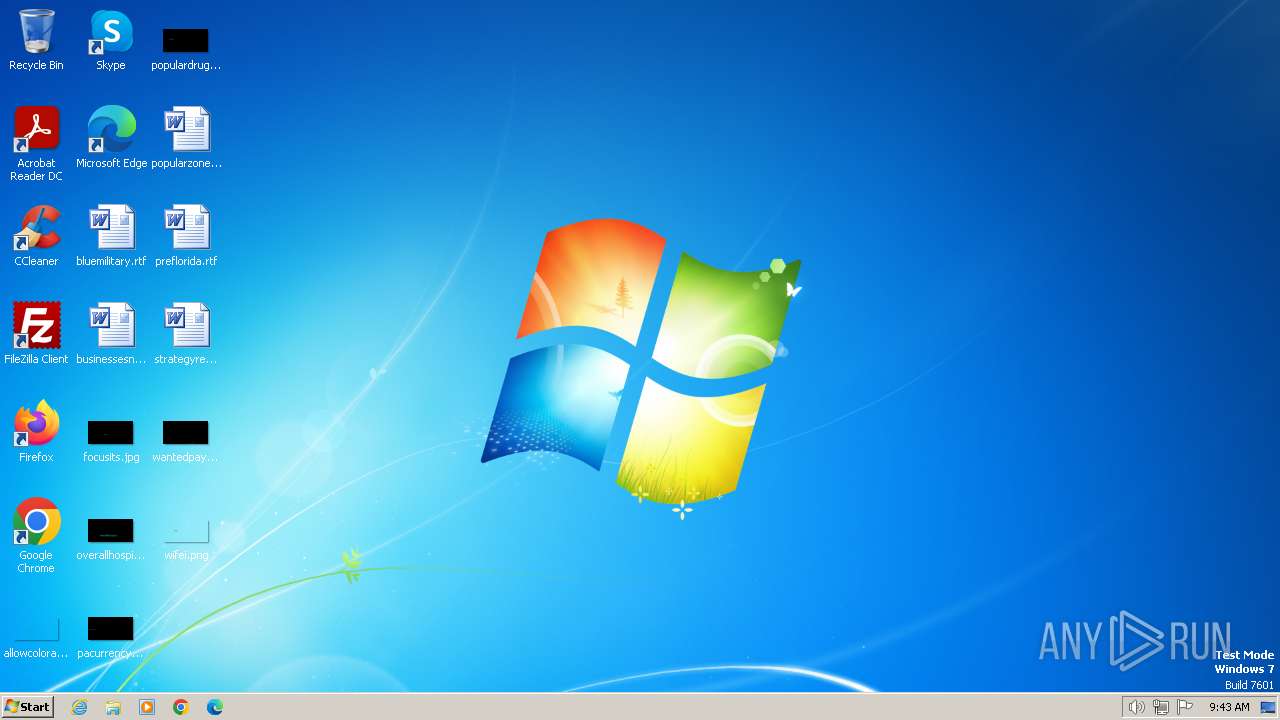
| File name: | FinancialInvestingDetails.pdf www.skype.vbs |
| Full analysis: | https://app.any.run/tasks/d0b6d1b1-b9a4-4156-b86f-f3aaffeadbbc |
| Verdict: | Malicious activity |
| Analysis date: | January 07, 2024, 09:43:05 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/plain |
| File info: | ASCII text, with CRLF line terminators |
| MD5: | D44BF7D816B38388410BBAAAFDD73CE5 |
| SHA1: | 3E75F8BDFF5817304E11201AAD556C646D371B83 |
| SHA256: | CE0E2C758444AE6E3BE95B83E0F53990E722472E75113D57B18A19CB8E397CA9 |
| SSDEEP: | 6:QSLQ/AHcilT5rPHwOd3qFtEKBNMfLoalNMfLoalNMfLojEmiAFb9nATRHAtIe4H1:Qp/ocA5roOGE02TFAtIe4EJe |
MALICIOUS
Creates internet connection object (SCRIPT)
- wscript.exe (PID: 2124)
Sends HTTP request (SCRIPT)
- wscript.exe (PID: 2124)
Opens an HTTP connection (SCRIPT)
- wscript.exe (PID: 2124)
SUSPICIOUS
Runs shell command (SCRIPT)
- wscript.exe (PID: 2124)
Reads the Internet Settings
- wscript.exe (PID: 2124)
Starts CMD.EXE for commands execution
- wscript.exe (PID: 2124)
INFO
Unusual connection from system programs
- wscript.exe (PID: 2124)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
35
Monitored processes
2
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1072 | "C:\Windows\System32\cmd.exe" <!DOCTYPE HTML PUBLIC "-//IETF//DTD HTML 2.0//EN"> <html><head> <title>404 Not Found</title> </head><body> <h1>Not Found</h1> <p>The requested URL was not found on this server.</p> <hr> <address>Apache/2.4.29 (Ubuntu) Server at naserviceebaysmman.shop Port 80</address> </body></html> | C:\Windows\System32\cmd.exe | — | wscript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2124 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\AppData\Local\Temp\FinancialInvestingDetails.pdf www.skype.vbs" | C:\Windows\System32\wscript.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
Total events
346
Read events
338
Write events
8
Delete events
0
Modification events
| (PID) Process: | (2124) wscript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2124) wscript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2124) wscript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2124) wscript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
0
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
5
DNS requests
1
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2124 | wscript.exe | GET | 404 | 5.2.68.76:80 | http://naserviceebaysmman.shop/muanluek | unknown | html | 285 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2124 | wscript.exe | 5.2.68.76:80 | naserviceebaysmman.shop | The Infrastructure Group B.V. | NL | unknown |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
naserviceebaysmman.shop |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2124 | wscript.exe | A Network Trojan was detected | ET MALWARE Suspected Malicious JS Loader Activity (GET) |