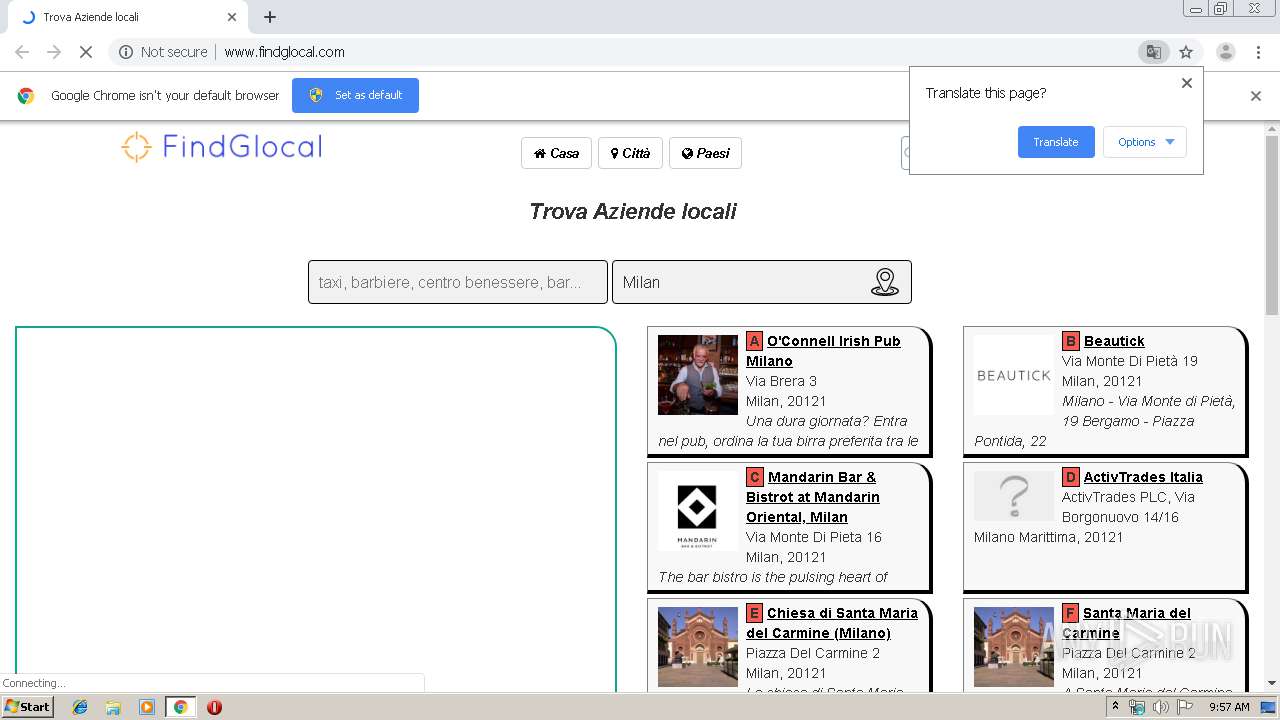
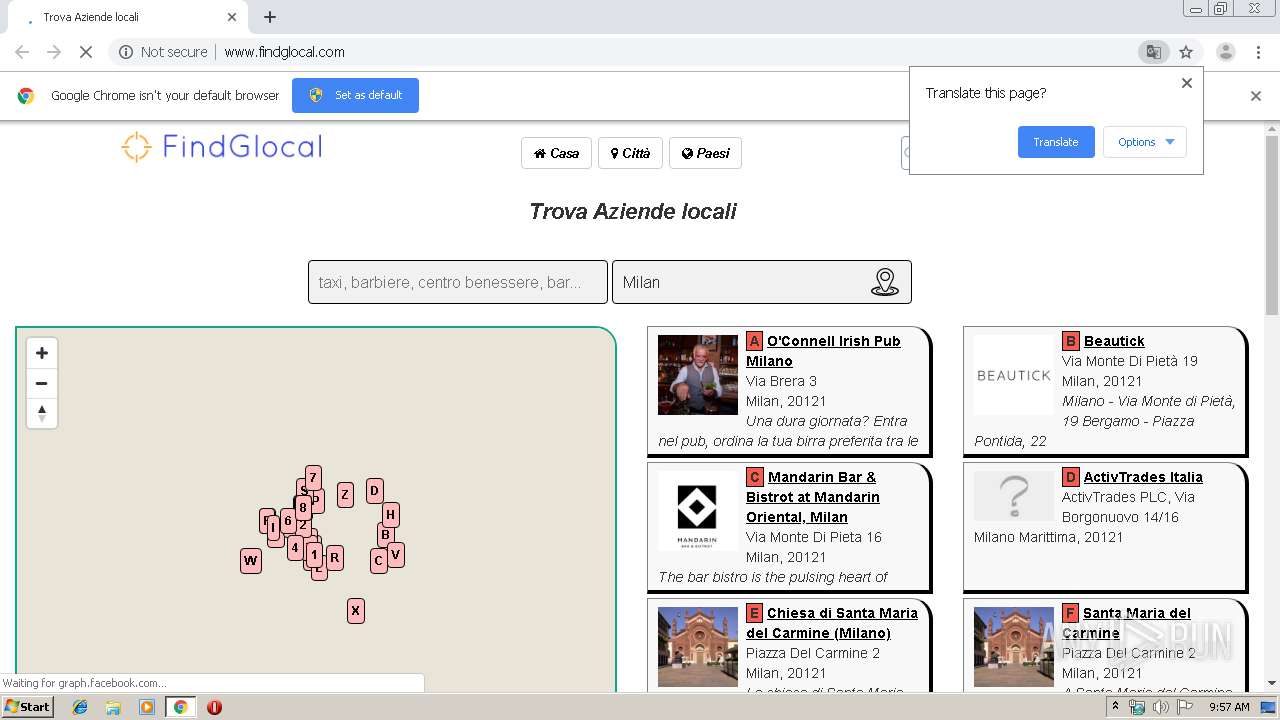
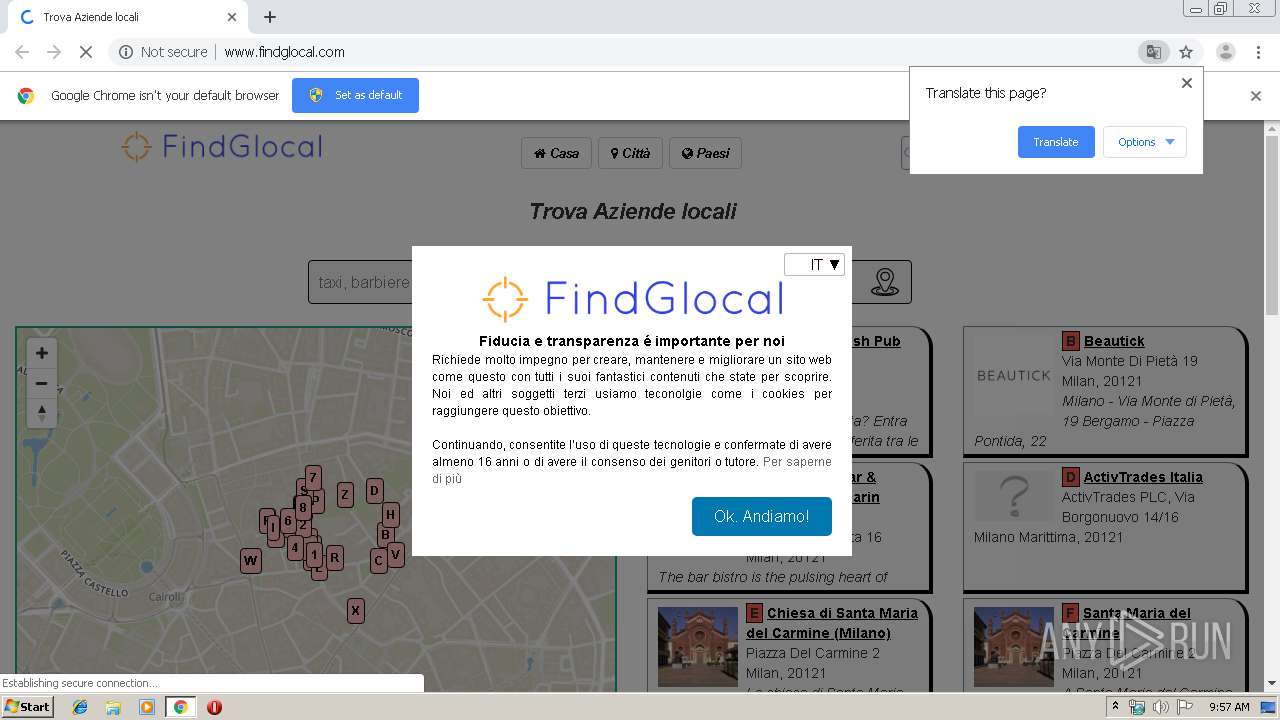
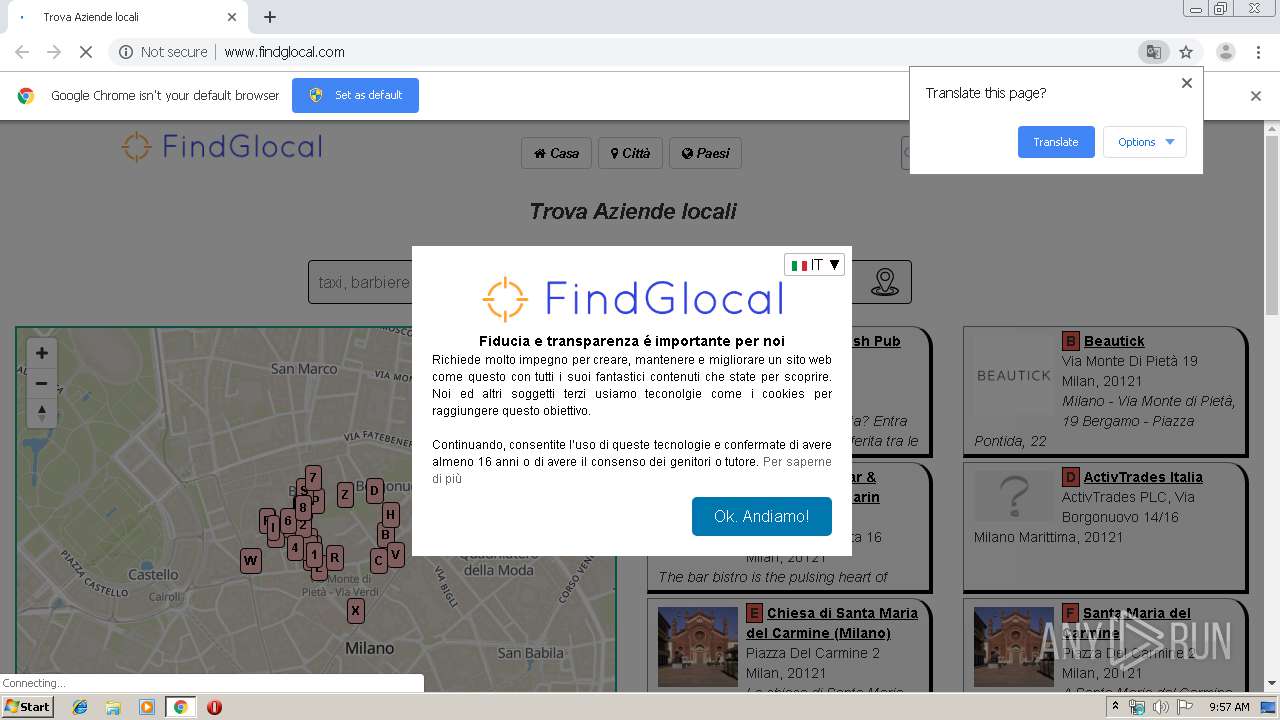
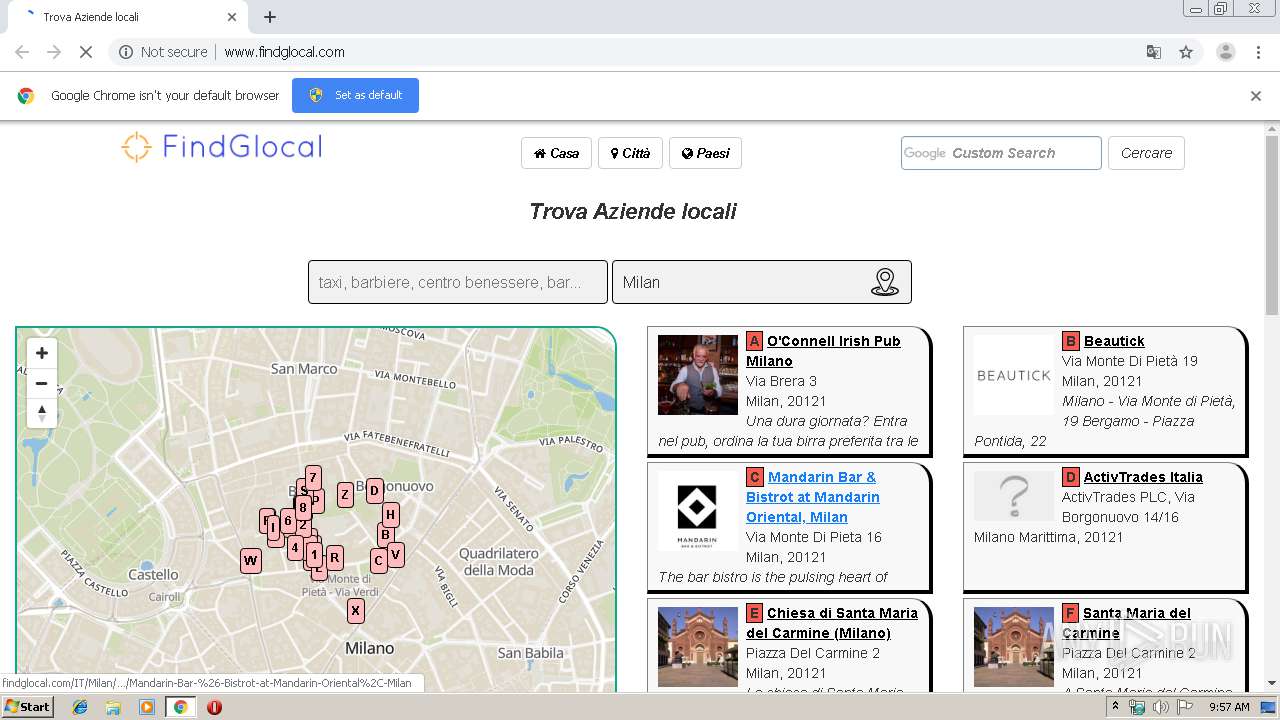
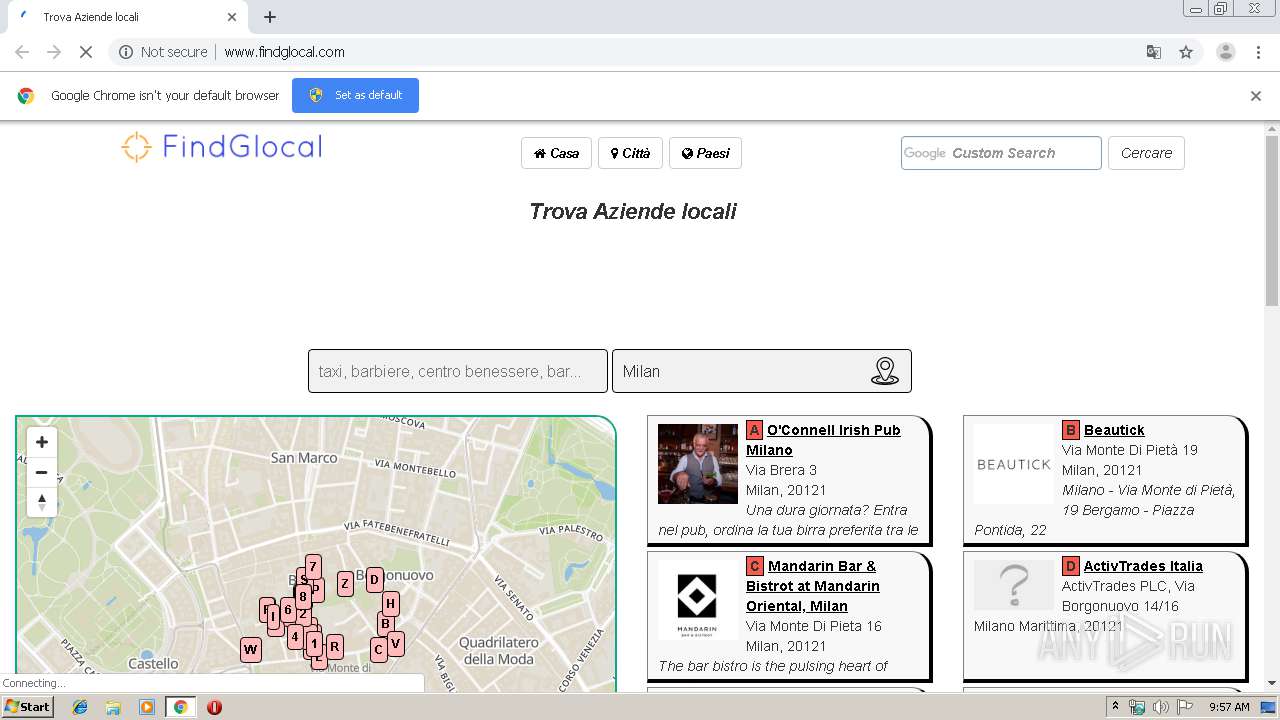
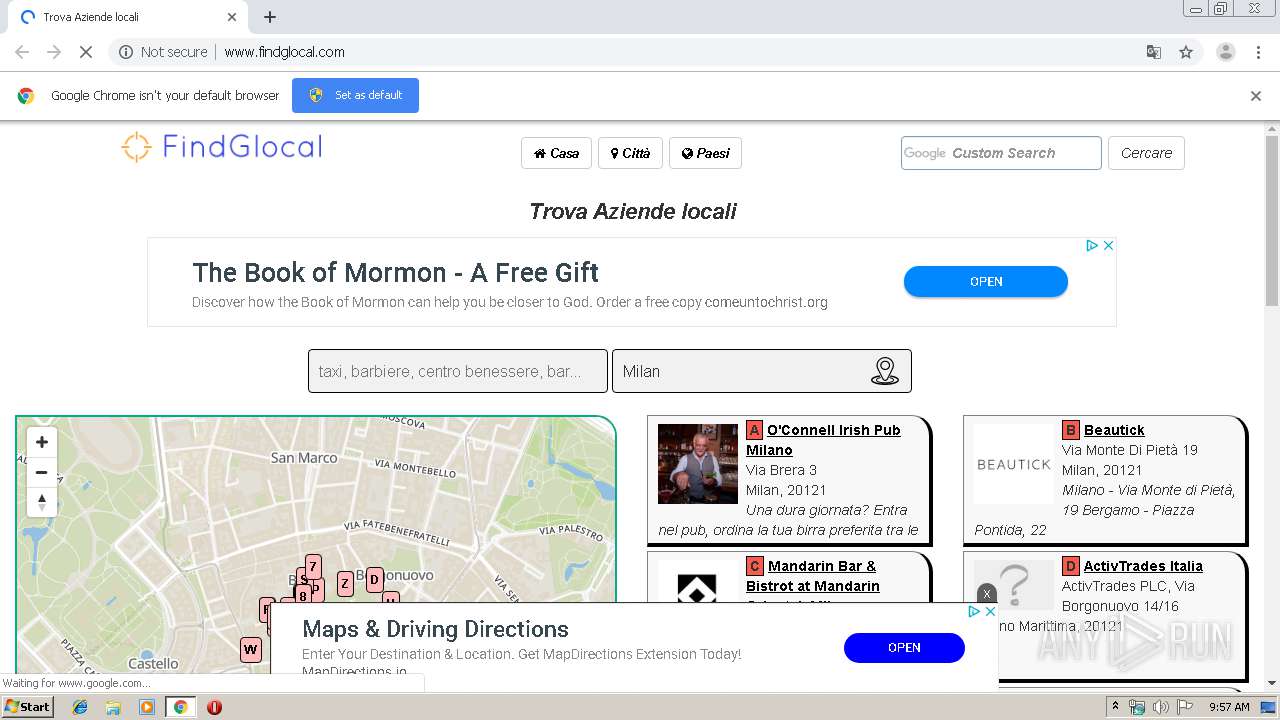
| URL: | http://findglocal.com |
| Full analysis: | https://app.any.run/tasks/91fd723b-03f8-4313-9872-60e0a806baa0 |
| Verdict: | Malicious activity |
| Analysis date: | October 14, 2019, 08:56:51 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 833F824ED711F471B993C13386438D38 |
| SHA1: | 1D4F0FB9869E4C6A7C1BAA4206F64D45B5CC89E7 |
| SHA256: | CE6F119DC759E5E7A0FDDB6ECCD9003A4AFF9EF53D40776A571F168C72225ACB |
| SSDEEP: | 3:N1KYaCEQ:CYaCp |
MALICIOUS
No malicious indicators.SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 1516)
INFO
Reads the hosts file
- chrome.exe (PID: 1944)
- chrome.exe (PID: 1516)
Application launched itself
- chrome.exe (PID: 1516)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
65
Monitored processes
30
