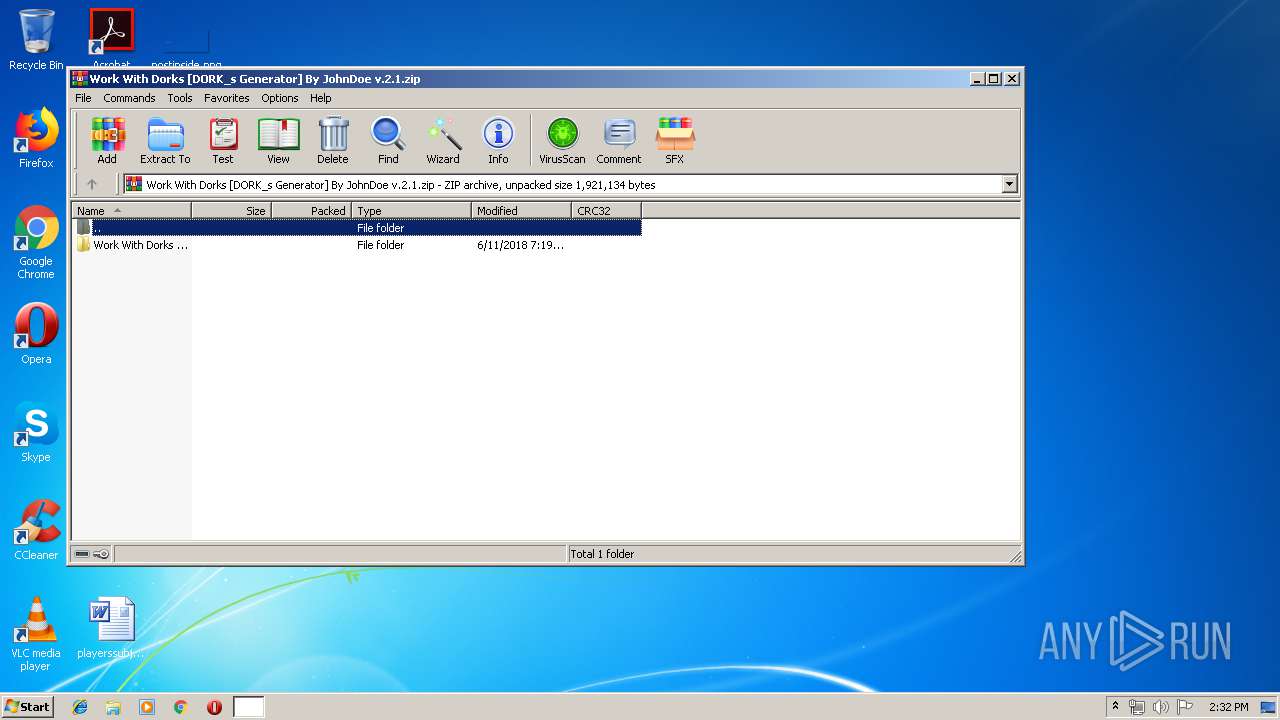
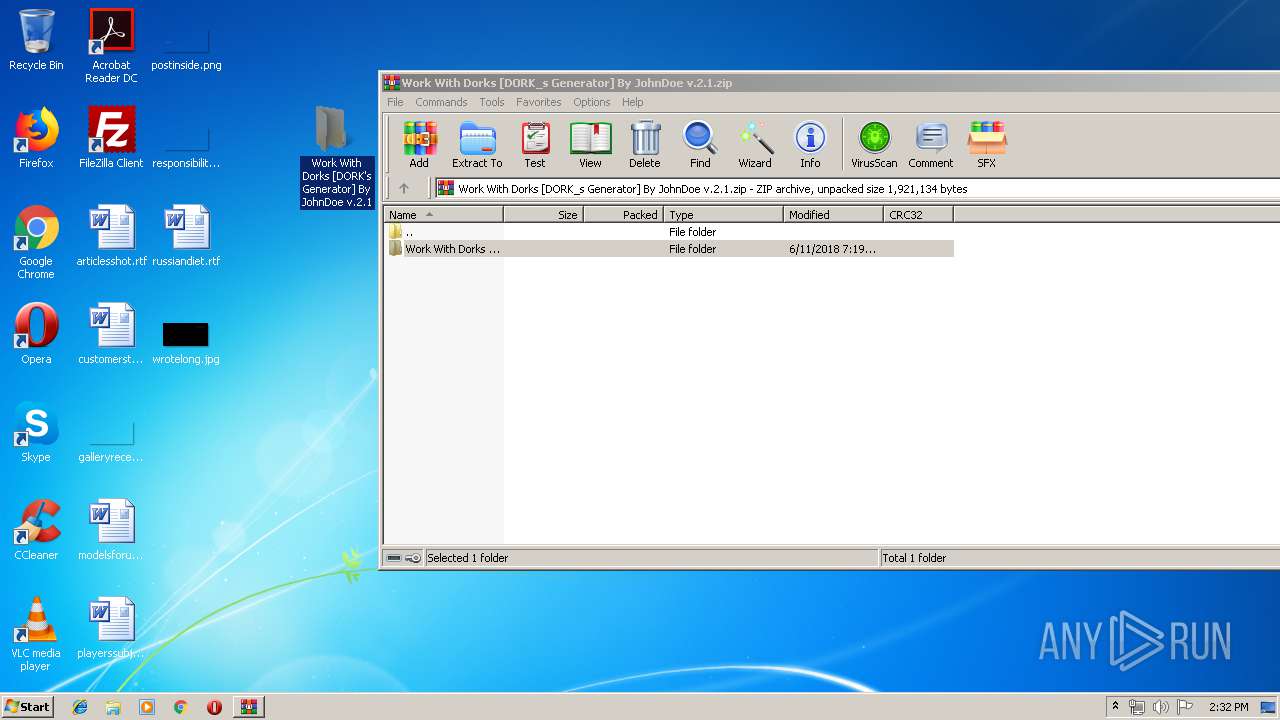
| File name: | Work With Dorks [DORK_s Generator] By JohnDoe v.2.1.zip |
| Full analysis: | https://app.any.run/tasks/d2ad636d-d5b0-43a8-94cf-e44d10734b6a |
| Verdict: | No threats detected |
| Analysis date: | August 12, 2019, 13:32:06 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | D34947A081A10FBD5BB48BDE348EE6F8 |
| SHA1: | 8D7038EFE105BBF1BF664F22E9305077ECB1AA12 |
| SHA256: | CE387E1E72E4B63370D5FDFBEDDBDB3D31AD39554265C79D84ED487A67C7BB8E |
| SSDEEP: | 24576:6yL/ymj3z19vo3idkhLLzybbxuy1CHyfxV8/eqnj:5yq3zldktuEy17xVEj |
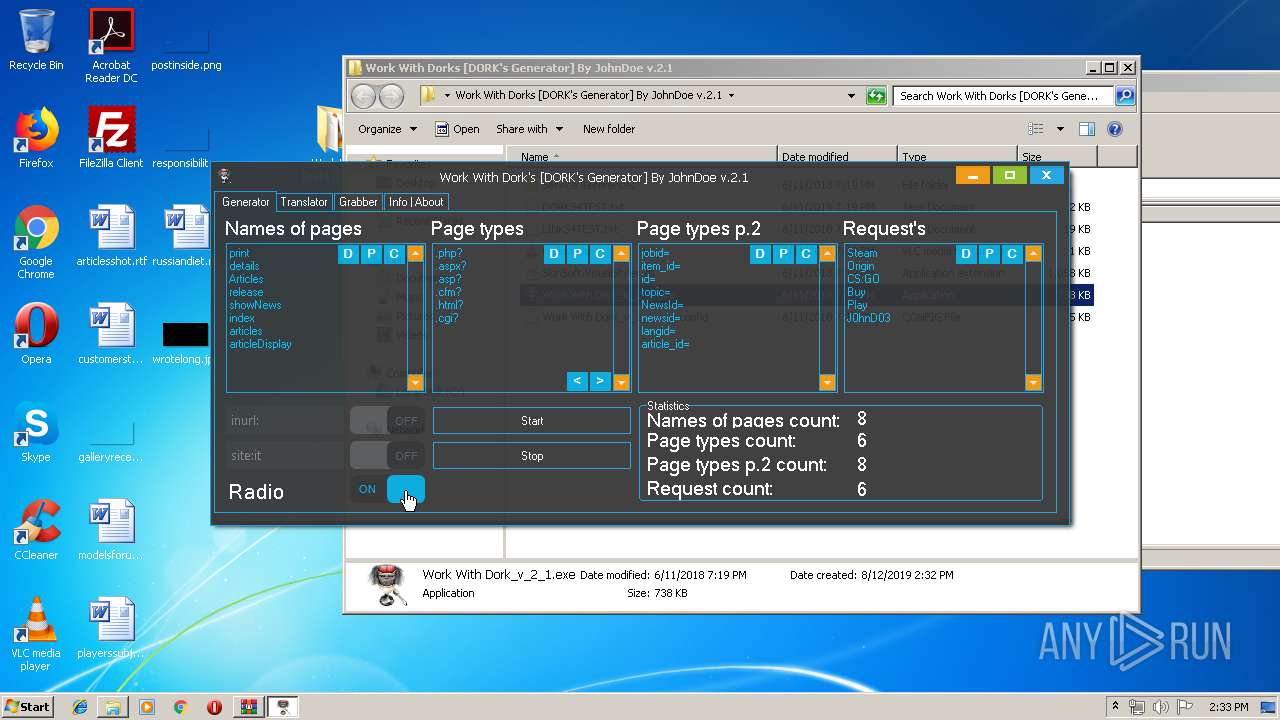
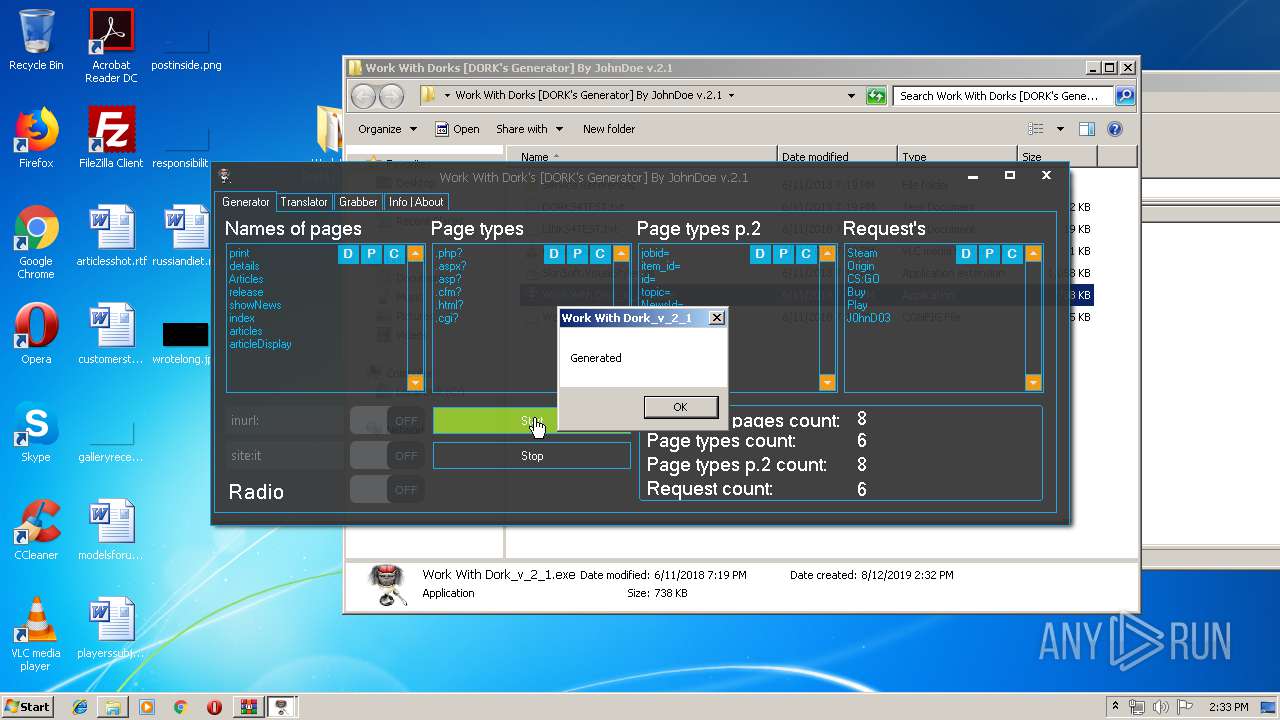
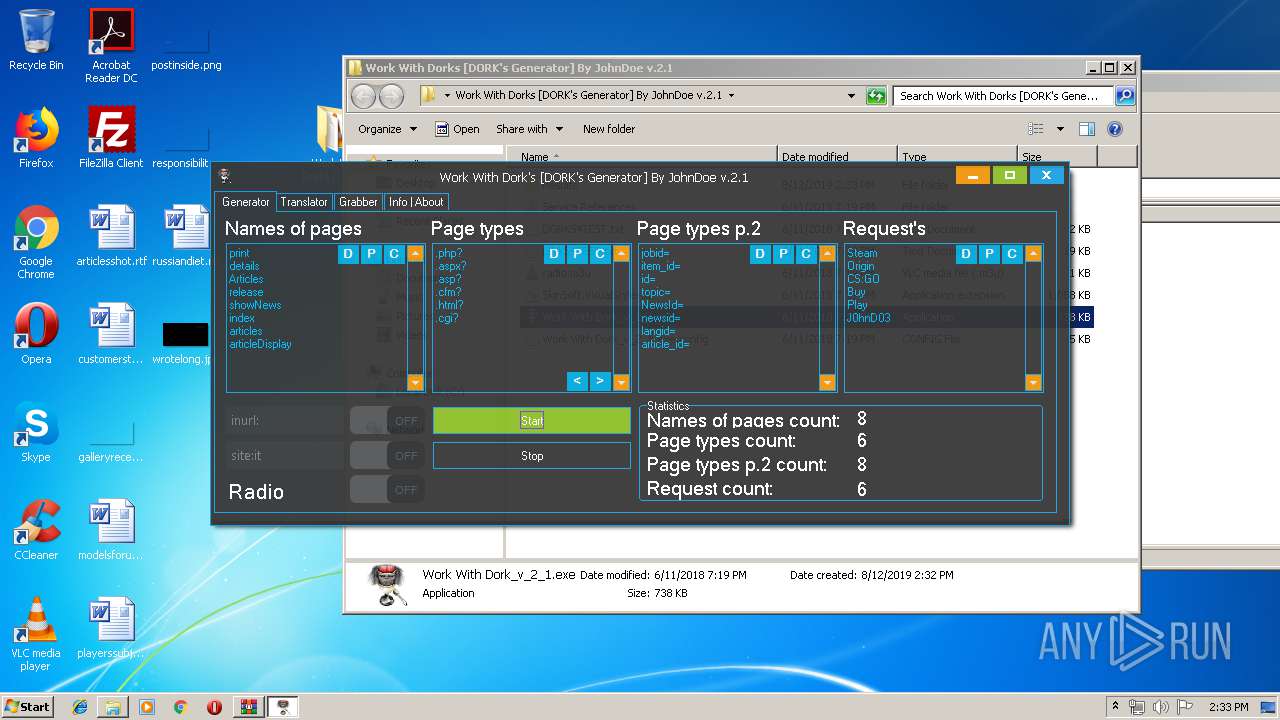
MALICIOUS
Loads dropped or rewritten executable
- Work With Dork_v_2_1.exe (PID: 912)
SUSPICIOUS
Reads Internet Cache Settings
- Work With Dork_v_2_1.exe (PID: 912)
Creates files in the user directory
- Work With Dork_v_2_1.exe (PID: 912)
Executable content was dropped or overwritten
- Work With Dork_v_2_1.exe (PID: 912)
INFO
Manual execution by user
- Work With Dork_v_2_1.exe (PID: 912)
- NOTEPAD.EXE (PID: 2620)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0008 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2018:06:11 19:19:24 |
| ZipCRC: | 0x624d1d35 |
| ZipCompressedSize: | 558 |
| ZipUncompressedSize: | 1861 |
| ZipFileName: | Work With Dorks [DORK's Generator] By JohnDoe v.2.1/DORKS4TEST.txt |
Total processes
40
Monitored processes
3
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
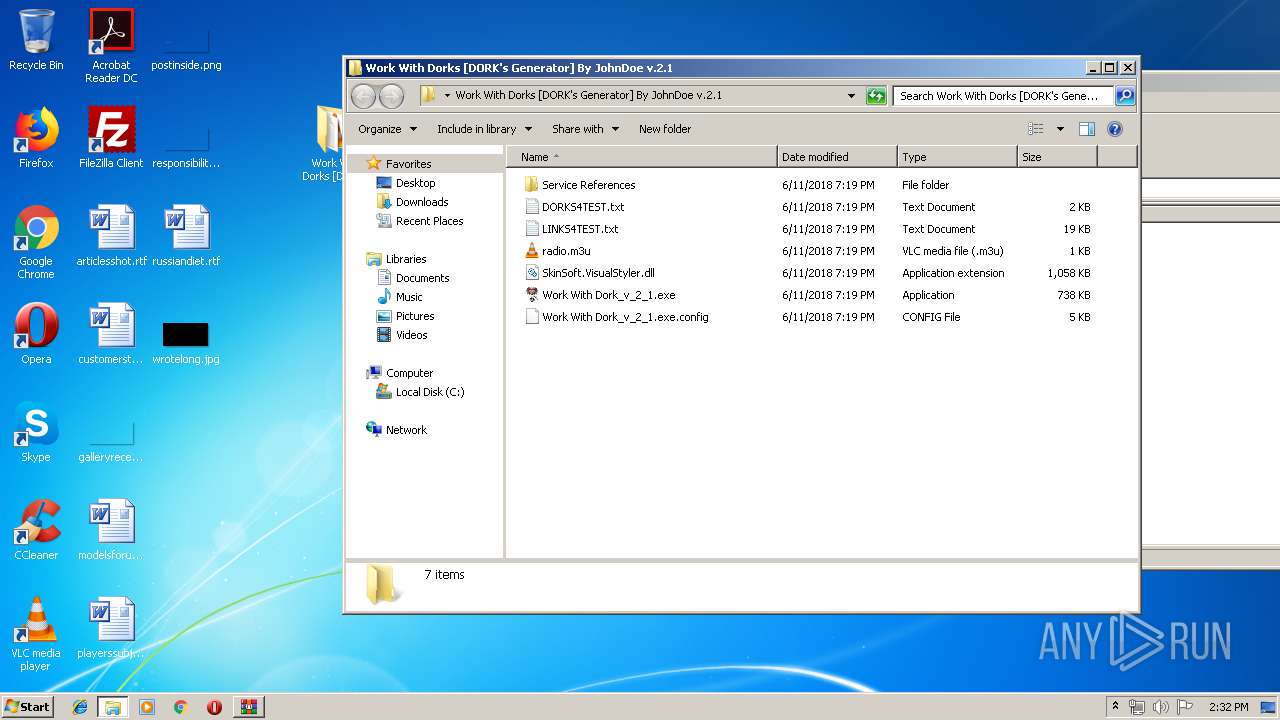
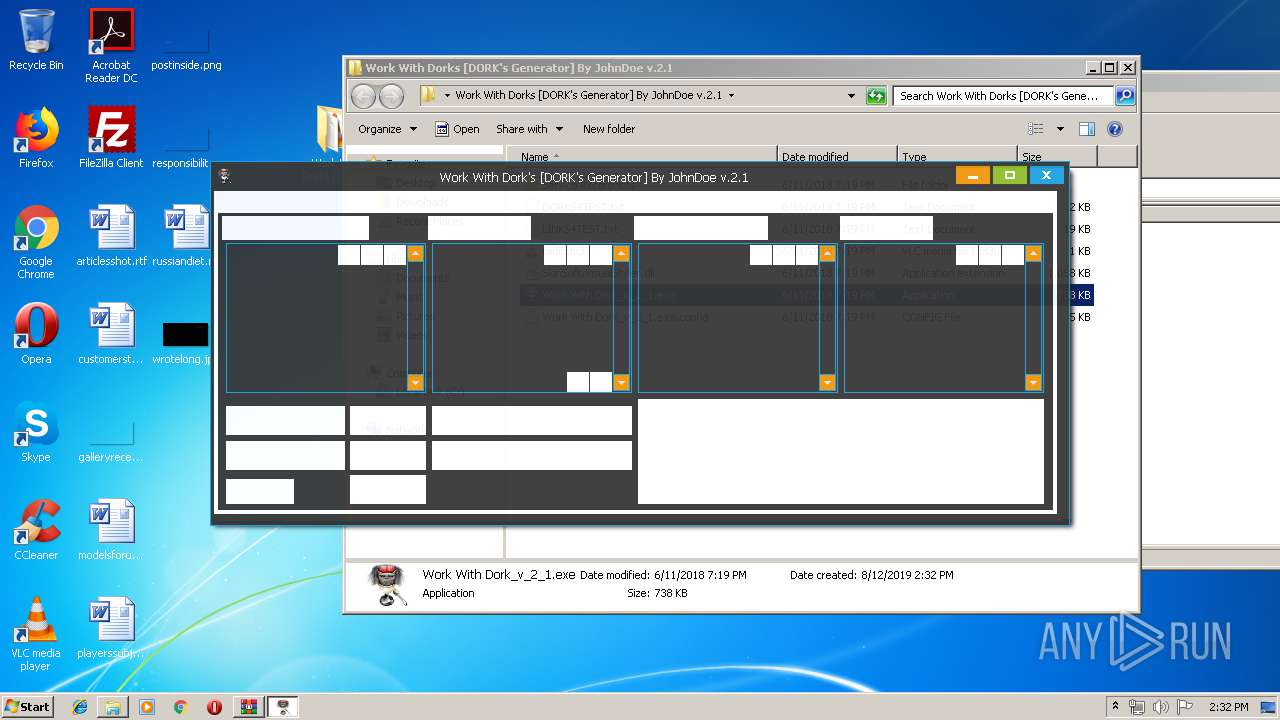
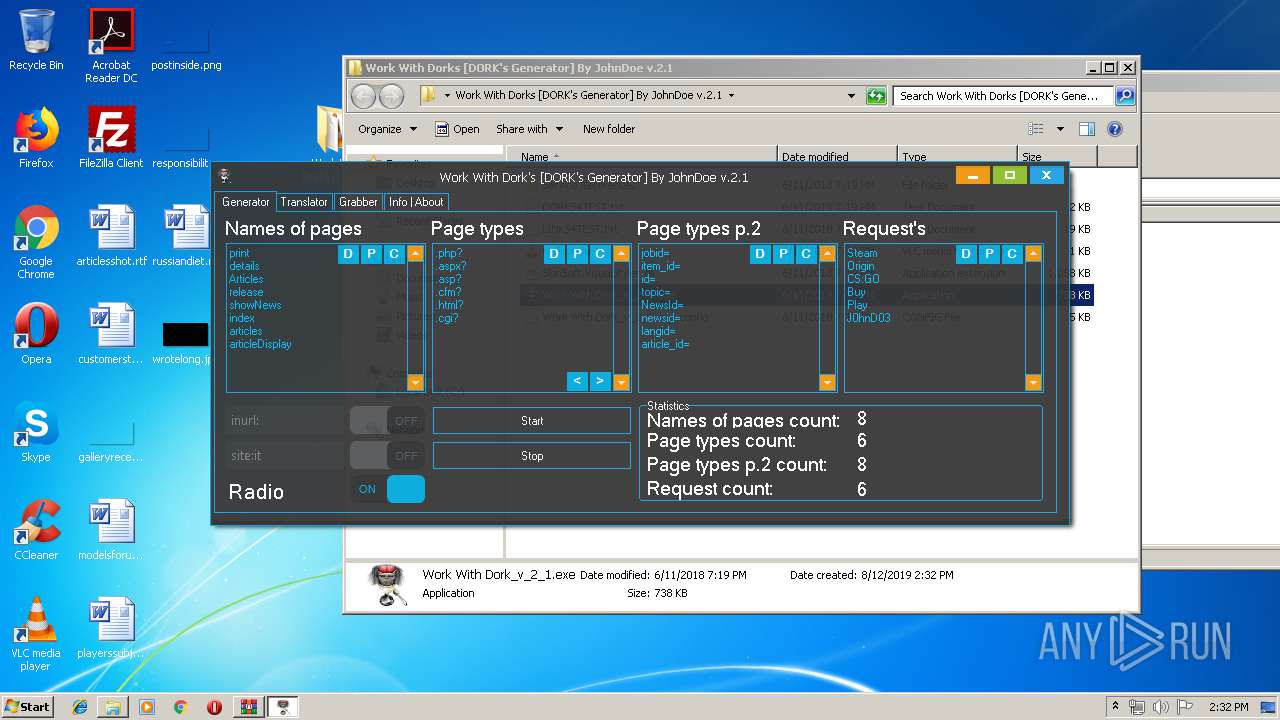
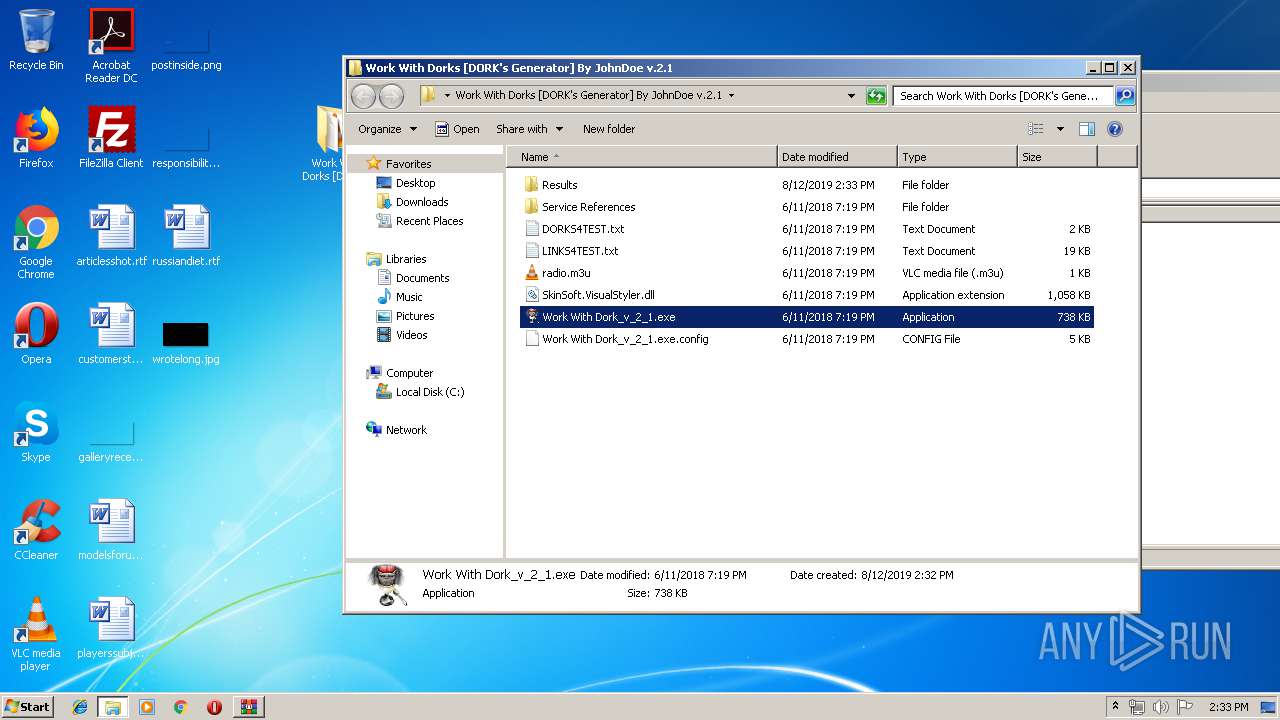
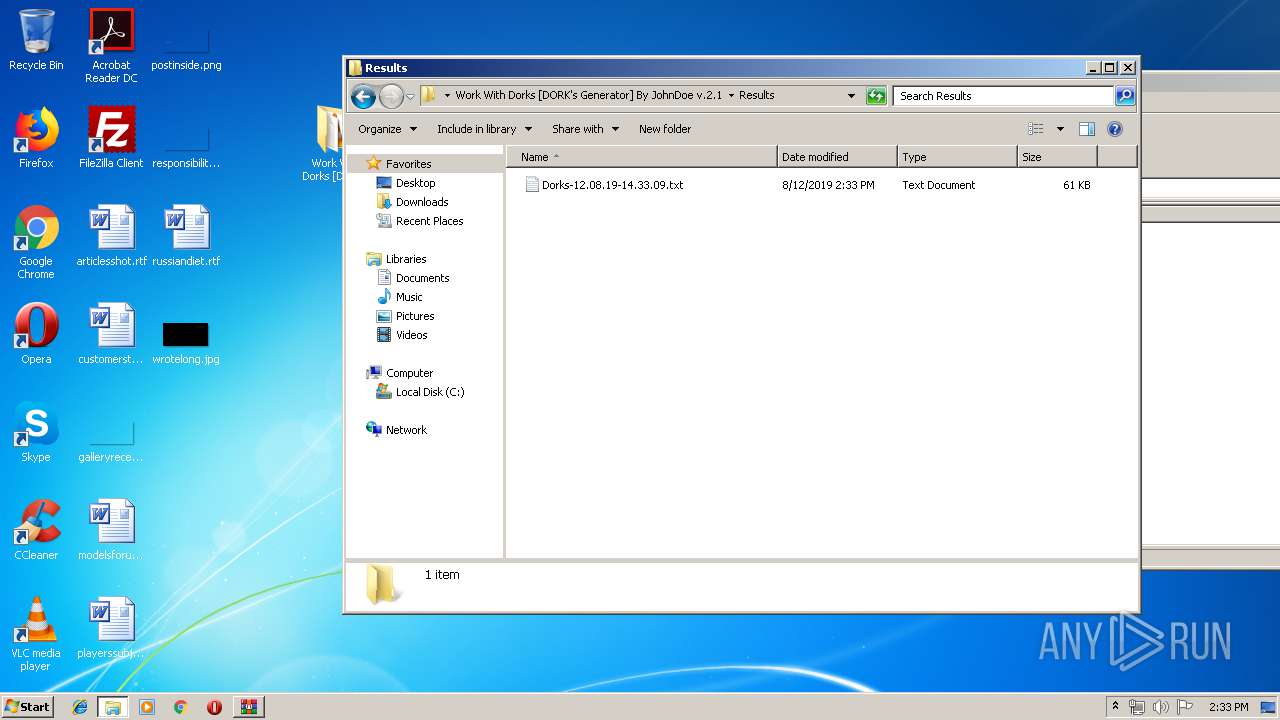
| 912 | "C:\Users\admin\Desktop\Work With Dorks [DORK's Generator] By JohnDoe v.2.1\Work With Dork_v_2_1.exe" | C:\Users\admin\Desktop\Work With Dorks [DORK's Generator] By JohnDoe v.2.1\Work With Dork_v_2_1.exe | explorer.exe | ||||||||||||
User: admin Company: J0hnD03 SoftWare Integrity Level: MEDIUM Description: Work With Dork_v_2_1 Exit code: 3221225547 Version: 2.1.0.0 Modules
| |||||||||||||||
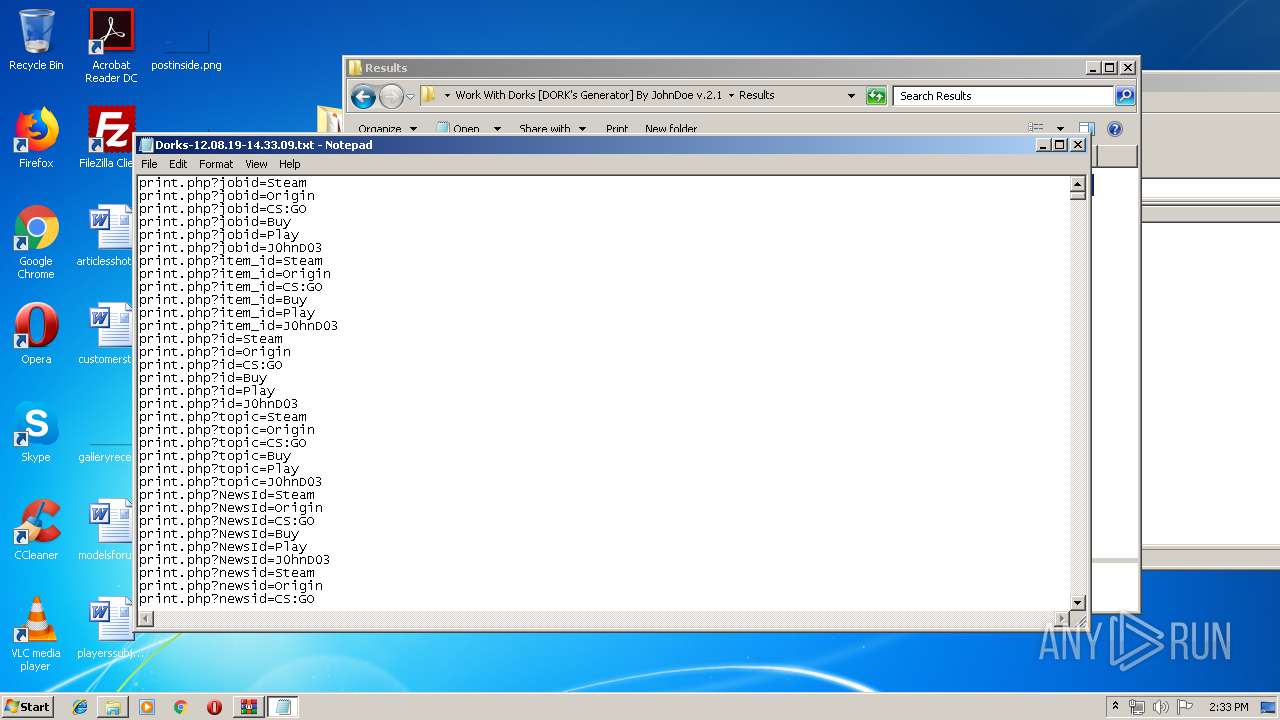
| 2620 | "C:\Windows\system32\NOTEPAD.EXE" C:\Users\admin\Desktop\Work With Dorks [DORK's Generator] By JohnDoe v.2.1\Results\Dorks-12.08.19-14.33.09.txt | C:\Windows\system32\NOTEPAD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2740 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\Work With Dorks [DORK_s Generator] By JohnDoe v.2.1.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
Total events
584
Read events
536
Write events
47
Delete events
1
Modification events
| (PID) Process: | (2740) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2740) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2740) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\72\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2740) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Work With Dorks [DORK_s Generator] By JohnDoe v.2.1.zip | |||
| (PID) Process: | (2740) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2740) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2740) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2740) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (912) Work With Dork_v_2_1.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (912) Work With Dork_v_2_1.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
1
Suspicious files
3
Text files
2
Unknown types
1
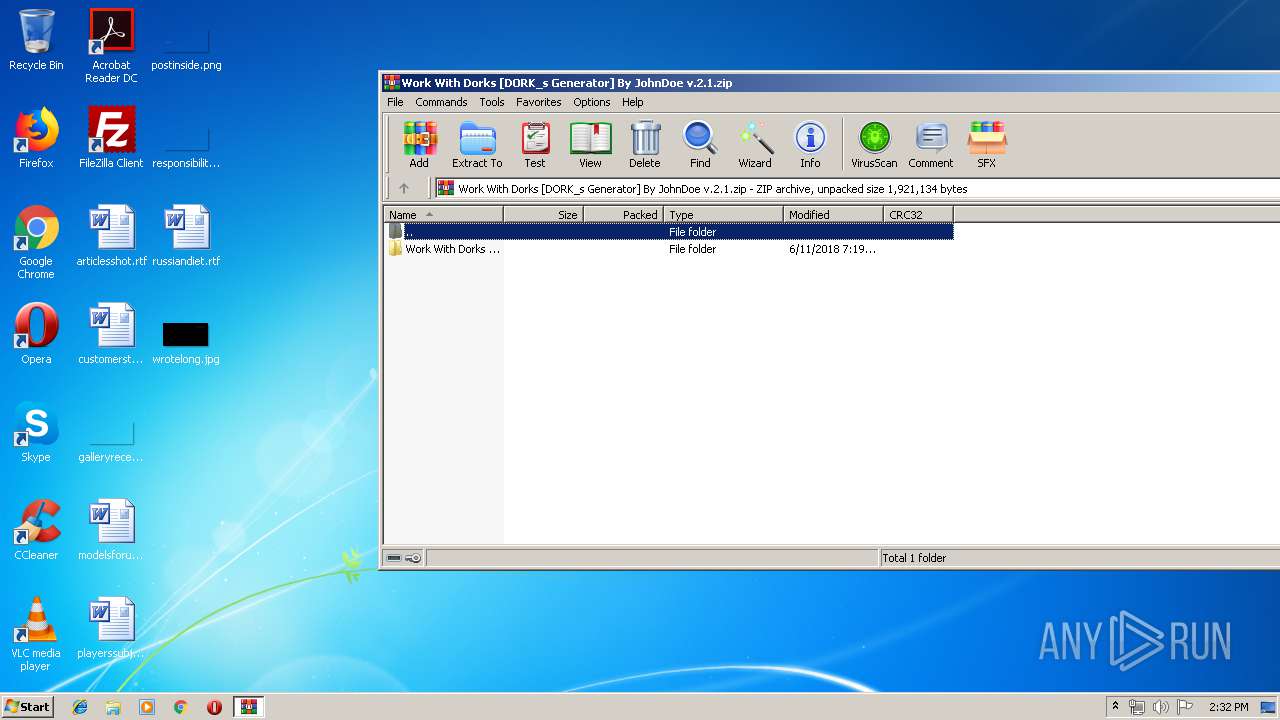
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2740 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2740.25412\Work With Dorks [DORK's Generator] By JohnDoe v.2.1\DORKS4TEST.txt | — | |
MD5:— | SHA256:— | |||
| 2740 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2740.25412\Work With Dorks [DORK's Generator] By JohnDoe v.2.1\LINKS4TEST.txt | — | |
MD5:— | SHA256:— | |||
| 2740 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2740.25412\Work With Dorks [DORK's Generator] By JohnDoe v.2.1\Service References\TranslatorService\Reference.svcmap | — | |
MD5:— | SHA256:— | |||
| 2740 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2740.25412\Work With Dorks [DORK's Generator] By JohnDoe v.2.1\Service References\TranslatorService\Reference.vb | — | |
MD5:— | SHA256:— | |||
| 2740 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2740.25412\Work With Dorks [DORK's Generator] By JohnDoe v.2.1\Service References\TranslatorService\SoapService.wsdl | — | |
MD5:— | SHA256:— | |||
| 2740 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2740.25412\Work With Dorks [DORK's Generator] By JohnDoe v.2.1\Service References\TranslatorService\SoapService1.wsdl | — | |
MD5:— | SHA256:— | |||
| 2740 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2740.25412\Work With Dorks [DORK's Generator] By JohnDoe v.2.1\Service References\TranslatorService\configuration.svcinfo | — | |
MD5:— | SHA256:— | |||
| 2740 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2740.25412\Work With Dorks [DORK's Generator] By JohnDoe v.2.1\Service References\TranslatorService\configuration91.svcinfo | — | |
MD5:— | SHA256:— | |||
| 2740 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2740.25412\Work With Dorks [DORK's Generator] By JohnDoe v.2.1\Service References\TranslatorService\soap.wsdl | — | |
MD5:— | SHA256:— | |||
| 2740 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2740.25412\Work With Dorks [DORK's Generator] By JohnDoe v.2.1\Service References\TranslatorService\soap.xsd | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
3
DNS requests
1
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
912 | Work With Dork_v_2_1.exe | GET | — | 163.172.84.49:80 | http://play.newtone.fm/live_01 | FR | — | — | unknown |
912 | Work With Dork_v_2_1.exe | GET | — | 163.172.84.49:80 | http://play.newtone.fm/live_01 | FR | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
912 | Work With Dork_v_2_1.exe | 163.172.84.49:80 | play.newtone.fm | Online S.a.s. | FR | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
play.newtone.fm |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
912 | Work With Dork_v_2_1.exe | Generic Protocol Command Decode | SURICATA Applayer Detect protocol only one direction |