| File name: | SecuriteInfo.com.Android.Spy.82.origin.26281.298 |
| Full analysis: | https://app.any.run/tasks/c7028169-cc7f-4c66-ad30-d691041d73db |
| Verdict: | Malicious activity |
| Analysis date: | December 09, 2023, 11:22:21 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 64 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | E83CF18F313D701FEB67A81F2A6B27AD |
| SHA1: | 33CC82552E7627F07A59E6F0340A6F2FA0D76FE4 |
| SHA256: | CE24A560C3A81494545478DBADA10A173180FD411DFEC08DB344E4B353E2C7B8 |
| SSDEEP: | 98304:cGBgHOqRySd50CRQhqeJ3vt+UndfMzaFNV5ukzbOuYjE4LgGDfCPQYPMBM1rpxV4:hQKl8xsn5L4FbZn |
MALICIOUS
Drops the executable file immediately after the start
- SecuriteInfo.com.Android.Spy.82.origin.26281.298.exe (PID: 1012)
- SecuriteInfo.com.Android.Spy.82.origin.26281.298.exe (PID: 2800)
- SecuriteInfo.com.Android.Spy.82.origin.26281.298.tmp (PID: 2488)
SUSPICIOUS
Process drops legitimate windows executable
- SecuriteInfo.com.Android.Spy.82.origin.26281.298.tmp (PID: 2488)
Reads the Windows owner or organization settings
- SecuriteInfo.com.Android.Spy.82.origin.26281.298.tmp (PID: 2488)
The process drops C-runtime libraries
- SecuriteInfo.com.Android.Spy.82.origin.26281.298.tmp (PID: 2488)
Reads the Internet Settings
- Root.exe (PID: 2124)
- RomasterConnection.exe (PID: 2264)
Reads security settings of Internet Explorer
- Root.exe (PID: 2124)
Checks Windows Trust Settings
- Root.exe (PID: 2124)
Reads settings of System Certificates
- Root.exe (PID: 2124)
INFO
Checks supported languages
- SecuriteInfo.com.Android.Spy.82.origin.26281.298.exe (PID: 1012)
- SecuriteInfo.com.Android.Spy.82.origin.26281.298.tmp (PID: 1828)
- SecuriteInfo.com.Android.Spy.82.origin.26281.298.exe (PID: 2800)
- SecuriteInfo.com.Android.Spy.82.origin.26281.298.tmp (PID: 2488)
- Root.exe (PID: 2124)
- romaster_daemon.exe (PID: 2964)
- RomasterConnection.exe (PID: 2264)
Reads the computer name
- SecuriteInfo.com.Android.Spy.82.origin.26281.298.tmp (PID: 1828)
- SecuriteInfo.com.Android.Spy.82.origin.26281.298.tmp (PID: 2488)
- Root.exe (PID: 2124)
- RomasterConnection.exe (PID: 2264)
- romaster_daemon.exe (PID: 2964)
Create files in a temporary directory
- SecuriteInfo.com.Android.Spy.82.origin.26281.298.exe (PID: 1012)
- SecuriteInfo.com.Android.Spy.82.origin.26281.298.exe (PID: 2800)
- SecuriteInfo.com.Android.Spy.82.origin.26281.298.tmp (PID: 2488)
- Root.exe (PID: 2124)
Creates files in the program directory
- SecuriteInfo.com.Android.Spy.82.origin.26281.298.tmp (PID: 2488)
Reads the machine GUID from the registry
- Root.exe (PID: 2124)
