| File name: | main.exe |
| Full analysis: | https://app.any.run/tasks/2c729e42-a575-47cb-bf51-303b503a9db5 |
| Verdict: | Malicious activity |
| Analysis date: | July 17, 2022, 11:46:30 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (console) Intel 80386, for MS Windows |
| MD5: | 4C441FC5C80B250C74C70D80045D7AA7 |
| SHA1: | 5855DB2DC51286DCEC9F01ABEDE95A408030AE28 |
| SHA256: | CE83E9A597479CA41AB170F7706AB8B57349B92DF2B0D148D946B0190AFB5845 |
| SSDEEP: | 393216:so2OMN5MkDJClW7Kr11UyK+naW0lPMcJ8qIdxl:soFMNOkYW7+1KyK+naXMK8XD |
MALICIOUS
Loads dropped or rewritten executable
- main.exe (PID: 3788)
- main.exe (PID: 3512)
Drops executable file immediately after starts
- main.exe (PID: 1912)
- main.exe (PID: 580)
SUSPICIOUS
Reads the computer name
- main.exe (PID: 1912)
- main.exe (PID: 3788)
- main.exe (PID: 580)
- main.exe (PID: 3512)
Checks supported languages
- main.exe (PID: 1912)
- main.exe (PID: 3788)
- cmd.exe (PID: 3080)
- main.exe (PID: 580)
- main.exe (PID: 3512)
Application launched itself
- main.exe (PID: 1912)
- main.exe (PID: 580)
Loads Python modules
- main.exe (PID: 3788)
- main.exe (PID: 3512)
Executed via COM
- DllHost.exe (PID: 600)
Executable content was dropped or overwritten
- main.exe (PID: 1912)
- main.exe (PID: 580)
Checks for external IP
- main.exe (PID: 3788)
- main.exe (PID: 3512)
Drops a file with a compile date too recent
- main.exe (PID: 1912)
- main.exe (PID: 580)
INFO
Dropped object may contain Bitcoin addresses
- main.exe (PID: 1912)
- main.exe (PID: 580)
Checks supported languages
- DllHost.exe (PID: 600)
Reads the computer name
- DllHost.exe (PID: 600)
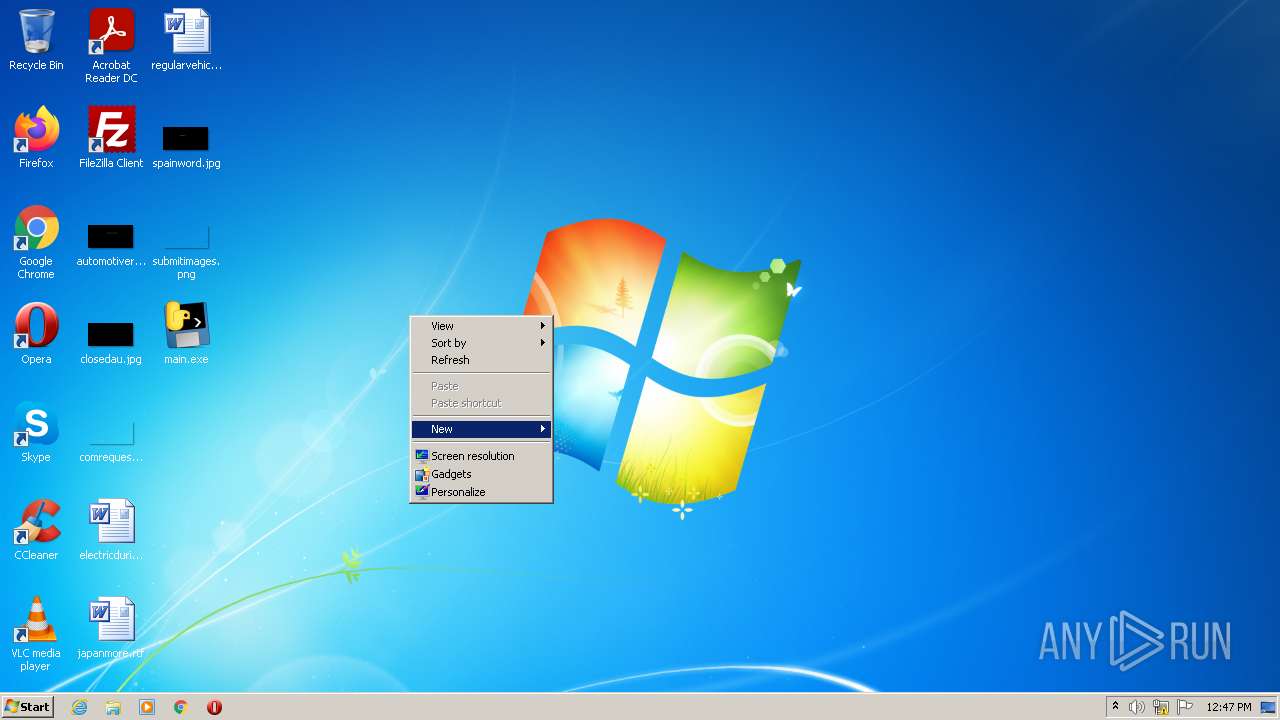
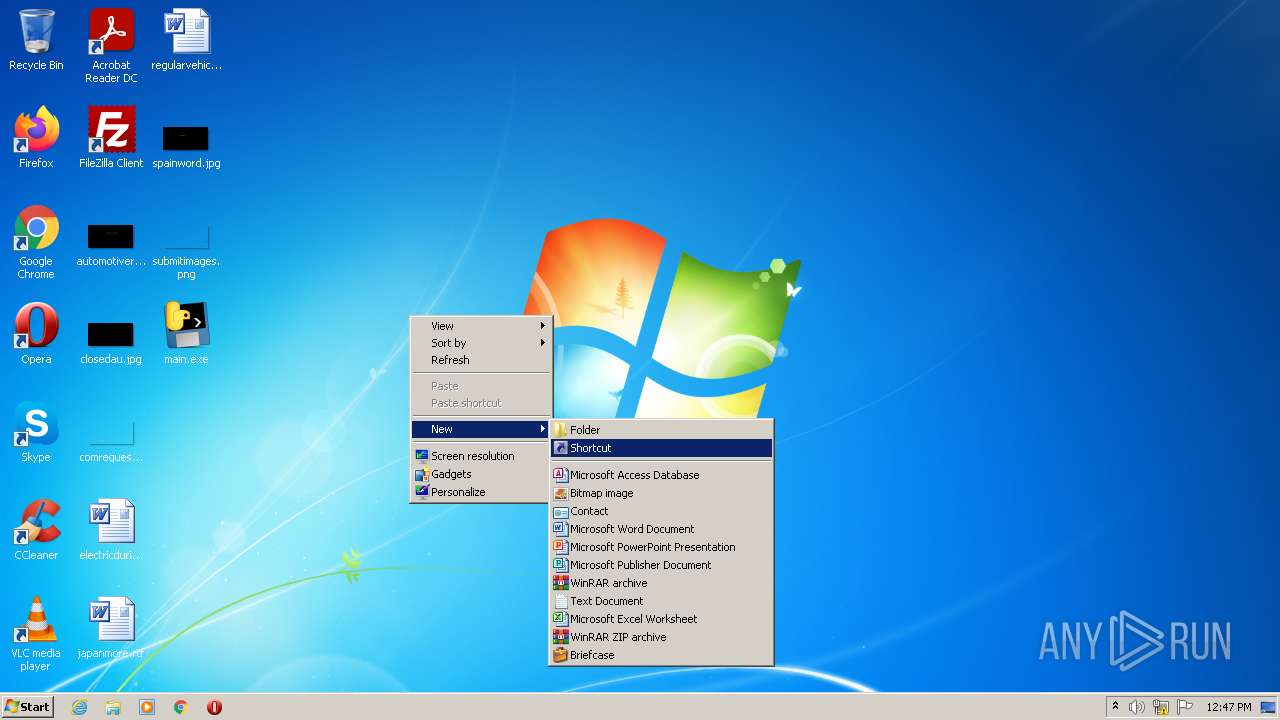
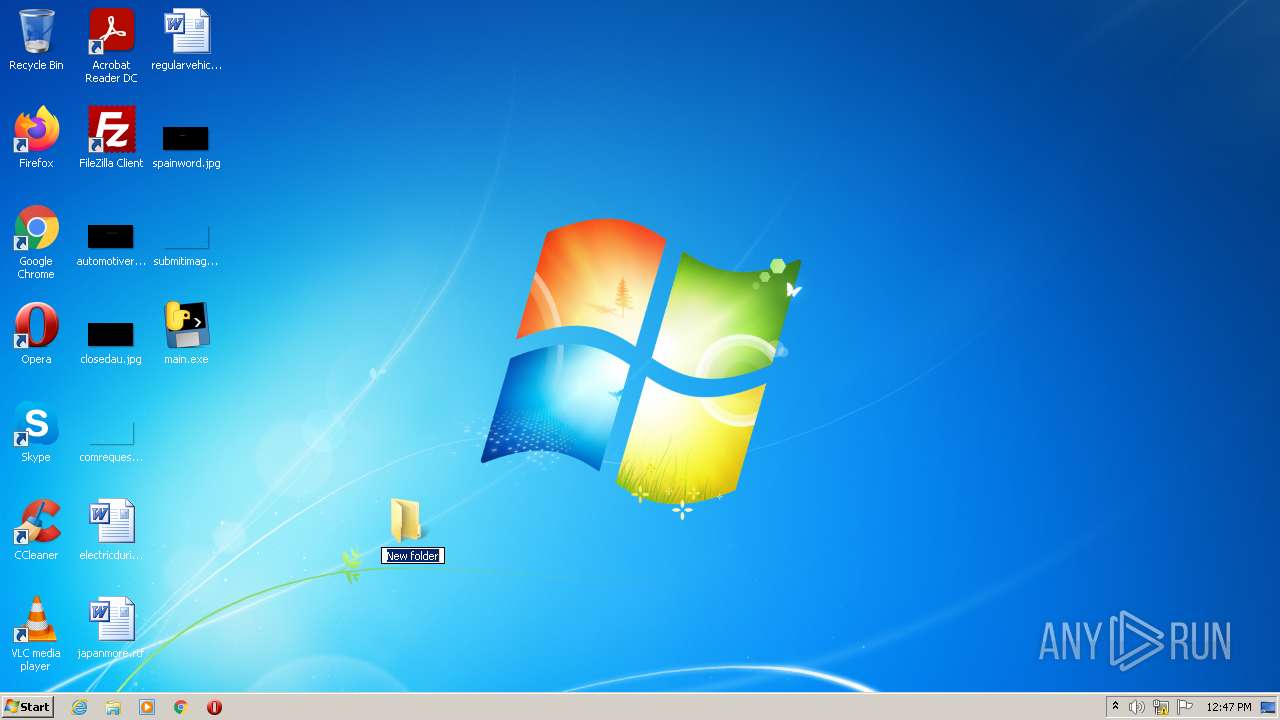
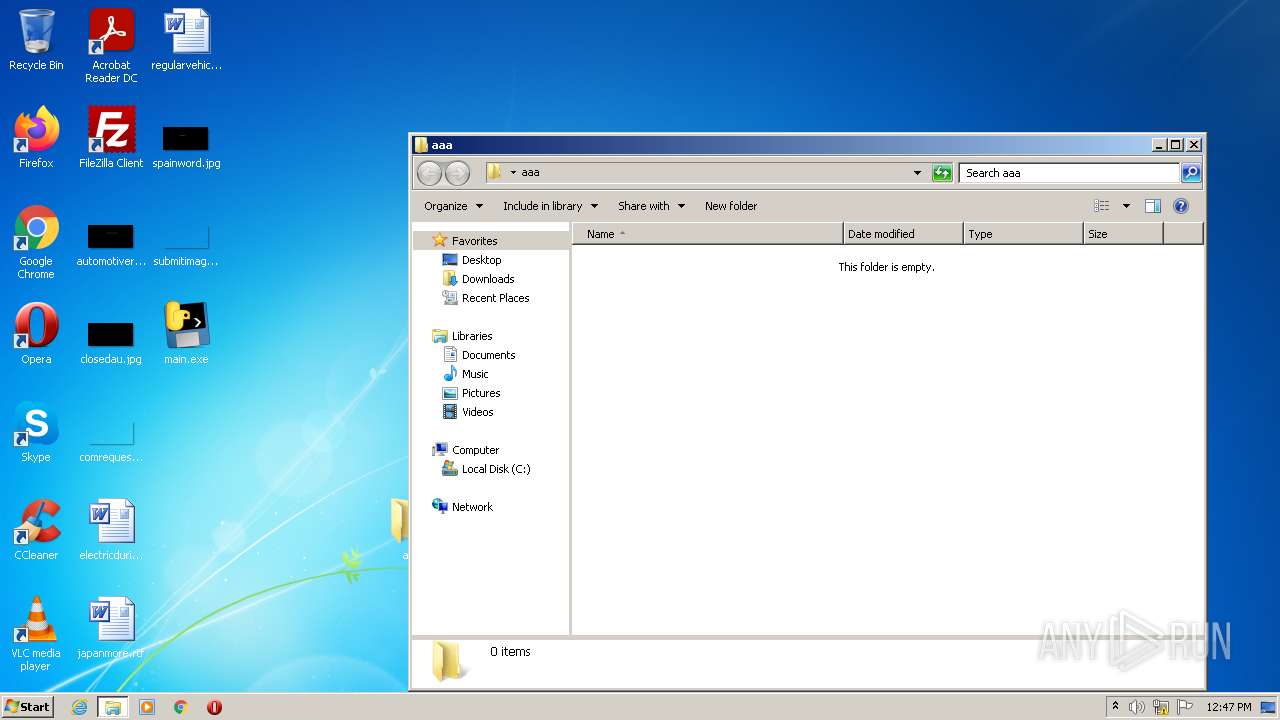
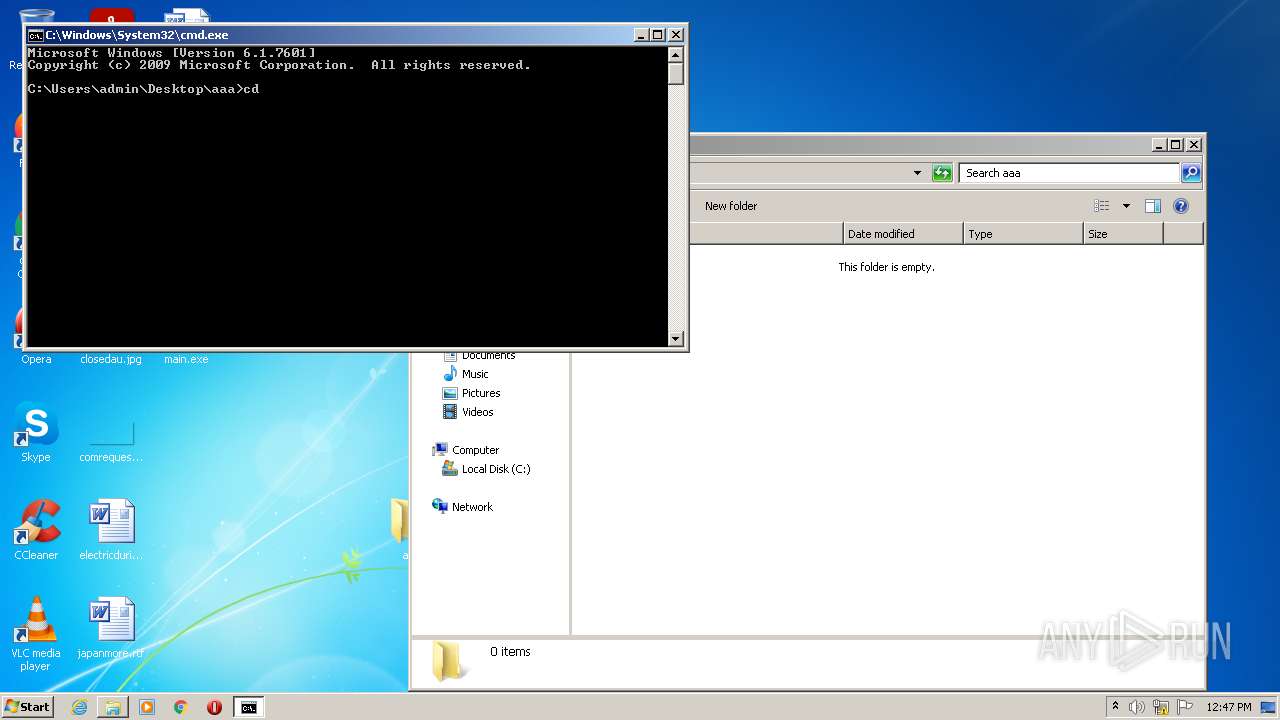
Manual execution by user
- cmd.exe (PID: 3080)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| Subsystem: | Windows command line |
|---|---|
| SubsystemVersion: | 5.1 |
| ImageVersion: | - |
| OSVersion: | 5.1 |
| EntryPoint: | 0x99a0 |
| UninitializedDataSize: | - |
| InitializedDataSize: | 128000 |
| CodeSize: | 151552 |
| LinkerVersion: | 14.32 |
| PEType: | PE32 |
| TimeStamp: | 2022:07:17 13:45:26+02:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_CUI |
