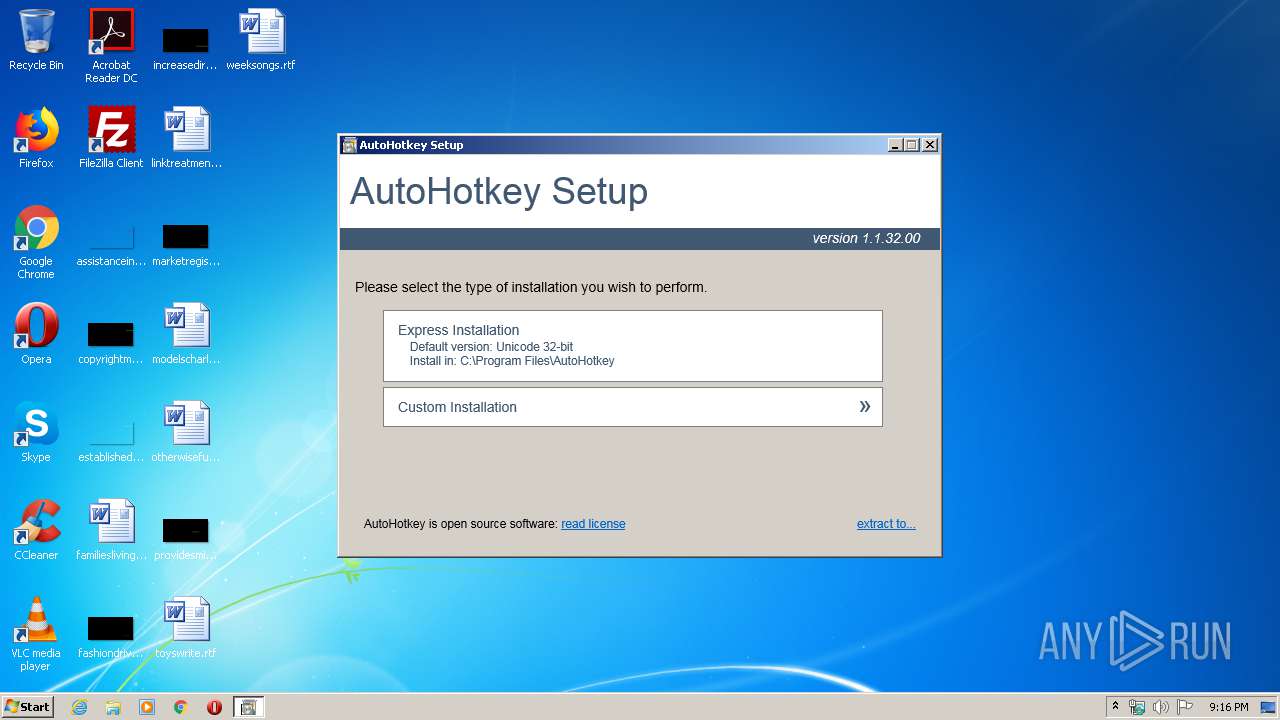
| File name: | AutoHotkey_1.1.32.00_setup.exe |
| Full analysis: | https://app.any.run/tasks/44017671-8356-42d8-8e95-e53ff9adee0e |
| Verdict: | Malicious activity |
| Analysis date: | January 23, 2020, 21:15:49 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 818105AB8672979AA12542EBC90C4518 |
| SHA1: | 04D41D3631A82E322B2F75D9E5E120DEA8804430 |
| SHA256: | CE505D272F8D36C5599AC81F005E1D2D586EEAAA778C779AD858E44FDADFDB0D |
| SSDEEP: | 98304:hPnuzWpYslvB7QUrd6sqsVLKYe/NXTTGrM:h9nSqd6sq5/NXp |
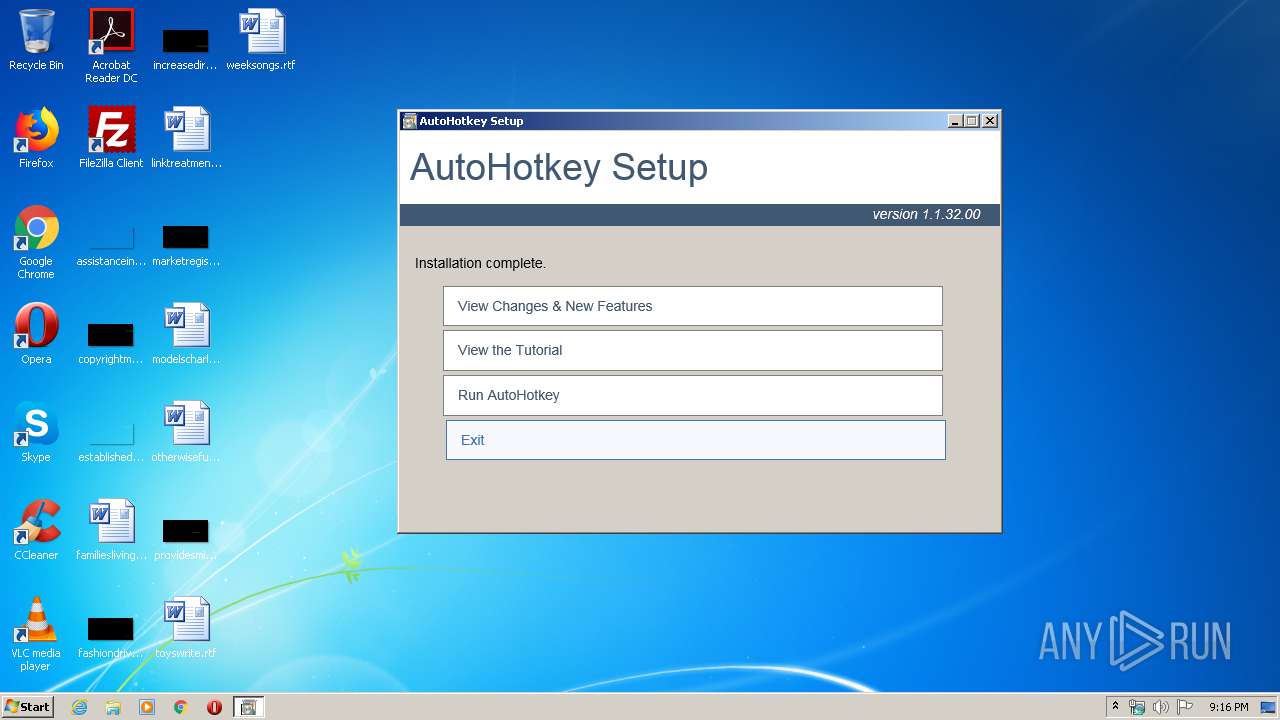
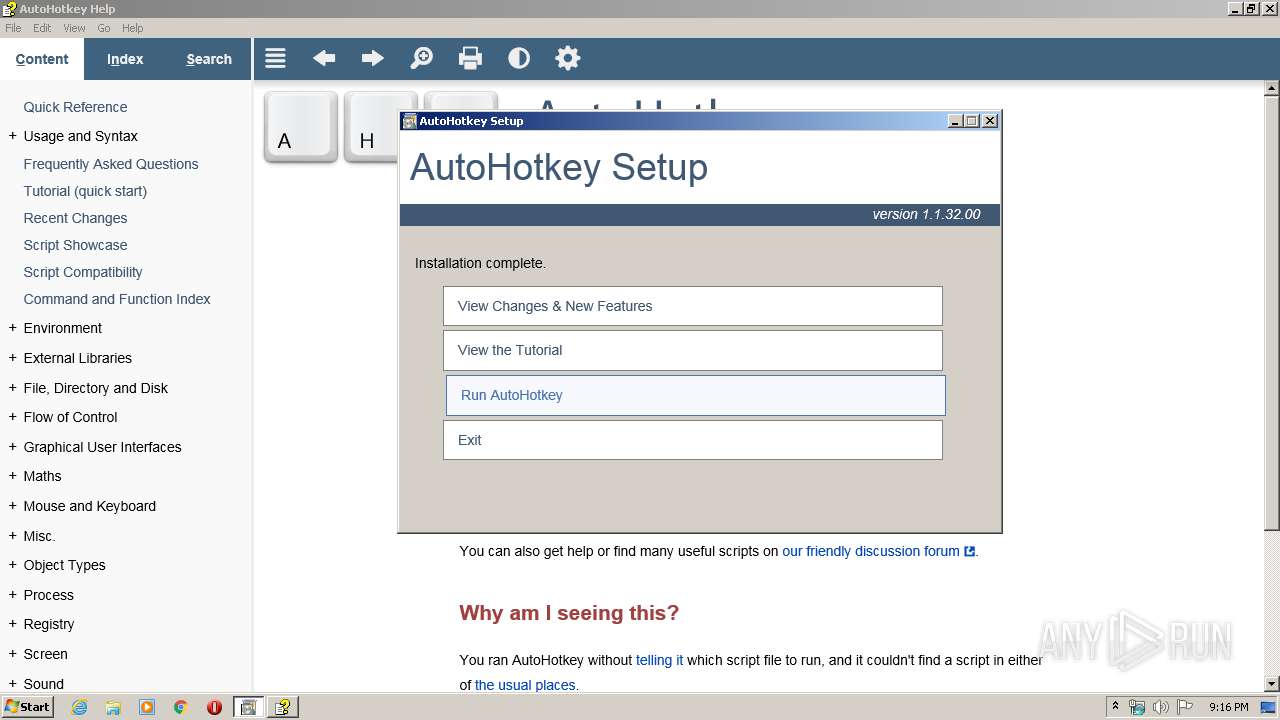
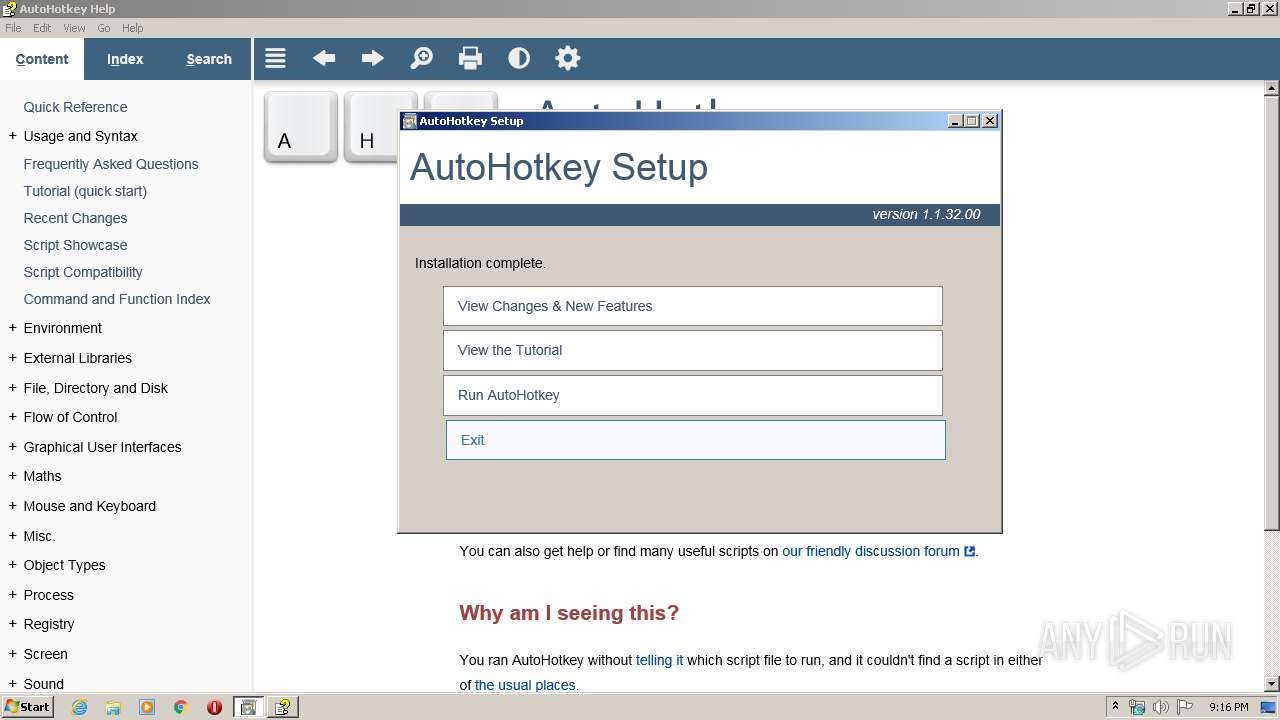
MALICIOUS
Application was dropped or rewritten from another process
- setup.exe (PID: 3516)
- AutoHotkey.exe (PID: 3504)
- AutoHotkey.exe (PID: 1828)
SUSPICIOUS
Executable content was dropped or overwritten
- AutoHotkey_1.1.32.00_setup.exe (PID: 2828)
- setup.exe (PID: 3516)
Reads internet explorer settings
- setup.exe (PID: 3516)
- hh.exe (PID: 4092)
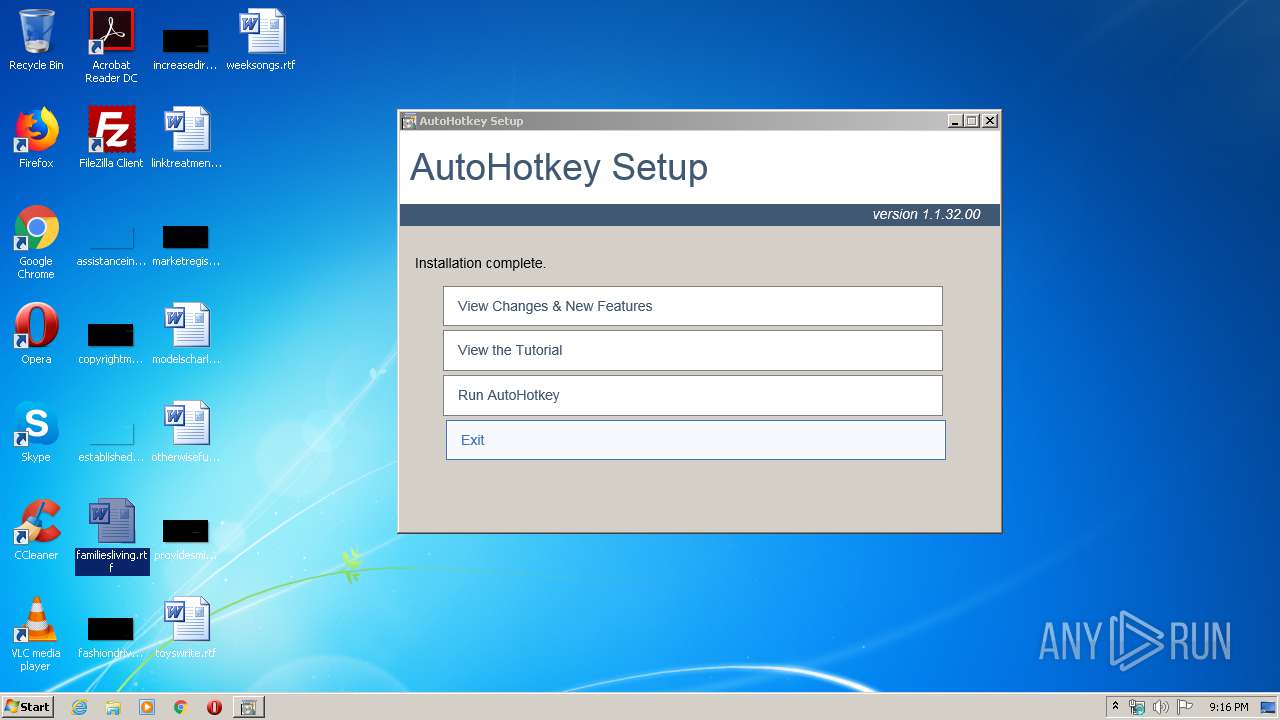
Creates files in the program directory
- setup.exe (PID: 3516)
Creates files in the Windows directory
- setup.exe (PID: 3516)
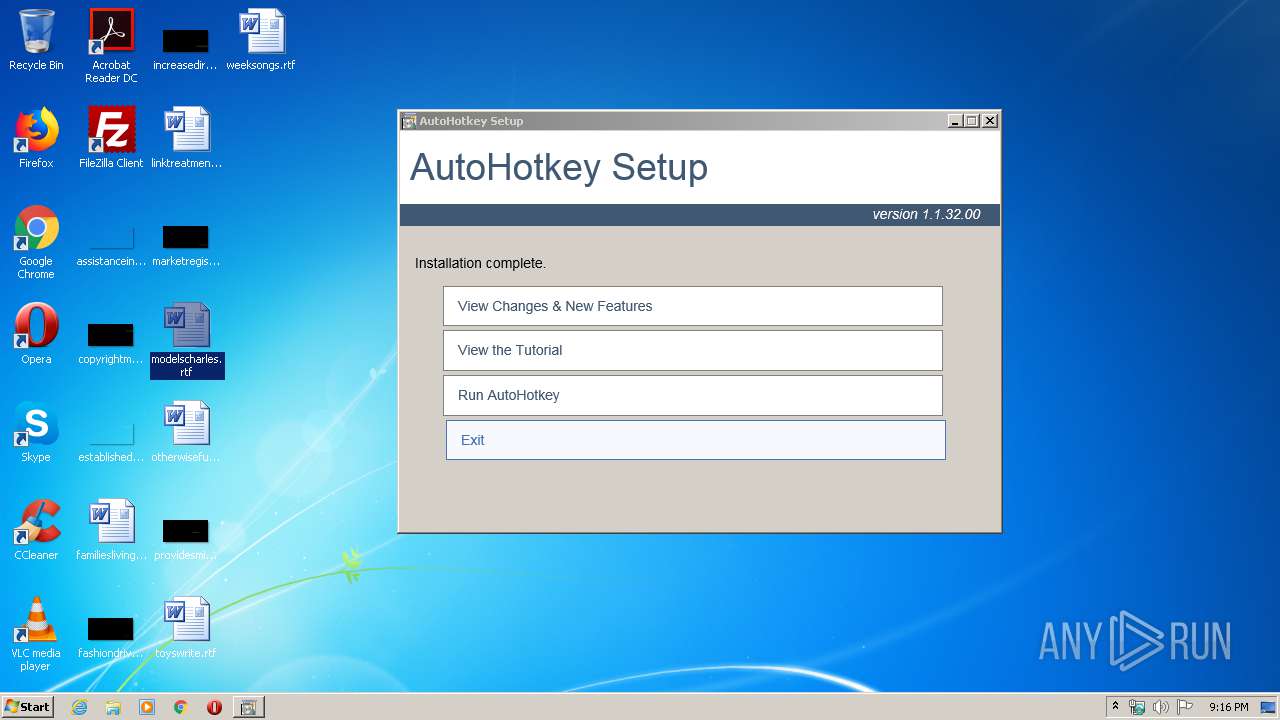
Creates a software uninstall entry
- setup.exe (PID: 3516)
Modifies the open verb of a shell class
- setup.exe (PID: 3516)
Application launched itself
- AutoHotkey.exe (PID: 3504)
INFO
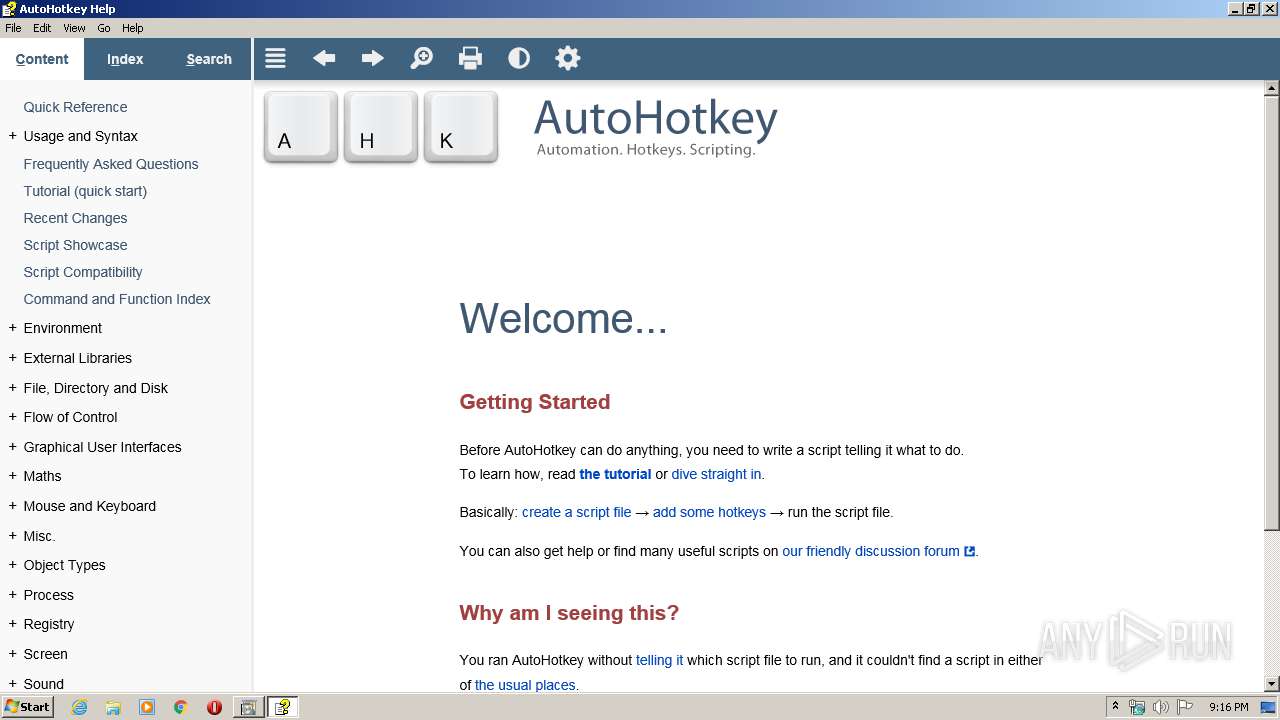
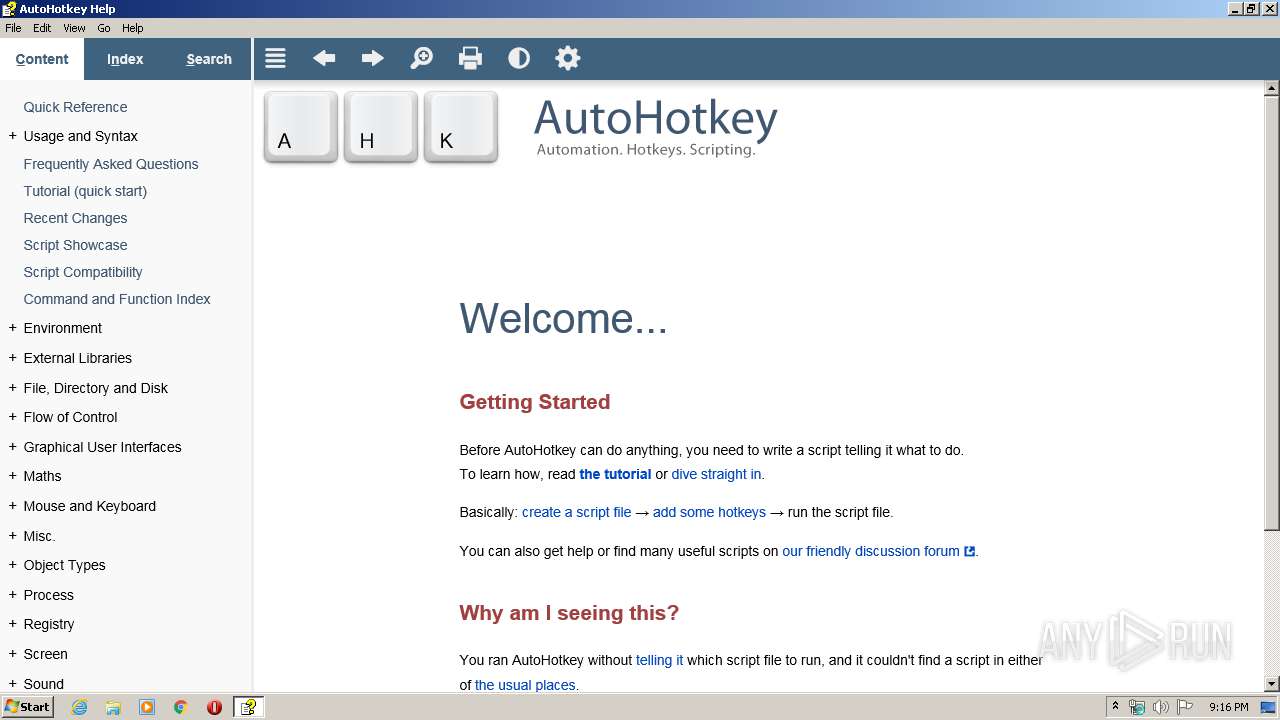
Manual execution by user
