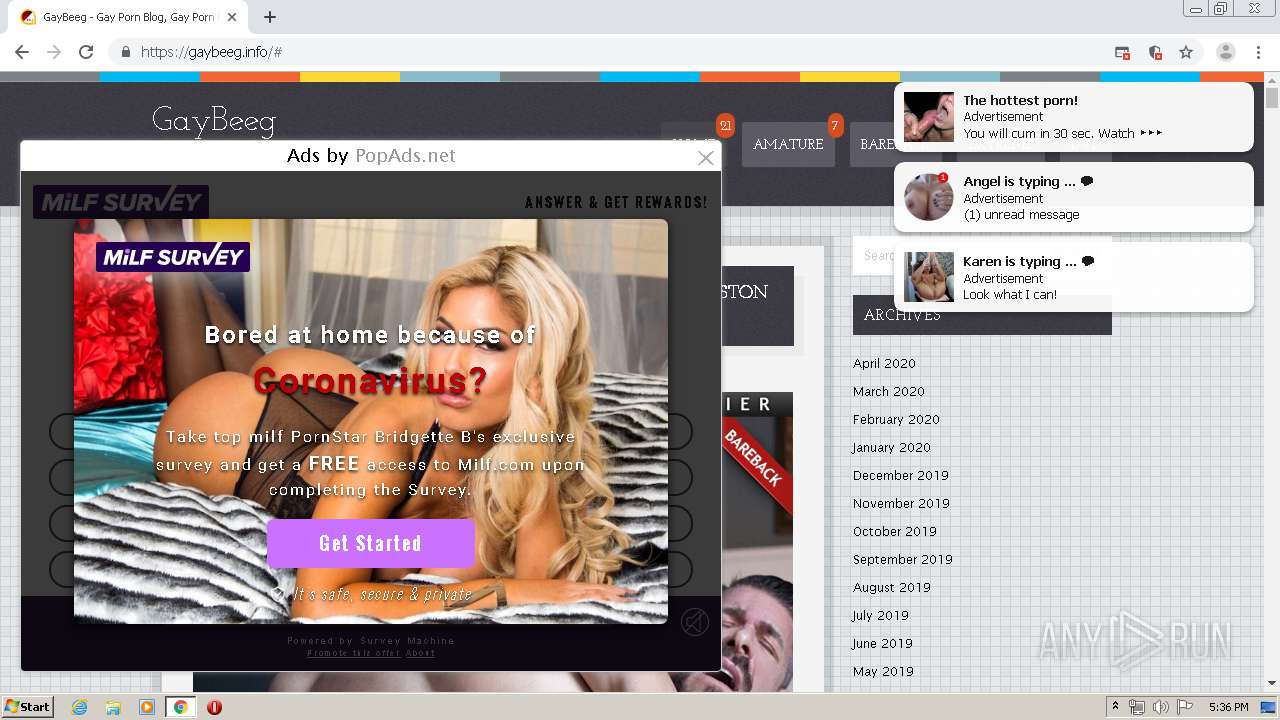
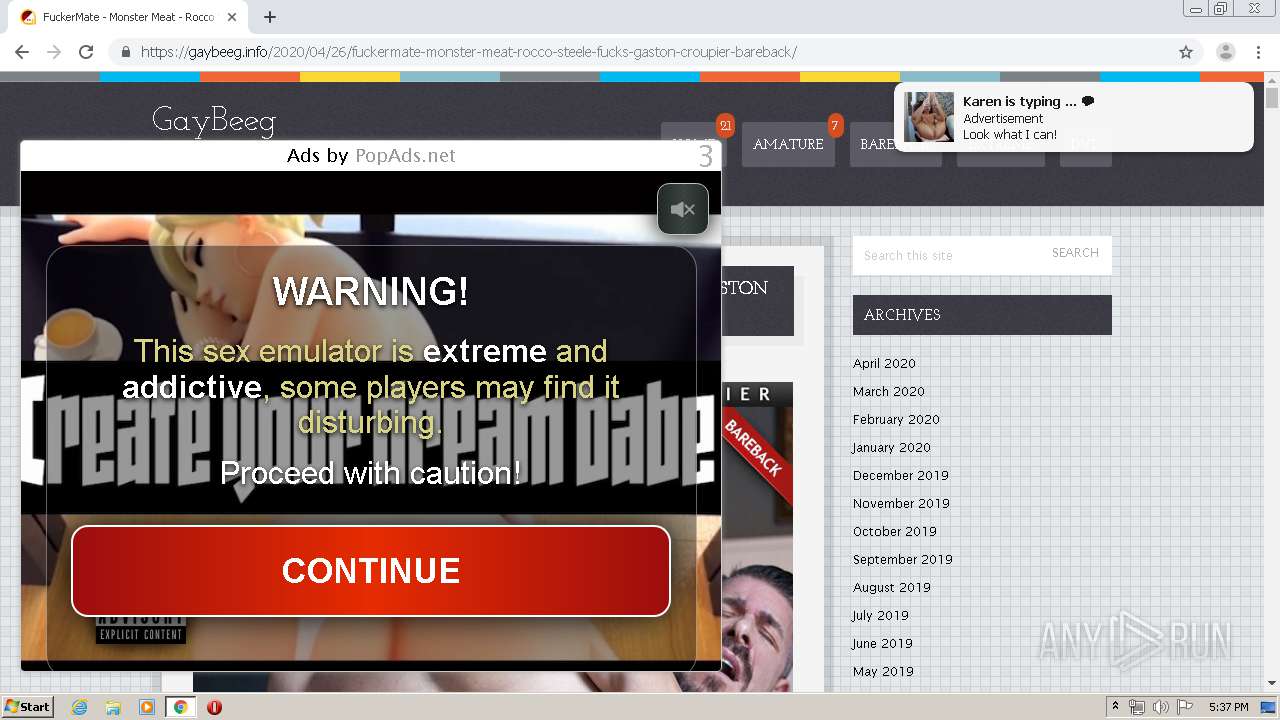
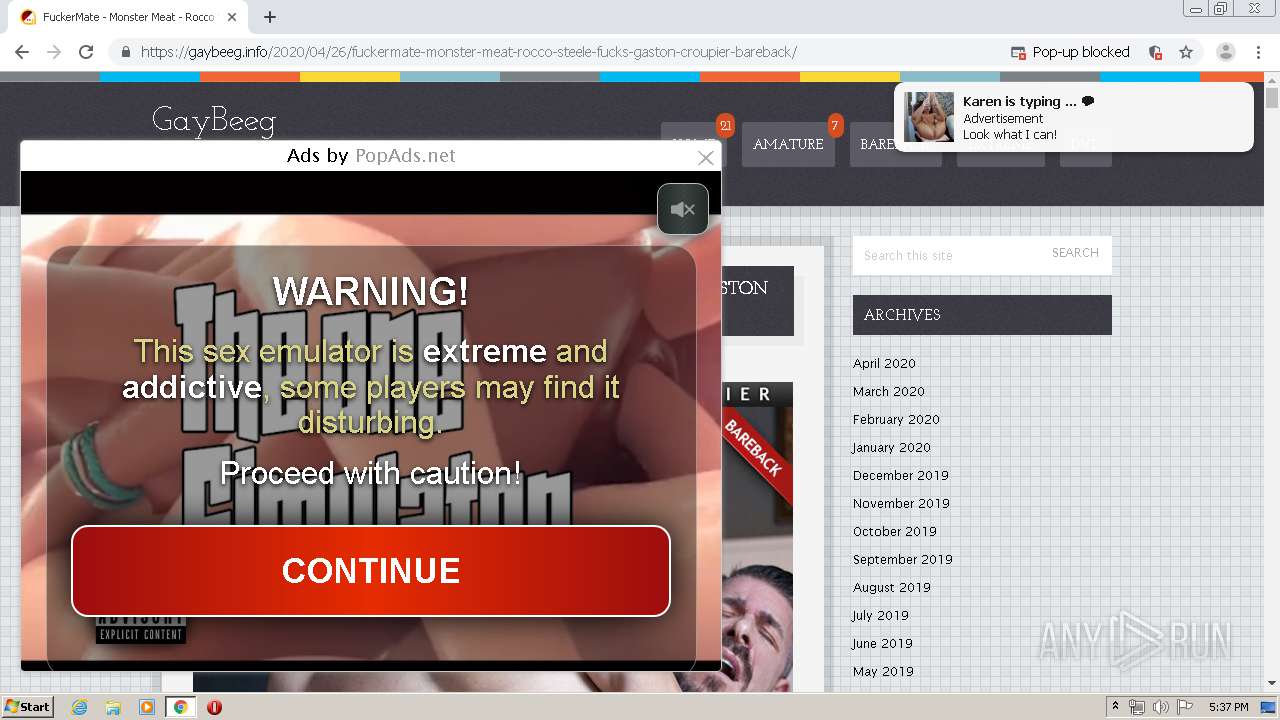
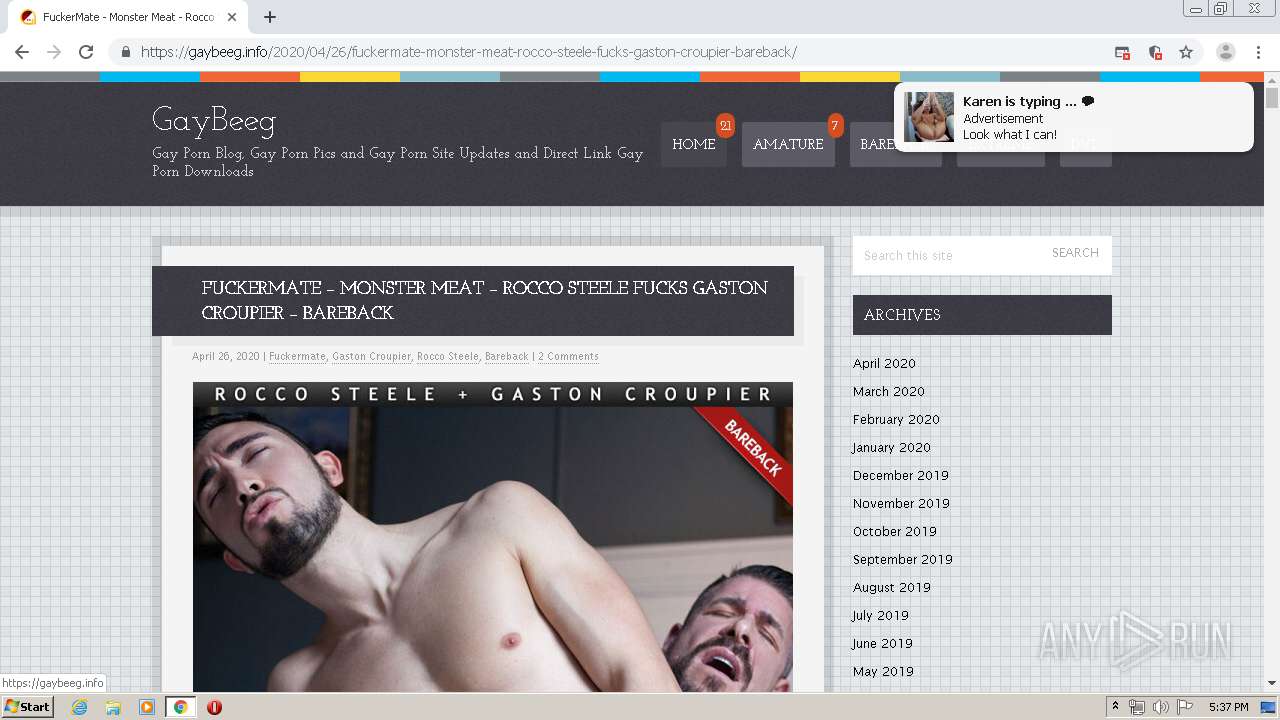
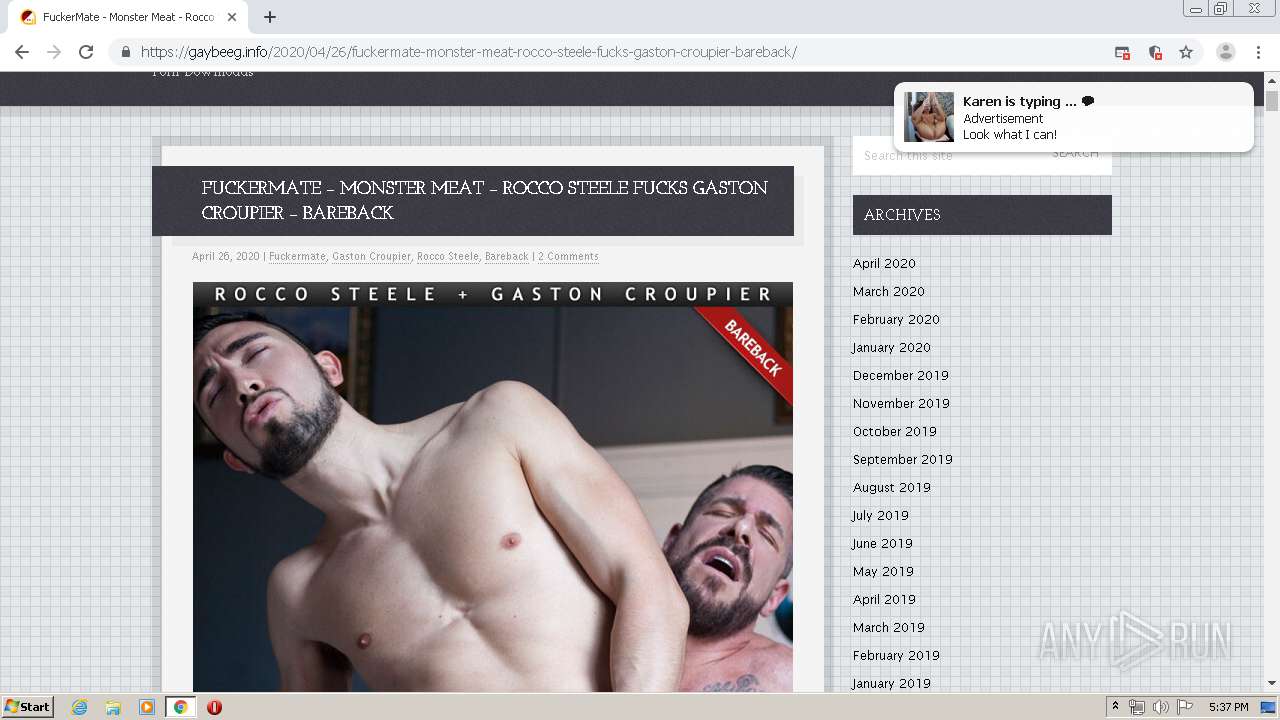
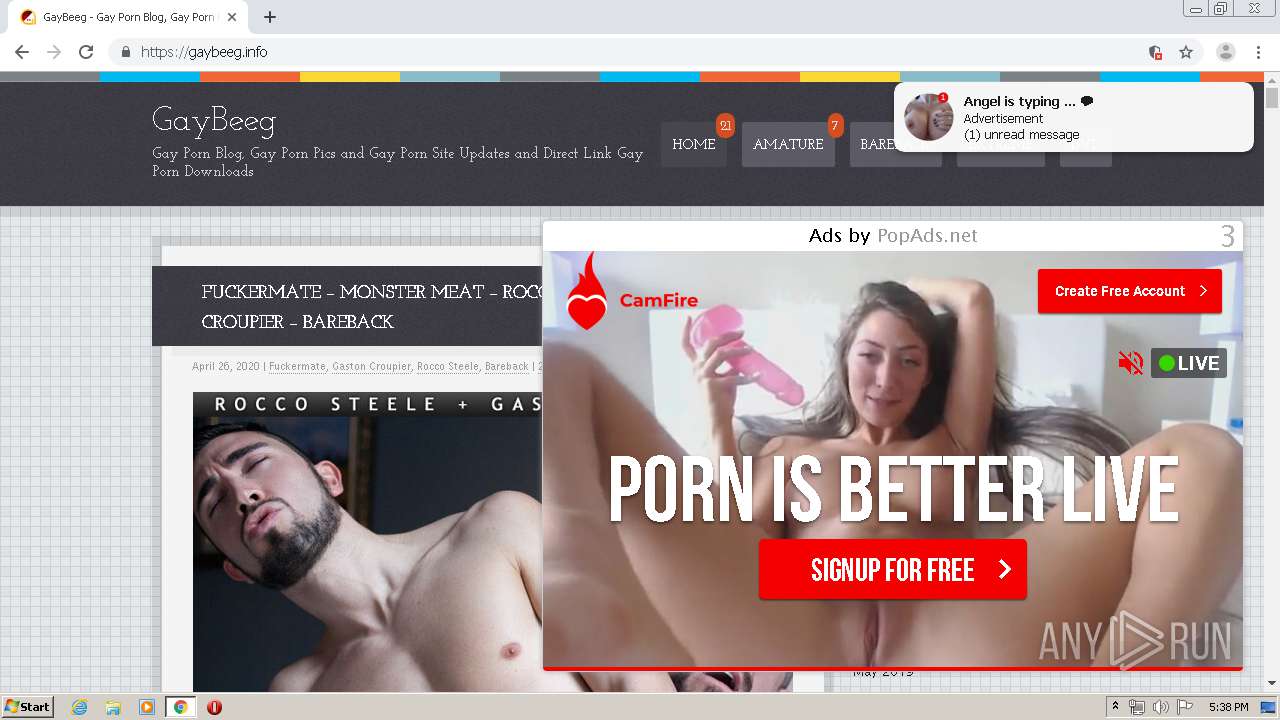
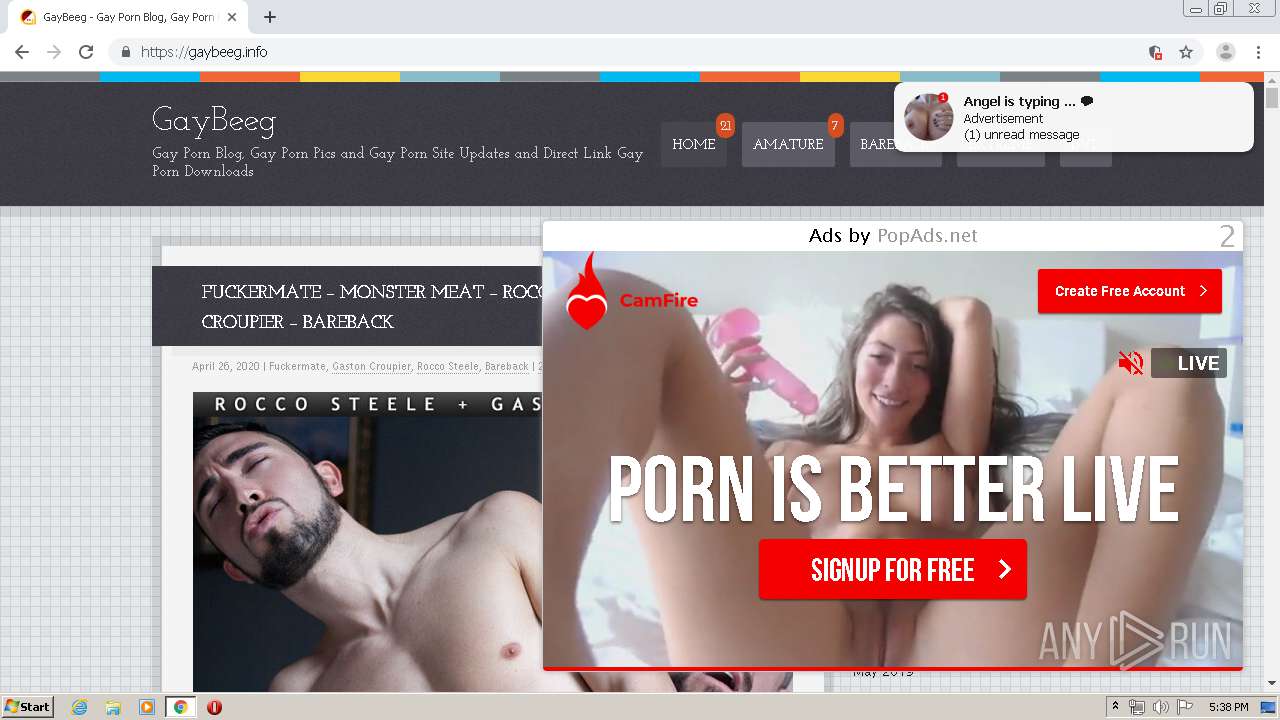
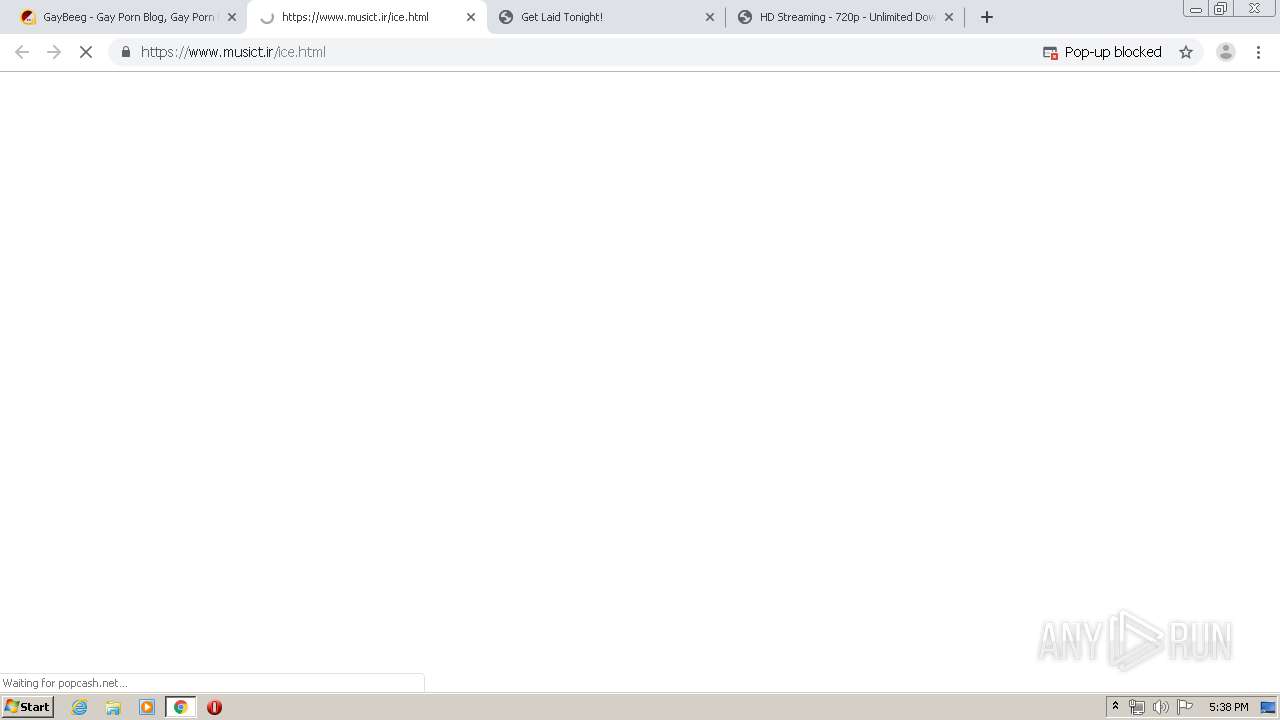
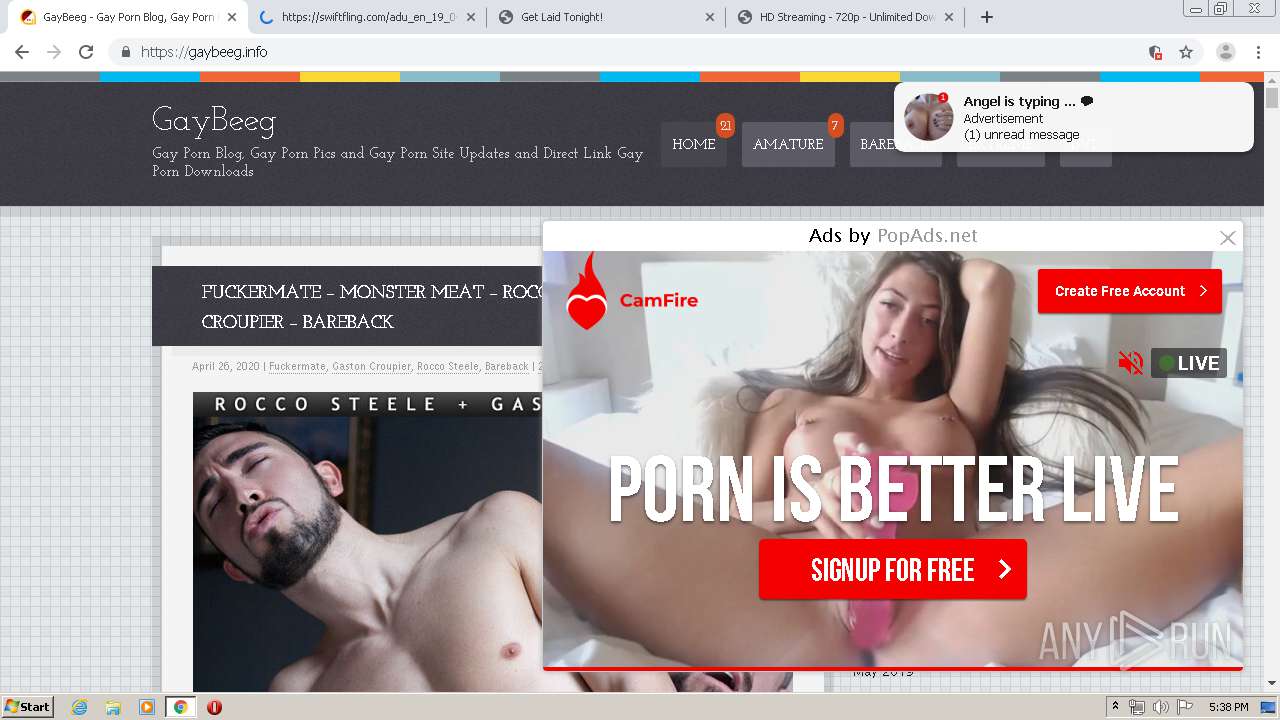
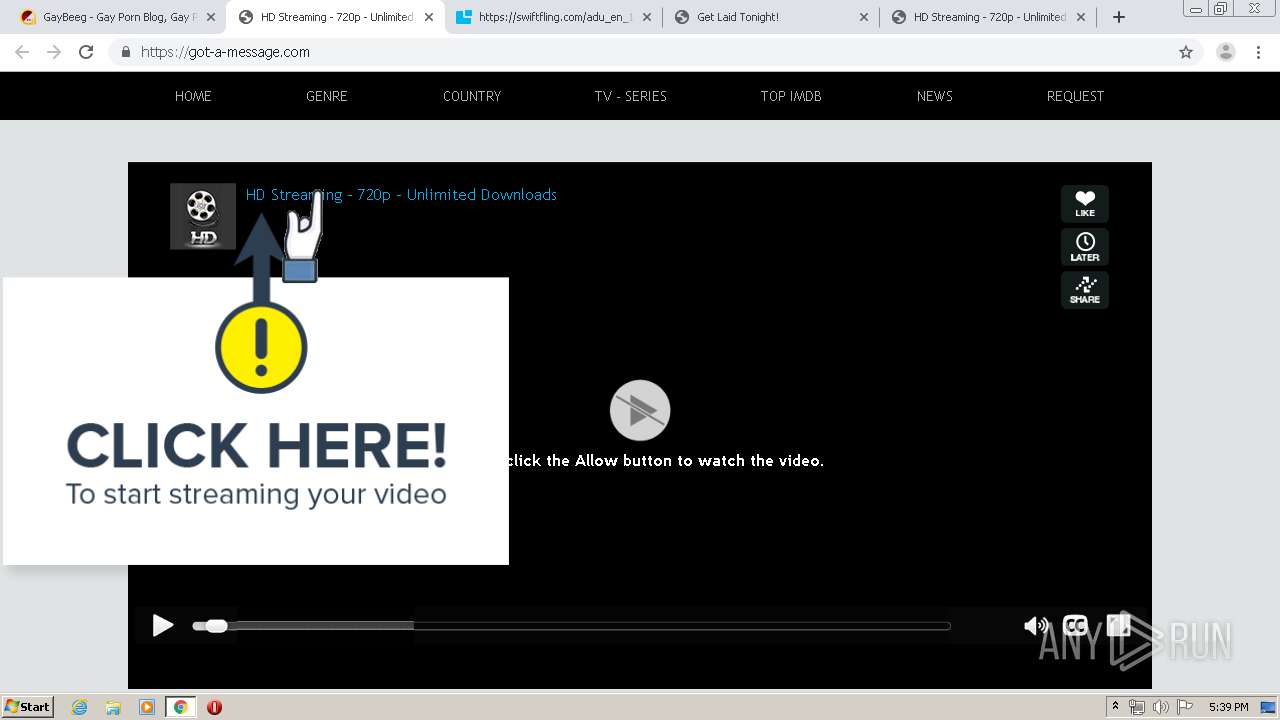
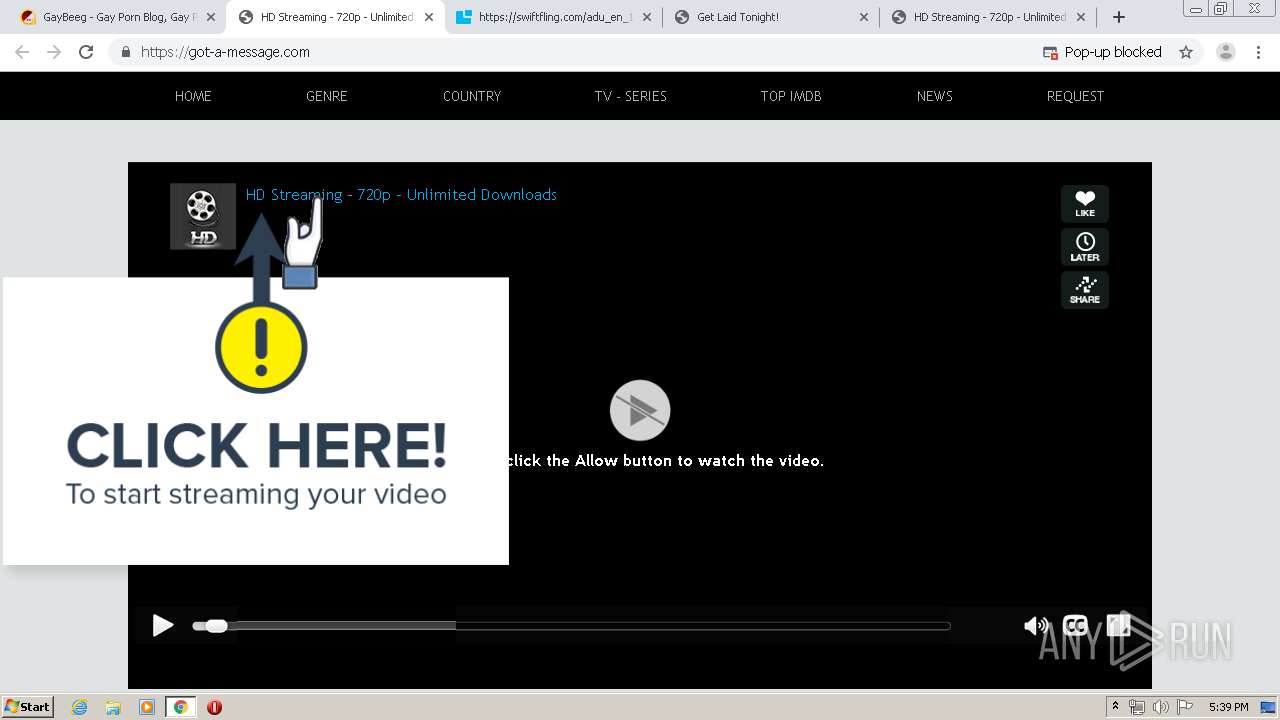
| URL: | https://gaybeeg.info/ |
| Full analysis: | https://app.any.run/tasks/68b54094-5781-45f6-817f-0b611f01bcf6 |
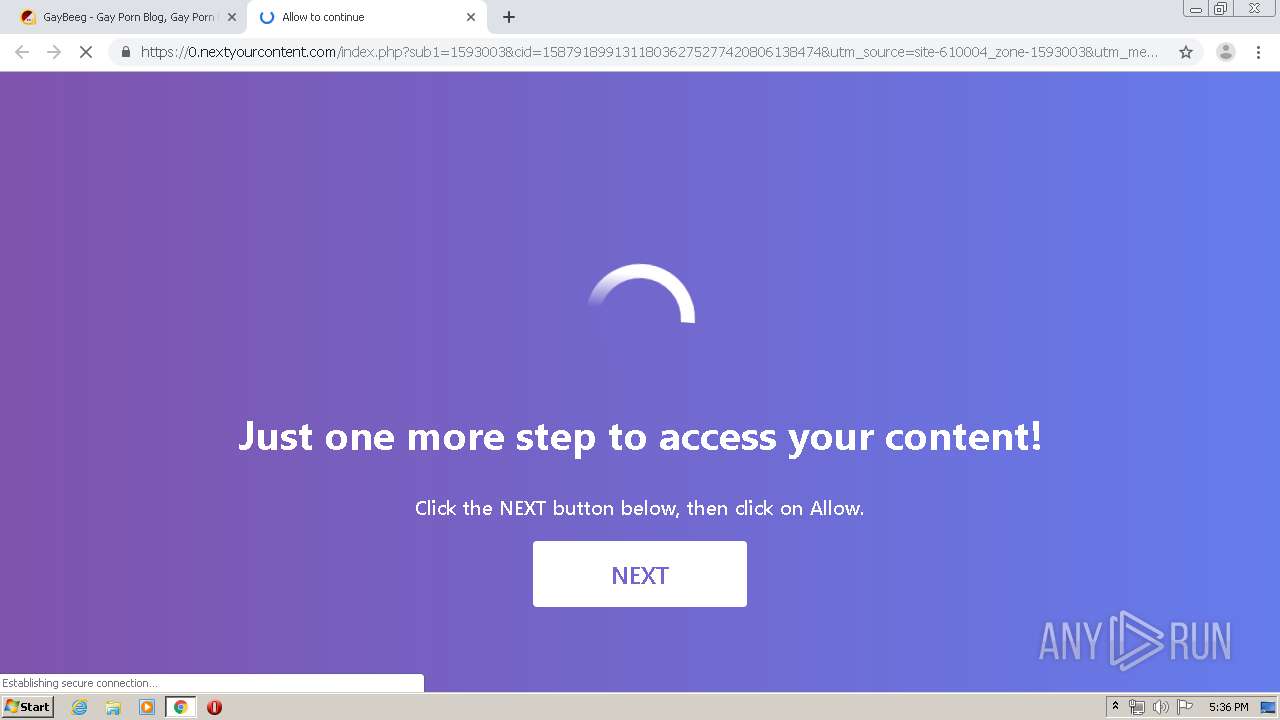
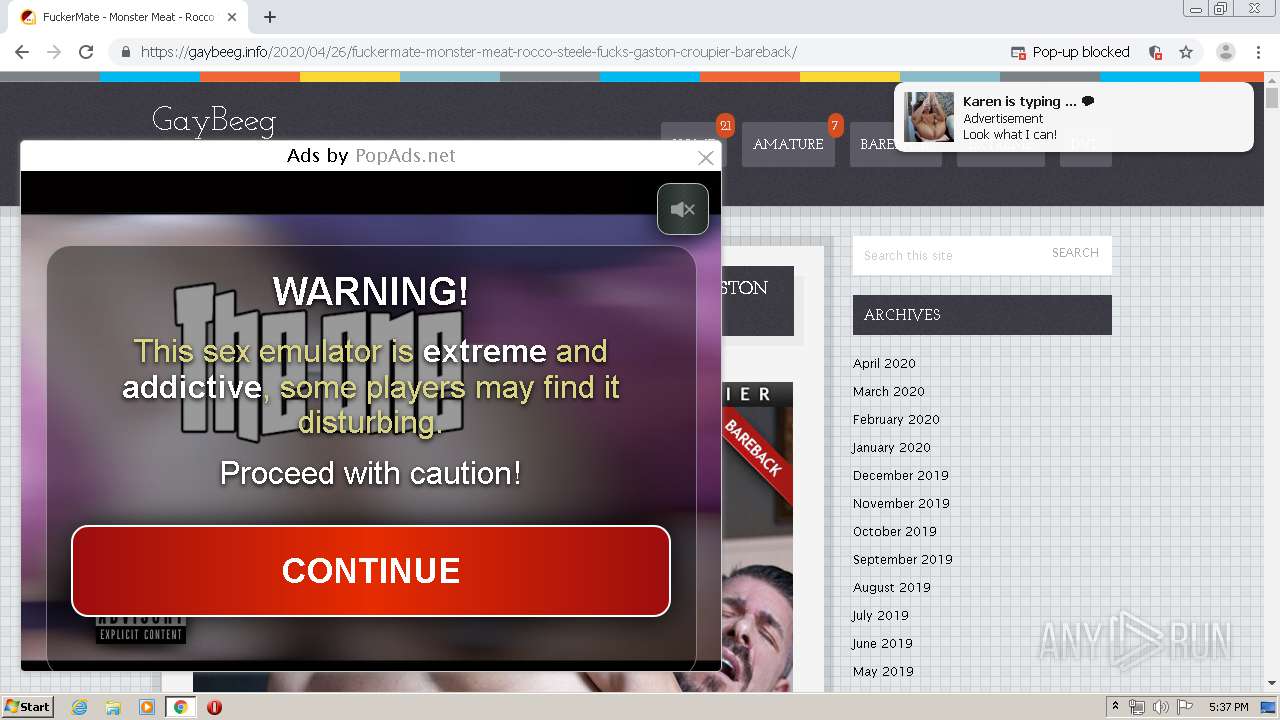
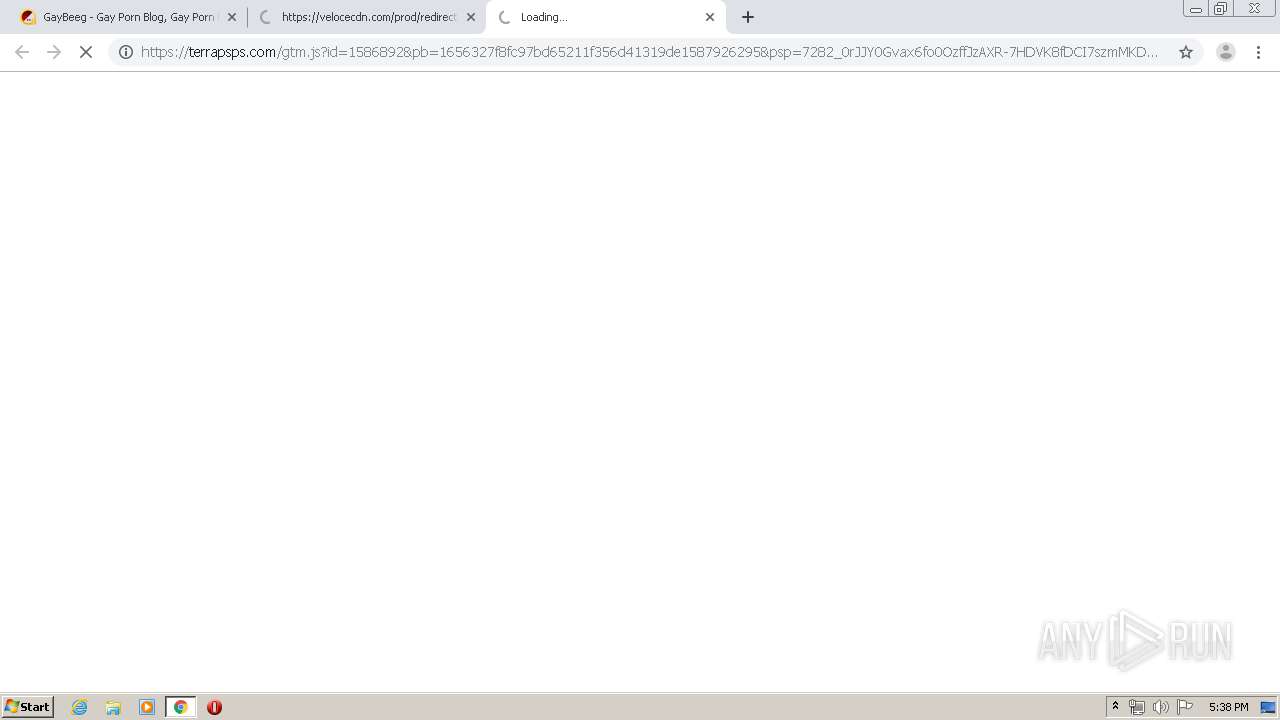
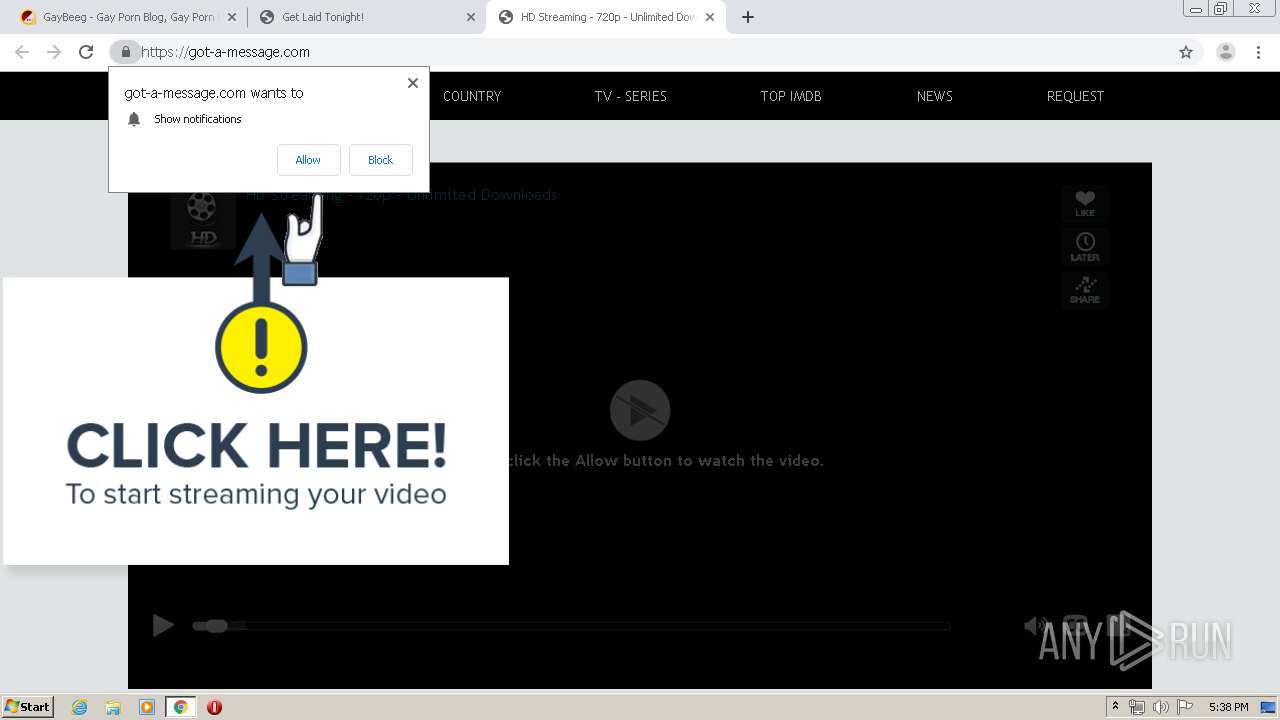
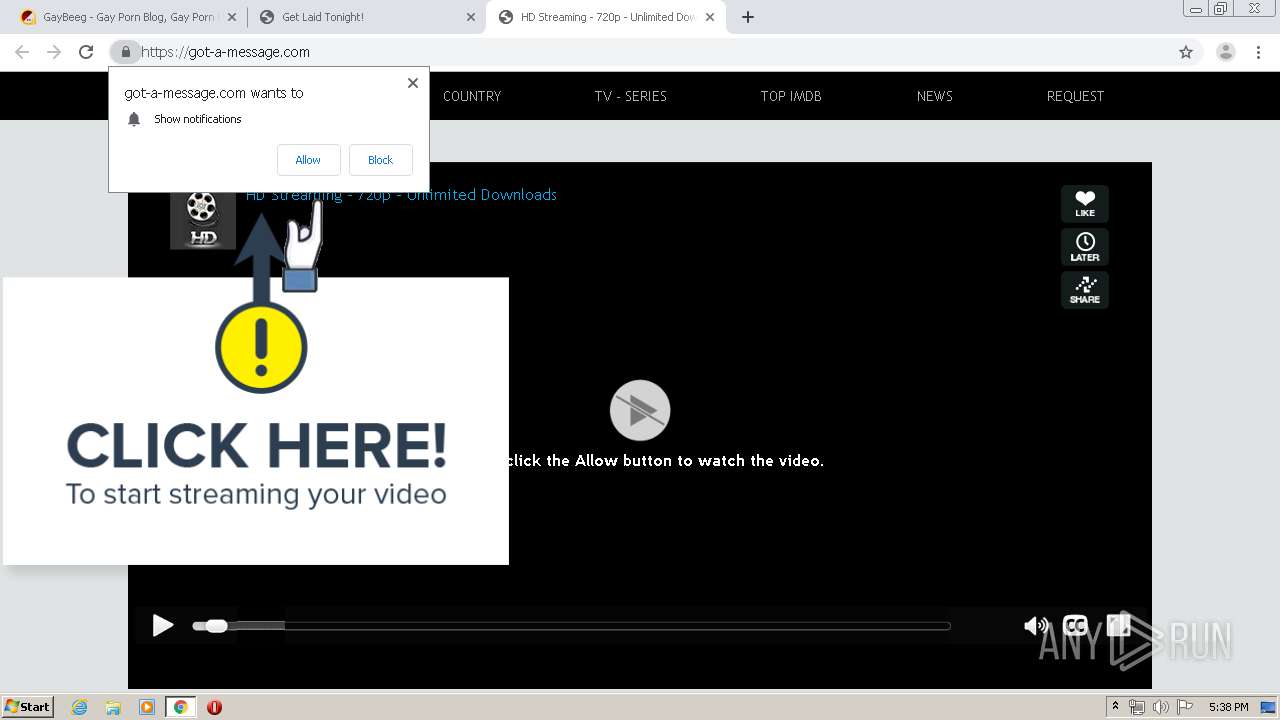
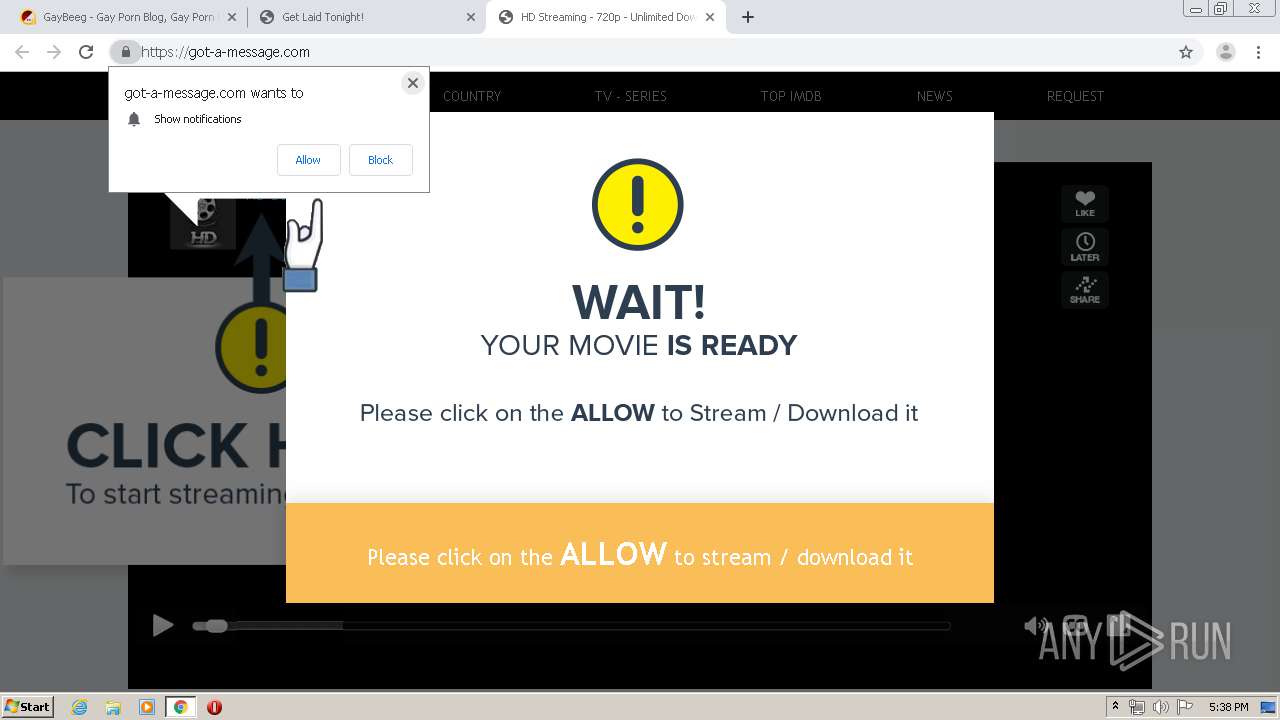
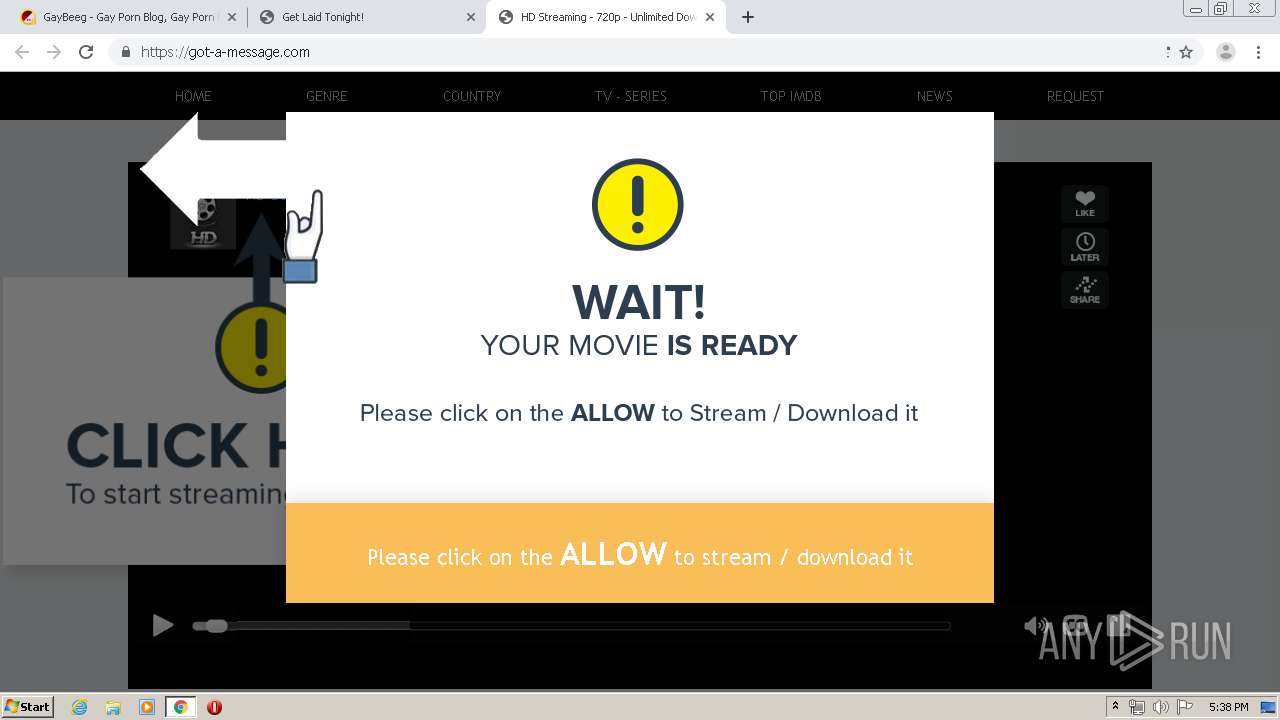
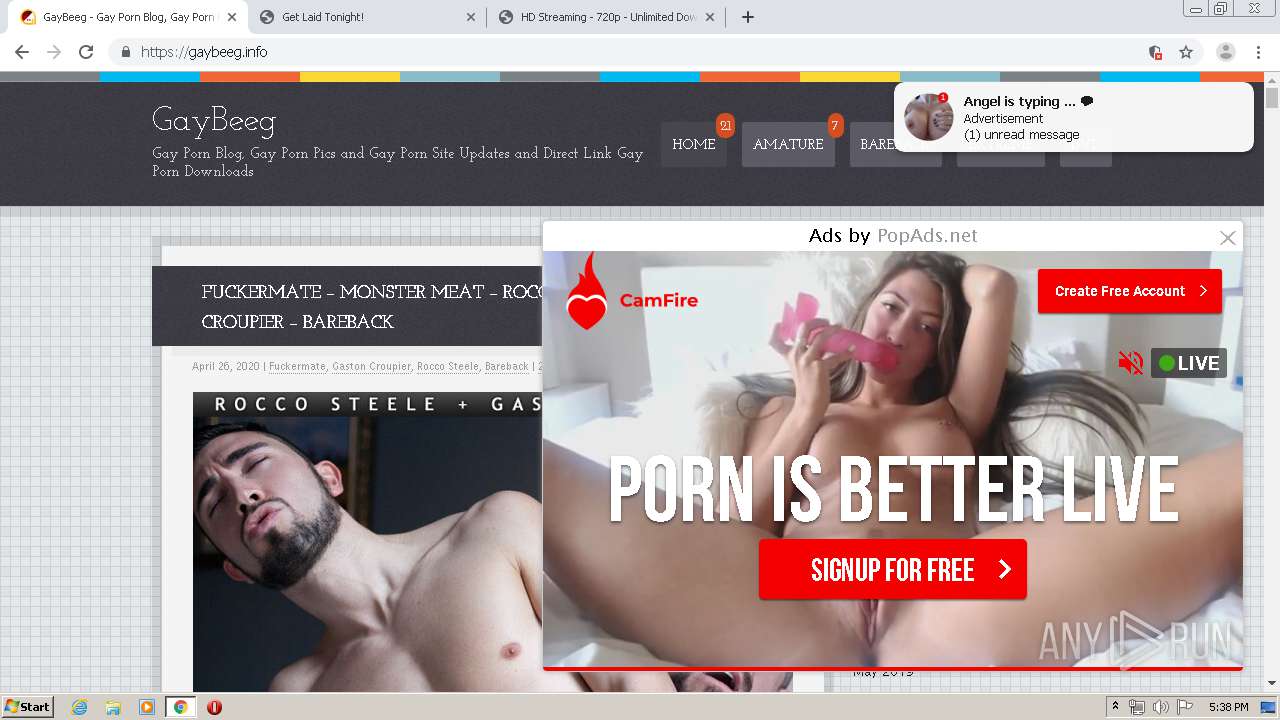
| Verdict: | Malicious activity |
| Analysis date: | April 26, 2020, 16:36:10 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 17ADF5AEB9233490C36844AE5FBD12AC |
| SHA1: | 564F4A3F5421FF61FD390B029DFE8B1A86B70E78 |
| SHA256: | CE878A09E100B2153EFAB2329ECA7D6D8419838D455CB780F4924F67E1343187 |
| SSDEEP: | 3:N8lnnLKn:2VnLK |
MALICIOUS
No malicious indicators.SUSPICIOUS
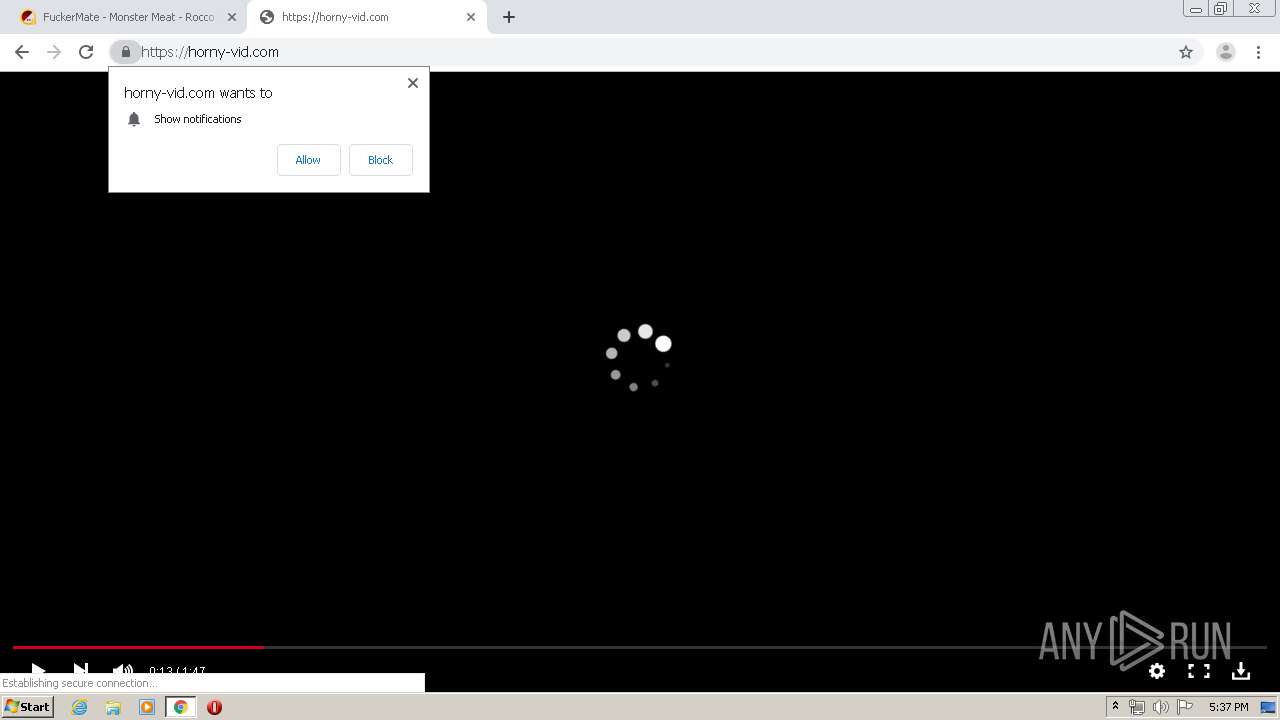
Modifies files in Chrome extension folder
- chrome.exe (PID: 3880)
INFO
Application launched itself
- chrome.exe (PID: 3880)
Reads the hosts file
- chrome.exe (PID: 2184)
- chrome.exe (PID: 3880)
Changes settings of System certificates
- chrome.exe (PID: 2184)
Creates files in the user directory
- chrome.exe (PID: 3880)
Reads settings of System Certificates
- chrome.exe (PID: 2184)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
134
Monitored processes
97
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 280 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1020,18099977384310483853,10735150176943137288,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=9530205786482406752 --renderer-client-id=10 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2968 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 440 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1020,18099977384310483853,10735150176943137288,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=9309848359229921581 --renderer-client-id=54 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=5248 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 564 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1020,18099977384310483853,10735150176943137288,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=8135313723117151312 --renderer-client-id=49 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4220 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 856 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1020,18099977384310483853,10735150176943137288,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=794572406331199261 --renderer-client-id=86 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3820 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 956 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1020,18099977384310483853,10735150176943137288,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=171269603925325442 --renderer-client-id=73 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=6304 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1380 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1020,18099977384310483853,10735150176943137288,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=6350190332894104686 --renderer-client-id=46 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2588 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1440 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1020,18099977384310483853,10735150176943137288,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=17254731982369101382 --renderer-client-id=44 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2500 