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 324 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1040,13295521692237414746,15435509559317568879,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=9690185886620694927 --renderer-client-id=11 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2876 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 892 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1040,13295521692237414746,15435509559317568879,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=8536852449569640675 --renderer-client-id=18 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4084 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1044 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2472 --on-initialized-event-handle=312 --parent-handle=316 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1516 | "C:\Program Files\Google\Chrome\Application\chrome.exe" "http://findglocal.com" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1704 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1040,13295521692237414746,15435509559317568879,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=6756640542721043556 --mojo-platform-channel-handle=4644 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1768 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1040,13295521692237414746,15435509559317568879,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=7920889579327101781 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2260 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1904 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1040,13295521692237414746,15435509559317568879,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=7936090881908788998 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2408 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1936 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1040,13295521692237414746,15435509559317568879,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=9144911334776804961 --mojo-platform-channel-handle=4336 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1944 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1040,13295521692237414746,15435509559317568879,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=2511764545276832588 --mojo-platform-channel-handle=1672 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2156 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1040,13295521692237414746,15435509559317568879,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=7950935020222085529 --mojo-platform-channel-handle=4424 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
631
Read events
532
Write events
94
Delete events
5
Modification events
| (PID) Process: | (1516) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1516) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1516) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (1516) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (1516) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1044) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 1516-13215517026251500 |
Value: 259 | |||
| (PID) Process: | (1516) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (1516) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (1516) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1512-13197841398593750 |
Value: 0 | |||
| (PID) Process: | (1516) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
98
Text files
193
Unknown types
9
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1516 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1516 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1516 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF39a91b.TMP | — | |
MD5:— | SHA256:— | |||
