| File name: | wfreerdp.exe |
| Full analysis: | https://app.any.run/tasks/8debd508-3357-45a1-9984-d804e5335659 |
| Verdict: | No threats detected |
| Analysis date: | September 01, 2020, 08:19:51 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 6BB943EAAE29F7075B25FC49A9FCF977 |
| SHA1: | 66D799EDCCACC1B3AD670E30E902D99FA365267C |
| SHA256: | CE8173BD3E152DD6E24E4890027D5A848A83656EDAD01F8431CE9432E376F24E |
| SSDEEP: | 49152:JqD2C9oxuqkXaEkyDk9qzYf6YLEHhmetTBojhH0R3JY67OPiBMc/fBg:JqDHexuqkXpkUuEHhmeXojiR5Y675B |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
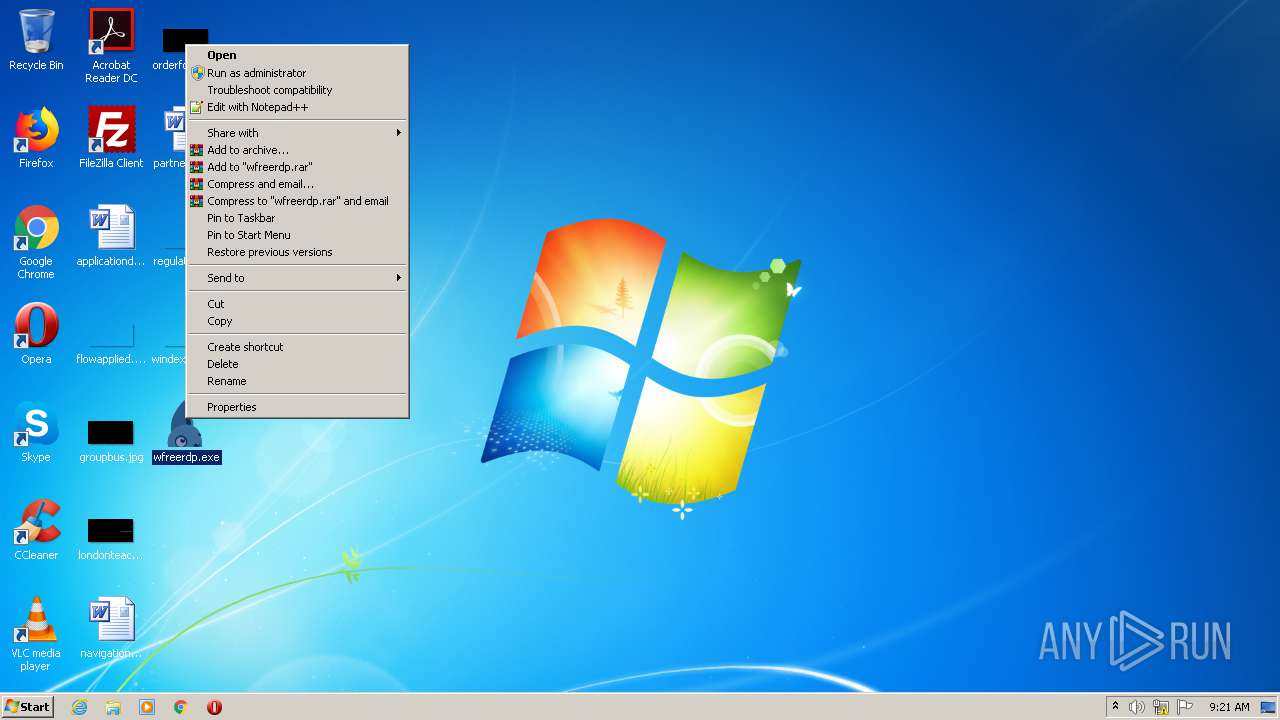
Manual execution by user
- wfreerdp.exe (PID: 3640)
- taskmgr.exe (PID: 2688)
- wfreerdp.exe (PID: 3492)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:05:17 10:01:09+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 12 |
| CodeSize: | 1764352 |
| InitializedDataSize: | 836608 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x180edc |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 17-May-2019 08:01:09 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000108 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 17-May-2019 08:01:09 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x001AEAED | 0x001AEC00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.65256 |
.rdata | 0x001B0000 | 0x00087178 | 0x00087200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.04833 |
.data | 0x00238000 | 0x0002226C | 0x0000D400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.86313 |
.tls | 0x0025B000 | 0x00000015 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x0025C000 | 0x0000C8D8 | 0x0000CA00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.40592 |
.reloc | 0x00269000 | 0x000161D0 | 0x00016200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.71044 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.91161 | 381 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 3.40132 | 296 | UNKNOWN | English - United States | RT_ICON |
3 | 4.08057 | 3752 | UNKNOWN | English - United States | RT_ICON |
4 | 4.55464 | 2216 | UNKNOWN | English - United States | RT_ICON |
5 | 4.70795 | 1384 | UNKNOWN | English - United States | RT_ICON |
6 | 7.82684 | 6586 | UNKNOWN | English - United States | RT_ICON |
7 | 3.18359 | 9640 | UNKNOWN | English - United States | RT_ICON |
8 | 3.21964 | 4264 | UNKNOWN | English - United States | RT_ICON |
9 | 3.90835 | 1128 | UNKNOWN | English - United States | RT_ICON |
100 | 3.33413 | 1972 | UNKNOWN | English - United States | RT_BITMAP |
Imports
ADVAPI32.dll |
GDI32.dll |
KERNEL32.dll |
MSIMG32.dll |
NTDSAPI.dll |
RPCRT4.dll |
SHELL32.dll |
SHLWAPI.dll |
USER32.dll |
WINMM.dll |
Exports
Title | Ordinal | Address |
|---|---|---|
Bitmap_Alloc | 1 | 0x00042570 |
Bitmap_SetDimensions | 2 | 0x00042610 |
Bitmap_SetRectangle | 3 | 0x00042650 |
FreeRDP_InitWtsApi | 4 | 0x00091070 |
Glyph_Alloc | 5 | 0x00042690 |
Pointer_Alloc | 6 | 0x00042750 |
RdpClientEntry | 7 | 0x0001F760 |
WTSChannelGetHandleById | 8 | 0x000B9790 |
WTSChannelGetHandleByName | 9 | 0x000B97D0 |
WTSChannelGetId | 10 | 0x000B9810 |
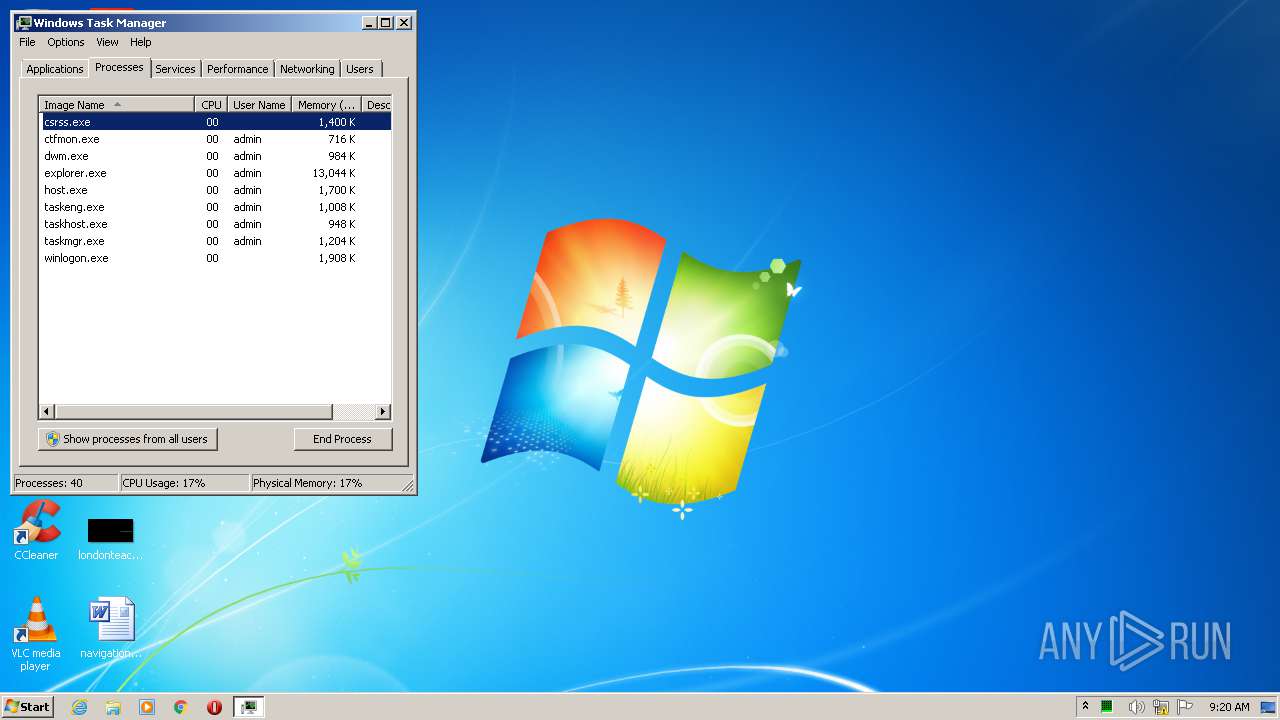
Total processes
48
Monitored processes
4
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
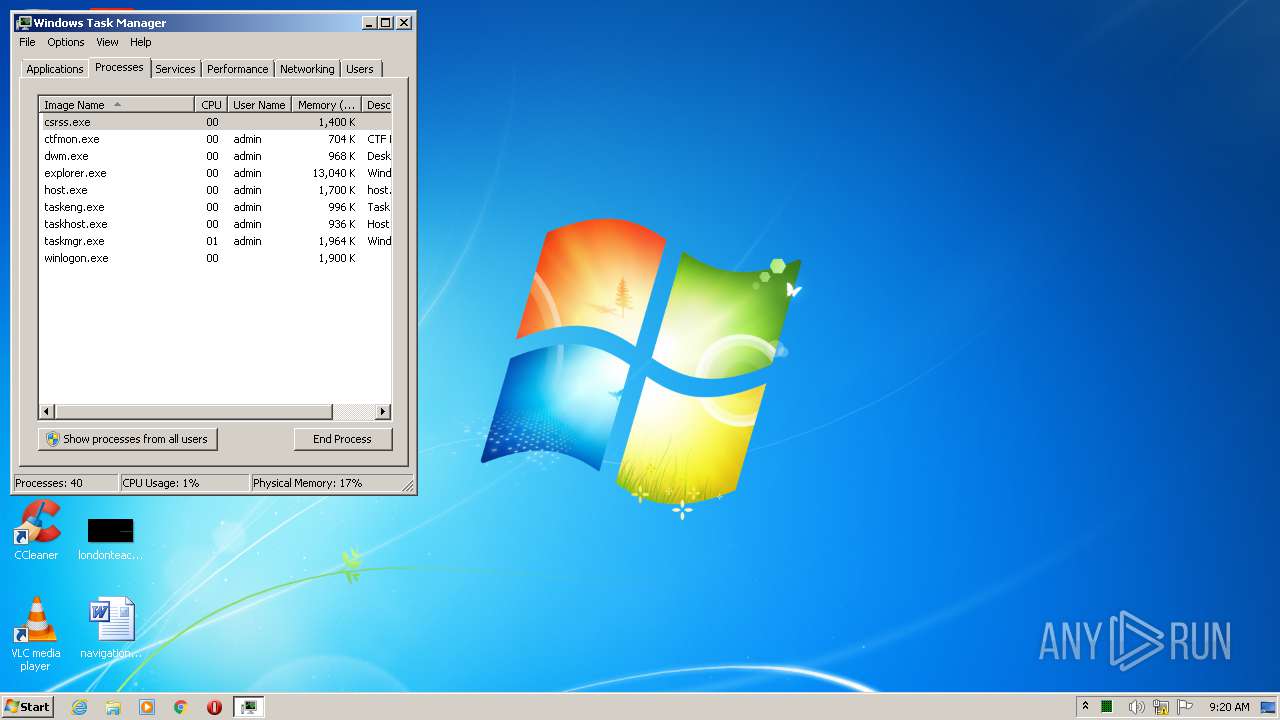
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2688 | "C:\Windows\system32\taskmgr.exe" /4 | C:\Windows\system32\taskmgr.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Task Manager Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3148 | "C:\Users\admin\Desktop\wfreerdp.exe" | C:\Users\admin\Desktop\wfreerdp.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 1 Modules
| |||||||||||||||
| 3492 | "C:\Users\admin\Desktop\wfreerdp.exe" | C:\Users\admin\Desktop\wfreerdp.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 1 Modules
| |||||||||||||||
| 3640 | "C:\Users\admin\Desktop\wfreerdp.exe" | C:\Users\admin\Desktop\wfreerdp.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 1 Modules
| |||||||||||||||
Total events
23
Read events
21
Write events
2
Delete events
0
Modification events
| (PID) Process: | (2688) taskmgr.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\TaskManager |
| Operation: | write | Name: | UsrColumnSettings |
Value: 1C0C0000340400000000000050000000010000001D0C0000350400000000000023000000010000001E0C000036040000000000003C000000010000001F0C000039040000000000004E00000001000000200C000037040000000000004E00000001000000 | |||
| (PID) Process: | (2688) taskmgr.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\TaskManager |
| Operation: | write | Name: | Preferences |
Value: 30030000E803000001000000010000000A0000000A000000A2010000F00100000100000001000000000000000000000001000000000000000100000000000000000000000200000004000000090000001D000000FFFFFFFF00000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000009C00000040000000210000004600000052000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF0000000002000000010000000300000004000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF0500000000000000FFFFFFFF00000000020000000300000004000000FFFFFFFF00000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000630060003C005A00FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF000000000000010000000200000003000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF0400000000000000FFFFFFFF00000000FFFFFFFF4F00000028000000500000003400000050000000000000000100000002000000030000000400000000000000FFFFFFFF43000000000000000000000001000000 | |||
Executable files
0
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
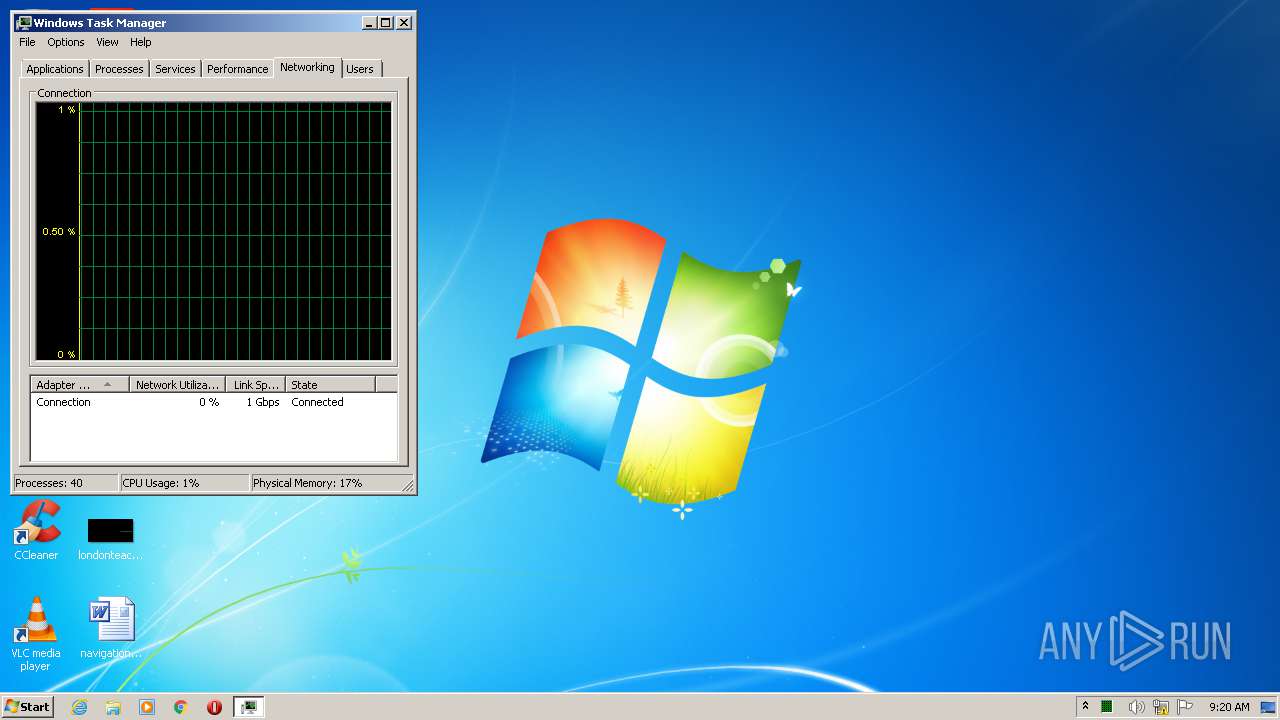
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report