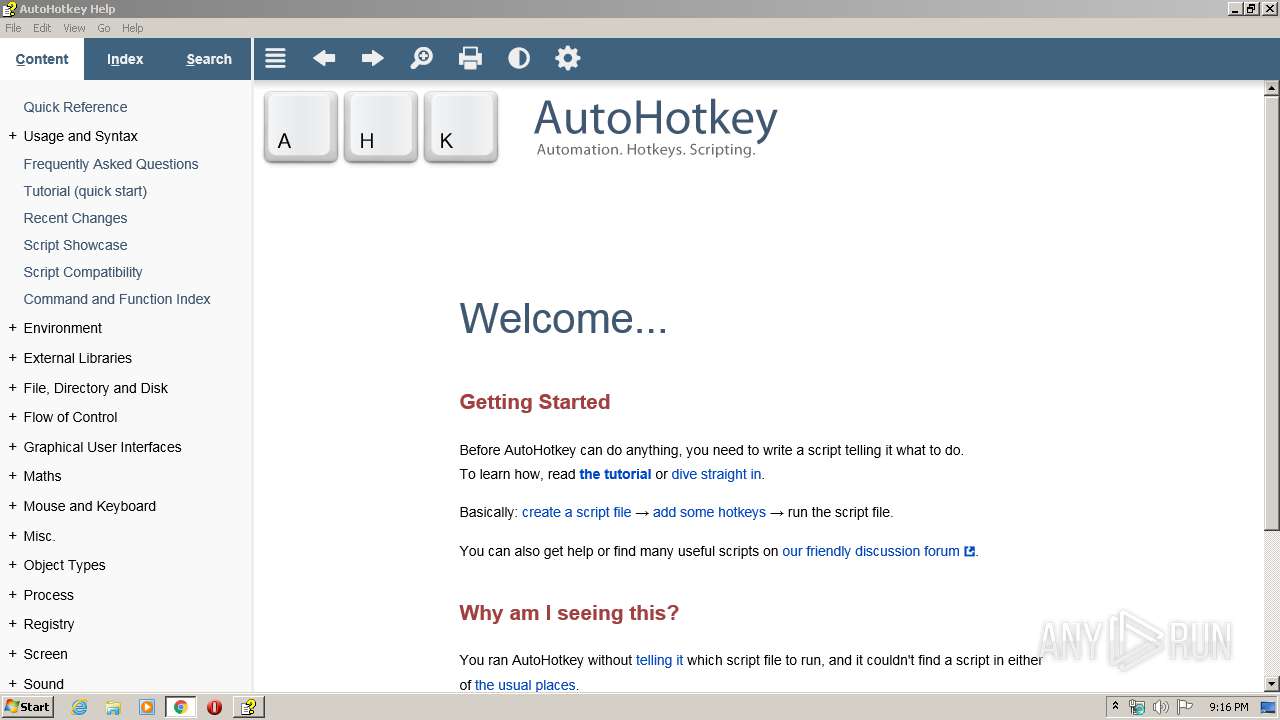
- AutoHotkey.exe (PID: 3504)
- chrome.exe (PID: 2152)
Reads the hosts file
- chrome.exe (PID: 340)
- chrome.exe (PID: 2152)
Application launched itself
- chrome.exe (PID: 2152)
Reads settings of System Certificates
- chrome.exe (PID: 340)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .dll | | | Win32 Dynamic Link Library (generic) (43.5) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (29.8) |
| .exe | | | Generic Win/DOS Executable (13.2) |
| .exe | | | DOS Executable Generic (13.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2010:11:18 19:41:55+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 22016 |
| InitializedDataSize: | 33792 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x643f |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.1.32.0 |
| ProductVersionNumber: | 1.1.32.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
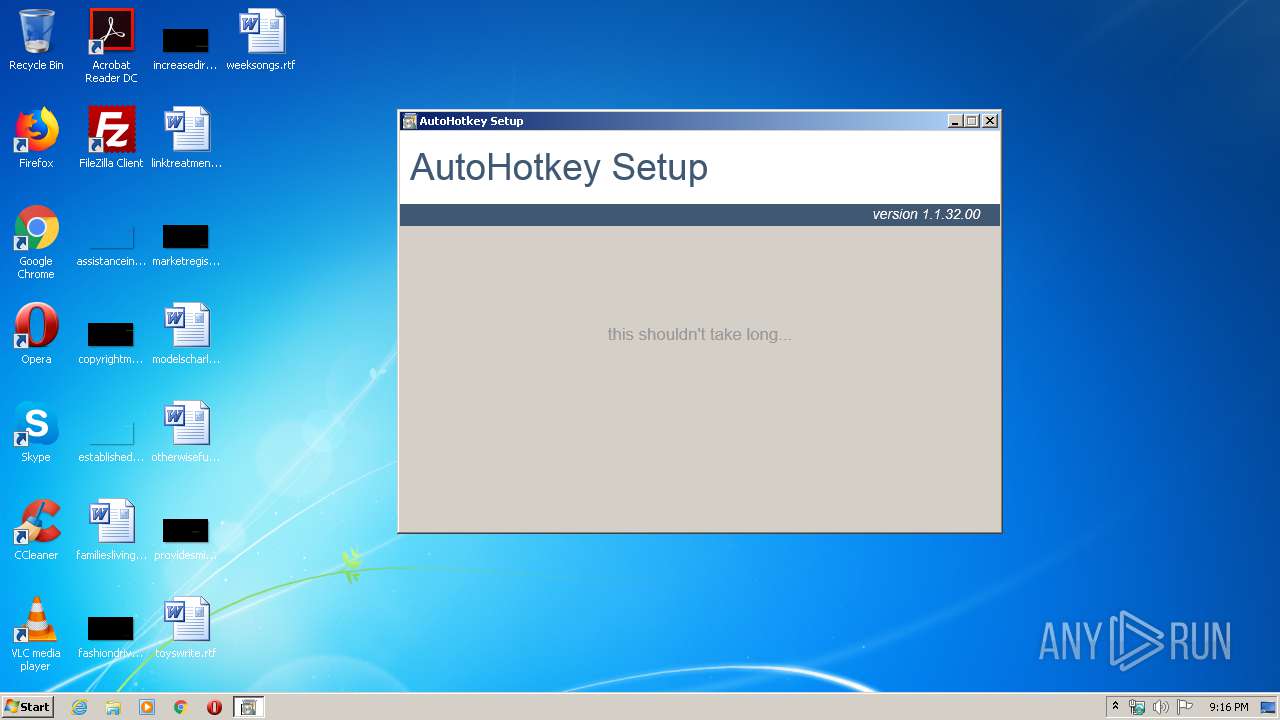
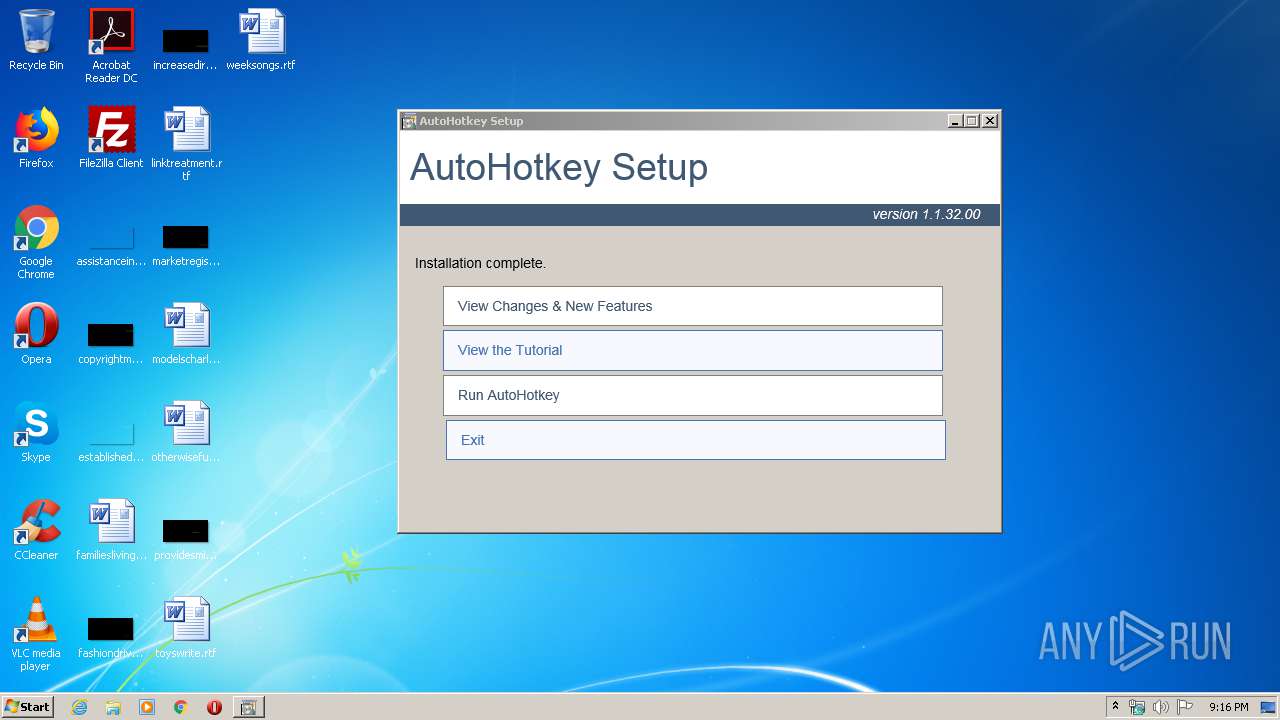
| FileDescription: | AutoHotkey Setup |
| FileVersion: | 1.1.32.00 |
| ProductName: | AutoHotkey |
| ProductVersion: | 1.1.32.00 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 18-Nov-2010 18:41:55 |
| Detected languages: |
|
| FileDescription: | AutoHotkey Setup |
| FileVersion: | 1.1.32.00 |
| ProductName: | AutoHotkey |
| ProductVersion: | 1.1.32.00 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 18-Nov-2010 18:41:55 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000055CC | 0x00005600 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.59892 |