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1448 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1020,18099977384310483853,10735150176943137288,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=16031424148075283772 --renderer-client-id=81 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2764 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1500 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=75.0.3770.100 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6ebaa9d0,0x6ebaa9e0,0x6ebaa9ec | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1564 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1020,18099977384310483853,10735150176943137288,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=11610950738339441225 --renderer-client-id=78 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1220 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
981
Read events
827
Write events
149
Delete events
5
Modification events
| (PID) Process: | (3600) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 3880-13232392586238375 |
Value: 259 | |||
| (PID) Process: | (3880) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3880) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3880) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3880) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3880) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3880) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3880) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3880) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3120-13213713943555664 |
Value: 0 | |||
| (PID) Process: | (3880) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
197
Text files
433
Unknown types
27
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3880 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5EA5B88A-F28.pma | — | |
MD5:— | SHA256:— | |||
| 3880 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3880 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Last Tabs | — | |
MD5:— | SHA256:— | |||
| 3880 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000028.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3880 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Platform Notifications\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3880 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3880 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\AvailabilityDB\LOG.old~RFa6e16f.TMP | text | |
MD5:— | SHA256:— | |||
| 3880 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old~RFa6e16f.TMP | text | |
MD5:— | SHA256:— | |||
| 3880 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3880 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RFa6e288.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
15
TCP/UDP connections
296
DNS requests
145
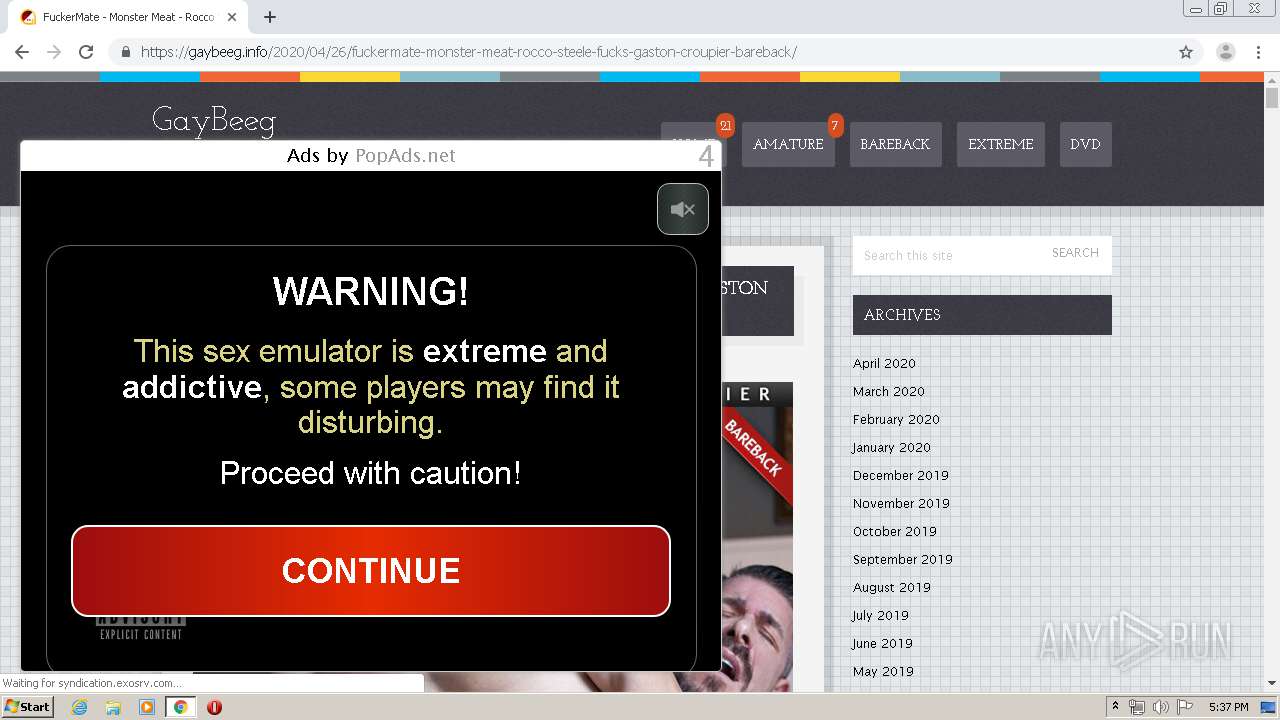
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2184 | chrome.exe | GET | 302 | 172.217.22.46:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvYjY5QUFXTEQwc2RPVXhRY3picjhxblh1dw/7619.603.0.2_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 525 b | whitelisted |
2184 | chrome.exe | GET | 200 | 173.194.139.6:80 | http://r1---sn-aigzrn7k.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvYjY5QUFXTEQwc2RPVXhRY3picjhxblh1dw/7619.603.0.2_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mh=Qx&mip=185.217.117.51&mm=28&mn=sn-aigzrn7k&ms=nvh&mt=1587918912&mv=m&mvi=0&pl=24&shardbypass=yes | US | crx | 816 Kb | whitelisted |
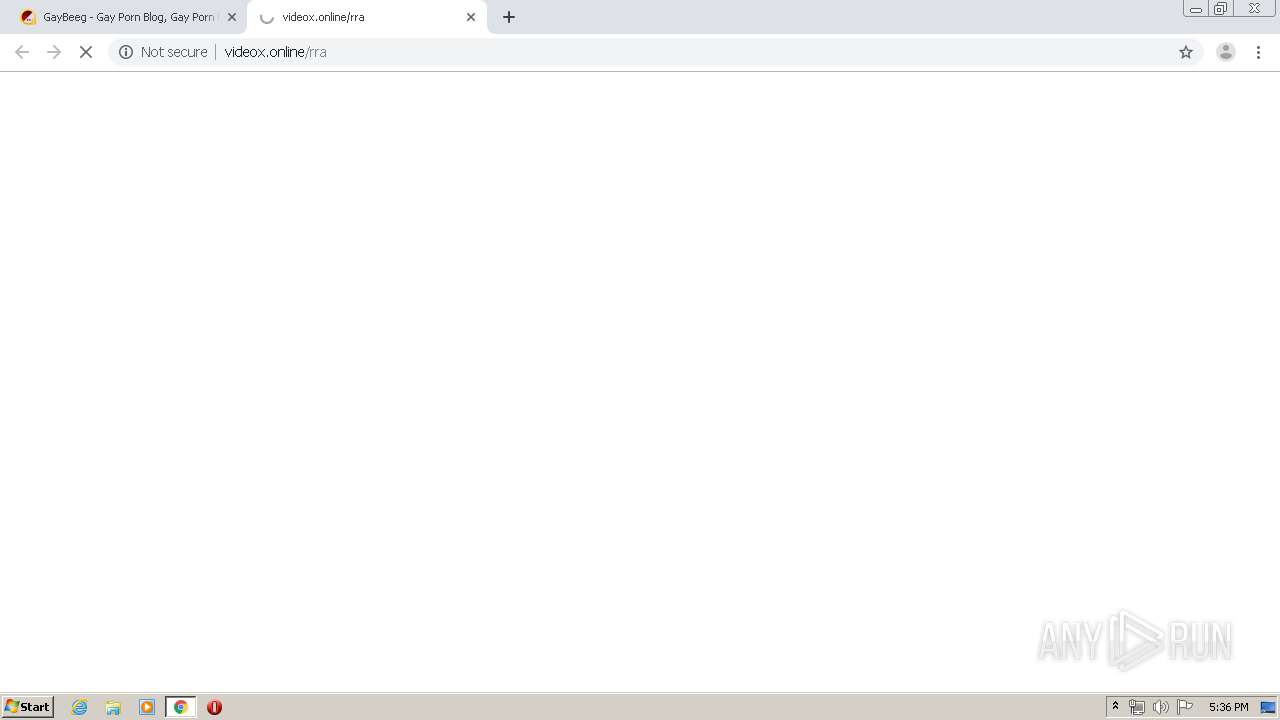
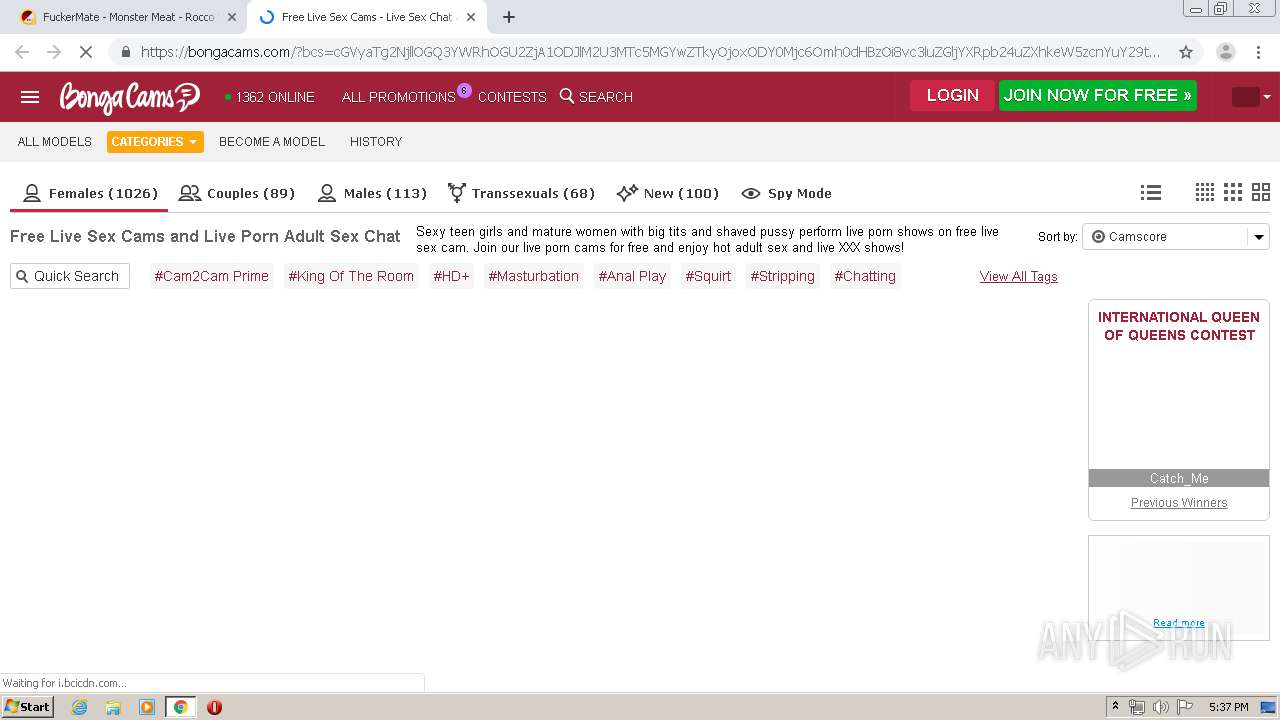
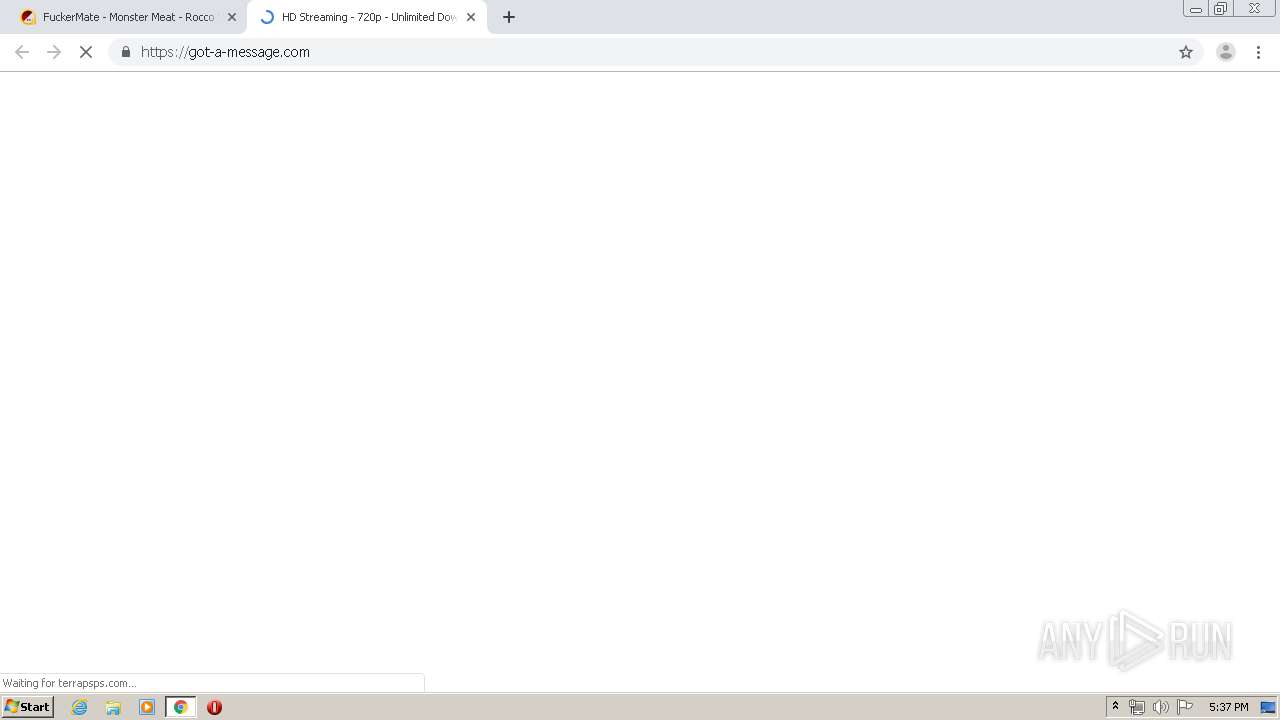
2184 | chrome.exe | GET | 200 | 104.27.159.141:80 | http://videox.online/rra | US | html | 336 b | suspicious |
2184 | chrome.exe | GET | 302 | 172.217.22.46:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 520 b | whitelisted |
2184 | chrome.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRJ9L2KGL92BpjF3kAtaDtxauTmhgQUPdNQpdagre7zSmAKZdMh1Pj41g8CEAy%2BK8lPT%2B%2Fr4u1gFxGeJoE%3D | US | der | 471 b | whitelisted |
2184 | chrome.exe | GET | 200 | 104.27.159.141:80 | http://videox.online/rraright?s=24 | US | html | 342 b | suspicious |
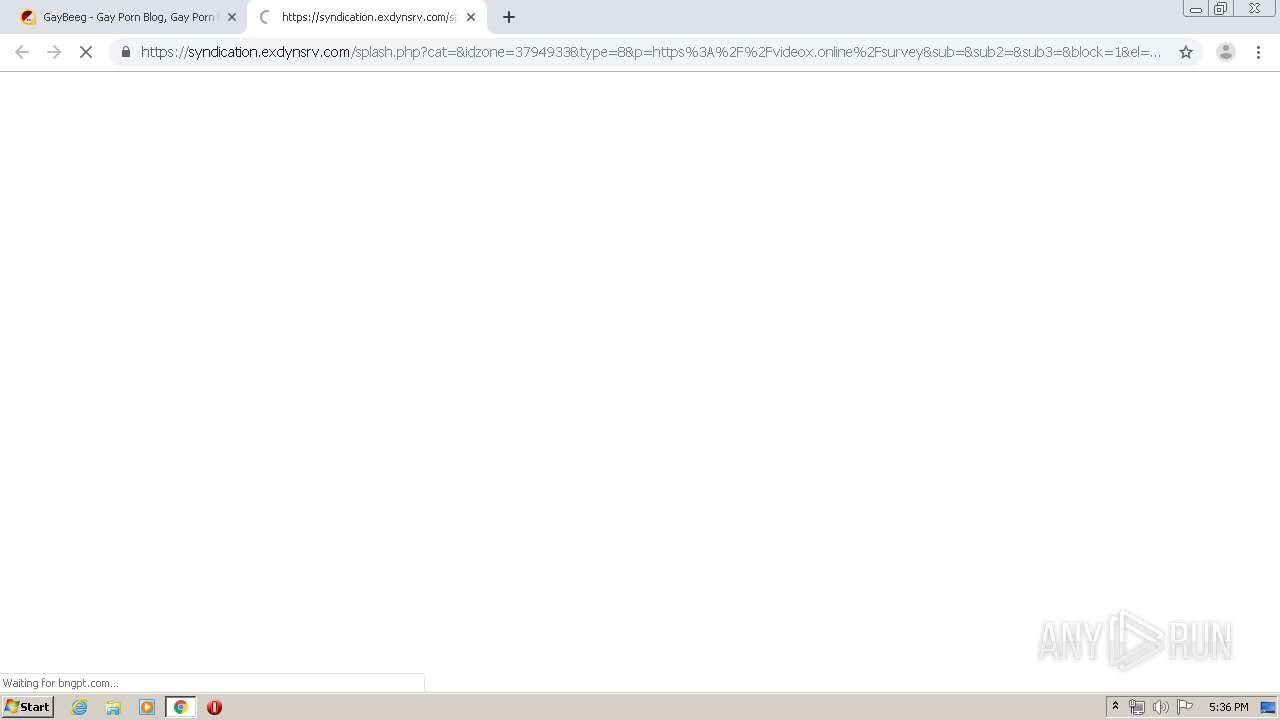
2184 | chrome.exe | GET | 301 | 104.24.125.234:80 | http://trk.autodayhome.com/c/20093/3?cid=15879190233118036275169434233177259&cost=0.000109824&z=1593003&adv=139550&cp=208078620&lg=EN&ban=23011184&udid=&ssp=Adcash | US | html | 608 b | unknown |
2184 | chrome.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfqhLjKLEJQZPin0KCzkdAQpVYowQUsT7DaQP4v0cB1JgmGggC72NkK8MCEAx5qUSwjBGVIJJhX%2BJrHYM%3D | US | der | 471 b | whitelisted |
2184 | chrome.exe | GET | 301 | 104.24.125.234:80 | http://trk.autodayhome.com/c/19927/6?cid=15879190953118036275082403154617472&cost=0.000078933&zone=1593003&website=1593003&SSP=Adcash | US | html | 608 b | unknown |
2184 | chrome.exe | GET | 303 | 52.0.120.49:80 | http://ps.popcash.net/ad/ad?p=258732&w=535730&t=940f8878643c90b3&r=&vw=1280&vh=620 | US | html | 295 b | shared |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2184 | chrome.exe | 104.28.16.21:443 | gaybeeg.info | Cloudflare Inc | US | shared |
2184 | chrome.exe | 172.217.23.106:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
2184 | chrome.exe | 172.217.16.173:443 | accounts.google.com | Google Inc. | US | whitelisted |
2184 | chrome.exe | 209.197.3.15:443 | netdna.bootstrapcdn.com | Highwinds Network Group, Inc. | US | whitelisted |
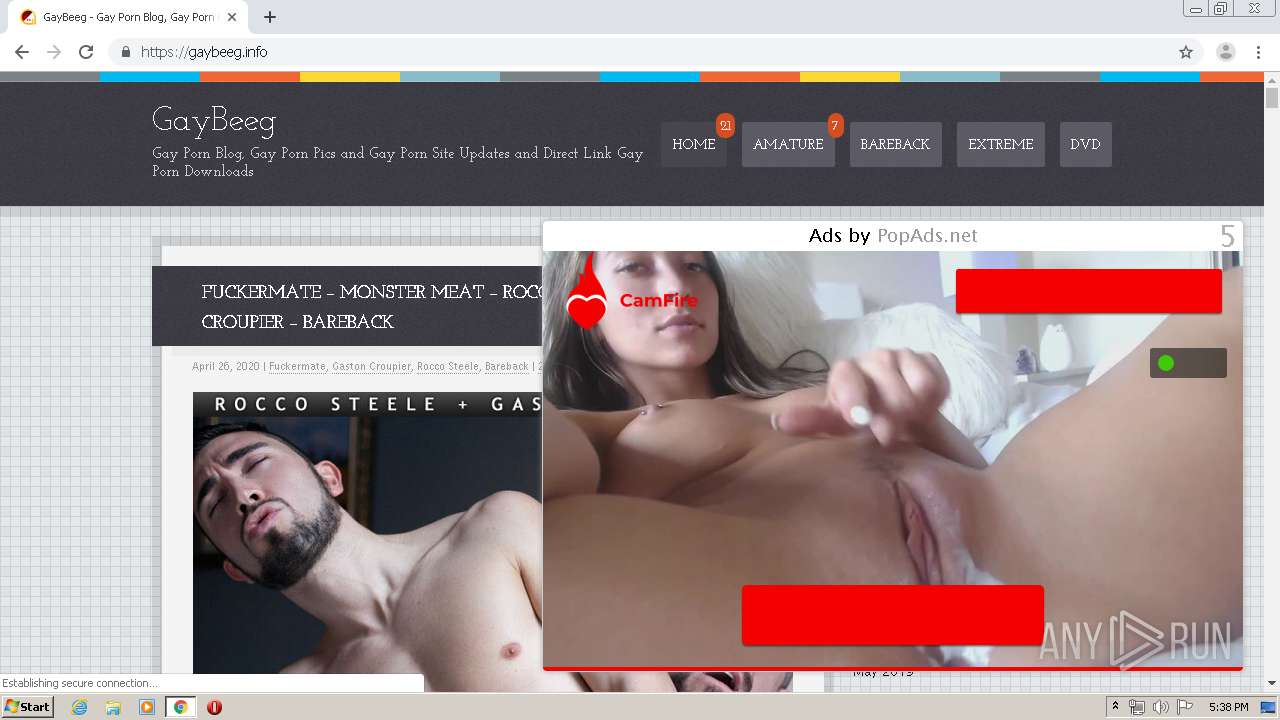
2184 | chrome.exe | 109.206.164.148:443 | crocopop.com | Serverel Inc. | NL | suspicious |
2184 | chrome.exe | 172.217.16.131:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
2184 | chrome.exe | 109.206.162.83:443 | terrapsps.com | Serverel Inc. | NL | suspicious |
2184 | chrome.exe | 192.0.76.3:443 | stats.wp.com | Automattic, Inc | US | suspicious |
2184 | chrome.exe | 216.58.208.40:443 | www.googletagmanager.com | Google Inc. | US | whitelisted |
2184 | chrome.exe | 35.190.65.213:443 | superfastcdn.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
gaybeeg.info |
| whitelisted |
accounts.google.com |
| shared |
fonts.googleapis.com |
| whitelisted |
netdna.bootstrapcdn.com |
| whitelisted |
terrapsps.com |
| whitelisted |
crocopop.com |
| suspicious |
fonts.gstatic.com |
| whitelisted |
s.w.org |
| whitelisted |
stats.wp.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2184 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Response) |
2184 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Response) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Response) |