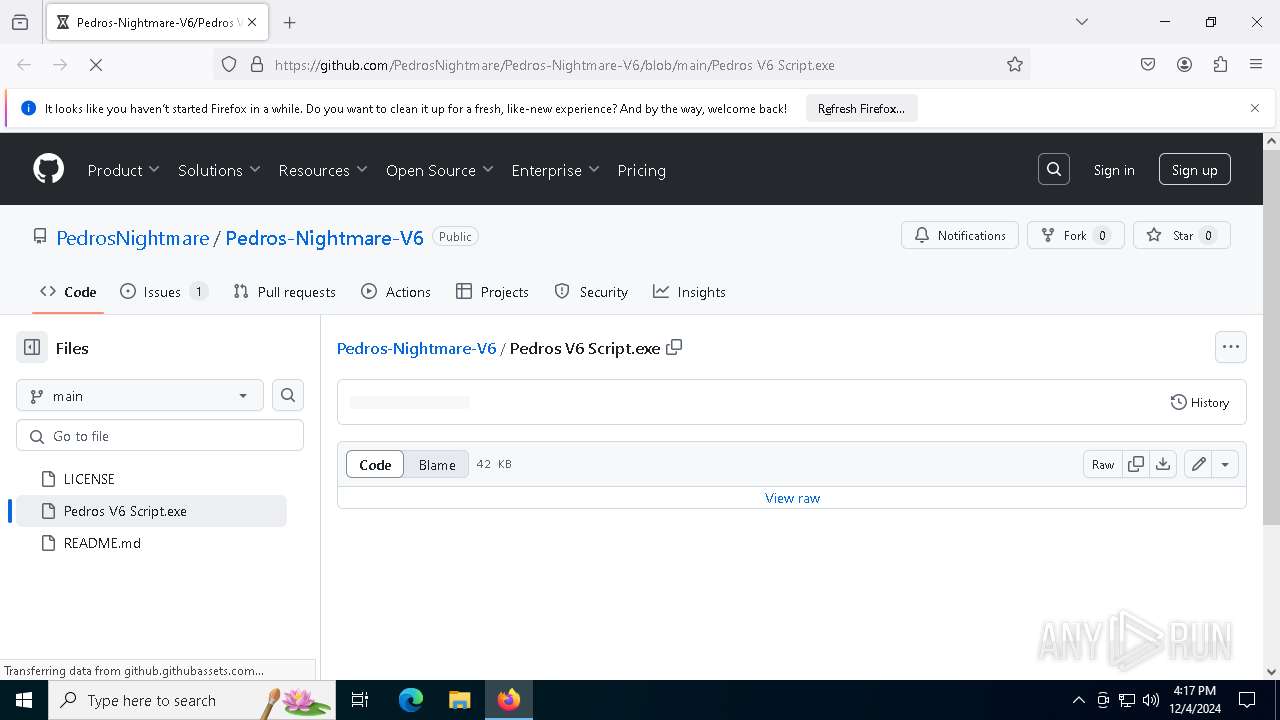
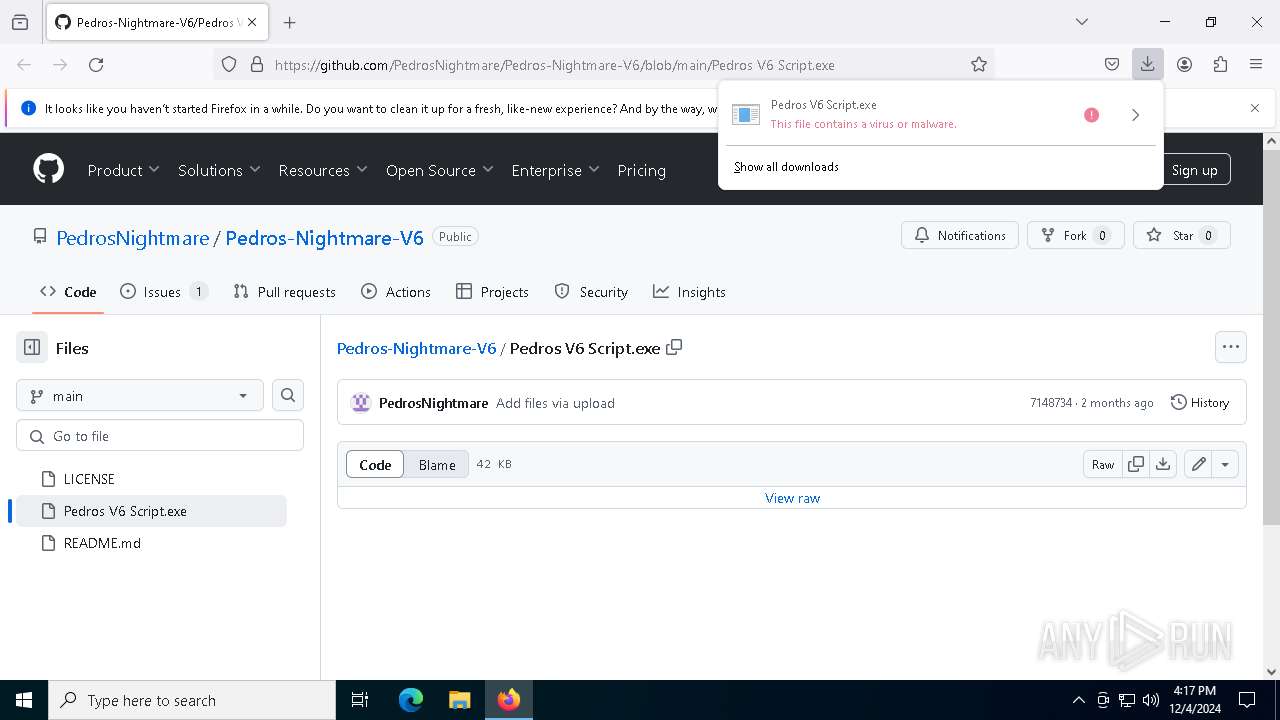
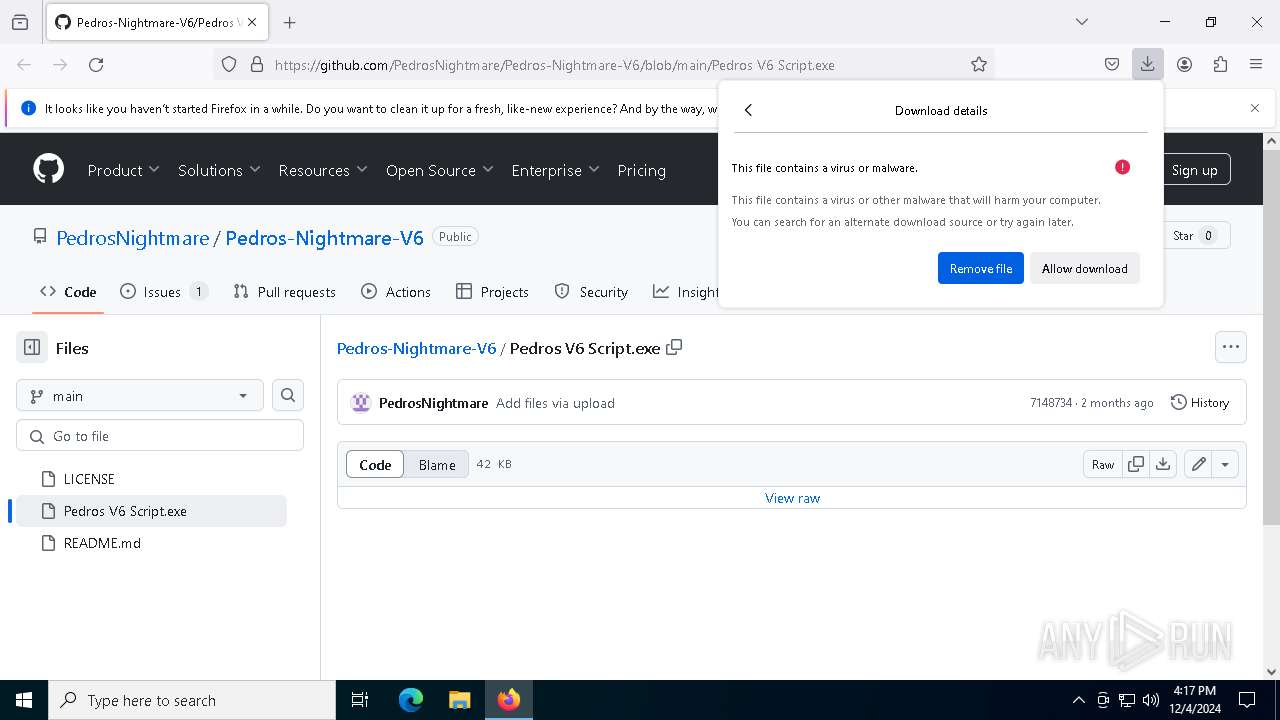
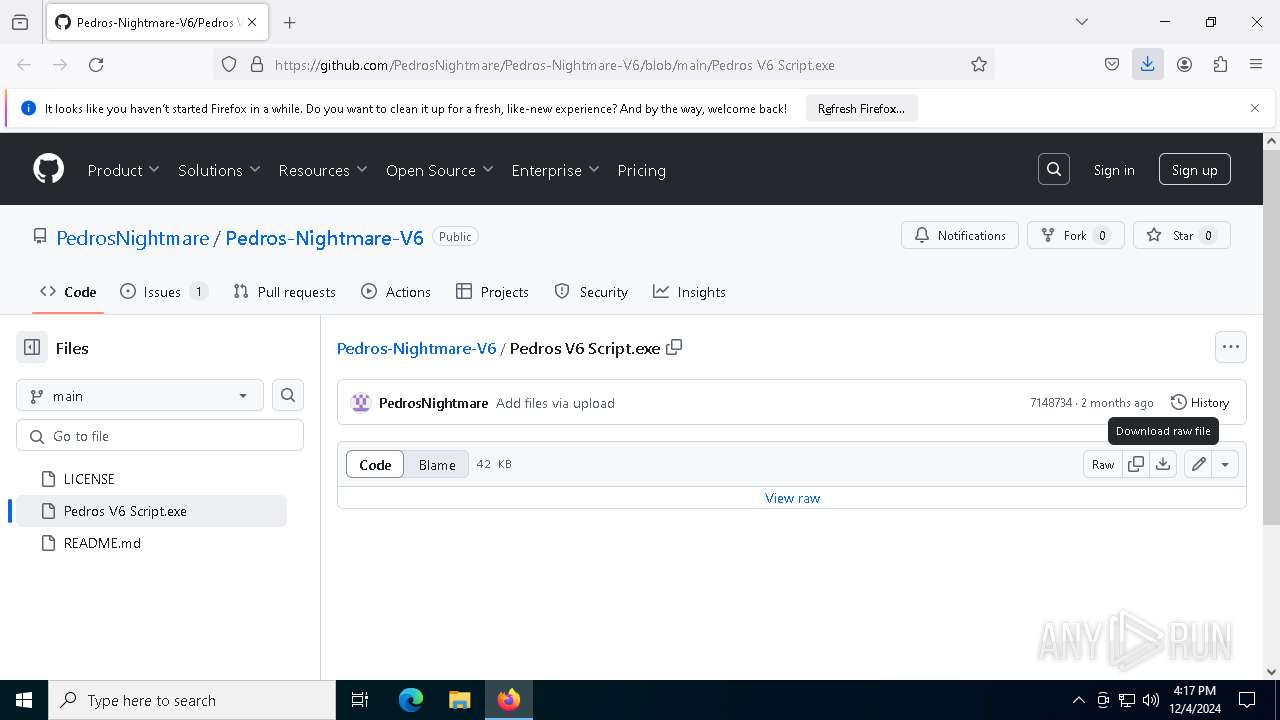
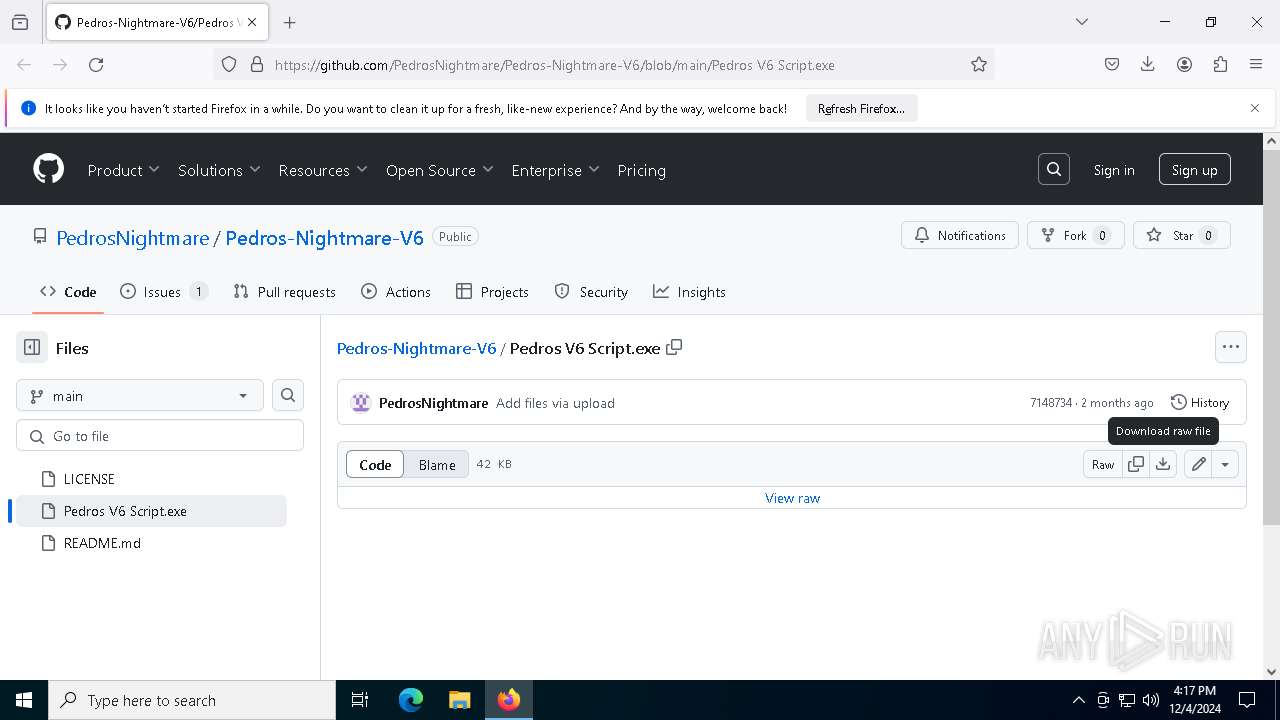
| URL: | https://github.com/PedrosNightmare/Pedros-Nightmare-V6/blob/main/Pedros%20V6%20Script.exe |
| Full analysis: | https://app.any.run/tasks/c58c096c-c509-4bcc-9cb4-e0c7f4110c13 |
| Verdict: | Malicious activity |
| Threats: | Stealers are a group of malicious software that are intended for gaining unauthorized access to users’ information and transferring it to the attacker. The stealer malware category includes various types of programs that focus on their particular kind of data, including files, passwords, and cryptocurrency. Stealers are capable of spying on their targets by recording their keystrokes and taking screenshots. This type of malware is primarily distributed as part of phishing campaigns. |
| Analysis date: | December 04, 2024, 16:16:51 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | E9BD5F8631A802A9E2D358982A092450 |
| SHA1: | 6A3FBCE0E7000DDCD1614ABB103C17049F4E19E8 |
| SHA256: | CE76F9B95251EEAE44BB9C116AD9A77E9164A7A07C855B6E81F891F4612B336F |
| SSDEEP: | 3:N8tEdoM+5XScD5XlHzERaXkVYcVv:2uI55saMV |
MALICIOUS
MERCURIALGRABBER has been detected (YARA)
- Pedros V6 Script.exe (PID: 8092)
Stealers network behavior
- Pedros V6 Script.exe (PID: 8092)
Attempting to use instant messaging service
- Pedros V6 Script.exe (PID: 8092)
SUSPICIOUS
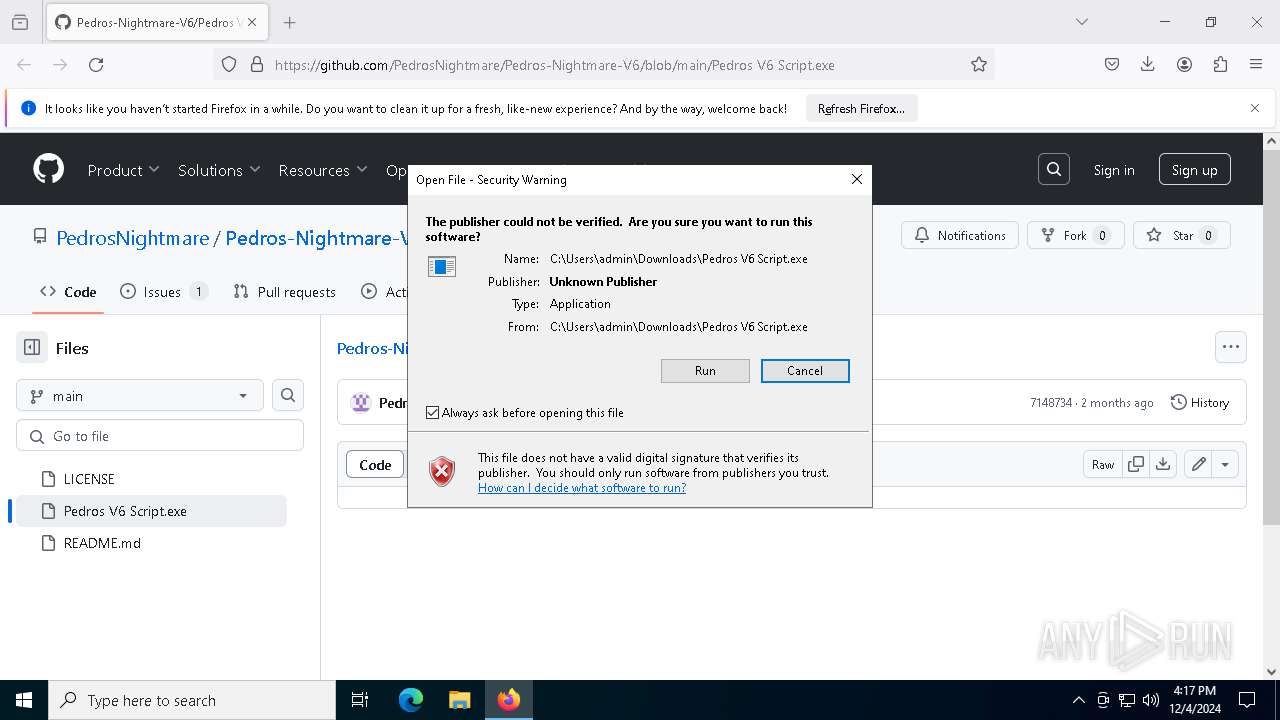
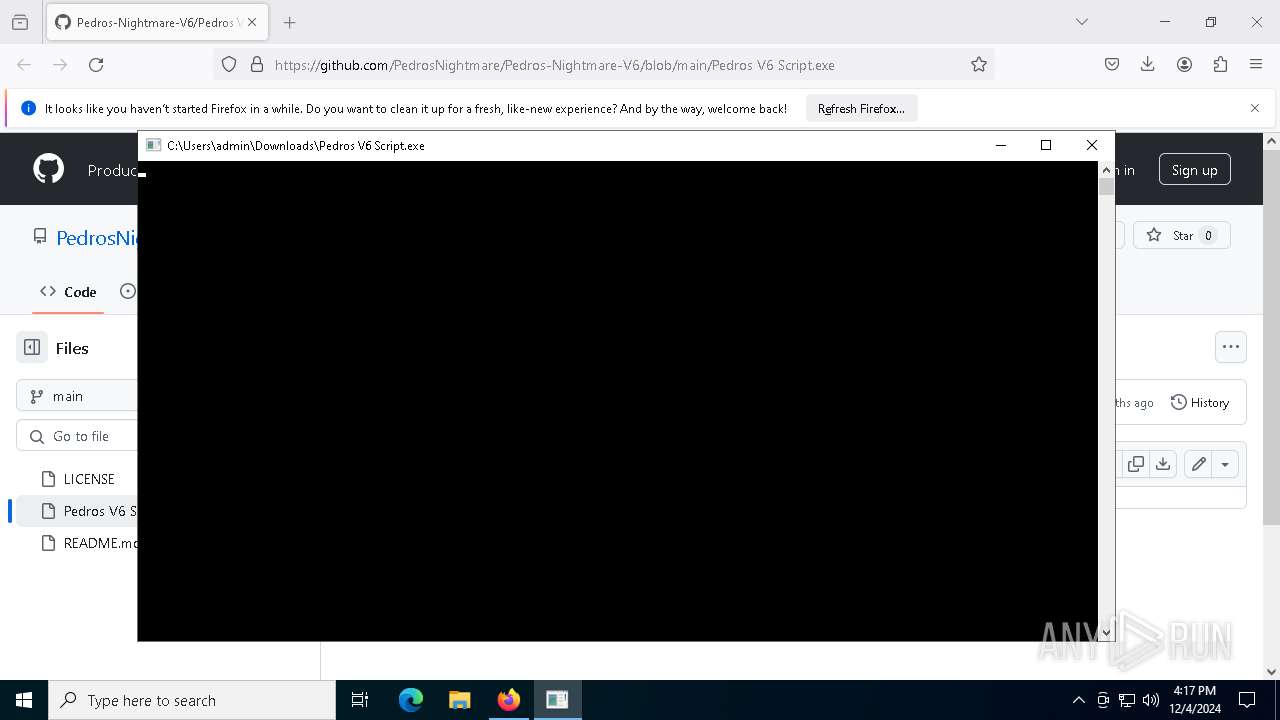
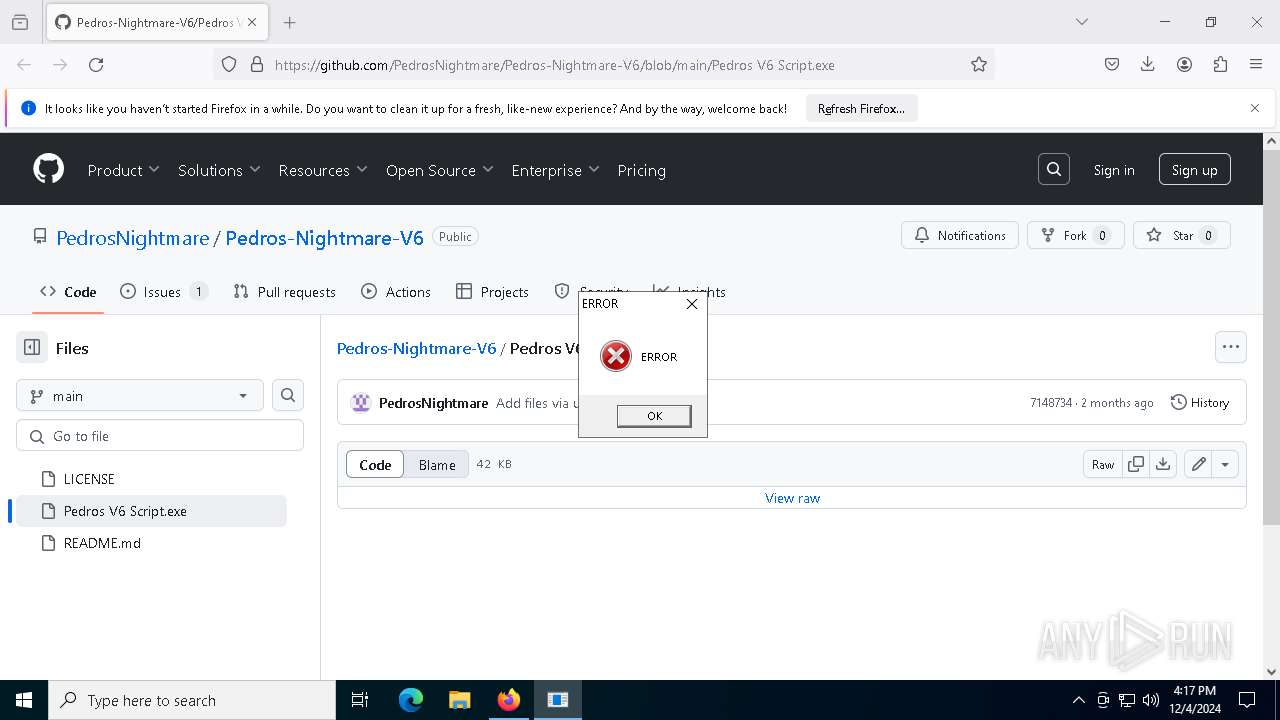
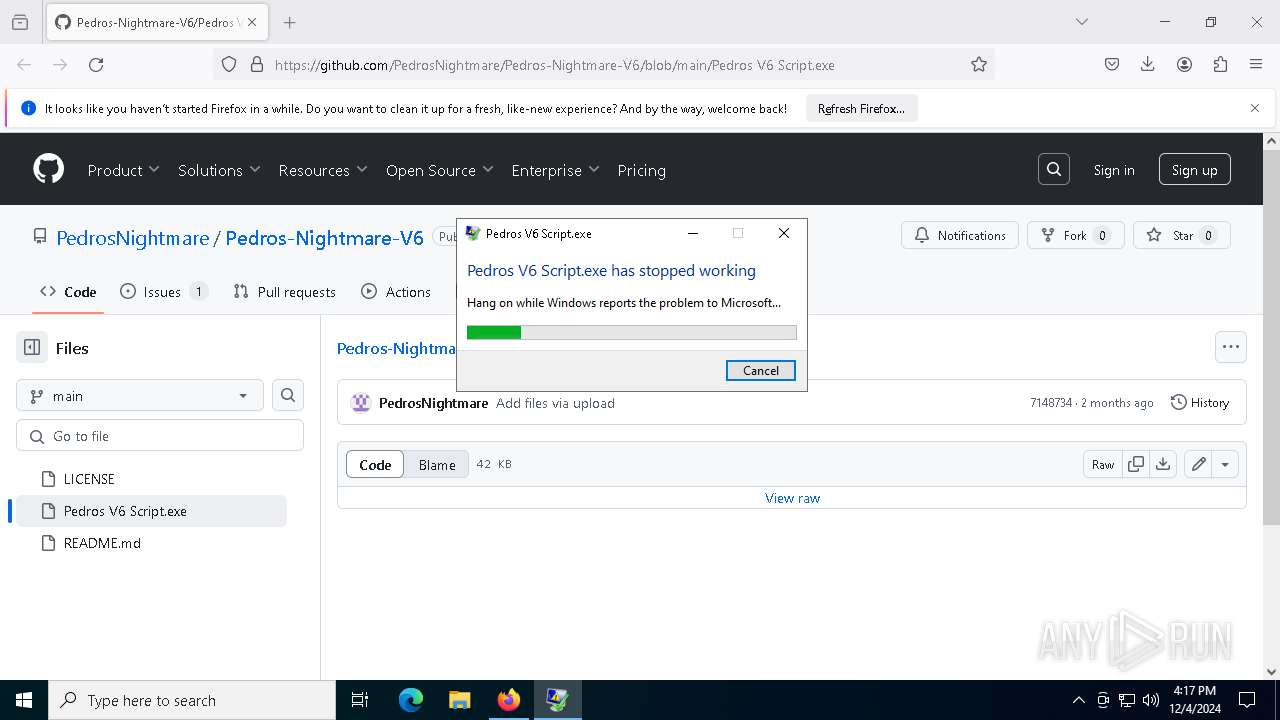