.rdata | 0x00007000 | 0x00000548 | 0x00000600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.38017 |
.data | 0x00008000 | 0x0000220C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.32755 |
.rsrc | 0x0000B000 | 0x000058DF | 0x00005A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.37688 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.31459 | 727 | UNKNOWN | UNKNOWN | RT_MANIFEST |
2 | 3.18403 | 296 | UNKNOWN | English - United States | RT_ICON |
3 | 3.1643 | 744 | UNKNOWN | UNKNOWN | RT_ICON |
4 | 3.5146 | 296 | UNKNOWN | UNKNOWN | RT_ICON |
5 | 5.93897 | 2216 | UNKNOWN | UNKNOWN | RT_ICON |
6 | 3.37592 | 1384 | UNKNOWN | UNKNOWN | RT_ICON |
7 | 5.199 | 9640 | UNKNOWN | UNKNOWN | RT_ICON |
8 | 5.44465 | 4264 | UNKNOWN | UNKNOWN | RT_ICON |
9 | 4.85349 | 1128 | UNKNOWN | UNKNOWN | RT_ICON |
Imports
KERNEL32.dll |
MSVCRT.dll |
SHELL32.dll |
USER32.dll |
Total processes
60
Monitored processes
21
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 340 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1020,3474301155111338167,5843348650607888487,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=10939790474129113554 --mojo-platform-channel-handle=1632 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 564 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1020,3474301155111338167,5843348650607888487,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=18089206509843323496 --renderer-client-id=7 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2456 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1084 | "C:\Users\admin\AppData\Local\Temp\AutoHotkey_1.1.32.00_setup.exe" | C:\Users\admin\AppData\Local\Temp\AutoHotkey_1.1.32.00_setup.