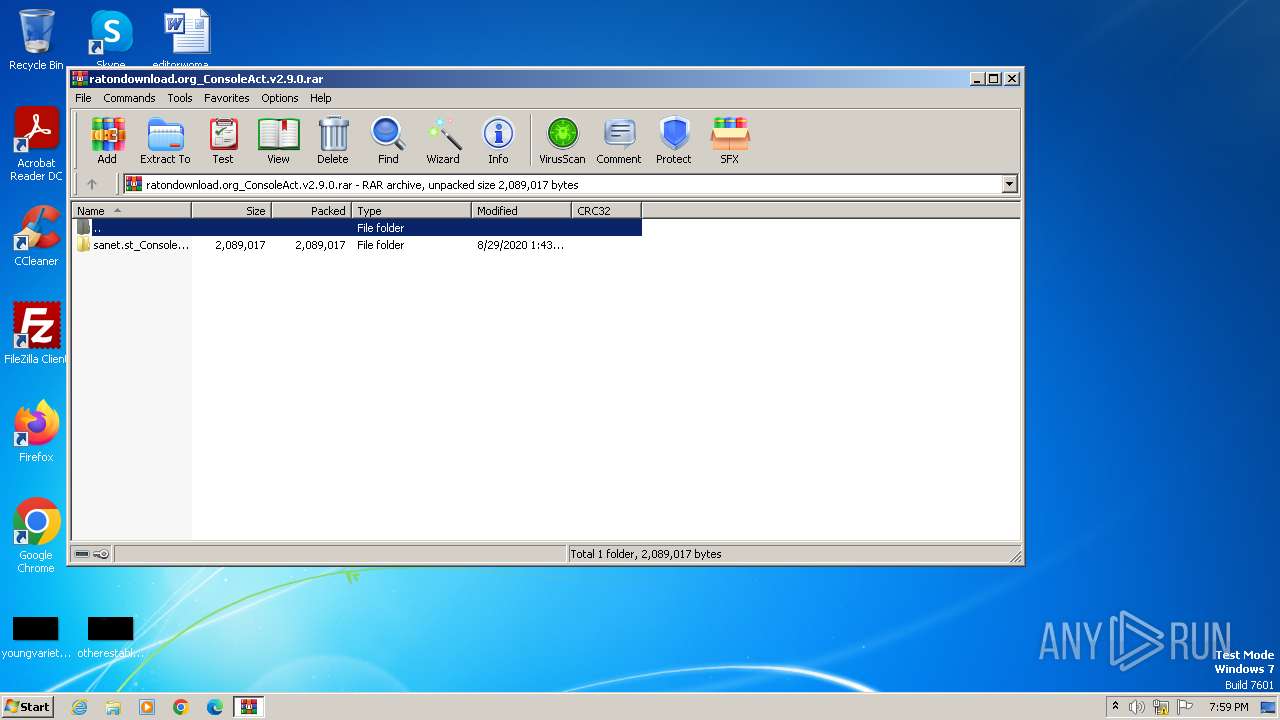
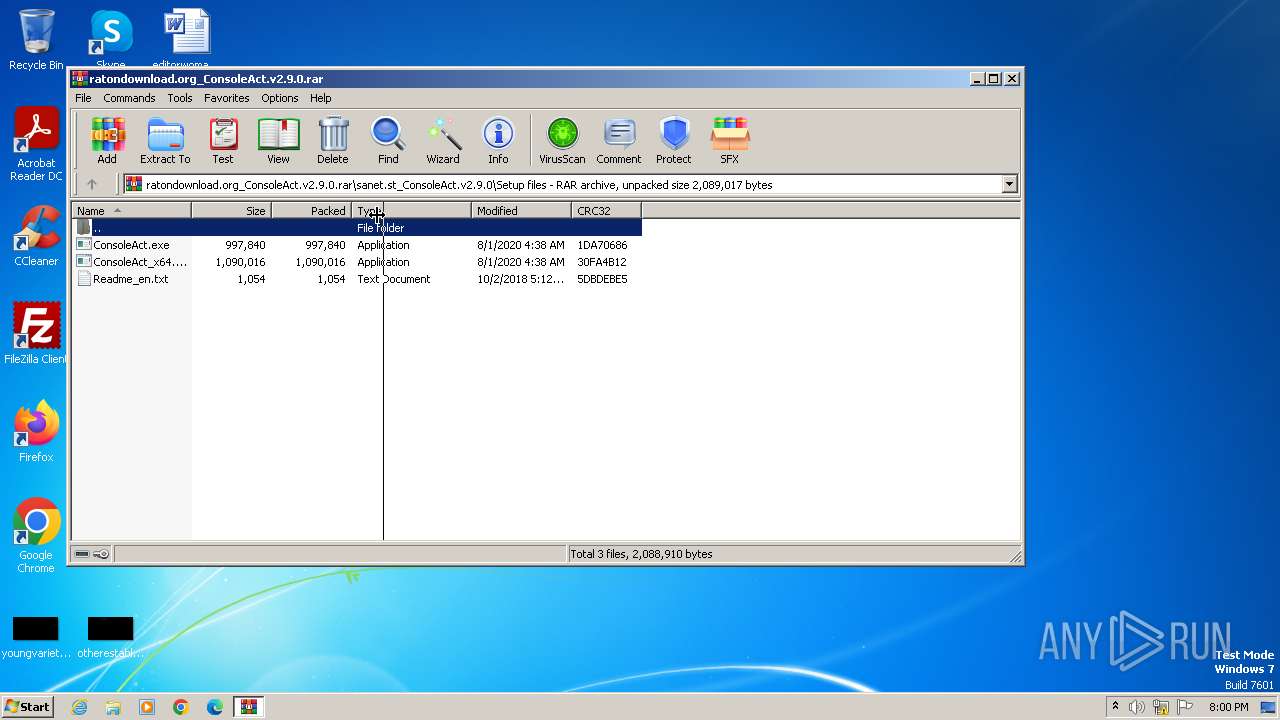
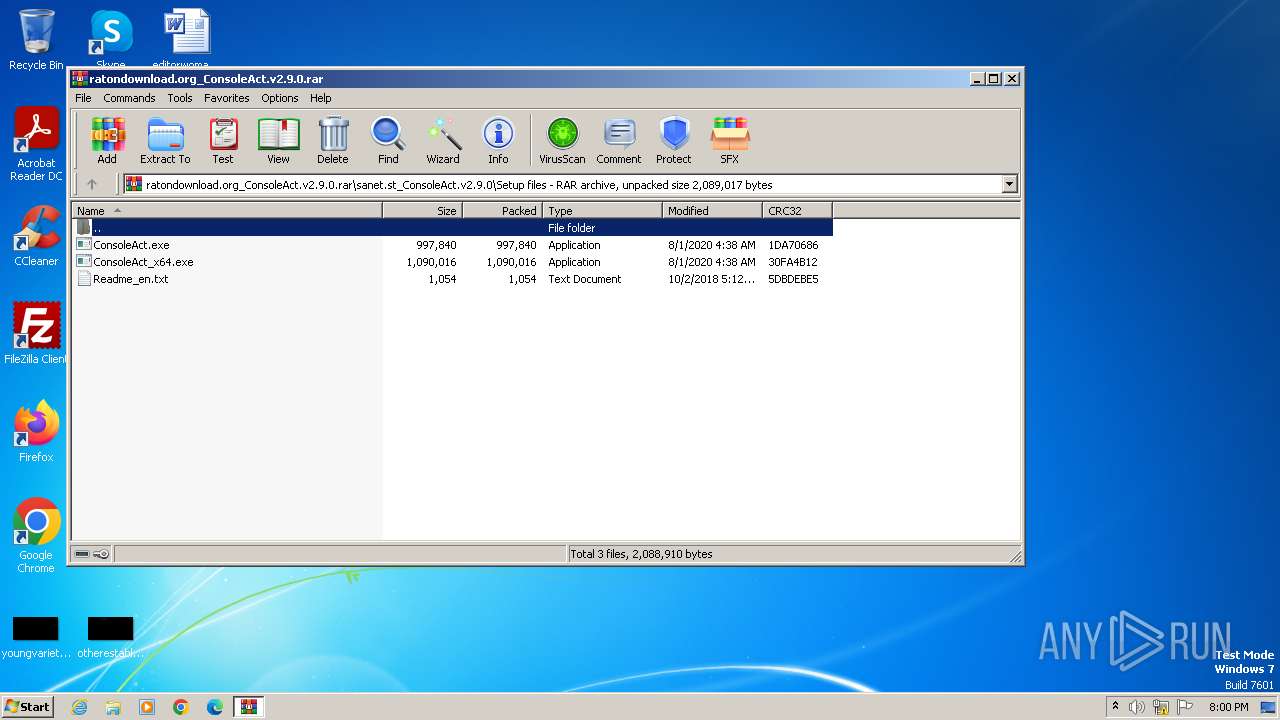
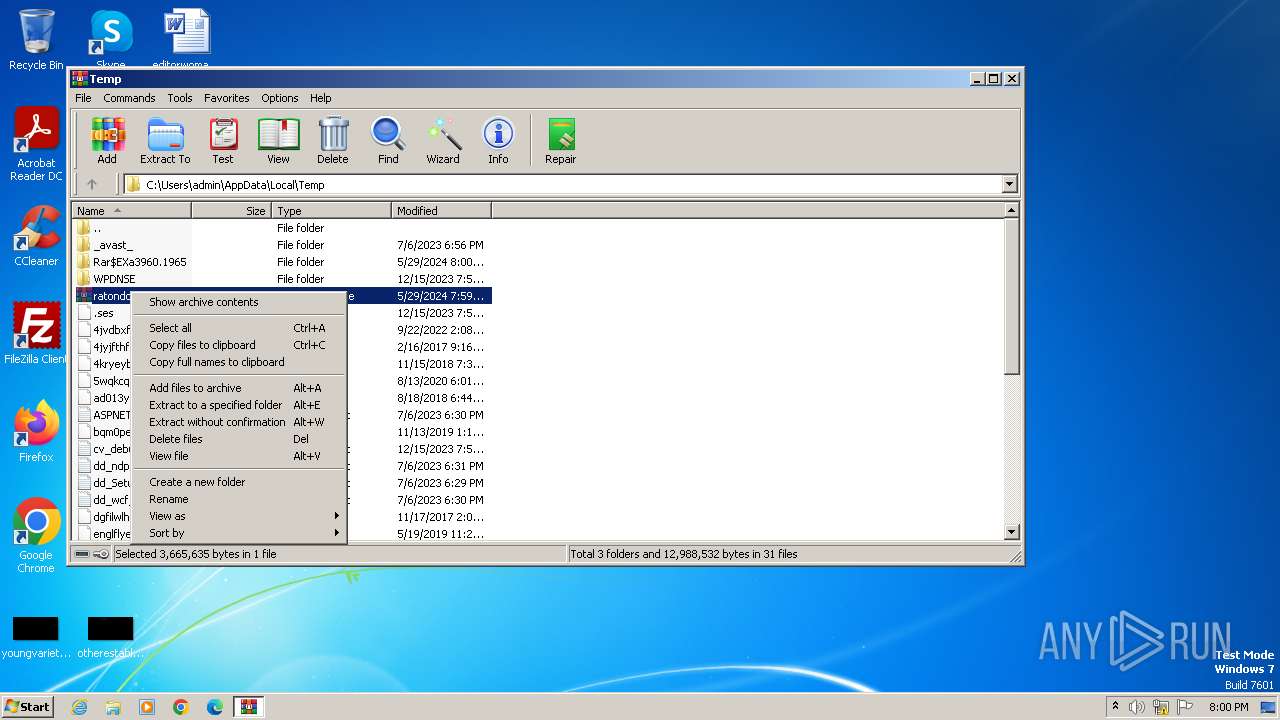
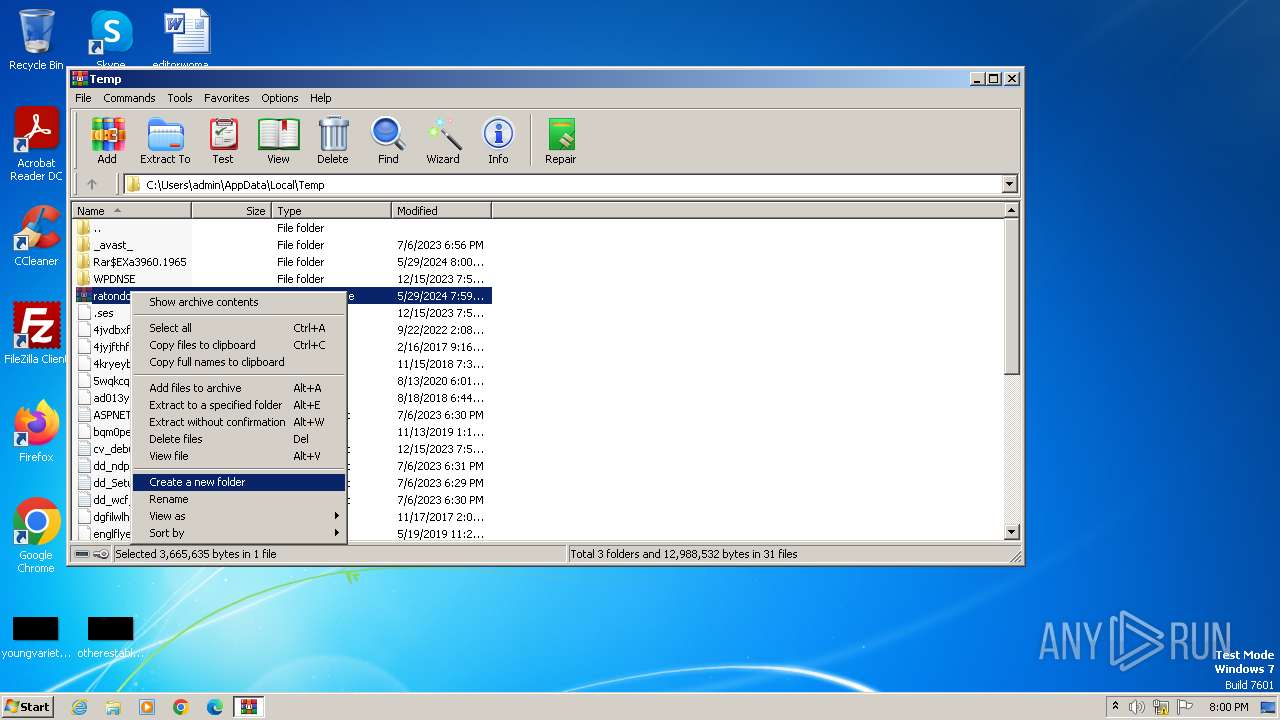
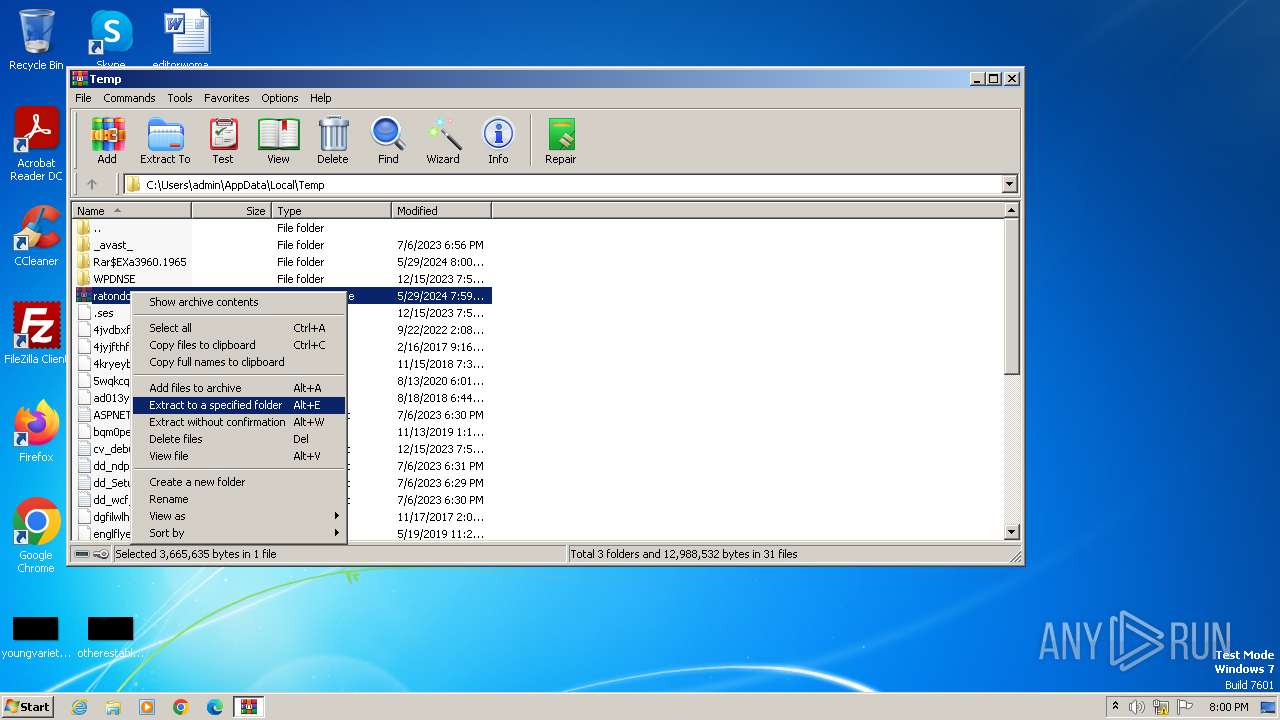
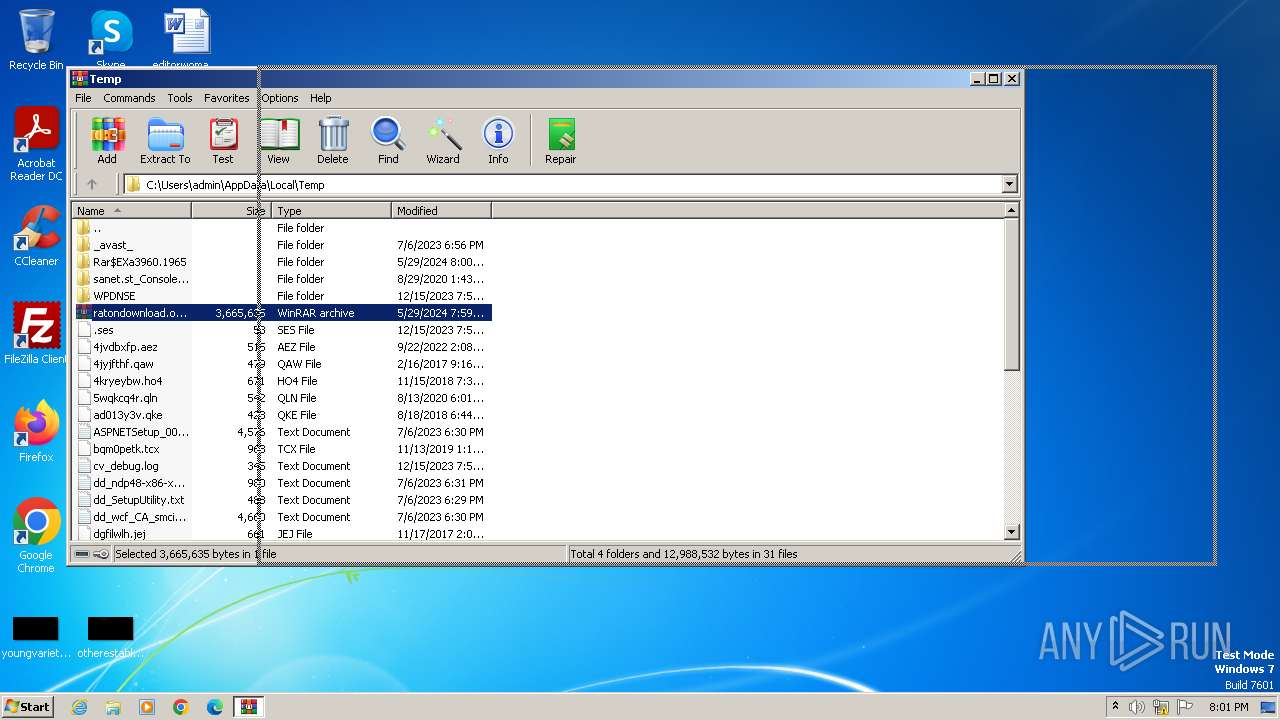
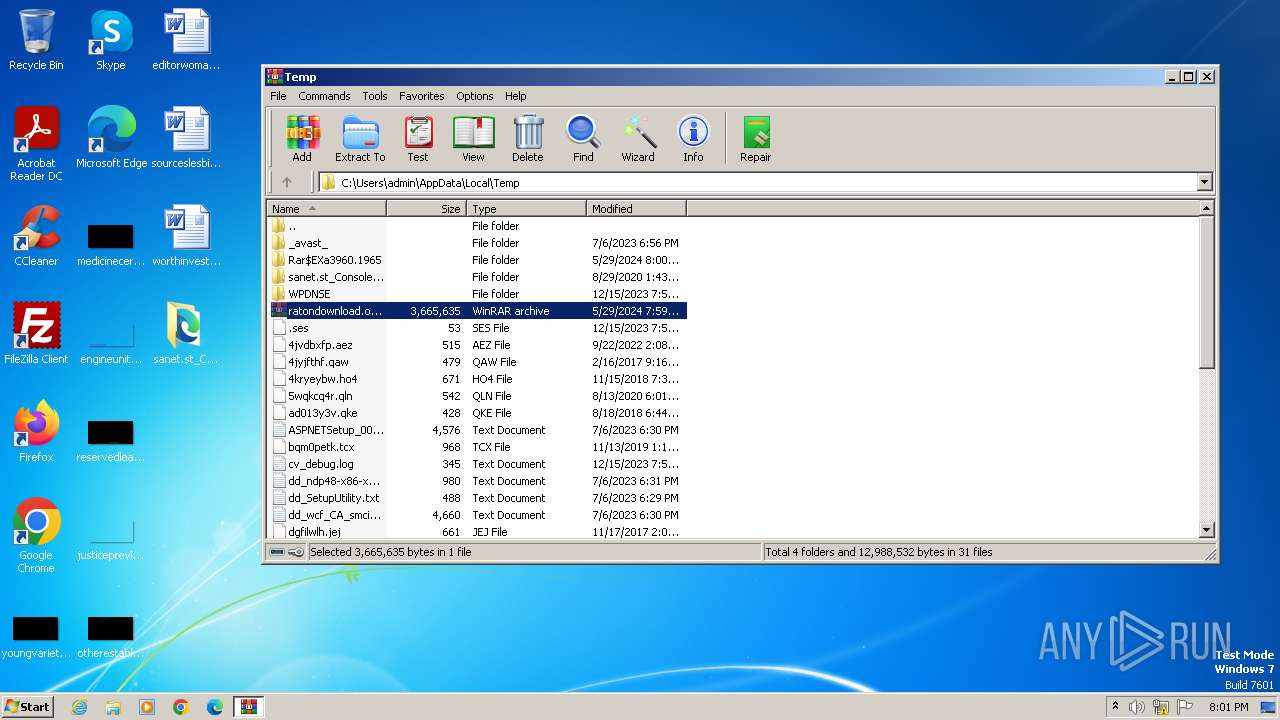
| File name: | ratondownload.org_ConsoleAct.v2.9.0.rar |
| Full analysis: | https://app.any.run/tasks/62b47089-a596-4b4f-a9a3-de5c01d44c7b |
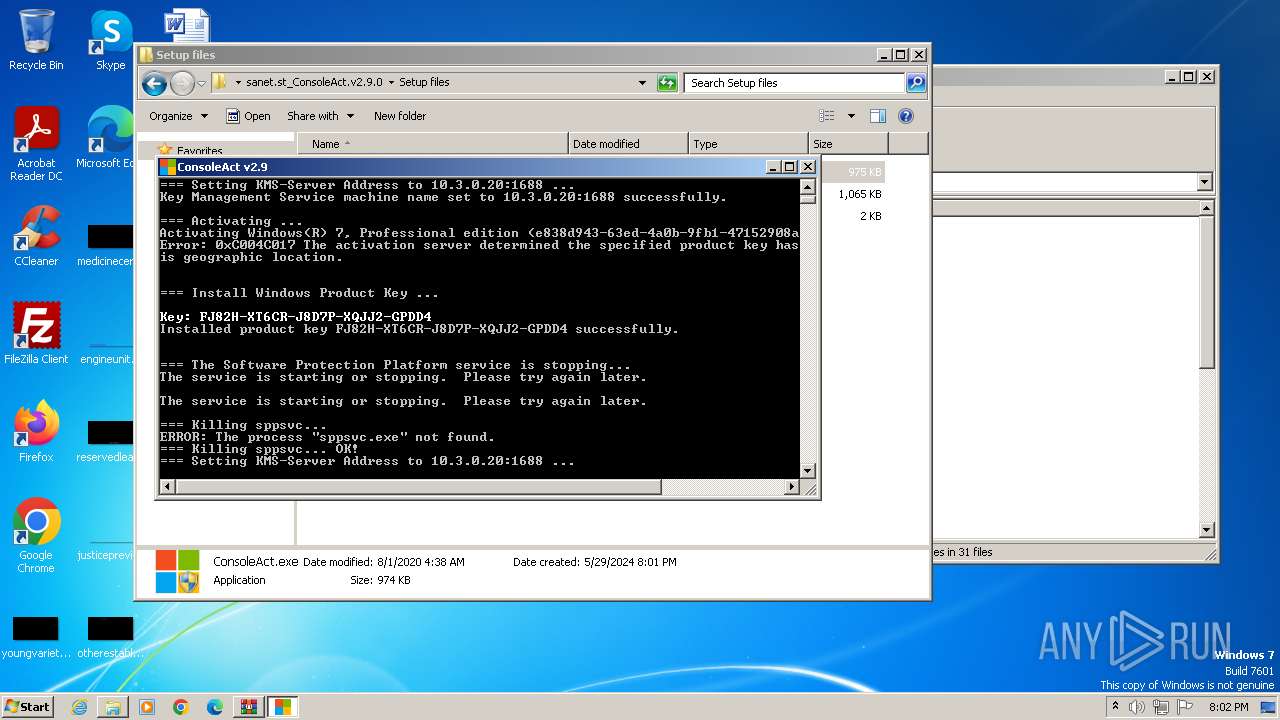
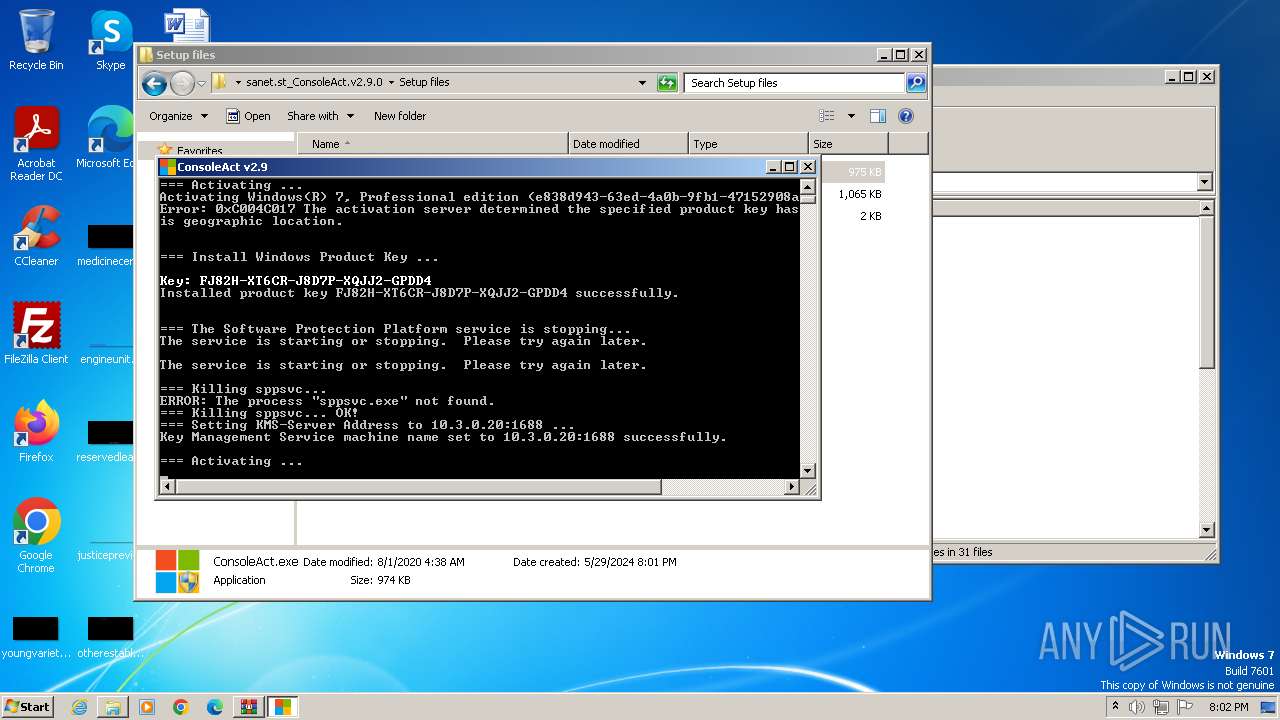
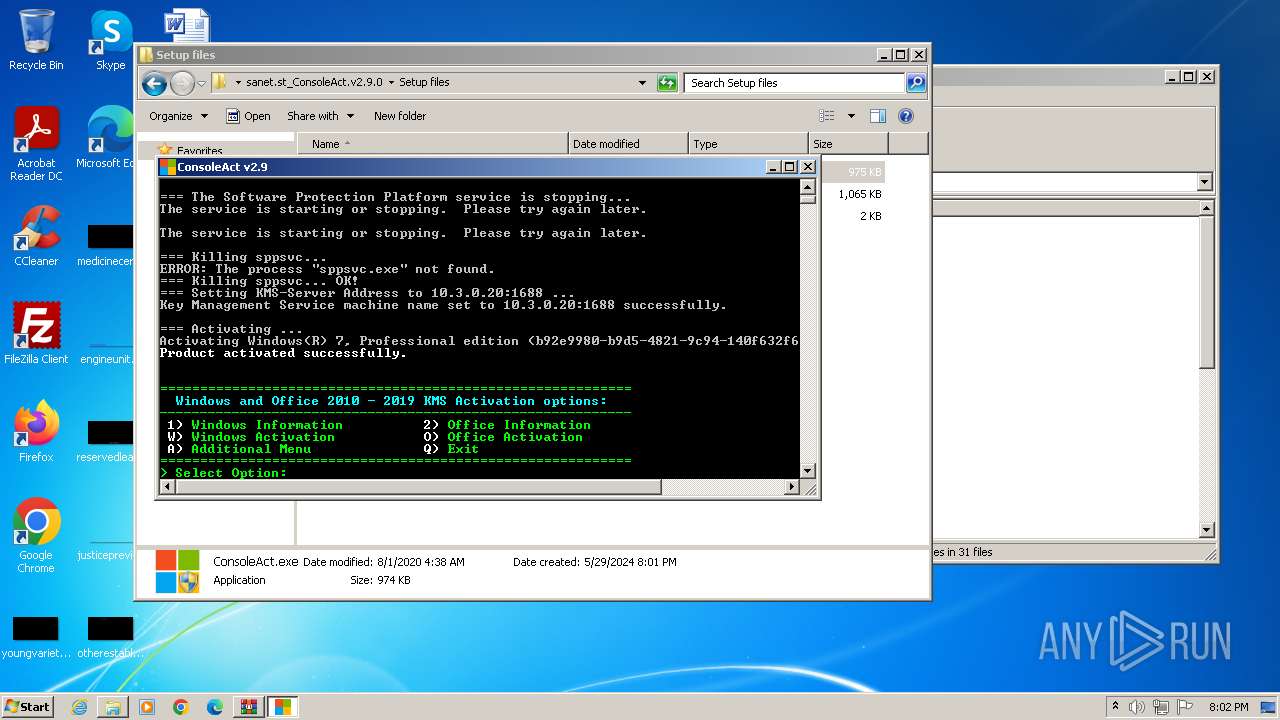
| Verdict: | Malicious activity |
| Analysis date: | May 29, 2024, 18:59:30 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | 2E7F362DF996FD04C863DA7BC5D91341 |
| SHA1: | B941CA75E9156490EB4F6B9B9B880CA8A1D3E974 |
| SHA256: | CE0AB3F73CD9524625998A9E70B9C8C4296F2B549A15D804872F5A90FC897564 |
| SSDEEP: | 98304:qvOd3fmj4zpdOsKhi904X8WsKMaPhfD4netPF2Xwfqi/KVOLj2hwe1Oggkst58DZ:GyKqOCo |
MALICIOUS
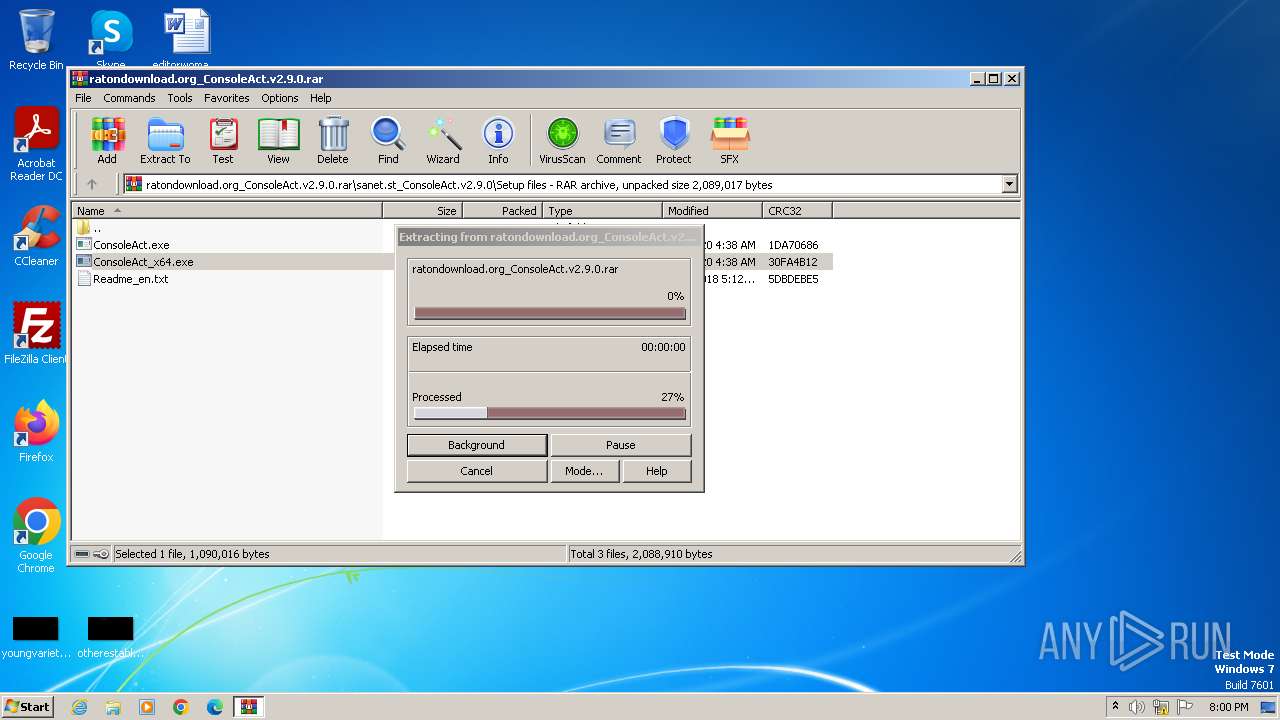
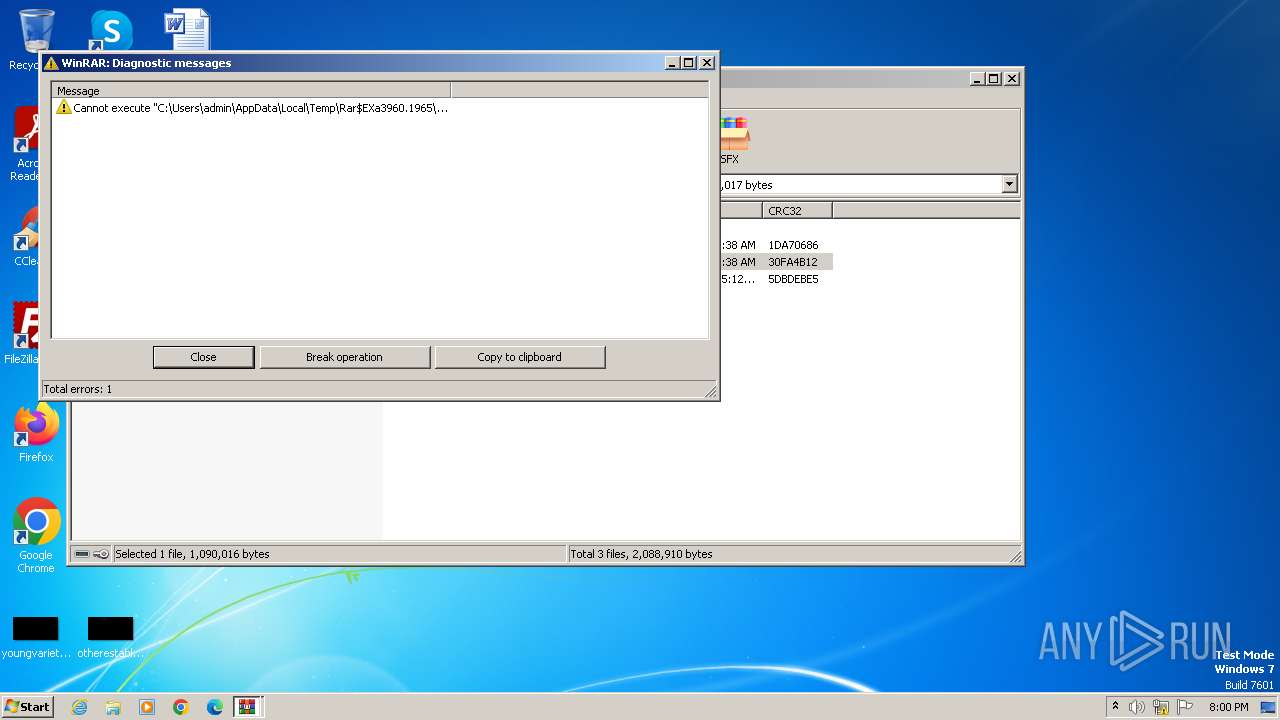
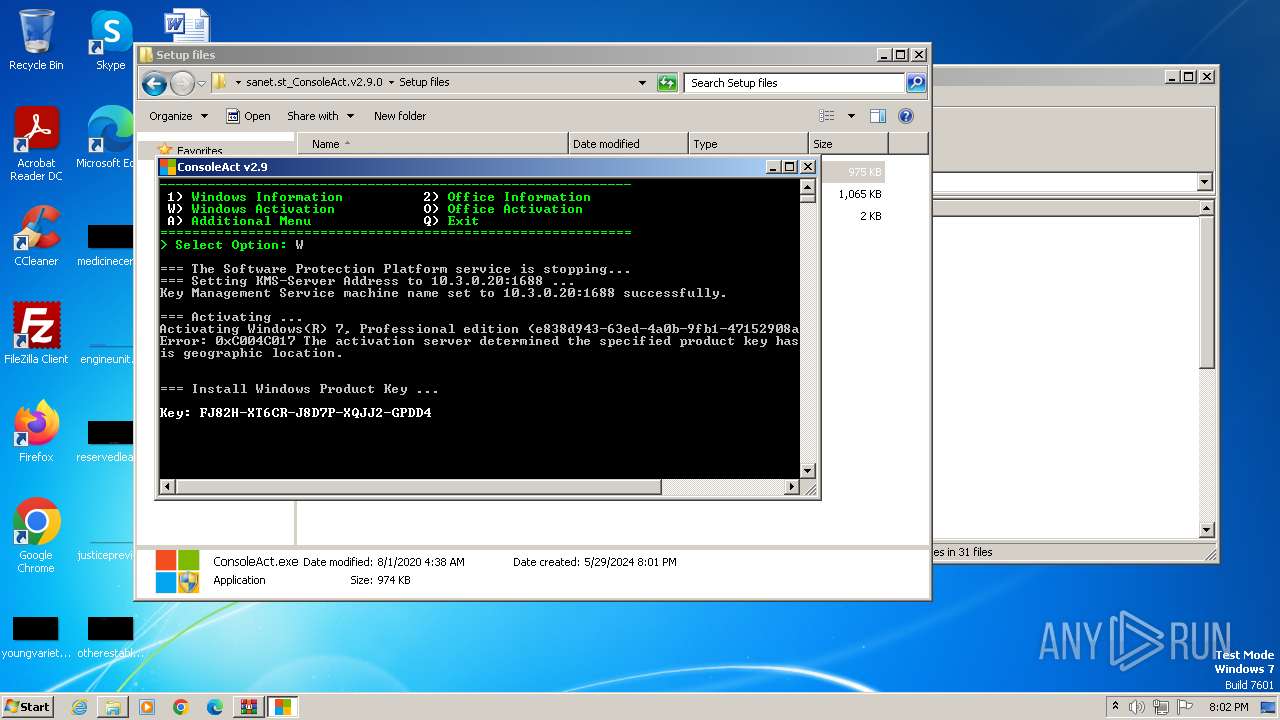
Drops the executable file immediately after the start
- WinRAR.exe (PID: 3960)
- ConsoleAct.exe (PID: 1552)
Creates a writable file in the system directory
- ConsoleAct.exe (PID: 1552)
Opens a text file (SCRIPT)
- cscript.exe (PID: 2748)
- cscript.exe (PID: 1480)
- cscript.exe (PID: 2928)
- cscript.exe (PID: 1312)
- cscript.exe (PID: 2992)
- cscript.exe (PID: 3016)
- cscript.exe (PID: 3756)
- cscript.exe (PID: 3624)
- cscript.exe (PID: 3900)
- cscript.exe (PID: 2172)
- cscript.exe (PID: 2600)
- cscript.exe (PID: 2356)
- cscript.exe (PID: 1976)
- cscript.exe (PID: 2692)
- cscript.exe (PID: 1848)
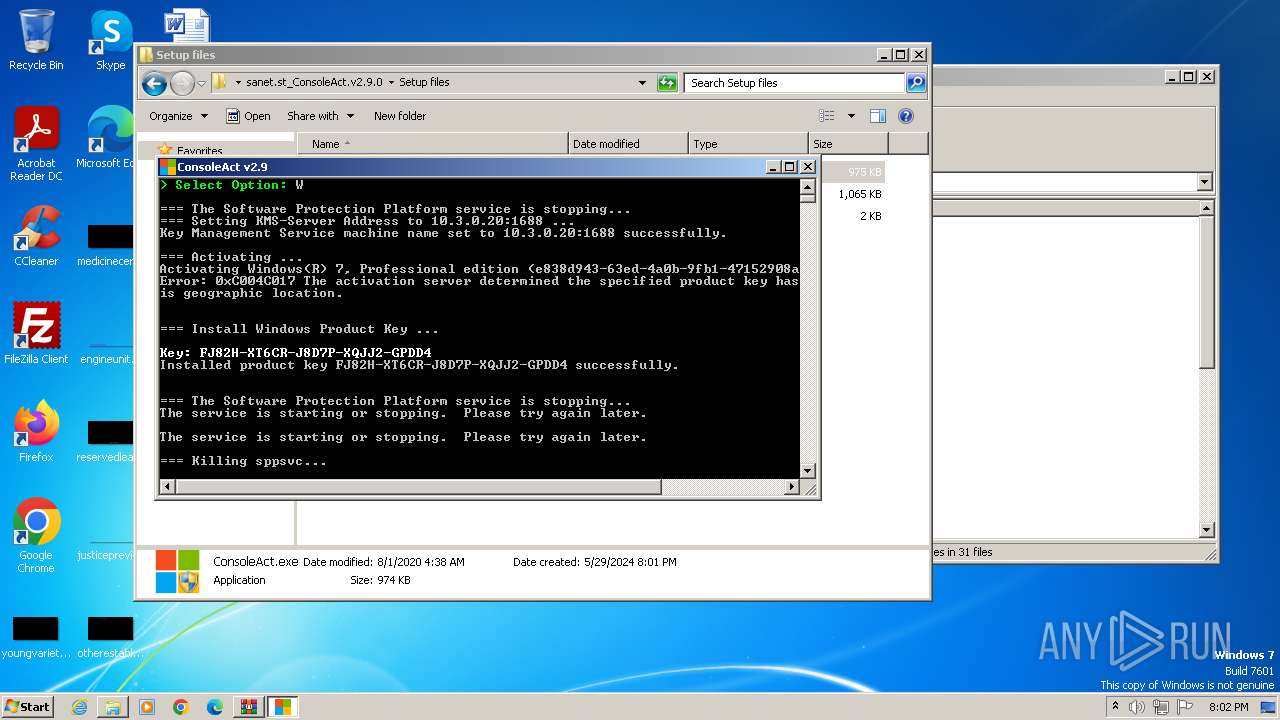
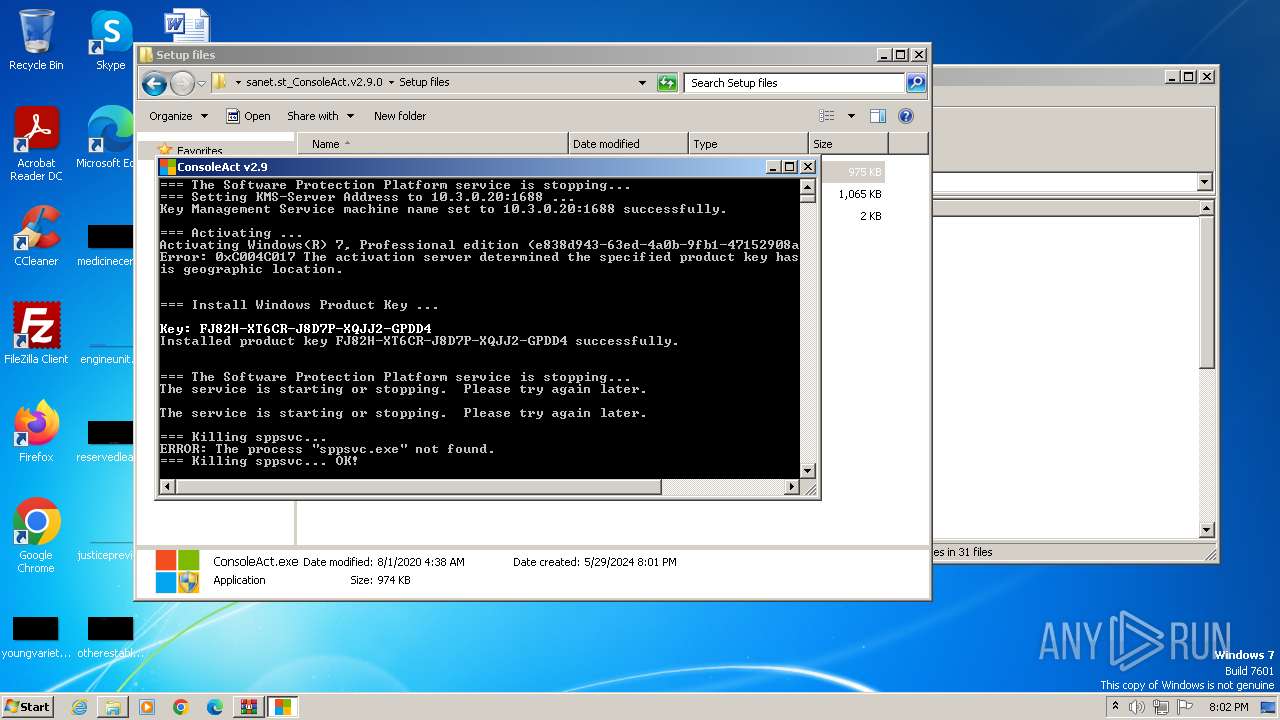
Starts NET.EXE for service management
- cmd.exe (PID: 3304)
- cmd.exe (PID: 3160)
