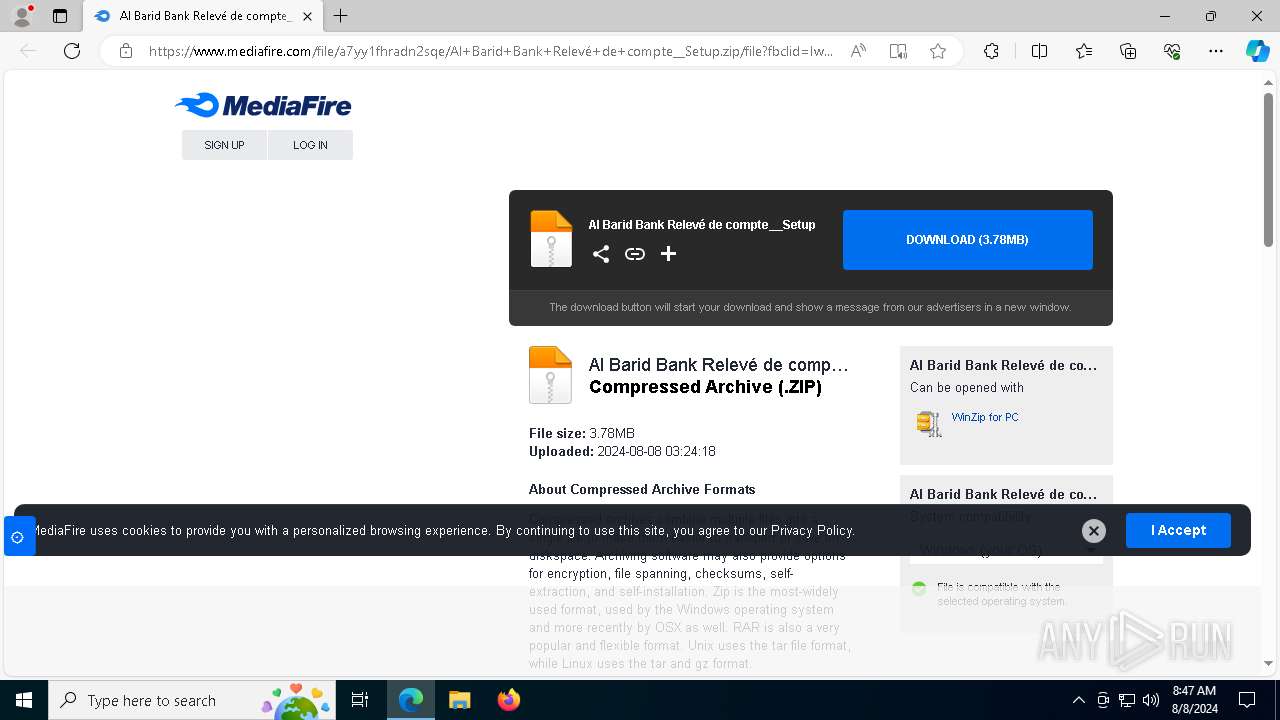
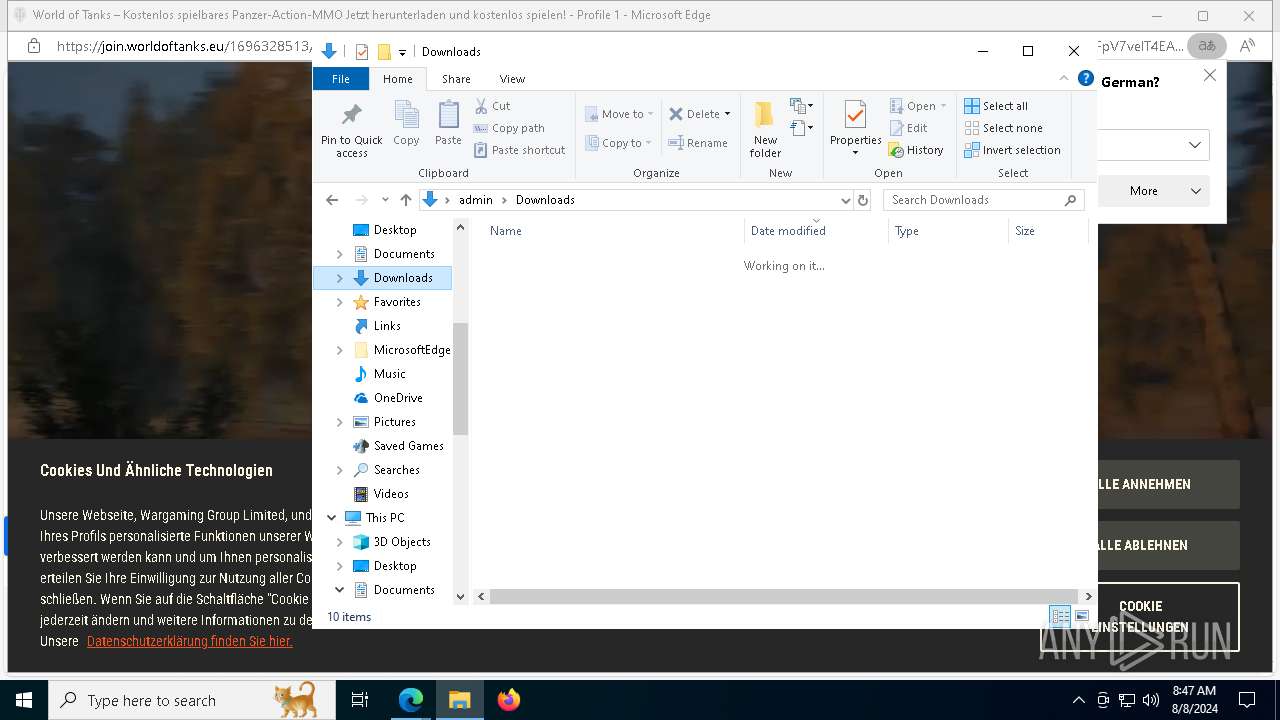
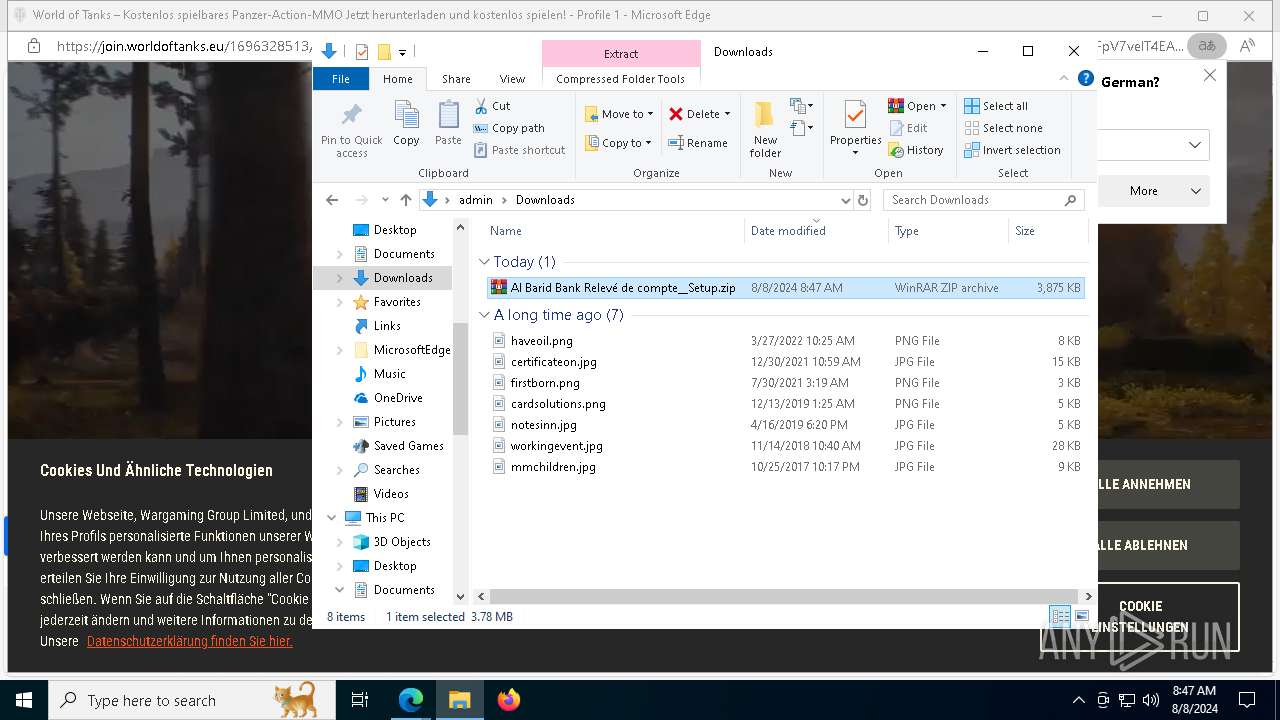
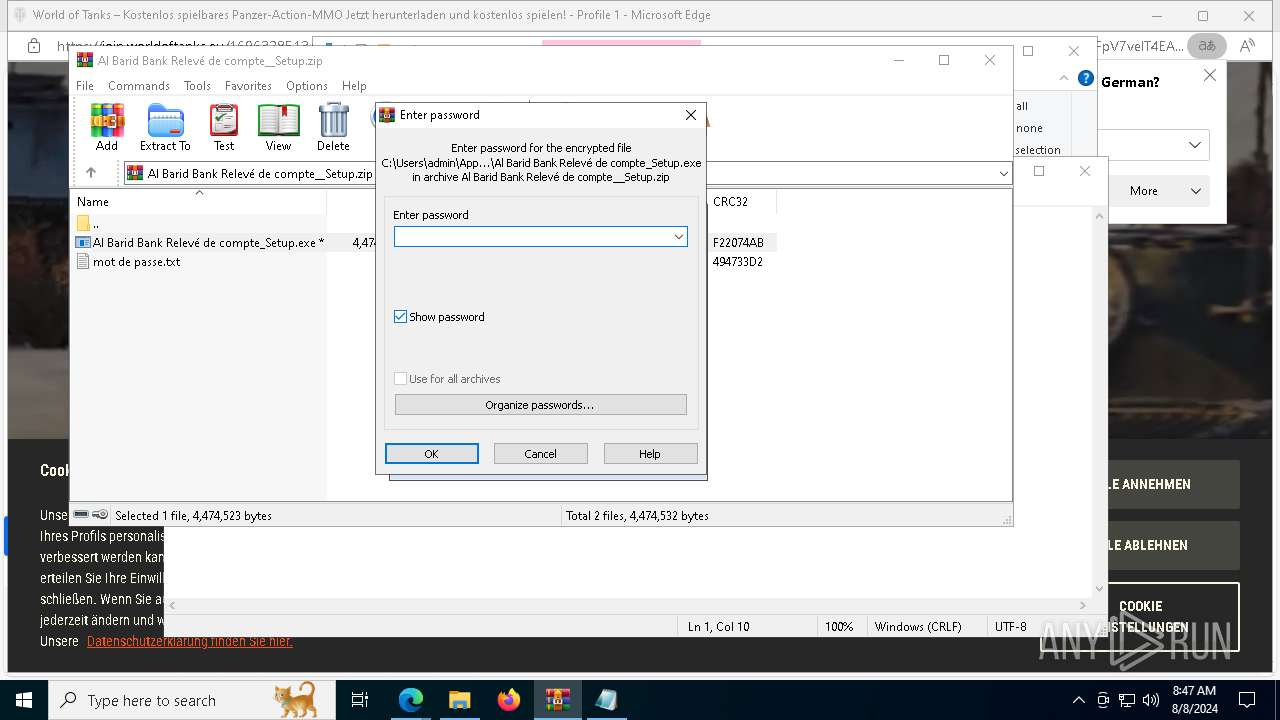
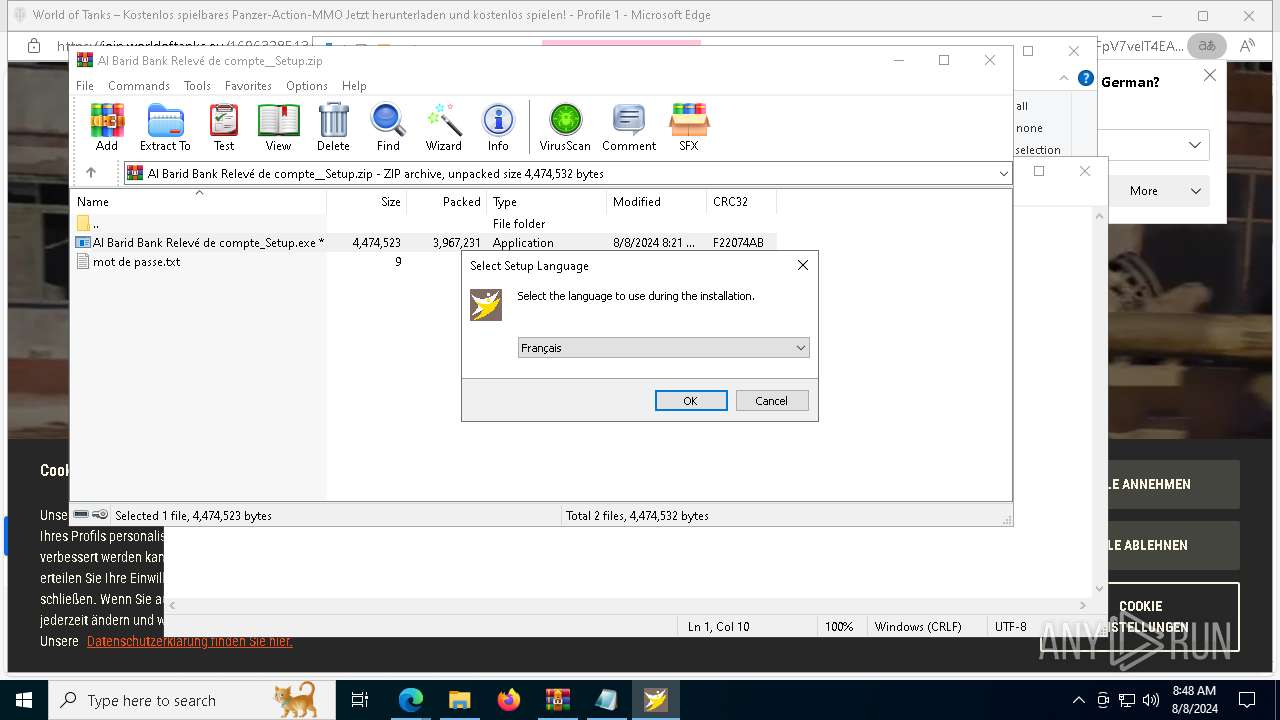
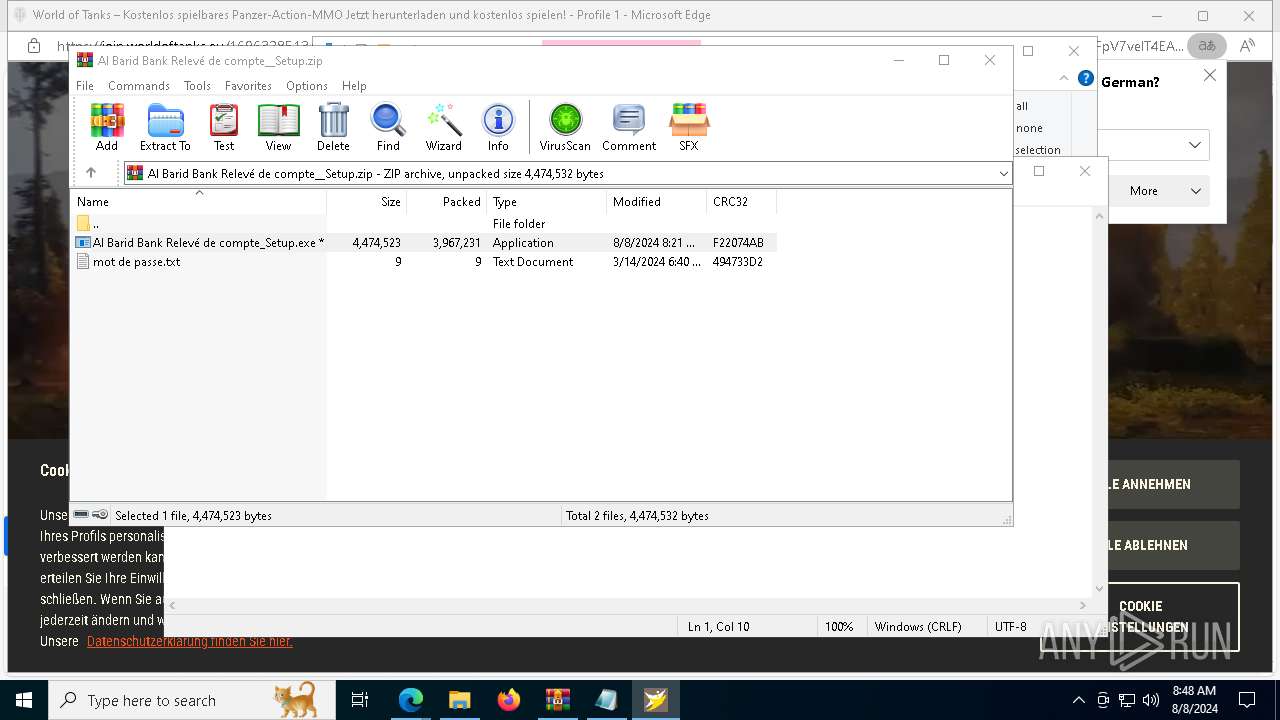
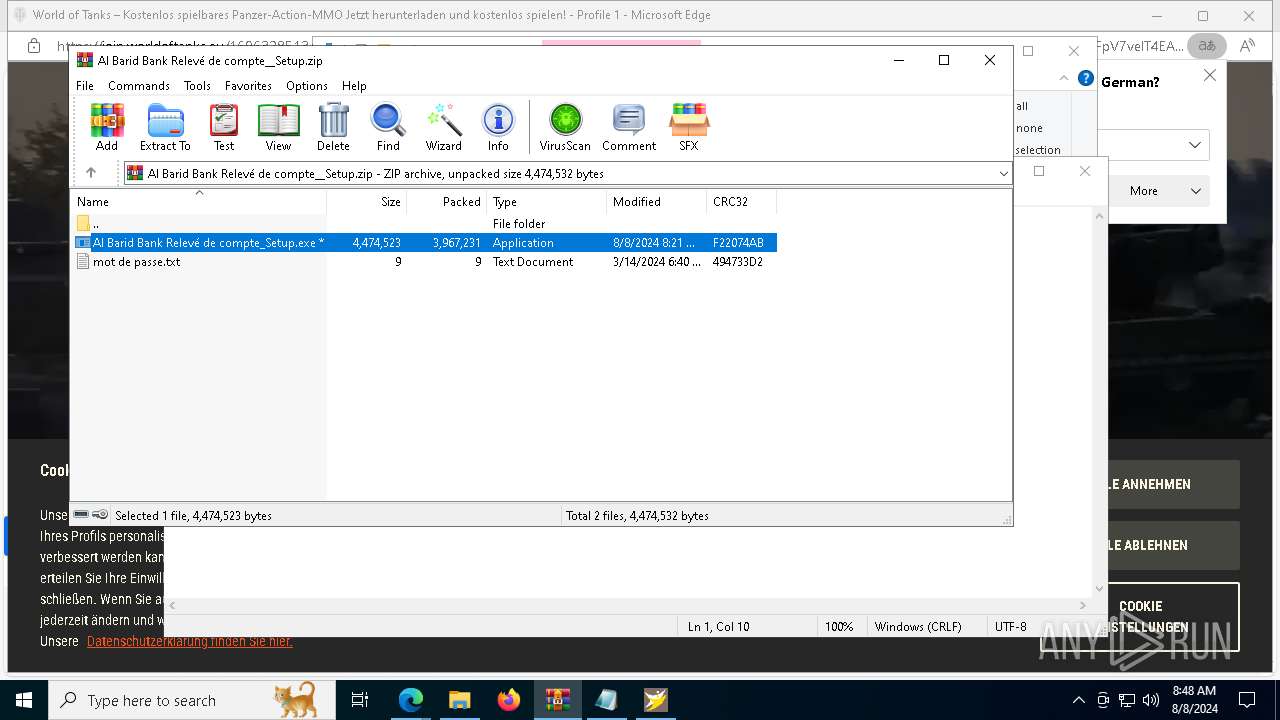
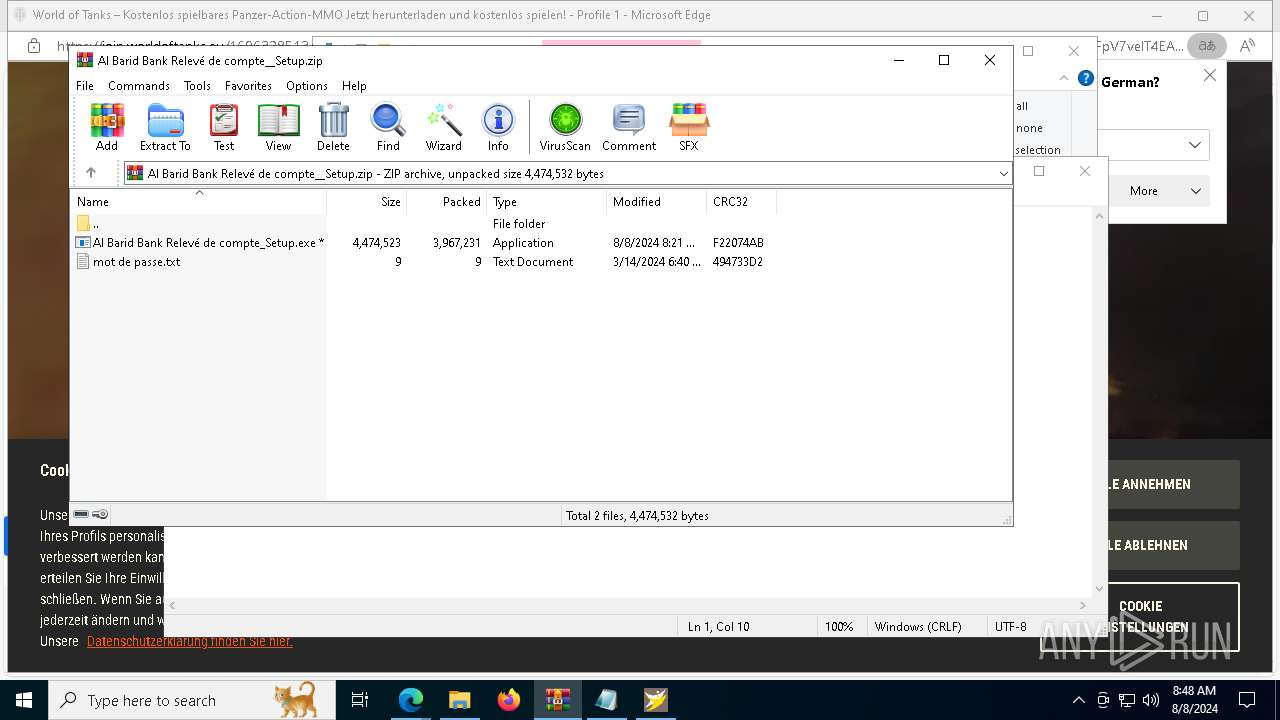
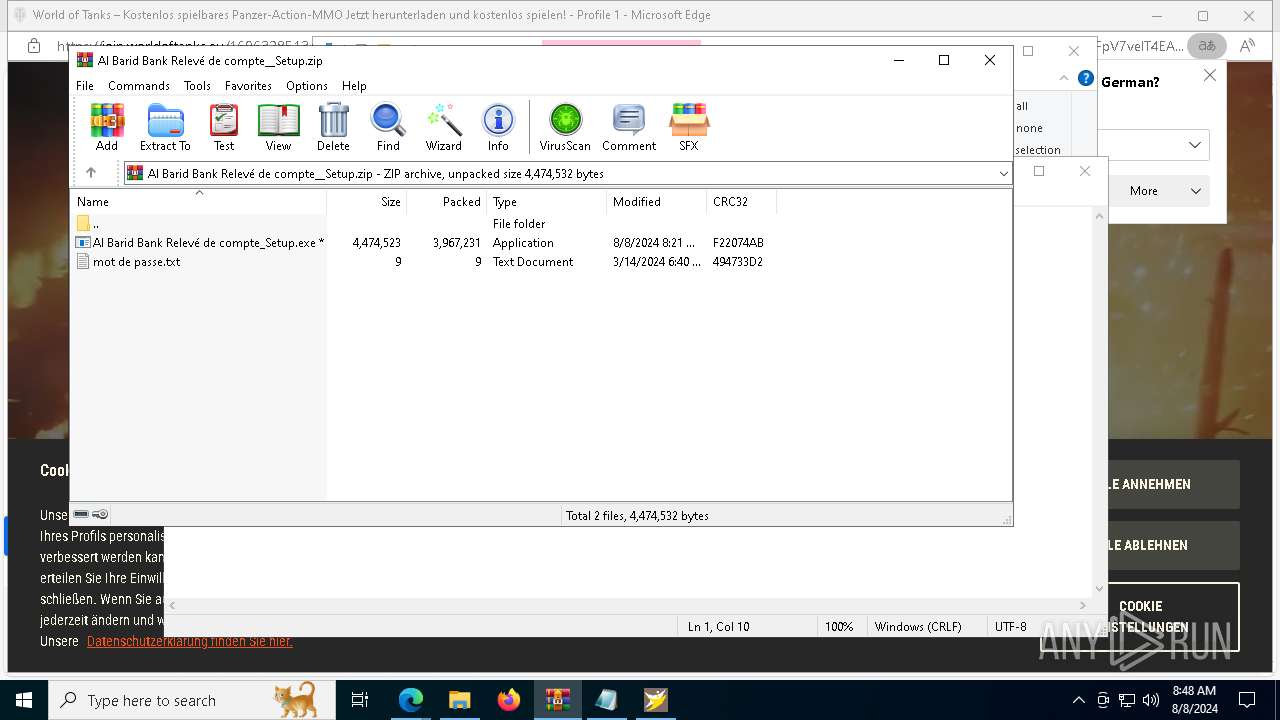
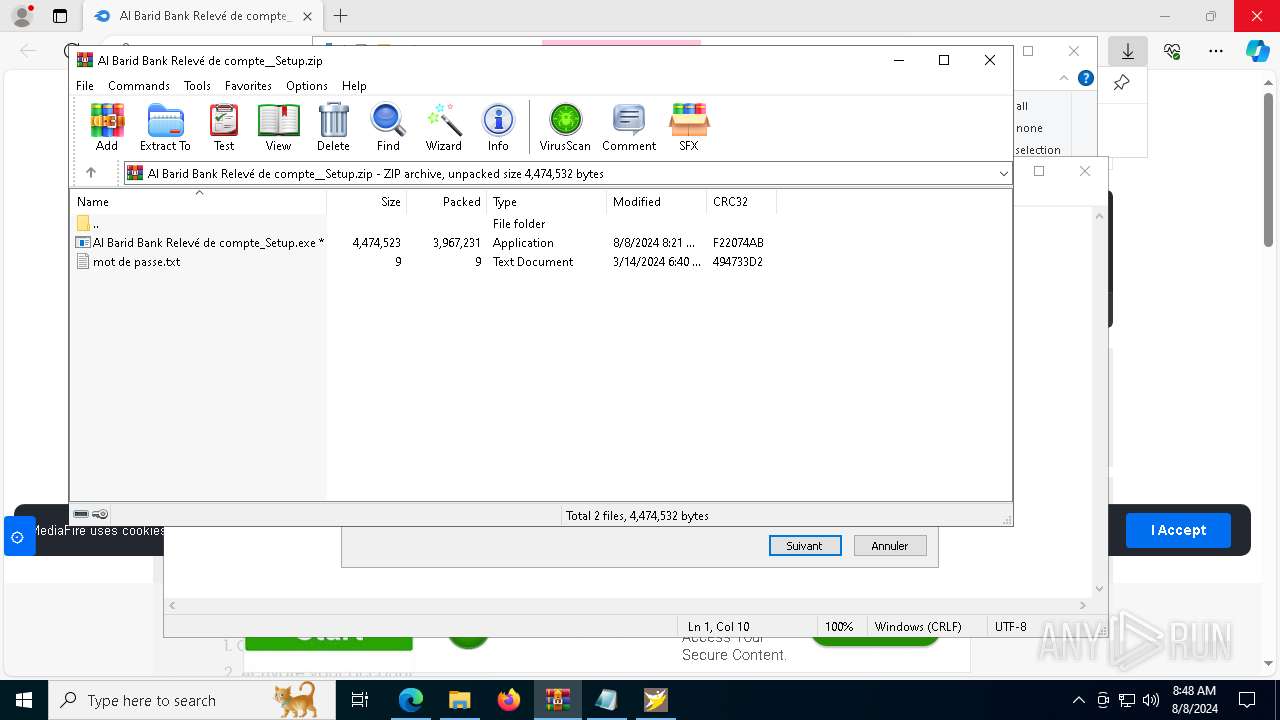
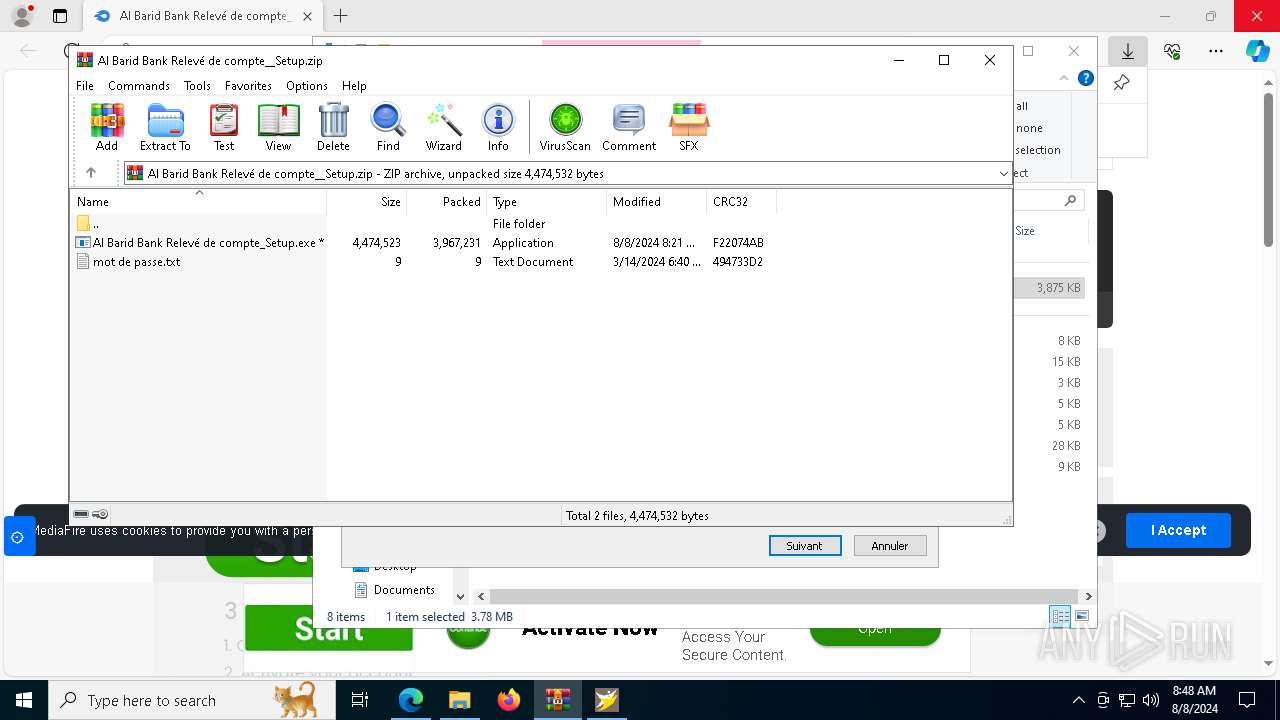
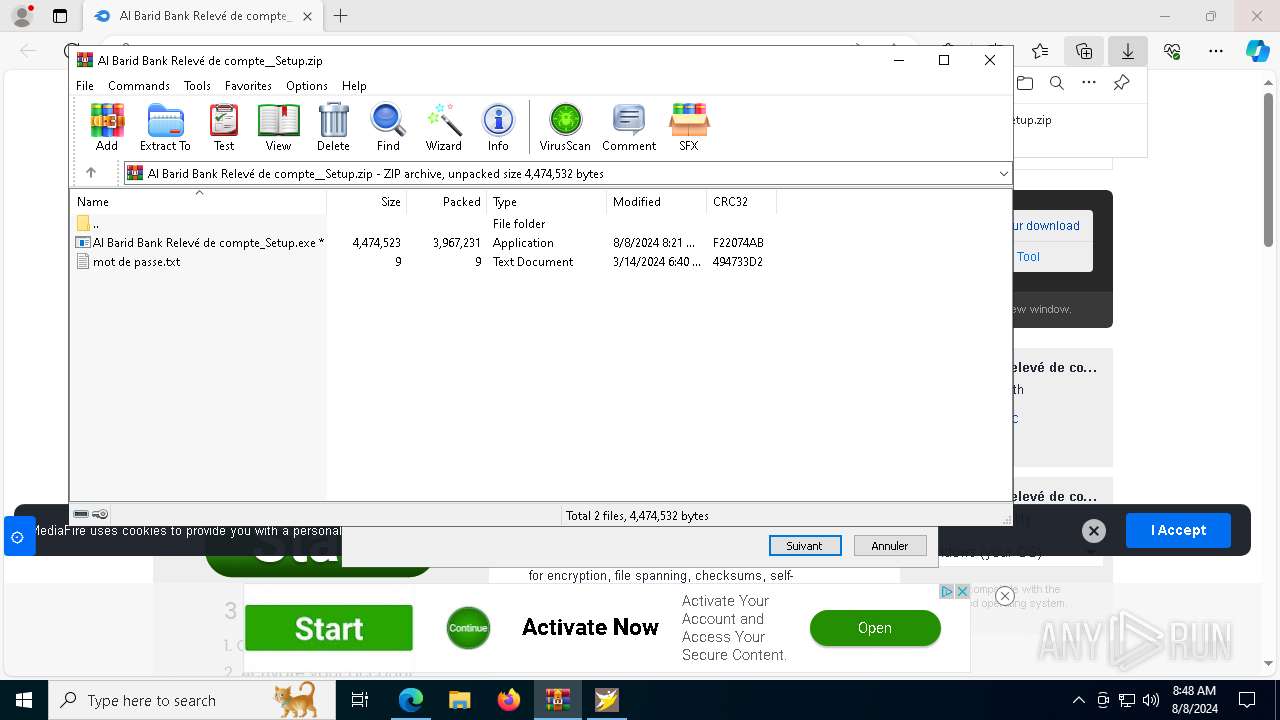
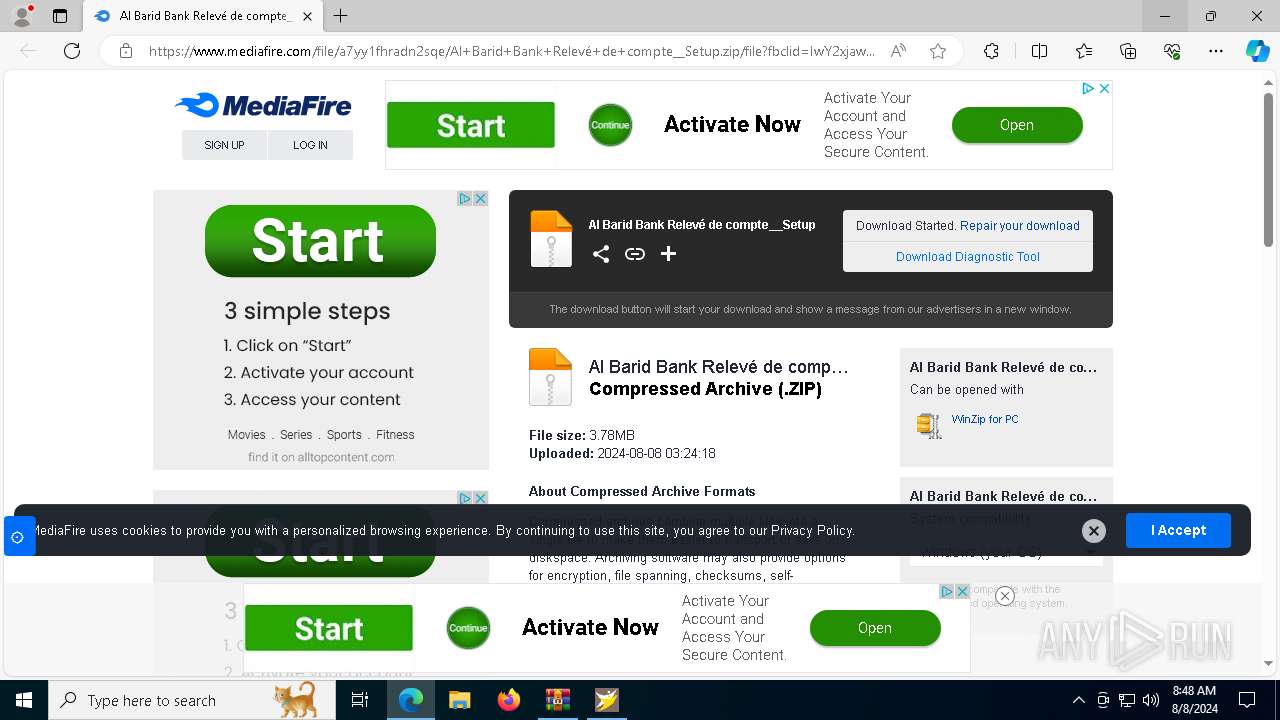
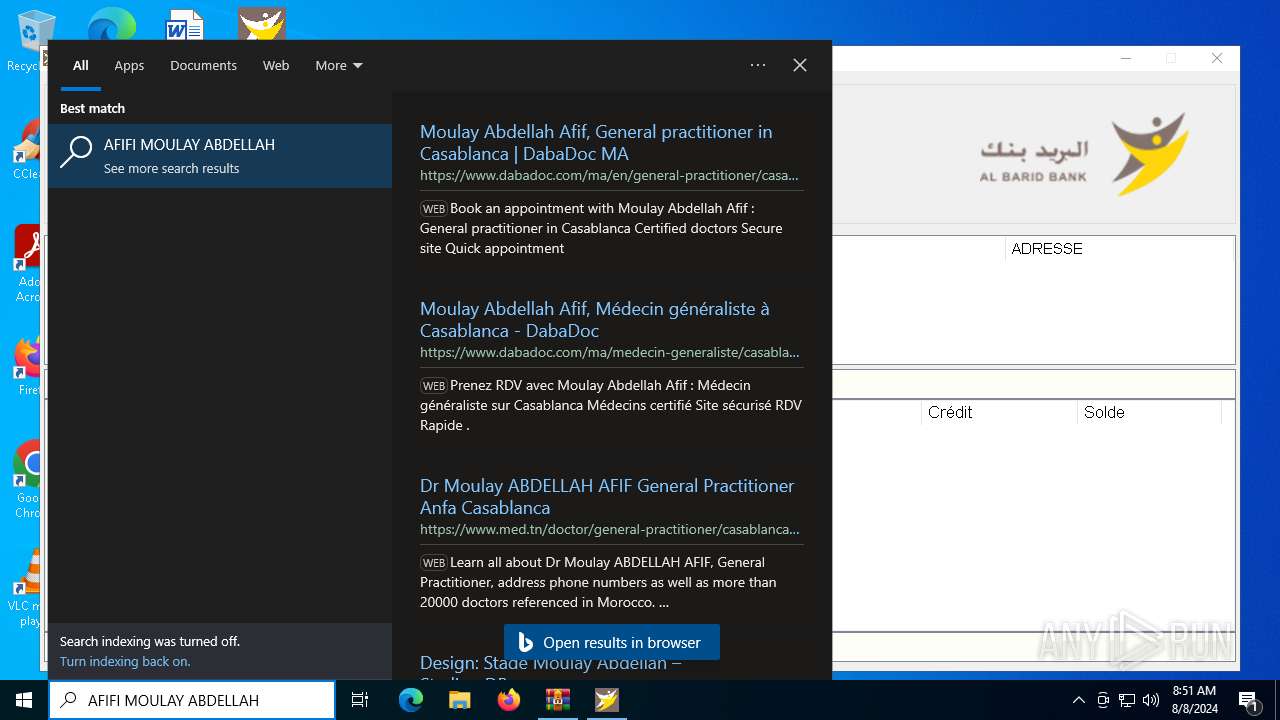
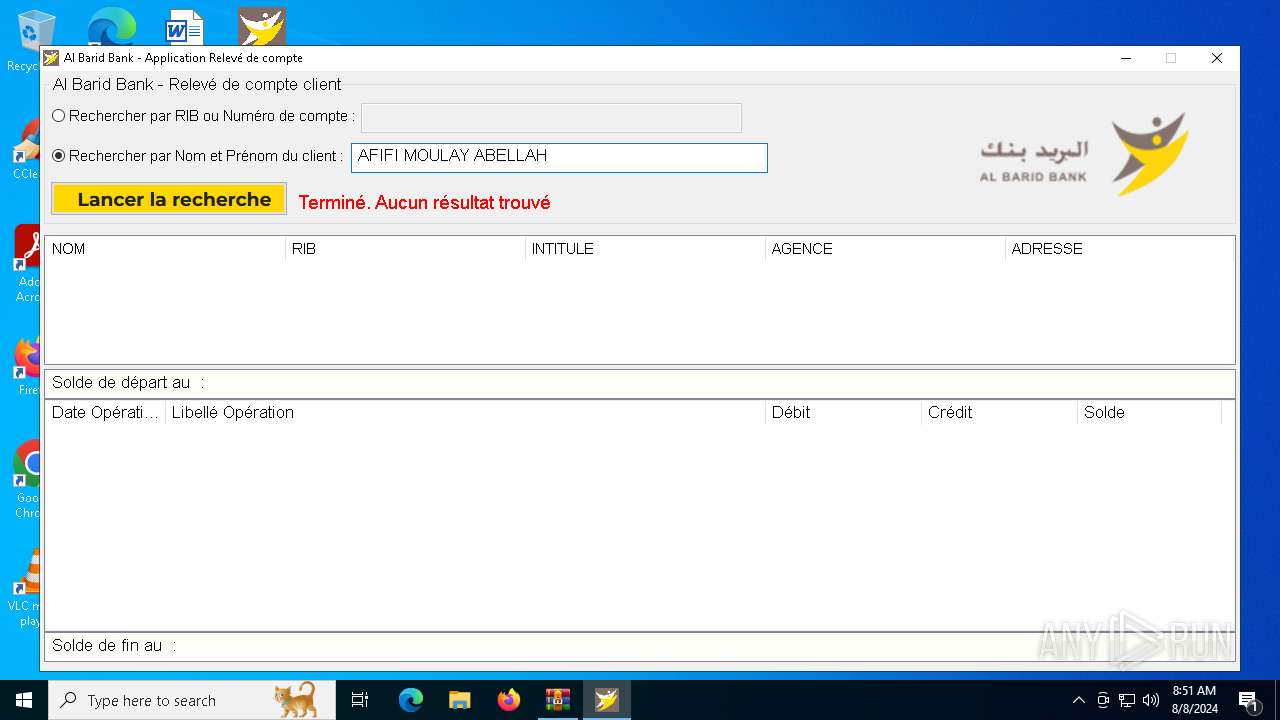
| URL: | https://www.mediafire.com/file/a7yy1fhradn2sqe/Al+Barid+Bank+Relev%C3%A9+de+compte__Setup.zip/file?fbclid=IwY2xjawEhYRVleHRuA2FlbQIxMQABHf5xcu2XKh_XSMQZhvvLFHrbaqqzmD8iyKhHG5CvX2eWlhzCZlfzxwA0-g_aem_jAdKkprIhmEI0hnuAjdFWw |
| Full analysis: | https://app.any.run/tasks/4ec8d252-4829-46a0-bf67-340e6a4ad107 |
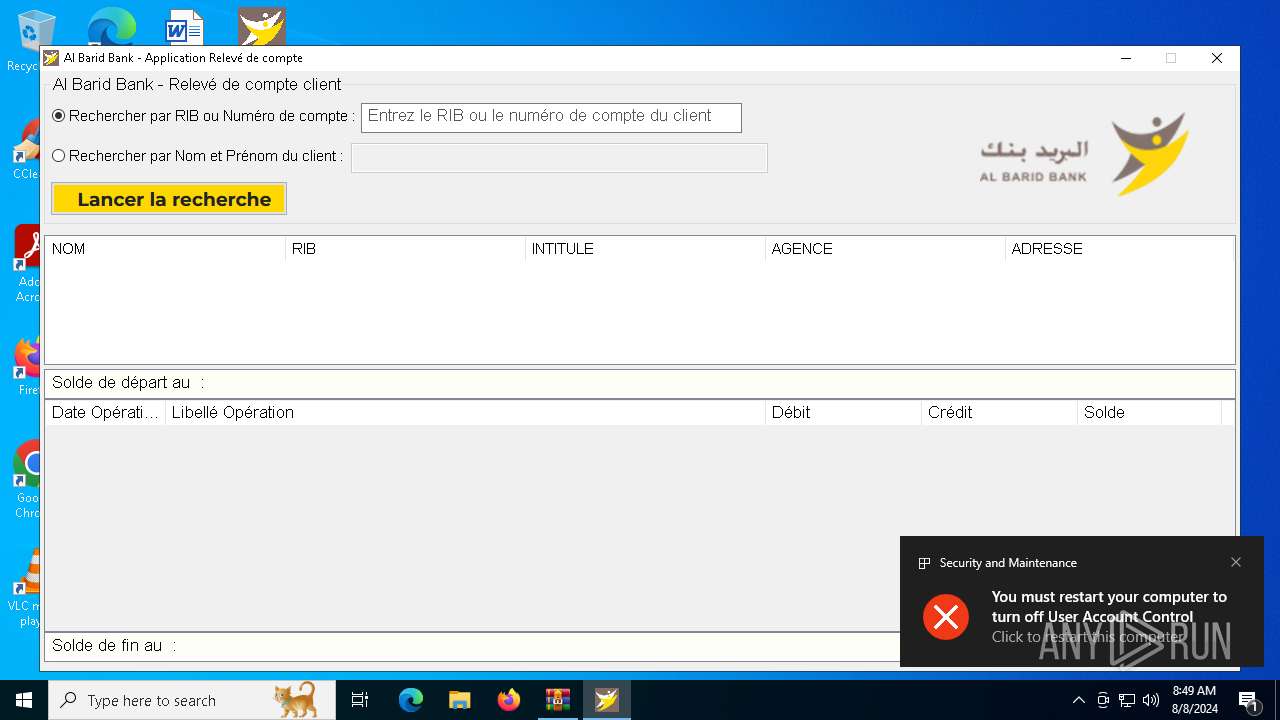
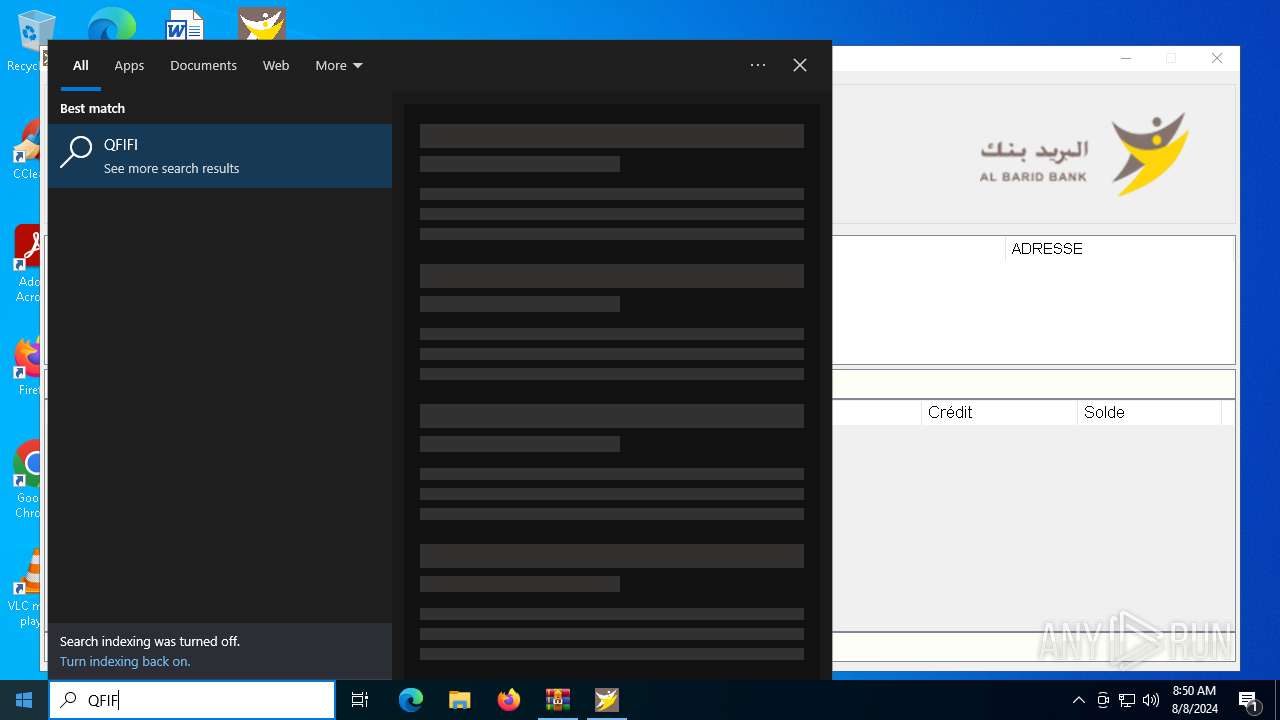
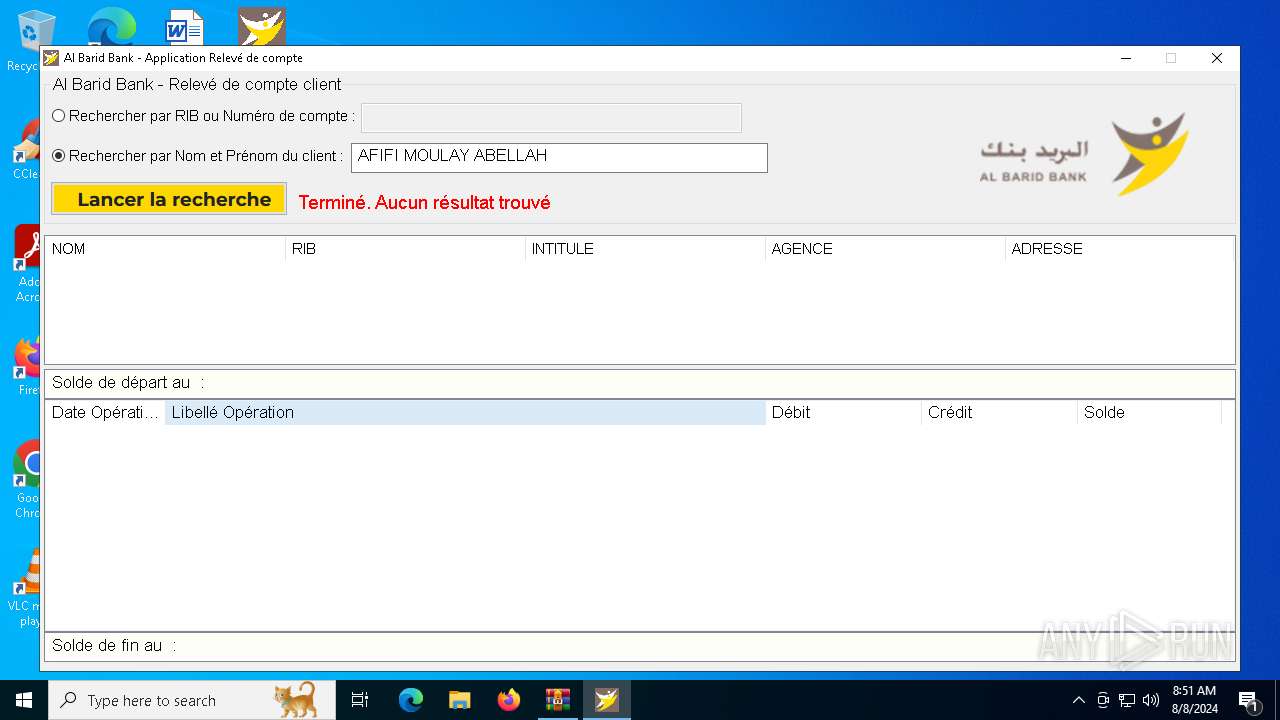
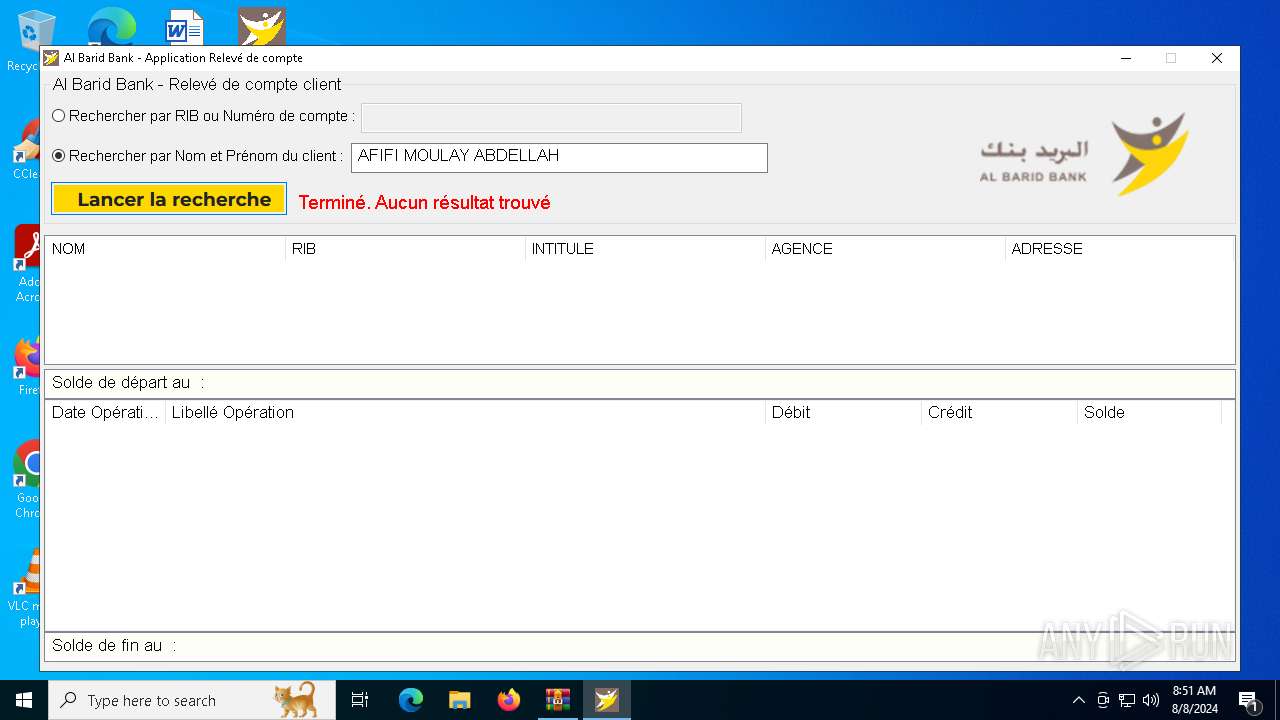
| Verdict: | Malicious activity |
| Analysis date: | August 08, 2024, 08:46:58 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
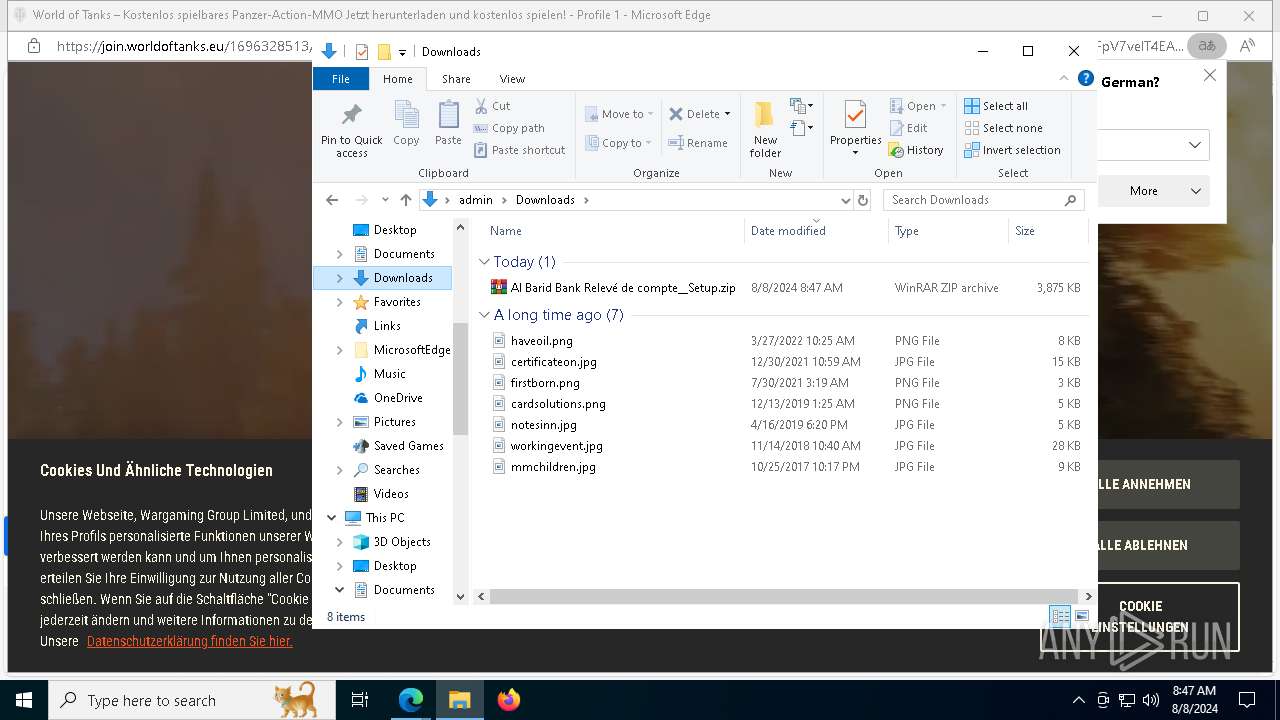
| MD5: | DBFA165F489F470C2114C2236A40356F |
| SHA1: | 8B7FA22265D7FE9E93DA8CAEE8594051F5CC08D1 |
| SHA256: | CE3D8A1B7FEBCCE9C7F953C54276E991E4B9A9992357F8081FB95E9F16FBB97A |
| SSDEEP: | 6:2OLw3eGMZuvzqELsOpq2AywBwZigYferg6j/v59:273eRi/qnyw6ZigYfergg/v |
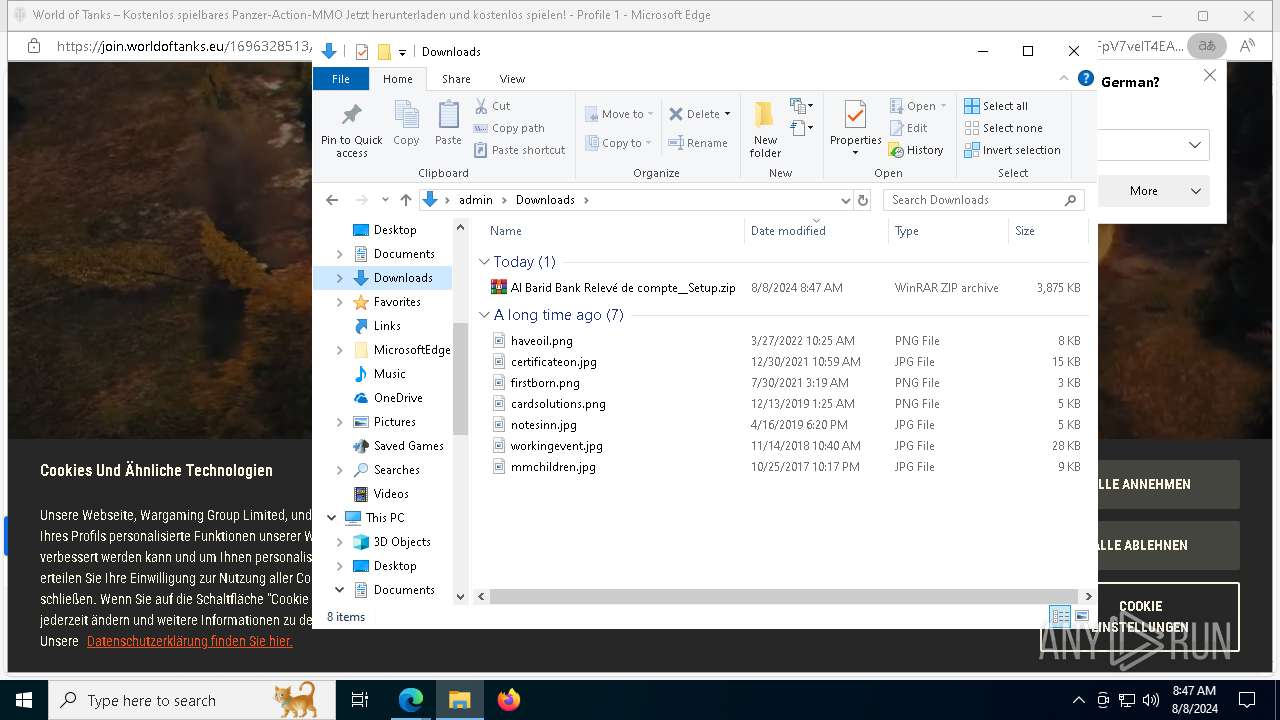
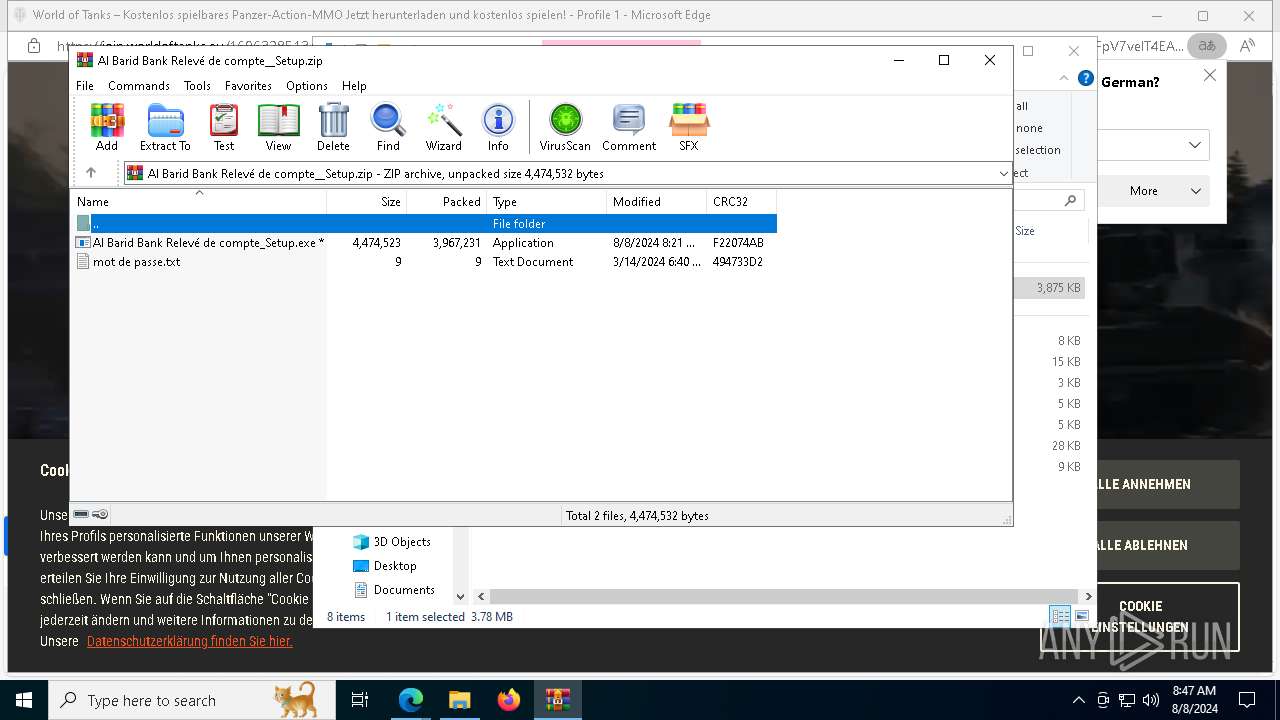
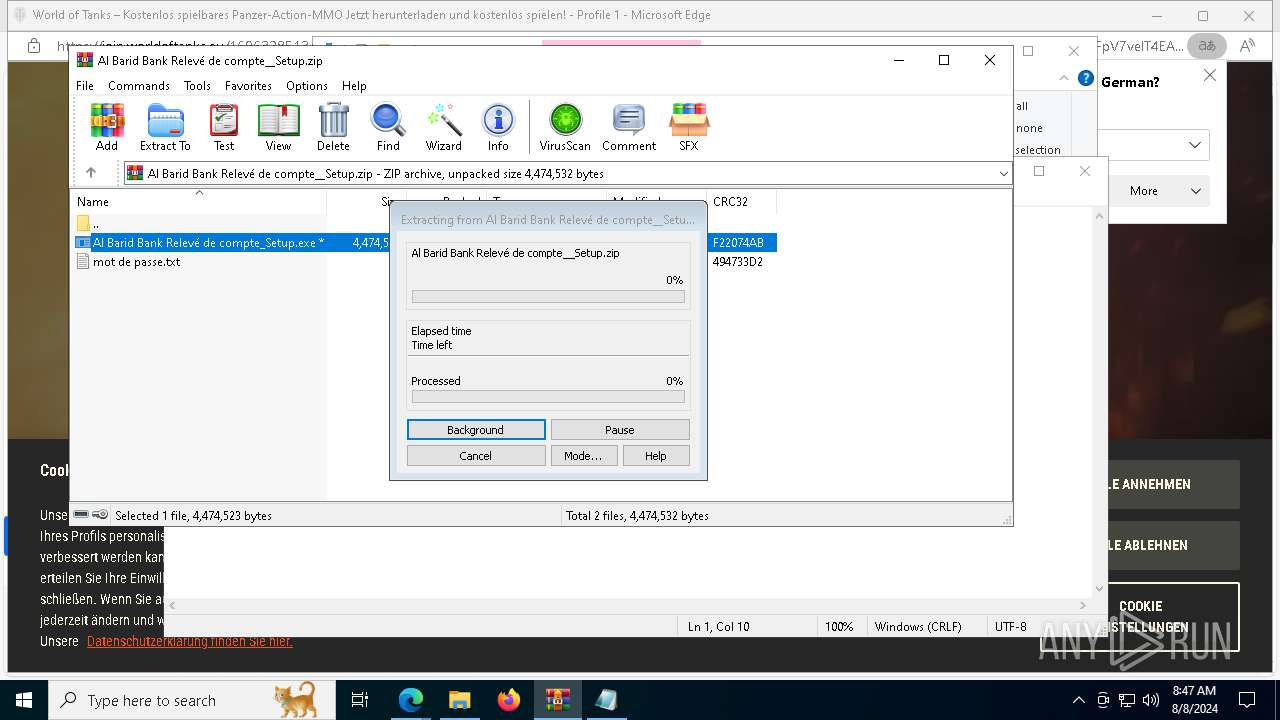
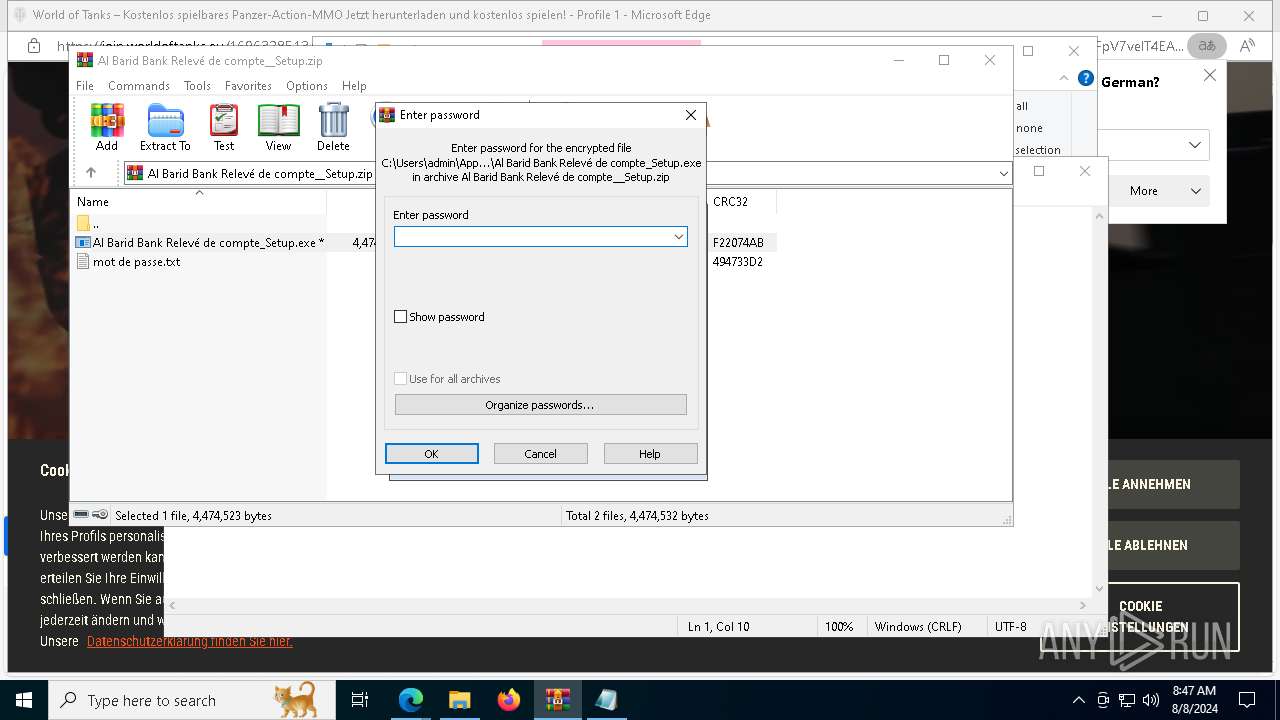
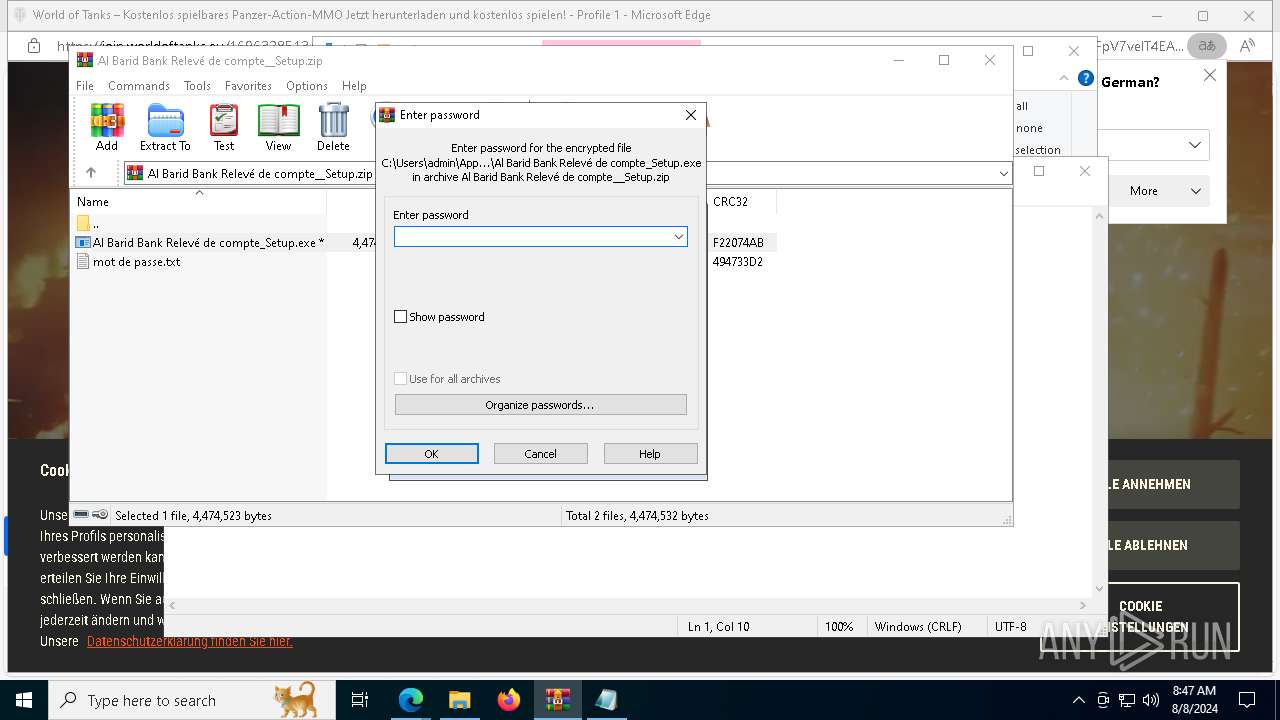
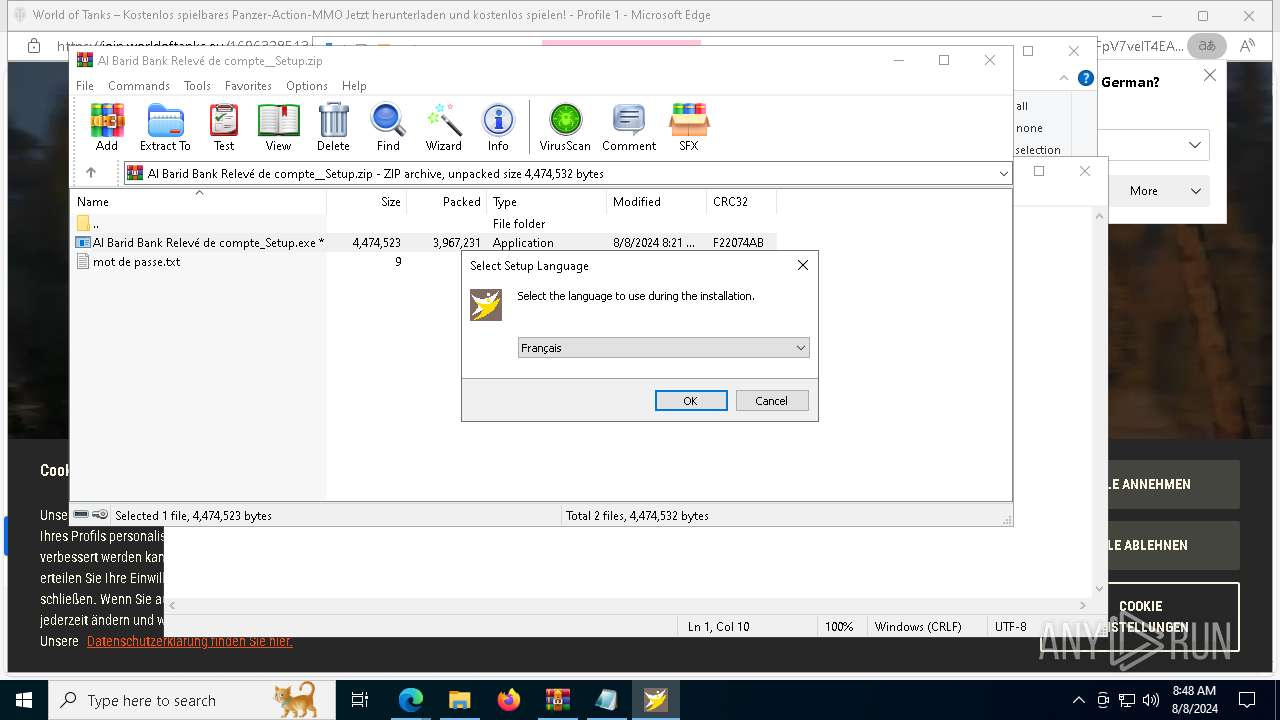
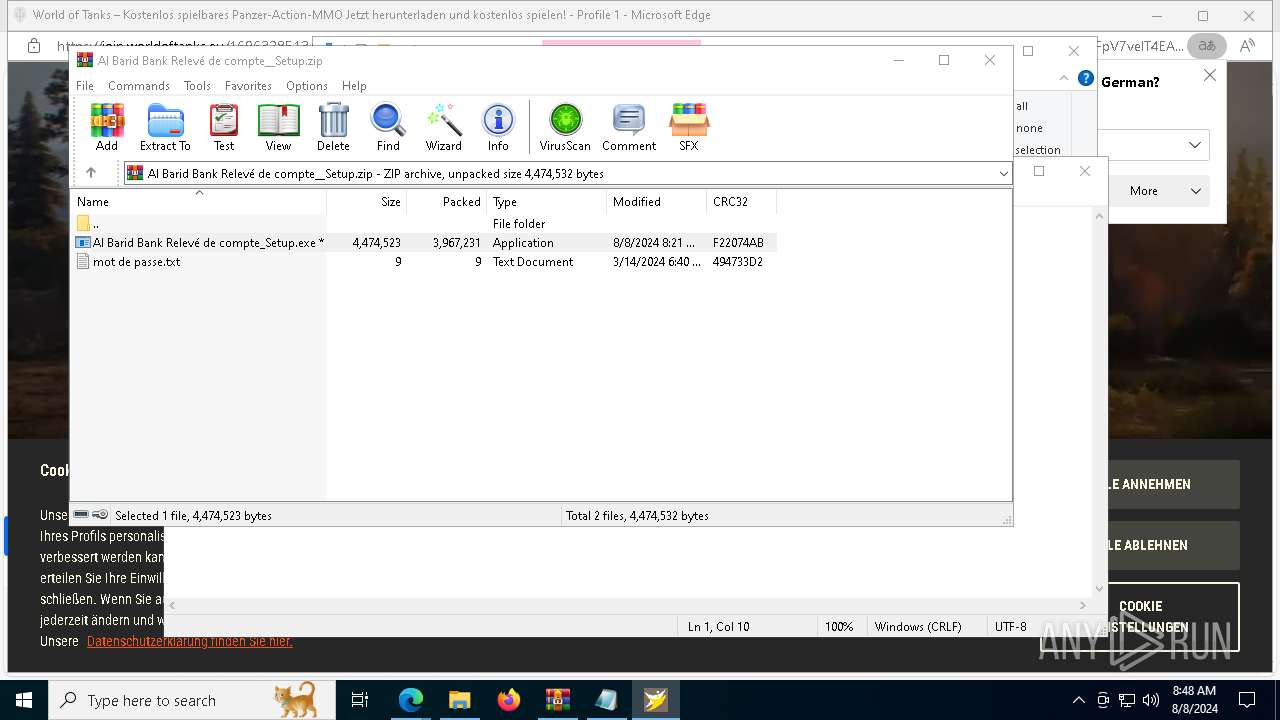
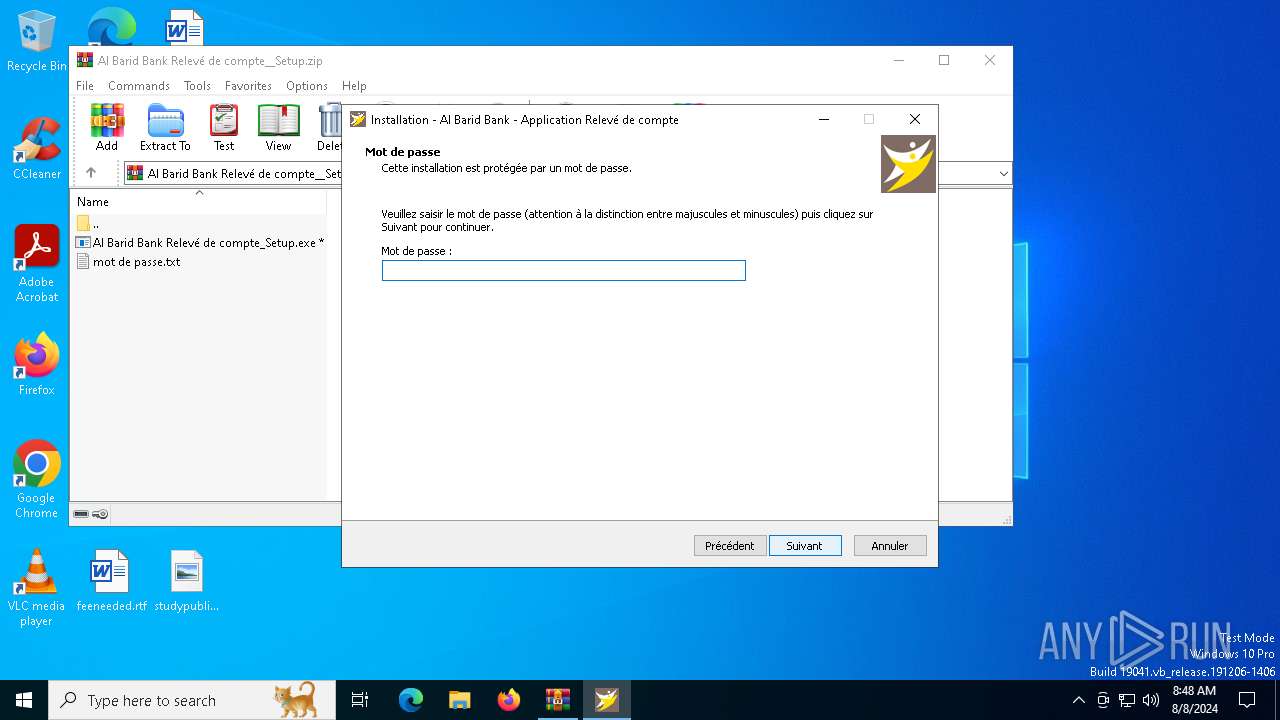
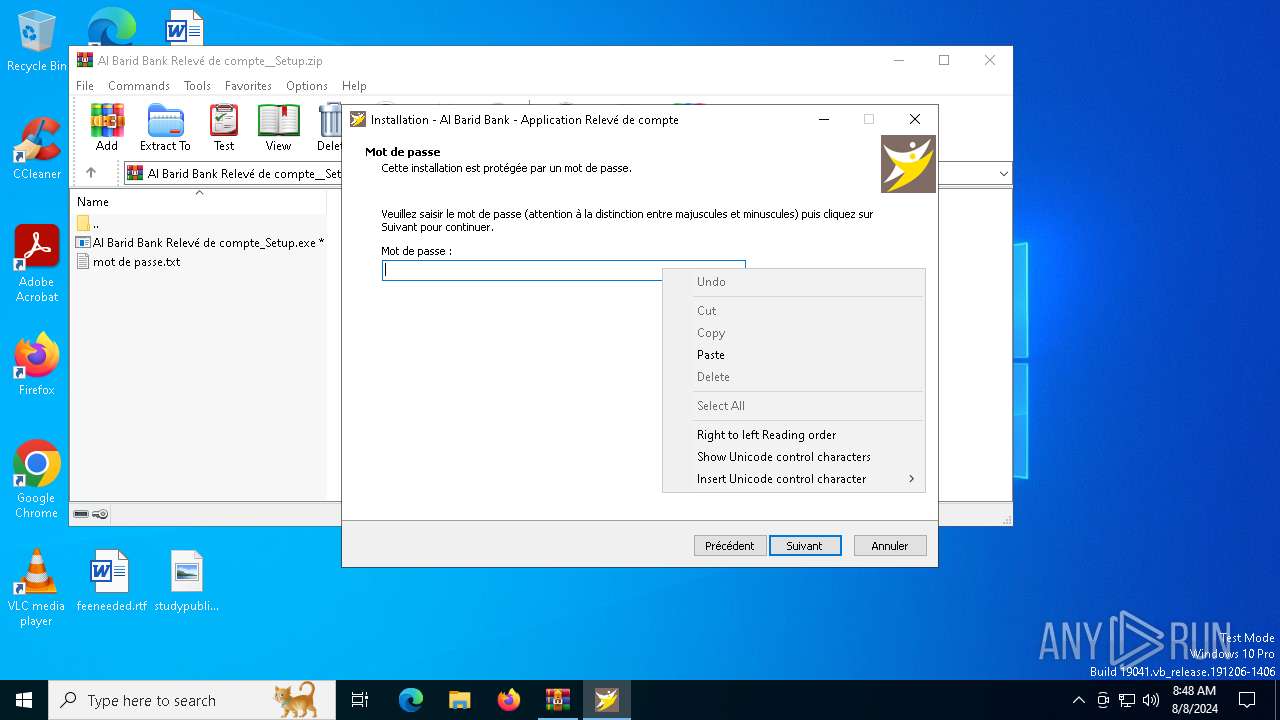
MALICIOUS
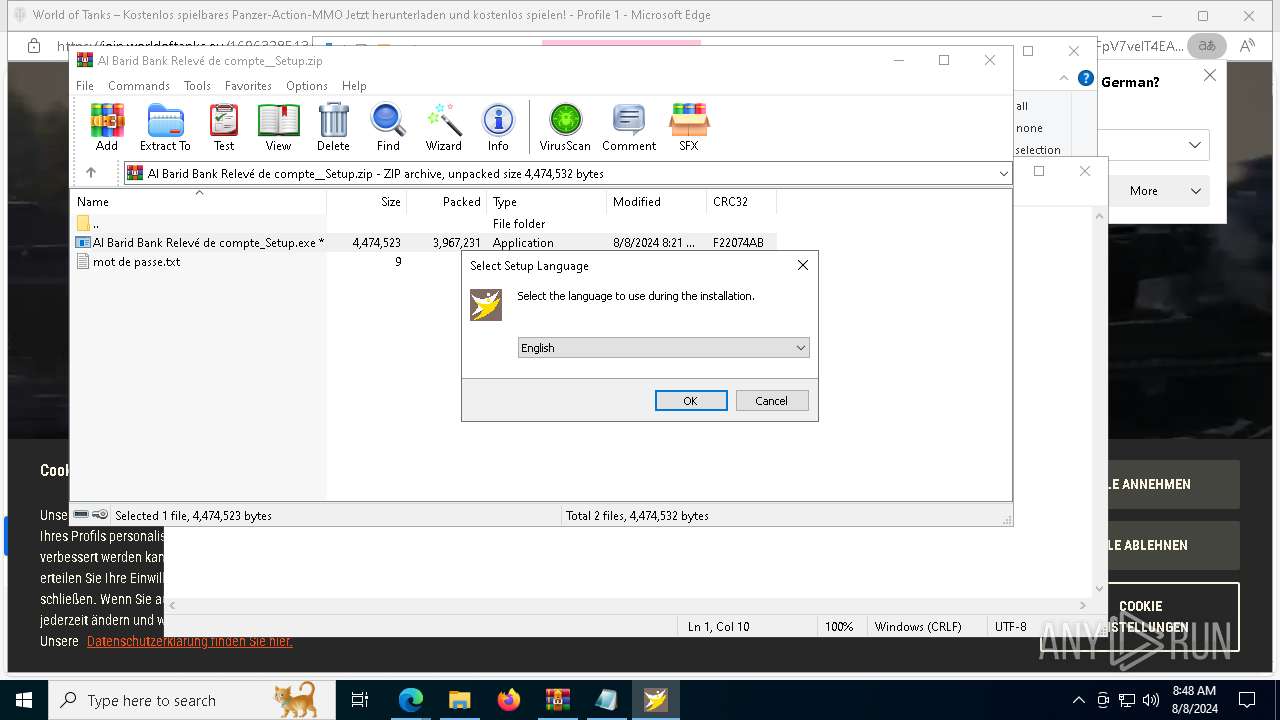
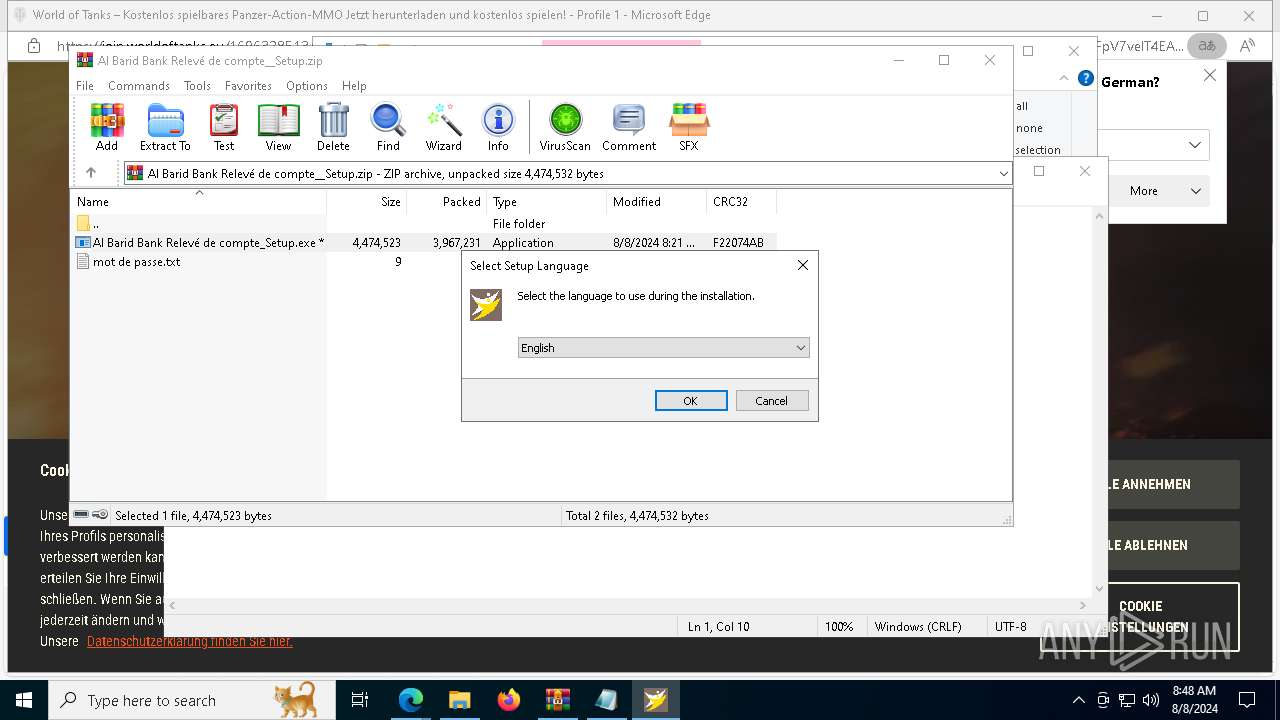
Drops the executable file immediately after the start
- Al Barid Bank Relevé de compte_Setup.exe (PID: 5852)
- Al Barid Bank Relevé de compte_Setup.exe (PID: 8796)
- Al Barid Bank Relevé de compte_Setup.tmp (PID: 8784)
- admin_microsoft_account.exe (PID: 6644)
Adds path to the Windows Defender exclusion list
- Al Barid Bank Relevé de compte_Setup.tmp (PID: 8784)