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: AutoHotkey Setup Exit code: 3221226540 Version: 1.1.32.00 Modules
| |||||||||||||||
| 1792 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1020,3474301155111338167,5843348650607888487,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=2978276629469536390 --mojo-platform-channel-handle=3656 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1828 | AutoHotkey.exe | C:\Program Files\AutoHotkey\AutoHotkey.exe | — | AutoHotkey.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: AutoHotkey Unicode 32-bit Exit code: 2 Version: 1.1.32.00 Modules
| |||||||||||||||
| 2152 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 3221225547 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2500 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1020,3474301155111338167,5843348650607888487,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=10334697342701357653 --mojo-platform-channel-handle=3748 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2664 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=848 --on-initialized-event-handle=324 --parent-handle=328 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2828 | "C:\Users\admin\AppData\Local\Temp\AutoHotkey_1.1.32.00_setup.exe" | C:\Users\admin\AppData\Local\Temp\AutoHotkey_1.1.32.00_setup.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: AutoHotkey Setup Exit code: 0 Version: 1.1.32.00 Modules
| |||||||||||||||
| 2864 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1020,3474301155111338167,5843348650607888487,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=588798243329419210 --mojo-platform-channel-handle=3744 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
768
Read events
669
Write events
95
Delete events
4
Modification events
| (PID) Process: | (3516) setup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3516) setup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3516) setup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3516) setup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3516) setup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3516) setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\AutoHotkey |
| Operation: | write | Name: | InstallDir |
Value: C:\Program Files\AutoHotkey | |||
| (PID) Process: | (3516) setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\AutoHotkey |
| Operation: | write | Name: | Version |
Value: 1.1.32.00 | |||
| (PID) Process: | (3516) setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\AutoHotkey |
| Operation: | write | Name: | StartMenuFolder |
Value: AutoHotkey | |||
| (PID) Process: | (3516) setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\.ahk |
| Operation: | write | Name: | |
Value: AutoHotkeyScript | |||
| (PID) Process: | (3516) setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\.ahk\ShellNew |
| Operation: | write | Name: | FileName |
Value: Template.ahk | |||
Executable files
16
Suspicious files
22
Text files
144
Unknown types
17
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2828 | AutoHotkey_1.1.32.00_setup.exe | C:\Users\admin\AppData\Local\Temp\7z65A44B0C\Compiler\Unicode 64-bit.bin | executable | |
MD5:C18F3CF171B20A7643957DCCD8C66D3D | SHA256:6617C07DB1E2C681302C33F1A97380DC70D866FEEC3346F1CD5BFBDB79AD6193 | |||
| 2828 | AutoHotkey_1.1.32.00_setup.exe | C:\Users\admin\AppData\Local\Temp\7z65A44B0C\AutoHotkeyU32.exe | executable | |
MD5:0D0D4BCD65381208F55825B2C4247287 | SHA256:7D978A454F0F0B60B33069ABDADD324D6A7C1A2BF6A1F97390C6DE3D11BD9BDA | |||
| 2828 | AutoHotkey_1.1.32.00_setup.exe | C:\Users\admin\AppData\Local\Temp\7z65A44B0C\Template.ahk | text | |
MD5:A85EEB1DC6F9A33897C407B4240DC20F | SHA256:23E5115A25E2D539057443B0F0E9740B9AE85D7DE0DA204F1D739C9B2E206058 | |||
| 2828 | AutoHotkey_1.1.32.00_setup.exe | C:\Users\admin\AppData\Local\Temp\7z65A44B0C\Installer.ahk | text | |
MD5:F69C2AC693E9E4D6B8ED3935CA504F48 | SHA256:58EE4041964BC96FFE6316DF7A08141748A5279C458C32F11424C74B93A85A23 | |||
| 2828 | AutoHotkey_1.1.32.00_setup.exe | C:\Users\admin\AppData\Local\Temp\7z65A44B0C\Compiler\Ahk2Exe.exe | executable | |
MD5:B3E0FA020816185B057C990F2B3D21B4 | SHA256:D7B698C277870D4E29633F420D1DE8B52025FFF7B31680614739290443AABB3C | |||
| 2828 | AutoHotkey_1.1.32.00_setup.exe | C:\Users\admin\AppData\Local\Temp\7z65A44B0C\AutoHotkeyU64.exe | executable | |
MD5:B7FD8ED4BFBAB2E795A83FE5AE3CFF4C | SHA256:F62FF2E9B365893BFF3B8338EE65564A5753EDFB505AB5B4964B9788D4E0DF87 | |||
| 2828 | AutoHotkey_1.1.32.00_setup.exe | C:\Users\admin\AppData\Local\Temp\7z65A44B0C\AutoHotkeyA32.exe | executable | |
MD5:64225529A3DDA8EFDABE8C7A94418585 | SHA256:D2D54BB1950CE24CC94D7AA7514CB8D057E2F05AF86A8957FEE85BBB7B1A4A70 | |||
| 2828 | AutoHotkey_1.1.32.00_setup.exe | C:\Users\admin\AppData\Local\Temp\7z65A44B0C\setup.exe | executable | |
MD5:72E46B87E9D264512AF11A34B1645552 | SHA256:809CDE49325A1834AC63BA879D1E751F80086D0AC5A5B3B096CF8257CA2E5531 | |||
| 2828 | AutoHotkey_1.1.32.00_setup.exe | C:\Users\admin\AppData\Local\Temp\7z65A44B0C\license.txt | text | |
MD5:E3F2AD7733F3166FE770E4DC00AF6C45 | SHA256:B27C1A7C92686E47F8740850AD24877A50BE23FD3DBD44EDEE50AC1223135E38 | |||
| 2828 | AutoHotkey_1.1.32.00_setup.exe | C:\Users\admin\AppData\Local\Temp\7z65A44B0C\Compiler\readme.txt | text | |
MD5:7DC396DF6D33B515684FC351F3D84410 | SHA256:EA06BAFAE404A13B5F4AE9AB7901D0865FAACC1E252306AC52051E6AF5CD80A7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
14
DNS requests
14
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
340 | chrome.exe | GET | 302 | 172.217.22.78:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 518 b | whitelisted |
340 | chrome.exe | GET | 302 | 172.217.22.78:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 523 b | whitelisted |
340 | chrome.exe | GET | 200 | 195.95.178.175:80 | http://r4---sn-pouxga5o-vu2s.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=85.203.45.27&mm=28&mn=sn-pouxga5o-vu2s&ms=nvh&mt=1579814178&mv=m&mvi=3&pl=25&shardbypass=yes | RO | crx | 862 Kb | whitelisted |
340 | chrome.exe | GET | 200 | 195.95.178.206:80 | http://r3---sn-pouxga5o-vu2l.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx?cms_redirect=yes&mip=85.203.45.27&mm=28&mn=sn-pouxga5o-vu2l&ms=nvh&mt=1579814178&mv=m&mvi=2&pl=25&shardbypass=yes | RO | crx | 293 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
340 | chrome.exe | 172.217.23.163:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
340 | chrome.exe | 216.58.207.45:443 | accounts.google.com | Google Inc. | US | whitelisted |
340 | chrome.exe | 172.217.18.163:443 | www.google.com.ua | Google Inc. | US | whitelisted |
340 | chrome.exe | 172.217.18.170:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
340 | chrome.exe | 172.217.18.3:443 | www.gstatic.com | Google Inc. | US | whitelisted |
340 | chrome.exe | 216.58.210.3:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
340 | chrome.exe | 172.217.23.174:443 | clients2.google.com | Google Inc. | US | whitelisted |
340 | chrome.exe | 172.217.16.193:443 | clients2.googleusercontent.com | Google Inc. | US | whitelisted |
340 | chrome.exe | 172.217.21.228:443 | www.google.com | Google Inc. | US | whitelisted |
340 | chrome.exe | 172.217.22.78:80 | ogs.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com.ua |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
ogs.google.com |
| whitelisted |
clients2.google.com |
| whitelisted |
redirector.gvt1.com |
| whitelisted |