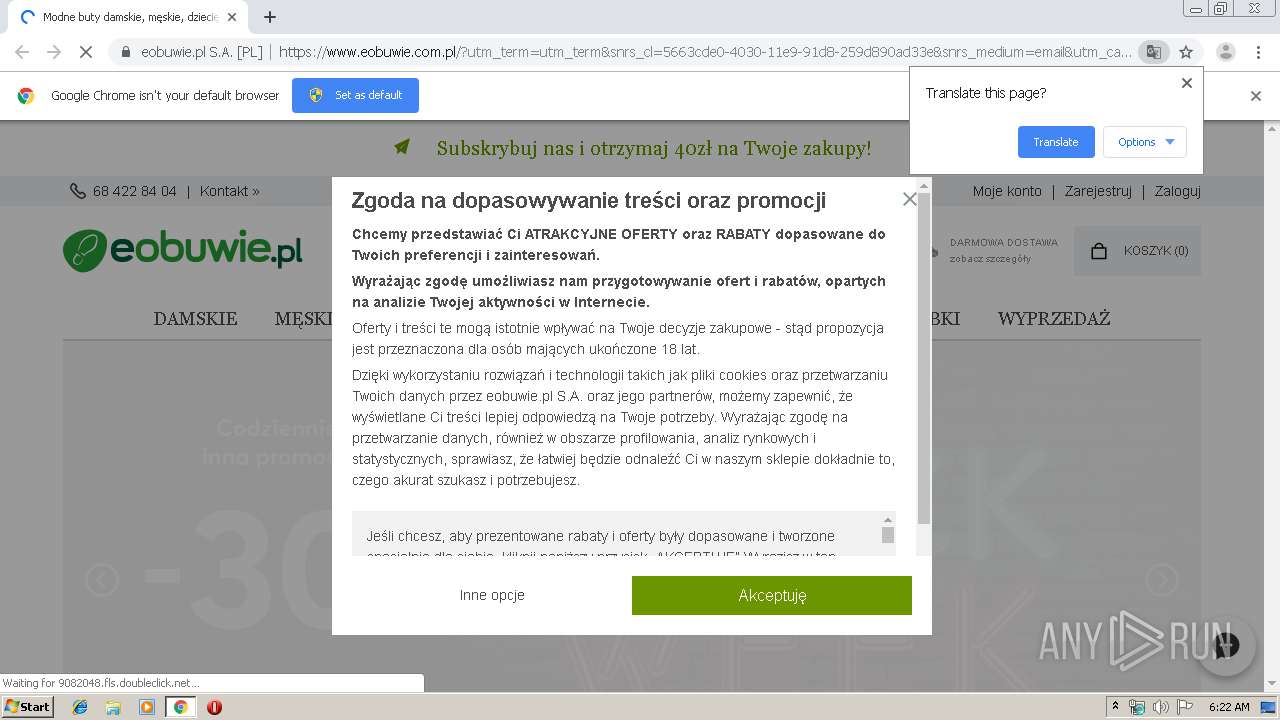
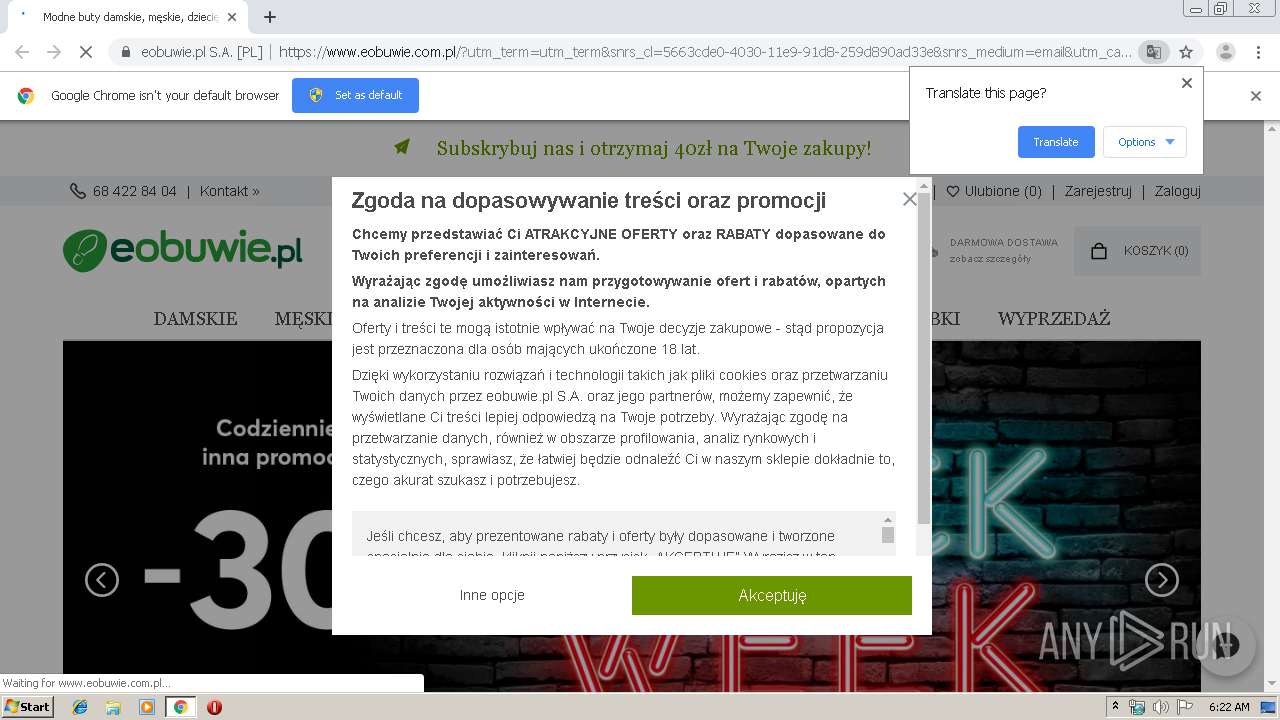
| URL: | http://eobuwiepl.emaillabs.info.pl/click/?lt=aHR0cHM6Ly9zbnJsaW5rLXBhZ2UuY29tP3E9YUhSMGNITTZMeTkzZDNjdVpXOWlkWGRwWlM1amIyMHVjR3d2UDNWMGJWOTBaWEp0UFhWMGJWOTBaWEp0Sm5OdWNuTmZZMnc5TlRZMk0yTmtaVEF0TkRBek1DMHhNV1U1TFRreFpEZ3RNalU1WkRnNU1HRmtNek5sSm5OdWNuTmZiV1ZrYVhWdFBXVnRZV2xzSm5WMGJWOWpZVzF3WVdsbmJqMHlNREU1TVRFeU5GOWlkMTloYkd3bWRYUnRYMjFsWkdsMWJUMWxiV0ZwYkNaemJuSnpYMk53UFdKaFlUazBNVFppTFdNd1ltRXRORGd3TnkxaU5qQXdMVFJsWXpKbFpUVTNOVEkyTXlaemJuSnpYMmhsUFRFMU1qZ3lNelU1TURRbWRYUnRYM052ZFhKalpUMXplVzVsY21selpTWjFkRzFmWTI5dWRHVnVkRDEyWVhKcFlXNTBYMkVtYzI1eWMxOXVQVEVtYzI1eWMxOWhZM1JwYjI0OWJtVjNjMnhsZEhSbGNpNWpiR2xqYXlaemJuSnpYMk5oZEdWbmIzSjVQV05zYVdWdWRDNWZSRVZXU1VORlh5NWljbTkzYzJWeUxtMWhhV3dtYzI1eWMxOTJZWEk5TVRVek5EYzNOUT09Jmg9OTZkNTgzZjQ1ZmY3ZjNkMjQ0OTM0MzIxZGNiMDQ1MDN8YzNsdVpYSnBjMlV1UlUxQlNVdzZZbUZoT1RReE5tSXRZekJpWVMwME9EQTNMV0kyTURBdE5HVmpNbVZsTlRjMU1qWXpPalUyTmpOalpHVXdMVFF3TXpBdE1URmxPUzA1TVdRNExUSTFPV1E0T1RCaFpETXpaUzR4TlRNME56YzFRR1Z0WVdsc2JHRmljeTV1WlhRdWNHeDhVM1Z1TENBeU5DQk9iM1lnTWpBeE9TQXdPVG8wTWpveE5TQkhUVlI4WVc1dVlTNXliMmRoYkhOcllVQmllbmRpYXk1d2JIdzJMbVZ2WW5WM2FXVndiQzV6YlhSd2ZISmxaR2R5YVdRME1ud3c= |
| Full analysis: | https://app.any.run/tasks/c68c8d92-c917-40e9-902e-ef1a670dd0df |
| Verdict: | Suspicious activity |
| Analysis date: | November 27, 2019, 06:21:50 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | F2C866E2A2508EA1ABBAA0411D7F1DD7 |
| SHA1: | B96E43942146B2E944B5B643EC33AA1C9F12CF9C |
| SHA256: | CE7094EB5BE9911EC2F35404EC74B54759FC17E21ABD56DE0F530C5F7AFE4A2A |
| SSDEEP: | 24:5fLNs1BUArKn238EV36y4nSOUGQ18AFWLhCVjS3u6NOYHZXOD:BLfAq23b3v4nSOdunMhCV0oYHp2 |
MALICIOUS
No malicious indicators.SUSPICIOUS
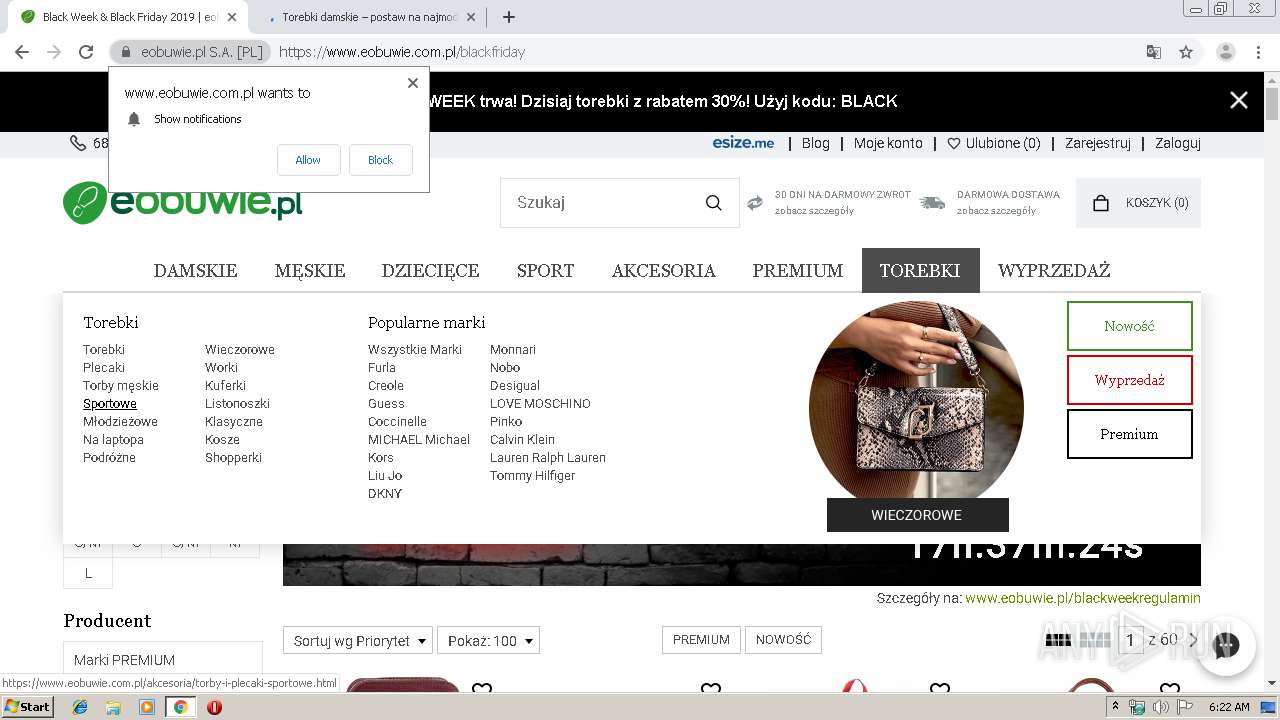
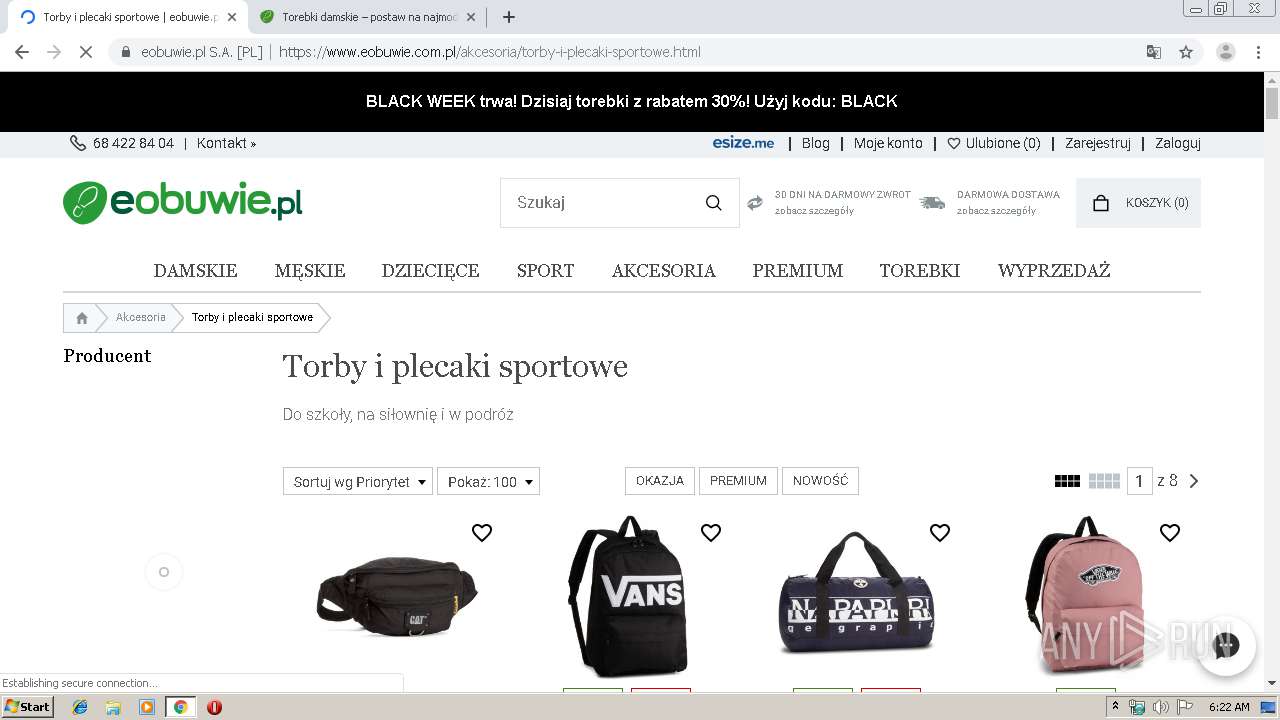
Modifies files in Chrome extension folder
- chrome.exe (PID: 1972)
INFO
Reads the hosts file
- chrome.exe (PID: 4080)
- chrome.exe (PID: 1972)
Application launched itself
- chrome.exe (PID: 1972)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
68
Monitored processes
32
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 324 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1032,2249942421517559100,7704110724703682479,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=2039811186927839420 --mojo-platform-channel-handle=3844 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 332 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1032,2249942421517559100,7704110724703682479,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=14808916769953114474 --mojo-platform-channel-handle=4292 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 388 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1032,2249942421517559100,7704110724703682479,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=237458669214544365 --renderer-client-id=24 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4672 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 436 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1032,2249942421517559100,7704110724703682479,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=16267451932781520501 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2248 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 564 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1032,2249942421517559100,7704110724703682479,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=11281012604383789767 --renderer-client-id=8 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3048 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 928 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1032,2249942421517559100,7704110724703682479,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=4444171863938269038 --renderer-client-id=17 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3960 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1212 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1032,2249942421517559100,7704110724703682479,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=14809673558442263112 --renderer-client-id=27 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4680 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1244 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=1928 --on-initialized-event-handle=312 --parent-handle=316 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1328 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1032,2249942421517559100,7704110724703682479,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=6241522361173564882 --mojo-platform-channel-handle=4244 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1740 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1032,2249942421517559100,7704110724703682479,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=5806234285058147832 --mojo-platform-channel-handle=3840 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
631
Read events
527
Write events
99
Delete events
5
Modification events
| (PID) Process: | (1972) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1972) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1972) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (1972) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (1972) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1244) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 1972-13219309332578875 |
Value: 259 | |||
| (PID) Process: | (1972) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (1972) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (1972) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1512-13197841398593750 |
Value: 0 | |||
| (PID) Process: | (1972) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1972-13219309332578875 |
Value: 259 | |||
Executable files
0
Suspicious files
99
Text files
238
Unknown types
9
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1972 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1972 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1972 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1972 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF39b9d5.TMP | — | |
MD5:— | SHA256:— | |||
| 1972 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\20b02b6e-1ea3-4e86-bbaa-06476e849f40.tmp | — | |
MD5:— | SHA256:— | |||
| 1972 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 1972 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1972 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 1972 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1972 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
79
DNS requests
51
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4080 | chrome.exe | GET | 302 | 185.143.32.28:80 | http://eobuwiepl.emaillabs.info.pl/click/?lt=aHR0cHM6Ly9zbnJsaW5rLXBhZ2UuY29tP3E9YUhSMGNITTZMeTkzZDNjdVpXOWlkWGRwWlM1amIyMHVjR3d2UDNWMGJWOTBaWEp0UFhWMGJWOTBaWEp0Sm5OdWNuTmZZMnc5TlRZMk0yTmtaVEF0TkRBek1DMHhNV1U1TFRreFpEZ3RNalU1WkRnNU1HRmtNek5sSm5OdWNuTmZiV1ZrYVhWdFBXVnRZV2xzSm5WMGJWOWpZVzF3WVdsbmJqMHlNREU1TVRFeU5GOWlkMTloYkd3bWRYUnRYMjFsWkdsMWJUMWxiV0ZwYkNaemJuSnpYMk53UFdKaFlUazBNVFppTFdNd1ltRXRORGd3TnkxaU5qQXdMVFJsWXpKbFpUVTNOVEkyTXlaemJuSnpYMmhsUFRFMU1qZ3lNelU1TURRbWRYUnRYM052ZFhKalpUMXplVzVsY21selpTWjFkRzFmWTI5dWRHVnVkRDEyWVhKcFlXNTBYMkVtYzI1eWMxOXVQVEVtYzI1eWMxOWhZM1JwYjI0OWJtVjNjMnhsZEhSbGNpNWpiR2xqYXlaemJuSnpYMk5oZEdWbmIzSjVQV05zYVdWdWRDNWZSRVZXU1VORlh5NWljbTkzYzJWeUxtMWhhV3dtYzI1eWMxOTJZWEk5TVRVek5EYzNOUT09Jmg9OTZkNTgzZjQ1ZmY3ZjNkMjQ0OTM0MzIxZGNiMDQ1MDN8YzNsdVpYSnBjMlV1UlUxQlNVdzZZbUZoT1RReE5tSXRZekJpWVMwME9EQTNMV0kyTURBdE5HVmpNbVZsTlRjMU1qWXpPalUyTmpOalpHVXdMVFF3TXpBdE1URmxPUzA1TVdRNExUSTFPV1E0T1RCaFpETXpaUzR4TlRNME56YzFRR1Z0WVdsc2JHRmljeTV1WlhRdWNHeDhVM1Z1TENBeU5DQk9iM1lnTWpBeE9TQXdPVG8wTWpveE5TQkhUVlI4WVc1dVlTNXliMmRoYkhOcllVQmllbmRpYXk1d2JIdzJMbVZ2WW5WM2FXVndiQzV6YlhSd2ZISmxaR2R5YVdRME1ud3c= | PL | — | — | suspicious |
4080 | chrome.exe | GET | 200 | 93.184.220.29:80 | http://status.geotrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTIyCPRUzvKHRw7iRE1lF%2BfcLu%2FjgQUypJnUmHervy6Iit%2FHIdMJftvmVgCEAVc3f6nEdOC%2FZ5nH%2FOglC8%3D | US | der | 471 b | whitelisted |
4080 | chrome.exe | GET | 302 | 172.217.21.206:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 514 b | whitelisted |
4080 | chrome.exe | GET | 302 | 172.217.21.206:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 509 b | whitelisted |
4080 | chrome.exe | GET | 200 | 173.194.163.74:80 | http://r4---sn-4g5ednls.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx?cms_redirect=yes&mip=89.187.165.57&mm=28&mn=sn-4g5ednls&ms=nvh&mt=1574835685&mv=m&mvi=3&pl=24&shardbypass=yes | US | crx | 293 Kb | whitelisted |
4080 | chrome.exe | GET | 200 | 173.194.151.233:80 | http://r3---sn-4g5edn7s.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=89.187.165.57&mm=28&mn=sn-4g5edn7s&ms=nvh&mt=1574835685&mv=m&mvi=2&pl=24&shardbypass=yes | US | crx | 862 Kb | whitelisted |
4080 | chrome.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfqhLjKLEJQZPin0KCzkdAQpVYowQUsT7DaQP4v0cB1JgmGggC72NkK8MCEAP%2B7xu1tkg0miCVD4vGl1M%3D | US | der | 471 b | whitelisted |
4080 | chrome.exe | GET | 200 | 93.184.221.240:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 57.4 Kb | whitelisted |
4080 | chrome.exe | GET | 200 | 143.204.208.222:80 | http://x.ss2.us/x.cer | US | der | 1.27 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4080 | chrome.exe | 172.217.21.200:443 | www.googletagmanager.com | Google Inc. | US | whitelisted |
4080 | chrome.exe | 216.58.205.238:443 | clients1.google.com | Google Inc. | US | whitelisted |
4080 | chrome.exe | 2.16.186.81:443 | photorankapi-a.akamaihd.net | Akamai International B.V. | — | whitelisted |
4080 | chrome.exe | 172.217.21.202:443 | translate.googleapis.com | Google Inc. | US | whitelisted |
4080 | chrome.exe | 172.217.22.46:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
4080 | chrome.exe | 216.58.207.34:443 | www.googleadservices.com | Google Inc. | US | whitelisted |
4080 | chrome.exe | 172.217.18.166:443 | 9082048.fls.doubleclick.net | Google Inc. | US | whitelisted |
4080 | chrome.exe | 104.20.21.239:443 | rum-static.pingdom.net | Cloudflare Inc | US | shared |
4080 | chrome.exe | 212.77.100.251:443 | px.wp.pl | Wirtualna Polska S.A. | PL | unknown |
4080 | chrome.exe | 172.217.23.163:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
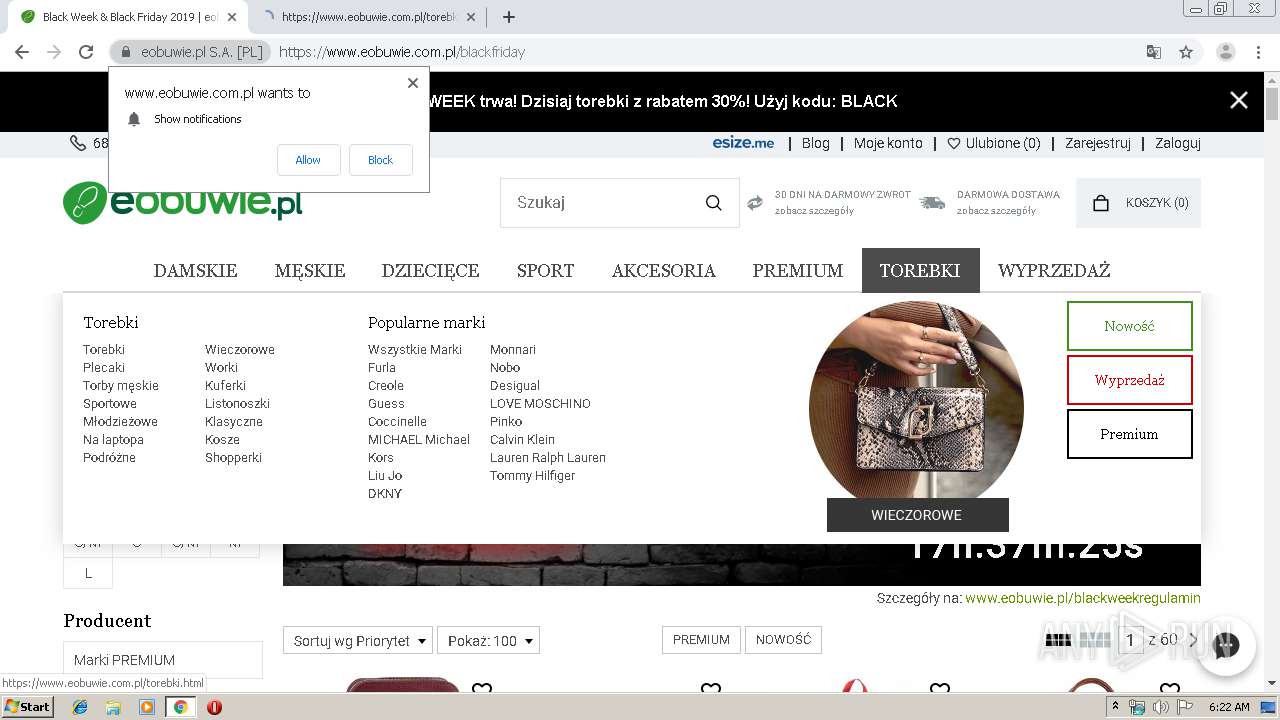
eobuwiepl.emaillabs.info.pl |
| suspicious |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
snrlink-page.com |
| suspicious |
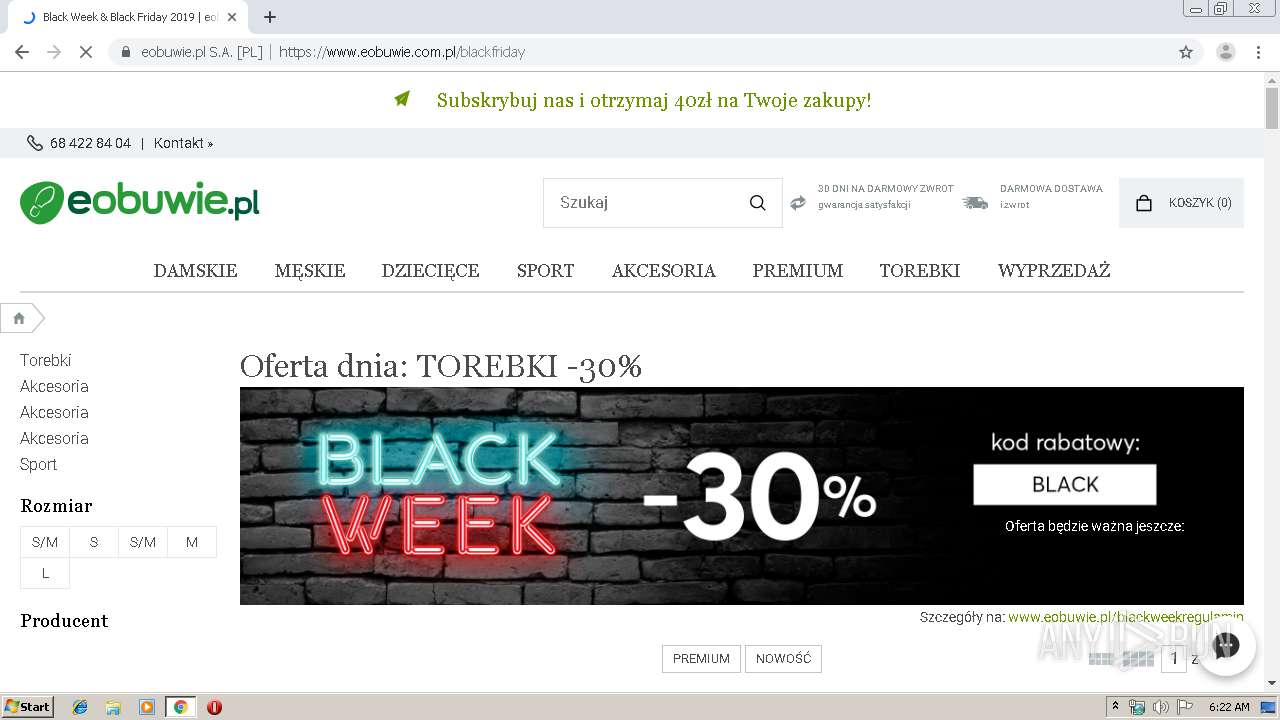
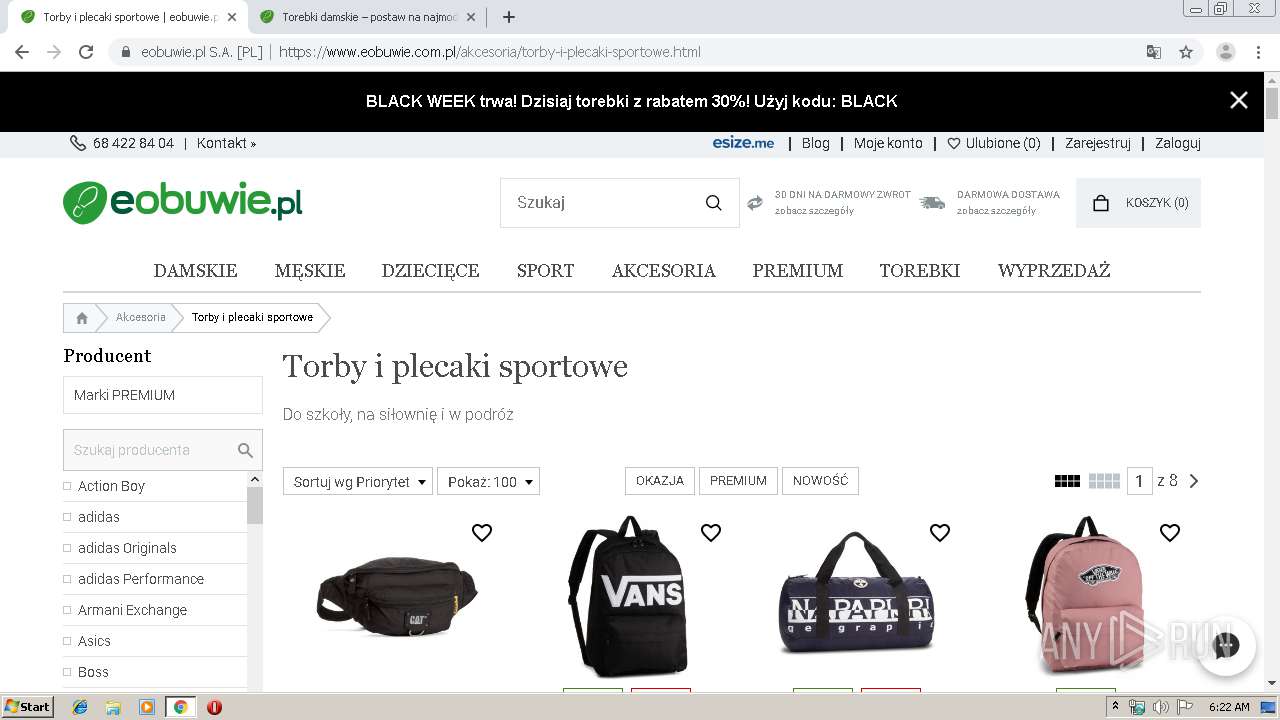
www.eobuwie.com.pl |
| unknown |
ocsp.digicert.com |
| whitelisted |
status.geotrust.com |
| whitelisted |
cdn.speedcurve.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
ai.synerise.com |
| unknown |
Threats
Process | Message |
|---|---|
chrome.exe | Error - |
chrome.exe | Too long restart command line passed |
chrome.exe |