- romaster_daemon.exe (PID: 2964)
Checks proxy server information
- Root.exe (PID: 2124)
Creates files or folders in the user directory
- RomasterConnection.exe (PID: 2264)
- Root.exe (PID: 2124)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Inno Setup installer (74.3) |
|---|---|---|
| .exe | | | Win32 Executable Delphi generic (9.6) |
| .scr | | | Windows screen saver (8.8) |
| .exe | | | Win32 Executable (generic) (3) |
| .exe | | | Win16/32 Executable Delphi generic (1.4) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1992:06:20 00:22:17+02:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, Bytes reversed lo, 32-bit, Bytes reversed hi |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 40448 |
| InitializedDataSize: | 204800 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xa5f8 |
| OSVersion: | 1 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.7.3.4388 |
| ProductVersionNumber: | 1.7.3.4388 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
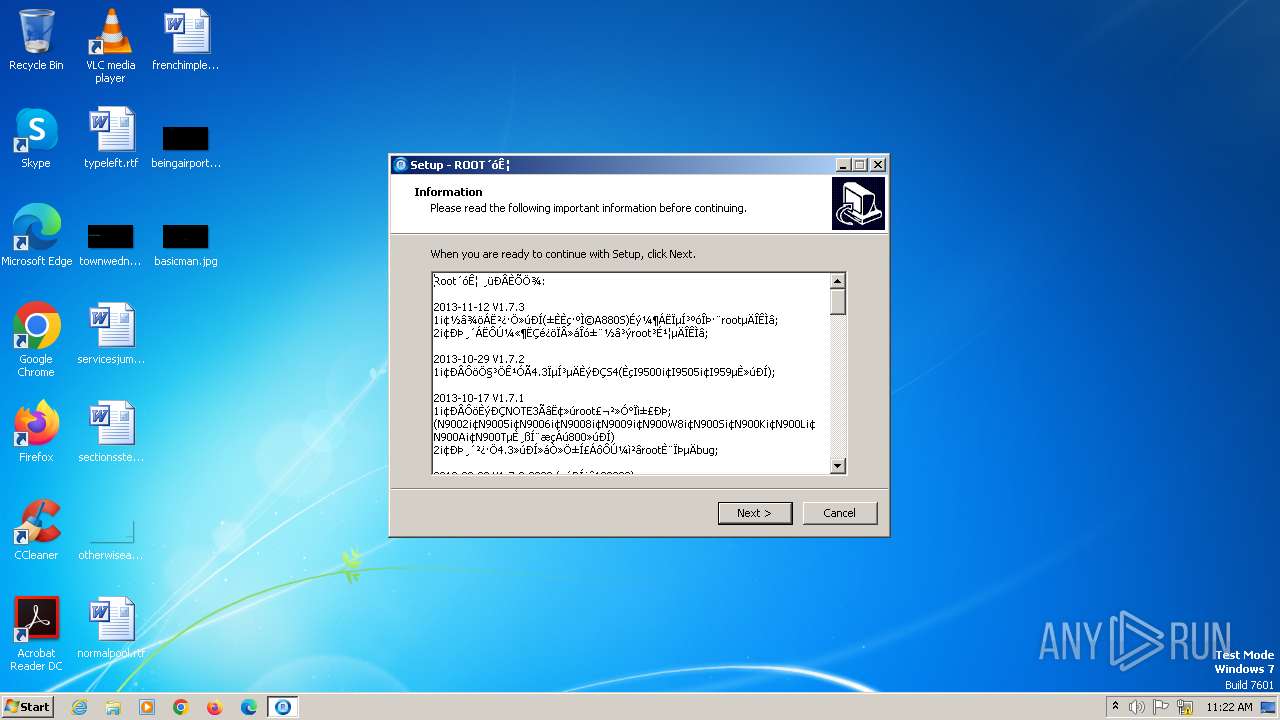
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | 深圳市信一网络有限公司 |
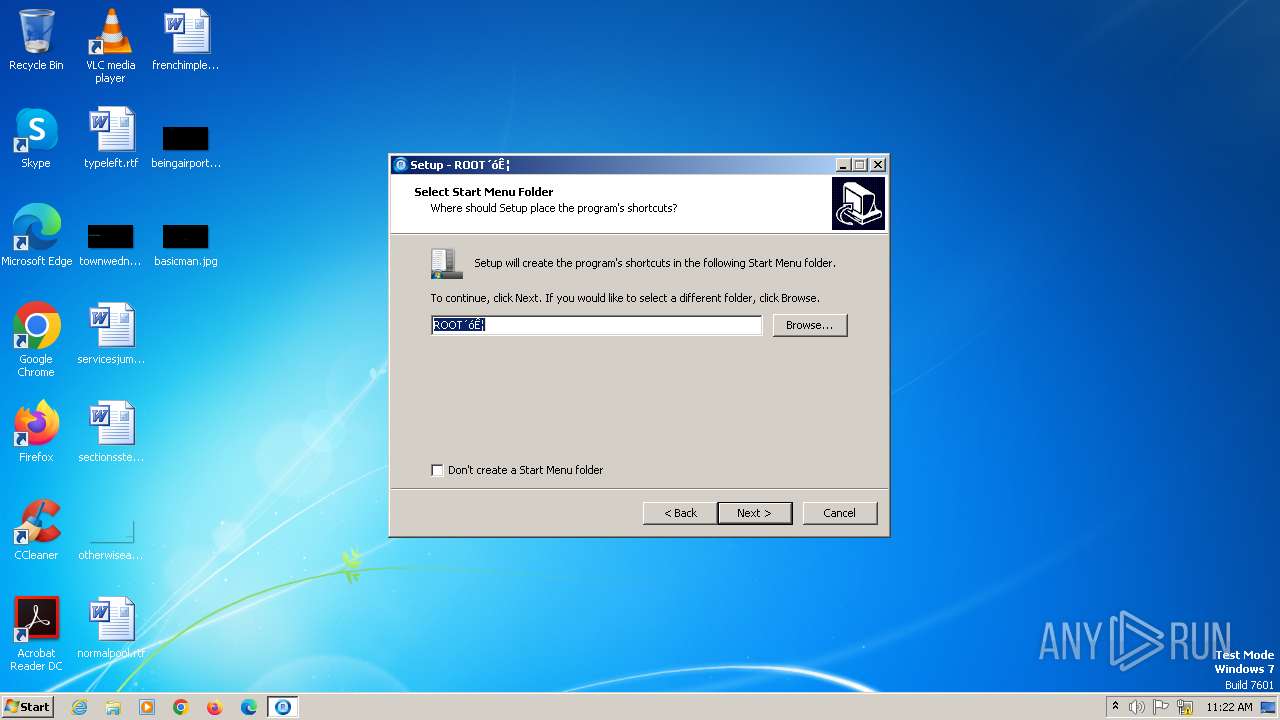
| FileDescription: | ROOT大师 Setup |
| FileVersion: | 1.7.3.4388 |
| LegalCopyright: | Copyright © 2013 Xinyi All Rights Reserved |
| ProductName: | ROOT大师 |
| ProductVersion: | 1.7.3.4388 |
Total processes
43
Monitored processes
7
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1012 | "C:\Users\admin\AppData\Local\Temp\SecuriteInfo.com.Android.Spy.82.origin.26281.298.exe" | C:\Users\admin\AppData\Local\Temp\SecuriteInfo.com.Android.Spy.82.origin.26281.298.exe | — | explorer.exe | |||||||||||
User: admin Company: 深圳市信一网络有限公司 Integrity Level: MEDIUM Description: ROOT大师 Setup Exit code: 0 Version: 1.7.3.4388 Modules
| |||||||||||||||
| 1828 | "C:\Users\admin\AppData\Local\Temp\is-DLVQ0.tmp\SecuriteInfo.com.Android.Spy.82.origin.26281.298.tmp" /SL5="$1B03D8,4929135,246272,C:\Users\admin\AppData\Local\Temp\SecuriteInfo.com.Android.Spy.82.origin.26281.298.exe" | C:\Users\admin\AppData\Local\Temp\is-DLVQ0.tmp\SecuriteInfo.com.Android.Spy.82.origin.26281.298.tmp | — | SecuriteInfo.com.Android.Spy.82.origin.26281.298.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Setup/Uninstall Exit code: 0 Version: 51.52.0.0 Modules
| |||||||||||||||
| 2124 | "C:\Program Files (x86)\VROOT\Root.exe" | C:\Program Files (x86)\VROOT\Root.exe | SecuriteInfo.com.Android.Spy.82.origin.26281.298.tmp | ||||||||||||
User: admin Company: 信一网络 Integrity Level: MEDIUM Description: Root大师 Exit code: 0 Version: 1, 7, 3, 0 Modules
| |||||||||||||||
| 2264 | "C:\Program Files (x86)\VROOT\RomasterConnection.exe" /hwnd=1115058 | C:\Program Files (x86)\VROOT\RomasterConnection.exe | Root.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2488 | "C:\Users\admin\AppData\Local\Temp\is-67SG7.tmp\SecuriteInfo.com.Android.Spy.82.origin.26281.298.tmp" /SL5="$1C0208,4929135,246272,C:\Users\admin\AppData\Local\Temp\SecuriteInfo.com.Android.Spy.82.origin.26281.298.exe" /SPAWNWND=$180136 /NOTIFYWND=$1B03D8 | C:\Users\admin\AppData\Local\Temp\is-67SG7.tmp\SecuriteInfo.com.Android.Spy.82.origin.26281.298.tmp | — | SecuriteInfo.com.Android.Spy.82.origin.26281.298.exe | |||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.52.0.0 Modules
| |||||||||||||||
| 2800 | "C:\Users\admin\AppData\Local\Temp\SecuriteInfo.com.Android.Spy.82.origin.26281.298.exe" /SPAWNWND=$180136 /NOTIFYWND=$1B03D8 | C:\Users\admin\AppData\Local\Temp\SecuriteInfo.com.Android.Spy.82.origin.26281.298.exe | SecuriteInfo.com.Android.Spy.82.origin.26281.298.tmp | ||||||||||||
User: admin Company: 深圳市信一网络有限公司 Integrity Level: HIGH Description: ROOT大师 Setup Exit code: 0 Version: 1.7.3.4388 Modules
| |||||||||||||||
| 2964 | "C:\Program Files (x86)\VROOT\romaster_daemon.exe" fork-server server | C:\Program Files (x86)\VROOT\romaster_daemon.exe | — | RomasterConnection.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Android Debug Bridge Exit code: 0 Version: 1.0.26.21 Modules
| |||||||||||||||
Total events
2 760
Read events
2 729
Write events
25
Delete events
6
Modification events
| (PID) Process: | (2124) Root.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2124) Root.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2124) Root.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2124) Root.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000C1000000010000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2488) SecuriteInfo.com.Android.Spy.82.origin.26281.298.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | delete value | Name: | RegFilesHash |
Value: E5384D470E6B7608BB72349E59981D92AA4A2C93708124465C2D2730C731653D | |||
| (PID) Process: | (2488) SecuriteInfo.com.Android.Spy.82.origin.26281.298.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | delete value | Name: | RegFiles0000 |
Value: C:\Program Files (x86)\VROOT\ISTask.dll | |||
| (PID) Process: | (2488) SecuriteInfo.com.Android.Spy.82.origin.26281.298.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | delete value | Name: | Sequence |
Value: 1 | |||
| (PID) Process: | (2488) SecuriteInfo.com.Android.Spy.82.origin.26281.298.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | delete value | Name: | SessionHash |
Value: 475DDFFE07FC949DB1401192901226A1F009074AC5F95AFAFEFABE73347AF47B | |||
| (PID) Process: | (2488) SecuriteInfo.com.Android.Spy.82.origin.26281.298.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | delete value | Name: | Owner |
Value: B8090000D45EE508922ADA01 | |||
| (PID) Process: | (2488) SecuriteInfo.com.Android.Spy.82.origin.26281.298.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | delete key | Name: | (default) |
Value: | |||
Executable files
39
Suspicious files
12
Text files
10
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1012 | SecuriteInfo.com.Android.Spy.82.origin.26281.298.exe | C:\Users\admin\AppData\Local\Temp\is-DLVQ0.tmp\SecuriteInfo.com.Android.Spy.82.origin.26281.298.tmp | executable | |
MD5:36F318225B460DBDD6A2E7B94EEA313E | SHA256:59614E4DA65D9E38D7568C54CDBDE6D8B2392D87065C9A100B26DA457850EAC5 | |||
| 2488 | SecuriteInfo.com.Android.Spy.82.origin.26281.298.tmp | C:\Program Files (x86)\VROOT\is-EURFH.tmp | executable | |
MD5:7D4329C2828D6B58A9794DC9C5677DA1 | SHA256:AFD873D9521C73492CE2AC1F4565695D79CB5B73497923F45022D28FAED064F9 | |||
| 2488 | SecuriteInfo.com.Android.Spy.82.origin.26281.298.tmp | C:\Program Files (x86)\VROOT\is-H9DRQ.tmp | executable | |
MD5:176765BA0452D91B460C229F5BA4B9A2 | SHA256:8D24A69834BE1AE2471F405A76F3427EDE9DF741368B11B56B32B797E429A02E | |||
| 2488 | SecuriteInfo.com.Android.Spy.82.origin.26281.298.tmp | C:\Program Files (x86)\VROOT\Common.dll | executable | |
MD5:7D4329C2828D6B58A9794DC9C5677DA1 | SHA256:AFD873D9521C73492CE2AC1F4565695D79CB5B73497923F45022D28FAED064F9 | |||
| 2488 | SecuriteInfo.com.Android.Spy.82.origin.26281.298.tmp | C:\Program Files (x86)\VROOT\is-8TJOI.tmp | executable | |
MD5:CDC59F9A2DE0ACA428BB338F9154C7C0 | SHA256:66A77EC6AB203DF737301088E5167D56ED3F4FE2868B9A037B0F08E1BD6D1837 | |||
| 2488 | SecuriteInfo.com.Android.Spy.82.origin.26281.298.tmp | C:\Program Files (x86)\VROOT\is-DJF5N.tmp | executable | |
MD5:ABC01ED3DED0435B141A745C0632CEEC | SHA256:896F924E9CFD7ADCD90E9D7175007886777F8F12BA3F3608263F582C484A513F | |||
| 2488 | SecuriteInfo.com.Android.Spy.82.origin.26281.298.tmp | C:\Program Files (x86)\VROOT\Root.exe | executable | |
MD5:CDC59F9A2DE0ACA428BB338F9154C7C0 | SHA256:66A77EC6AB203DF737301088E5167D56ED3F4FE2868B9A037B0F08E1BD6D1837 | |||
| 2488 | SecuriteInfo.com.Android.Spy.82.origin.26281.298.tmp | C:\Program Files (x86)\VROOT\AdbWinUsbApi.dll | executable | |
MD5:176765BA0452D91B460C229F5BA4B9A2 | SHA256:8D24A69834BE1AE2471F405A76F3427EDE9DF741368B11B56B32B797E429A02E | |||
| 2488 | SecuriteInfo.com.Android.Spy.82.origin.26281.298.tmp | C:\Program Files (x86)\VROOT\is-8TCCA.tmp | executable | |
MD5:969234331326A238EA1D7F1D06B174F4 | SHA256:4182B57512DEF34DC571269D316E7C00F7C5C17AAD239B3BEE0CD3E52EF5E05F | |||
| 2488 | SecuriteInfo.com.Android.Spy.82.origin.26281.298.tmp | C:\Program Files (x86)\VROOT\is-HP8VE.tmp | executable | |
MD5:A4C9AA7C8B4BBD7105B3574F4BADA0BA | SHA256:FADB3F633DEC710A811BB7895EA9D7B317D4772412719C71C33E1FB46D53DD8D | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
7
DNS requests
6
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2124 | Root.exe | GET | 200 | 23.50.131.94:80 | http://aia.startssl.com/certs/ca.crt | unknown | binary | 1.95 Kb | unknown |
2124 | Root.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?c1c6990d644b27a7 | unknown | compressed | 65.2 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 224.0.0.252:5355 | — | — | — | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1956 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
324 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
2124 | Root.exe | 23.50.131.94:80 | aia.startssl.com | Akamai International B.V. | DE | unknown |
2124 | Root.exe | 93.184.221.240:80 | ctldl.windowsupdate.com | EDGECAST | GB | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
log.ibutian.com |
| unknown |
products.mgyun.com |
| unknown |
api.mgyun.com |
| unknown |
aia.startssl.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
links.mgyun.com |
| unknown |
Threats
Process | Message |
|---|---|
Root.exe | start of Thread::ThreadMain(report_thread)
|
Root.exe | start of Thread::ThreadMain(main_work_bk)
|
Root.exe | start of Thread::ThreadMain(autoupdate_thread)
|
RomasterConnection.exe | start of Thread::ThreadMain(adb_keeper_thread)
|
RomasterConnection.exe | start of Thread::ThreadMain(device_helper_thread)
|
RomasterConnection.exe | 2023-12-09 11:23:02 [2420] DEBUG [wWinMain] commandline: /hwnd=1115058 [RomasterConnection.cpp:45]
|
RomasterConnection.exe | 2023-12-09 11:23:02 [2420] DEBUG [CCommunication::ExchangeWndProc] new connection:1115058 [Communication.cpp:167]
|
RomasterConnection.exe | start of Thread::ThreadMain(connection_get_identify_thread)
|
RomasterConnection.exe | 2023-12-09 11:23:02 [2420] DEBUG [CCommunication::AddCommuWndHandle] curent vec size:1 [Communication.cpp:358]
|
RomasterConnection.exe | start of Thread::ThreadMain(delayed_notify_thread)
|