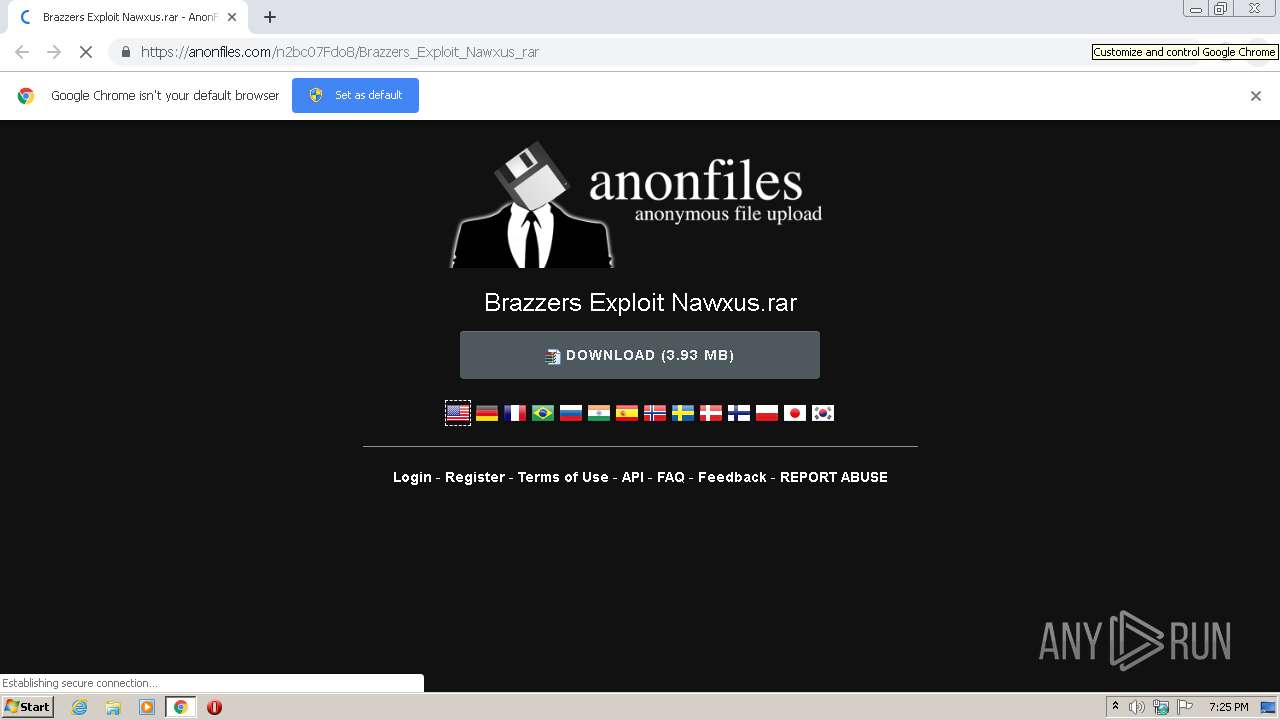
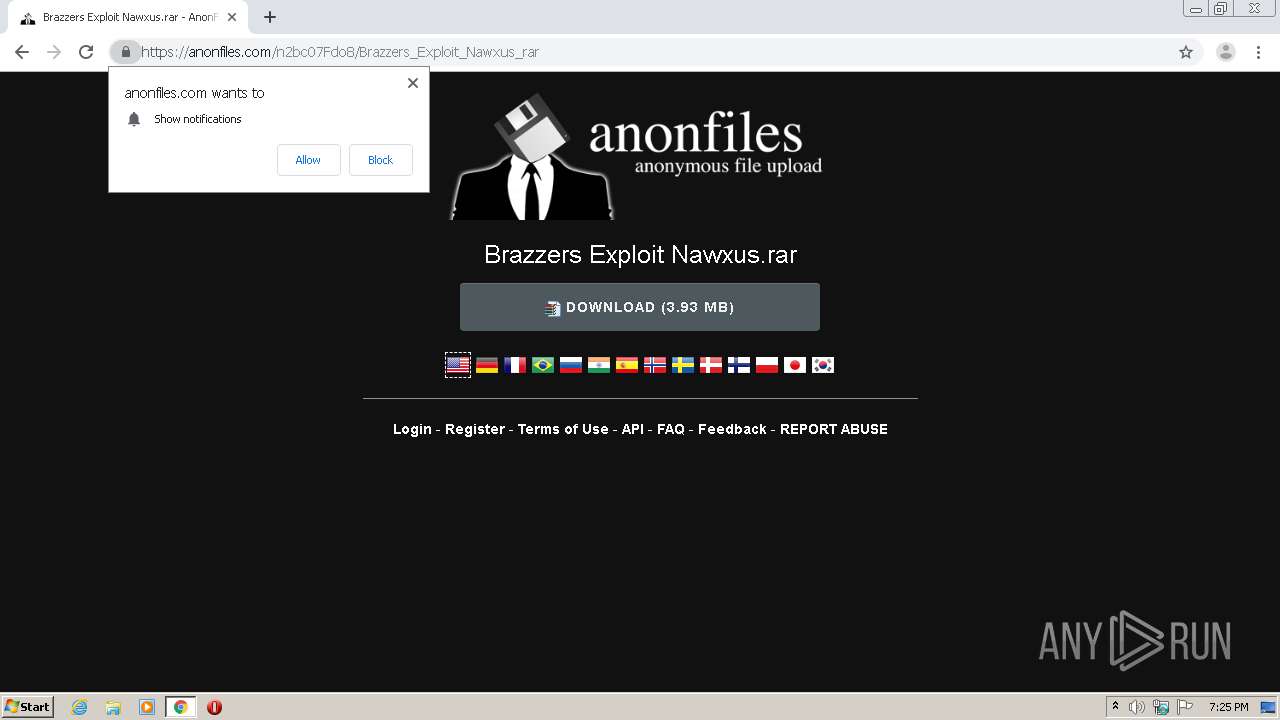
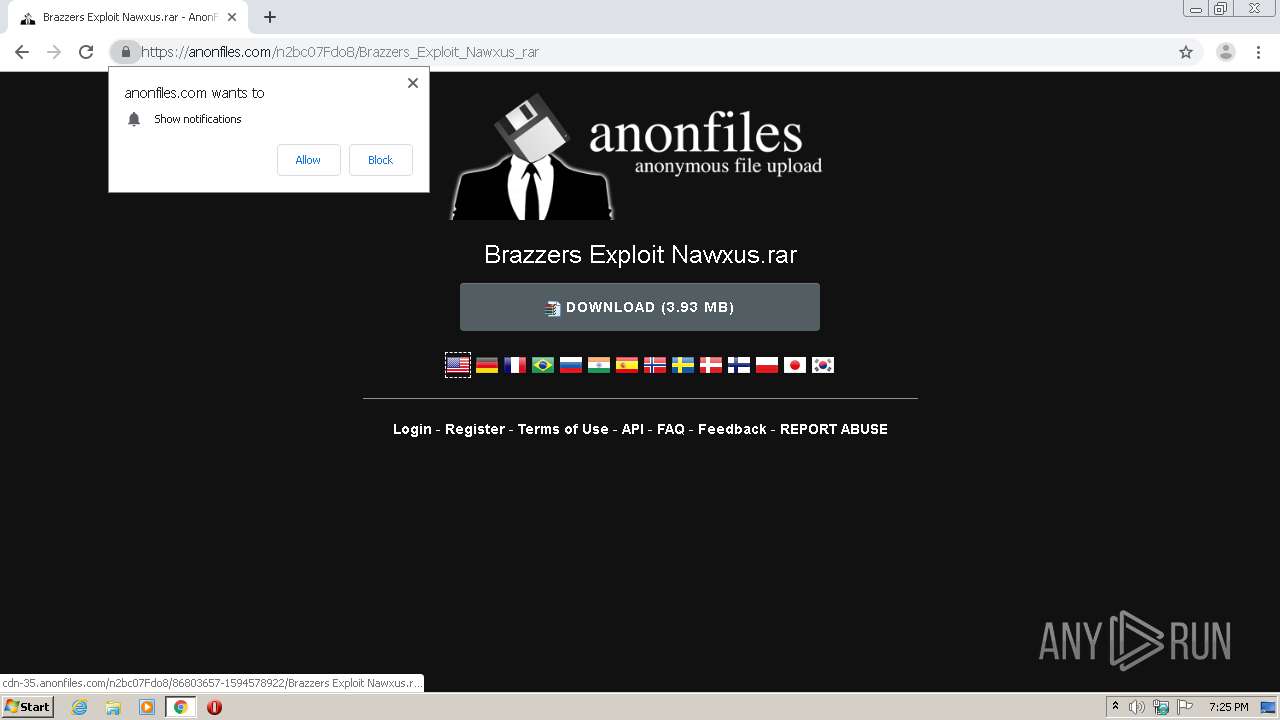
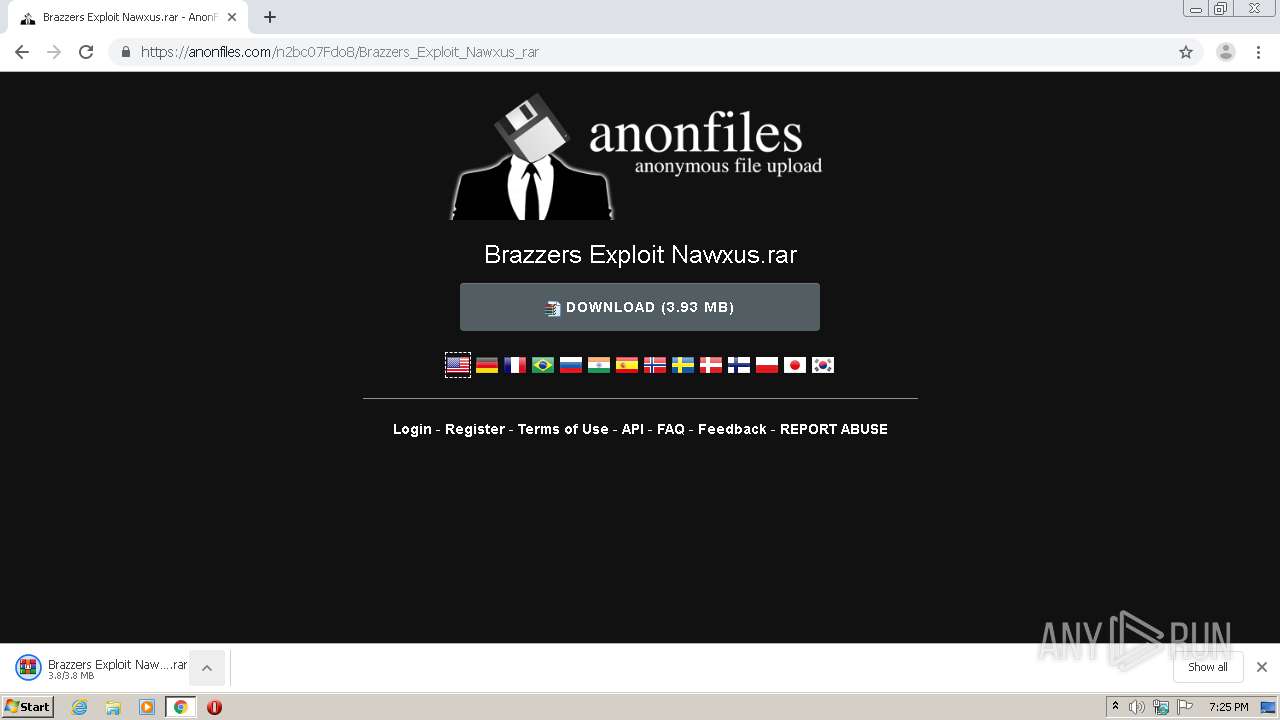
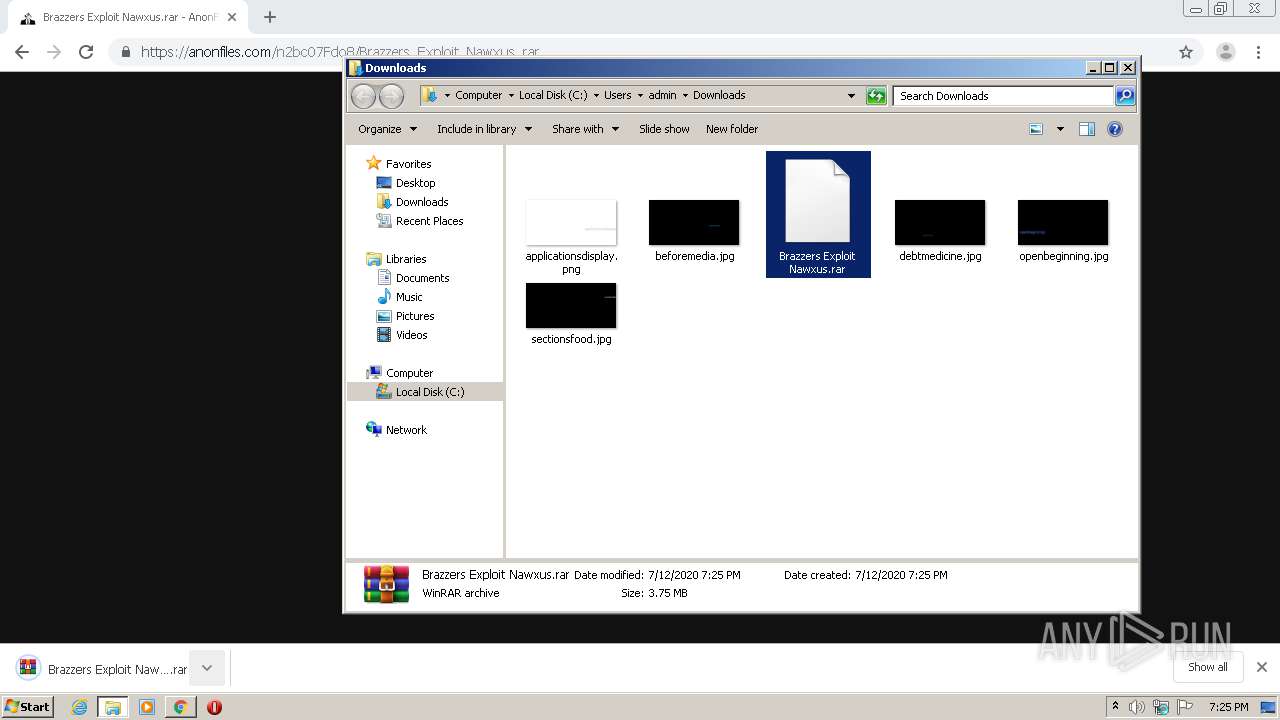
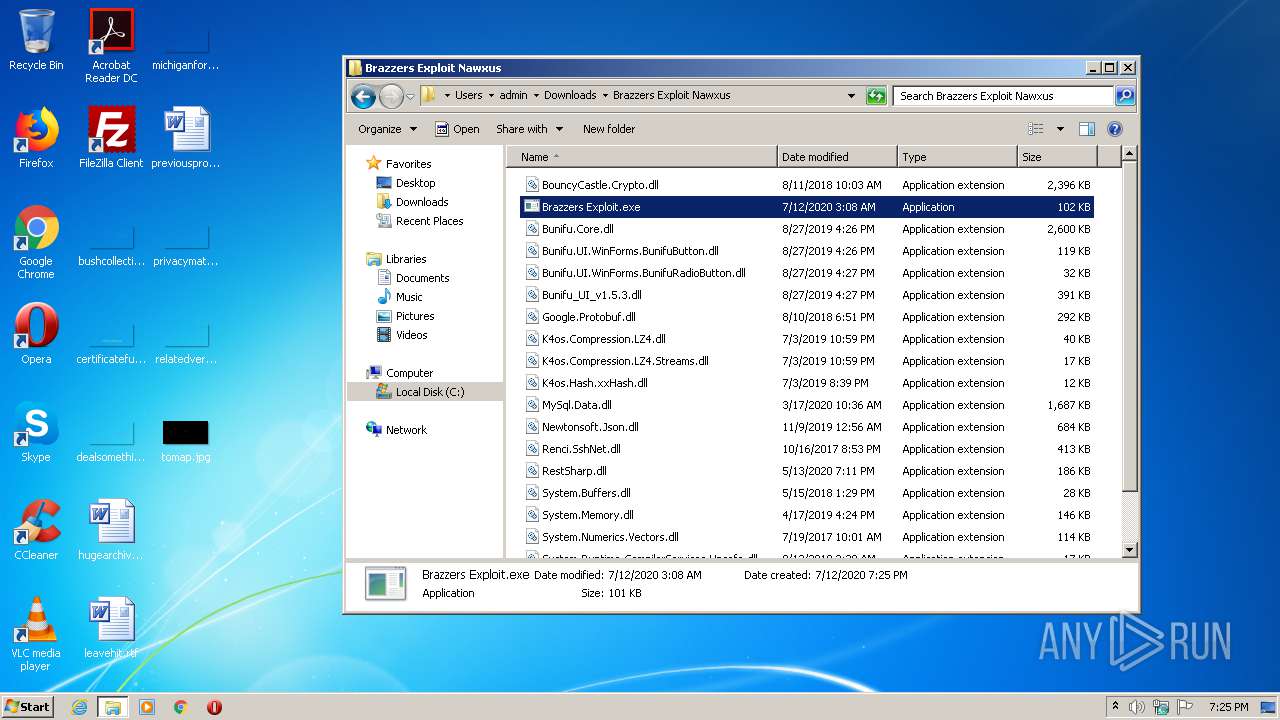
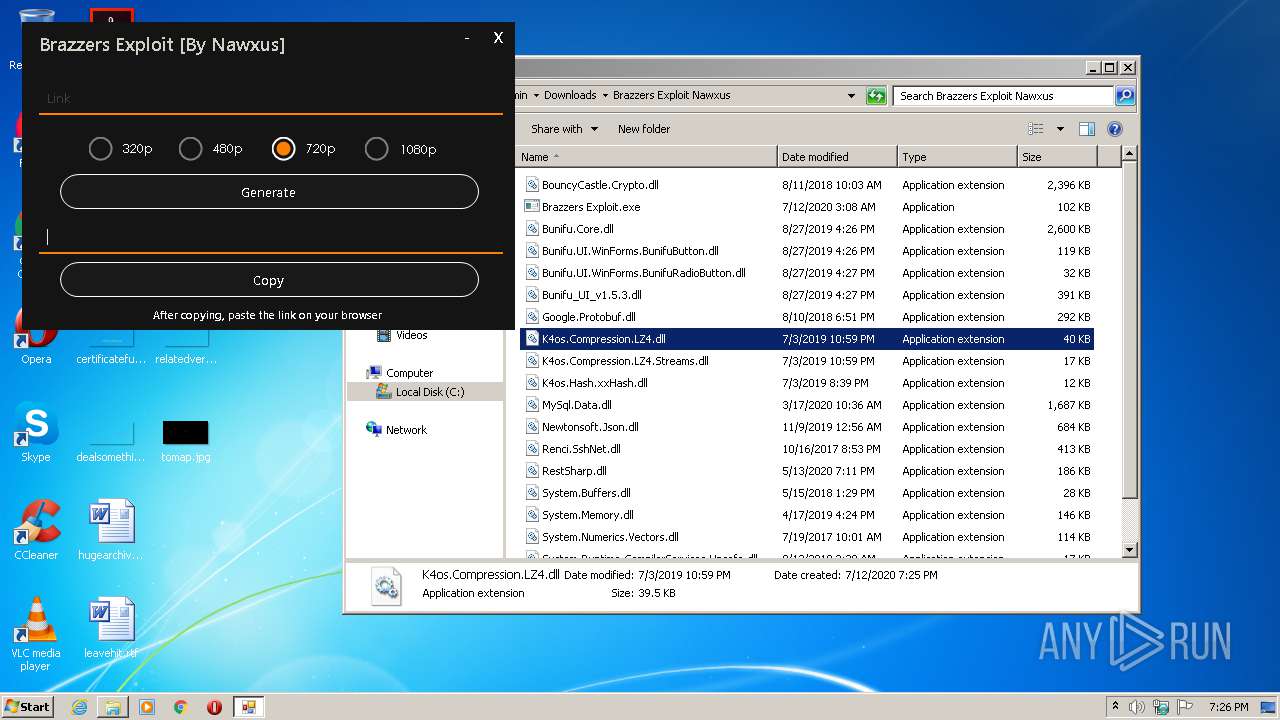
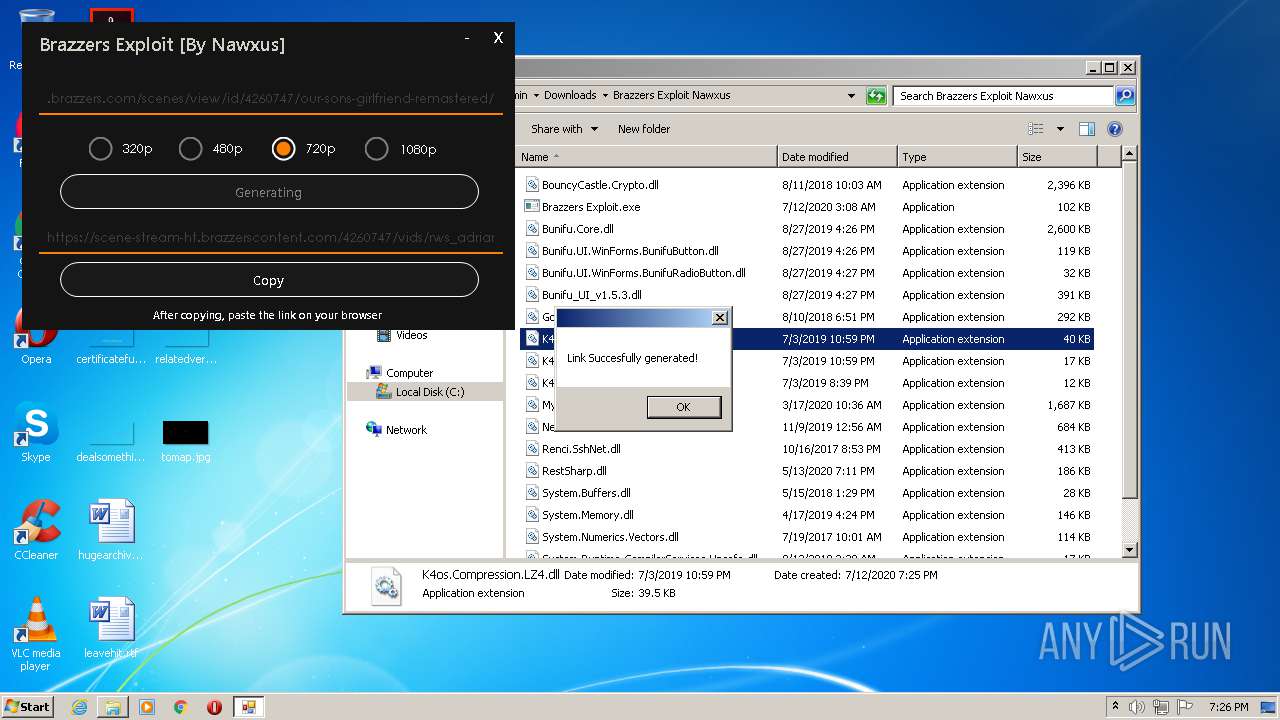
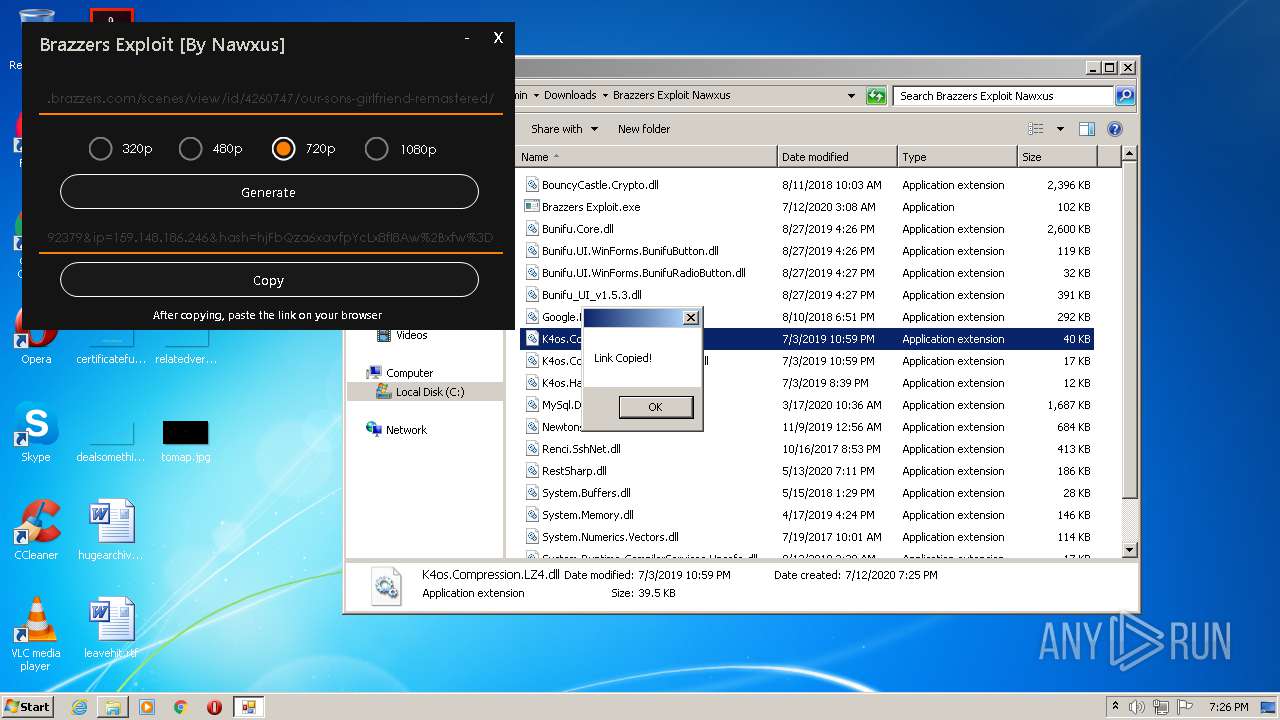
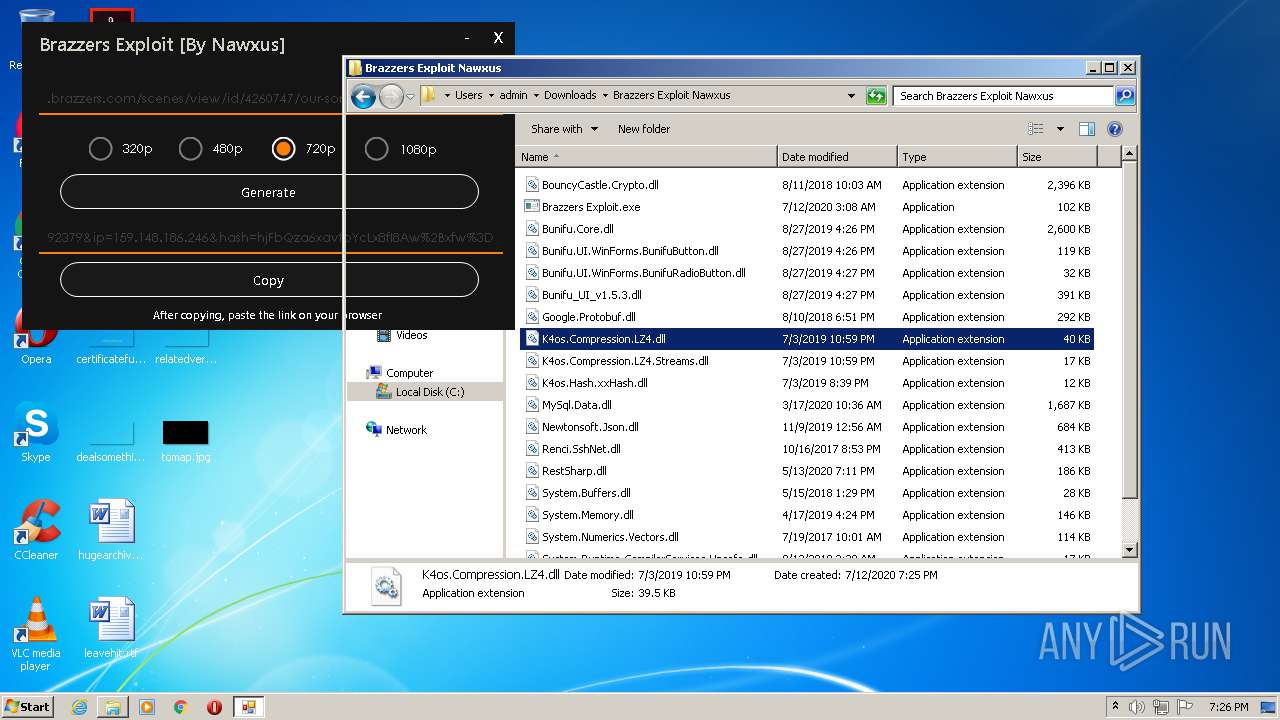
| URL: | https://anonfiles.com/n2bc07Fdo8/Brazzers_Exploit_Nawxus_rar |
| Full analysis: | https://app.any.run/tasks/264b039b-5aa8-4e6a-b767-34a462180aa9 |
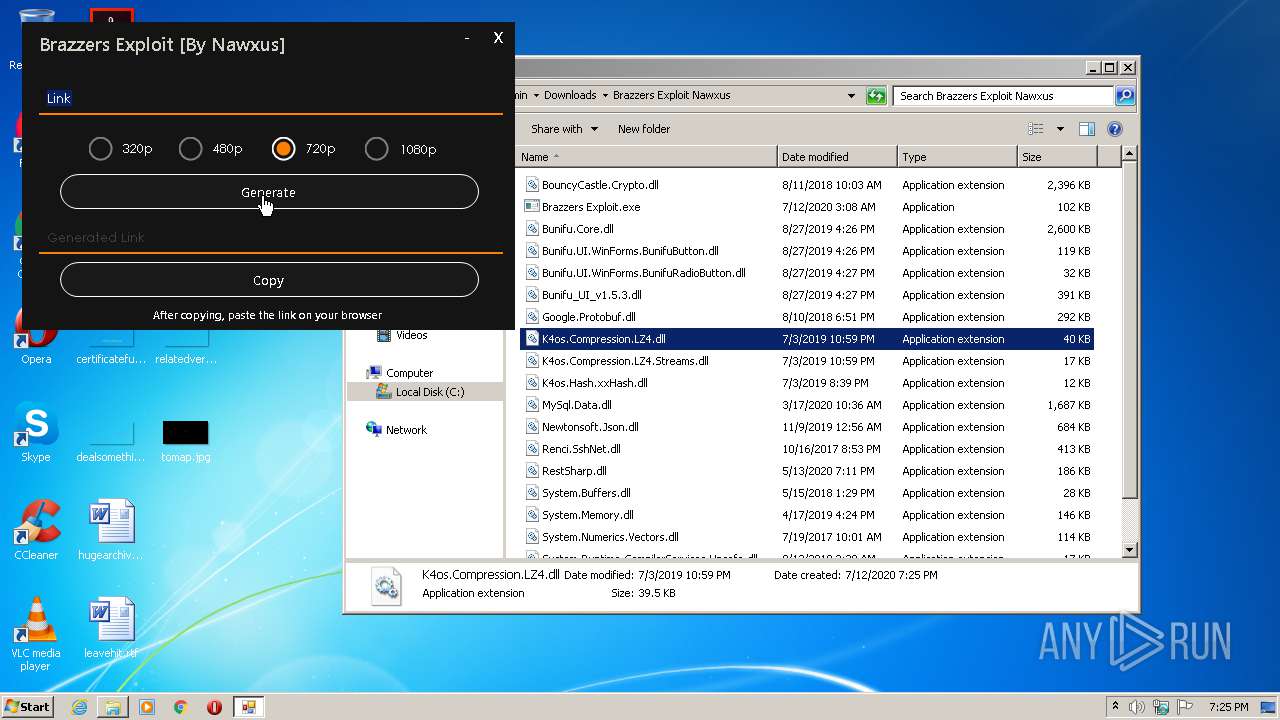
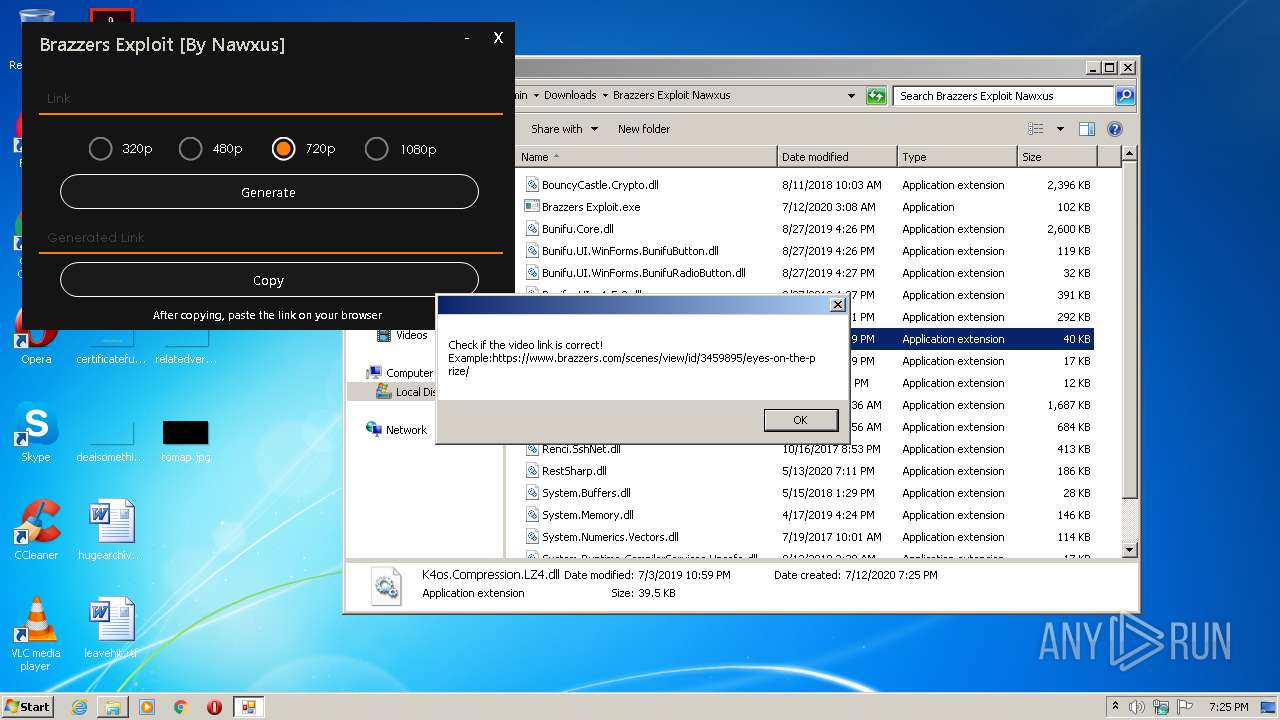
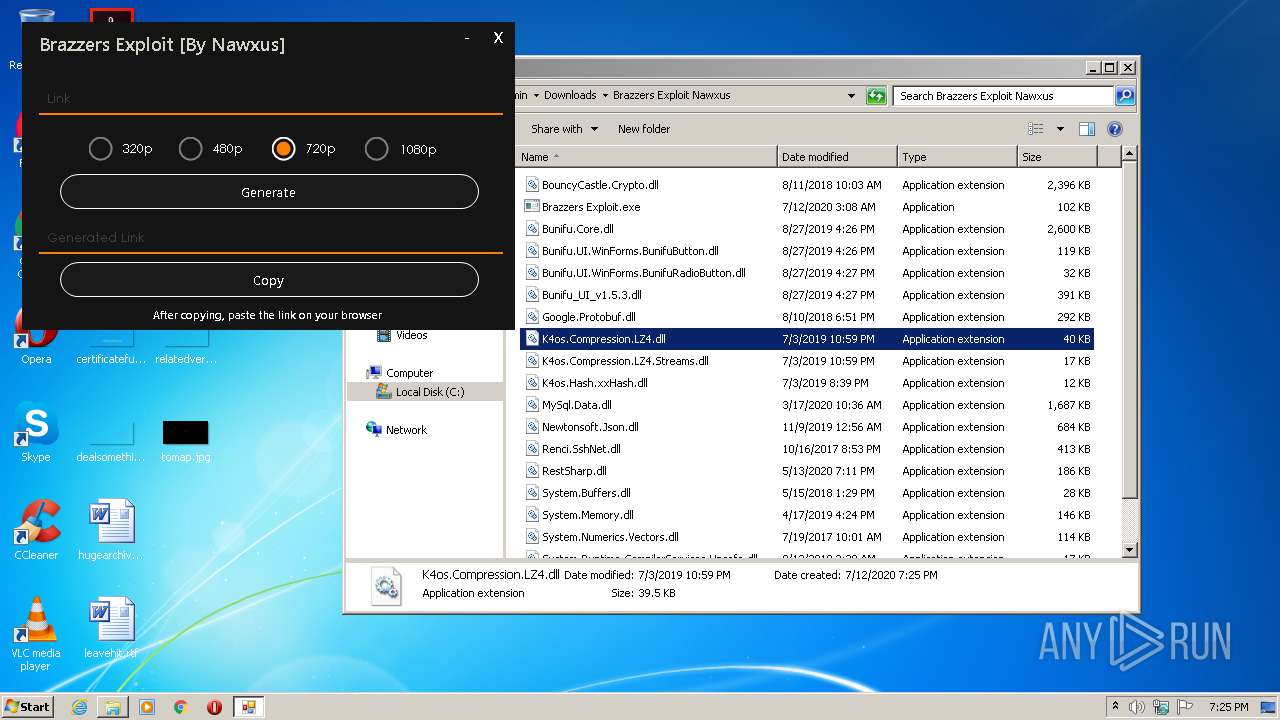
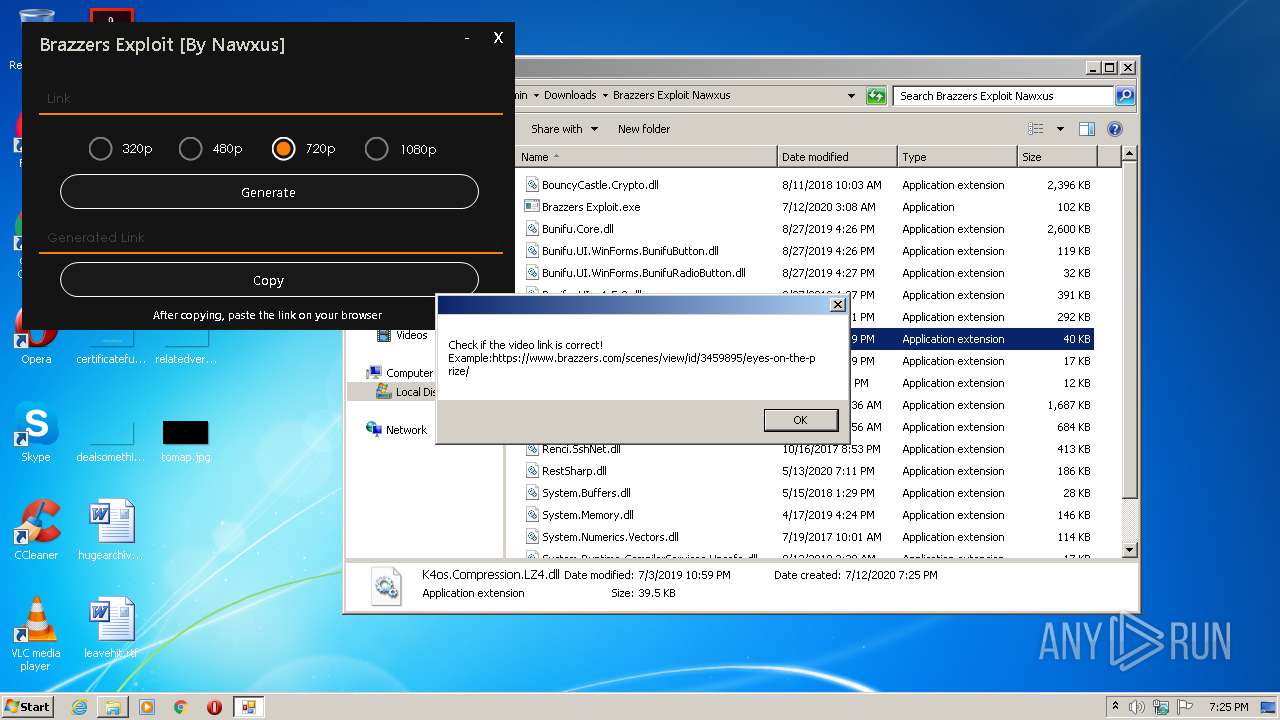
| Verdict: | Malicious activity |
| Analysis date: | July 12, 2020, 18:25:05 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | A2C36D33D933763B06CFC0E7E9E73DEC |
| SHA1: | 2D3AB857F39FFE441E0D5C09C30CBCEB08C04C31 |
| SHA256: | CE581CB780D9E482710837BBAFC100CC5C72AA29243DBA6D08F2482BFCD1DEA6 |
| SSDEEP: | 3:N8M2QXHFTUwXC0o+6O:2M2Lib6O |
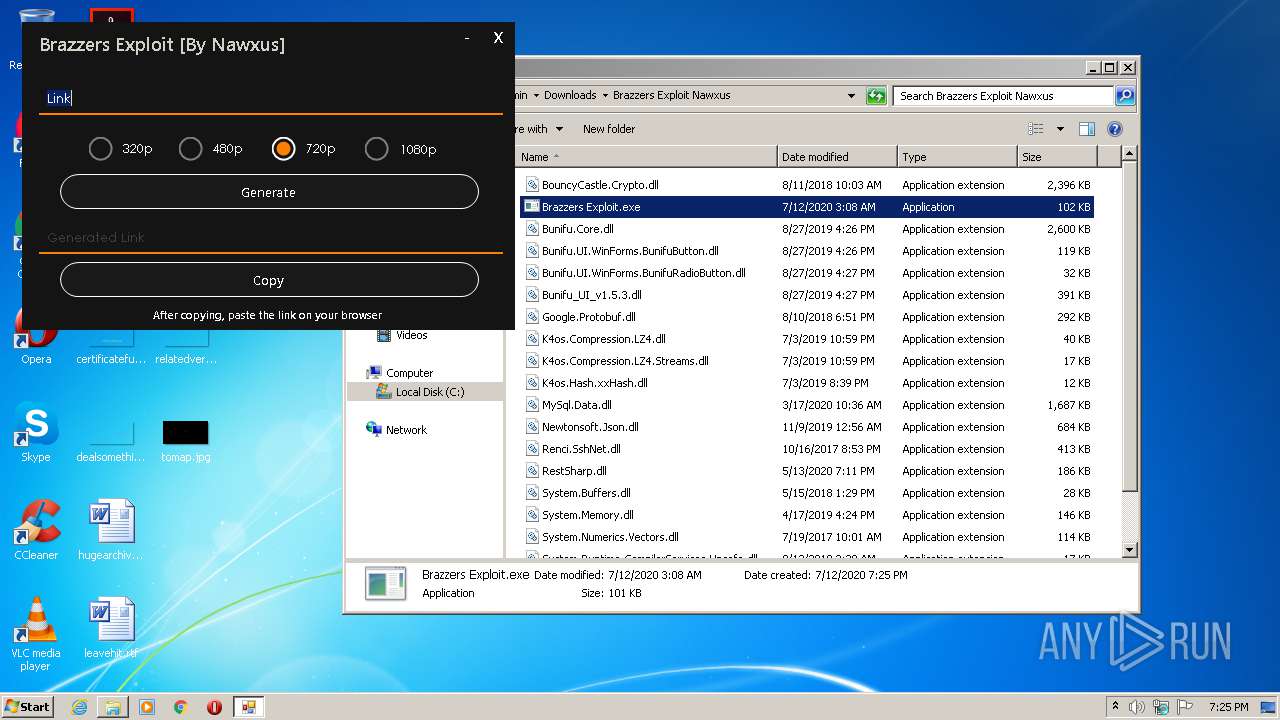
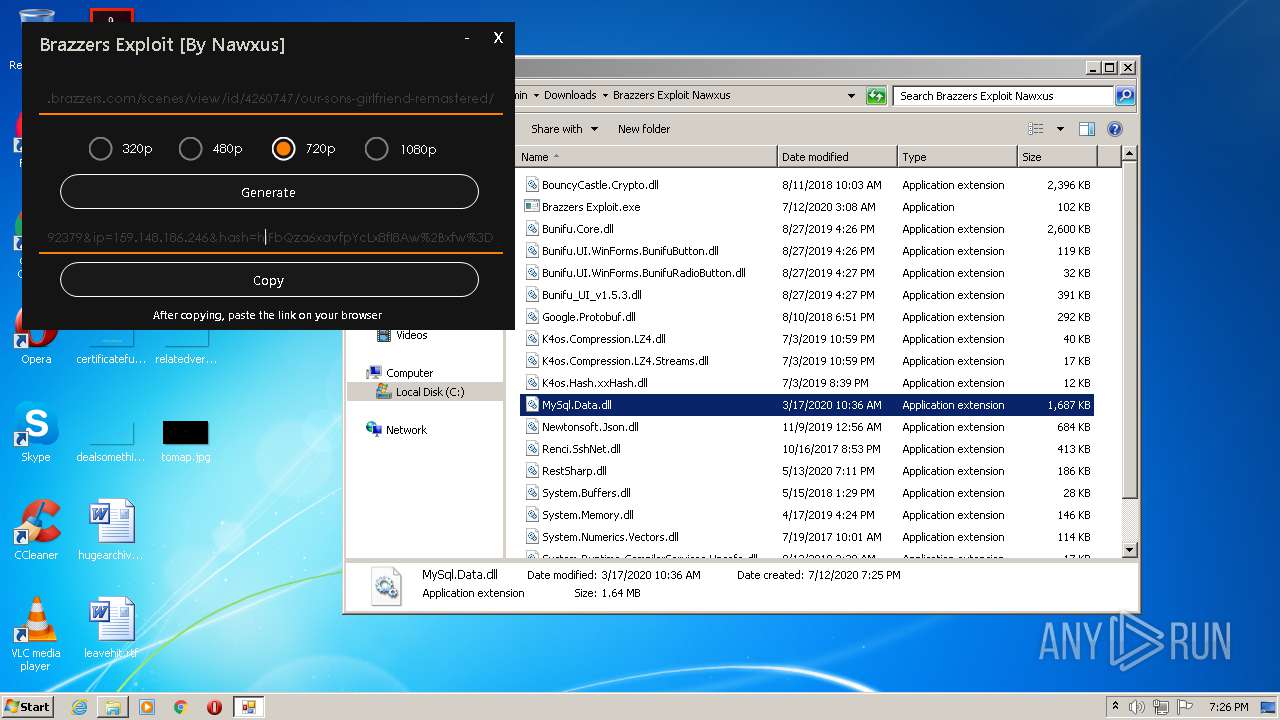
MALICIOUS
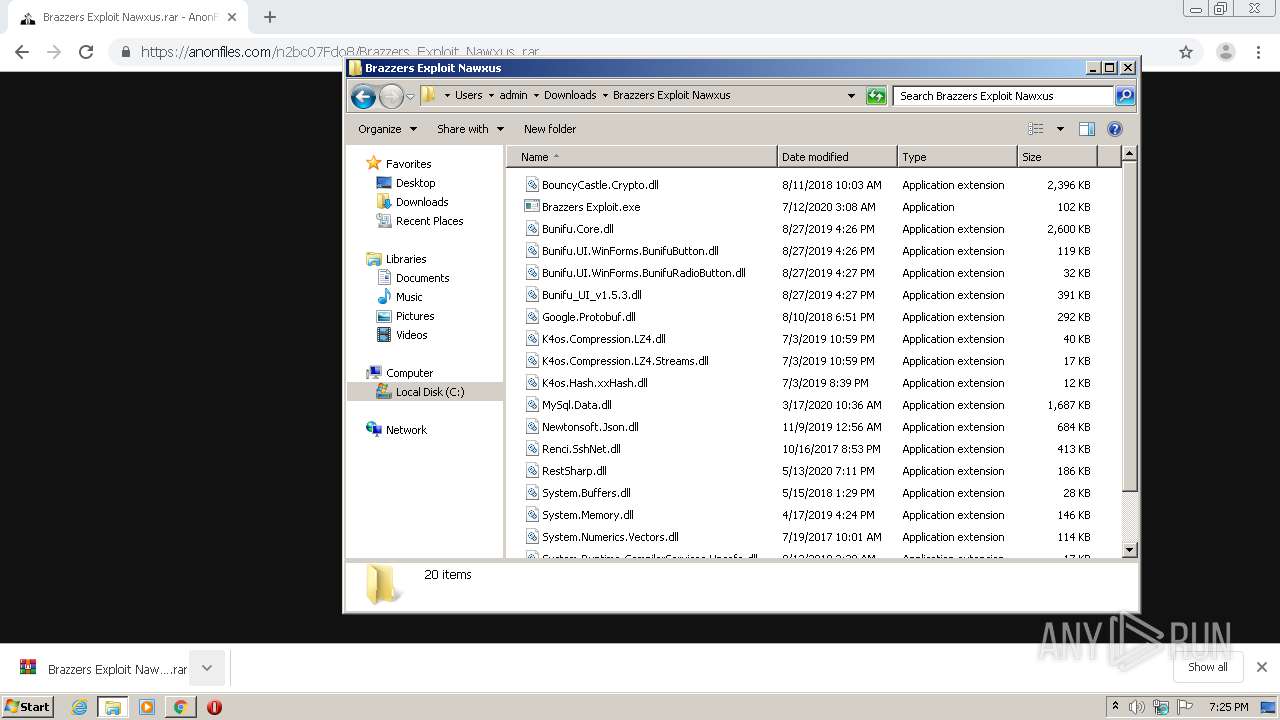
Loads dropped or rewritten executable
- SearchProtocolHost.exe (PID: 3560)
- Brazzers Exploit.exe (PID: 2452)
- explorer.exe (PID: 308)
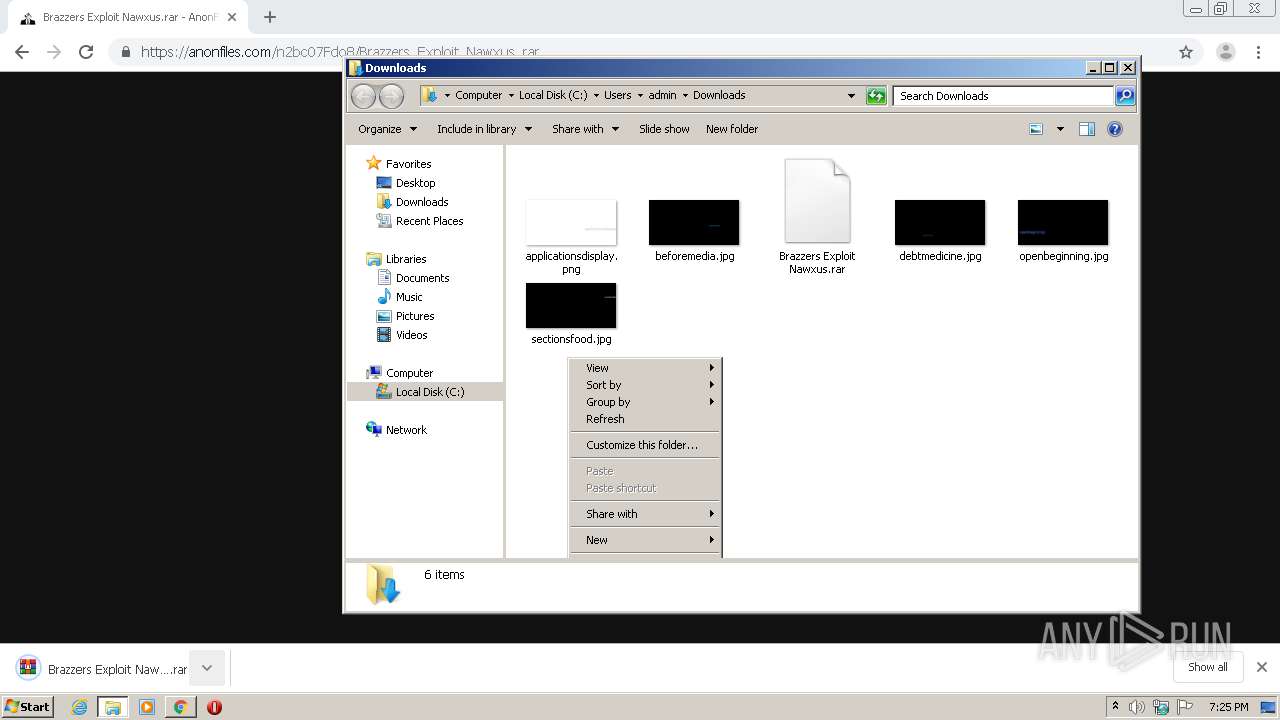
Application was dropped or rewritten from another process
- Brazzers Exploit.exe (PID: 2452)
Changes settings of System certificates
- Brazzers Exploit.exe (PID: 2452)
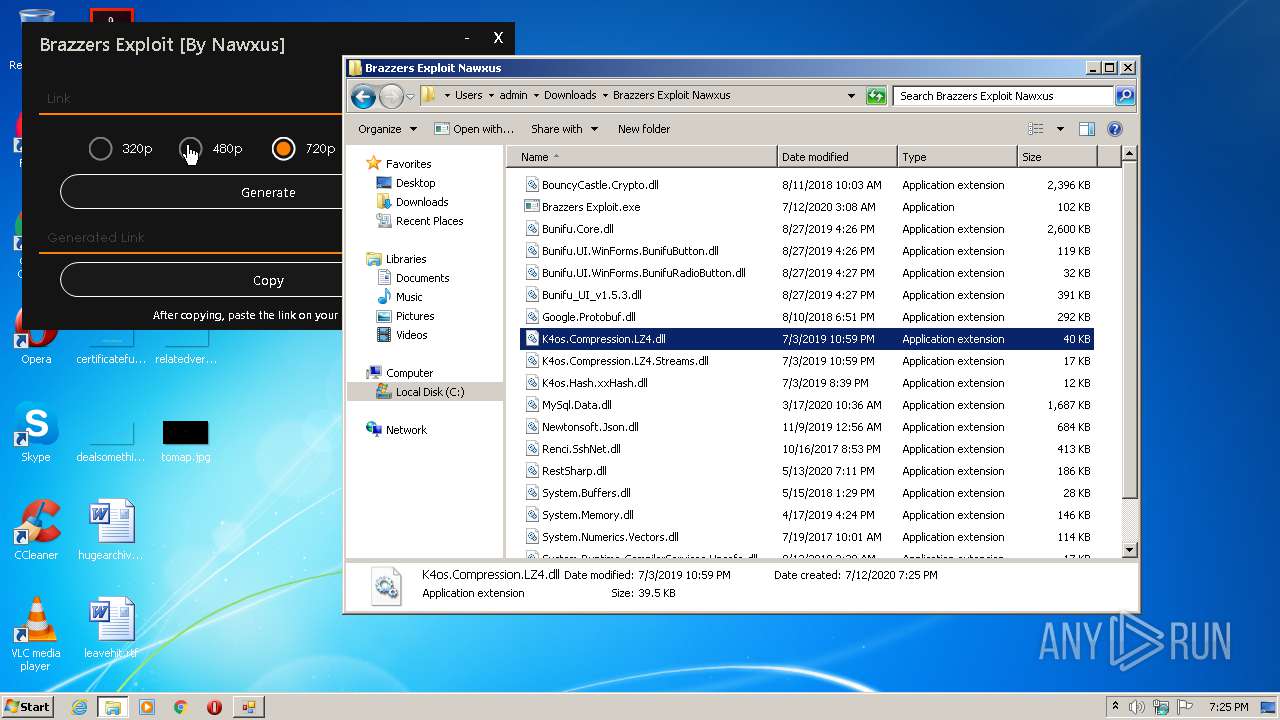
SUSPICIOUS
Creates files in the user directory
- explorer.exe (PID: 308)
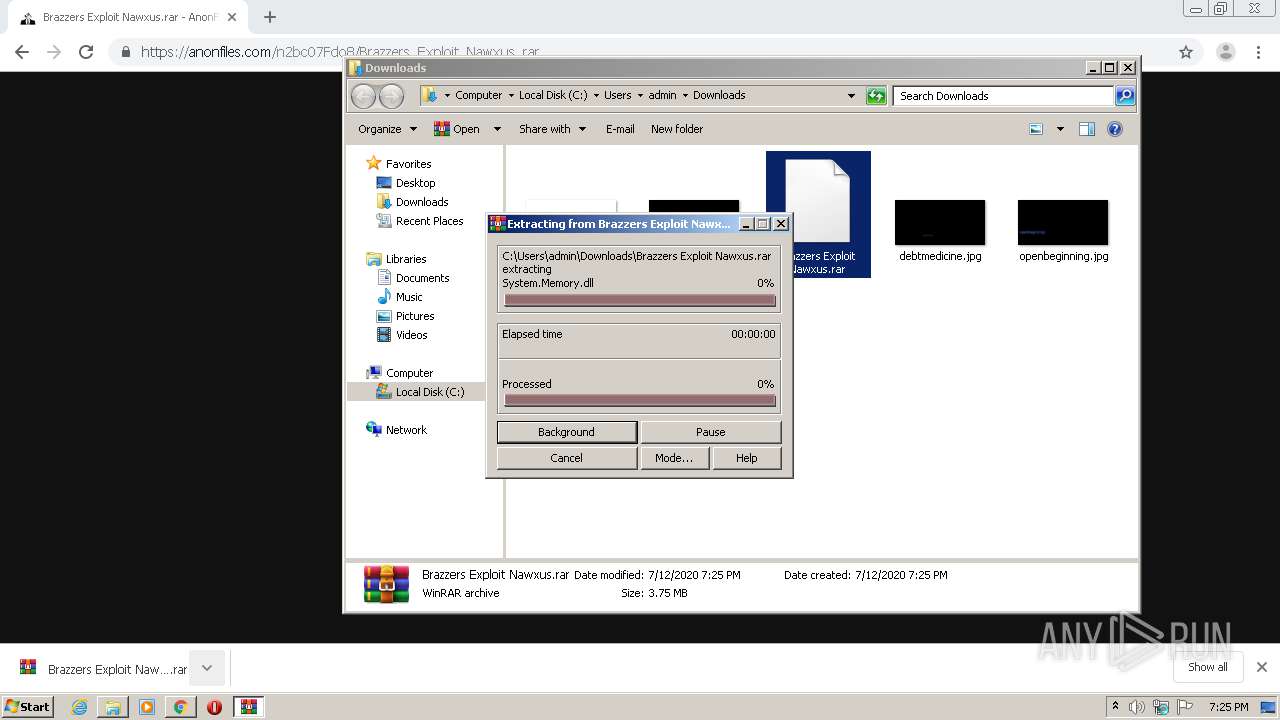
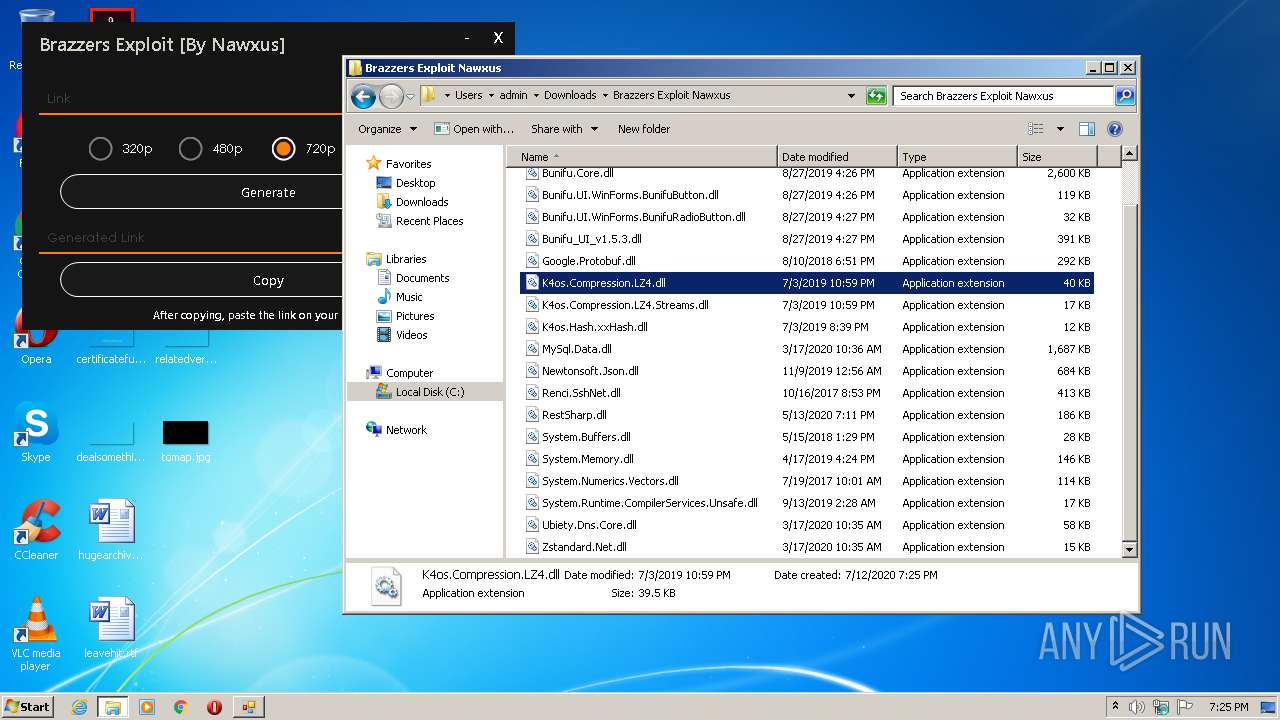
Executable content was dropped or overwritten
- WinRAR.exe (PID: 1772)
Reads Environment values
- Brazzers Exploit.exe (PID: 2452)
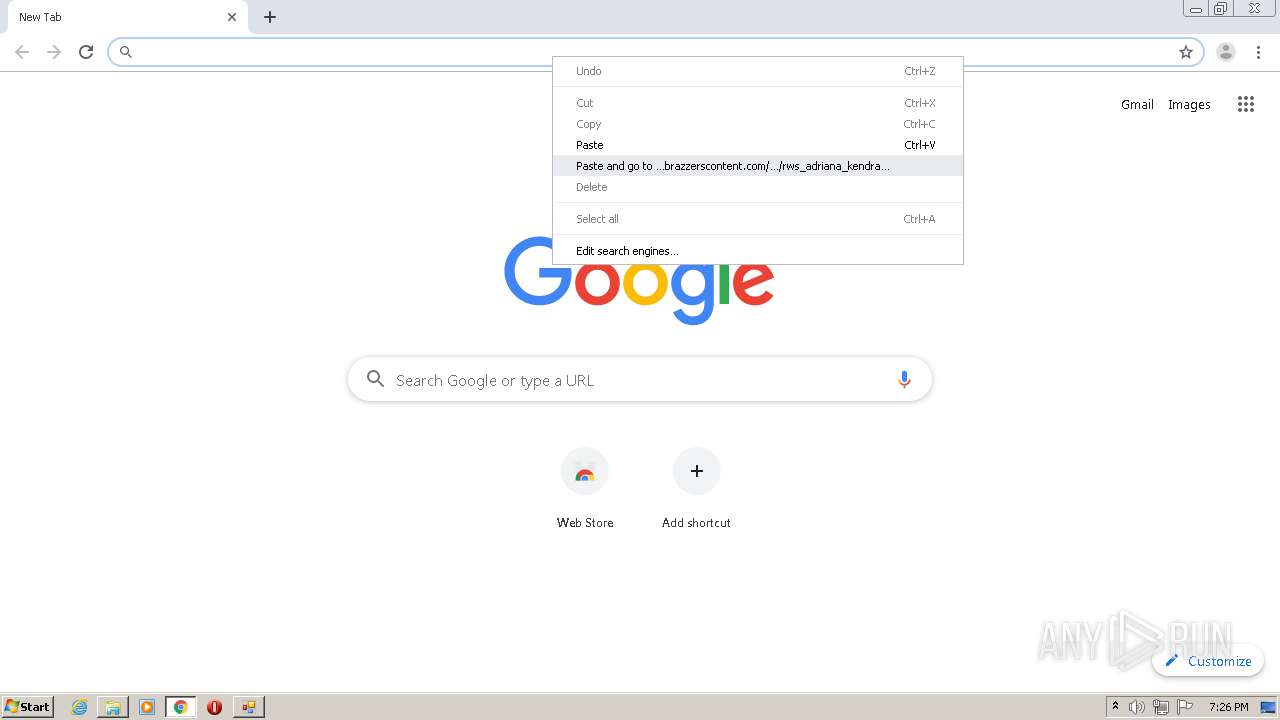
Modifies files in Chrome extension folder
- chrome.exe (PID: 2348)
Adds / modifies Windows certificates
- Brazzers Exploit.exe (PID: 2452)
INFO
Application launched itself
- chrome.exe (PID: 1176)
- chrome.exe (PID: 2348)
Reads the hosts file
- chrome.exe (PID: 1176)
- chrome.exe (PID: 816)
- chrome.exe (PID: 2348)
- chrome.exe (PID: 2288)
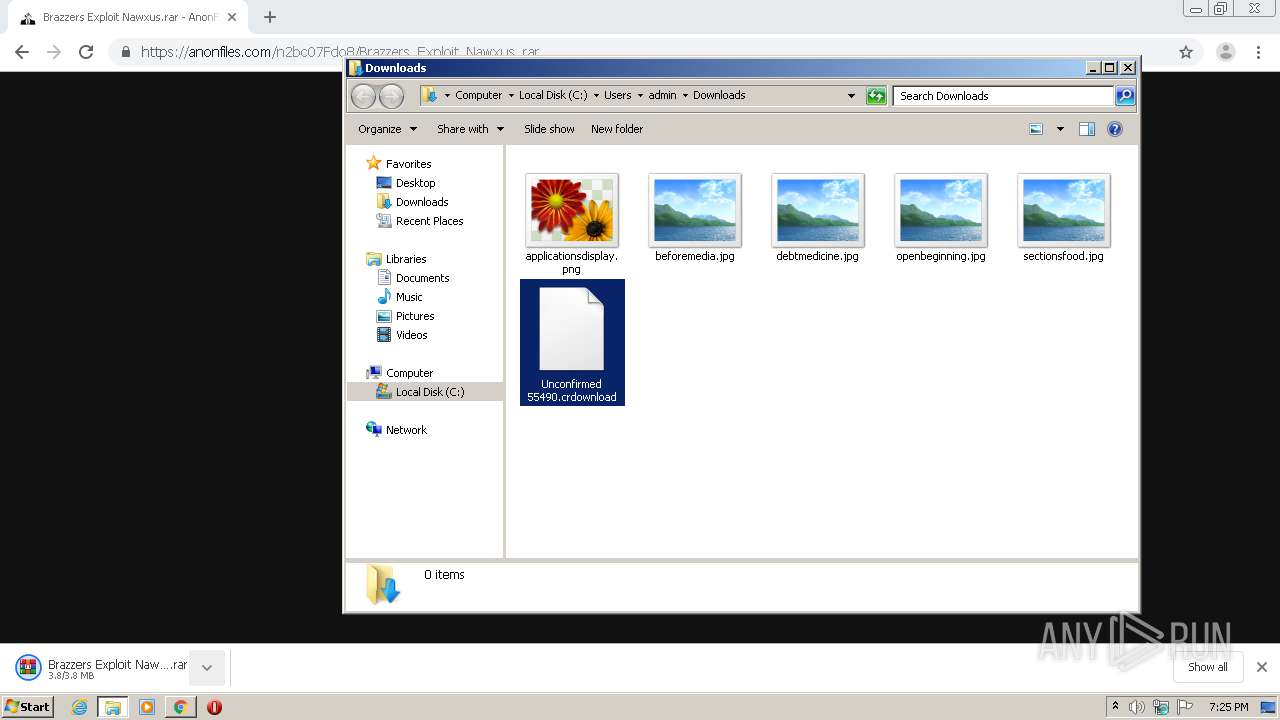
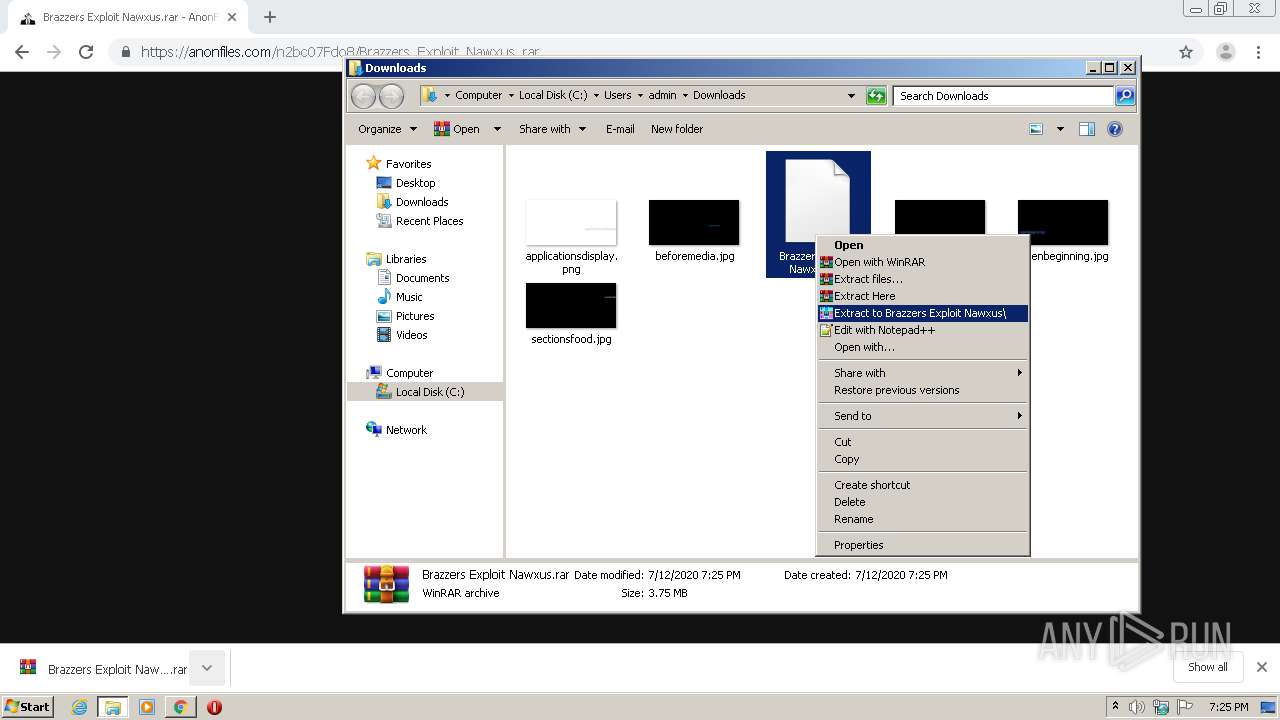
Manual execution by user
- WinRAR.exe (PID: 1772)
- Brazzers Exploit.exe (PID: 2452)
Creates files in the user directory
- chrome.exe (PID: 1176)
Reads Internet Cache Settings
- chrome.exe (PID: 1176)
Reads settings of System Certificates
- Brazzers Exploit.exe (PID: 2452)
- chrome.exe (PID: 816)
- chrome.exe (PID: 2288)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
86
Monitored processes
47
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 308 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | — | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 544 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1008,17773006920686989728,15050327539053365966,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=12921326357766045434 --renderer-client-id=7 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2576 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 588 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1032,5524259647794948354,14356240240906599980,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=2155080840976310975 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2248 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 788 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1032,5524259647794948354,14356240240906599980,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=17005572880915414471 --mojo-platform-channel-handle=4852 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 816 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1032,5524259647794948354,14356240240906599980,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=8134102012208458441 --mojo-platform-channel-handle=1644 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 872 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1032,5524259647794948354,14356240240906599980,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=3193803628588223986 --renderer-client-id=7 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3396 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 880 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1032,5524259647794948354,14356240240906599980,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=13424396331491769795 --mojo-platform-channel-handle=4868 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1176 | "C:\Program Files\Google\Chrome\Application\chrome.exe" "https://anonfiles.com/n2bc07Fdo8/Brazzers_Exploit_Nawxus_rar" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 3221225547 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1528 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1032,5524259647794948354,14356240240906599980,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=2992978679326968207 --renderer-client-id=17 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3876 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1716 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1032,5524259647794948354,14356240240906599980,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=6300269966013928266 --mojo-platform-channel-handle=4448 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
3 324
Read events
1 764
Write events
1 551
Delete events
9
Modification events
| (PID) Process: | (1872) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 1176-13239051919064500 |
Value: 259 | |||
| (PID) Process: | (1176) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1176) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1176) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (1176) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (1176) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1176) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (1176) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (1176) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3120-13213713943555664 |
Value: 0 | |||
| (PID) Process: | (1176) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1176-13239051919064500 |
Value: 259 | |||
Executable files
20
Suspicious files
109
Text files
332
Unknown types
18
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1176 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5F0B5590-498.pma | — | |
MD5:— | SHA256:— | |||
| 1176 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\fe544a9c-6846-43d7-a148-a39bc249d632.tmp | — | |
MD5:— | SHA256:— | |||
| 1176 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000028.dbtmp | — | |
MD5:— | SHA256:— | |||
| 1176 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1176 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\AvailabilityDB\LOG.old~RF168c66.TMP | text | |
MD5:— | SHA256:— | |||
| 1176 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old~RF168be9.TMP | text | |
MD5:— | SHA256:— | |||
| 1176 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old~RF168c18.TMP | text | |
MD5:— | SHA256:— | |||
| 1176 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\AvailabilityDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1176 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1176 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RF168d8f.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
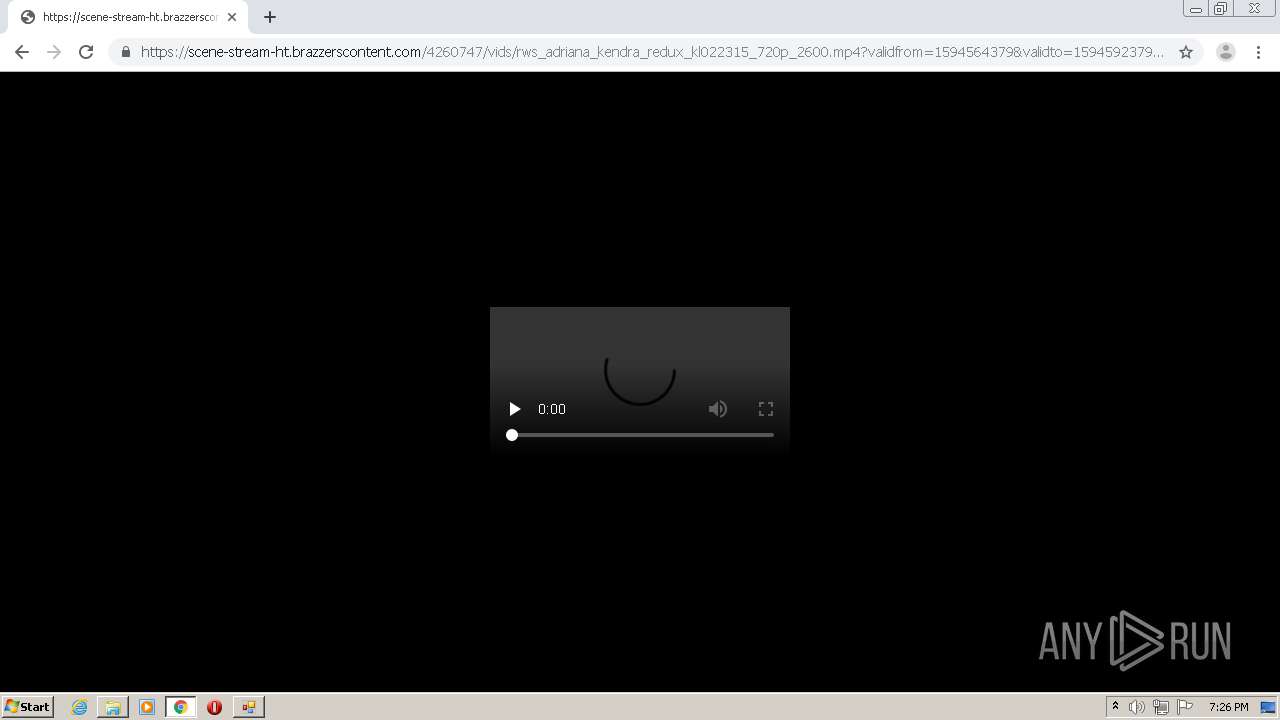
HTTP(S) requests
7
TCP/UDP connections
58
DNS requests
32
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
816 | chrome.exe | GET | 302 | 172.217.16.206:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 527 b | whitelisted |
2452 | Brazzers Exploit.exe | GET | 304 | 205.185.216.10:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 57.0 Kb | whitelisted |
816 | chrome.exe | GET | 200 | 159.148.69.141:80 | http://r2---sn-a5uoxu-gpme.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvY2Y1QUFXUjZlVjI5UldyLVpDTFJFcEx6QQ/7719.805.0.2_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mh=Nf&mip=159.148.186.246&mm=28&mn=sn-a5uoxu-gpme&ms=nvh&mt=1594577870&mv=u&mvi=2&pl=24&shardbypass=yes | LV | crx | 823 Kb | whitelisted |
2452 | Brazzers Exploit.exe | GET | 200 | 205.185.216.10:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 57.0 Kb | whitelisted |
2452 | Brazzers Exploit.exe | GET | 304 | 205.185.216.10:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 57.0 Kb | whitelisted |
816 | chrome.exe | GET | 200 | 159.148.69.143:80 | http://r4---sn-a5uoxu-gpme.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx?cms_redirect=yes&mh=QJ&mip=159.148.186.246&mm=28&mn=sn-a5uoxu-gpme&ms=nvh&mt=1594577870&mv=u&mvi=4&pl=24&shardbypass=yes | LV | crx | 293 Kb | whitelisted |
816 | chrome.exe | GET | 302 | 172.217.16.206:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvY2Y1QUFXUjZlVjI5UldyLVpDTFJFcEx6QQ/7719.805.0.2_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 532 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
816 | chrome.exe | 104.24.116.23:443 | anonfiles.com | Cloudflare Inc | US | unknown |
816 | chrome.exe | 172.217.18.3:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
816 | chrome.exe | 52.222.167.97:443 | djv99sxoqpv11.cloudfront.net | Amazon.com, Inc. | US | unknown |
816 | chrome.exe | 151.101.2.217:443 | vjs.zencdn.net | Fastly | US | suspicious |
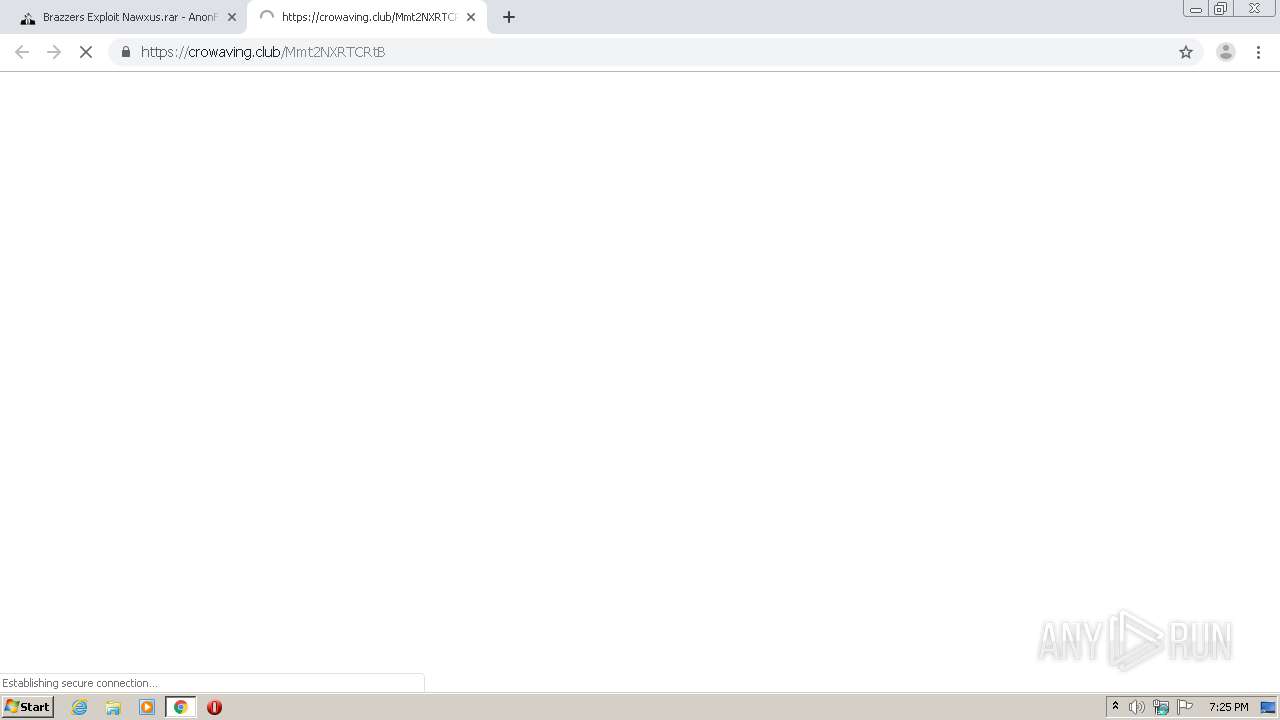
816 | chrome.exe | 52.222.166.3:443 | crowaving.club | Amazon.com, Inc. | US | malicious |
816 | chrome.exe | 216.58.207.68:443 | www.google.com | Google Inc. | US | whitelisted |
816 | chrome.exe | 52.222.166.90:443 | consideher.club | Amazon.com, Inc. | US | unknown |
816 | chrome.exe | 52.222.166.32:443 | providentsopport.site | Amazon.com, Inc. | US | unknown |
816 | chrome.exe | 172.217.22.46:443 | clients2.google.com | Google Inc. | US | whitelisted |
816 | chrome.exe | 18.184.67.93:443 | smtwv.voluumtrk3.com | — | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
anonfiles.com |
| shared |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
vjs.zencdn.net |
| whitelisted |
djv99sxoqpv11.cloudfront.net |
| shared |
baconaces.pro |
| shared |
www.google.com |
| malicious |
crowaving.club |
| malicious |
consideher.club |
| malicious |
providentsopport.site |
| whitelisted |