| File name: | OpenMe.bat |
| Full analysis: | https://app.any.run/tasks/183040bc-f348-47f9-99a2-f1b8106bbc52 |
| Verdict: | Malicious activity |
| Analysis date: | November 29, 2020, 21:33:51 |
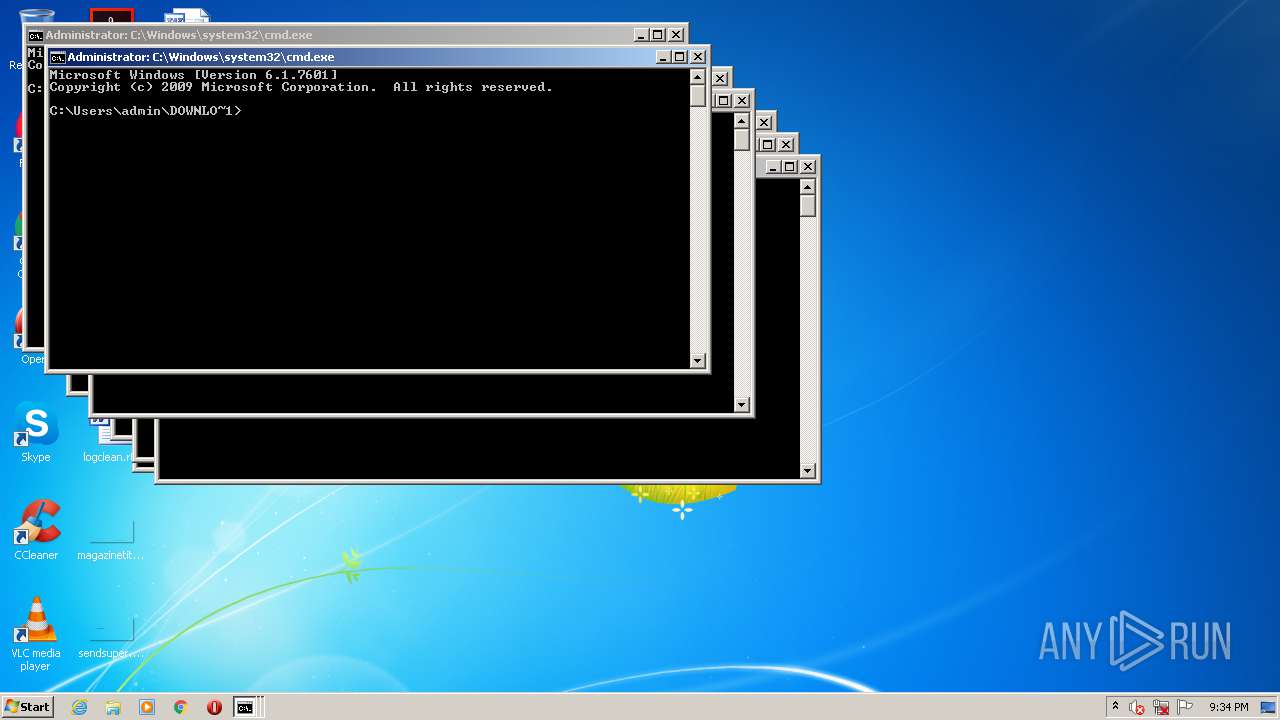
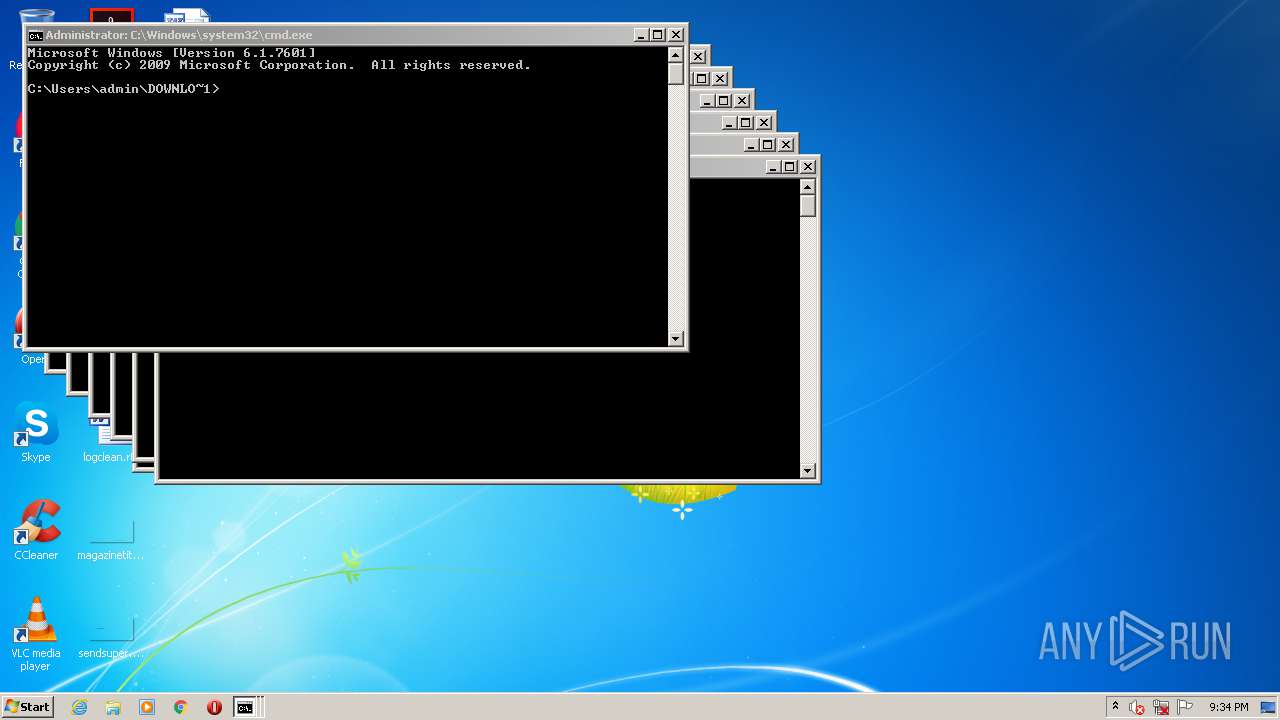
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/x-msdos-batch |
| File info: | DOS batch file, ASCII text, with very long lines |
| MD5: | 90912A048F7442FDF29C4D8F13076A72 |
| SHA1: | 6D99CD120AC38D6CF4042A84E09E35151F3B36CA |
| SHA256: | CE2A1B1E42E096F9C23A9D3B72DE39E1607C909D1281BA68E912D29AF4521ABD |
| SSDEEP: | 24:JotrlyRYdH7grM8OQzMzYizoVUD+V2MZK7iu+l+V2MZKHLFk9LQ9gu+lyJmkdu/o:n+mrOrzFzo9p0Wep0HP9gCI1mprMq |
MALICIOUS
Changes the autorun value in the registry
- reg.exe (PID: 1016)
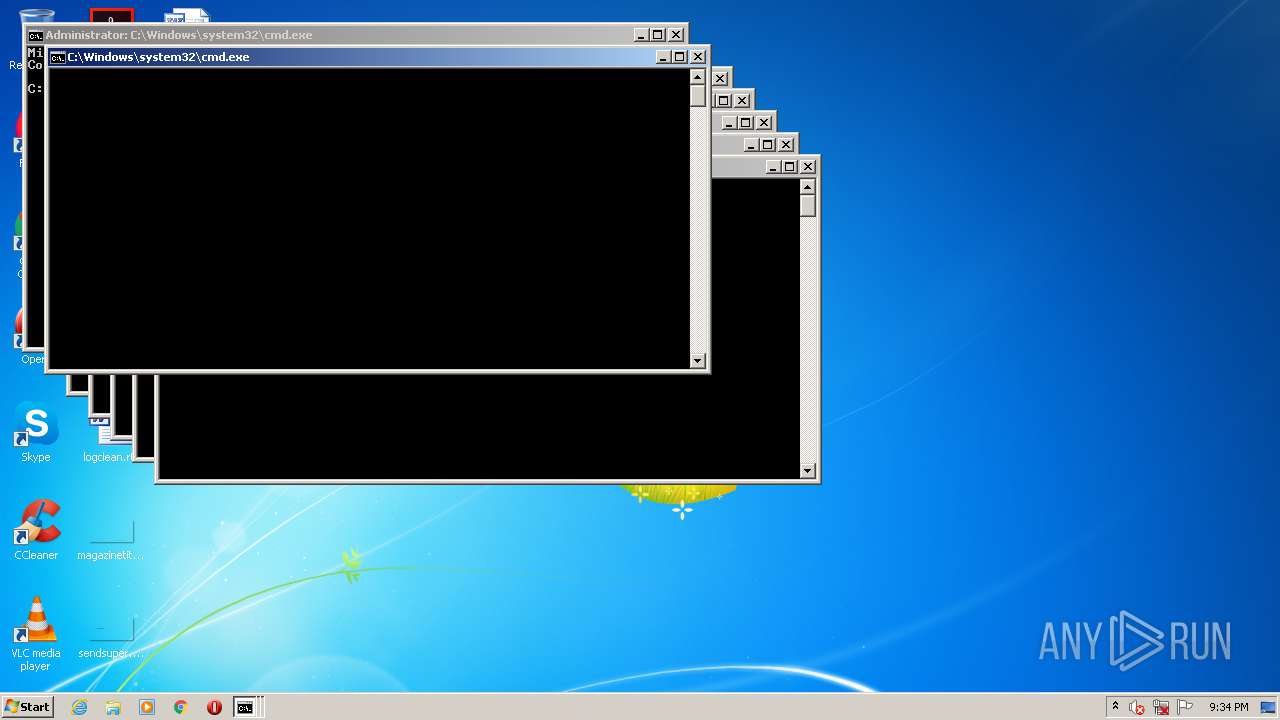
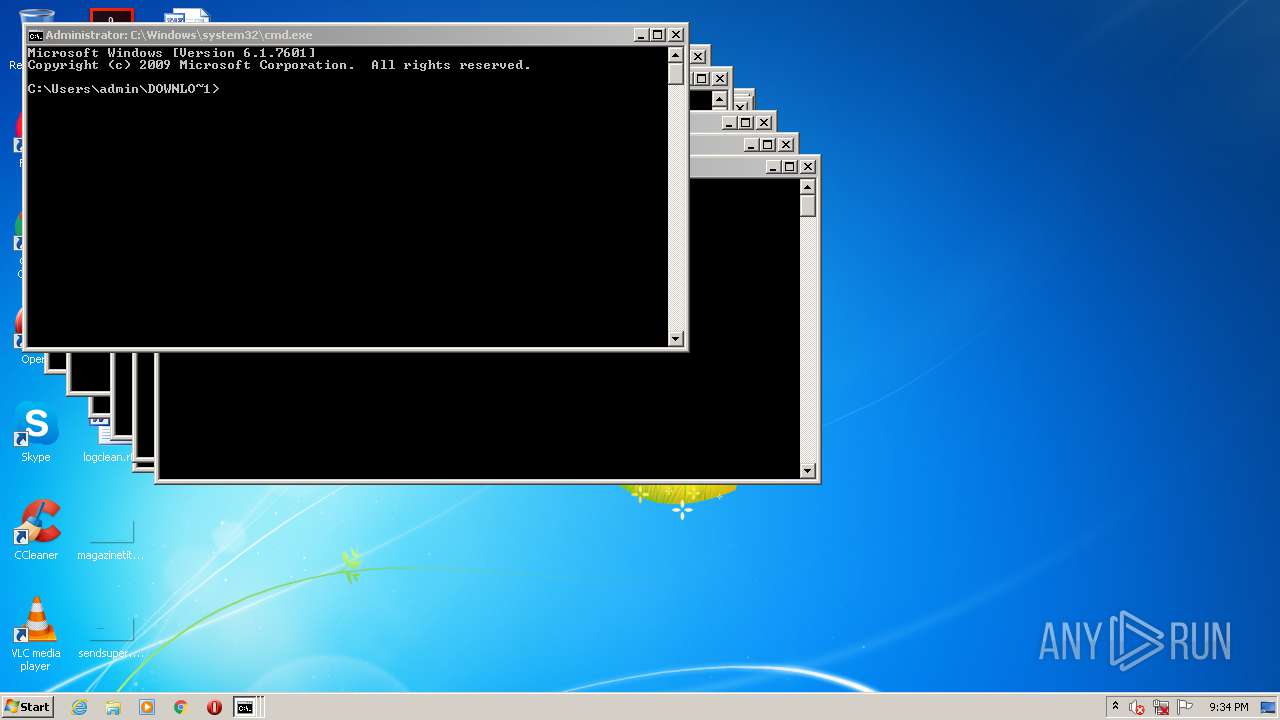
Runs app for hidden code execution
- cmd.exe (PID: 2660)
SUSPICIOUS
Uses REG.EXE to modify Windows registry
- cmd.exe (PID: 2660)
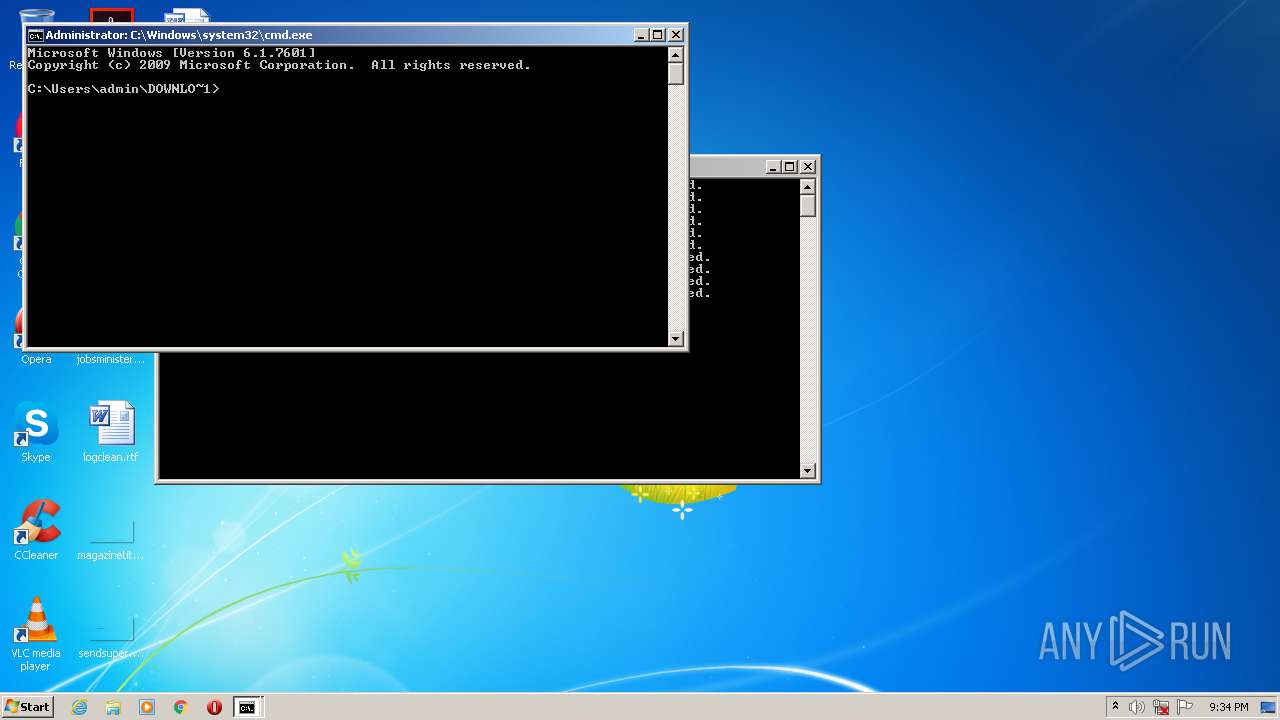
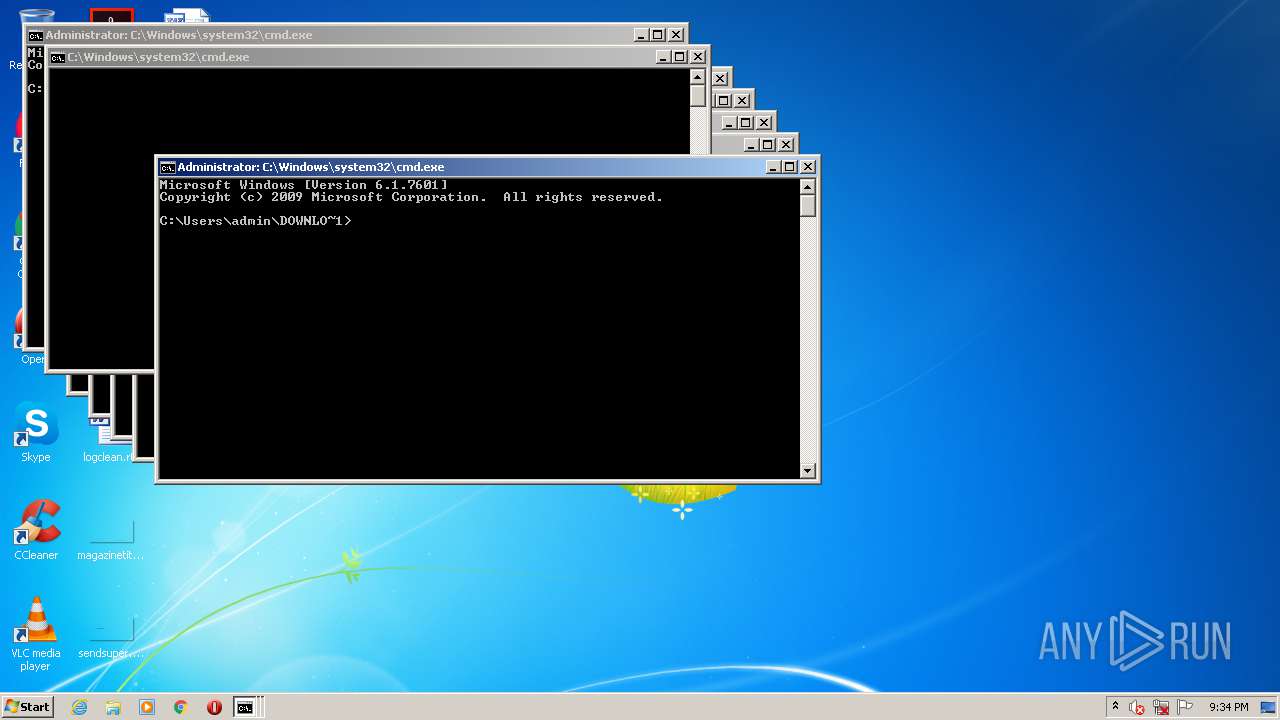
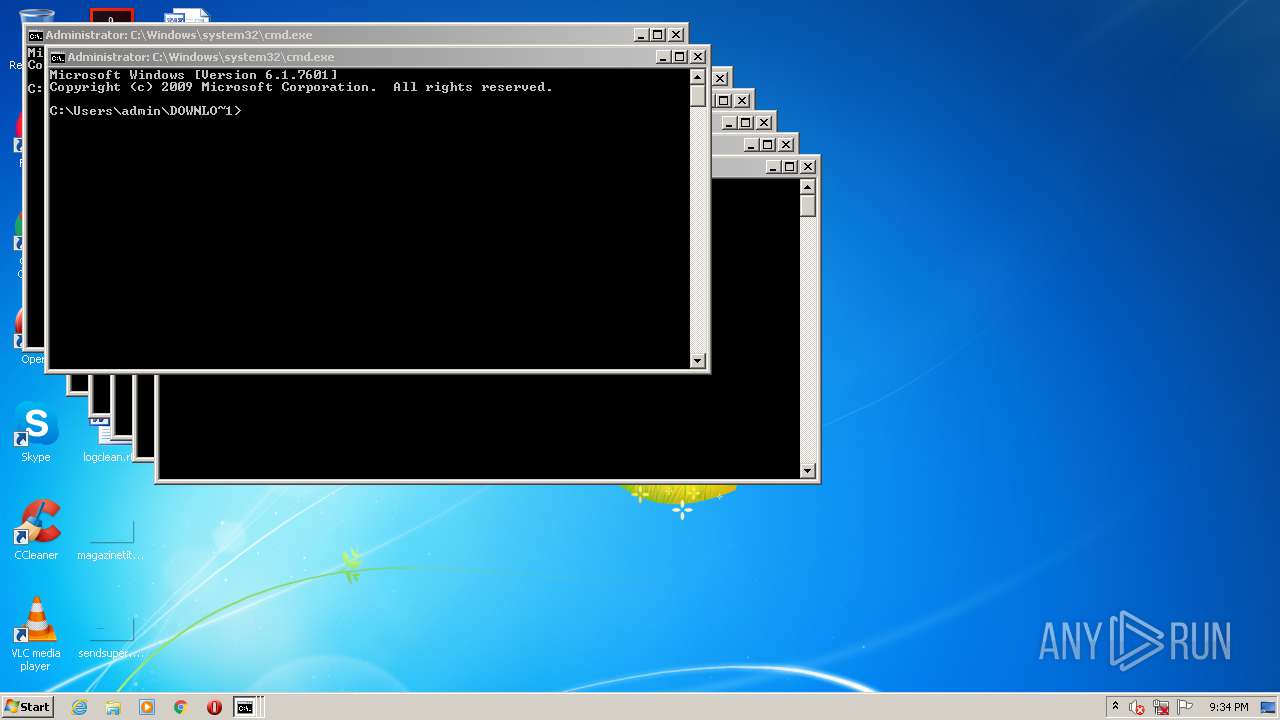
Starts CMD.EXE for commands execution
- WScript.exe (PID: 2788)
- cmd.exe (PID: 2660)
Executes scripts
- cmd.exe (PID: 2804)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 2660)
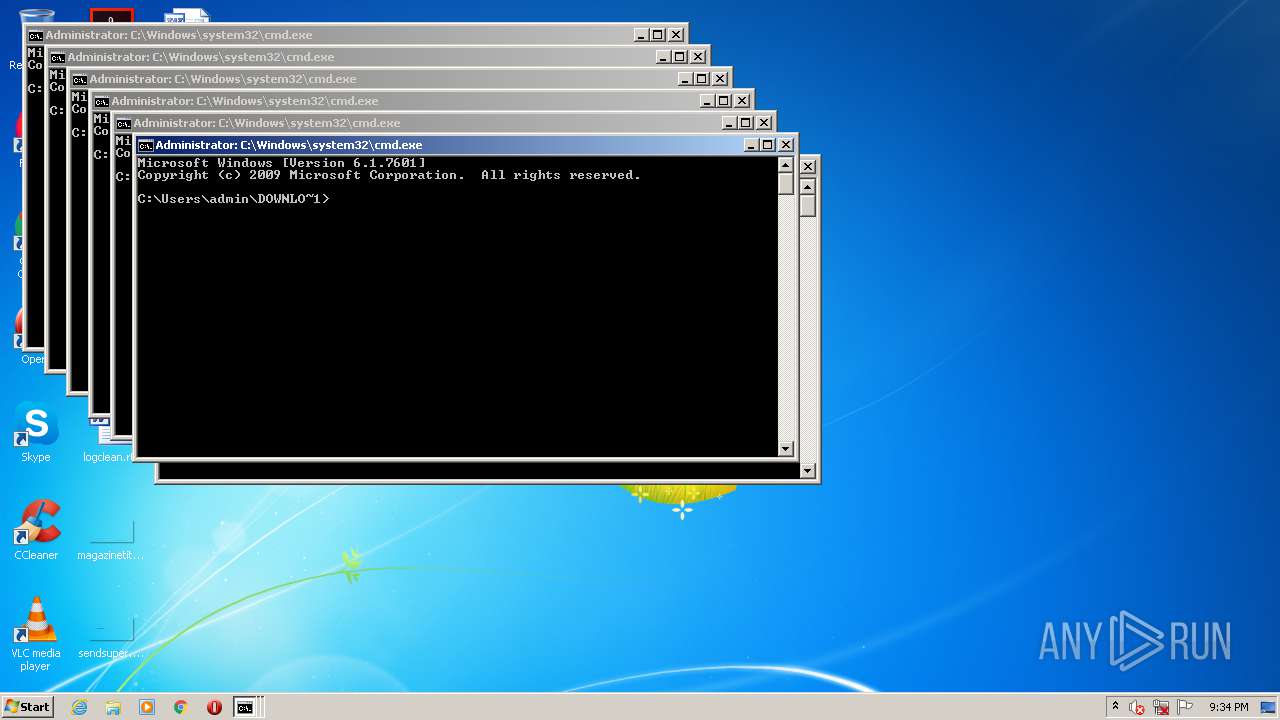
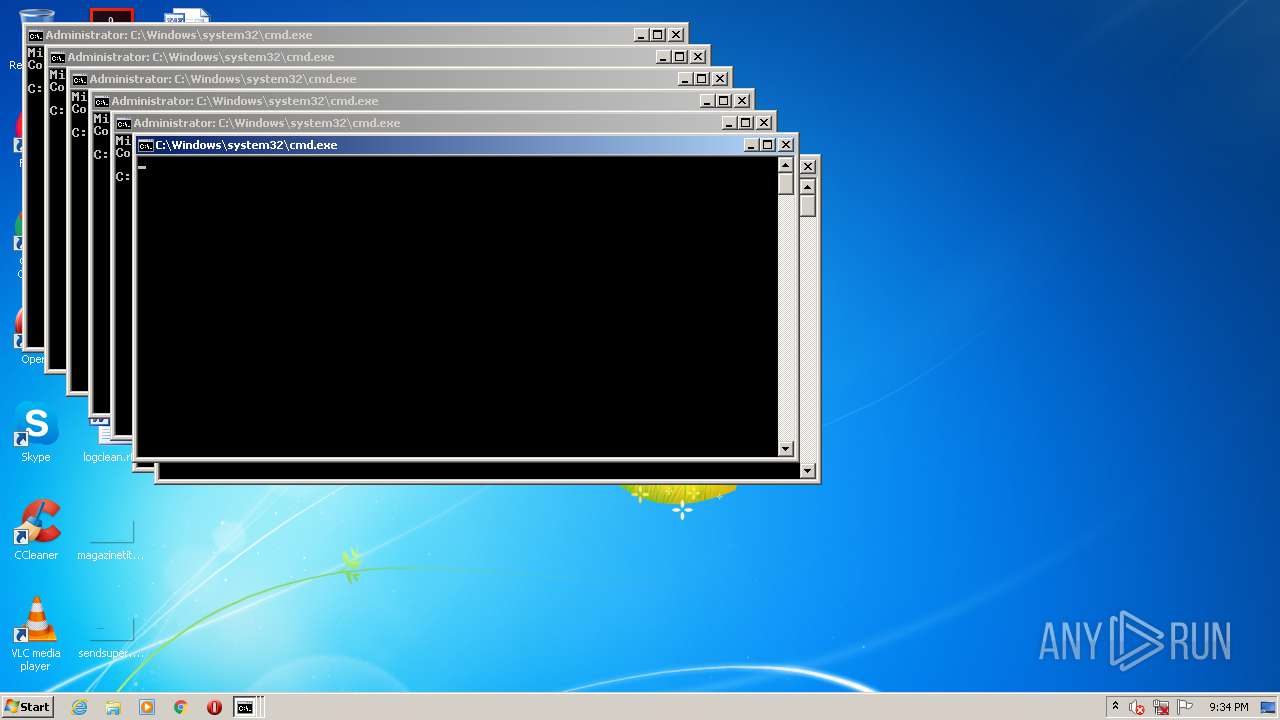
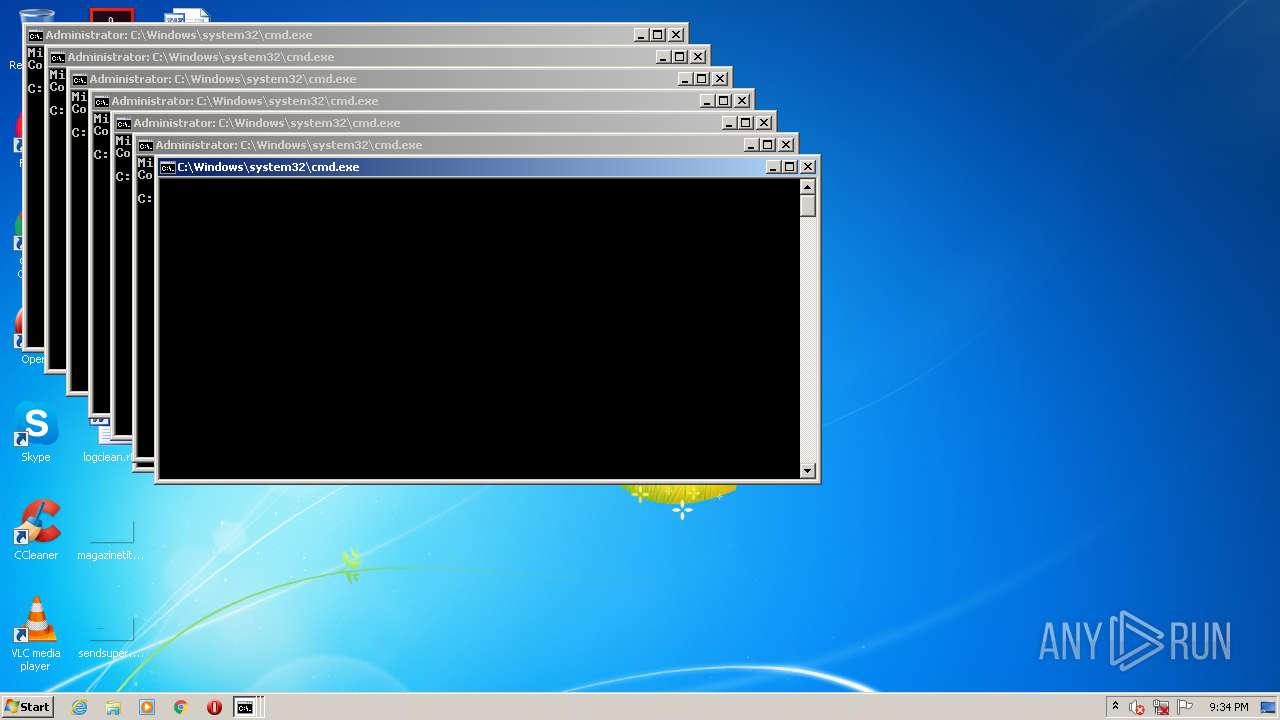
Application launched itself
- cmd.exe (PID: 2660)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
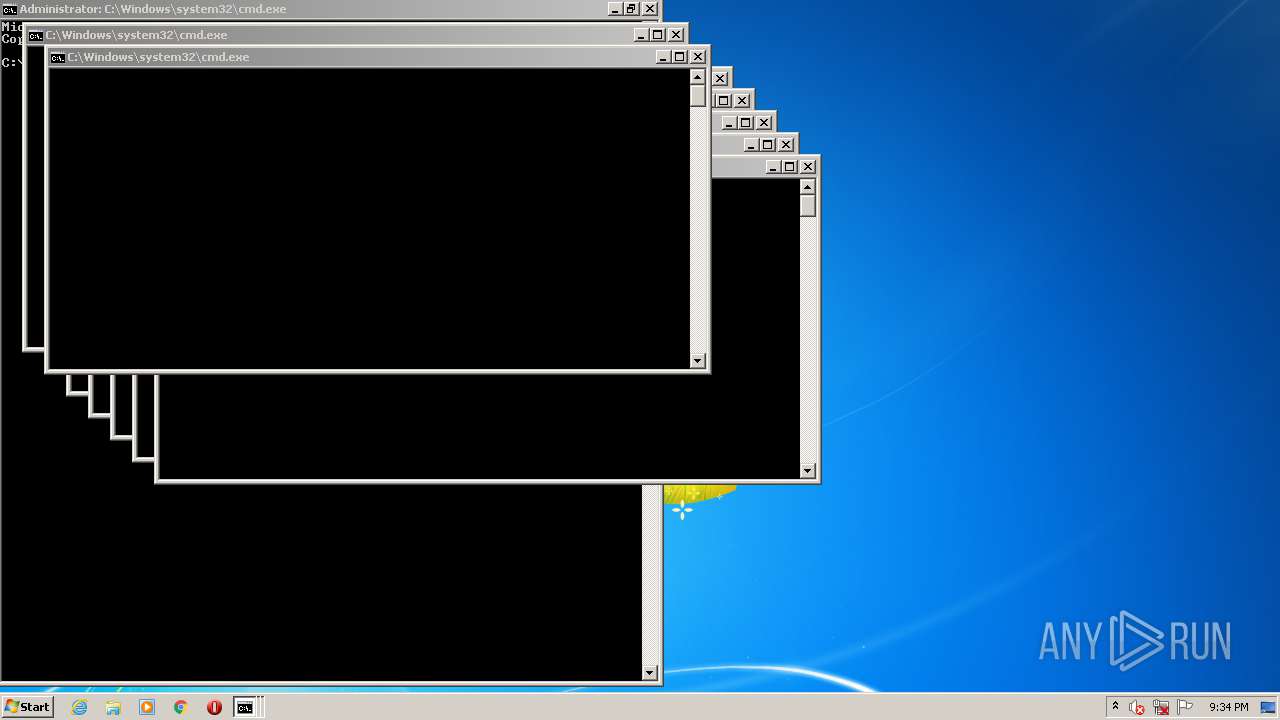
Total processes
338
Monitored processes
151
Malicious processes
3
Suspicious processes
0
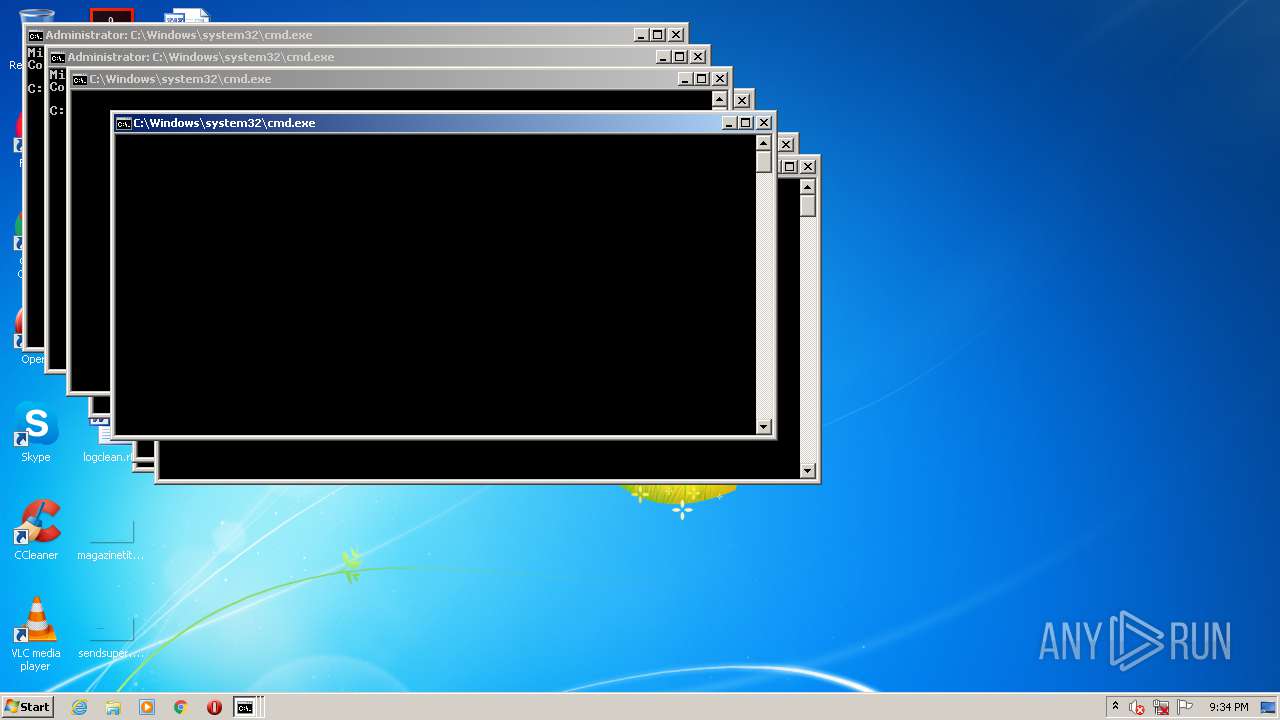
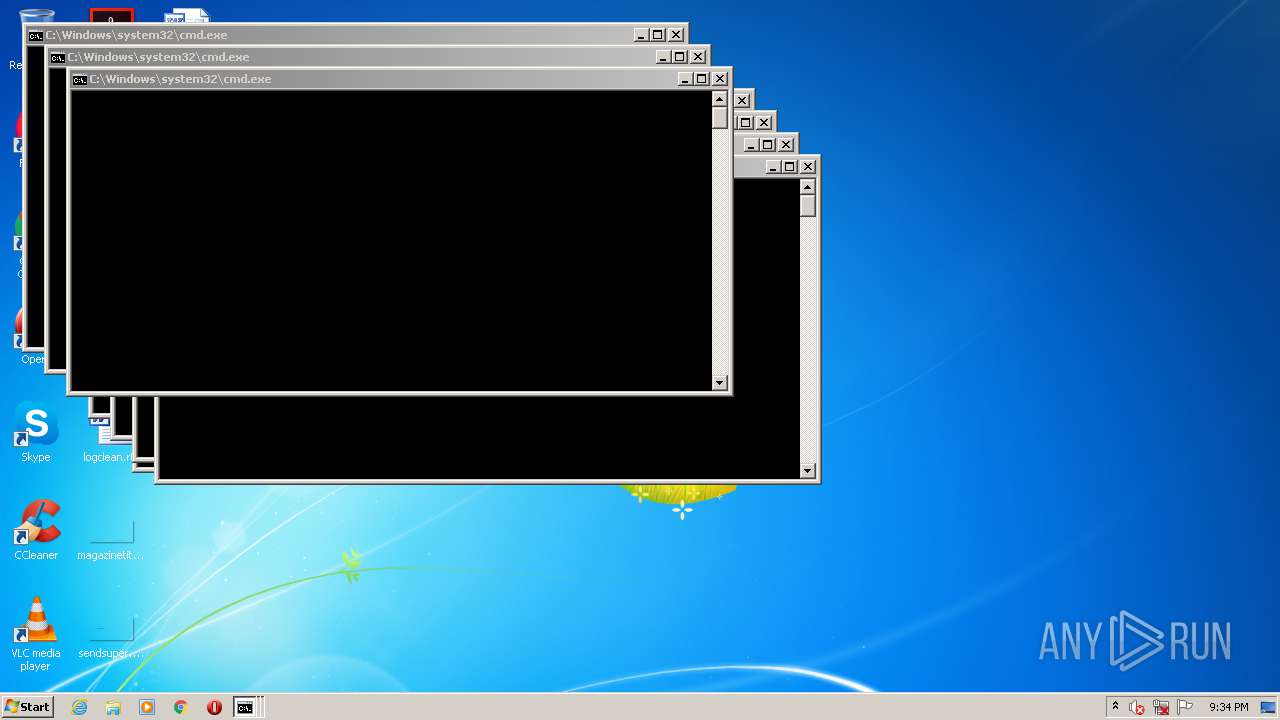
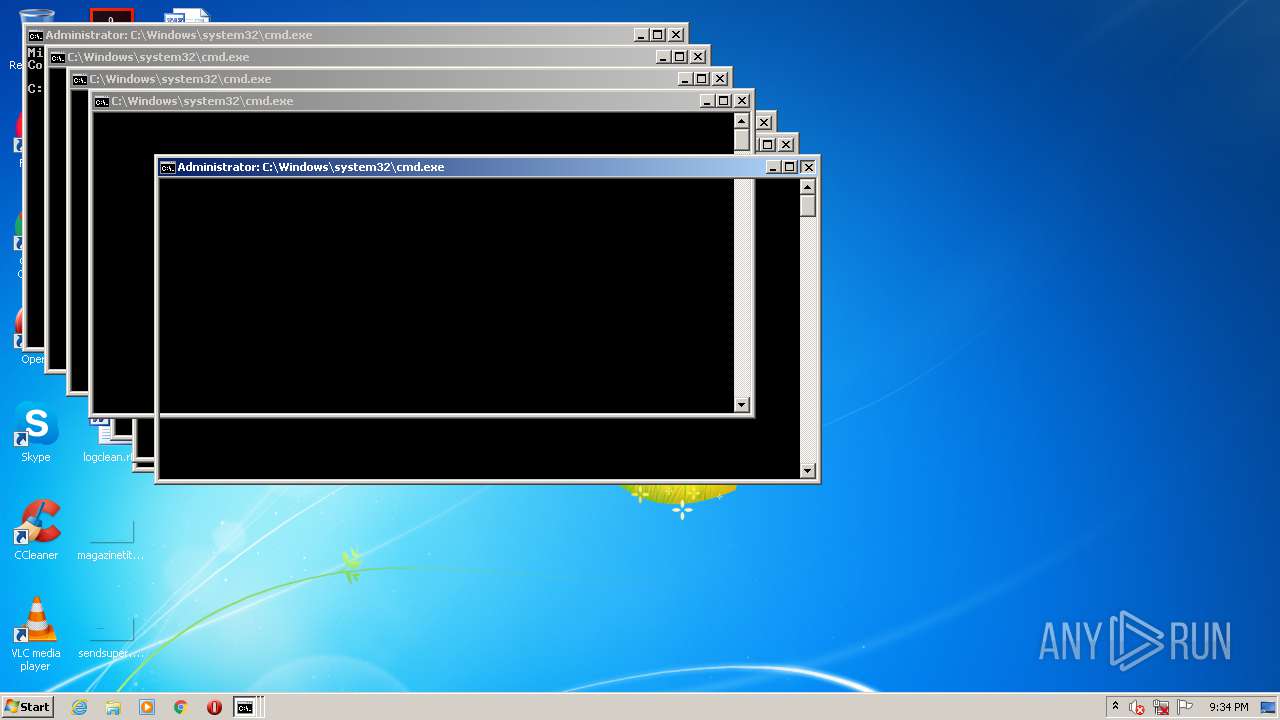
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
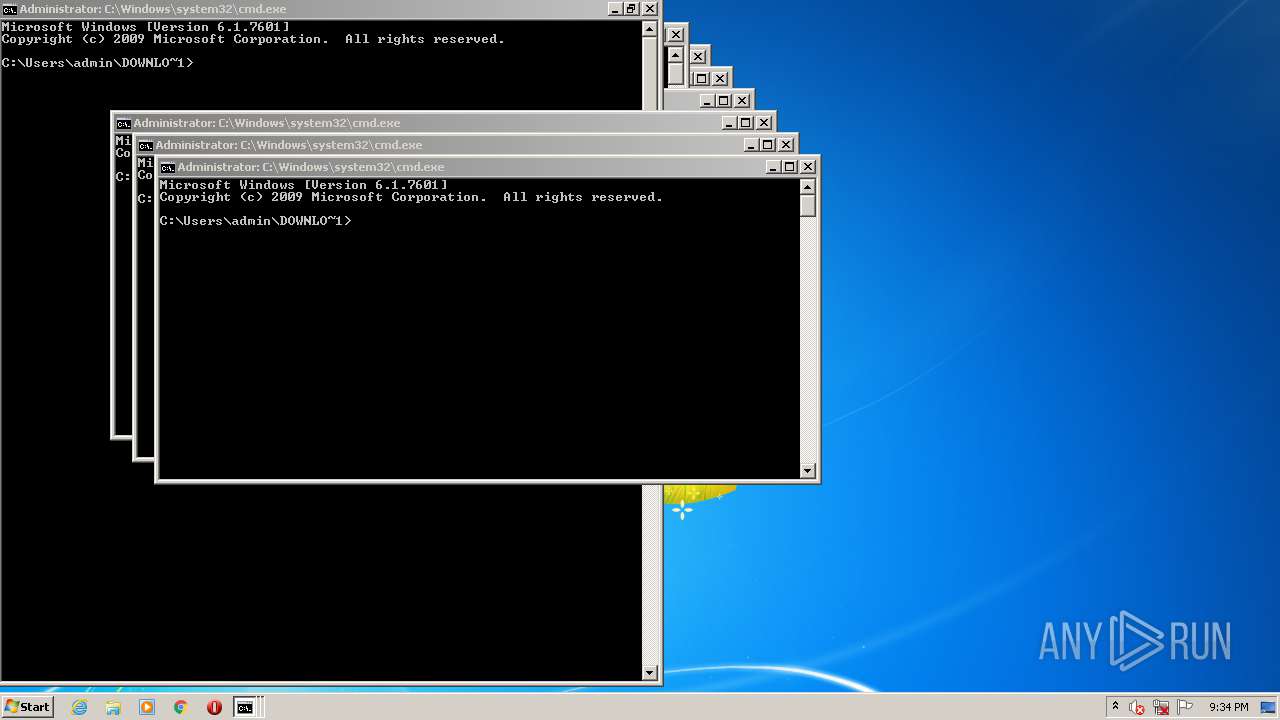
| 144 | cmd.exe | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 324 | cmd.exe | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 616 | cmd.exe | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 680 | cmd.exe | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 684 | cmd.exe | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 692 | cmd.exe | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 756 | cmd.exe | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 784 | cmd.exe | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 812 | cmd.exe | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 832 | cmd.exe | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
1 192
Read events
1 182
Write events
10
Delete events
0
Modification events
| (PID) Process: | (2788) WScript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2788) WScript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2804) cmd.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2804) cmd.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (1016) reg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | R |
Value: | |||
| (PID) Process: | (1512) reg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\batfile\shell\edit\command |
| Operation: | write | Name: | (Default) |
Value: C:\Users\admin\DOWNLO~1\OpenMe.bat | |||
Executable files
0
Suspicious files
0
Text files
623
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2660 | cmd.exe | C:\Users\admin\Downloads\4ever.txt | — | |
MD5:— | SHA256:— | |||
| 2804 | cmd.exe | C:\Users\admin\AppData\Local\Temp\getadmin.vbs | text | |
MD5:— | SHA256:— | |||
| 2660 | cmd.exe | C:\Users\admin\Downloads\bcd.bat | text | |
MD5:— | SHA256:— | |||
| 2660 | cmd.exe | C:\Users\admin\DOWNLO~1\738115911188829032739410750125423029125799137649903.txt | text | |
MD5:— | SHA256:— | |||
| 2660 | cmd.exe | C:\Users\admin\AppData\Local\Temp\BOOT.txt | text | |
MD5:— | SHA256:— | |||
| 2660 | cmd.exe | C:\Users\admin\DOWNLO~1\1895411946172012012224790778450721854220100269182177.txt | text | |
MD5:— | SHA256:— | |||
| 2660 | cmd.exe | C:\Users\admin\DOWNLO~1\12682191641264728011043467121805623342157201213325569.txt | text | |
MD5:— | SHA256:— | |||
| 2660 | cmd.exe | C:\Users\admin\DOWNLO~1\225354518250226909406814679243432182349891275623052.txt | text | |
MD5:— | SHA256:— | |||
| 2660 | cmd.exe | C:\Users\admin\DOWNLO~1\32506189962870415679225699661697724385267951175729463.txt | text | |
MD5:— | SHA256:— | |||
| 2660 | cmd.exe | C:\Users\admin\DOWNLO~1\1259421082573815569302803035060635791231092243310649.txt | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report