| File name: | Panda-21.0.3-installer-.exe |
| Full analysis: | https://app.any.run/tasks/b827715c-4534-4835-9b0c-cda9929712ae |
| Verdict: | Malicious activity |
| Analysis date: | May 22, 2023, 15:03:52 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 41605E09AD14313F2E9965912848D844 |
| SHA1: | 9C4EEC2DC478D1542067B1C4950D7341F27E19CB |
| SHA256: | CE858F2A85FDA007639514495F331DEE8A28A5907264A5BEA977BB8D1BC87BD0 |
| SSDEEP: | 12288:SNpszYhvXWSVJdMaeX7HJJA9fm5nPRDyzfdrqFJxDSSYUNOF2Jg0WRF0K02zUBsu:OhvJVJdMnHw9fm5nPJyzS+WIR2KJzi3 |
MALICIOUS
No malicious indicators.SUSPICIOUS
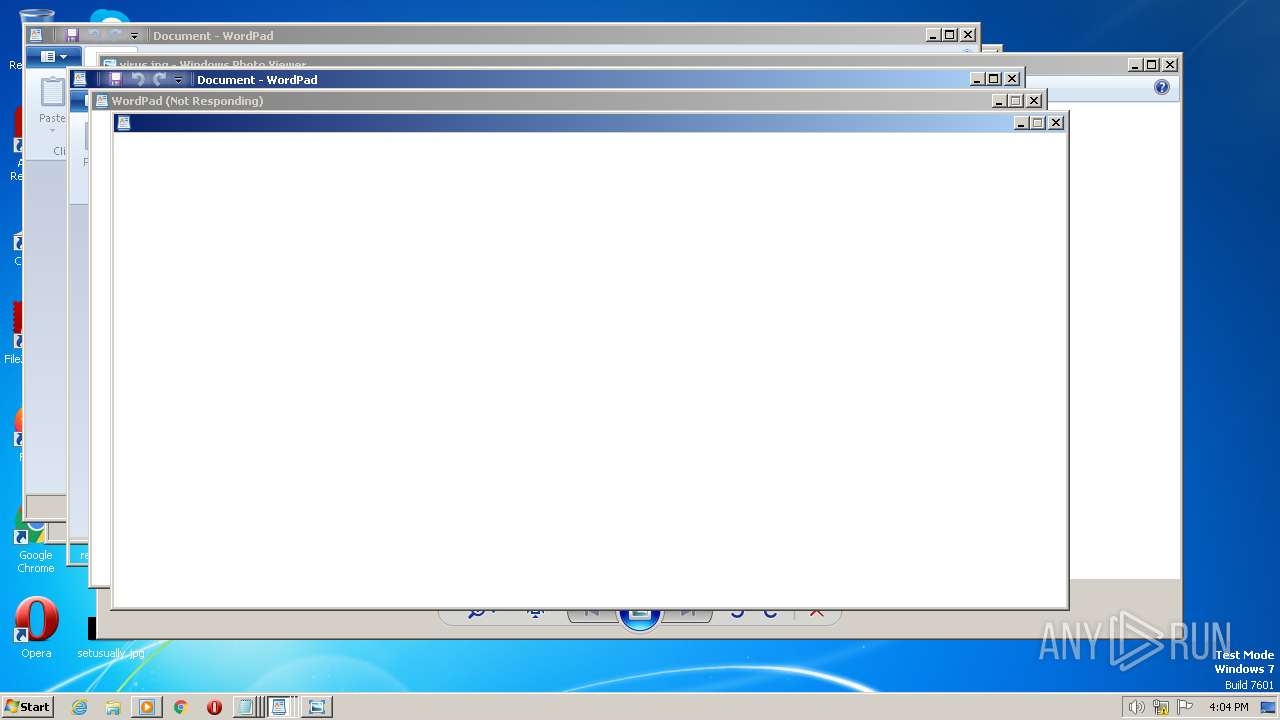
Executing commands from a ".bat" file
- Panda-21.0.3-installer-.exe (PID: 3988)
Reads the Internet Settings
- write.exe (PID: 988)
- Panda-21.0.3-installer-.exe (PID: 3988)
- write.exe (PID: 2420)
- write.exe (PID: 3172)
- write.exe (PID: 2300)
- write.exe (PID: 1896)
- write.exe (PID: 3788)
- write.exe (PID: 1280)
- write.exe (PID: 1464)
- write.exe (PID: 3124)
- write.exe (PID: 2288)
Starts CMD.EXE for commands execution
- Panda-21.0.3-installer-.exe (PID: 3988)
INFO
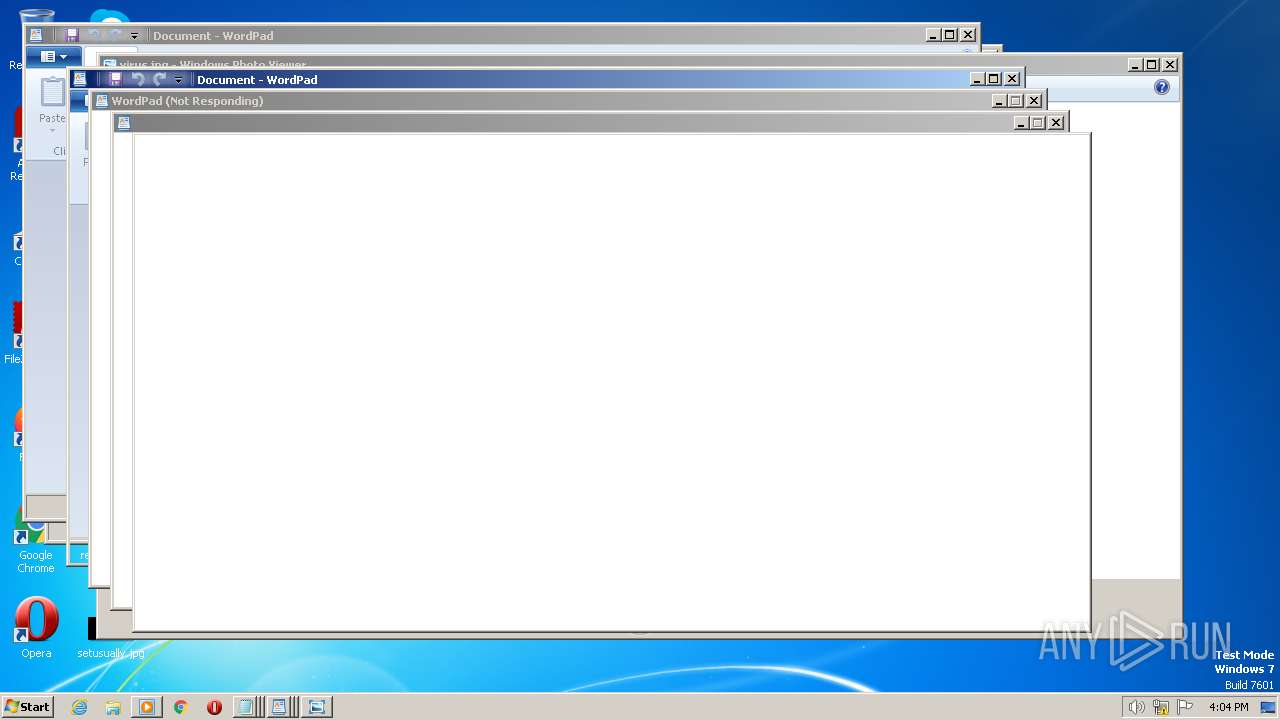
Checks supported languages
- Panda-21.0.3-installer-.exe (PID: 3988)
- wordpad.exe (PID: 2584)
- wordpad.exe (PID: 3324)
- wordpad.exe (PID: 4088)
- wordpad.exe (PID: 2220)
- wordpad.exe (PID: 3200)
- wordpad.exe (PID: 1172)
- wordpad.exe (PID: 1816)
- wordpad.exe (PID: 748)
- wordpad.exe (PID: 2596)
- wordpad.exe (PID: 3260)
The process checks LSA protection
- Panda-21.0.3-installer-.exe (PID: 3988)
- write.exe (PID: 988)
- write.exe (PID: 2420)
- write.exe (PID: 3172)
- write.exe (PID: 3788)
- write.exe (PID: 1280)
- write.exe (PID: 2300)
- write.exe (PID: 1896)
- write.exe (PID: 2288)
- dllhost.exe (PID: 2816)
- write.exe (PID: 1464)
- write.exe (PID: 3124)
- wordpad.exe (PID: 3324)
- wordpad.exe (PID: 2584)
Reads the computer name
- Panda-21.0.3-installer-.exe (PID: 3988)
- wordpad.exe (PID: 2584)
- wordpad.exe (PID: 3324)
- wordpad.exe (PID: 4088)
- wordpad.exe (PID: 2220)
- wordpad.exe (PID: 3200)
- wordpad.exe (PID: 1172)
- wordpad.exe (PID: 1816)
- wordpad.exe (PID: 748)
- wordpad.exe (PID: 2596)
- wordpad.exe (PID: 3260)
Create files in a temporary directory
- Panda-21.0.3-installer-.exe (PID: 3988)
Reads the machine GUID from the registry
- Panda-21.0.3-installer-.exe (PID: 3988)
- wordpad.exe (PID: 3324)
- wordpad.exe (PID: 2584)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (52.9) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.5) |
| .exe | | | DOS Executable Generic (23.5) |
EXIF
EXE
| Subsystem: | Windows GUI |
|---|---|
| SubsystemVersion: | 5.1 |
| ImageVersion: | - |
| OSVersion: | 5.1 |
| EntryPoint: | 0x1ed60 |
| UninitializedDataSize: | - |
| InitializedDataSize: | 162816 |
| CodeSize: | 201728 |
| LinkerVersion: | 14 |
| PEType: | PE32 |
| ImageFileCharacteristics: | Executable, 32-bit |
| TimeStamp: | 2021:04:07 14:39:21+00:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 07-Apr-2021 14:39:21 |
| Detected languages: |
|
| Debug artifacts: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000118 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 07-Apr-2021 14:39:21 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0003122A | 0x00031400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.70389 |
.rdata | 0x00033000 | 0x0000A612 | 0x0000A800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.22369 |
.data | 0x0003E000 | 0x00023728 | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.70882 |
.didat | 0x00062000 | 0x00000188 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.28777 |
.rsrc | 0x00063000 | 0x00019D40 | 0x00019E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.33337 |
.reloc | 0x0007D000 | 0x00002274 | 0x00002400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.55896 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.25329 | 1875 | Latin 1 / Western European | English - United States | RT_MANIFEST |
7 | 3.1586 | 482 | Latin 1 / Western European | English - United States | RT_STRING |
8 | 3.11685 | 460 | Latin 1 / Western European | English - United States | RT_STRING |
9 | 3.11236 | 440 | Latin 1 / Western European | English - United States | RT_STRING |
10 | 2.99727 | 326 | Latin 1 / Western European | English - United States | RT_STRING |
11 | 3.2036 | 1094 | Latin 1 / Western European | English - United States | RT_STRING |
12 | 3.12889 | 358 | Latin 1 / Western European | English - United States | RT_STRING |
13 | 3.01704 | 338 | Latin 1 / Western European | English - United States | RT_STRING |
14 | 2.94627 | 266 | Latin 1 / Western European | English - United States | RT_STRING |
15 | 2.83619 | 188 | Latin 1 / Western European | English - United States | RT_STRING |
Imports
KERNEL32.dll |
USER32.dll (delay-loaded) |
gdiplus.dll |
Total processes
69
Monitored processes
33
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 528 | C:\Windows\system32\notepad.exe | C:\Windows\System32\notepad.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 748 | "C:\Program Files\Windows NT\Accessories\wordpad.exe" | C:\Program Files\Windows NT\Accessories\wordpad.exe | — | write.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Wordpad Application Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 796 | C:\Windows\system32\notepad.exe | C:\Windows\System32\notepad.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 988 | C:\Windows\system32\write.exe | C:\Windows\System32\write.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Write Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1004 | C:\Windows\system32\notepad.exe | C:\Windows\System32\notepad.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1172 | "C:\Program Files\Windows NT\Accessories\wordpad.exe" | C:\Program Files\Windows NT\Accessories\wordpad.exe | — | write.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Wordpad Application Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1280 | C:\Windows\system32\write.exe | C:\Windows\System32\write.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Write Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1464 | C:\Windows\system32\write.exe | C:\Windows\System32\write.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Write Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1816 | "C:\Program Files\Windows NT\Accessories\wordpad.exe" | C:\Program Files\Windows NT\Accessories\wordpad.exe | — | write.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Wordpad Application Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1836 | C:\Windows\system32\cmd.exe /c ""C:\Users\admin\AppData\Local\Temp\RarSFX0\my.bat" " | C:\Windows\System32\cmd.exe | — | Panda-21.0.3-installer-.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
2 786
Read events
2 694
Write events
92
Delete events
0
Modification events
| (PID) Process: | (3988) Panda-21.0.3-installer-.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3988) Panda-21.0.3-installer-.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3988) Panda-21.0.3-installer-.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3988) Panda-21.0.3-installer-.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (988) write.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (988) write.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (988) write.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (988) write.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (2420) write.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2420) write.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
Executable files
0
Suspicious files
0
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3988 | Panda-21.0.3-installer-.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\my.bat | text | |
MD5:975046E6317C3DC30372DA6AC30C658F | SHA256:A41B4F639199087678D71A16805FE4804421FBFB9F854CD1DF6452079BA115B2 | |||
| 3988 | Panda-21.0.3-installer-.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\virus.jpg | image | |
MD5:2313762B44124C31029DF266E32B8120 | SHA256:0D573B7FC4AC6682DA9E4A8F8DB51372C2BC06F1FB1AC2ACE05157DDF4FEEC5D | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
4
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1076 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
— | — | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
3404 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |