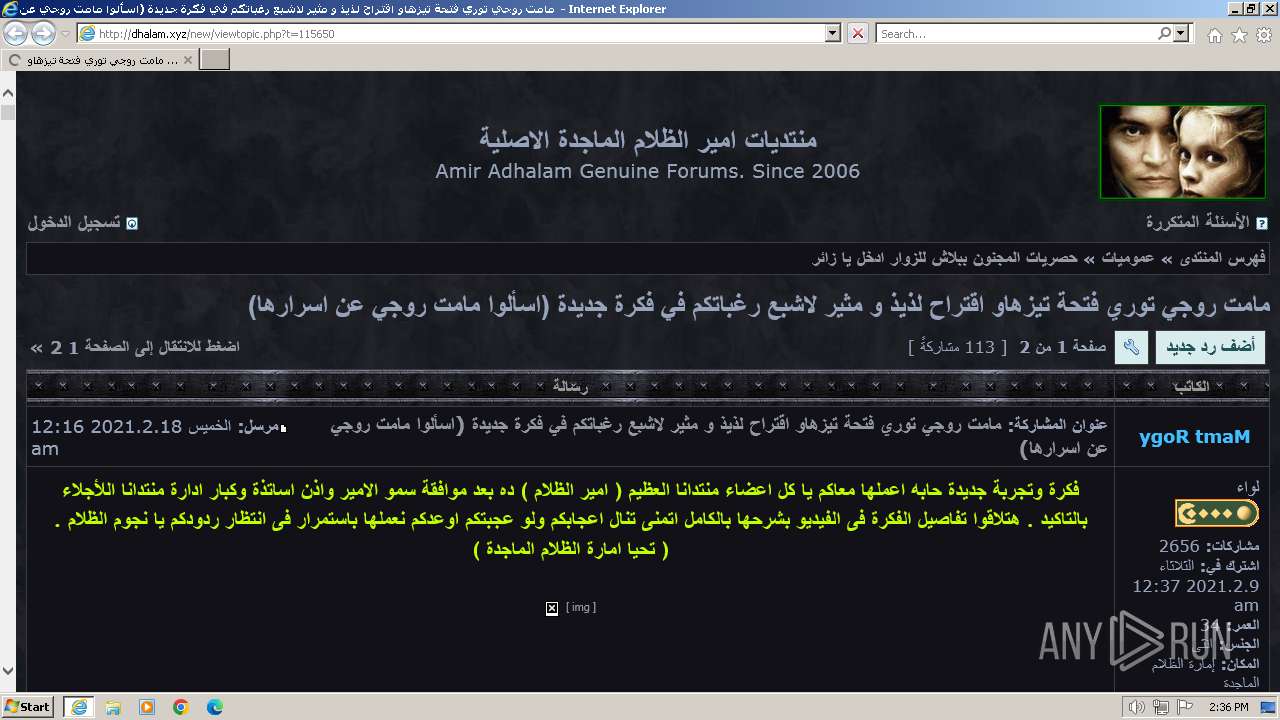
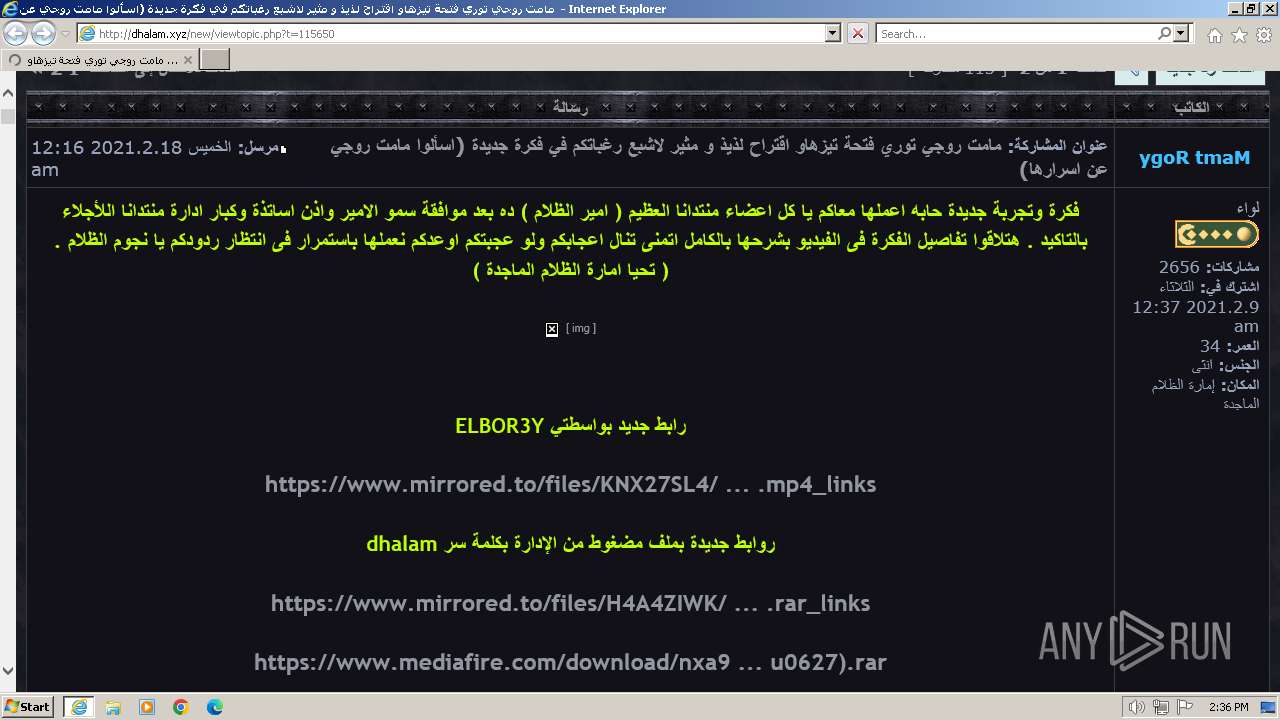
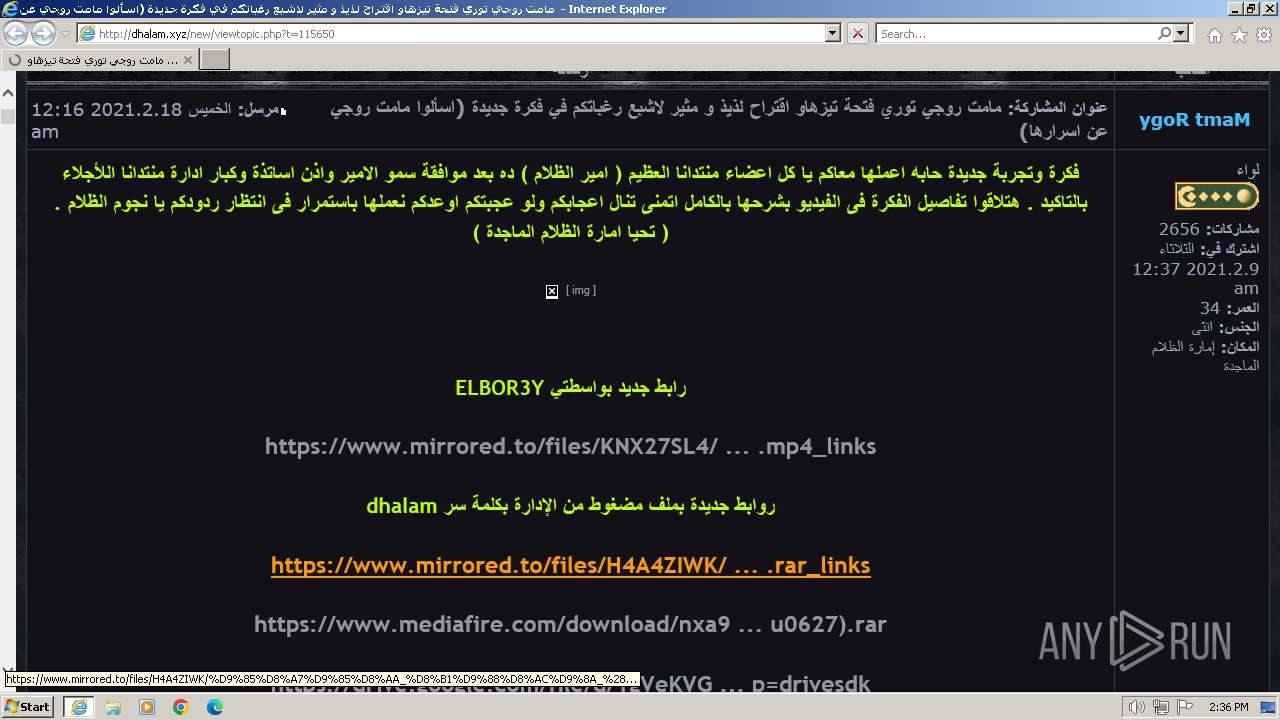
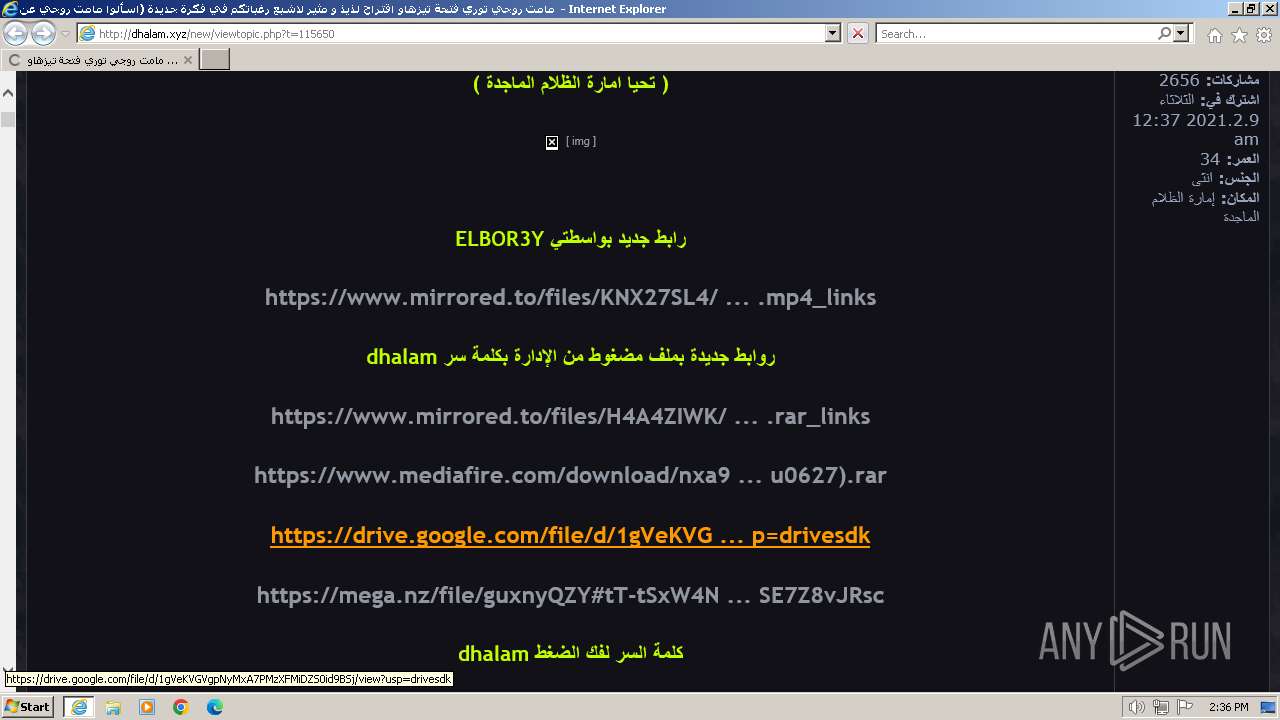
| URL: | http://dhalam.xyz/new/viewtopic.php?t=115650 |
| Full analysis: | https://app.any.run/tasks/d6fbc1dd-1bdc-4555-aa8f-dcd0de74ae26 |
| Verdict: | Malicious activity |
| Analysis date: | April 06, 2024, 13:36:22 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | A4498A6287D8E8971AF850330ED9CE6A |
| SHA1: | 2922D52F196503AE8F139F94C6085E6FD0248C63 |
| SHA256: | CE1DC99501D373378C90D1B2C550E9E011688F1A6252BA09F8225D2F679E5C88 |
| SSDEEP: | 3:N1KaNkuK05TBpVMGbVaZQVn:CaNPNV7VBVn |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Application launched itself
- iexplore.exe (PID: 3956)
Modifies the phishing filter of IE
- iexplore.exe (PID: 3956)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
39
Monitored processes
2
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3956 | "C:\Program Files\Internet Explorer\iexplore.exe" "http://dhalam.xyz/new/viewtopic.php?t=115650" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3964 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3956 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
31 114
Read events
30 971
Write events
105
Delete events
38
Modification events
| (PID) Process: | (3956) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (3956) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (3956) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 31098919 | |||
| (PID) Process: | (3956) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (3956) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 31098919 | |||
| (PID) Process: | (3956) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3956) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3956) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3956) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3956) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
0
Suspicious files
32
Text files
107
Unknown types
17
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3964 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\7JONOM7H.txt | text | |
MD5:— | SHA256:— | |||
| 3964 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\060EYAQY.txt | text | |
MD5:— | SHA256:— | |||
| 3964 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\NY0CYG1G.txt | text | |
MD5:— | SHA256:— | |||
| 3964 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\viewtopic[1].htm | html | |
MD5:— | SHA256:— | |||
| 3964 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\stylesheet[1].css | text | |
MD5:— | SHA256:— | |||
| 3964 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\site_logo[1].gif | image | |
MD5:— | SHA256:— | |||
| 3964 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\YTOWV792\icon_mini_faq[1].gif | image | |
MD5:— | SHA256:— | |||
| 3964 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\YTOWV792\icon_post_target[1].gif | image | |
MD5:— | SHA256:— | |||
| 3964 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5IWPIAR9\icon_mini_login[1].gif | image | |
MD5:— | SHA256:— | |||
| 3964 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5IWPIAR9\give_rose[1].gif | image | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
90
TCP/UDP connections
199
DNS requests
39
Threats
69
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3964 | iexplore.exe | GET | 200 | 169.60.204.202:80 | http://dhalam.xyz/new/styles/newdi/theme/stylesheet.css?assets_version=127 | US | text | 7.60 Kb | unknown |
3964 | iexplore.exe | GET | 200 | 169.60.204.202:80 | http://dhalam.xyz/new/styles/newdi/theme/images/icon_mini_faq.gif | US | image | 216 b | unknown |
3964 | iexplore.exe | GET | 200 | 169.60.204.202:80 | http://dhalam.xyz/new/viewtopic.php?t=115650 | US | html | 25.6 Kb | unknown |
3964 | iexplore.exe | GET | 200 | 169.60.204.202:80 | http://dhalam.xyz/new/styles/newdi/template/forum_fn.js?assets_version=127 | US | text | 8.80 Kb | unknown |
3964 | iexplore.exe | GET | 200 | 169.60.204.202:80 | http://dhalam.xyz/new/download/file.php?avatar=63163_1520255939.jpg | US | image | 357 b | unknown |
3964 | iexplore.exe | GET | 200 | 169.60.204.202:80 | http://dhalam.xyz/new/download/file.php?avatar=1857_1537979969.jpg | US | image | 2.61 Kb | unknown |
3964 | iexplore.exe | GET | 200 | 169.60.204.202:80 | http://dhalam.xyz/new/images/ranks/special_ranks/003.gif | US | image | 8.71 Kb | unknown |
3964 | iexplore.exe | GET | — | 169.60.204.202:80 | http://dhalam.xyz/new/download/file.php?avatar=62028_1613777796.jpeg | US | — | — | unknown |
3964 | iexplore.exe | GET | 200 | 169.60.204.202:80 | http://dhalam.xyz/new/images/smilies/slider_winesmiley.gif | US | image | 1.77 Kb | unknown |
3964 | iexplore.exe | GET | 200 | 169.60.204.202:80 | http://dhalam.xyz/new/download/file.php?avatar=61684_1607719494.jpg | US | image | 1.79 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 224.0.0.252:5355 | — | — | — | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3964 | iexplore.exe | 169.60.204.202:80 | dhalam.xyz | SOFTLAYER | US | unknown |
3964 | iexplore.exe | 92.243.23.175:80 | pics.adresaro.com | GANDI SAS | FR | unknown |
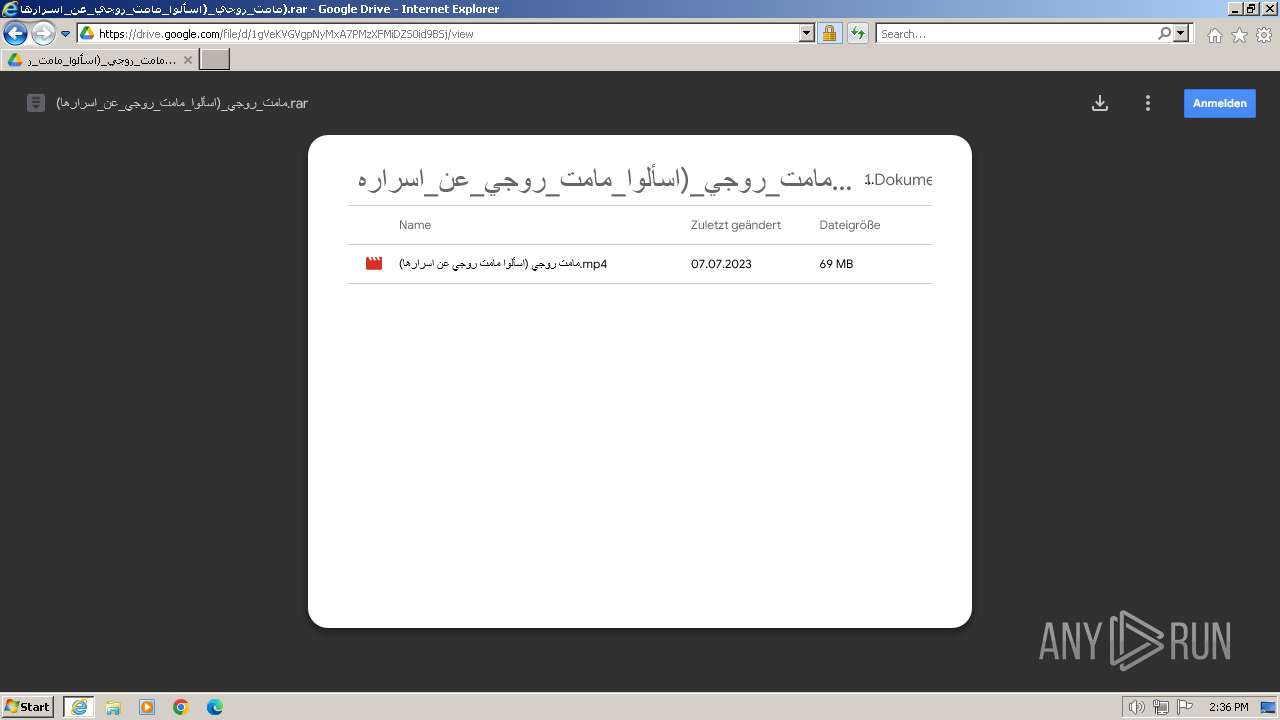
3964 | iexplore.exe | 162.19.58.160:443 | i.ibb.co | OVH SAS | FR | unknown |
3964 | iexplore.exe | 162.19.88.68:443 | i.postimg.cc | OVH SAS | FR | unknown |
3964 | iexplore.exe | 185.85.196.6:80 | twemoji.maxcdn.com | StackPath LLC | US | unknown |
3964 | iexplore.exe | 110.232.118.81:80 | img9.uploadhouse.com | RackCorp | AU | unknown |
3964 | iexplore.exe | 110.232.118.81:443 | img9.uploadhouse.com | RackCorp | AU | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
dhalam.xyz |
| whitelisted |
pics.adresaro.com |
| unknown |
share.adresaro.com |
| unknown |
i.ibb.co |
| shared |
img9.uploadhouse.com |
| unknown |
img6.uploadhouse.com |
| unknown |
i.postimg.cc |
| whitelisted |
twemoji.maxcdn.com |
| whitelisted |
www.stackpath.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3964 | iexplore.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
1080 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .cc TLD |
3964 | iexplore.exe | Not Suspicious Traffic | INFO [ANY.RUN] Image hosting service ImgBB |
3964 | iexplore.exe | Not Suspicious Traffic | INFO [ANY.RUN] Image hosting service ImgBB |
3964 | iexplore.exe | Not Suspicious Traffic | INFO [ANY.RUN] Image hosting service ImgBB |
3964 | iexplore.exe | Not Suspicious Traffic | INFO [ANY.RUN] Image hosting service ImgBB |
3964 | iexplore.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
3964 | iexplore.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
3964 | iexplore.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
3964 | iexplore.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |