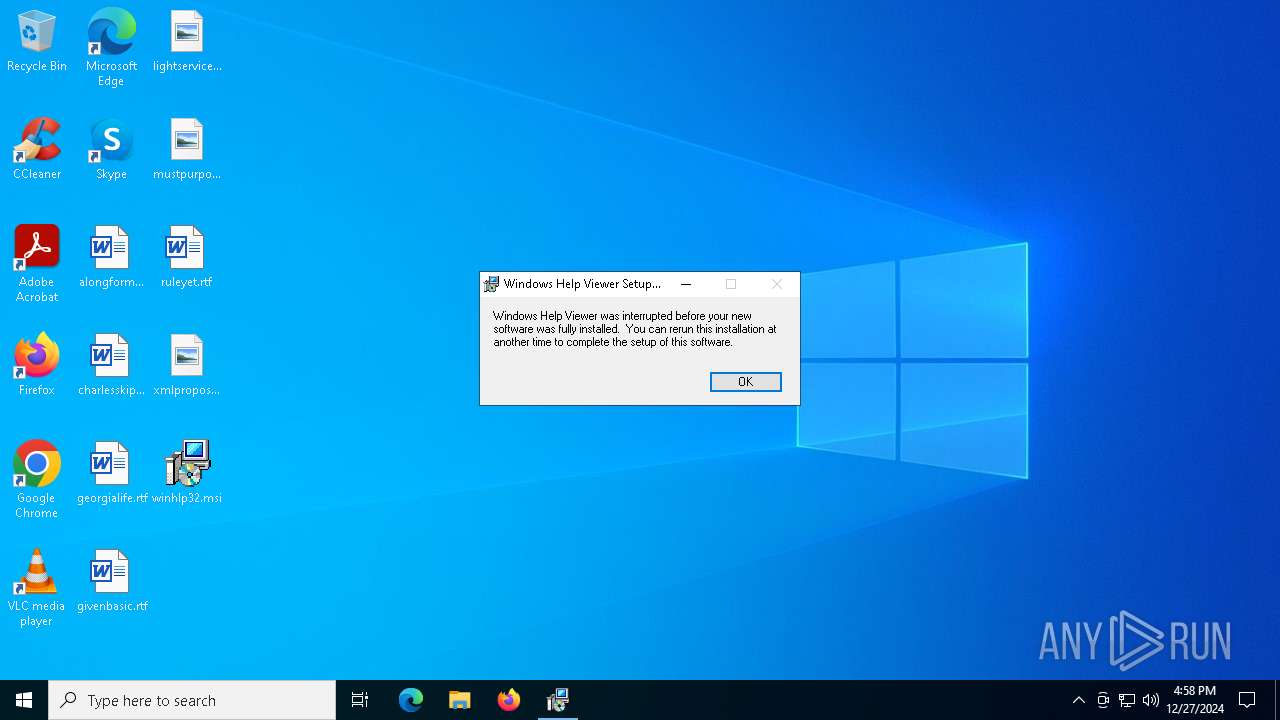
| File name: | winhlp32.msi |
| Full analysis: | https://app.any.run/tasks/f5f09f0e-fab2-48a1-8565-c8be1df96c78 |
| Verdict: | Malicious activity |
| Analysis date: | December 27, 2024, 16:57:56 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/x-msi |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.2, MSI Installer, Code page: 1252, Name of Creating Application: Windows Installer Editor Standalone, Last Saved Time/Date: Wed Nov 28 19:21:26 2018, Last Printed: 17:10:47, Title: Installation Database, Subject: Windows Help Viewer, Author: Microsoft Corporation, Template: Intel;1033, Last Saved By: nvicoadm, Revision Number: {55F80DCA-BAC3-4E7A-AA2D-2A6E16101BB1}, Number of Pages: 200, Number of Words: 2 |
| MD5: | 10BA7330EAB7DBAEC93BEE5112DF47D4 |
| SHA1: | AC30060E6442CF260C63D47FB12E2DE0DE1FE661 |
| SHA256: | CE4C0FFB97BDAE423D197EC902DB88F298B699E7279F315C0694C7F48A7BD546 |
| SSDEEP: | 24576:p8ddR0M4KDbhrKowVhhMReUqU8ZaoZ3kcw02m1KkR5dEbMR:p8ddR0M4KDbhWowVhhSeUqU8VZ3kcwbY |
MALICIOUS
No malicious indicators.SUSPICIOUS
Executes as Windows Service
- VSSVC.exe (PID: 6896)
Process drops legitimate windows executable
- msiexec.exe (PID: 6172)
Changes default file association
- msiexec.exe (PID: 6172)
INFO
Reads the computer name
- msiexec.exe (PID: 6172)
- msiexec.exe (PID: 6220)
- msiexec.exe (PID: 4876)
- msiexec.exe (PID: 6780)
Checks supported languages
- msiexec.exe (PID: 6220)
- msiexec.exe (PID: 6172)
- msiexec.exe (PID: 4876)
- msiexec.exe (PID: 6780)
The sample compiled with english language support
- msiexec.exe (PID: 5488)
- msiexec.exe (PID: 6172)
- msiexec.exe (PID: 6536)
Executable content was dropped or overwritten
- msiexec.exe (PID: 5488)
- msiexec.exe (PID: 6172)
- msiexec.exe (PID: 6536)
Manages system restore points
- SrTasks.exe (PID: 1412)
The sample compiled with arabic language support
- msiexec.exe (PID: 6172)
The sample compiled with french language support
- msiexec.exe (PID: 6172)
The sample compiled with german language support
- msiexec.exe (PID: 6172)
The sample compiled with czech language support
- msiexec.exe (PID: 6172)
The sample compiled with spanish language support
- msiexec.exe (PID: 6172)
The sample compiled with Italian language support
- msiexec.exe (PID: 6172)
The sample compiled with japanese language support
- msiexec.exe (PID: 6172)
The sample compiled with swedish language support
- msiexec.exe (PID: 6172)
The sample compiled with portuguese language support
- msiexec.exe (PID: 6172)
The sample compiled with turkish language support
- msiexec.exe (PID: 6172)
The sample compiled with chinese language support
- msiexec.exe (PID: 6172)
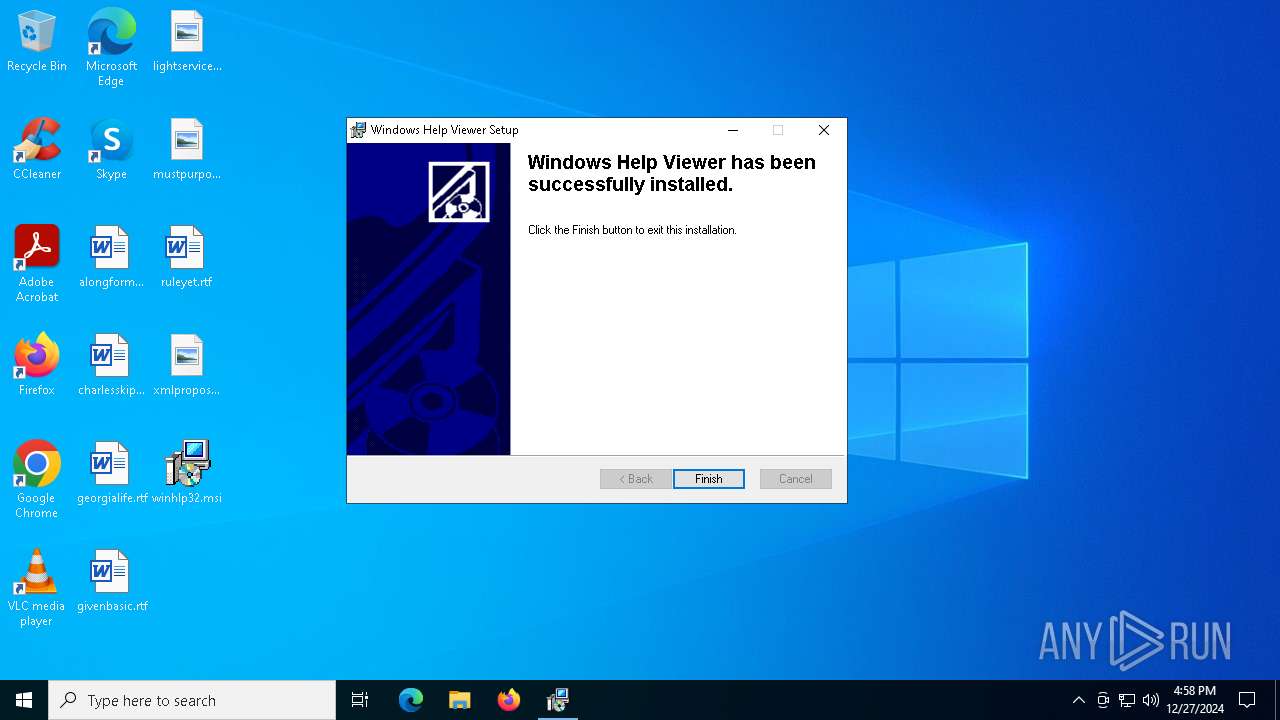
Creates a software uninstall entry
- msiexec.exe (PID: 6172)
The sample compiled with polish language support
- msiexec.exe (PID: 6172)
The sample compiled with russian language support
- msiexec.exe (PID: 6172)
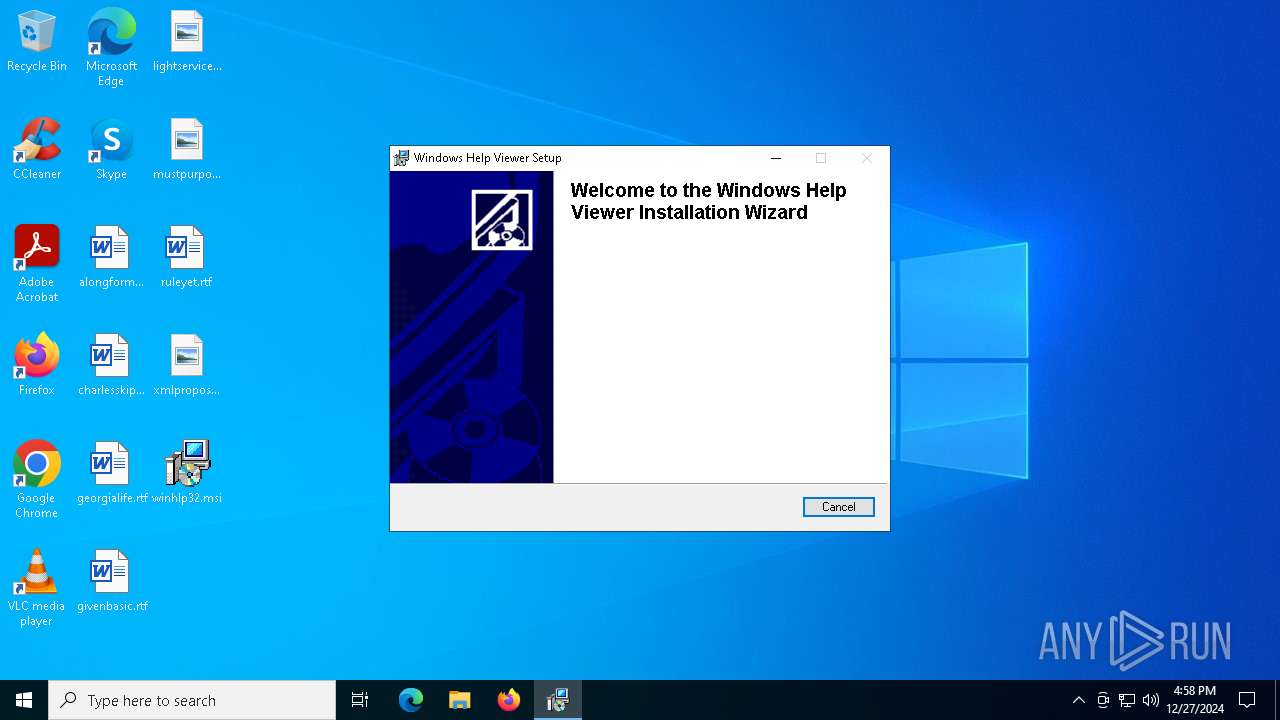
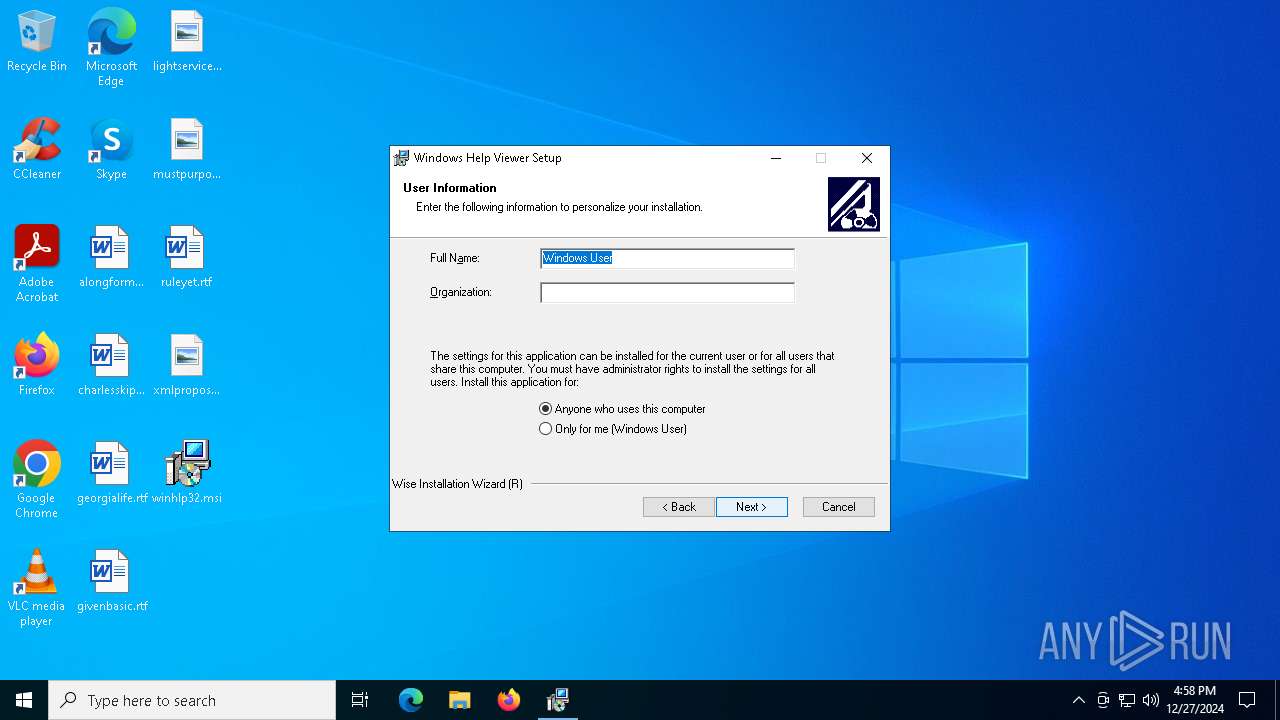
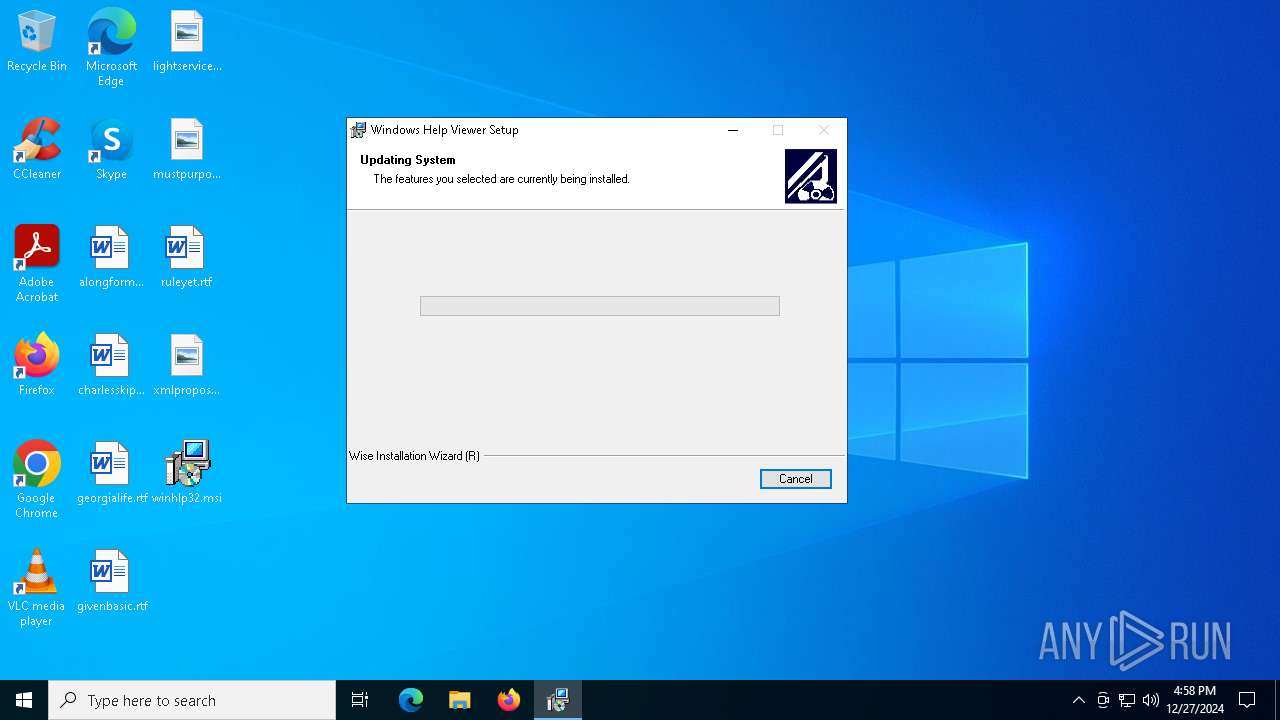
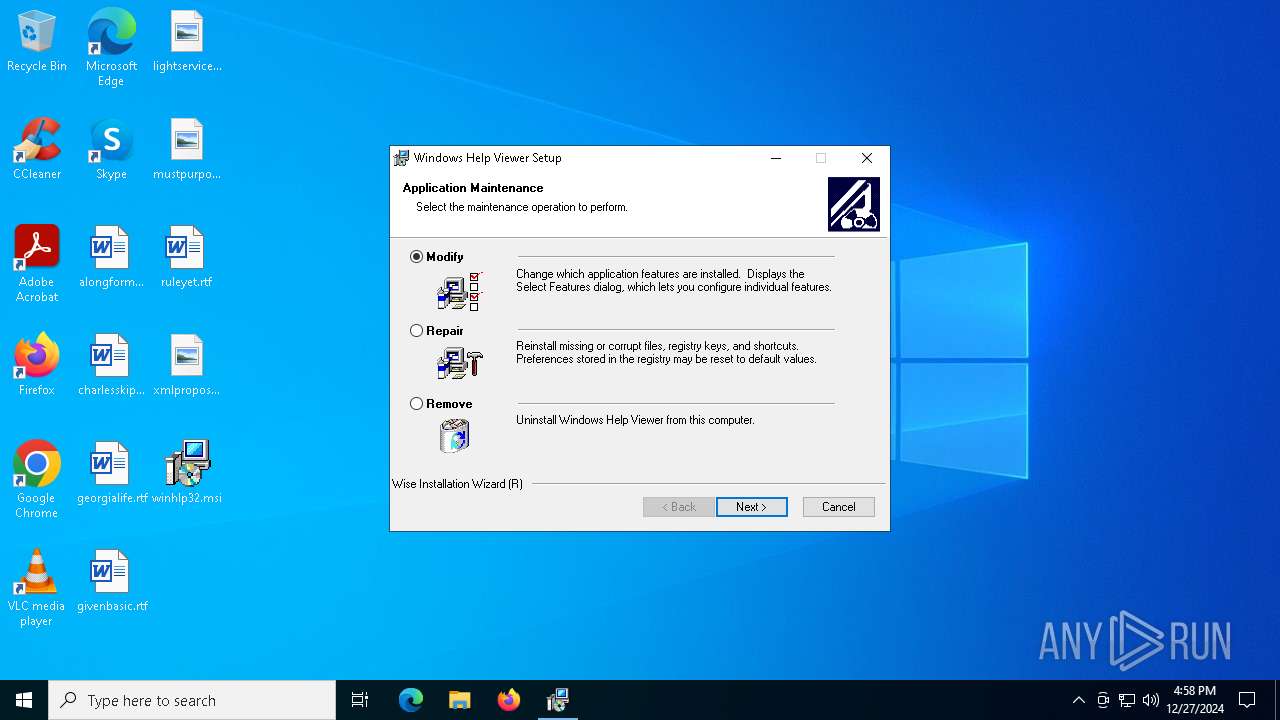
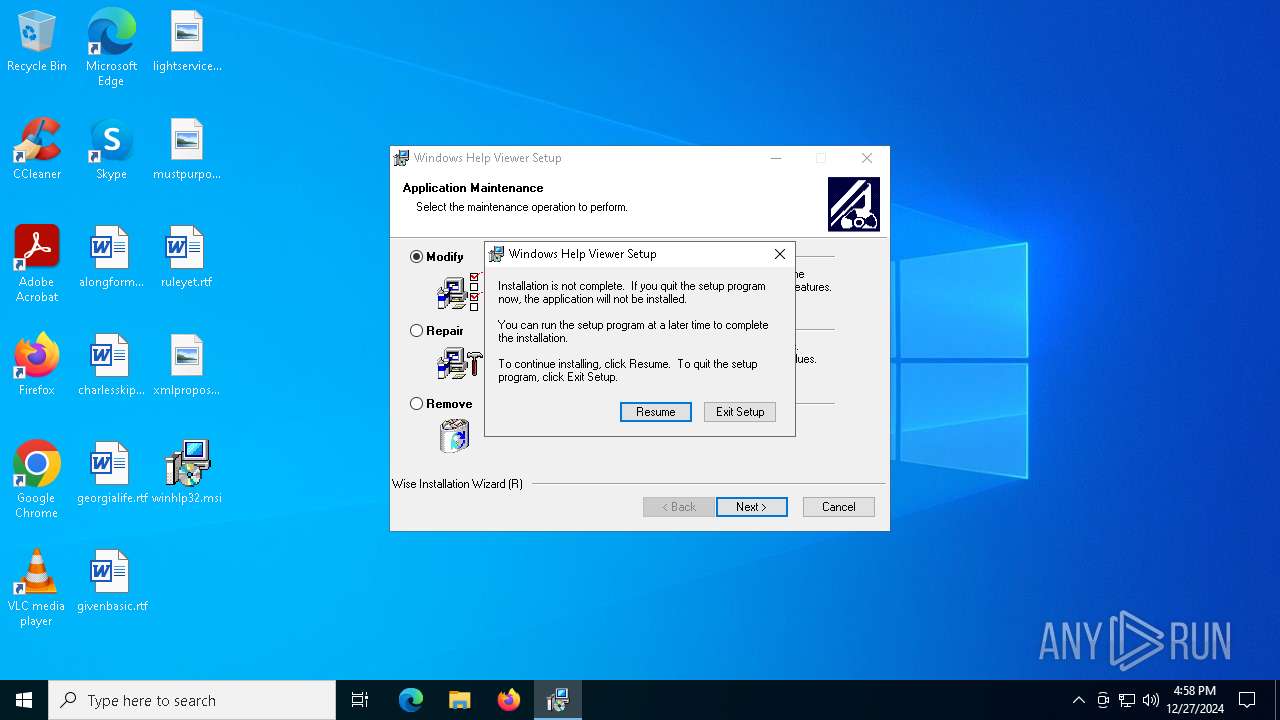
Manual execution by a user
- msiexec.exe (PID: 6536)
The sample compiled with korean language support
- msiexec.exe (PID: 6172)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msi | | | Microsoft Windows Installer (88.6) |
|---|---|---|
| .mst | | | Windows SDK Setup Transform Script (10) |
| .msi | | | Microsoft Installer (100) |
EXIF
FlashPix
| CodePage: | Windows Latin 1 (Western European) |
|---|---|
| Software: | Windows Installer Editor Standalone |
| ModifyDate: | 2018:11:28 19:21:26 |
| LastPrinted: | 61847.7276368 |
| Title: | Installation Database |
| Subject: | Windows Help Viewer |
| Author: | Microsoft Corporation |
| Keywords: | - |
| Comments: | - |
| Template: | Intel;1033 |
| LastModifiedBy: | nvicoadm |
| RevisionNumber: | {55F80DCA-BAC3-4E7A-AA2D-2A6E16101BB1} |
| Pages: | 200 |
| Words: | 2 |
Total processes
138
Monitored processes
9
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1412 | C:\WINDOWS\system32\srtasks.exe ExecuteScopeRestorePoint /WaitForRestorePoint:11 | C:\Windows\System32\SrTasks.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Windows System Protection background tasks. Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2828 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | SrTasks.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4876 | C:\Windows\syswow64\MsiExec.exe -Embedding 9D8DBC5E7C11589739F33E8C40748CAC | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5488 | "C:\Windows\System32\msiexec.exe" /i C:\Users\admin\Desktop\winhlp32.msi | C:\Windows\System32\msiexec.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6172 | C:\WINDOWS\system32\msiexec.exe /V | C:\Windows\System32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6220 | C:\Windows\syswow64\MsiExec.exe -Embedding 304971F4C9E70FF3BFFB3E4537D634E6 C | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6536 | "C:\WINDOWS\System32\msiexec.exe" /i "C:\Users\admin\Desktop\winhlp32.msi" | C:\Windows\System32\msiexec.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 1602 Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6780 | C:\Windows\syswow64\MsiExec.exe -Embedding 69CB6C13E5B6822544631C747C0E8EDF C | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6896 | C:\WINDOWS\system32\vssvc.exe | C:\Windows\System32\VSSVC.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
3 651
Read events
3 304
Write events
330
Delete events
17
Modification events
| (PID) Process: | (6172) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 48000000000000006FEFC6818058DB011C180000E01A0000D50700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6172) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Enter) |
Value: 48000000000000006FEFC6818058DB011C180000E01A0000D20700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6172) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Leave) |
Value: 480000000000000012E104828058DB011C180000E01A0000D20700000100000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6172) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Enter) |
Value: 480000000000000012E104828058DB011C180000E01A0000D10700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6172) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Leave) |
Value: 4800000000000000854407828058DB011C180000E01A0000D10700000100000000000000010000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6172) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppCreate (Enter) |
Value: 4800000000000000A10C0C828058DB011C180000E01A0000D00700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6896) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\BCD00000000\Objects\{9dea862c-5cdd-4e70-acc1-f32b344d4795}\Elements\11000001 |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (6896) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\COM+ REGDB Writer |
| Operation: | write | Name: | IDENTIFY (Leave) |
Value: 4800000000000000455B44838058DB01F01A00006C1B0000E80300000000000001000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6896) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\BCD00000000\Objects\{9dea862c-5cdd-4e70-acc1-f32b344d4795}\Elements\11000001 |
| Operation: | write | Name: | Element |
Value: 0000000000000000000000000000000006000000000000004800000000000000715E5C2FA985EB1190A89A9B763584210000000000000000745E5C2FA985EB1190A89A9B7635842100000000000000000000000000000000 | |||
| (PID) Process: | (6896) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\BCD00000000\Objects\{9dea862c-5cdd-4e70-acc1-f32b344d4795}\Elements\12000002 |
| Operation: | delete key | Name: | (default) |
Value: | |||
Executable files
61
Suspicious files
18
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6172 | msiexec.exe | C:\System Volume Information\SPP\metadata-2 | — | |
MD5:— | SHA256:— | |||
| 6172 | msiexec.exe | C:\Windows\Installer\13b48e.msi | executable | |
MD5:10BA7330EAB7DBAEC93BEE5112DF47D4 | SHA256:CE4C0FFB97BDAE423D197EC902DB88F298B699E7279F315C0694C7F48A7BD546 | |||
| 6172 | msiexec.exe | C:\Windows\Installer\MSIB78C.tmp | binary | |
MD5:69C34887C8D4D128ED87A2C2A7C425A0 | SHA256:F5B74A6AA25333B12366BD7E9ECA75BB09ADFB7BC8D52BE133EC905046CF60E8 | |||
| 5488 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\MSI548C.tmp | executable | |
MD5:B5DEE73421D4C156143371161173BC3F | SHA256:D3BE2427CA4D43D08C8A8F7575C2B0748092E52F4A976F894746F962CA977841 | |||
| 6172 | msiexec.exe | C:\Windows\Installer\inprogressinstallinfo.ipi | binary | |
MD5:68E53D456AAE3A2C9ABD84557A8663A5 | SHA256:A4F572D036176AB13E53C2A25A09A2E36C7E74569AB17F7FAF19FB3C2B52C1A7 | |||
| 6172 | msiexec.exe | C:\Windows\Installer\MSIB6E0.tmp | executable | |
MD5:B5DEE73421D4C156143371161173BC3F | SHA256:D3BE2427CA4D43D08C8A8F7575C2B0748092E52F4A976F894746F962CA977841 | |||
| 5488 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\MSI6853.tmp | executable | |
MD5:B5DEE73421D4C156143371161173BC3F | SHA256:D3BE2427CA4D43D08C8A8F7575C2B0748092E52F4A976F894746F962CA977841 | |||
| 5488 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\MSI73DE.tmp | executable | |
MD5:B5DEE73421D4C156143371161173BC3F | SHA256:D3BE2427CA4D43D08C8A8F7575C2B0748092E52F4A976F894746F962CA977841 | |||
| 6172 | msiexec.exe | C:\System Volume Information\SPP\snapshot-2 | binary | |
MD5:8341EFA58447673CCDBEF7F063523C45 | SHA256:7A1753C7D066638AD6007F10D317E3F077CE8D055DDEC23F14213BDFCA9BE99E | |||
| 6172 | msiexec.exe | C:\Windows\WinHelp\ftlx041e.dll | executable | |
MD5:9FCB1B145BDE46BBCB3A2AF76350E201 | SHA256:44DE3E1C916C87FE7E2C144BC4B4823BD5BAC65E384BFED615A2197CA95BB7D5 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
34
DNS requests
17
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | GET | 200 | 2.16.241.19:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5064 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
3696 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
3696 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6292 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4308 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4712 | MoUsoCoreWorker.exe | 2.16.241.19:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 88.221.169.152:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
— | — | 88.221.169.152:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5064 | SearchApp.exe | 2.23.209.130:443 | www.bing.com | Akamai International B.V. | GB | whitelisted |
1176 | svchost.exe | 20.190.160.22:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1176 | svchost.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
arc.msn.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |