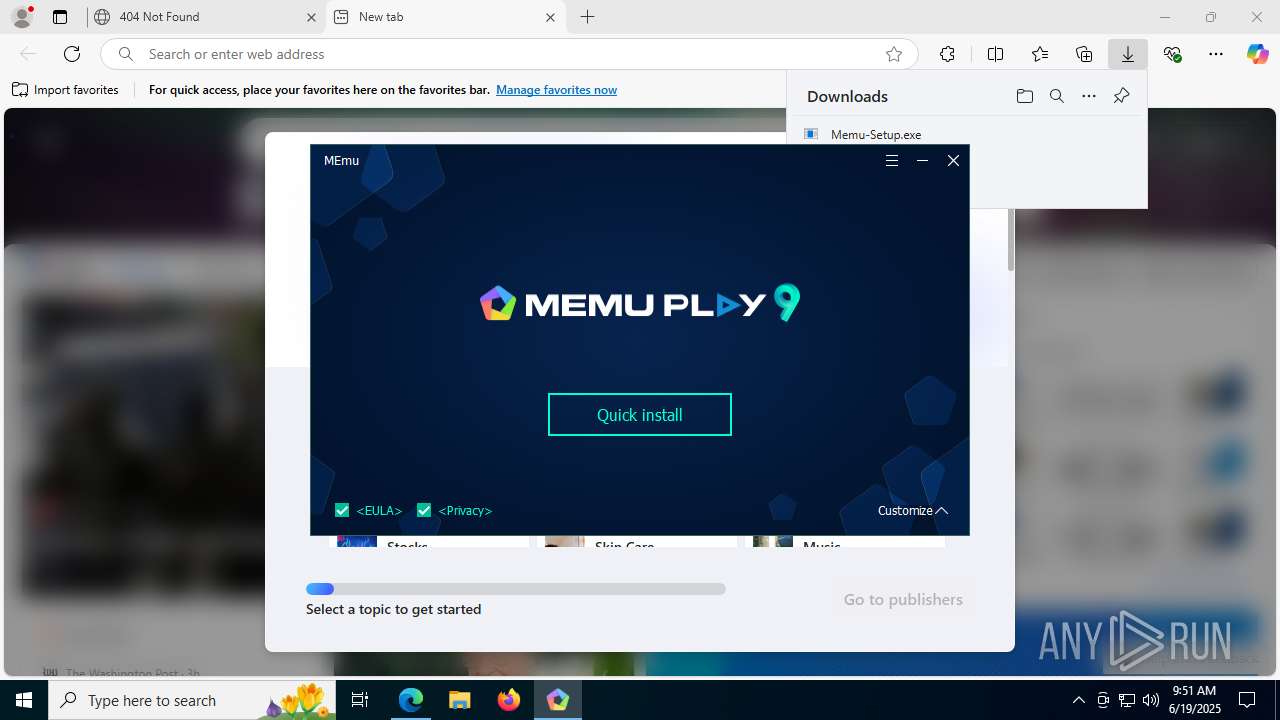
| URL: | dl.memuplay.com |
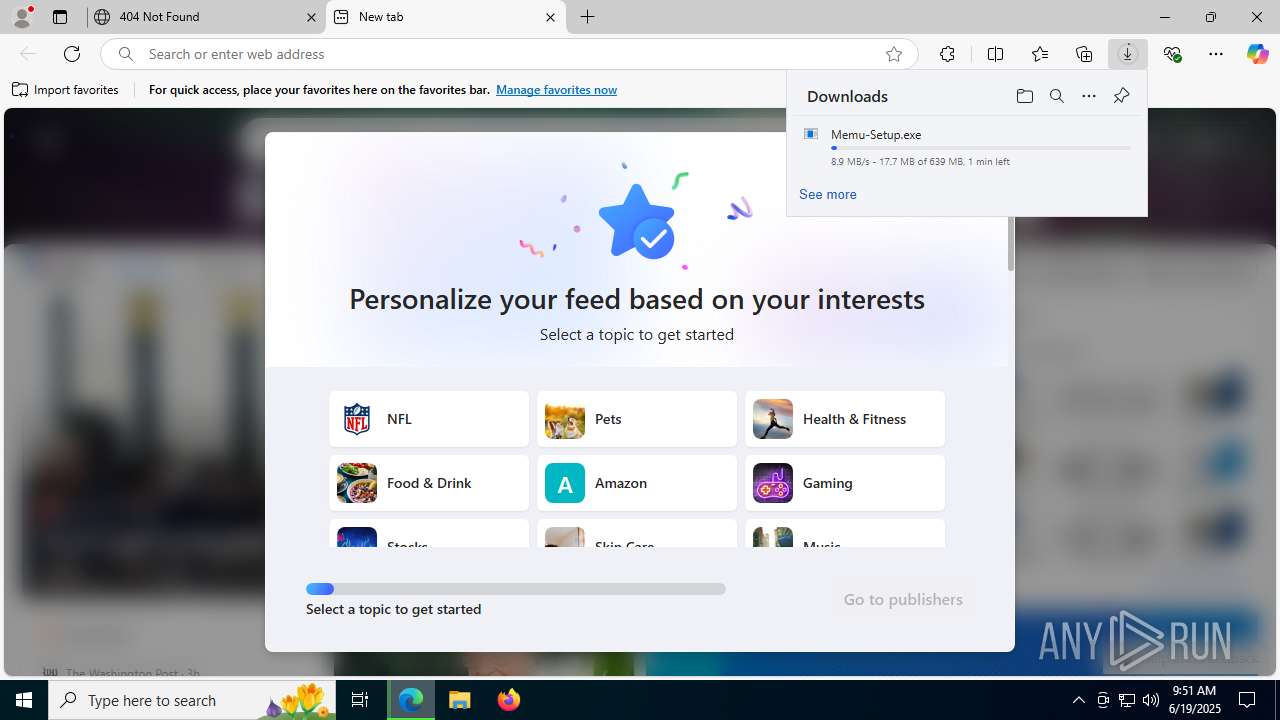
| Full analysis: | https://app.any.run/tasks/721440fe-c3df-4729-950d-7035a67d3aa0 |
| Verdict: | Malicious activity |
| Analysis date: | June 19, 2025, 09:50:44 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MD5: | 5806DE3BC0FE50B78B319A8B574E5CE9 |
| SHA1: | 215C070E78238AAE9EDDC5DD69828243E02F865E |
| SHA256: | CE32A8503256306989D7E15255C5EA5323A3762C5007014CF5B1BB2B29A65680 |
| SSDEEP: | 3:UtQVHZI:UiRZI |
MALICIOUS
Executing a file with an untrusted certificate
- MEmuDrvInst.exe (PID: 6524)
- MemuService.exe (PID: 316)
Registers / Runs the DLL via REGSVR32.EXE
- Memu-Setup.exe (PID: 3100)
SUSPICIOUS
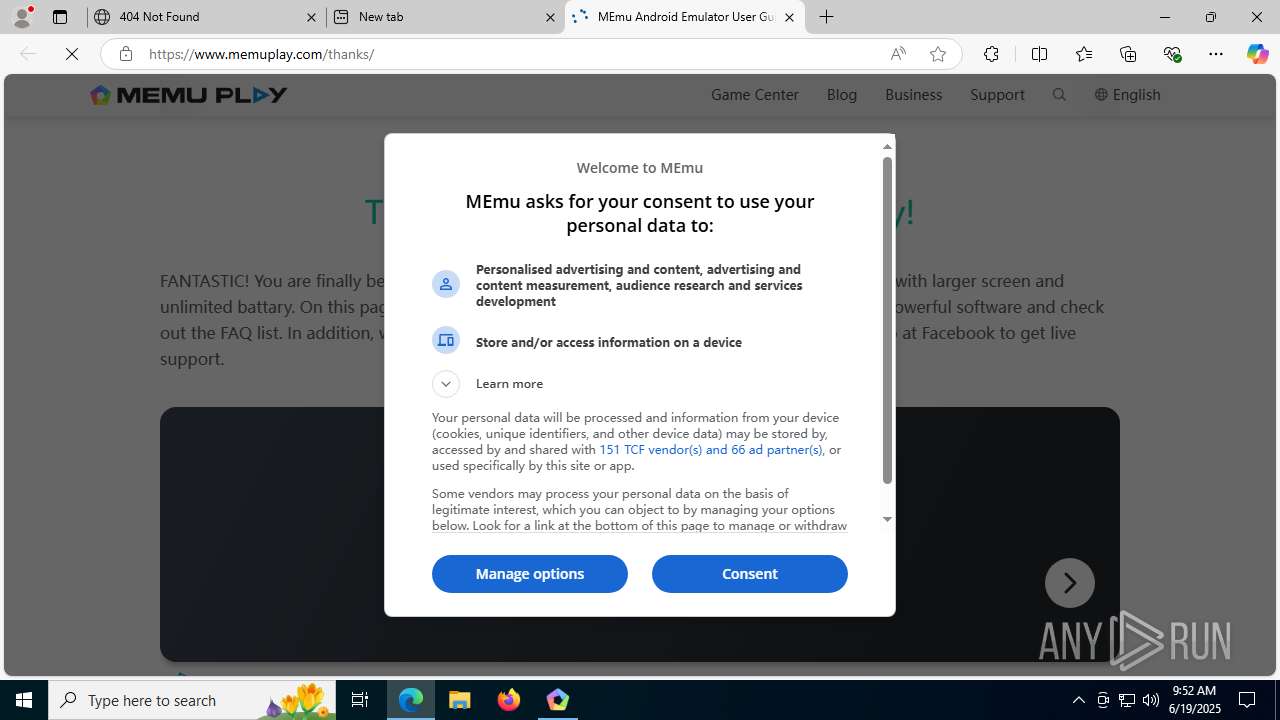
Potential Corporate Privacy Violation
- msedge.exe (PID: 2228)
There is functionality for taking screenshot (YARA)
- Memu-Setup.exe (PID: 3100)
Drops 7-zip archiver for unpacking
- Memu-Setup.exe (PID: 3100)
- 7za.exe (PID: 2368)
Windows service management via SC.EXE
- sc.exe (PID: 6172)
- sc.exe (PID: 2512)
- sc.exe (PID: 1056)
- sc.exe (PID: 2276)
- sc.exe (PID: 2356)
- sc.exe (PID: 8040)
- sc.exe (PID: 2468)
- sc.exe (PID: 7000)
- sc.exe (PID: 7532)
- sc.exe (PID: 7784)
- sc.exe (PID: 4888)
- sc.exe (PID: 7864)
- sc.exe (PID: 2072)
- sc.exe (PID: 1324)
- sc.exe (PID: 7960)
- sc.exe (PID: 4920)
- sc.exe (PID: 304)
- sc.exe (PID: 2044)
- sc.exe (PID: 6148)
- sc.exe (PID: 6620)
- sc.exe (PID: 4172)
- sc.exe (PID: 2708)
- sc.exe (PID: 5768)
- sc.exe (PID: 7180)
- sc.exe (PID: 6176)
- sc.exe (PID: 2952)
Executable content was dropped or overwritten
- Memu-Setup.exe (PID: 3100)
- 7za.exe (PID: 2368)
- 7za.exe (PID: 8180)
- 7za.exe (PID: 7548)
- MEmuDrvInst.exe (PID: 6524)
Process drops legitimate windows executable
- Memu-Setup.exe (PID: 3100)
- 7za.exe (PID: 8180)
- 7za.exe (PID: 2368)
- 7za.exe (PID: 7548)
The process creates files with name similar to system file names
- 7za.exe (PID: 8180)
The process drops C-runtime libraries
- 7za.exe (PID: 2368)
- 7za.exe (PID: 8180)
- 7za.exe (PID: 7548)
Drops a system driver (possible attempt to evade defenses)
- 7za.exe (PID: 8180)
- MEmuDrvInst.exe (PID: 6524)
Reads security settings of Internet Explorer
- MEmuDrvInst.exe (PID: 6524)
Creates files in the driver directory
- MEmuDrvInst.exe (PID: 6524)
Creates/Modifies COM task schedule object
- MEmuManage.exe (PID: 6808)
- regsvr32.exe (PID: 6172)
- regsvr32.exe (PID: 4828)
Executes as Windows Service
- MemuService.exe (PID: 316)
Creates a software uninstall entry
- Memu-Setup.exe (PID: 3100)
Searches for installed software
- MEmuConsole.exe (PID: 7776)
INFO
Checks supported languages
- identity_helper.exe (PID: 7952)
- Memu-Setup.exe (PID: 3100)
- Memu-Setup.exe (PID: 8096)
- 7za.exe (PID: 8180)
- 7za.exe (PID: 2368)
- 7za.exe (PID: 7548)
- MEmuDrvInst.exe (PID: 6524)
- MEmuSVC.exe (PID: 6352)
- MEmuSVC.exe (PID: 6192)
- MEmuSVC.exe (PID: 4168)
- MEmuSVC.exe (PID: 3196)
- MemuService.exe (PID: 316)
- MEmuManage.exe (PID: 6808)
- MEmuManage.exe (PID: 3108)
- MEmuSVC.exe (PID: 2028)
- MEmuRepair.exe (PID: 2232)
- MEmuConsole.exe (PID: 7776)
- memuc.exe (PID: 8116)
- MEmuManage.exe (PID: 4380)
- MEmuManage.exe (PID: 8036)
- MEmuSVC.exe (PID: 6148)
- MEmu.exe (PID: 4100)
- MEmuSVC.exe (PID: 5500)
- MEmuManage.exe (PID: 6772)
- MEmuSVC.exe (PID: 2848)
- screenrecord.exe (PID: 6428)
- MEmu.exe (PID: 2028)
- MEmuManage.exe (PID: 3388)
Reads the computer name
- identity_helper.exe (PID: 7952)
- Memu-Setup.exe (PID: 3100)
- Memu-Setup.exe (PID: 8096)
- 7za.exe (PID: 8180)
- 7za.exe (PID: 2368)
- 7za.exe (PID: 7548)
- MEmuDrvInst.exe (PID: 6524)
- MEmuSVC.exe (PID: 6352)
- MEmuManage.exe (PID: 6808)
- MEmuSVC.exe (PID: 3196)
- MEmuManage.exe (PID: 3108)
- MemuService.exe (PID: 316)
- MEmuSVC.exe (PID: 2028)
- MEmuSVC.exe (PID: 6148)
- MEmuConsole.exe (PID: 7776)
- MEmuManage.exe (PID: 4380)
- MEmuManage.exe (PID: 8036)
- MEmuRepair.exe (PID: 2232)
- MEmu.exe (PID: 4100)
- MEmuSVC.exe (PID: 5500)
- MEmuManage.exe (PID: 6772)
- MEmuSVC.exe (PID: 2848)
- MEmu.exe (PID: 2028)
- MEmuManage.exe (PID: 3388)
Application launched itself
- msedge.exe (PID: 1984)
Creates files or folders in the user directory
- Memu-Setup.exe (PID: 3100)
Executable content was dropped or overwritten
- msedge.exe (PID: 1984)
Reads Environment values
- identity_helper.exe (PID: 7952)
Creates files in the program directory
- Memu-Setup.exe (PID: 3100)
- 7za.exe (PID: 8180)
- 7za.exe (PID: 2368)
- 7za.exe (PID: 7548)
- MemuService.exe (PID: 316)
- MEmuConsole.exe (PID: 7776)
- MEmuSVC.exe (PID: 6148)
- MEmuSVC.exe (PID: 5500)
The sample compiled with english language support
- Memu-Setup.exe (PID: 3100)
- 7za.exe (PID: 2368)
- 7za.exe (PID: 8180)
- 7za.exe (PID: 7548)
- MEmuDrvInst.exe (PID: 6524)
Reads CPU info
- Memu-Setup.exe (PID: 3100)
- MEmuRepair.exe (PID: 2232)
- MEmuConsole.exe (PID: 7776)
- MEmu.exe (PID: 2028)
Reads the software policy settings
- MEmuDrvInst.exe (PID: 6524)
- slui.exe (PID: 7712)
Reads the machine GUID from the registry
- MEmuDrvInst.exe (PID: 6524)
- MEmuConsole.exe (PID: 7776)
Checks proxy server information
- MEmuConsole.exe (PID: 7776)
- slui.exe (PID: 7712)
Reads security settings of Internet Explorer
- explorer.exe (PID: 1700)
- explorer.exe (PID: 7752)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
297
Monitored processes
148
Malicious processes
6
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 304 | C:\WINDOWS\System32\sc query MEmuSVC | C:\Windows\SysWOW64\sc.exe | — | Memu-Setup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Service Control Manager Configuration Tool Exit code: 1060 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 316 | "C:\Program Files\Microvirt\MEmu\MemuService.exe" | C:\Program Files\Microvirt\MEmu\MemuService.exe | — | services.exe | |||||||||||
User: SYSTEM Integrity Level: SYSTEM Modules
| |||||||||||||||
| 424 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | 7za.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 868 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=26 --always-read-main-dll --field-trial-handle=6600,i,8992209075589570568,17489591374183908140,262144 --variations-seed-version --mojo-platform-channel-handle=5536 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 888 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | sc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1056 | C:\WINDOWS\System32\sc query MEmuNetLwf | C:\Windows\SysWOW64\sc.exe | — | Memu-Setup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Service Control Manager Configuration Tool Exit code: 1060 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1268 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=32 --always-read-main-dll --field-trial-handle=6752,i,8992209075589570568,17489591374183908140,262144 --variations-seed-version --mojo-platform-channel-handle=2872 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1324 | "C:\Users\admin\Downloads\Memu-Setup.exe" | C:\Users\admin\Downloads\Memu-Setup.exe | — | msedge.exe | |||||||||||
User: admin Company: Microvirt Software Technology Co. Ltd. Integrity Level: MEDIUM Description: MEmu Installer Exit code: 3221226540 Version: 9.2.3.0 Modules
| |||||||||||||||
| 1324 | "C:\WINDOWS\system32\sc" query MEmuNetLwf | C:\Windows\SysWOW64\sc.exe | — | Memu-Setup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Service Control Manager Configuration Tool Exit code: 1060 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1332 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | sc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
21 356
Read events
20 146
Write events
375
Delete events
835
Modification events
| (PID) Process: | (1984) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1984) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1984) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1984) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (1984) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 8100E9F67F962F00 | |||
| (PID) Process: | (1984) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328406 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {493440C4-26A9-4EBA-A8E1-659F66996843} | |||
| (PID) Process: | (1984) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328406 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {0929BE5B-9DC9-4156-B0DF-A65DA3198DE0} | |||
| (PID) Process: | (1984) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328406 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {BD5F240D-69B7-44AC-9C29-14091015BF17} | |||
| (PID) Process: | (1984) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | MicrosoftEdgeAutoLaunch_29EBC4579851B72EE312C449CF839B1A |
Value: "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --no-startup-window --win-session-start | |||
| (PID) Process: | (1984) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 282E24F77F962F00 | |||
Executable files
218
Suspicious files
625
Text files
189
Unknown types
127
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1984 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old~RF17691a.TMP | — | |
MD5:— | SHA256:— | |||
| 1984 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RF176949.TMP | — | |
MD5:— | SHA256:— | |||
| 1984 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1984 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF176949.TMP | — | |
MD5:— | SHA256:— | |||
| 1984 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF176949.TMP | — | |
MD5:— | SHA256:— | |||
| 1984 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1984 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF176958.TMP | — | |
MD5:— | SHA256:— | |||
| 1984 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1984 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF17691a.TMP | — | |
MD5:— | SHA256:— | |||
| 1984 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
31
TCP/UDP connections
174
DNS requests
210
Threats
15
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2228 | msedge.exe | GET | 200 | 150.171.27.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:K5CecS7NNicIz7sj8-J2icFqd8PYzz141qXIMPWhTug&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
3768 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 2.18.121.147:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
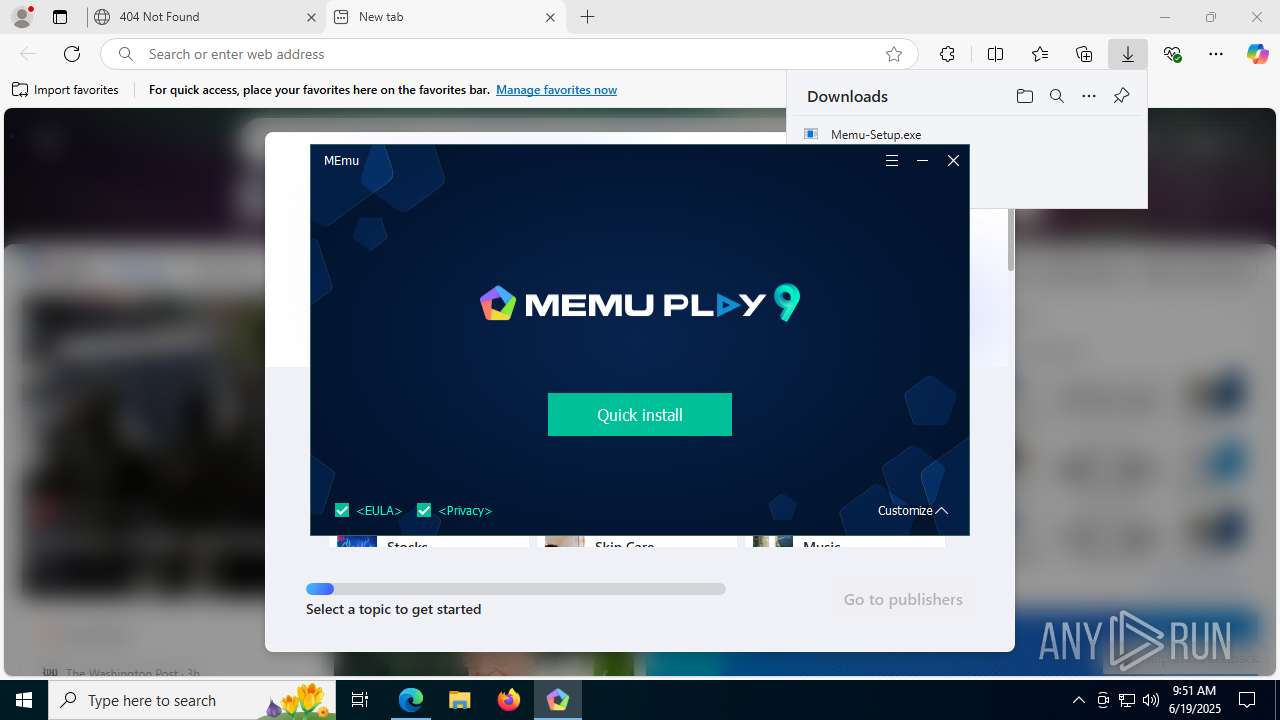
2228 | msedge.exe | GET | — | 18.245.31.52:80 | http://dl.memuplay.com/download/Memu-Setup.exe | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
8040 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
8040 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
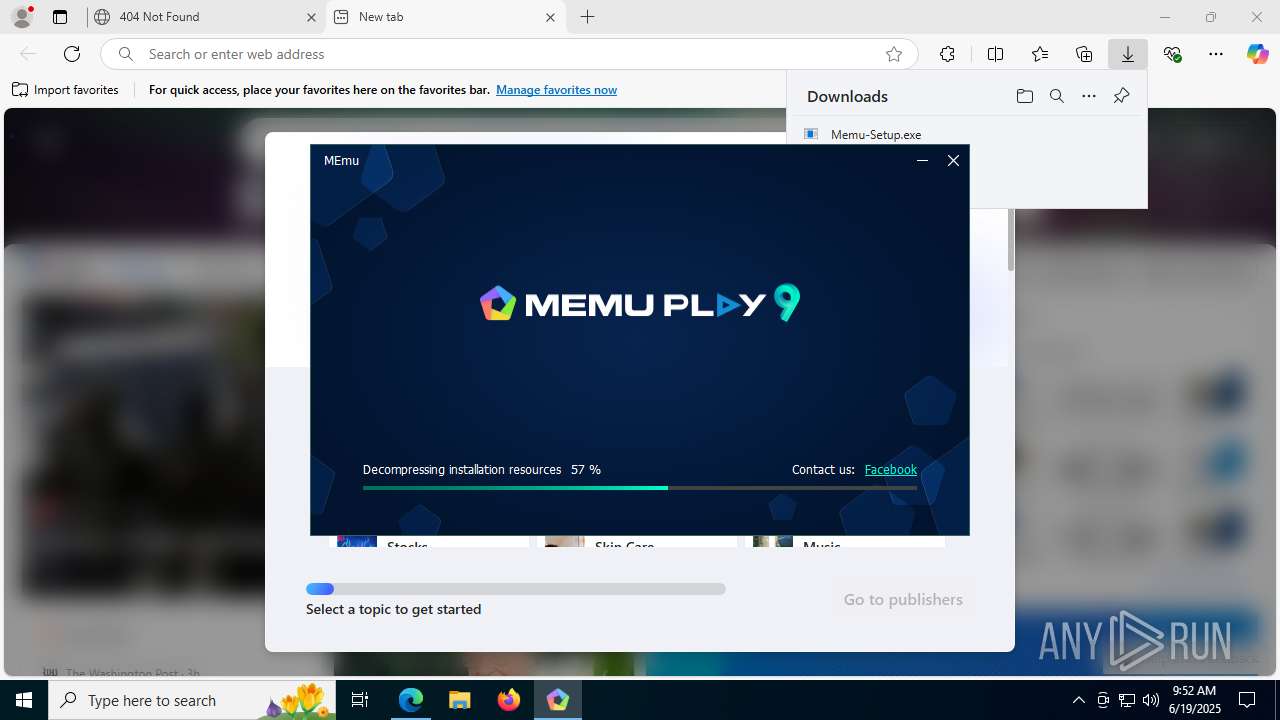
3100 | Memu-Setup.exe | GET | 200 | 154.85.69.60:80 | http://stat.microvirt.com/new_market/service.php?action=postmemusetupinfo&table=memusetupinfo&packageName=Memu-Setup&insMode=ins&version=9.2.3.0&channel=cd5e1e00&silence=0&currPage=StepStart&lifeCycle=0&exitCode=0&mac=E4:B0:1C:8A:DE:7F&error=&initTime=0 | unknown | — | — | unknown |
8096 | Memu-Setup.exe | GET | 200 | 154.85.69.60:80 | http://stat.microvirt.com/new_market/service.php?action=postmemusetupinfo&table=memusetupinfo&packageName=Memu-Setup&insMode=ins&version=9.2.3.0&channel=cd5e1e00&silence=0&currPage=StepStart&lifeCycle=0&exitCode=0&mac=E4:B0:1C:8A:DE:7F&error=&initTime=0 | unknown | — | — | unknown |
8096 | Memu-Setup.exe | GET | 200 | 154.85.69.60:80 | http://stat.microvirt.com/new_market/service.php?action=postmemusetupinfo&table=memusetupinfo&packageName=Memu-Setup&insMode=ins&version=9.2.3.0&channel=cd5e1e00&silence=0&currPage=StepWelcomePage&lifeCycle=0&exitCode=-4&mac=E4:B0:1C:8A:DE:7F&error=&initTime=0 | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
5944 | MoUsoCoreWorker.exe | 51.104.136.2:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1268 | svchost.exe | 51.104.136.2:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4808 | RUXIMICS.exe | 51.104.136.2:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2228 | msedge.exe | 150.171.27.11:80 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
2228 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
2228 | msedge.exe | 150.171.27.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
2228 | msedge.exe | 2.23.227.211:443 | copilot.microsoft.com | Ooredoo Q.S.C. | QA | whitelisted |
2228 | msedge.exe | 18.245.31.52:80 | dl.memuplay.com | — | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
dl.memuplay.com |
| whitelisted |
copilot.microsoft.com |
| whitelisted |
update.googleapis.com |
| whitelisted |
www.bing.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
edgeassetservice.azureedge.net |
| whitelisted |
login.live.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2228 | msedge.exe | Potential Corporate Privacy Violation | ET INFO PE EXE or DLL Windows file download HTTP |
3100 | Memu-Setup.exe | Misc activity | INFO [ANY.RUN] USER_AGENTS Suspicious User-Agent (Mozilla/5.0) |
8096 | Memu-Setup.exe | Misc activity | INFO [ANY.RUN] USER_AGENTS Suspicious User-Agent (Mozilla/5.0) |
8096 | Memu-Setup.exe | Misc activity | INFO [ANY.RUN] USER_AGENTS Suspicious User-Agent (Mozilla/5.0) |
3100 | Memu-Setup.exe | Misc activity | INFO [ANY.RUN] USER_AGENTS Suspicious User-Agent (Mozilla/5.0) |
3100 | Memu-Setup.exe | Misc activity | INFO [ANY.RUN] USER_AGENTS Suspicious User-Agent (Mozilla/5.0) |
3100 | Memu-Setup.exe | Misc activity | INFO [ANY.RUN] USER_AGENTS Suspicious User-Agent (Mozilla/5.0) |
3100 | Memu-Setup.exe | Misc activity | INFO [ANY.RUN] USER_AGENTS Suspicious User-Agent (Mozilla/5.0) |
3100 | Memu-Setup.exe | Misc activity | INFO [ANY.RUN] USER_AGENTS Suspicious User-Agent (Mozilla/5.0) |
2228 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
Process | Message |
|---|---|
Memu-Setup.exe | Qt: Untested Windows version 10.0 detected!
|
Memu-Setup.exe | QWindowsWindow::setGeometryDp: Unable to set geometry 21x14+320+100 on QWidgetWindow/'QCheckBoxClassWindow'. Resulting geometry: 120x14+320+100 (frame: 8, 31, 8, 8, custom margin: 0, 0, 0, 0, minimum size: 0x0, maximum size: 16777215x16777215).
|
Memu-Setup.exe | QWindowsWindow::setGeometryDp: Unable to set geometry 55x14+320+100 on QWidgetWindow/'QLabelClassWindow'. Resulting geometry: 120x14+320+100 (frame: 8, 31, 8, 8, custom margin: 0, 0, 0, 0, minimum size: 0x0, maximum size: 16777215x16777215).
|
Memu-Setup.exe | Qt: Untested Windows version 10.0 detected!
|
Memu-Setup.exe | QWindowsWindow::setGeometryDp: Unable to set geometry 21x14+320+100 on QWidgetWindow/'QCheckBoxClassWindow'. Resulting geometry: 120x14+320+100 (frame: 8, 31, 8, 8, custom margin: 0, 0, 0, 0, minimum size: 0x0, maximum size: 16777215x16777215).
|
Memu-Setup.exe | QWindowsWindow::setGeometryDp: Unable to set geometry 55x14+320+100 on QWidgetWindow/'QLabelClassWindow'. Resulting geometry: 120x14+320+100 (frame: 8, 31, 8, 8, custom margin: 0, 0, 0, 0, minimum size: 0x0, maximum size: 16777215x16777215).
|