| 1516 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\672d2f34-8206-48aa-b3f8-8541cf63694b.tmp | — | |
MD5:— | SHA256:— | |||
| 1516 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 1516 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1516 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1516 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 1516 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF39a8fc.TMP | text | |
MD5:— | SHA256:— | |||
| 1516 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
65
TCP/UDP connections
124
DNS requests
74
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1944 | chrome.exe | GET | 200 | 104.18.53.181:80 | http://www.findglocal.com/img/findglocal/logo.png | US | image | 14.1 Kb | malicious |
1944 | chrome.exe | GET | 200 | 104.18.53.181:80 | http://www.findglocal.com/ | US | html | 28.4 Kb | malicious |
1944 | chrome.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfqhLjKLEJQZPin0KCzkdAQpVYowQUsT7DaQP4v0cB1JgmGggC72NkK8MCEAx5qUSwjBGVIJJhX%2BJrHYM%3D | US | der | 471 b | whitelisted |
1944 | chrome.exe | GET | 200 | 52.222.157.67:80 | http://cdn.pubguru.com/pg.js | US | text | 44.2 Kb | whitelisted |
— | — | GET | 301 | 104.18.52.181:80 | http://findglocal.com/ | US | html | 234 b | whitelisted |
1944 | chrome.exe | GET | 200 | 104.18.53.181:80 | http://www.findglocal.com/js/util.js | US | text | 891 b | malicious |
1944 | chrome.exe | GET | 200 | 104.20.21.239:80 | http://rum-static.pingdom.net/pa-5b83e81ccea07b0016000001.js | US | text | 2.65 Kb | whitelisted |
1944 | chrome.exe | GET | 200 | 13.35.253.103:80 | http://m2d.m2.ai/pghb.findglocalhome.js | US | text | 85.4 Kb | shared |
1944 | chrome.exe | GET | 200 | 52.222.157.67:80 | http://cdn.pubguru.com/unified_vendor_list.json | US | text | 28.9 Kb | whitelisted |
1944 | chrome.exe | GET | 302 | 172.217.16.206:80 | http://www.google-analytics.com/r/collect?v=1&_v=j79&a=204646594&t=pageview&_s=1&dl=http%3A%2F%2Fwww.findglocal.com%2F&ul=en-us&de=UTF-8&dt=Trova%20Aziende%20locali&sd=24-bit&sr=1280x720&vp=1264x572&je=0&_u=YEBAAEAB~&jid=602687882&gjid=374755443&cid=199736542.1571043435&tid=UA-99108658-1&_gid=1725219588.1571043435&_r=1&cd1=&cd2=&cd3=&cd4=&z=38841873 | US | html | 415 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1944 | chrome.exe | 172.217.16.132:443 | www.google.com | Google Inc. | US | whitelisted |
1944 | chrome.exe | 104.20.21.239:80 | rum-static.pingdom.net | Cloudflare Inc | US | shared |
1944 | chrome.exe | 185.60.216.19:443 | static.xx.fbcdn.net | Facebook, Inc. | IE | whitelisted |
1944 | chrome.exe | 172.217.18.110:443 | cse.google.com | Google Inc. | US | whitelisted |
1944 | chrome.exe | 172.217.21.227:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
— | — | 104.18.52.181:80 | findglocal.com | Cloudflare Inc | US | shared |
1944 | chrome.exe | 216.58.207.77:443 | accounts.google.com | Google Inc. | US | whitelisted |
1944 | chrome.exe | 209.197.3.15:443 | maxcdn.bootstrapcdn.com | Highwinds Network Group, Inc. | US | whitelisted |
1944 | chrome.exe | 172.217.22.10:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
1944 | chrome.exe | 185.60.216.15:443 | graph.facebook.com | Facebook, Inc. | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
findglocal.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.findglocal.com |
| malicious |
maxcdn.bootstrapcdn.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
cdn.pubguru.com |
| whitelisted |
graph.facebook.com |
| whitelisted |
api.tiles.mapbox.com |
| suspicious |
ajax.googleapis.com |
| whitelisted |