- net.exe (PID: 3204)
- net.exe (PID: 3120)
SUSPICIOUS
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 3960)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 1596)
- cmd.exe (PID: 1936)
- cmd.exe (PID: 2080)
- cmd.exe (PID: 2512)
- cmd.exe (PID: 2624)
- cmd.exe (PID: 444)
- cmd.exe (PID: 2468)
- cmd.exe (PID: 1008)
- cmd.exe (PID: 2324)
- cmd.exe (PID: 2408)
- cmd.exe (PID: 1520)
- cmd.exe (PID: 2548)
- ConsoleAct.exe (PID: 1552)
- cmd.exe (PID: 1044)
- cmd.exe (PID: 3100)
- cmd.exe (PID: 3124)
- cmd.exe (PID: 2020)
- cmd.exe (PID: 3456)
- cmd.exe (PID: 3200)
- cmd.exe (PID: 3264)
- cmd.exe (PID: 3392)
- cmd.exe (PID: 3360)
- cmd.exe (PID: 2116)
- cmd.exe (PID: 3336)
- cmd.exe (PID: 1116)
- cmd.exe (PID: 588)
- cmd.exe (PID: 2340)
- cmd.exe (PID: 3680)
- cmd.exe (PID: 3708)
- cmd.exe (PID: 3472)
- cmd.exe (PID: 2232)
- cmd.exe (PID: 2316)
- cmd.exe (PID: 1060)
- cmd.exe (PID: 1660)
- cmd.exe (PID: 1948)
- cmd.exe (PID: 284)
- cmd.exe (PID: 1440)
- cmd.exe (PID: 2544)
- cmd.exe (PID: 2892)
- cmd.exe (PID: 4016)
- cmd.exe (PID: 1880)
- cmd.exe (PID: 2740)
- cmd.exe (PID: 2780)
Executable content was dropped or overwritten
- ConsoleAct.exe (PID: 1552)
Starts CMD.EXE for commands execution
- ConsoleAct.exe (PID: 1552)
Uses NETSH.EXE to add a firewall rule or allowed programs
- cmd.exe (PID: 2504)
- cmd.exe (PID: 2068)
Reads data from a binary Stream object (SCRIPT)
- cscript.exe (PID: 1480)
- cscript.exe (PID: 2748)
- cscript.exe (PID: 1312)
- cscript.exe (PID: 2928)
- cscript.exe (PID: 2992)
- cscript.exe (PID: 3016)
- cscript.exe (PID: 3756)
- cscript.exe (PID: 3624)
- cscript.exe (PID: 3900)
- cscript.exe (PID: 2600)
- cscript.exe (PID: 2172)
- cscript.exe (PID: 1976)
- cscript.exe (PID: 2356)
- cscript.exe (PID: 1848)
- cscript.exe (PID: 2692)
The process executes VB scripts
- cmd.exe (PID: 2636)
- cmd.exe (PID: 916)
- cmd.exe (PID: 2536)
- cmd.exe (PID: 2444)
- cmd.exe (PID: 3008)
- cmd.exe (PID: 3044)
- cmd.exe (PID: 3616)
- cmd.exe (PID: 3764)
- cmd.exe (PID: 3868)
- cmd.exe (PID: 736)
- cmd.exe (PID: 324)
- cmd.exe (PID: 1120)
- cmd.exe (PID: 1696)
- cmd.exe (PID: 1408)
- cmd.exe (PID: 2680)
Uses WMI to retrieve WMI-managed resources (SCRIPT)
- cscript.exe (PID: 1480)
- cscript.exe (PID: 2748)
- cscript.exe (PID: 1312)
- cscript.exe (PID: 2992)
- cscript.exe (PID: 2928)
- cscript.exe (PID: 3016)
- cscript.exe (PID: 3756)
- cscript.exe (PID: 3624)
- cscript.exe (PID: 3900)
- cscript.exe (PID: 2172)
- cscript.exe (PID: 2356)
- cscript.exe (PID: 2600)
- cscript.exe (PID: 1976)
- cscript.exe (PID: 2692)
- cscript.exe (PID: 1848)
Gets full path of the running script (SCRIPT)
- cscript.exe (PID: 1480)
- cscript.exe (PID: 2748)
- cscript.exe (PID: 1312)
- cscript.exe (PID: 2928)
- cscript.exe (PID: 2992)
- cscript.exe (PID: 3016)
- cscript.exe (PID: 3624)
- cscript.exe (PID: 3756)
- cscript.exe (PID: 3900)
- cscript.exe (PID: 2600)
- cscript.exe (PID: 2172)
- cscript.exe (PID: 1976)
- cscript.exe (PID: 2356)
- cscript.exe (PID: 2692)
- cscript.exe (PID: 1848)
Checks whether a specific file exists (SCRIPT)
- cscript.exe (PID: 1480)
- cscript.exe (PID: 2748)
- cscript.exe (PID: 1312)
- cscript.exe (PID: 2928)
- cscript.exe (PID: 2992)
- cscript.exe (PID: 3016)
- cscript.exe (PID: 3624)
- cscript.exe (PID: 3756)
- cscript.exe (PID: 3900)
- cscript.exe (PID: 2172)
- cscript.exe (PID: 2600)
- cscript.exe (PID: 2356)
- cscript.exe (PID: 1976)
- cscript.exe (PID: 2692)
- cscript.exe (PID: 1848)
Executes WMI query (SCRIPT)
- cscript.exe (PID: 1480)
- cscript.exe (PID: 1312)
- cscript.exe (PID: 2992)
- cscript.exe (PID: 3016)
- cscript.exe (PID: 3756)
- cscript.exe (PID: 3900)
- cscript.exe (PID: 3624)
- cscript.exe (PID: 2172)
- cscript.exe (PID: 2356)
- cscript.exe (PID: 1848)
- cscript.exe (PID: 2692)
Creates FileSystem object to access computer's file system (SCRIPT)
- cscript.exe (PID: 2748)
- cscript.exe (PID: 1480)
- cscript.exe (PID: 1312)
- cscript.exe (PID: 2928)
- cscript.exe (PID: 3016)
- cscript.exe (PID: 2992)
- cscript.exe (PID: 3756)
- cscript.exe (PID: 3624)
- cscript.exe (PID: 3900)
- cscript.exe (PID: 2172)
- cscript.exe (PID: 2600)
- cscript.exe (PID: 2356)
- cscript.exe (PID: 1976)
- cscript.exe (PID: 2692)
- cscript.exe (PID: 1848)
The process downloads a VBScript from the remote host
- cmd.exe (PID: 3008)
- cmd.exe (PID: 1408)
Uses NETSH.EXE to delete a firewall rule or allowed programs
- cmd.exe (PID: 3436)
- cmd.exe (PID: 2748)
Accesses system date via WMI (SCRIPT)
- cscript.exe (PID: 3624)
Starts SC.EXE for service management
- cmd.exe (PID: 3968)
Hides command output
- cmd.exe (PID: 3968)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 3192)
- cmd.exe (PID: 2824)
INFO
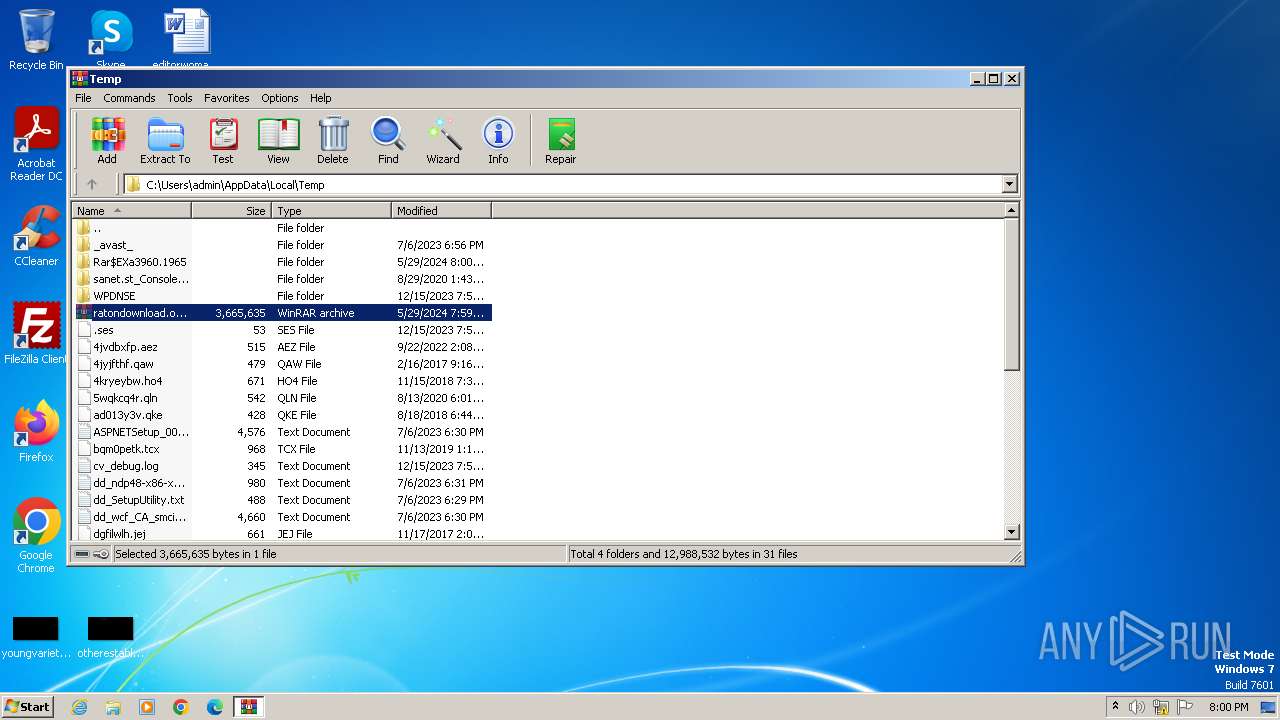
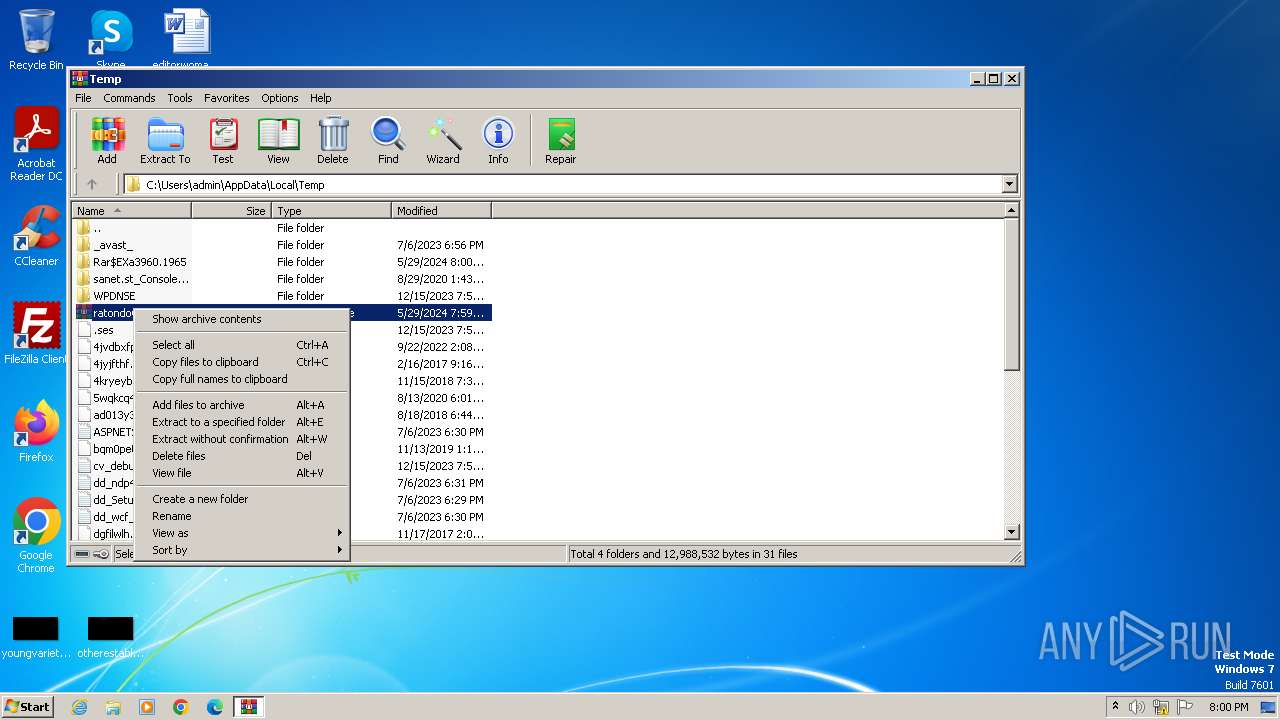
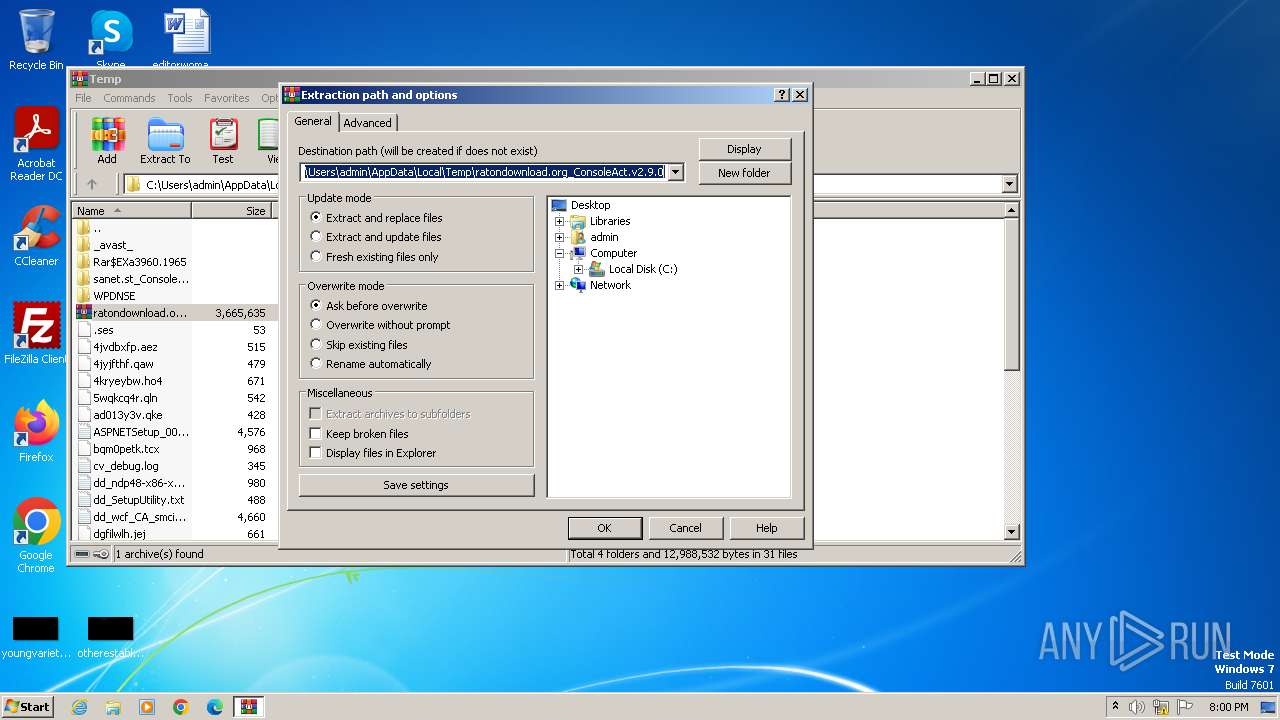
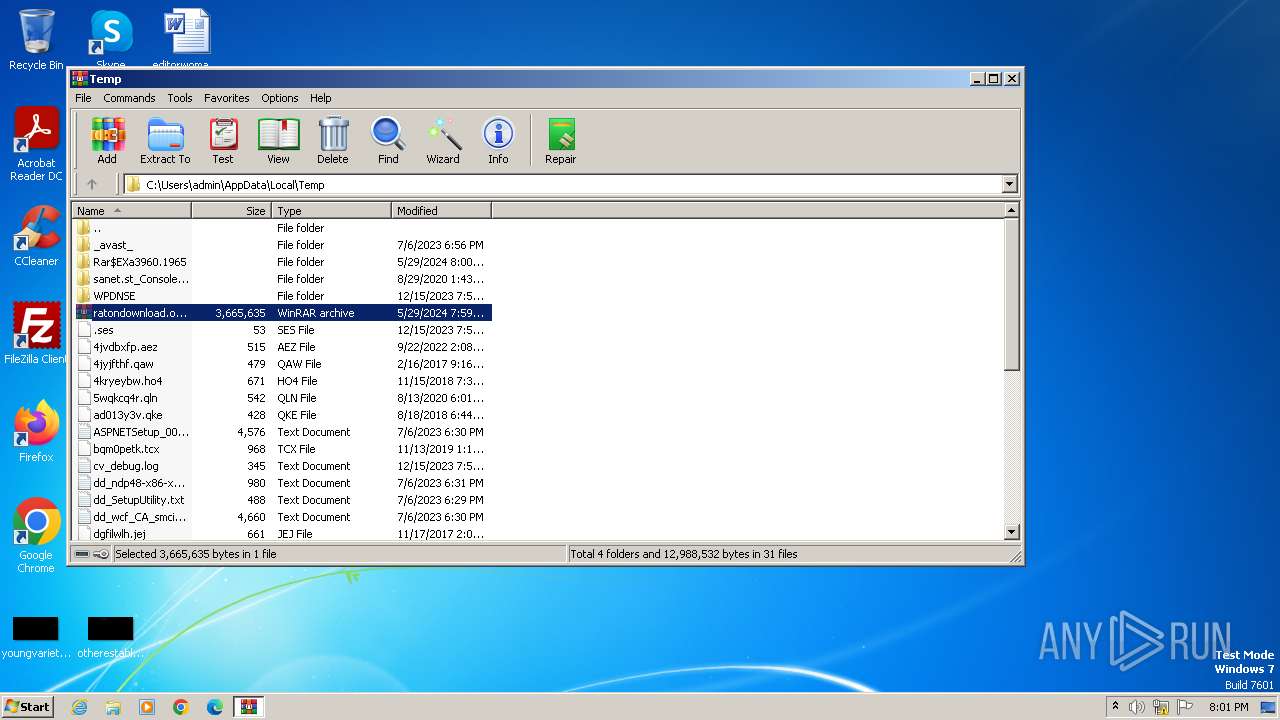
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3960)
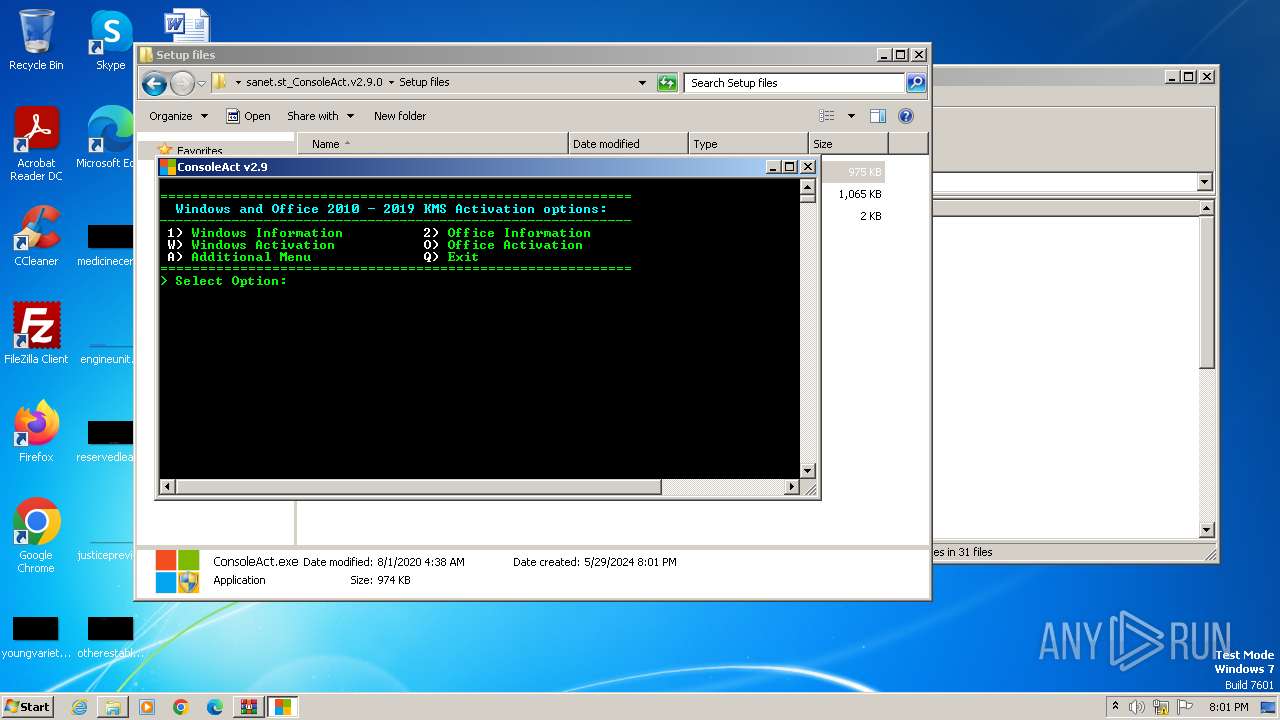
Manual execution by a user
- ConsoleAct.exe (PID: 1620)
- ConsoleAct.exe (PID: 1552)
- wmpnscfg.exe (PID: 2756)
Checks supported languages
- ConsoleAct.exe (PID: 1552)
- wmpnscfg.exe (PID: 2756)
Reads Environment values
- ConsoleAct.exe (PID: 1552)
Reads product name
- ConsoleAct.exe (PID: 1552)
Reads Microsoft Office registry keys
- reg.exe (PID: 2588)
- reg.exe (PID: 1128)
- reg.exe (PID: 1292)
- reg.exe (PID: 2092)
Reads security settings of Internet Explorer
- cscript.exe (PID: 1480)
- cscript.exe (PID: 2748)
- cscript.exe (PID: 1312)
- cscript.exe (PID: 2928)
- cscript.exe (PID: 2992)
- cscript.exe (PID: 3016)
- cscript.exe (PID: 3756)
- cscript.exe (PID: 3624)
- cscript.exe (PID: 3900)
- cscript.exe (PID: 2172)
- cscript.exe (PID: 2600)
- cscript.exe (PID: 2356)
- cscript.exe (PID: 1976)
- cscript.exe (PID: 1848)
- cscript.exe (PID: 2692)
Reads the computer name
- wmpnscfg.exe (PID: 2756)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
Total processes
197
Monitored processes
148
Malicious processes
31
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 284 | "C:\Windows\System32\cmd.exe" /c reg.exe add "HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\osppsvc.exe" /f /v "KMS_RenewalInterval" /t REG_DWORD /d 10080 2>&1 | C:\Windows\System32\cmd.exe | — | ConsoleAct.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 324 | "C:\Windows\System32\cmd.exe" /c cscript.exe C:\Windows\System32\slmgr.vbs //NoLogo /ckms 2>&1 | C:\Windows\System32\cmd.exe | — | ConsoleAct.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 444 | "C:\Windows\System32\cmd.exe" /c reg.exe add "HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\sppsvc.exe" /f /v "VerifierDlls" /t REG_SZ /d "SppExtComObjHook.dll" 2>&1 | C:\Windows\System32\cmd.exe | — | ConsoleAct.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 568 | "C:\Windows\System32\cmd.exe" /c schtasks.exe /delete /f /tn "\Microsoft\Windows\SoftwareProtectionPlatform\SvcTrigger" 2>&1 | C:\Windows\System32\cmd.exe | — | ConsoleAct.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 588 | "C:\Windows\System32\cmd.exe" /c reg.exe delete "HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\osppsvc.exe" /f /v Debugger 2>&1 | C:\Windows\System32\cmd.exe | — | ConsoleAct.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 736 | reg.exe delete "HKLM\SOFTWARE\Policies\Microsoft\Windows NT\CurrentVersion\Software Protection Platform" /v "NoGenTicket" /f | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 736 | "C:\Windows\System32\cmd.exe" /c cscript.exe C:\Windows\System32\slmgr.vbs //NoLogo /sdns 2>&1 | C:\Windows\System32\cmd.exe | — | ConsoleAct.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 916 | "C:\Windows\System32\cmd.exe" /c cscript.exe C:\Windows\System32\slmgr.vbs //NoLogo /act-type 0 2>&1 | C:\Windows\System32\cmd.exe | — | ConsoleAct.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1008 | "C:\Windows\System32\cmd.exe" /c reg.exe add "HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\osppsvc.exe" /f /v "KMS_ActivationInterval" /t REG_DWORD /d 120 2>&1 | C:\Windows\System32\cmd.exe | — | ConsoleAct.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1044 | "C:\Windows\System32\cmd.exe" /c reg.exe add "HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\osppsvc.exe" /f /v "GlobalFlag" /t REG_DWORD /d 256 2>&1 | C:\Windows\System32\cmd.exe | — | ConsoleAct.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
14 185
Read events
13 910
Write events
263
Delete events
12
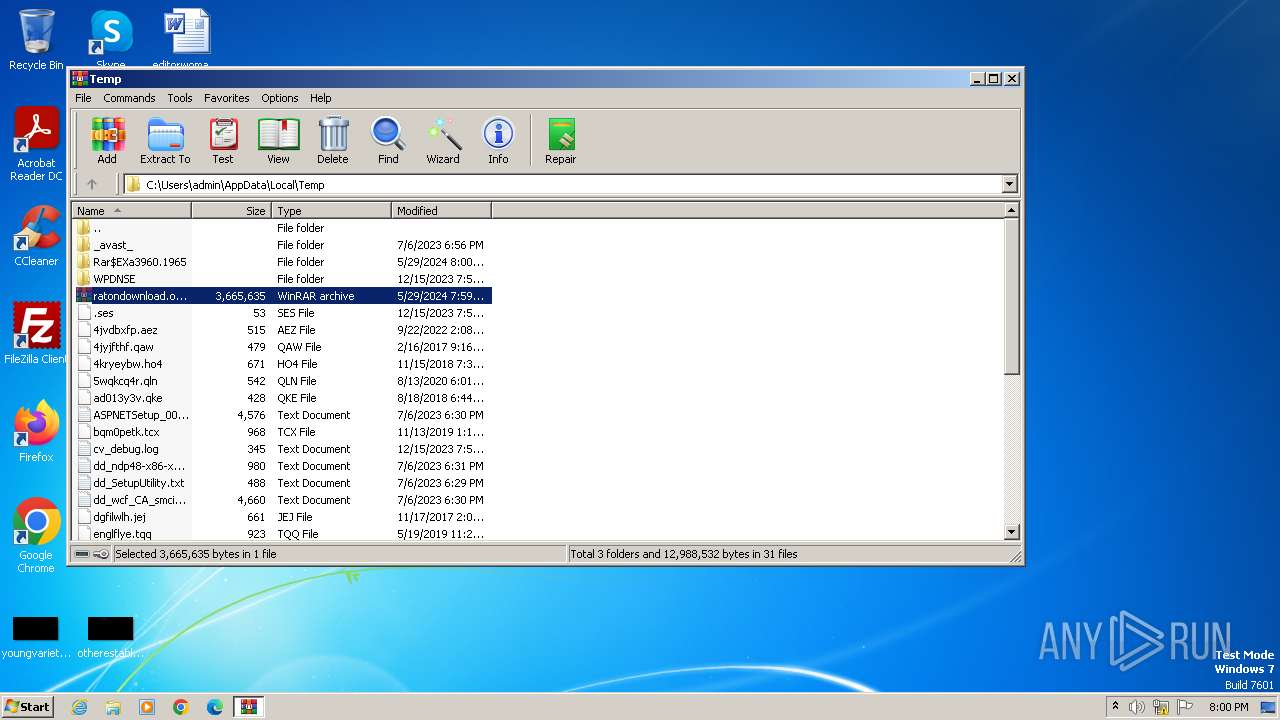
Modification events
| (PID) Process: | (3960) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3960) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3960) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3960) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\phacker.zip | |||
| (PID) Process: | (3960) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (3960) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\curl-8.5.0_1-win32-mingw.zip | |||
| (PID) Process: | (3960) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\ratondownload.org_ConsoleAct.v2.9.0.rar | |||
| (PID) Process: | (3960) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3960) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3960) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
Executable files
7
Suspicious files
3
Text files
3
Unknown types
0
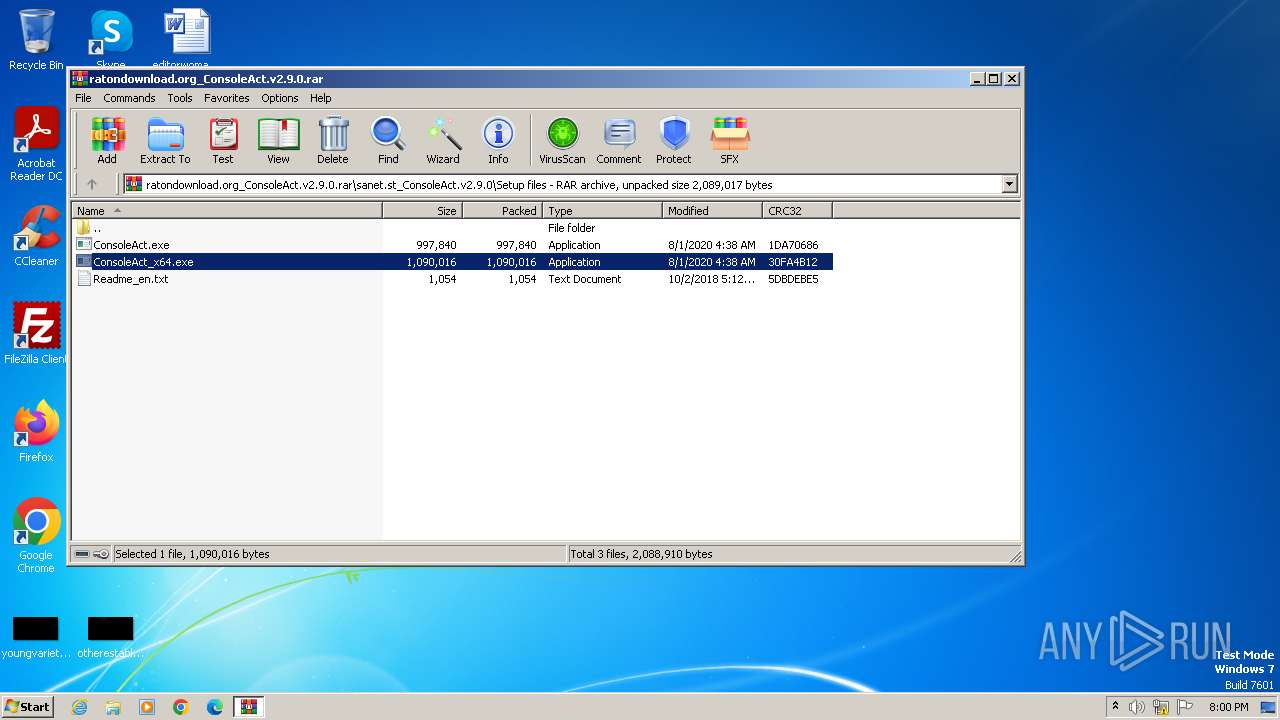
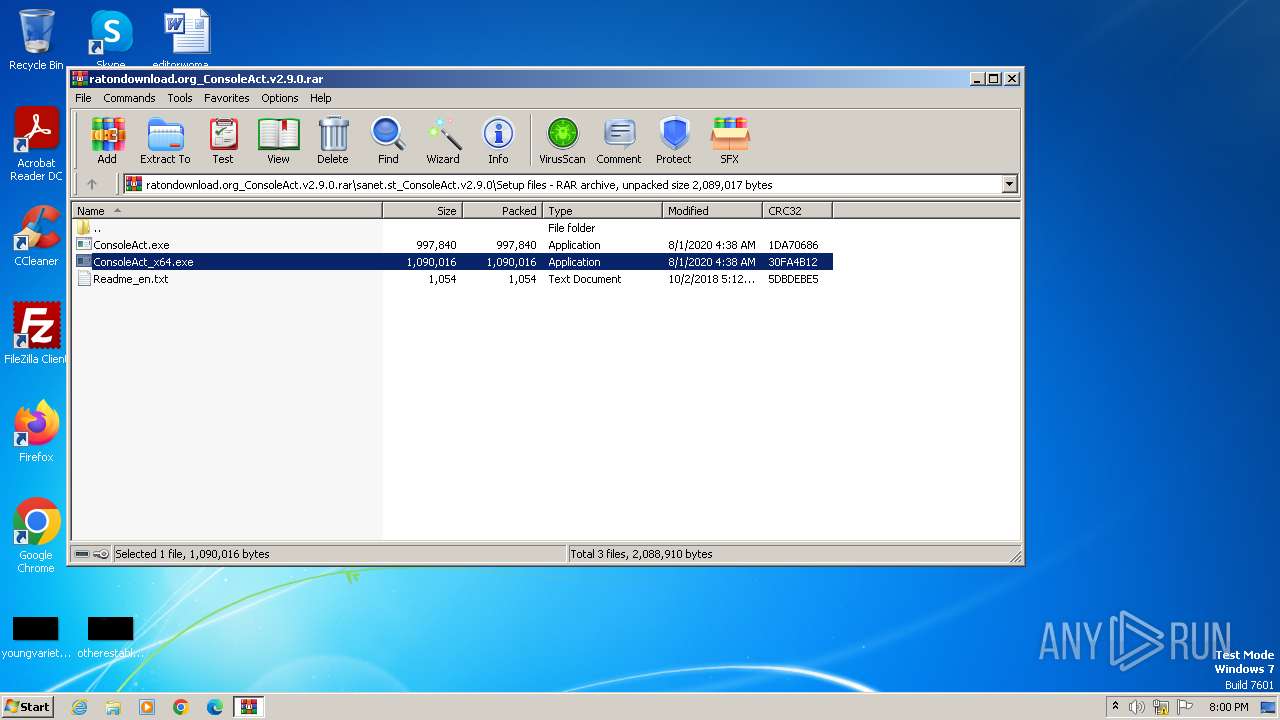
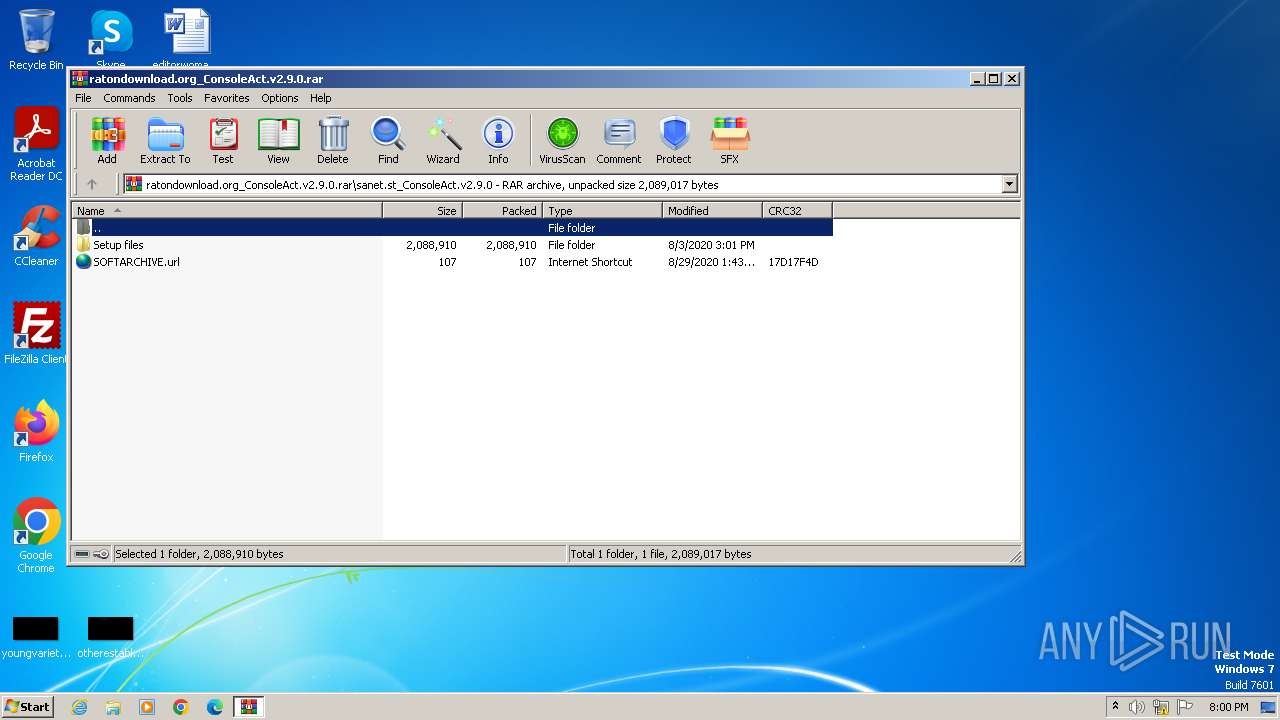
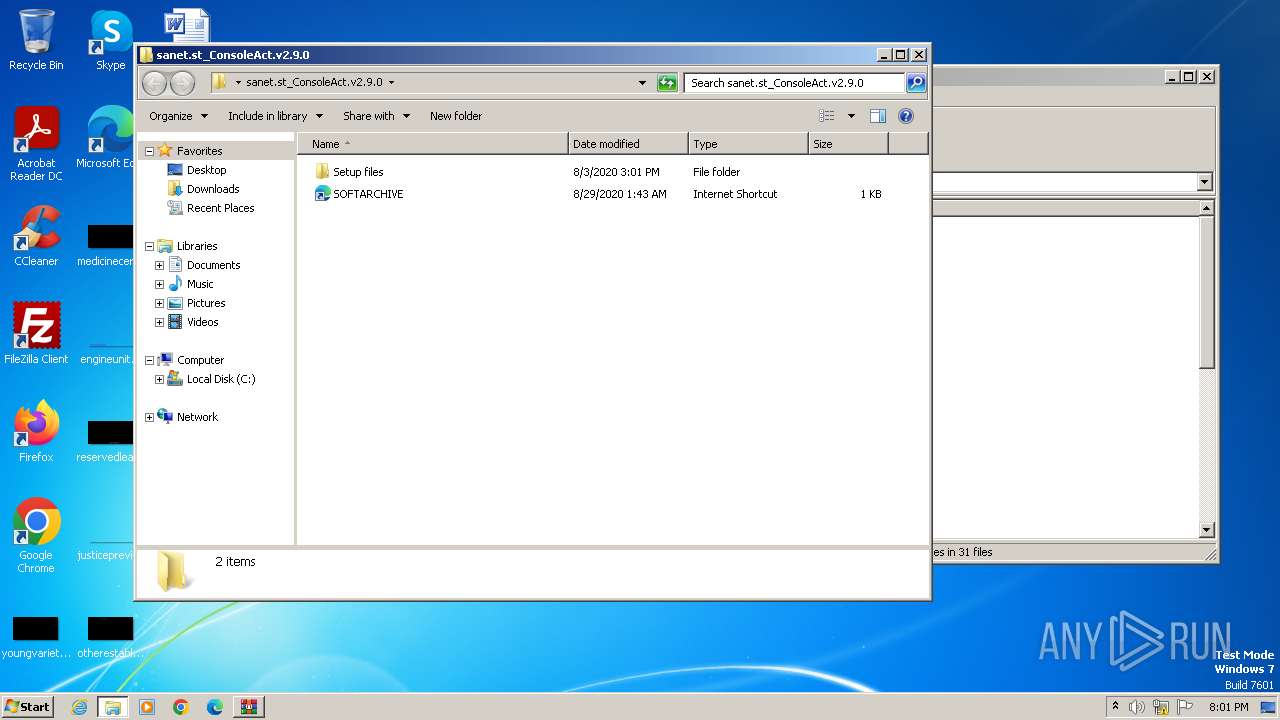
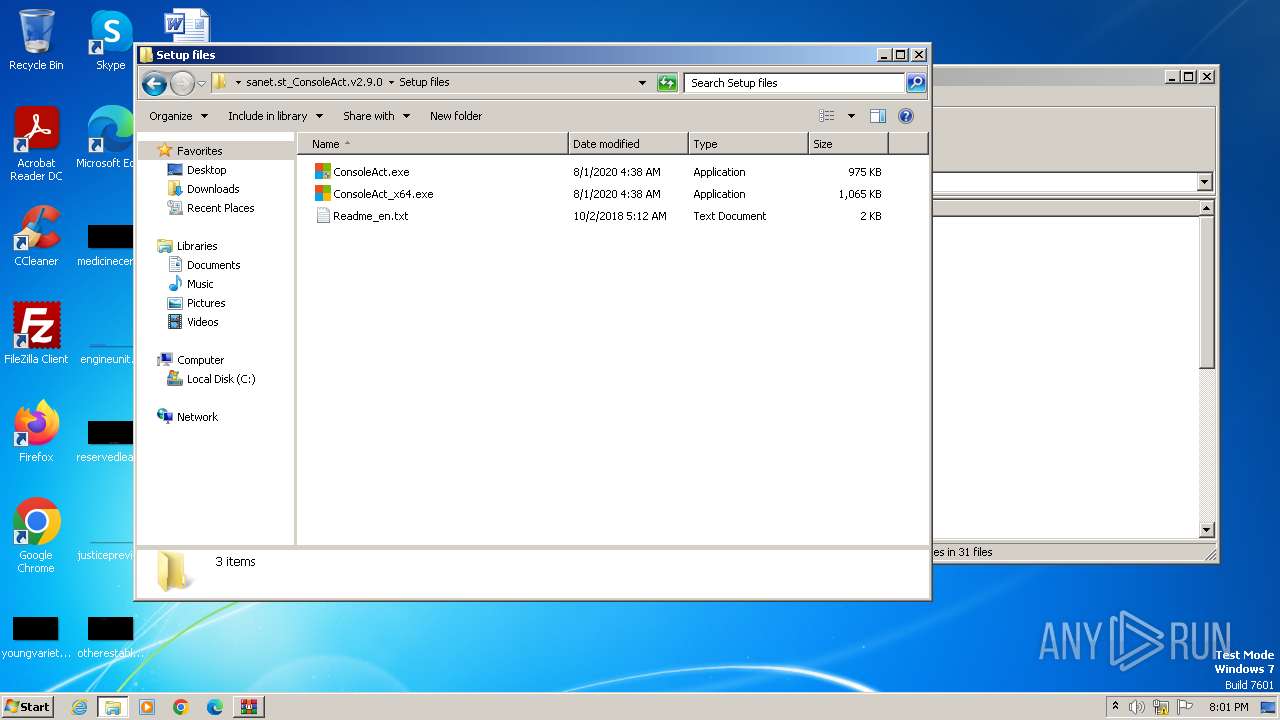
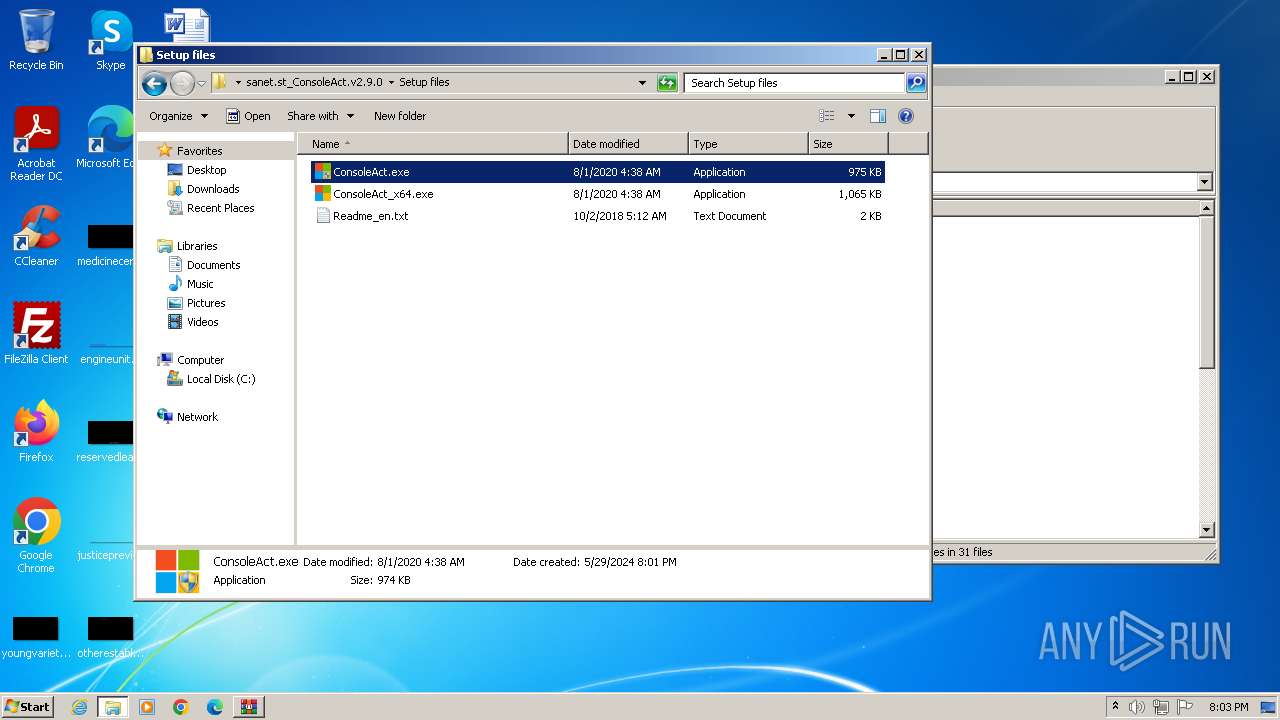
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
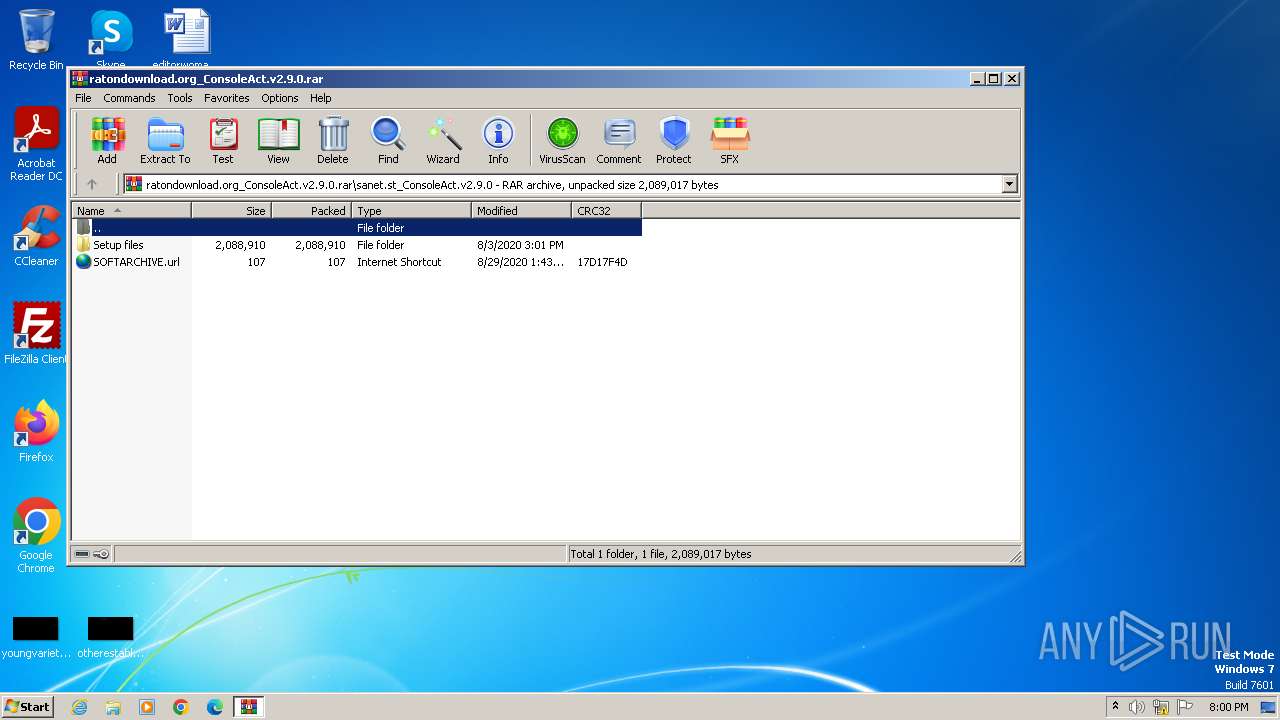
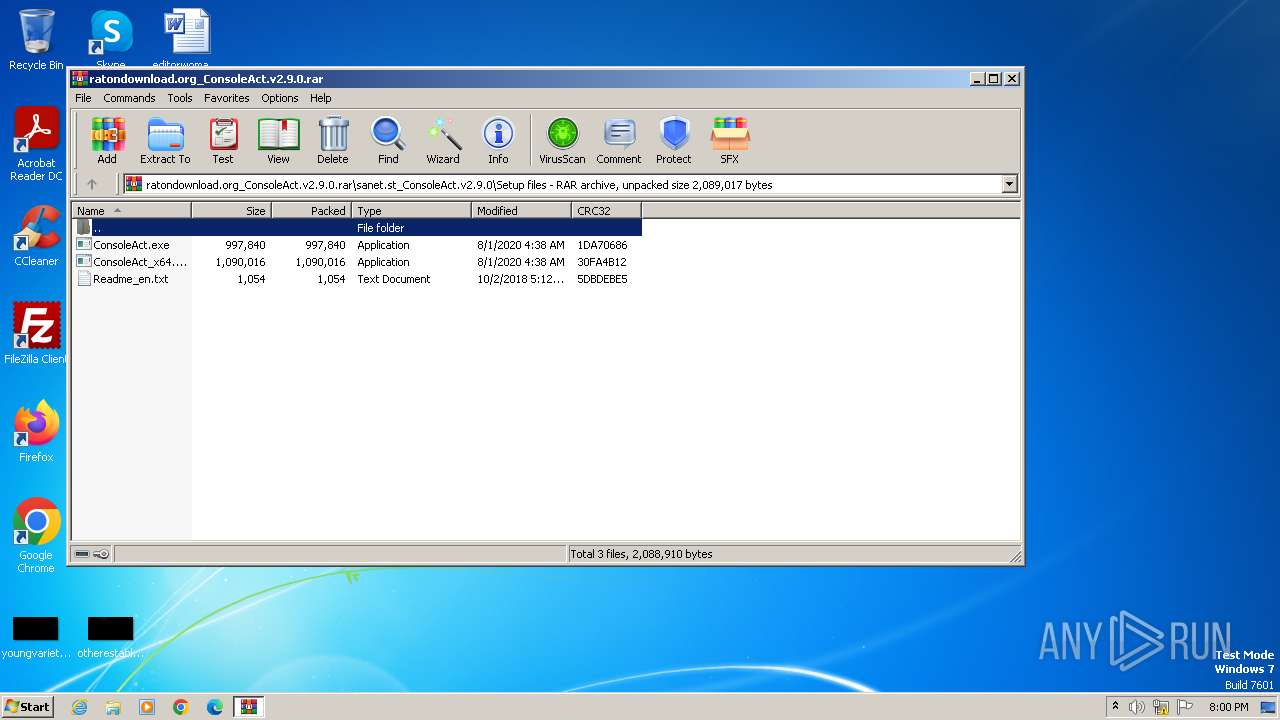
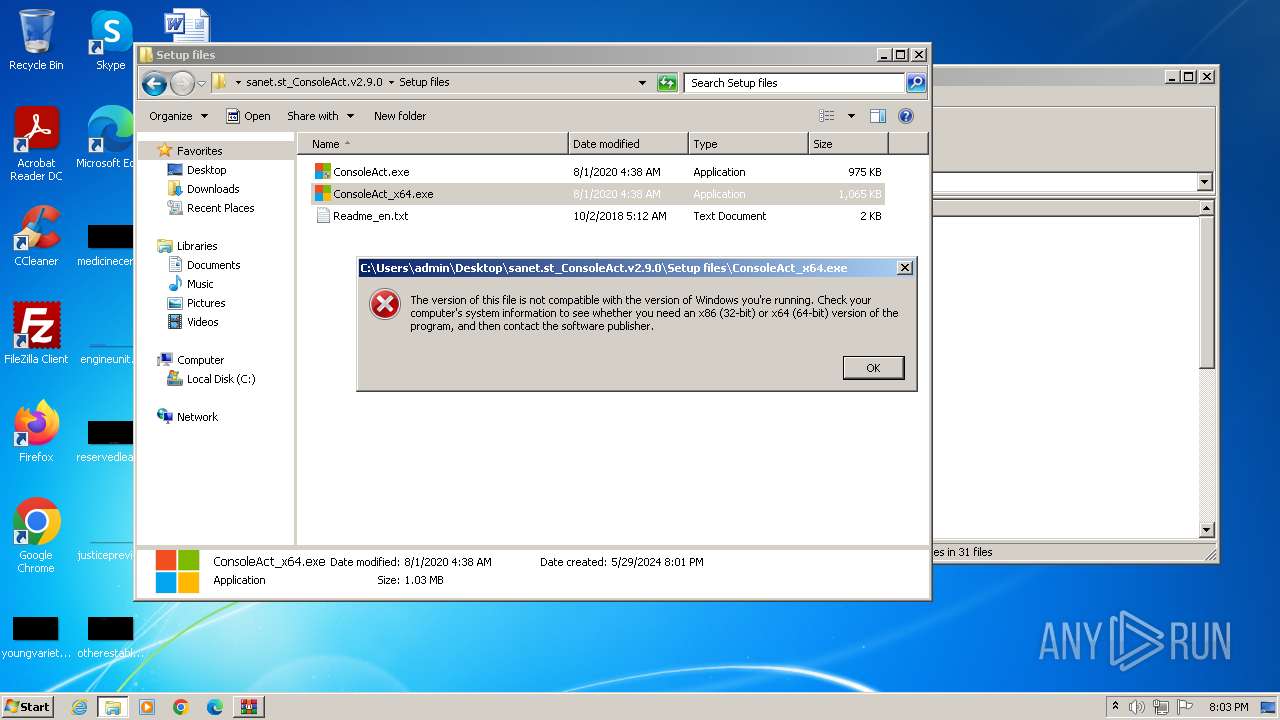
| 3960 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa3960.1965\sanet.st_ConsoleAct.v2.9.0\Setup files\ConsoleAct.exe | executable | |
MD5:BD48478CD0E48380A90C440AFF9764CE | SHA256:0ABD4CB2211EFB1AD57E45C64633D170FA2B4280B598DB034B65945F45F6B111 | |||
| 3960 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa3960.1965\sanet.st_ConsoleAct.v2.9.0\Setup files\Readme_en.txt | text | |
MD5:2DBE0A32D52CF34BD7961E069F8AE91F | SHA256:FBF136CD8DF4F00AE8967E0296F4700F2C7F60754881C1F02594A54548FE9264 | |||
| 3960 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa3960.1965\sanet.st_ConsoleAct.v2.9.0\Setup files\ConsoleAct_x64.exe | executable | |
MD5:B7B3BEE624F57C37BD75F7F799C1A784 | SHA256:CFC2ED90F980FC038124865D3AE990C978EE7CB16B995E603D54B4584A70BFD2 | |||
| 3960 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\sanet.st_ConsoleAct.v2.9.0\Setup files\ConsoleAct_x64.exe | executable | |
MD5:B7B3BEE624F57C37BD75F7F799C1A784 | SHA256:CFC2ED90F980FC038124865D3AE990C978EE7CB16B995E603D54B4584A70BFD2 | |||
| 3960 | WinRAR.exe | C:\Users\admin\Desktop\sanet.st_ConsoleAct.v2.9.0\Setup files\ConsoleAct_x64.exe | executable | |
MD5:B7B3BEE624F57C37BD75F7F799C1A784 | SHA256:CFC2ED90F980FC038124865D3AE990C978EE7CB16B995E603D54B4584A70BFD2 | |||
| 3960 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa3960.1965\sanet.st_ConsoleAct.v2.9.0\SOFTARCHIVE.url | url | |
MD5:574E091A47298617DA20176CD382F913 | SHA256:58A6CFFECB6D07E964738F6F71A83550B4373F1BC9B1F43FEC1BD8BB339D630C | |||
| 3960 | WinRAR.exe | C:\Users\admin\Desktop\sanet.st_ConsoleAct.v2.9.0\SOFTARCHIVE.url | url | |
MD5:574E091A47298617DA20176CD382F913 | SHA256:58A6CFFECB6D07E964738F6F71A83550B4373F1BC9B1F43FEC1BD8BB339D630C | |||
| 3960 | WinRAR.exe | C:\Users\admin\Desktop\sanet.st_ConsoleAct.v2.9.0\Setup files\Readme_en.txt | text | |
MD5:2DBE0A32D52CF34BD7961E069F8AE91F | SHA256:FBF136CD8DF4F00AE8967E0296F4700F2C7F60754881C1F02594A54548FE9264 | |||
| 3960 | WinRAR.exe | C:\Users\admin\Desktop\sanet.st_ConsoleAct.v2.9.0\Setup files\ConsoleAct.exe | executable | |
MD5:BD48478CD0E48380A90C440AFF9764CE | SHA256:0ABD4CB2211EFB1AD57E45C64633D170FA2B4280B598DB034B65945F45F6B111 | |||
| 3960 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\sanet.st_ConsoleAct.v2.9.0\Setup files\ConsoleAct.exe | executable | |
MD5:BD48478CD0E48380A90C440AFF9764CE | SHA256:0ABD4CB2211EFB1AD57E45C64633D170FA2B4280B598DB034B65945F45F6B111 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
6
DNS requests
2
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2404 | WmiPrvSE.exe | POST | 302 | 184.28.89.167:80 | http://go.microsoft.com/fwlink/?LinkID=88339 | US | — | — | unknown |
2404 | WmiPrvSE.exe | POST | 302 | 184.28.89.167:80 | http://go.microsoft.com/fwlink/?LinkID=88340 | US | — | — | unknown |
2404 | WmiPrvSE.exe | POST | 302 | 184.28.89.167:80 | http://go.microsoft.com/fwlink/?LinkID=88341 | US | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 224.0.0.252:5355 | — | — | — | unknown |
1088 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
2404 | WmiPrvSE.exe | 184.28.89.167:80 | go.microsoft.com | AKAMAI-AS | US | unknown |
2404 | WmiPrvSE.exe | 40.91.76.224:443 | activation.sls.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
go.microsoft.com |
| whitelisted |
activation.sls.microsoft.com |
| whitelisted |