- admin_microsoft_account.exe (PID: 6644)
Changes powershell execution policy (Bypass)
- Al Barid Bank Relevé de compte_Setup.tmp (PID: 8784)
- admin_microsoft_account.exe (PID: 6644)
Changes the autorun value in the registry
- admin_microsoft_account.exe (PID: 6644)
- securitysvc.exe (PID: 6680)
- securitysvc.exe (PID: 2336)
Bypass execution policy to execute commands
- powershell.exe (PID: 2876)
- powershell.exe (PID: 1248)
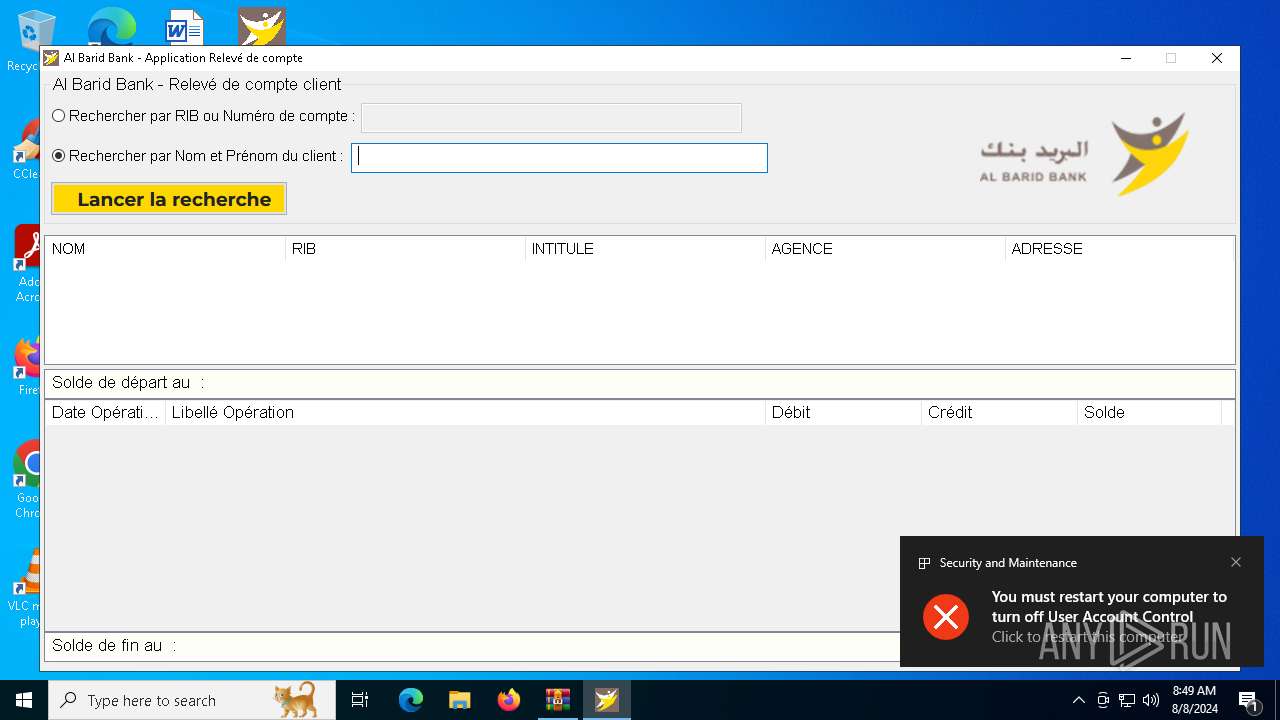
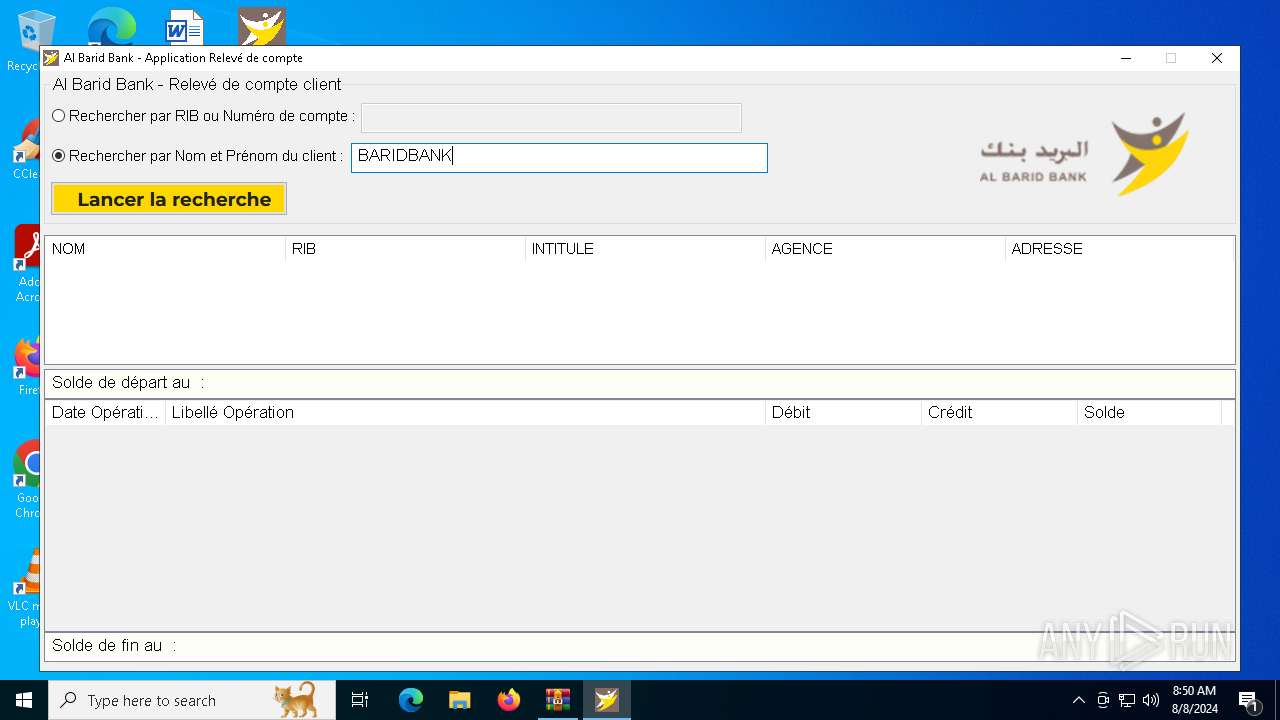
UAC/LUA settings modification
- reg.exe (PID: 8396)
Uses Task Scheduler to run other applications
- admin_microsoft_account.exe (PID: 6644)
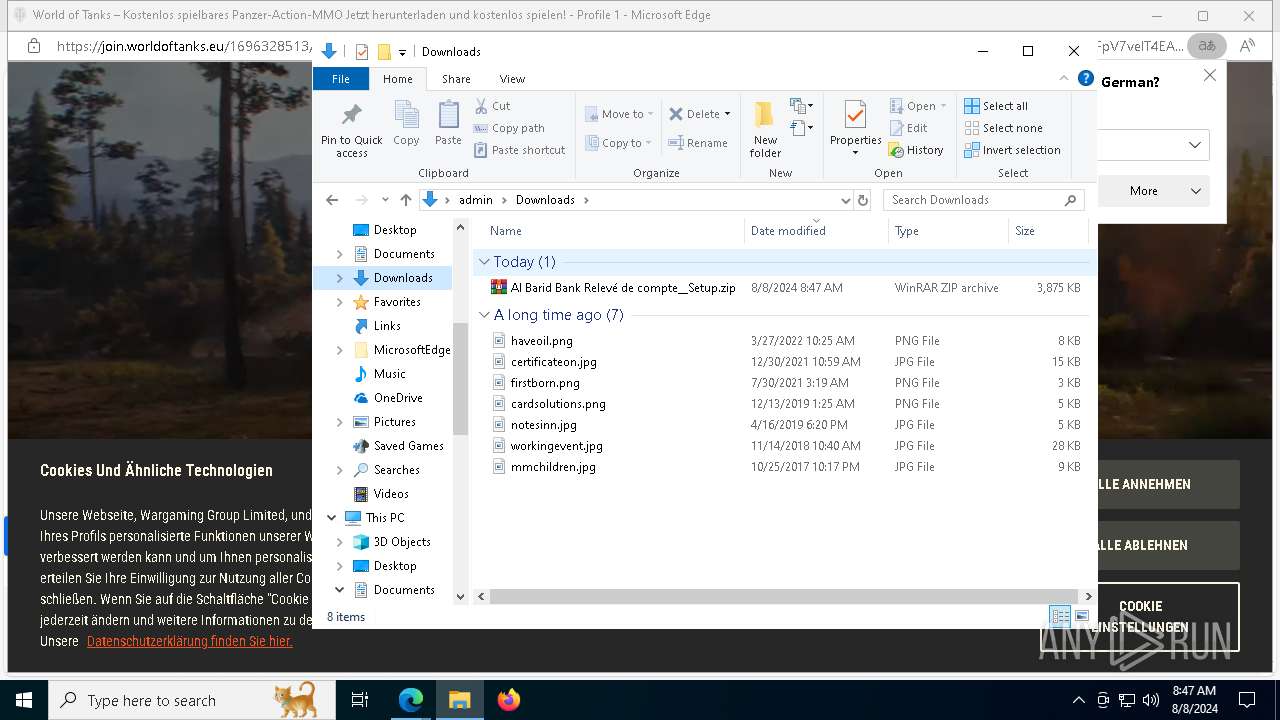
SUSPICIOUS
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 9148)
- Al Barid Bank Relevé de compte_Setup.tmp (PID: 5920)
- ShellExperienceHost.exe (PID: 7704)
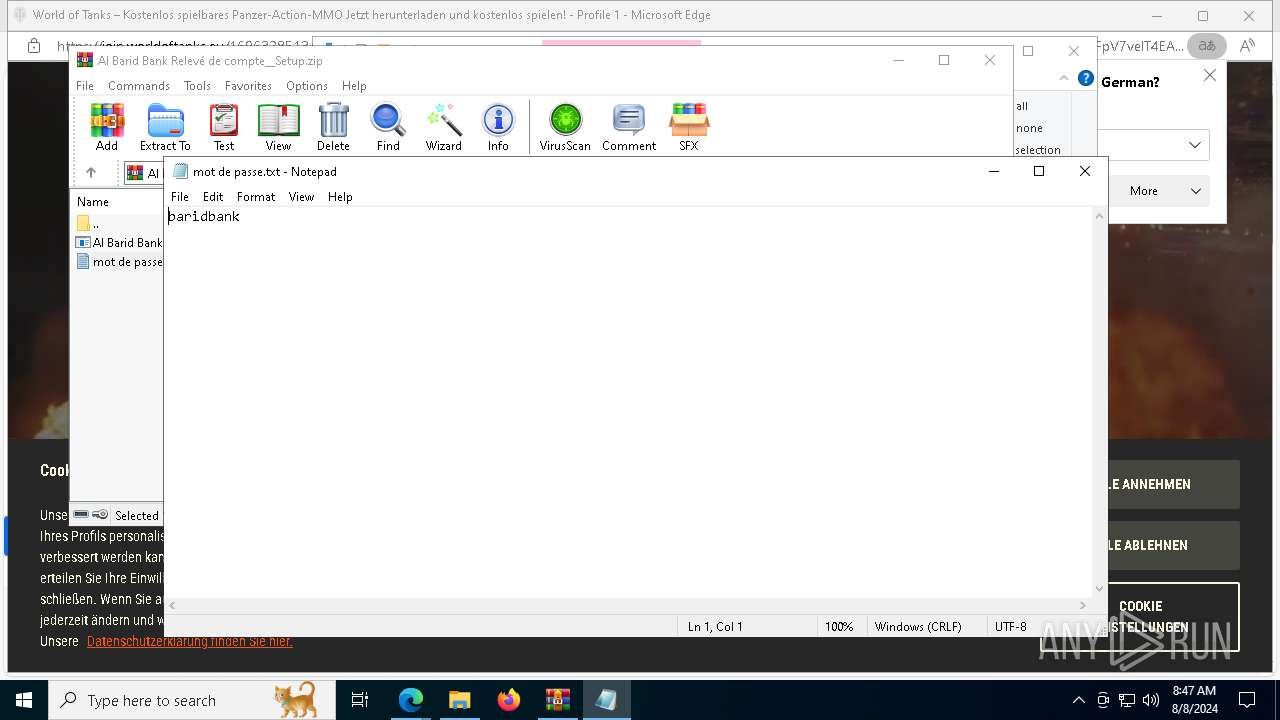
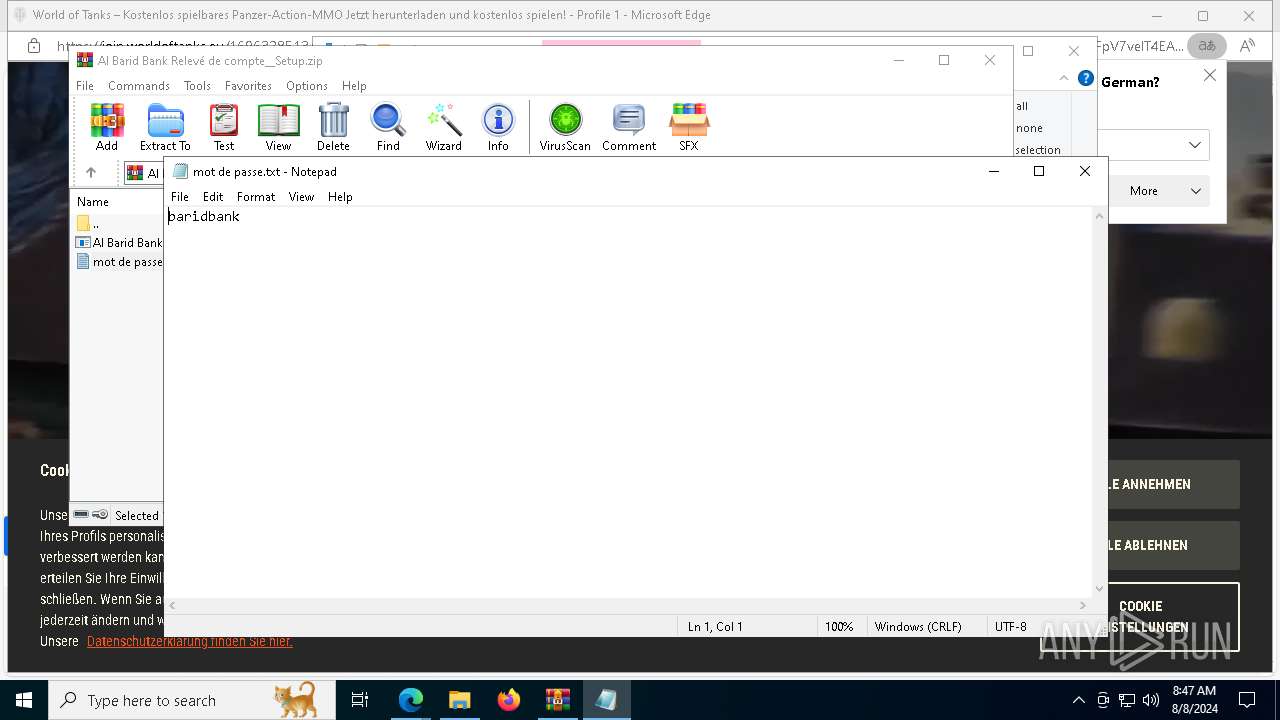
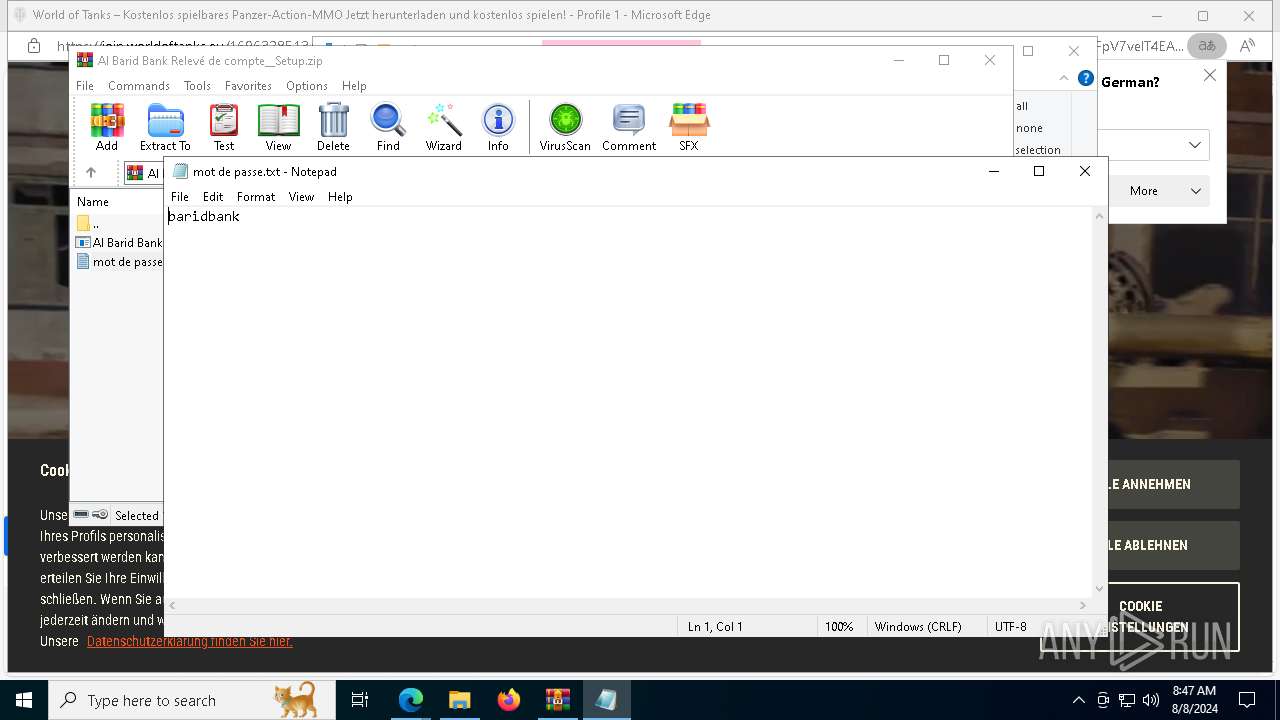
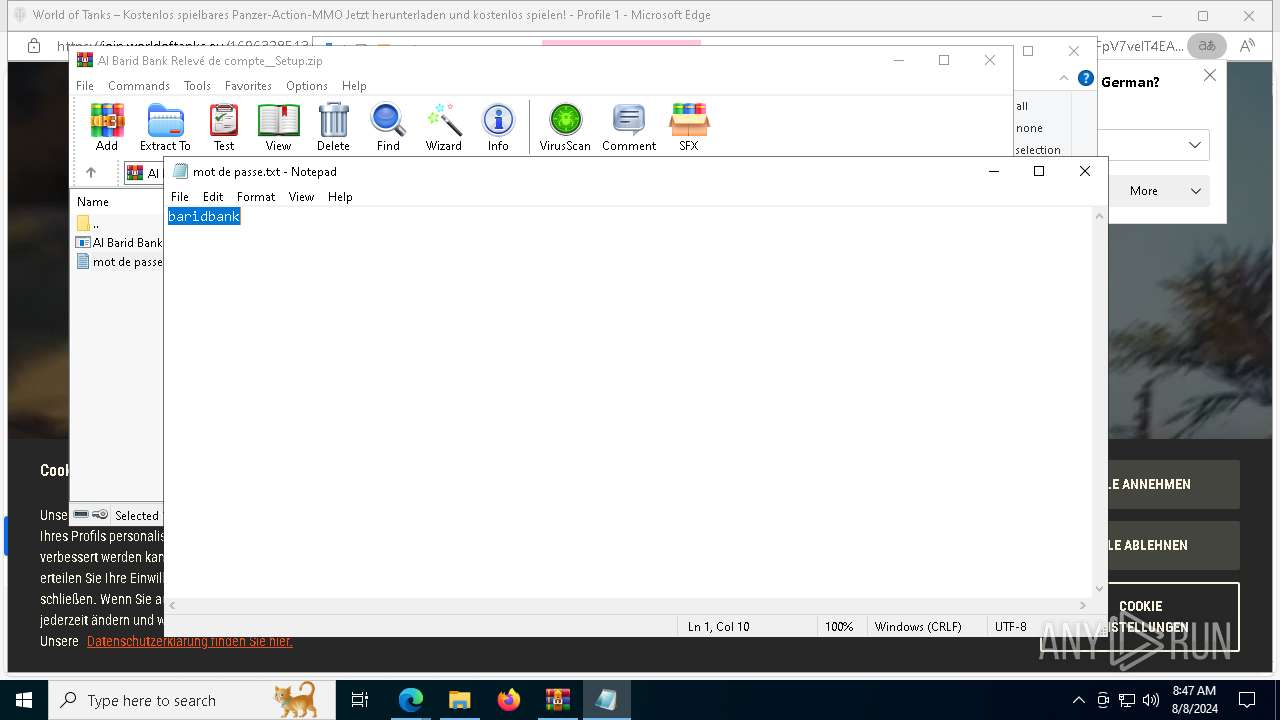
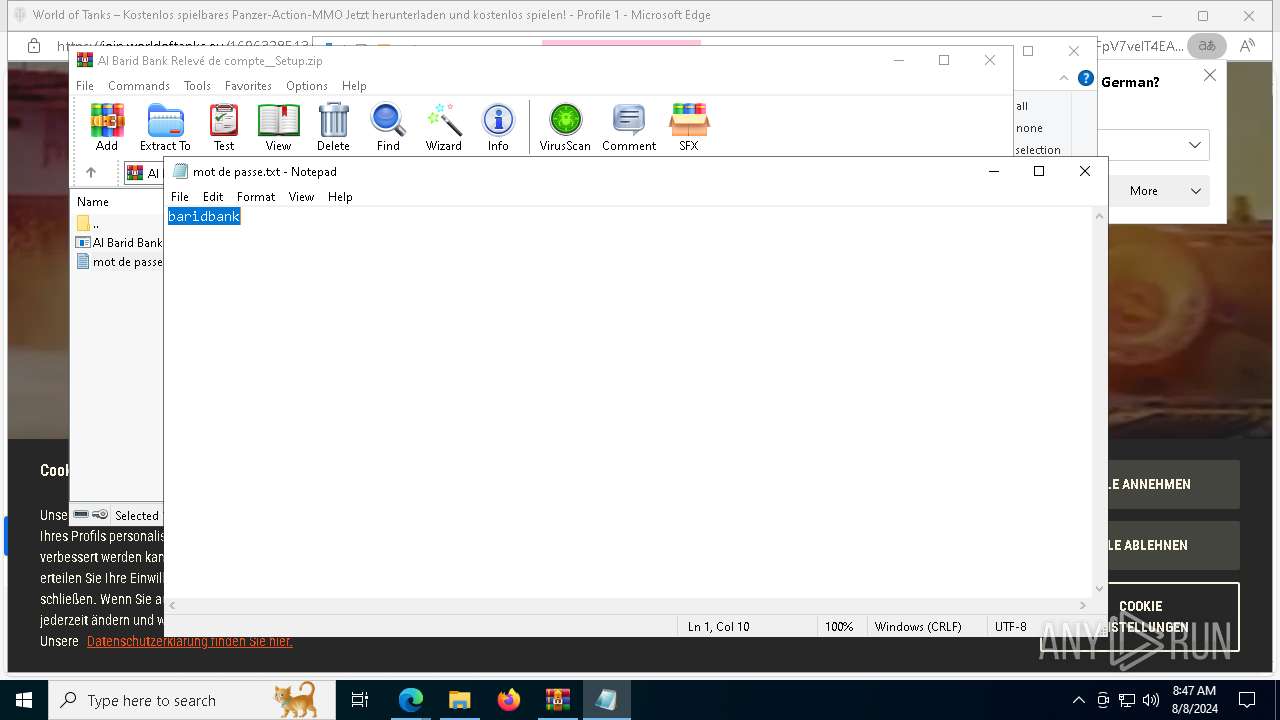
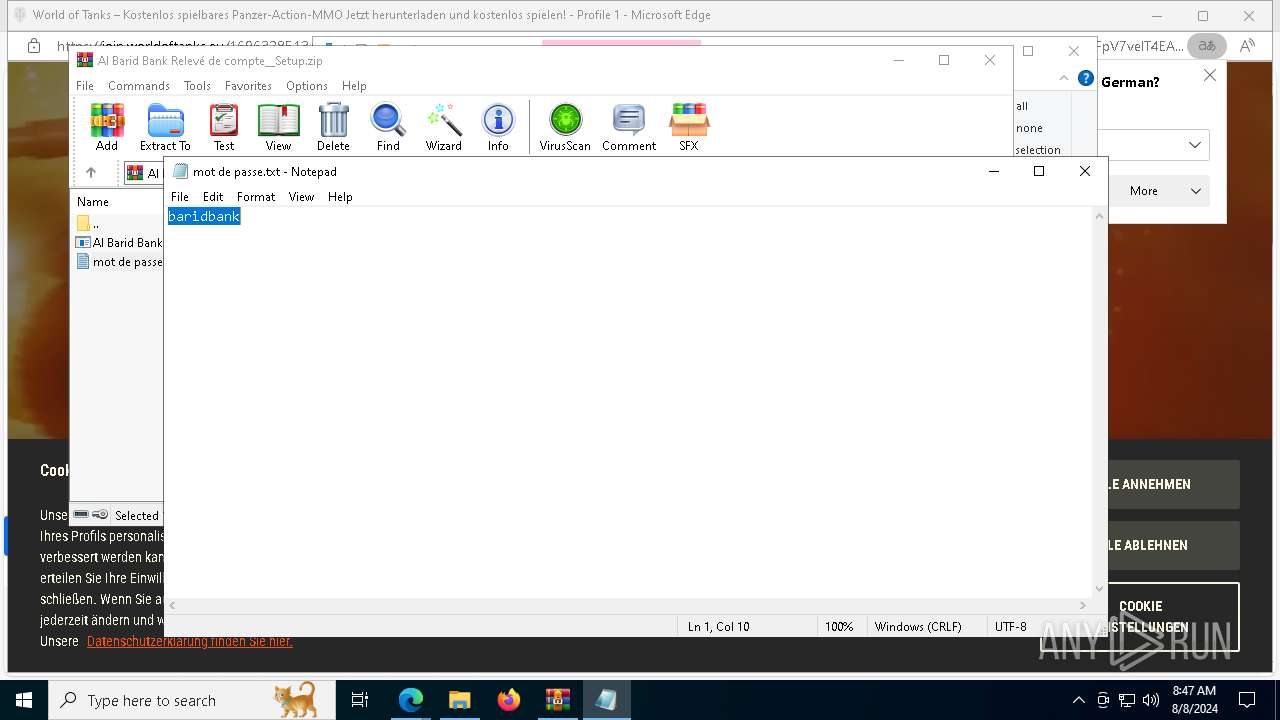
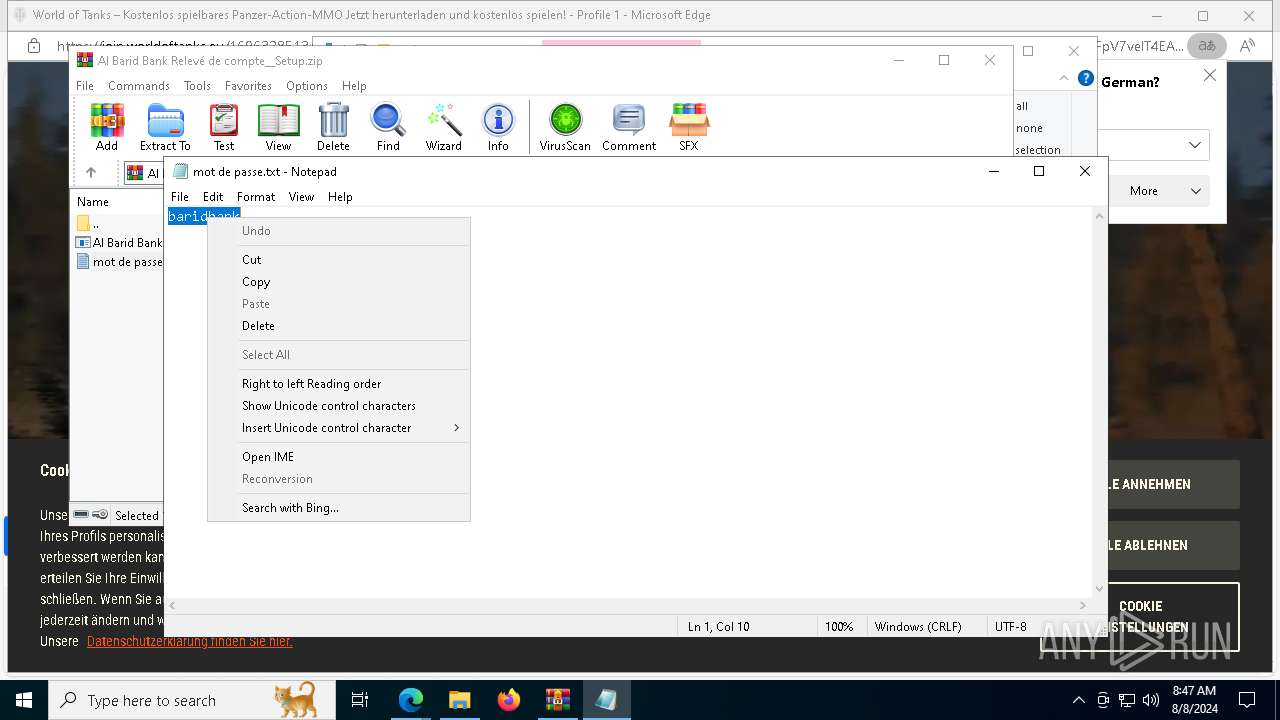
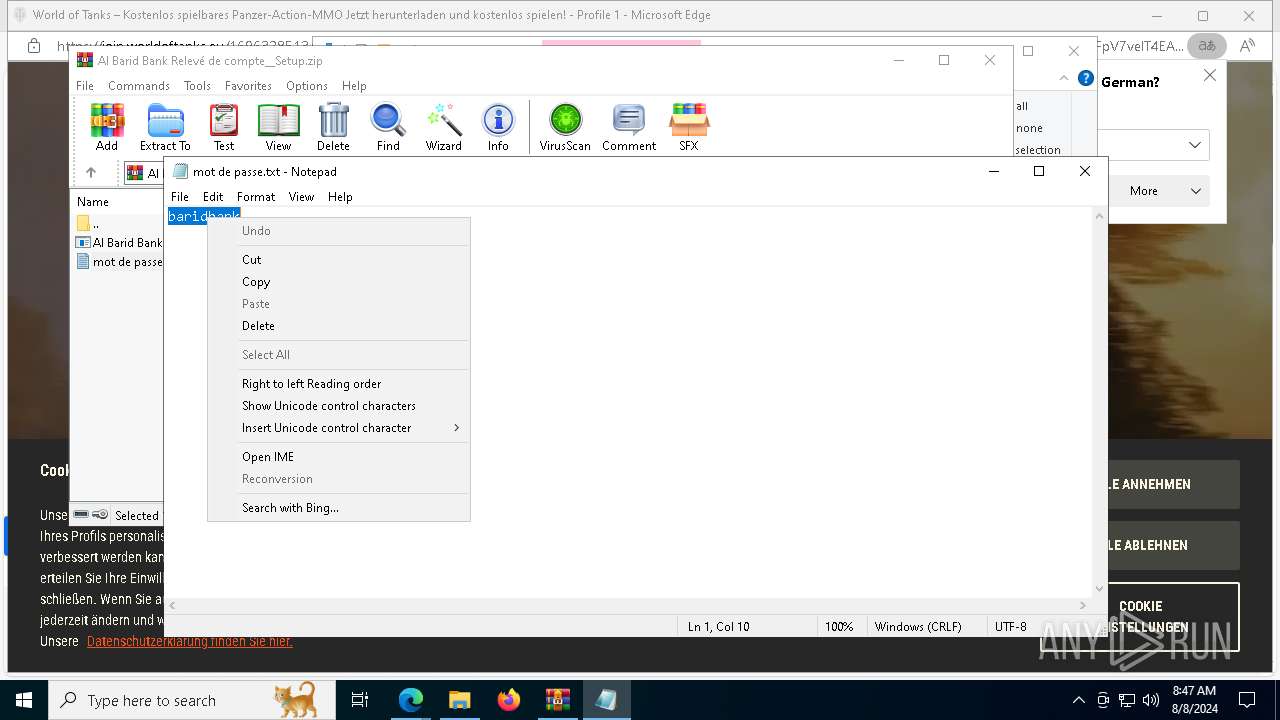
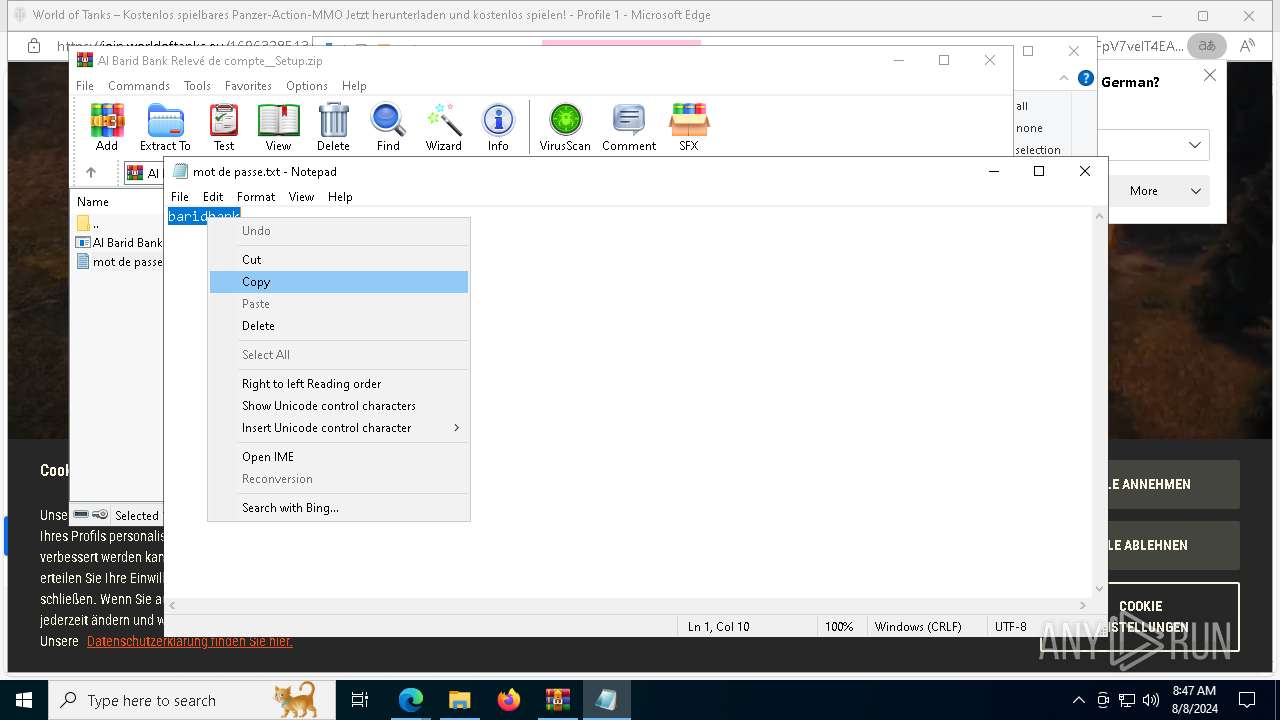
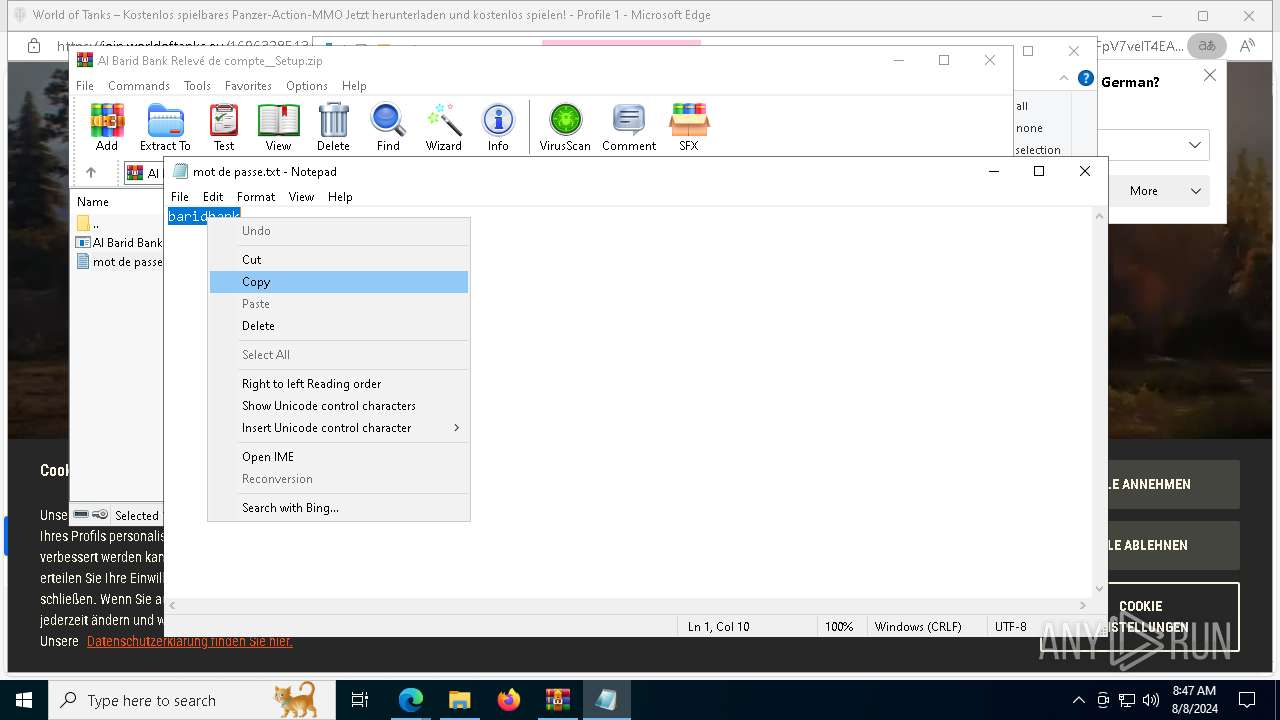
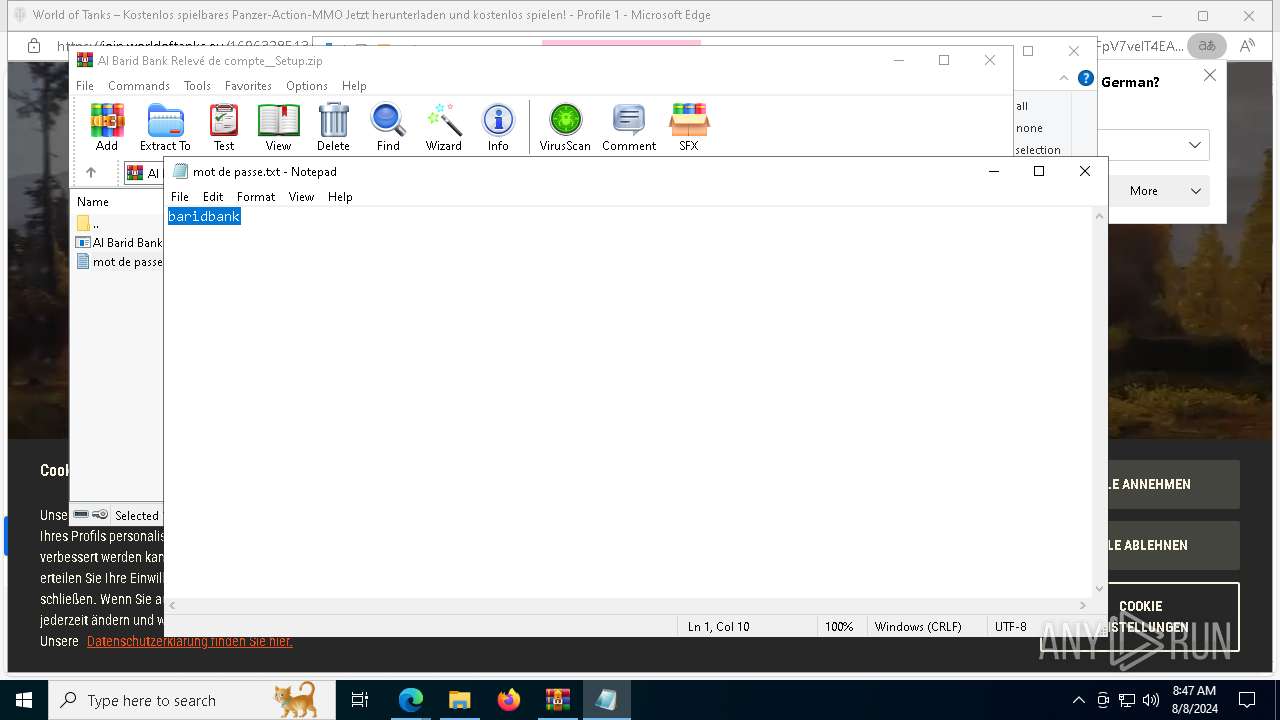
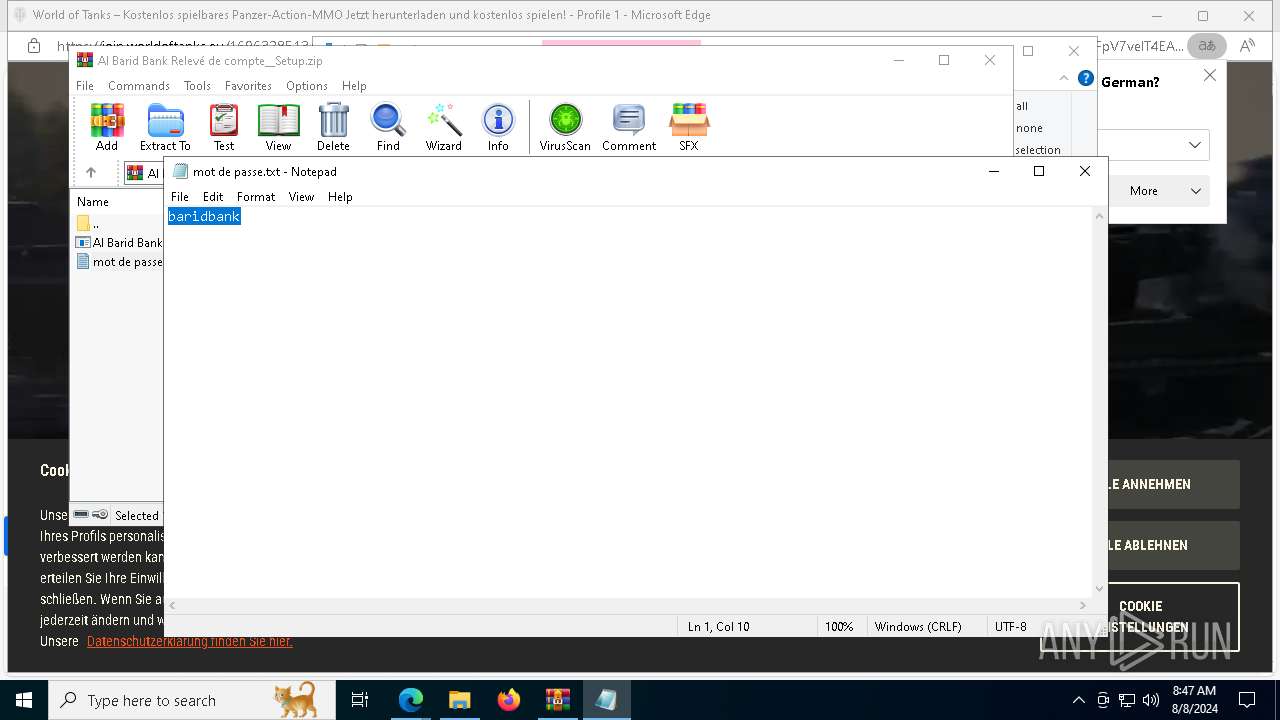
Start notepad (likely ransomware note)
- WinRAR.exe (PID: 9148)
Executable content was dropped or overwritten
- Al Barid Bank Relevé de compte_Setup.exe (PID: 5852)
- Al Barid Bank Relevé de compte_Setup.exe (PID: 8796)
- Al Barid Bank Relevé de compte_Setup.tmp (PID: 8784)
- admin_microsoft_account.exe (PID: 6644)
Reads the date of Windows installation
- Al Barid Bank Relevé de compte_Setup.tmp (PID: 5920)
Reads the Windows owner or organization settings
- Al Barid Bank Relevé de compte_Setup.tmp (PID: 8784)
Script adds exclusion path to Windows Defender
- Al Barid Bank Relevé de compte_Setup.tmp (PID: 8784)
- admin_microsoft_account.exe (PID: 6644)
Starts POWERSHELL.EXE for commands execution
- Al Barid Bank Relevé de compte_Setup.tmp (PID: 8784)
- admin_microsoft_account.exe (PID: 6644)
Starts CMD.EXE for commands execution
- Al Barid Bank Relevé de compte_Setup.tmp (PID: 8784)
Process drops legitimate windows executable
- admin_microsoft_account.exe (PID: 6644)
Uses REG/REGEDIT.EXE to modify registry
- admin_microsoft_account.exe (PID: 6644)
The process executes via Task Scheduler
- admin_microsoft_account.exe (PID: 7880)
- admin_microsoft_account.exe (PID: 7916)
The process drops C-runtime libraries
- admin_microsoft_account.exe (PID: 6644)
Uses TASKKILL.EXE to kill process
- admin_microsoft_account.exe (PID: 6644)
Contacting a server suspected of hosting an CnC
- msedge.exe (PID: 6824)
Executes as Windows Service
- securitysvc.exe (PID: 7476)
- securitysvc.exe (PID: 6140)
Connects to unusual port
- AlBaridBank_Relevé.exe (PID: 7136)
- admin_microsoft_account.exe (PID: 6644)
- securitysvc.exe (PID: 7476)
- securitysvc.exe (PID: 6140)
Application launched itself
- securitysvc.exe (PID: 7008)
- securitysvc.exe (PID: 7476)
- securitysvc.exe (PID: 6140)
- securitysvc.exe (PID: 8692)
Potential Corporate Privacy Violation
- securitysvc.exe (PID: 7476)
- securitysvc.exe (PID: 6140)
INFO
Reads Microsoft Office registry keys
- msedge.exe (PID: 6480)
- WinRAR.exe (PID: 9148)
- msedge.exe (PID: 5624)
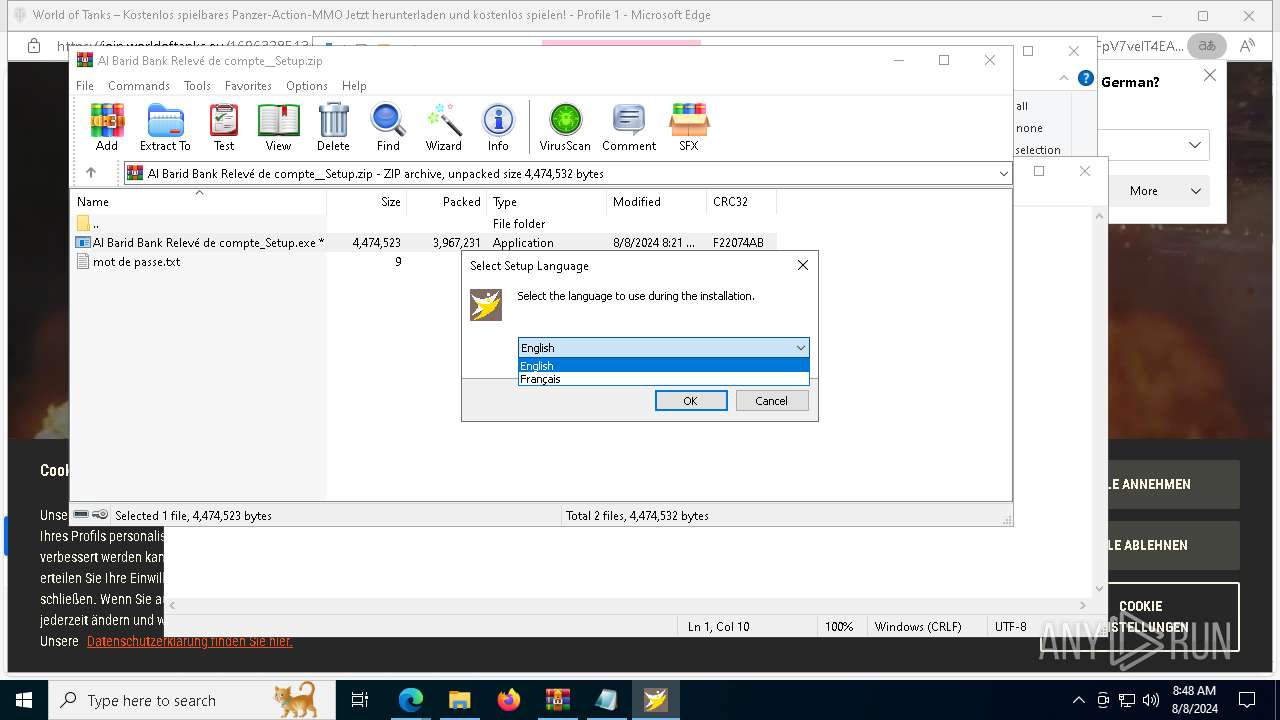
Checks supported languages
- TextInputHost.exe (PID: 1948)
- identity_helper.exe (PID: 420)
- Al Barid Bank Relevé de compte_Setup.exe (PID: 5852)
- Al Barid Bank Relevé de compte_Setup.tmp (PID: 5920)
- Al Barid Bank Relevé de compte_Setup.tmp (PID: 8784)
- Al Barid Bank Relevé de compte_Setup.exe (PID: 8796)
- identity_helper.exe (PID: 2900)
- admin_microsoft_account.exe (PID: 6644)
- admin_microsoft_account.exe (PID: 7880)
- ShellExperienceHost.exe (PID: 7704)
- AlBaridBank_Relevé.exe (PID: 7136)
- securitysvc.exe (PID: 7112)
- securitysvc.exe (PID: 7008)
- securitysvc.exe (PID: 6256)
- securitysvc.exe (PID: 7476)
- securitysvc.exe (PID: 6752)
- securitysvc.exe (PID: 6628)
- securitysvc.exe (PID: 7644)
- securitysvc.exe (PID: 2336)
- securitysvc.exe (PID: 8692)
- securitysvc.exe (PID: 3256)
- securitysvc.exe (PID: 6140)
- securitysvc.exe (PID: 8804)
- securitysvc.exe (PID: 5388)
- admin_microsoft_account.exe (PID: 7916)
- securitysvc.exe (PID: 6680)
Reads Environment values
- identity_helper.exe (PID: 420)
- identity_helper.exe (PID: 2900)
Reads the computer name
- TextInputHost.exe (PID: 1948)
- identity_helper.exe (PID: 420)
- Al Barid Bank Relevé de compte_Setup.tmp (PID: 8784)
- Al Barid Bank Relevé de compte_Setup.tmp (PID: 5920)
- identity_helper.exe (PID: 2900)
- admin_microsoft_account.exe (PID: 6644)
- ShellExperienceHost.exe (PID: 7704)
- AlBaridBank_Relevé.exe (PID: 7136)
- securitysvc.exe (PID: 7008)
- securitysvc.exe (PID: 6680)
- securitysvc.exe (PID: 7112)
- securitysvc.exe (PID: 7476)
- securitysvc.exe (PID: 7644)
- securitysvc.exe (PID: 6752)
- securitysvc.exe (PID: 2336)
- securitysvc.exe (PID: 6140)
- securitysvc.exe (PID: 8692)
- securitysvc.exe (PID: 5388)
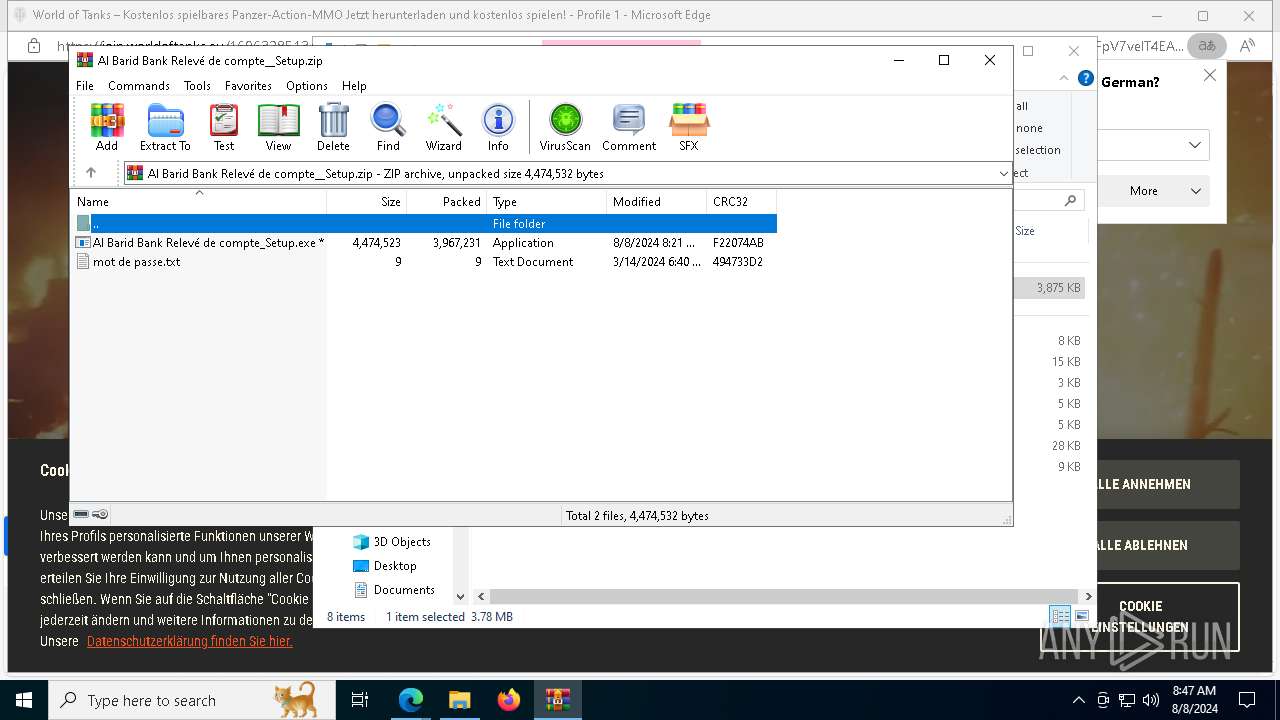
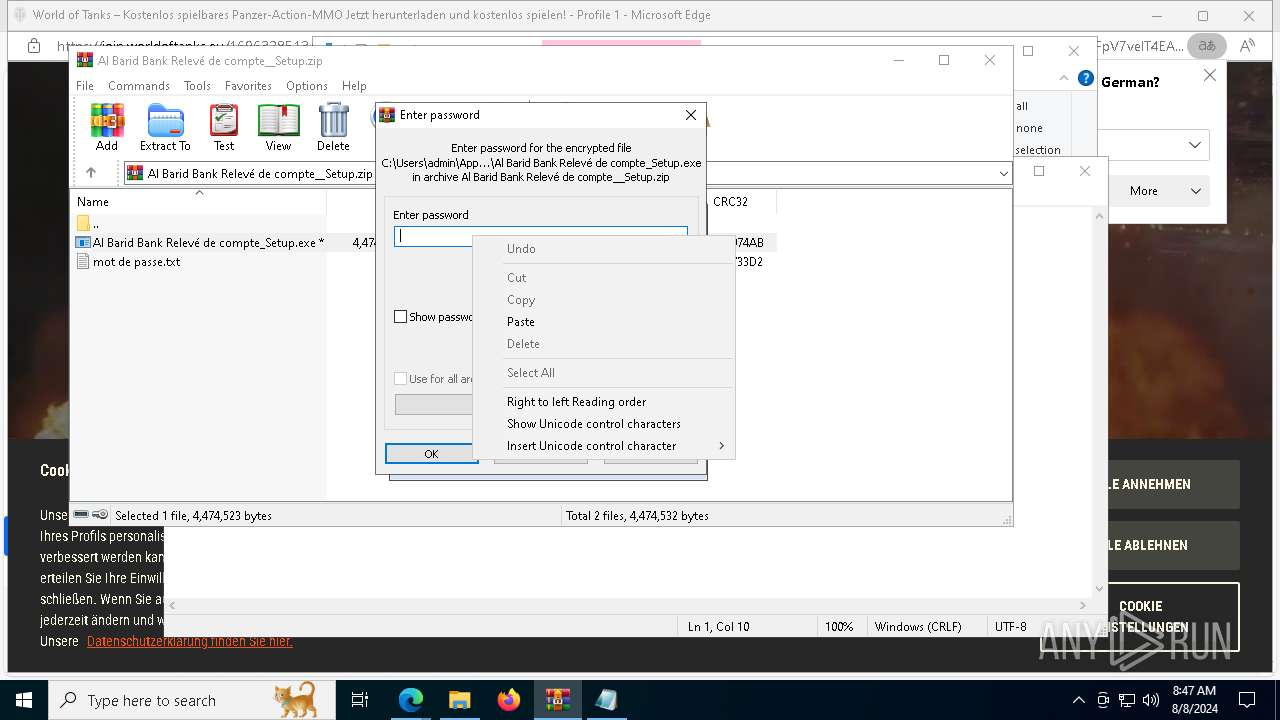
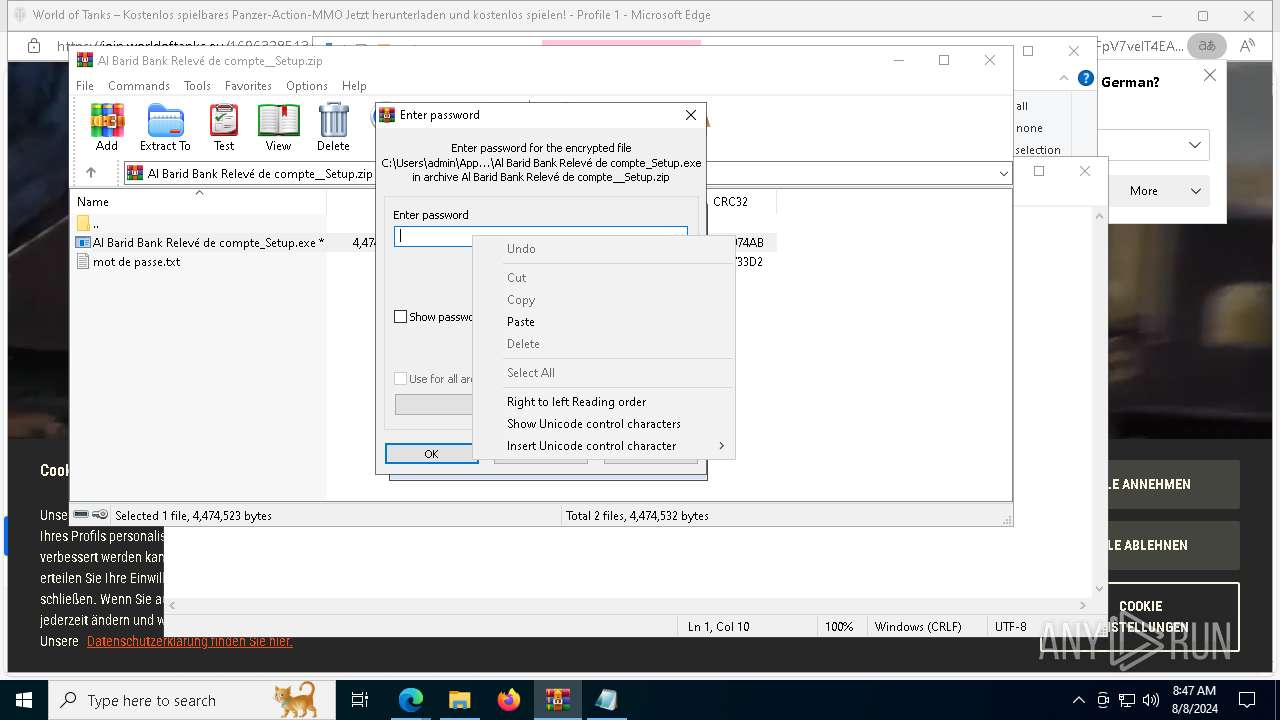
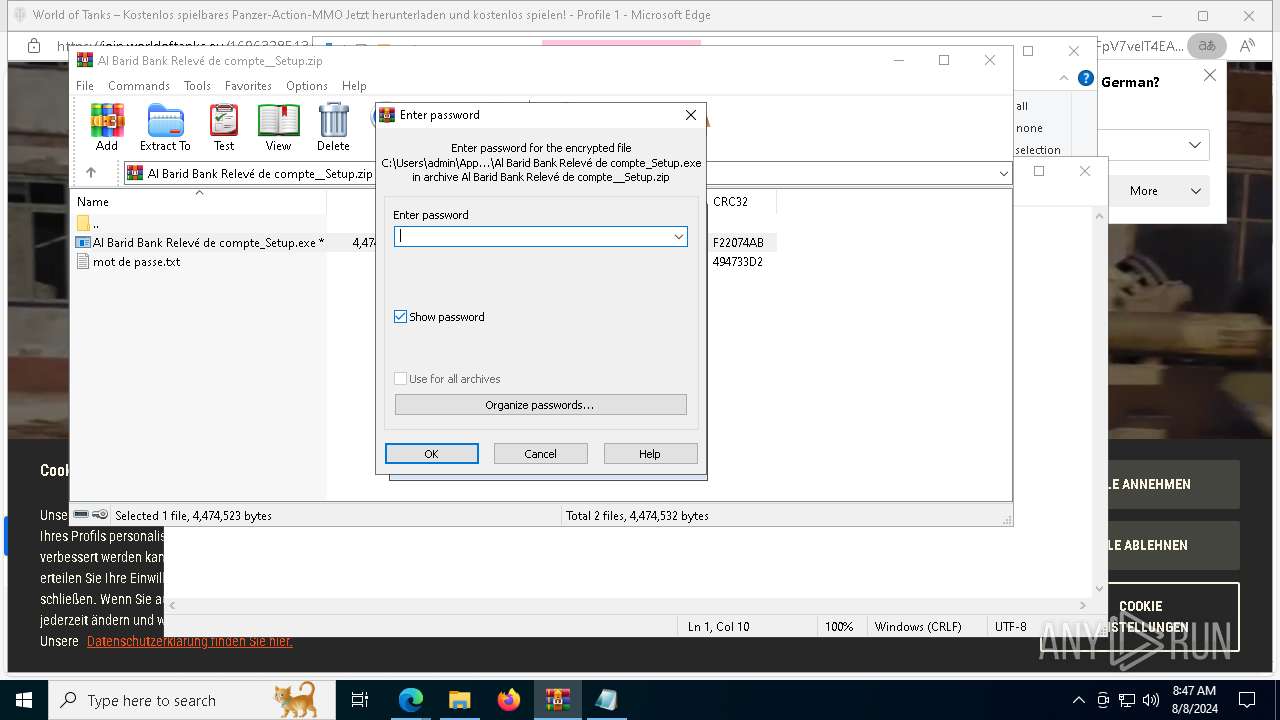
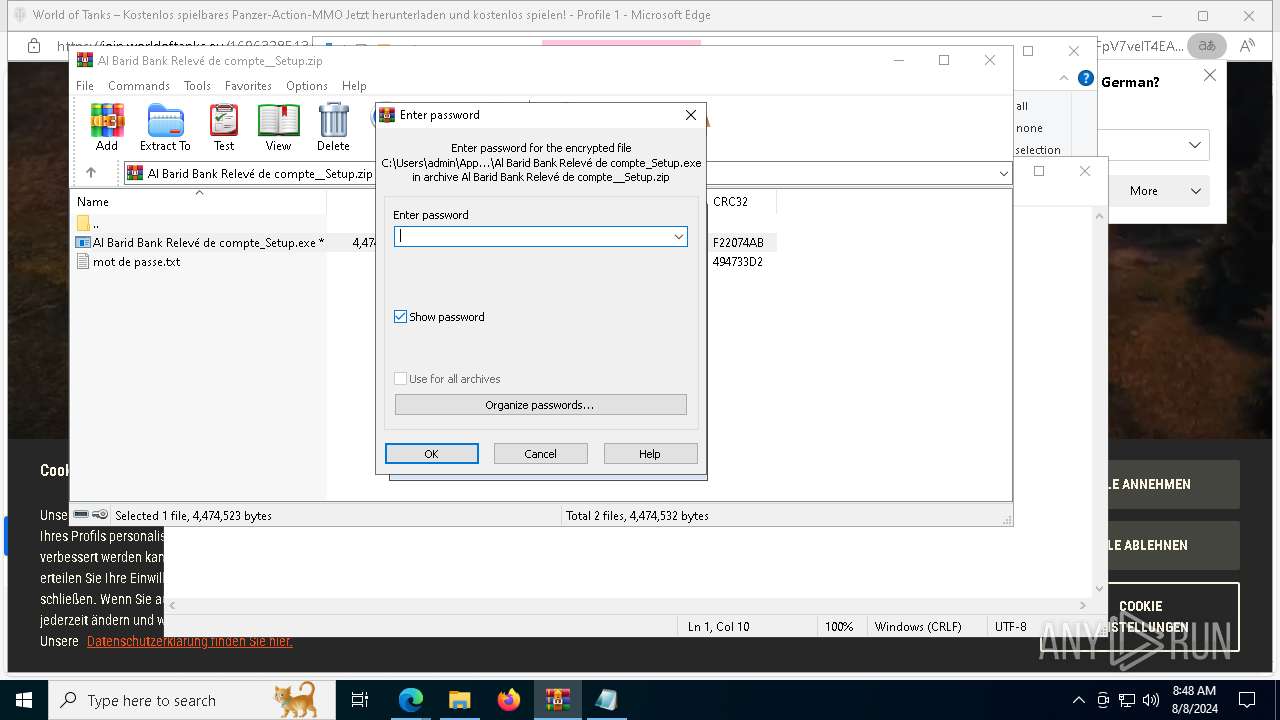
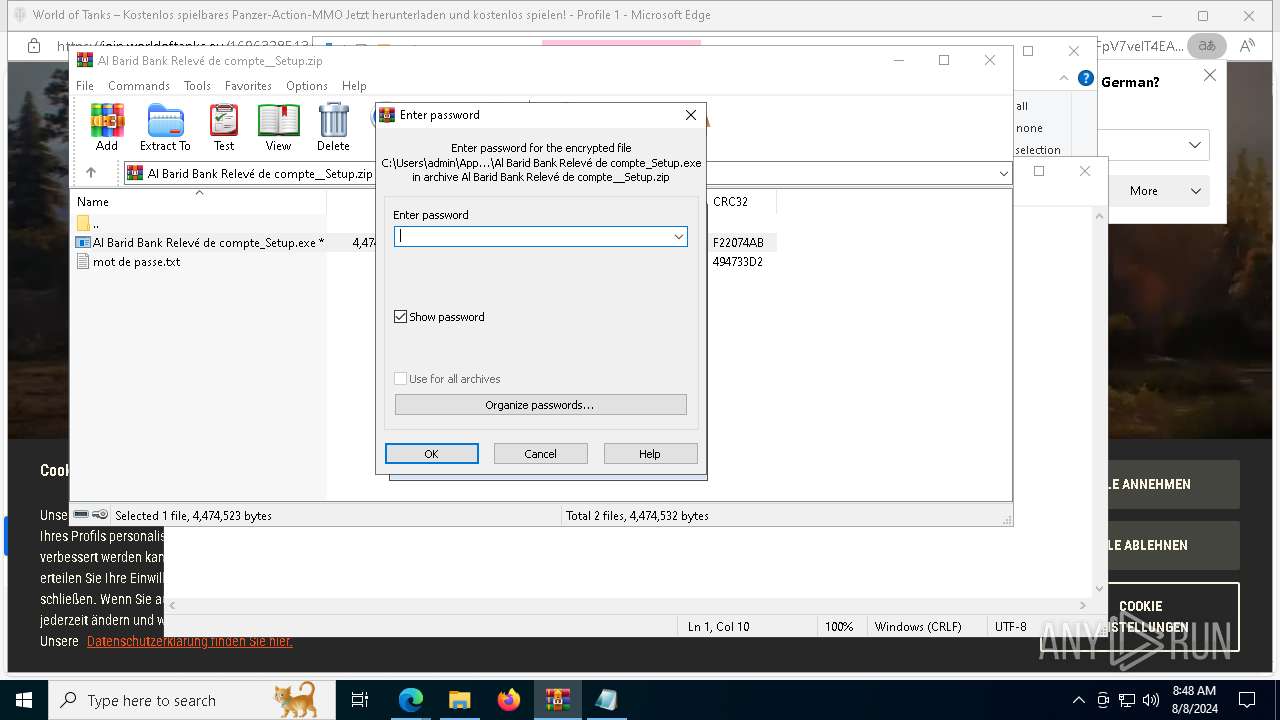
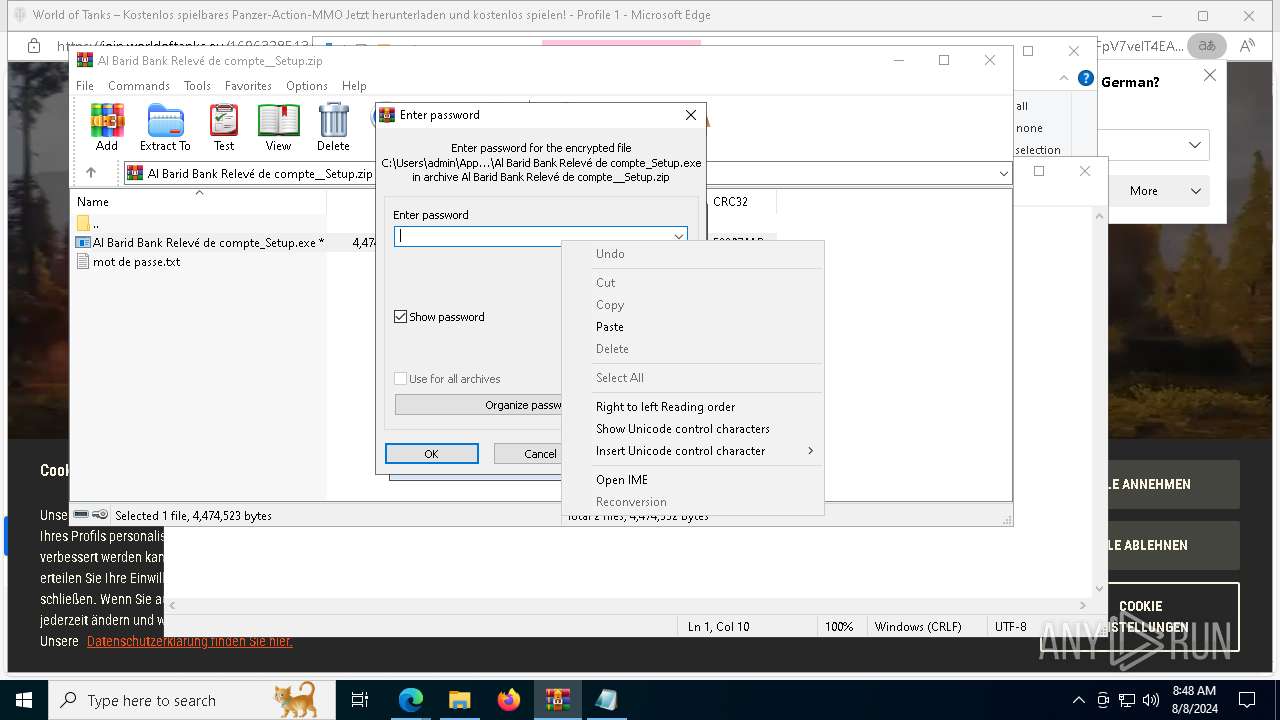
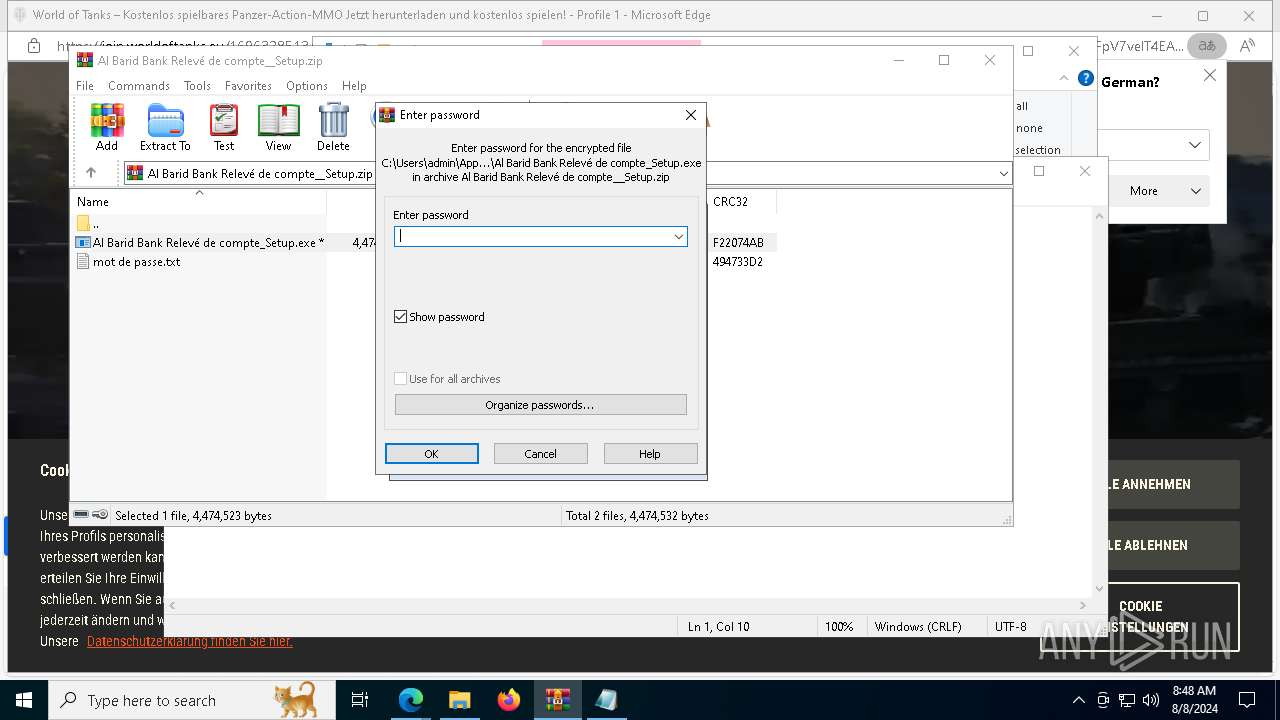
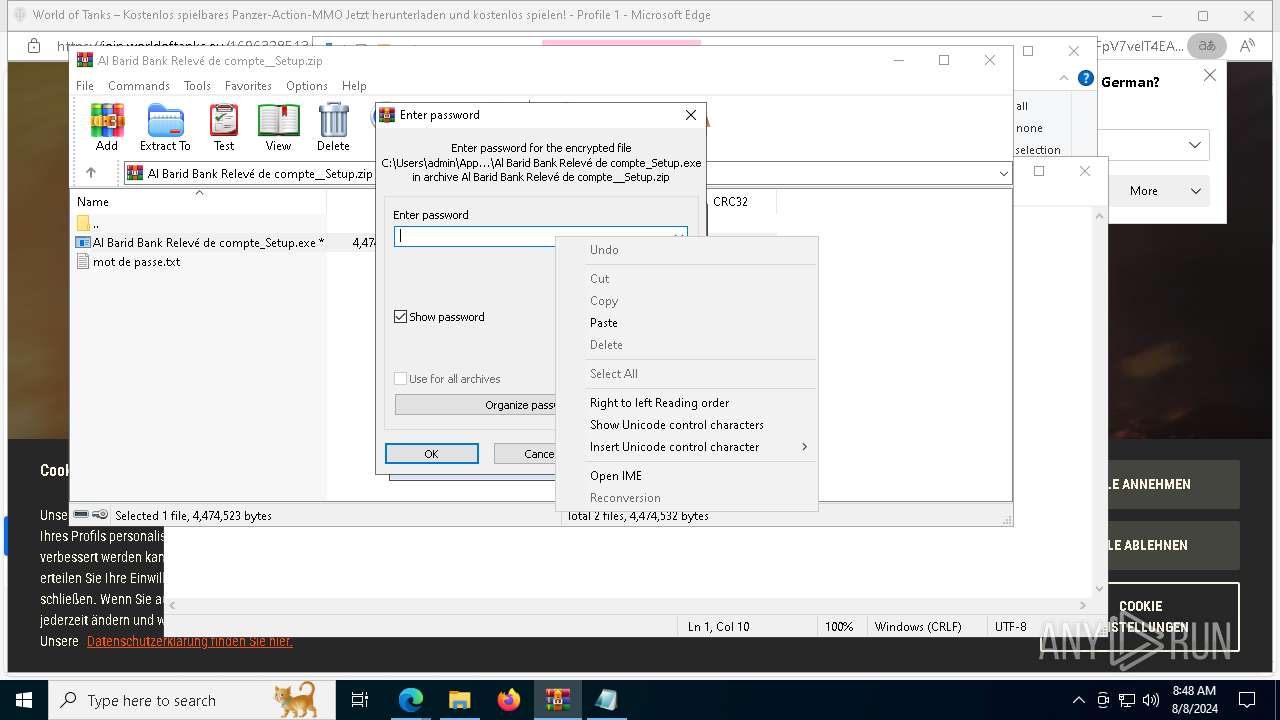
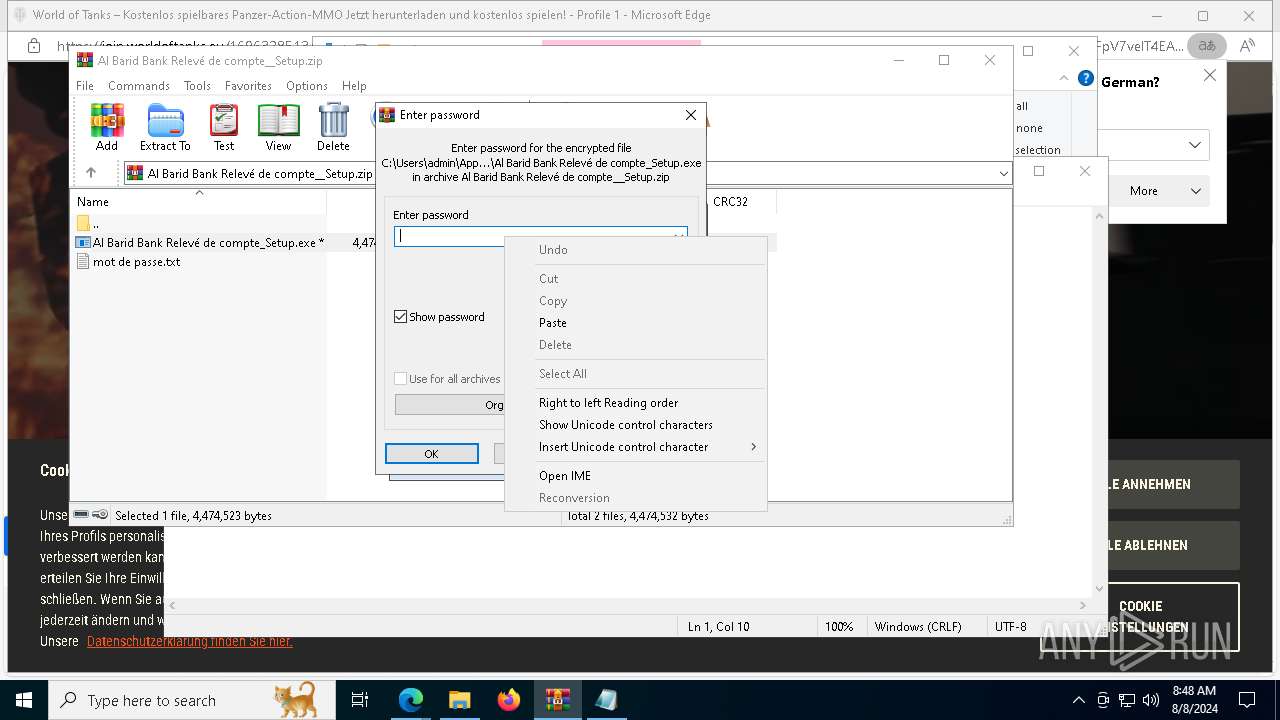
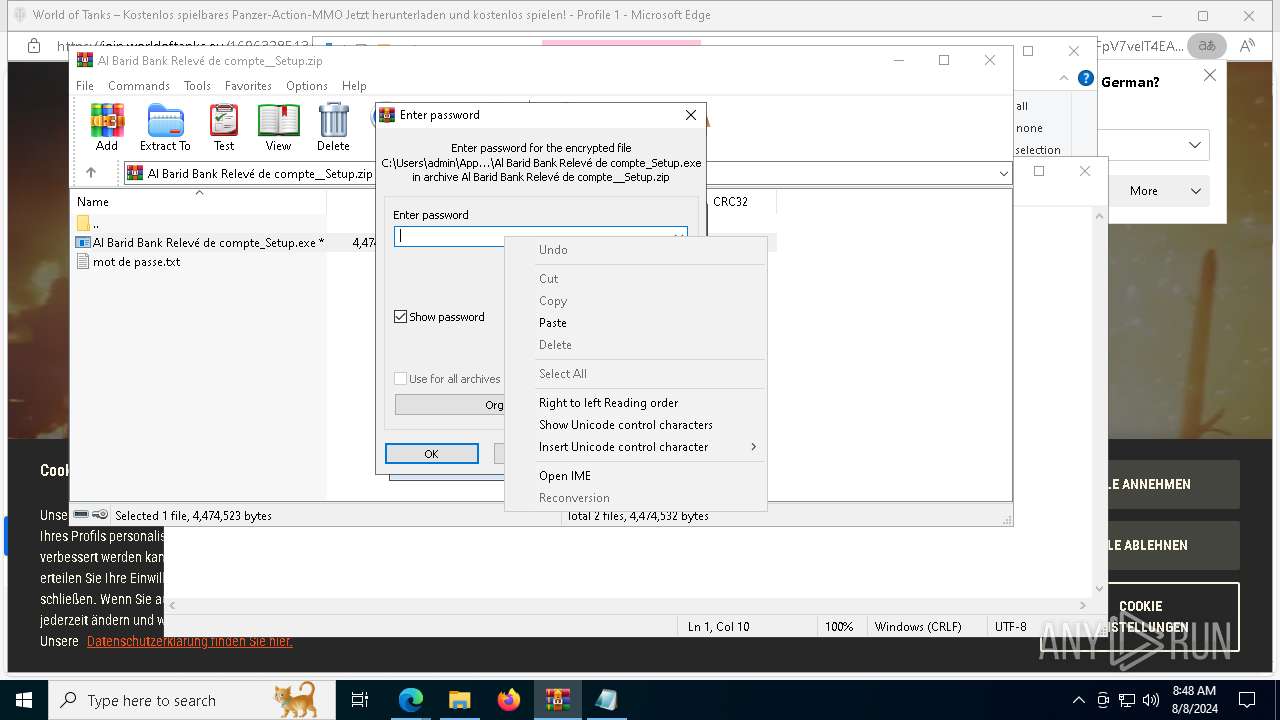
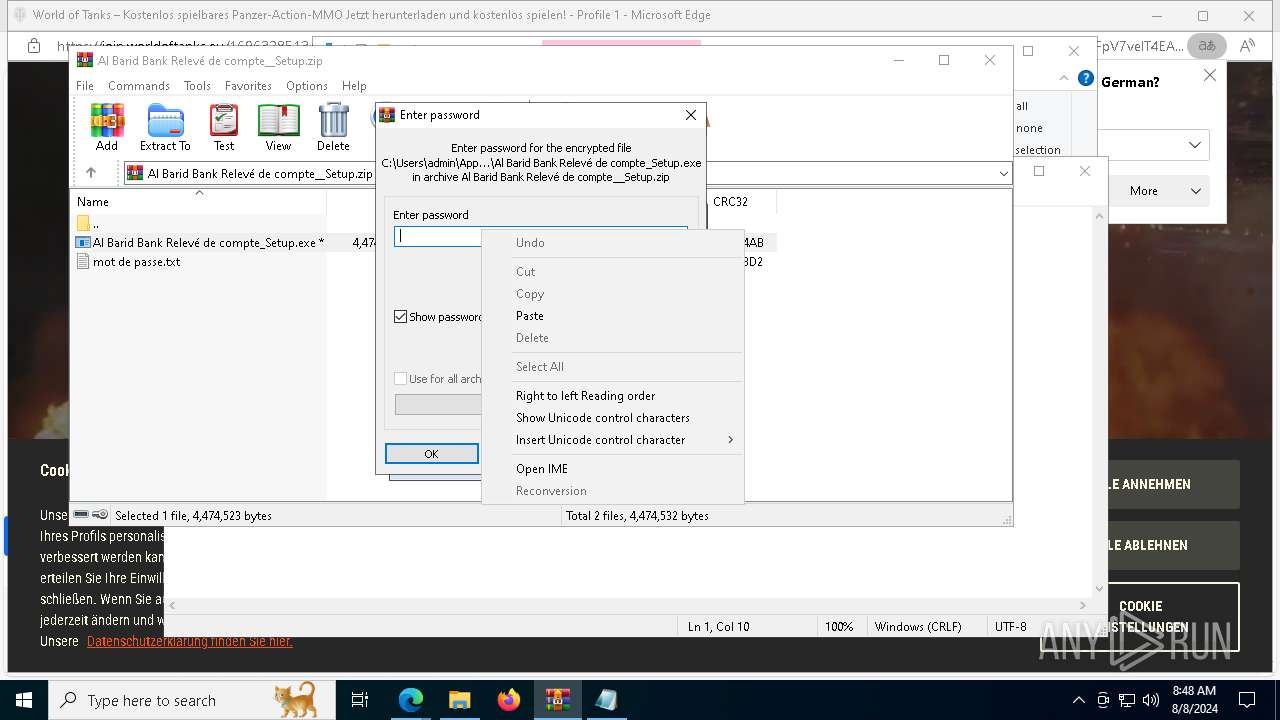
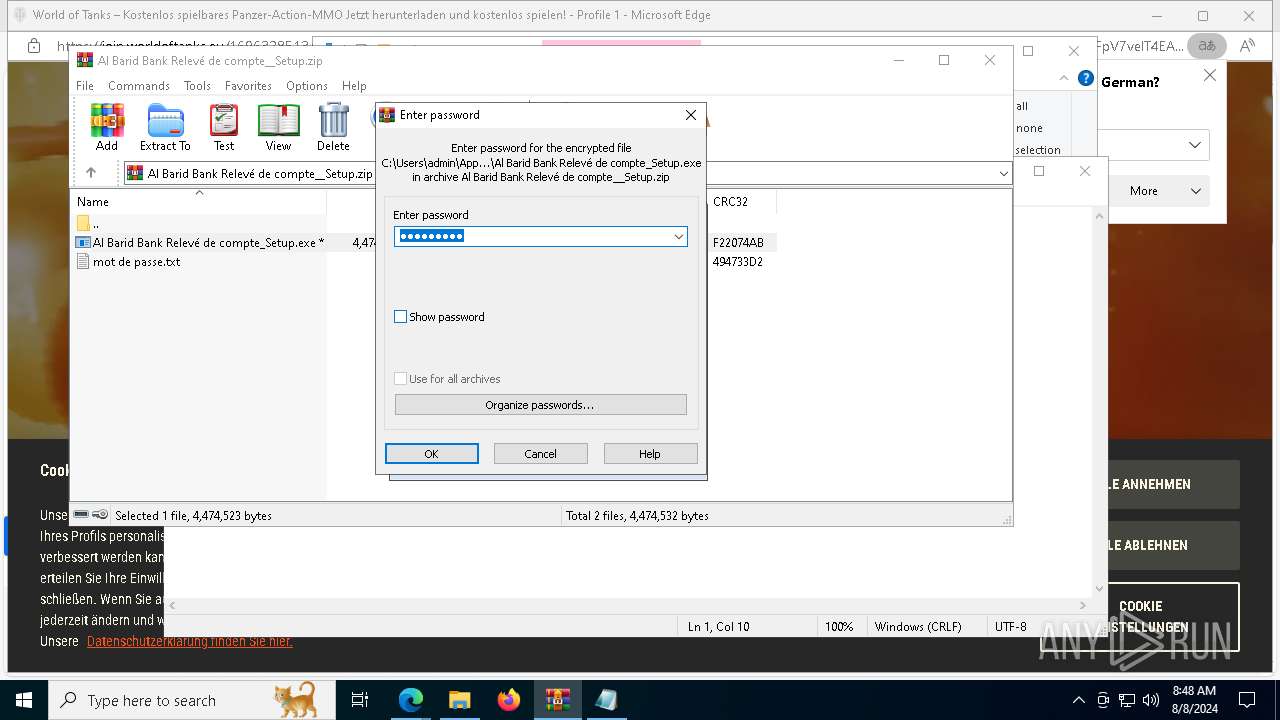
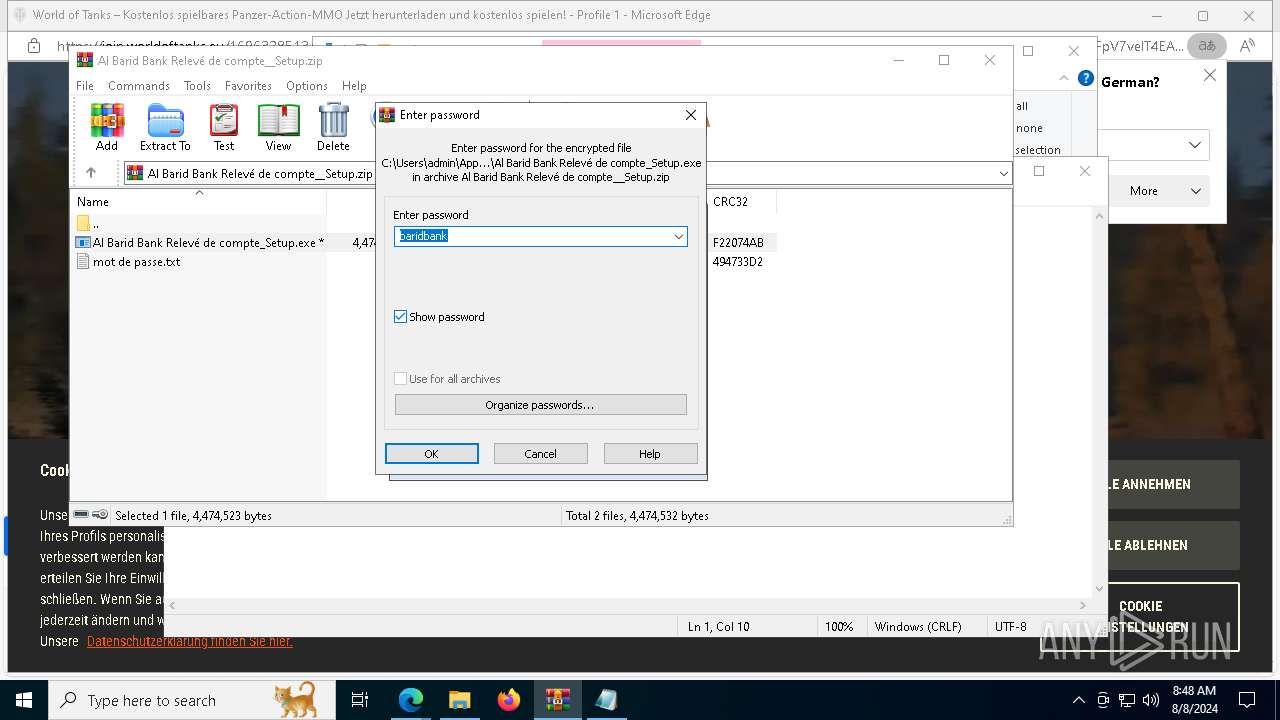
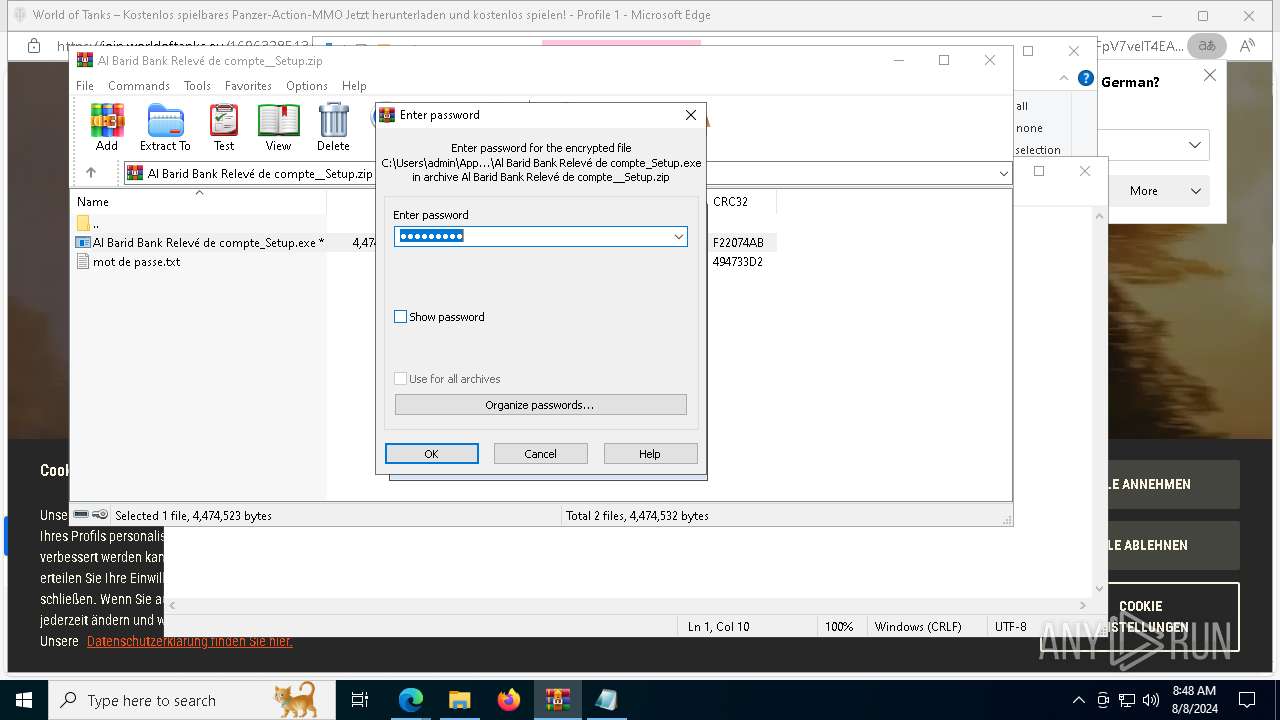
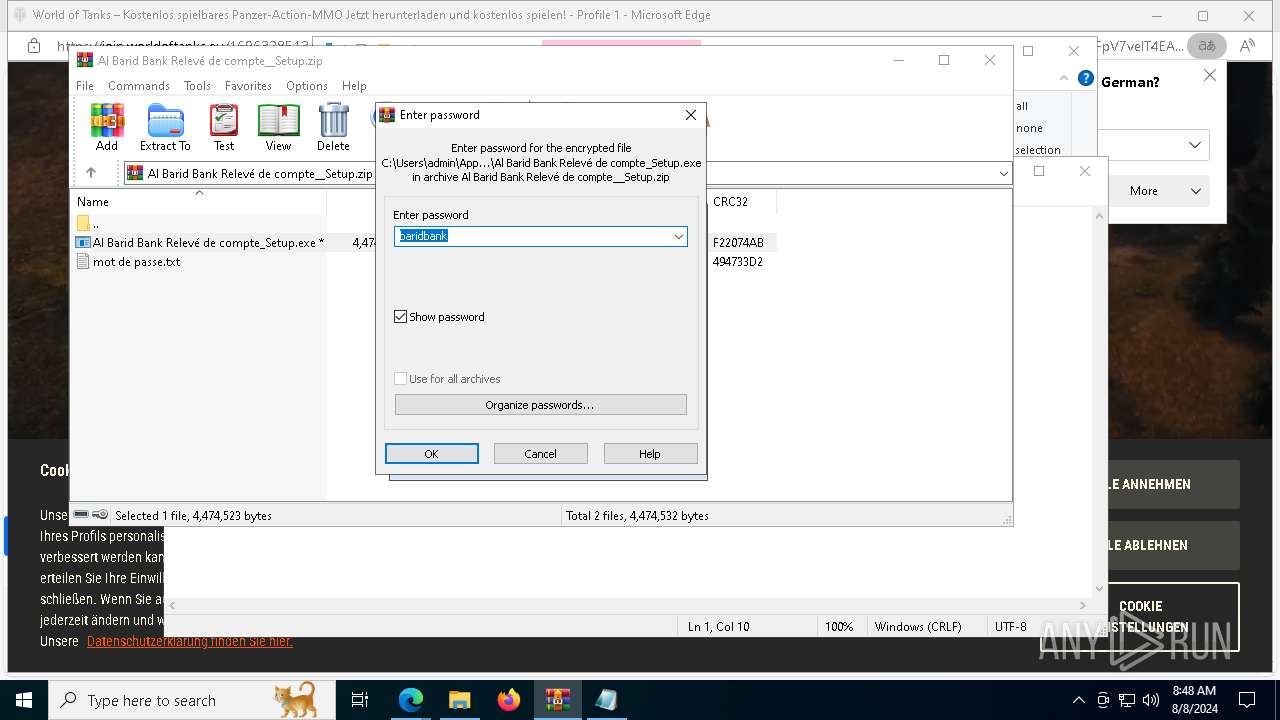
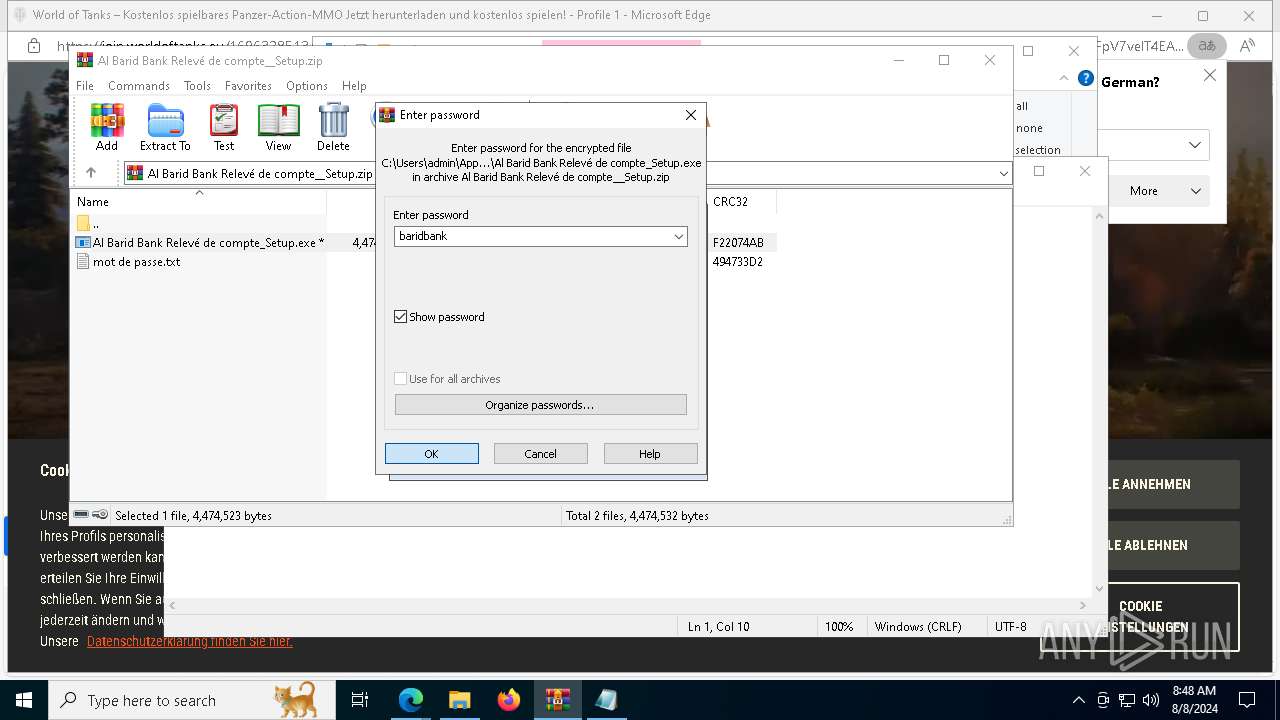
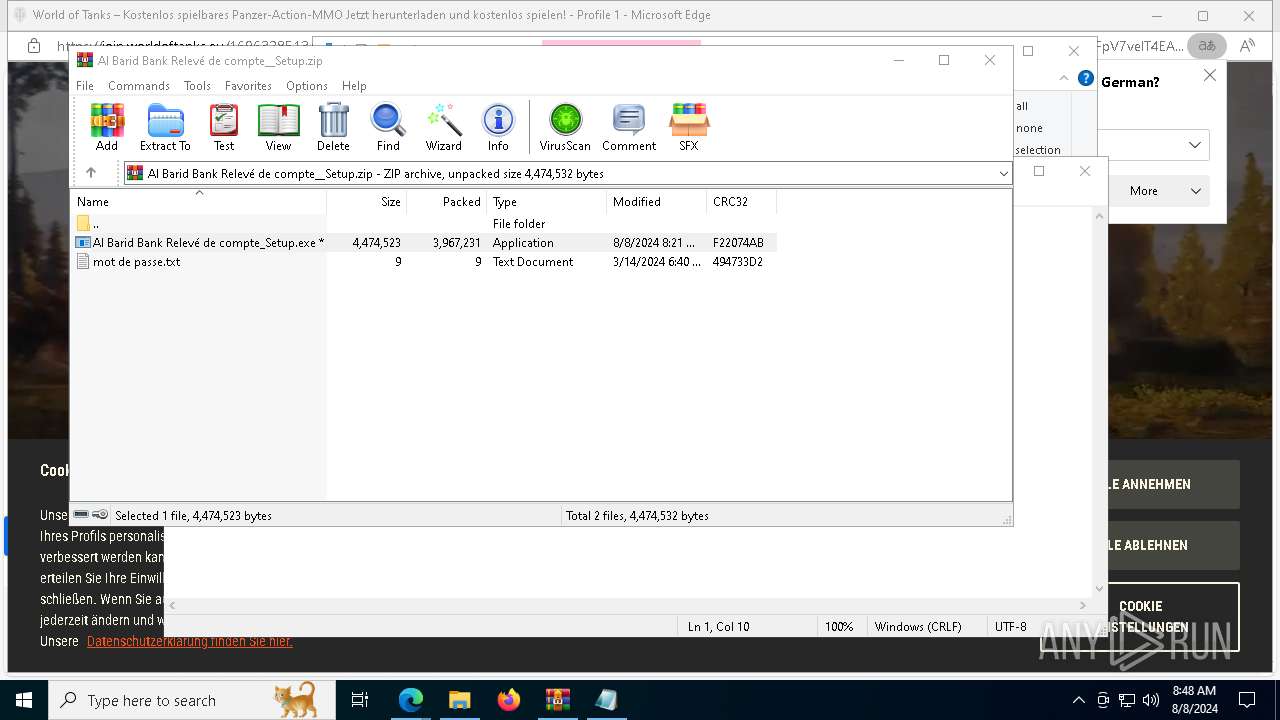
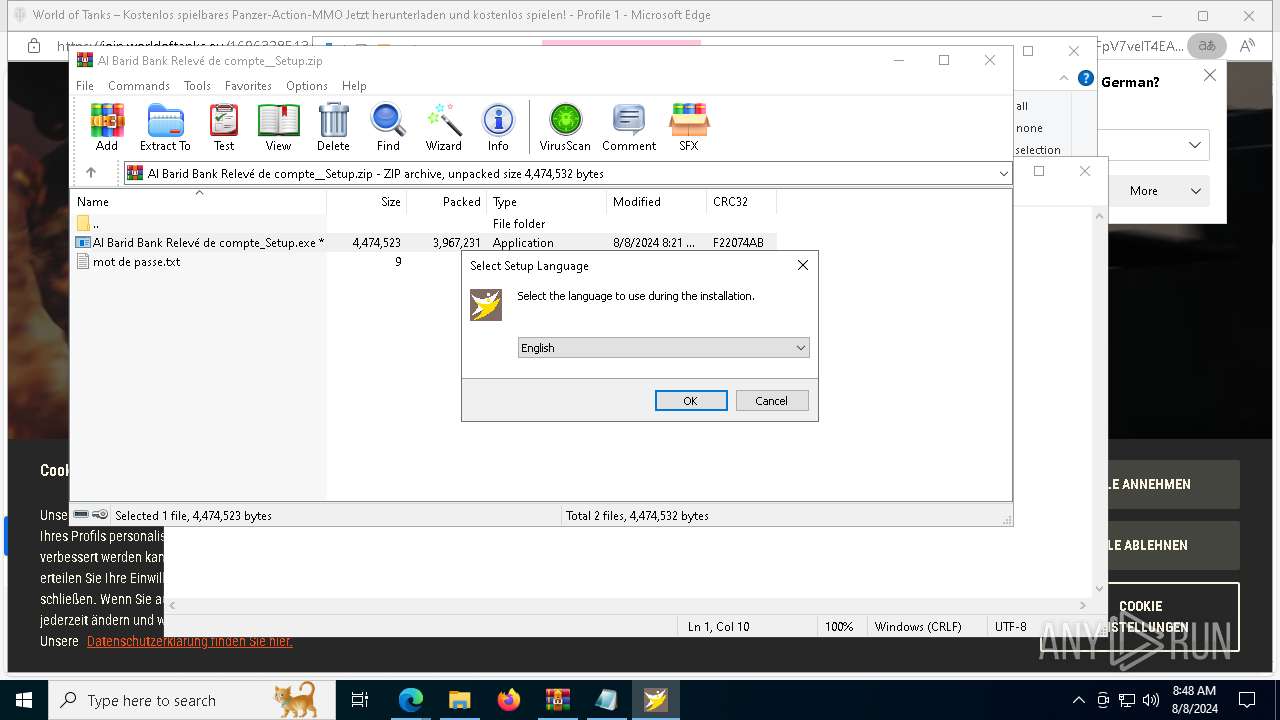
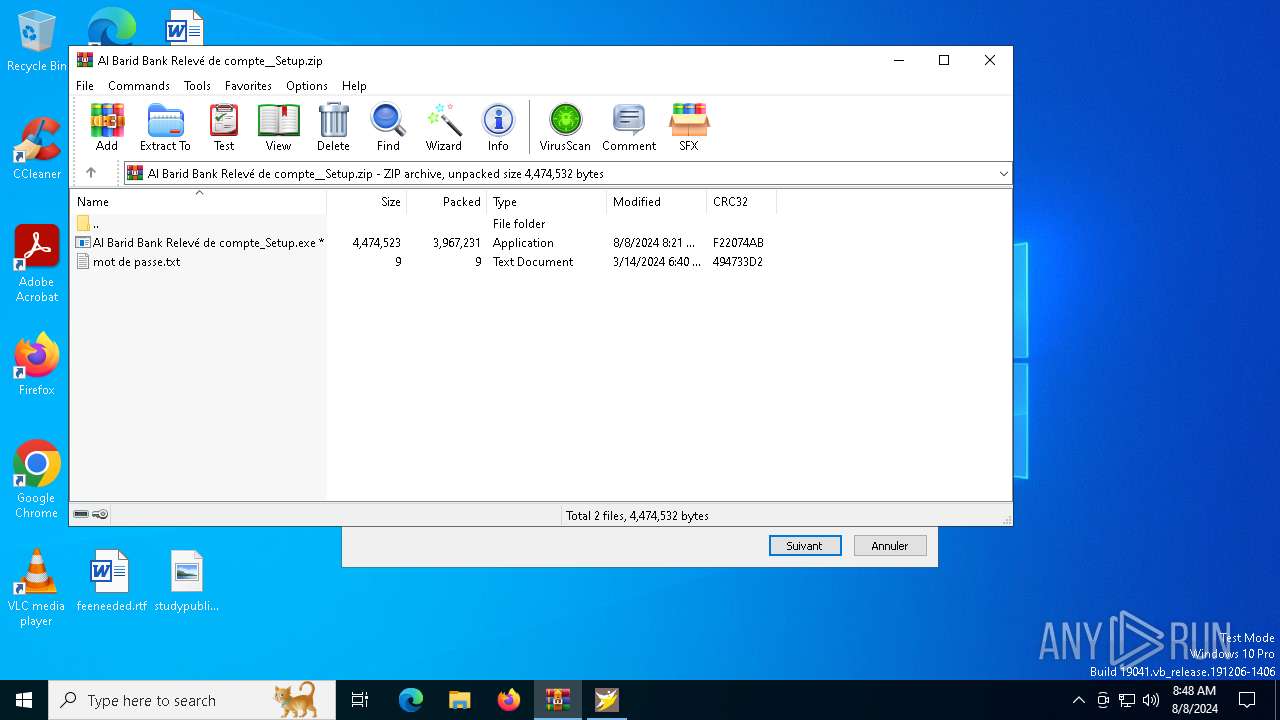
The process uses the downloaded file
- msedge.exe (PID: 8300)
- WinRAR.exe (PID: 9148)
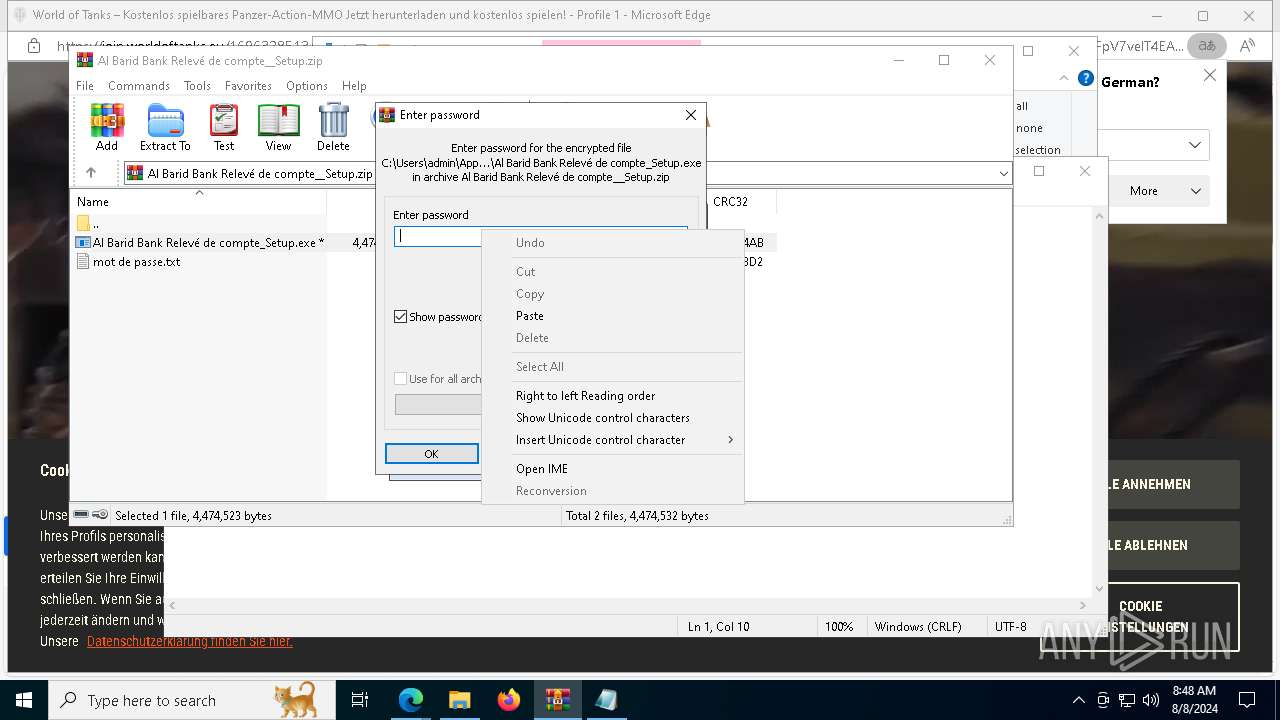
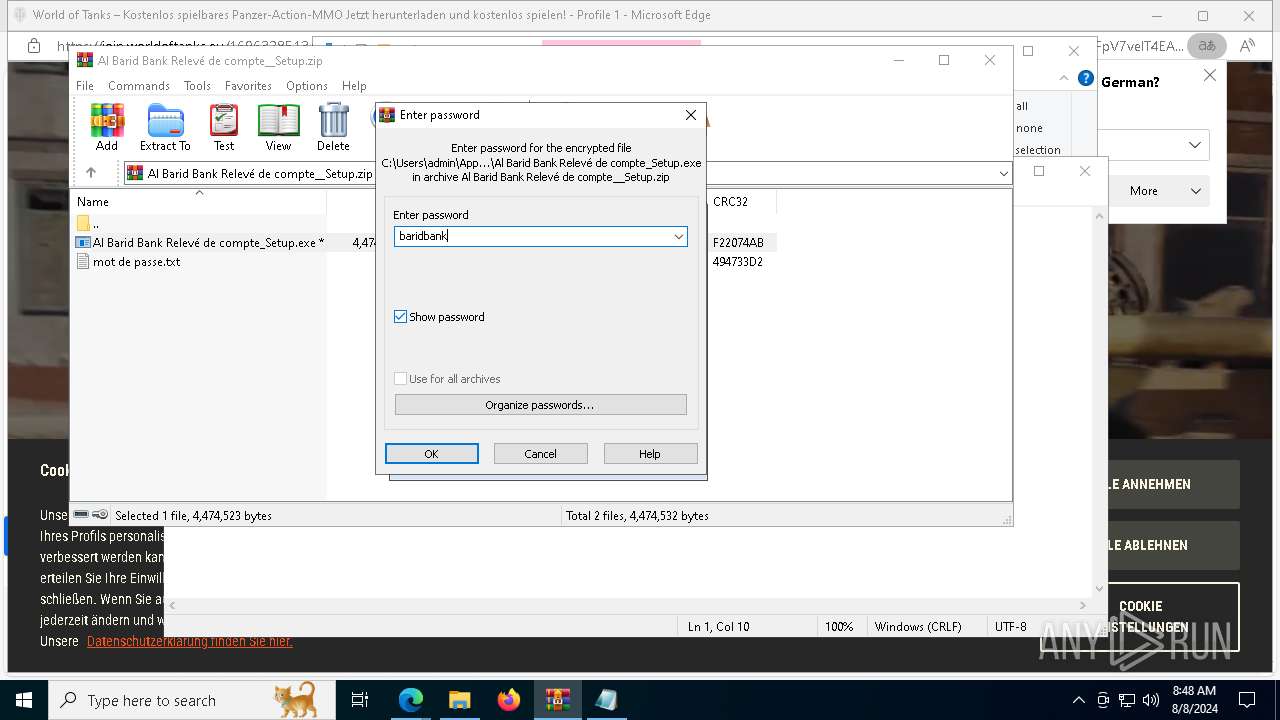
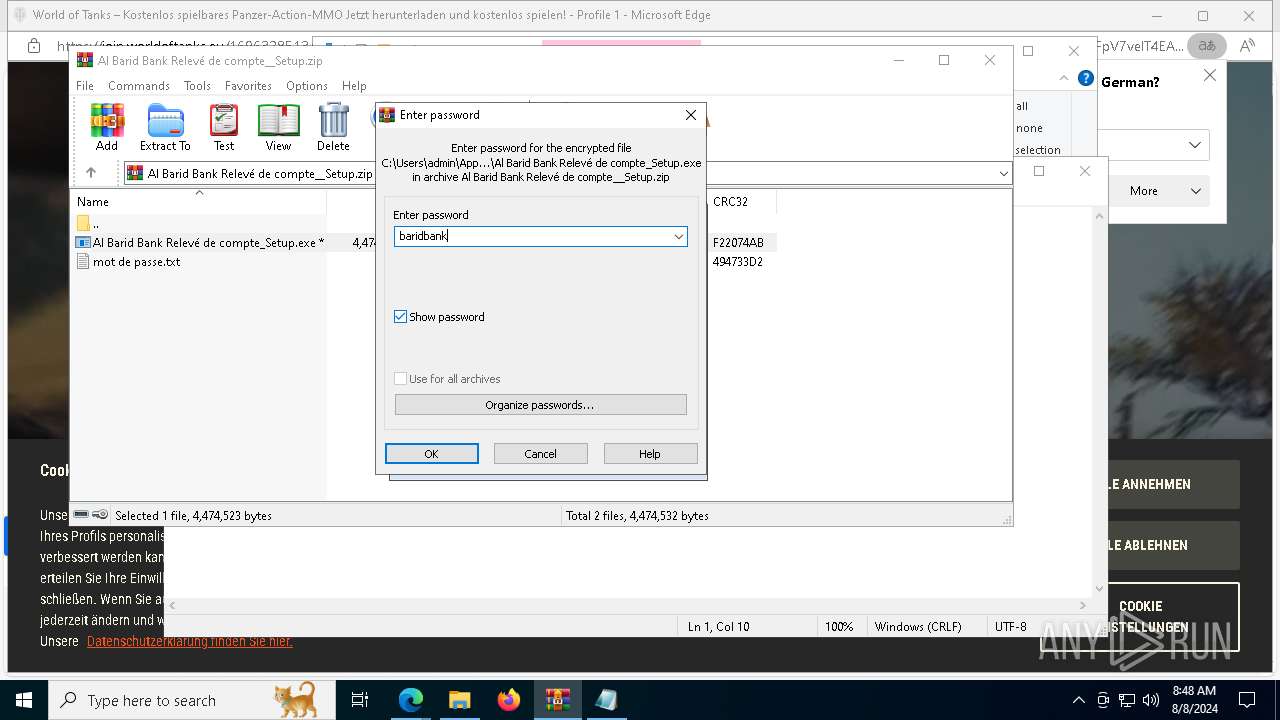
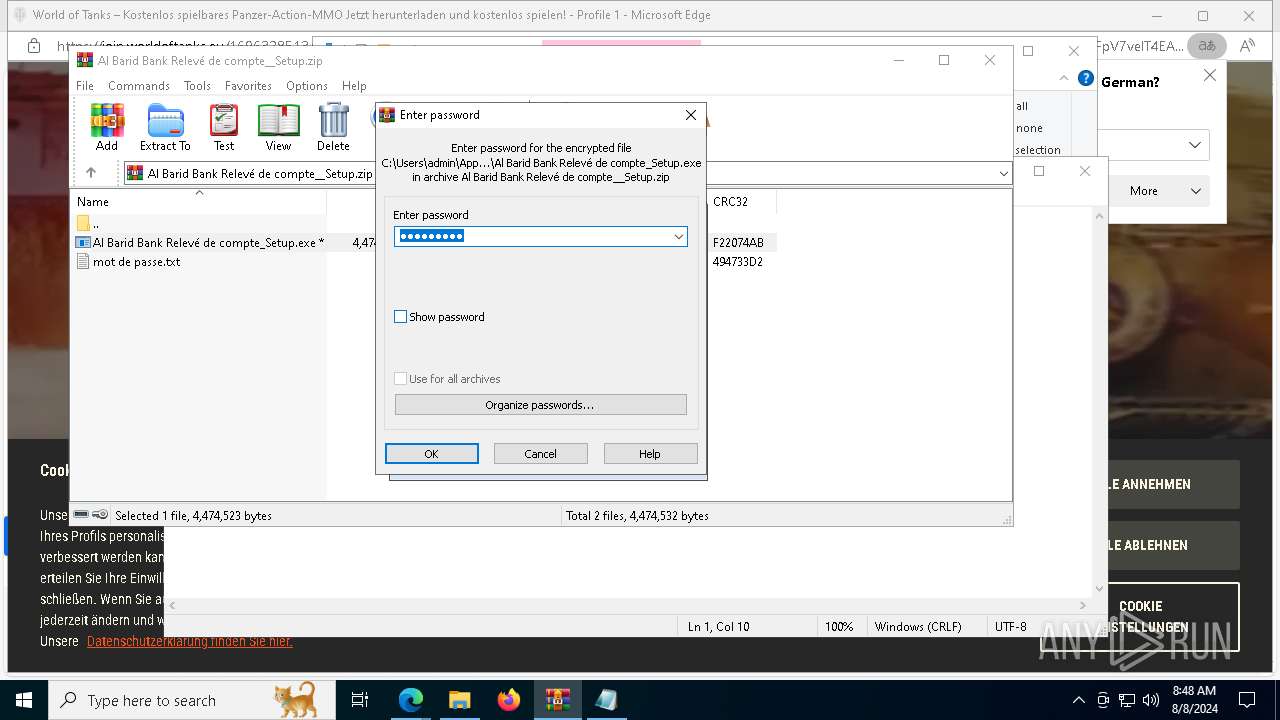
Manual execution by a user
- WinRAR.exe (PID: 9148)
Application launched itself
- msedge.exe (PID: 6480)
- msedge.exe (PID: 5624)
Reads security settings of Internet Explorer
- notepad.exe (PID: 9208)
Drops the executable file immediately after the start
- WinRAR.exe (PID: 9148)
Create files in a temporary directory
- Al Barid Bank Relevé de compte_Setup.exe (PID: 5852)
- Al Barid Bank Relevé de compte_Setup.tmp (PID: 8784)
- Al Barid Bank Relevé de compte_Setup.exe (PID: 8796)
Process checks computer location settings
- Al Barid Bank Relevé de compte_Setup.tmp (PID: 5920)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 1248)
- powershell.exe (PID: 2876)
Creates files in the program directory
- Al Barid Bank Relevé de compte_Setup.tmp (PID: 8784)
Creates a software uninstall entry
- Al Barid Bank Relevé de compte_Setup.tmp (PID: 8784)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 9148)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 1248)
- powershell.exe (PID: 2876)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
260
Monitored processes
113
Malicious processes
5
Suspicious processes
5
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 320 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=2576 --field-trial-handle=2340,i,4426026162772896071,5010002586607089740,262144 --variations-seed-version /prefetch:3 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 420 | "C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=5328 --field-trial-handle=2328,i,13602101768383646364,13676364409634111137,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 840 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=1692 --field-trial-handle=2328,i,13602101768383646364,13676364409634111137,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1080 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=7712 --field-trial-handle=2328,i,13602101768383646364,13676364409634111137,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1116 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=edge_xpay_wallet.mojom.EdgeXPayWalletService --lang=en-US --service-sandbox-type=utility --no-appcompat-clear --mojo-platform-channel-handle=5212 --field-trial-handle=2328,i,13602101768383646364,13676364409634111137,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 | |||||||||||||||
| 1248 | "powershell" -ex bypass -C "Add-MpPreference -ExclusionPath 'C:\WINDOWS\Security\updateagent','c:','d:','e:','f:','g:','h:','i:'" | C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | — | Al Barid Bank Relevé de compte_Setup.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1556 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=3368 --field-trial-handle=2340,i,4426026162772896071,5010002586607089740,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1716 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --extension-process --renderer-sub-type=extension --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=45 --mojo-platform-channel-handle=4384 --field-trial-handle=2328,i,13602101768383646364,13676364409634111137,262144 --variations-seed-version /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1860 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | reg.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1948 | "C:\WINDOWS\SystemApps\MicrosoftWindows.Client.CBS_cw5n1h2txyewy\TextInputHost.exe" -ServerName:InputApp.AppXjd5de1g66v206tj52m9d0dtpppx4cgpn.mca | C:\Windows\SystemApps\MicrosoftWindows.Client.CBS_cw5n1h2txyewy\TextInputHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Version: 123.26505.0.0 Modules
| |||||||||||||||
Total events
45 590
Read events
45 311
Write events
268
Delete events
11
Modification events
| (PID) Process: | (6480) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6480) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6480) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (6480) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (6480) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6480) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\EdgeUpdate\ClientState\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (6480) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (6480) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge |
| Operation: | write | Name: | UsageStatsInSample |
Value: 1 | |||
| (PID) Process: | (6480) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (6480) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062} |
| Operation: | write | Name: | urlstats |
Value: 0 | |||
Executable files
15
Suspicious files
443
Text files
163
Unknown types
31
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6480 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RFe561a.TMP | — | |
MD5:— | SHA256:— | |||
| 6480 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6480 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RFe562a.TMP | — | |
MD5:— | SHA256:— | |||
| 6480 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RFe562a.TMP | — | |
MD5:— | SHA256:— | |||
| 6480 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6480 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6480 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RFe561a.TMP | — | |
MD5:— | SHA256:— | |||
| 6480 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6480 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RFe563a.TMP | — | |
MD5:— | SHA256:— | |||
| 6480 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
44
TCP/UDP connections
350
DNS requests
361
Threats
14
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2616 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
8328 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/e456c896-44a6-416b-bdf2-a332bb03a659?P1=1723474574&P2=404&P3=2&P4=kmWFDNcbmt7fR%2bxsCM9IGKkKHP7PFxoWskcgHaiCON0wPldLU2Rl9r%2fVfMJQeJxr4jZHLzEBaLcGDWnrs25vzw%3d%3d | unknown | — | — | whitelisted |
8328 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/e456c896-44a6-416b-bdf2-a332bb03a659?P1=1723474574&P2=404&P3=2&P4=kmWFDNcbmt7fR%2bxsCM9IGKkKHP7PFxoWskcgHaiCON0wPldLU2Rl9r%2fVfMJQeJxr4jZHLzEBaLcGDWnrs25vzw%3d%3d | unknown | — | — | whitelisted |
7652 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
5336 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
5336 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEApDqVCbATUviZV57HIIulA%3D | unknown | — | — | whitelisted |
8328 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/a10da0da-8991-4166-aadf-622aa0b2ce62?P1=1723708734&P2=404&P3=2&P4=kL%2fD3%2fxsWbhWTDxxDk15ZQBDoJ94%2f6qxK3G7t4jCwJfsv5cD0v3AJwxt9wxCyGhXn6FOcnmWGCYywpcx2IJZVQ%3d%3d | unknown | — | — | whitelisted |
5336 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEA77flR%2B3w%2FxBpruV2lte6A%3D | unknown | — | — | whitelisted |
8328 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/e456c896-44a6-416b-bdf2-a332bb03a659?P1=1723474574&P2=404&P3=2&P4=kmWFDNcbmt7fR%2bxsCM9IGKkKHP7PFxoWskcgHaiCON0wPldLU2Rl9r%2fVfMJQeJxr4jZHLzEBaLcGDWnrs25vzw%3d%3d | unknown | — | — | whitelisted |
8328 | svchost.exe | HEAD | 200 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/e456c896-44a6-416b-bdf2-a332bb03a659?P1=1723474574&P2=404&P3=2&P4=kmWFDNcbmt7fR%2bxsCM9IGKkKHP7PFxoWskcgHaiCON0wPldLU2Rl9r%2fVfMJQeJxr4jZHLzEBaLcGDWnrs25vzw%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
812 | RUXIMICS.exe | 51.124.78.146:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2120 | MoUsoCoreWorker.exe | 51.124.78.146:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3268 | svchost.exe | 51.124.78.146:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 239.255.255.250:1900 | — | — | — | whitelisted |
6824 | msedge.exe | 104.16.114.74:443 | www.mediafire.com | — | — | unknown |
6824 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6824 | msedge.exe | 204.79.197.239:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
6824 | msedge.exe | 13.107.253.67:443 | edge-mobile-static.azureedge.net | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
www.mediafire.com |
| shared |
business.bing.com |
| whitelisted |
bzib.nelreports.net |
| whitelisted |
www.bing.com |
| whitelisted |
the.gatekeeperconsent.com |
| unknown |
www.googletagmanager.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6824 | msedge.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain (www .mediafire .com) in DNS Lookup |
6824 | msedge.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain (www .mediafire .com) in DNS Lookup |
6824 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
6824 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
6824 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
6824 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
6824 | msedge.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain in DNS Lookup (download .mediafire .com) |
6824 | msedge.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain in DNS Lookup (download .mediafire .com) |
6824 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
6824 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
1 ETPRO signatures available at the full report
Process | Message |
|---|---|
msedge.exe | [0808/084718.521:ERROR:process_reader_win.cc(200)] ResumeThread: The operation completed successfully. (0x0)
|
msedge.exe | [0808/084718.522:ERROR:process_reader_win.cc(164)] SuspendThread: Access is denied. (0x5)
|
msedge.exe | [0808/084718.522:ERROR:process_reader_win.cc(164)] SuspendThread: Access is denied. (0x5)
|
msedge.exe | [0808/084718.522:ERROR:process_reader_win.cc(164)] SuspendThread: Access is denied. (0x5)
|
msedge.exe | [0808/084718.522:ERROR:process_reader_win.cc(164)] SuspendThread: Access is denied. (0x5)
|
msedge.exe | [0808/084718.522:ERROR:process_reader_win.cc(164)] SuspendThread: Access is denied. (0x5)
|
msedge.exe | [0808/084718.522:ERROR:process_reader_win.cc(164)] SuspendThread: Access is denied. (0x5)
|
msedge.exe | [0808/084718.522:ERROR:process_reader_win.cc(164)] SuspendThread: Access is denied. (0x5)
|
msedge.exe | [0808/084733.595:WARNING:device_ticket.cc(151)] Timed out waiting for device ticket. Canceling async operation.
|
msedge.exe | [0808/084734.166:ERROR:process_memory_win.cc(74)] ReadMemory at 0x7ff6278d0000 of 64 bytes failed: Only part of a ReadProcessMemory or WriteProcessMemory request was completed. (0x12B)
|