| Compilation Date: | 17-Jul-2022 11:45:26 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000F8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 17-Jul-2022 11:45:26 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00024E52 | 0x00025000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.65753 |
.rdata | 0x00026000 | 0x0000D7E4 | 0x0000D800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.15305 |
.data | 0x00034000 | 0x0000F8D4 | 0x00000C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 1.88335 |
.reloc | 0x00044000 | 0x00001D88 | 0x00001E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.66216 |
.rsrc | 0x00046000 | 0x00010000 | 0x0000F200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.35485 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
0 | 2.71858 | 104 | UNKNOWN | UNKNOWN | RT_GROUP_ICON |
1 | 5.28693 | 1415 | UNKNOWN | UNKNOWN | RT_MANIFEST |
2 | 6.05629 | 2216 | UNKNOWN | UNKNOWN | RT_ICON |
3 | 5.5741 | 1384 | UNKNOWN | UNKNOWN | RT_ICON |
4 | 7.95079 | 37019 | UNKNOWN | UNKNOWN | RT_ICON |
5 | 5.29119 | 9640 | UNKNOWN | UNKNOWN | RT_ICON |
6 | 5.43869 | 4264 | UNKNOWN | UNKNOWN | RT_ICON |
7 | 5.89356 | 1128 | UNKNOWN | UNKNOWN | RT_ICON |
Imports
ADVAPI32.dll |
KERNEL32.dll |
Total processes
43
Monitored processes
6
Malicious processes
5
Suspicious processes
0
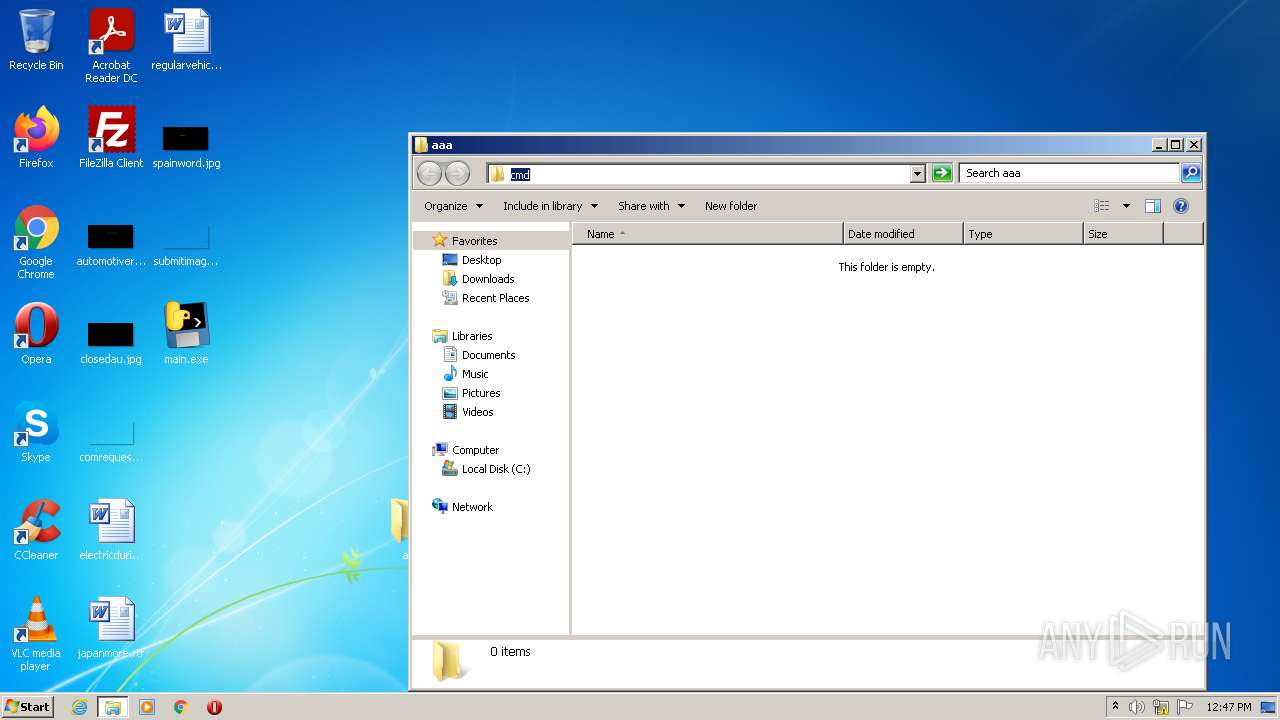
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 580 | main.exe | C:\Users\admin\Desktop\main.exe | cmd.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 1 Modules
| |||||||||||||||
| 600 | C:\Windows\system32\DllHost.exe /Processid:{76D0CB12-7604-4048-B83C-1005C7DDC503} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1912 | "C:\Users\admin\Desktop\main.exe" | C:\Users\admin\Desktop\main.exe | Explorer.EXE | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 1 Modules
| |||||||||||||||
| 3080 | "C:\Windows\System32\cmd.exe" | C:\Windows\System32\cmd.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3512 | main.exe | C:\Users\admin\Desktop\main.exe | main.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 1 Modules
| |||||||||||||||
| 3788 | "C:\Users\admin\Desktop\main.exe" | C:\Users\admin\Desktop\main.exe | main.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 1 Modules
| |||||||||||||||
Total events
541
Read events
539
Write events
2
Delete events
0
Modification events
| (PID) Process: | (600) DllHost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: DllHost.exe | |||
| (PID) Process: | (600) DllHost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows Photo Viewer\Viewer |
| Operation: | write | Name: | MainWndPos |
Value: 6000000034000000A00400008002000000000000 | |||
Executable files
134
Suspicious files
6
Text files
76
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1912 | main.exe | C:\Users\admin\AppData\Local\Temp\_MEI19122\PIL\_imaging.cp38-win32.pyd | executable | |
MD5:DACF9DBA8F4CEEDEF3A9D96E6278A544 | SHA256:161673BBDD09DC6E5EBF23D8A87ECF831D6AC43907A74441DD30DF3DB3485801 | |||
| 1912 | main.exe | C:\Users\admin\AppData\Local\Temp\_MEI19122\_decimal.pyd | executable | |
MD5:DD8724365CDF7372892B0220BC8007C0 | SHA256:FF753B671FE3A1D09B4676A0E08F85A4B19D0F5DD06B50DCA31339911730F343 | |||
| 1912 | main.exe | C:\Users\admin\AppData\Local\Temp\_MEI19122\_overlapped.pyd | executable | |
MD5:4E5C64134B6C40E187B7F8627A6D8A2D | SHA256:5EEF3EB8F87D332128569E4810F9283FF57417F1BB67D59D1AB2F471505DC1B1 | |||
| 1912 | main.exe | C:\Users\admin\AppData\Local\Temp\_MEI19122\VCRUNTIME140.dll | executable | |
MD5:87DD91C56BE82866BF96EF1666F30A99 | SHA256:49B0FD1751342C253CAC588DDA82EC08E4EF43CEBC5A9D80DEB7928109B90C4F | |||
| 1912 | main.exe | C:\Users\admin\AppData\Local\Temp\_MEI19122\_cffi_backend.cp38-win32.pyd | executable | |
MD5:FC7AAB36287CBEAE140E1BA35FF06DD2 | SHA256:2C939BEAE37667B797A04CD0EE36F25E7838E7F2FE7DC7C68C5203162187B573 | |||
| 1912 | main.exe | C:\Users\admin\AppData\Local\Temp\_MEI19122\_bz2.pyd | executable | |
MD5:445CE6BCEFB6EDDF0D953DBA17E0B320 | SHA256:CF721704D96F071DE10A1E174A07BB1211864EA588CE1C4D6023F11701AAAB13 | |||
| 1912 | main.exe | C:\Users\admin\AppData\Local\Temp\_MEI19122\PIL\_imagingtk.cp38-win32.pyd | executable | |
MD5:17FDDDD15568CAE490EE26AA626CB774 | SHA256:759C6DC85B712150E7D3276201EEEF746DD8153AA603971F5D70D543A0A928D4 | |||
| 1912 | main.exe | C:\Users\admin\AppData\Local\Temp\_MEI19122\_asyncio.pyd | executable | |
MD5:54414D216C4DEA54799DC0F5CE657FBE | SHA256:CEF9A3D83E7CC45D99D666A6F8E7E58CC68ACB14E8858FE5BC6ED54A0F7C3898 | |||
| 1912 | main.exe | C:\Users\admin\AppData\Local\Temp\_MEI19122\_hashlib.pyd | executable | |
MD5:76A7E9C182FB34121881B868829786E5 | SHA256:D6F37E0BC993D76BFD3D8F28963E0936D893C3EA1B6A4B2ABCB06A053FF0BB94 | |||
| 1912 | main.exe | C:\Users\admin\AppData\Local\Temp\_MEI19122\PIL\_imagingft.cp38-win32.pyd | executable | |
MD5:E0B3791F4242ADD3816F4FEFB8D8ABCA | SHA256:2BFB412C1953F89A2181D25F1B3B4895F40723A1236DCD1C7AAE6270D23383D0 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
2
DNS requests
1
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3788 | main.exe | GET | 200 | 34.160.111.145:80 | http://ifconfig.me/ | US | text | 13 b | shared |
3512 | main.exe | GET | 200 | 34.160.111.145:80 | http://ifconfig.me/ | US | text | 13 b | shared |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3512 | main.exe | 34.160.111.145:80 | ifconfig.me | — | US | malicious |
3788 | main.exe | 34.160.111.145:80 | ifconfig.me | — | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
ifconfig.me |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3788 | main.exe | Potential Corporate Privacy Violation | ET POLICY External IP Lookup Domain (ifconfig .me) |
3788 | main.exe | Potential Corporate Privacy Violation | AV POLICY Internal Host Retrieving External IP Address (ifconfig. me) |
3512 | main.exe | Potential Corporate Privacy Violation | ET POLICY External IP Lookup Domain (ifconfig .me) |
3512 | main.exe | Potential Corporate Privacy Violation | AV POLICY Internal Host Retrieving External IP Address (ifconfig. me) |
2 ETPRO signatures available at the full report