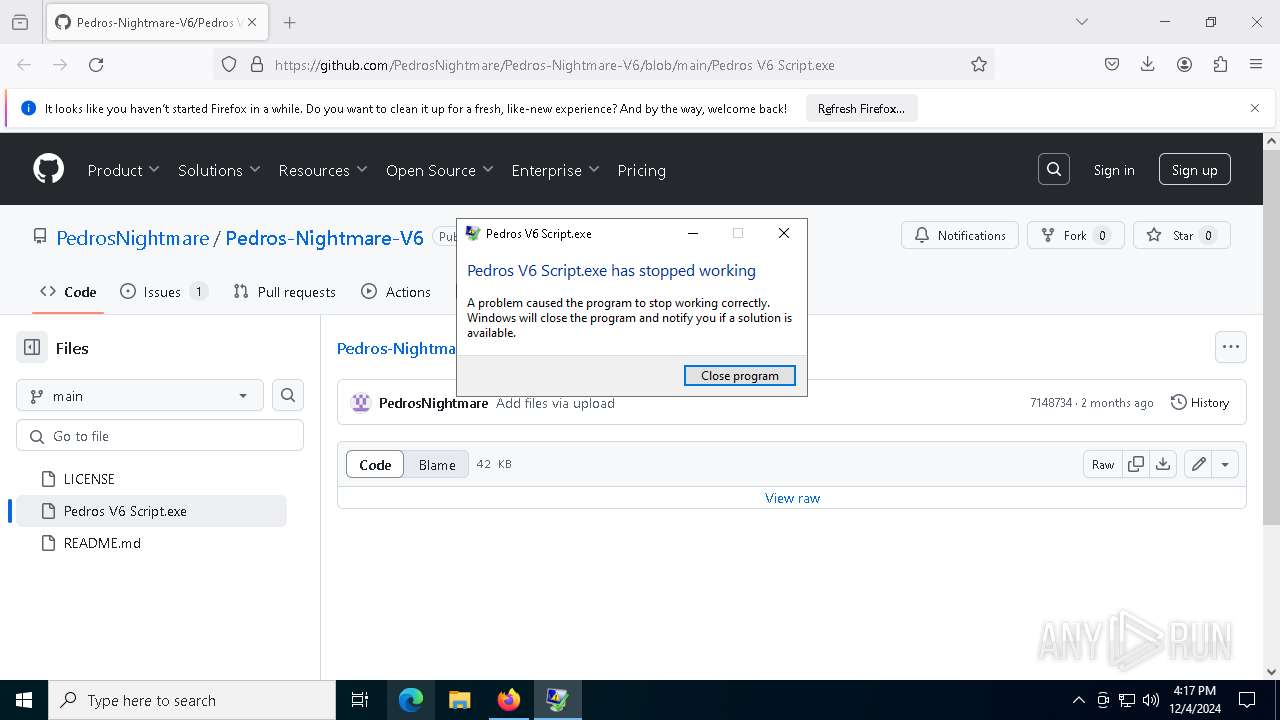
Executes application which crashes
- Pedros V6 Script.exe (PID: 8092)
Checks for external IP
- svchost.exe (PID: 2192)
- Pedros V6 Script.exe (PID: 8092)
The process connected to a server suspected of theft
- Pedros V6 Script.exe (PID: 8092)
Possible usage of Discord/Telegram API has been detected (YARA)
- Pedros V6 Script.exe (PID: 8092)
INFO
Application launched itself
- firefox.exe (PID: 6152)
- firefox.exe (PID: 1344)
Executable content was dropped or overwritten
- firefox.exe (PID: 6152)
Attempting to use instant messaging service
- Pedros V6 Script.exe (PID: 8092)
- svchost.exe (PID: 2192)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
MercurialGrabber
(PID) Process(8092) Pedros V6 Script.exe
C2https://discordapp.com/api/webhooks/1301311624250130544/2jis7mvj0IlQvtQROmrXvyZqQESd2I2DOetw_7w7WXGZnVcUYO4BjGVxMgkuBDhHlfZ9
ims-api
(PID) Process(8092) Pedros V6 Script.exe
Discord-Webhook-Tokens (1)1301311624250130544/2jis7mvj0IlQvtQROmrXvyZqQESd2I2DOetw_7w7WXGZnVcUYO4BjGVxMgkuBDhHlfZ9
Discord-Info-Links
1301311624250130544/2jis7mvj0IlQvtQROmrXvyZqQESd2I2DOetw_7w7WXGZnVcUYO4BjGVxMgkuBDhHlfZ9
Get Webhook Infohttps://discord.com/api/webhooks/1301311624250130544/2jis7mvj0IlQvtQROmrXvyZqQESd2I2DOetw_7w7WXGZnVcUYO4BjGVxMgkuBDhHlfZ9
Total processes
155
Monitored processes
17
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 236 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=4896 -childID 3 -isForBrowser -prefsHandle 4888 -prefMapHandle 4872 -prefsLen 31197 -prefMapSize 244583 -jsInitHandle 1132 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {b95db6ab-1670-4642-b136-adaf0e80b2b3} 6152 "\\.\pipe\gecko-crash-server-pipe.6152" 1a15413b690 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Version: 123.0 Modules
| |||||||||||||||
| 1344 | "C:\Program Files\Mozilla Firefox\firefox.exe" "https://github.com/PedrosNightmare/Pedros-Nightmare-V6/blob/main/Pedros%20V6%20Script.exe" | C:\Program Files\Mozilla Firefox\firefox.exe | — | explorer.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 123.0 Modules
| |||||||||||||||
| 1488 | "C:\WINDOWS\system32\UCPDMgr.exe" | C:\Windows\System32\UCPDMgr.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: User Choice Protection Manager Exit code: 0 Version: 1.0.0.414301 Modules
| |||||||||||||||
| 2192 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6152 | "C:\Program Files\Mozilla Firefox\firefox.exe" https://github.com/PedrosNightmare/Pedros-Nightmare-V6/blob/main/Pedros%20V6%20Script.exe | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Version: 123.0 Modules
| |||||||||||||||
| 6192 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=4824 -childID 6 -isForBrowser -prefsHandle 4904 -prefMapHandle 4900 -prefsLen 34930 -prefMapSize 244583 -jsInitHandle 1132 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {e41db6e0-1aec-496b-85ae-93dd4a89a1a3} 6152 "\\.\pipe\gecko-crash-server-pipe.6152" 1a156a1b4d0 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Version: 123.0 Modules
| |||||||||||||||
| 6276 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=4928 -childID 4 -isForBrowser -prefsHandle 5004 -prefMapHandle 5000 -prefsLen 31197 -prefMapSize 244583 -jsInitHandle 1132 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {70657149-5317-438a-adab-d6d3b08f52d9} 6152 "\\.\pipe\gecko-crash-server-pipe.6152" 1a1565e3690 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Version: 123.0 Modules
| |||||||||||||||
| 6356 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=1708 -parentBuildID 20240213221259 -prefsHandle 1752 -prefMapHandle 1728 -prefsLen 31031 -prefMapSize 244583 -appDir "C:\Program Files\Mozilla Firefox\browser" - {24a053f6-9e5f-4ca4-add1-0acfb8210e9a} 6152 "\\.\pipe\gecko-crash-server-pipe.6152" 1a14c2ea710 gpu | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Version: 123.0 Modules
| |||||||||||||||
| 6452 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=2072 -parentBuildID 20240213221259 -prefsHandle 2064 -prefMapHandle 2060 -prefsLen 31031 -prefMapSize 244583 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {819cec23-8751-48b7-9d9a-5150b6d36464} 6152 "\\.\pipe\gecko-crash-server-pipe.6152" 1a140383510 socket | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Version: 123.0 Modules
| |||||||||||||||
| 6644 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=4860 -childID 5 -isForBrowser -prefsHandle 5008 -prefMapHandle 5012 -prefsLen 31197 -prefMapSize 244583 -jsInitHandle 1132 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {7151e808-c071-41d2-84ac-90392c6d008f} 6152 "\\.\pipe\gecko-crash-server-pipe.6152" 1a156a1b310 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Version: 123.0 Modules
| |||||||||||||||
Total events
19 217
Read events
19 201
Write events
16
Delete events
0
Modification events
| (PID) Process: | (6152) firefox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Mozilla\Firefox\DllPrefetchExperiment |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe |
Value: 0 | |||
| (PID) Process: | (6152) firefox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | SlowContextMenuEntries |
Value: 6024B221EA3A6910A2DC08002B30309D0A010000BD0E0C47735D584D9CEDE91E22E23282770100000114020000000000C0000000000000468D0000006078A409B011A54DAFA526D86198A780390100009AD298B2EDA6DE11BA8CA68E55D895936E000000 | |||
| (PID) Process: | (8092) Pedros V6 Script.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Pedros V6 Script_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (8092) Pedros V6 Script.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Pedros V6 Script_RASAPI32 |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (8092) Pedros V6 Script.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Pedros V6 Script_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (8092) Pedros V6 Script.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Pedros V6 Script_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: | |||
| (PID) Process: | (8092) Pedros V6 Script.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Pedros V6 Script_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: | |||
| (PID) Process: | (8092) Pedros V6 Script.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Pedros V6 Script_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (8092) Pedros V6 Script.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Pedros V6 Script_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (8092) Pedros V6 Script.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Pedros V6 Script_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
Executable files
4
Suspicious files
175
Text files
47
Unknown types
9
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6152 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\scriptCache-current.bin | — | |
MD5:— | SHA256:— | |||
| 6152 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\urlCache-current.bin | binary | |
MD5:297E88D7CEB26E549254EC875649F4EB | SHA256:8B75D4FB1845BAA06122888D11F6B65E6A36B140C54A72CC13DF390FD7C95702 | |||
| 6152 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\prefs.js | text | |
MD5:2C99A16AED3906D92FFE3EF1808E2753 | SHA256:08412578CC3BB4922388F8FF8C23962F616B69A1588DA720ADE429129C73C452 | |||
| 6152 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\scriptCache-child-current.bin | binary | |
MD5:C95DDC2B1A525D1A243E4C294DA2F326 | SHA256:3A5919E086BFB31E36110CF636D2D5109EB51F2C410B107F126126AB25D67363 | |||
| 6152 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 6152 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite | — | |
MD5:— | SHA256:— | |||
| 6152 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\prefs-1.js | text | |
MD5:2C99A16AED3906D92FFE3EF1808E2753 | SHA256:08412578CC3BB4922388F8FF8C23962F616B69A1588DA720ADE429129C73C452 | |||
| 6152 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\sessionCheckpoints.json | binary | |
MD5:EA8B62857DFDBD3D0BE7D7E4A954EC9A | SHA256:792955295AE9C382986222C6731C5870BD0E921E7F7E34CC4615F5CD67F225DA | |||
| 6152 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\sessionCheckpoints.json.tmp | binary | |
MD5:EA8B62857DFDBD3D0BE7D7E4A954EC9A | SHA256:792955295AE9C382986222C6731C5870BD0E921E7F7E34CC4615F5CD67F225DA | |||
| 6152 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\1451318868ntouromlalnodry--epcr.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
35
TCP/UDP connections
117
DNS requests
144
Threats
11
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6152 | firefox.exe | POST | 200 | 172.64.149.23:80 | http://ocsp.sectigo.com/ | unknown | — | — | whitelisted |
6152 | firefox.exe | POST | 200 | 195.138.255.24:80 | http://r11.o.lencr.org/ | unknown | — | — | whitelisted |
6152 | firefox.exe | POST | 200 | 142.250.181.227:80 | http://o.pki.goog/wr2 | unknown | — | — | whitelisted |
3052 | svchost.exe | GET | 200 | 23.32.238.123:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
3052 | svchost.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6152 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/canonical.html | unknown | — | — | whitelisted |
6152 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/success.txt?ipv4 | unknown | — | — | whitelisted |
6152 | firefox.exe | POST | 200 | 142.250.181.227:80 | http://o.pki.goog/s/wr3/yvU | unknown | — | — | whitelisted |
6152 | firefox.exe | POST | 200 | 195.138.255.24:80 | http://r11.o.lencr.org/ | unknown | — | — | whitelisted |
6152 | firefox.exe | POST | 200 | 172.64.149.23:80 | http://ocsp.sectigo.com/ | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3052 | svchost.exe | 23.32.238.123:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
3052 | svchost.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
— | — | 104.126.37.123:443 | — | Akamai International B.V. | DE | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6152 | firefox.exe | 34.117.188.166:443 | contile.services.mozilla.com | — | — | whitelisted |
6152 | firefox.exe | 140.82.121.4:443 | github.com | GITHUB | US | shared |
6152 | firefox.exe | 172.217.23.106:443 | safebrowsing.googleapis.com | — | — | whitelisted |
6152 | firefox.exe | 34.107.221.82:80 | detectportal.firefox.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
github.com |
| shared |
detectportal.firefox.com |
| whitelisted |
prod.detectportal.prod.cloudops.mozgcp.net |
| whitelisted |
contile.services.mozilla.com |
| whitelisted |
example.org |
| whitelisted |
ipv4only.arpa |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2192 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
2192 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
2192 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
2192 | svchost.exe | Device Retrieving External IP Address Detected | INFO [ANY.RUN] External IP Check (ip-api .com) |
2192 | svchost.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup Domain in DNS Lookup (ip-api .com) |
2192 | svchost.exe | Misc activity | ET INFO Observed Discord Domain in DNS Lookup (discordapp .com) |
8092 | Pedros V6 Script.exe | Device Retrieving External IP Address Detected | ET POLICY External IP Lookup ip-api.com |
8092 | Pedros V6 Script.exe | Misc activity | ET INFO Observed Discord Domain (discordapp .com in TLS SNI) |
8092 | Pedros V6 Script.exe | Successful Credential Theft Detected | STEALER [ANY.RUN] Attempt to exfiltrate via Discord |
8092 | Pedros V6 Script.exe | Misc activity | ET INFO Observed Discord Domain (discordapp .com in TLS SNI) |
1 ETPRO signatures available at the full report