| File name: | Usb.exe |
| Full analysis: | https://app.any.run/tasks/2476391d-8946-49de-b789-248190c6b9f7 |
| Verdict: | Malicious activity |
| Analysis date: | December 03, 2025, 19:56:31 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows, 3 sections |
| MD5: | BBC4D43A4CAF11DA5AD27C2204E5506C |
| SHA1: | 36041B2D11BAA10DCE1D34EB016E7BB68F62AB94 |
| SHA256: | CE07940B60E29E1B3D8215A953FAF4A9A0F625E78A714A1318838F4057732399 |
| SSDEEP: | 98304:7oQe4HWYgmCcCEdMTkQSz969wwmqNh0cLOIIAhLNEpjc+KBCZA5fWxCWSzDK9/6j:Vaw2aT+gUBu0M |
MALICIOUS
Changes the autorun value in the registry
- Usb.exe (PID: 7312)
- EBI.exe (PID: 7704)
SUSPICIOUS
Reads security settings of Internet Explorer
- Usb.exe (PID: 7312)
- not.exe (PID: 7656)
The process creates files with name similar to system file names
- Usb.exe (PID: 7312)
Executable content was dropped or overwritten
- Usb.exe (PID: 7312)
- not.exe (PID: 7656)
Reads the date of Windows installation
- Usb.exe (PID: 7312)
Starts itself from another location
- Usb.exe (PID: 7312)
Application launched itself
- not.exe (PID: 7580)
There is functionality for taking screenshot (YARA)
- EBI.exe (PID: 7704)
Connects to SMTP port
- EBI.exe (PID: 7704)
INFO
Checks supported languages
- Usb.exe (PID: 7312)
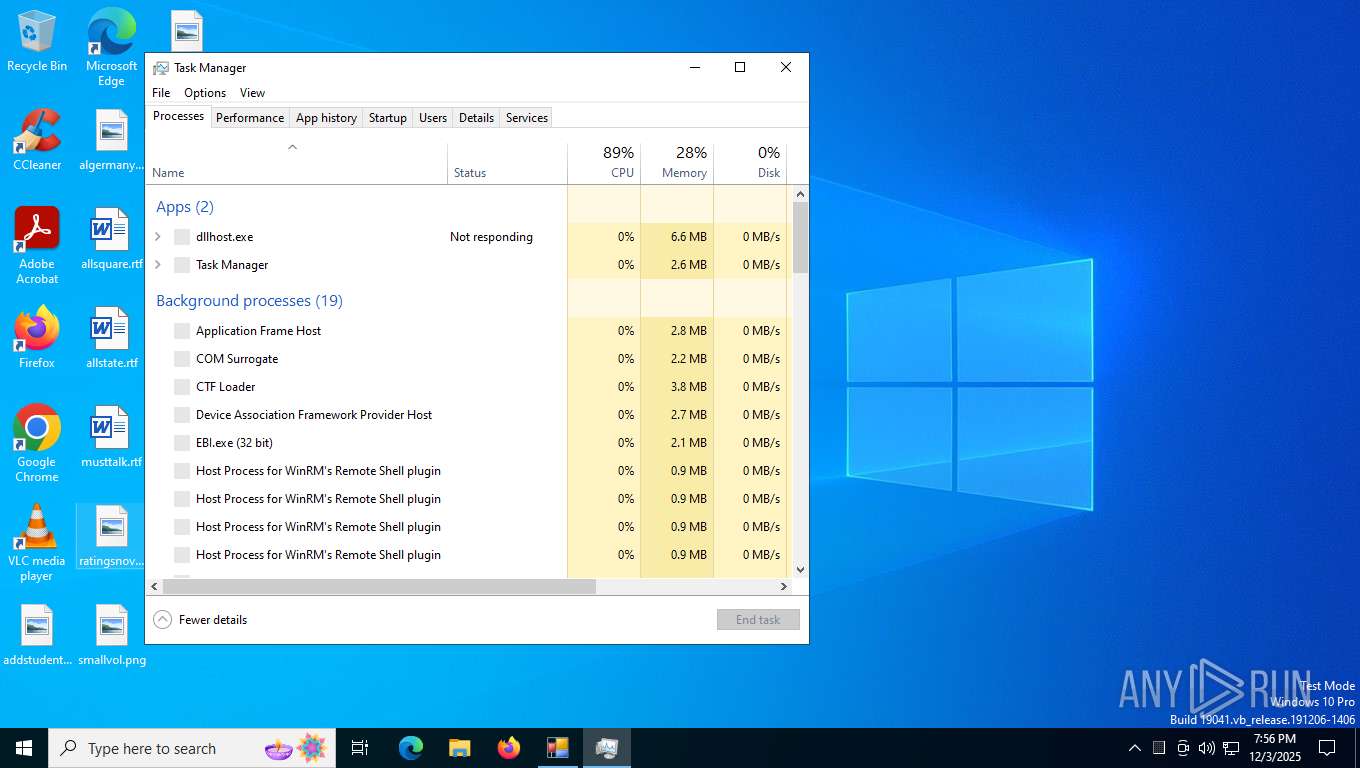
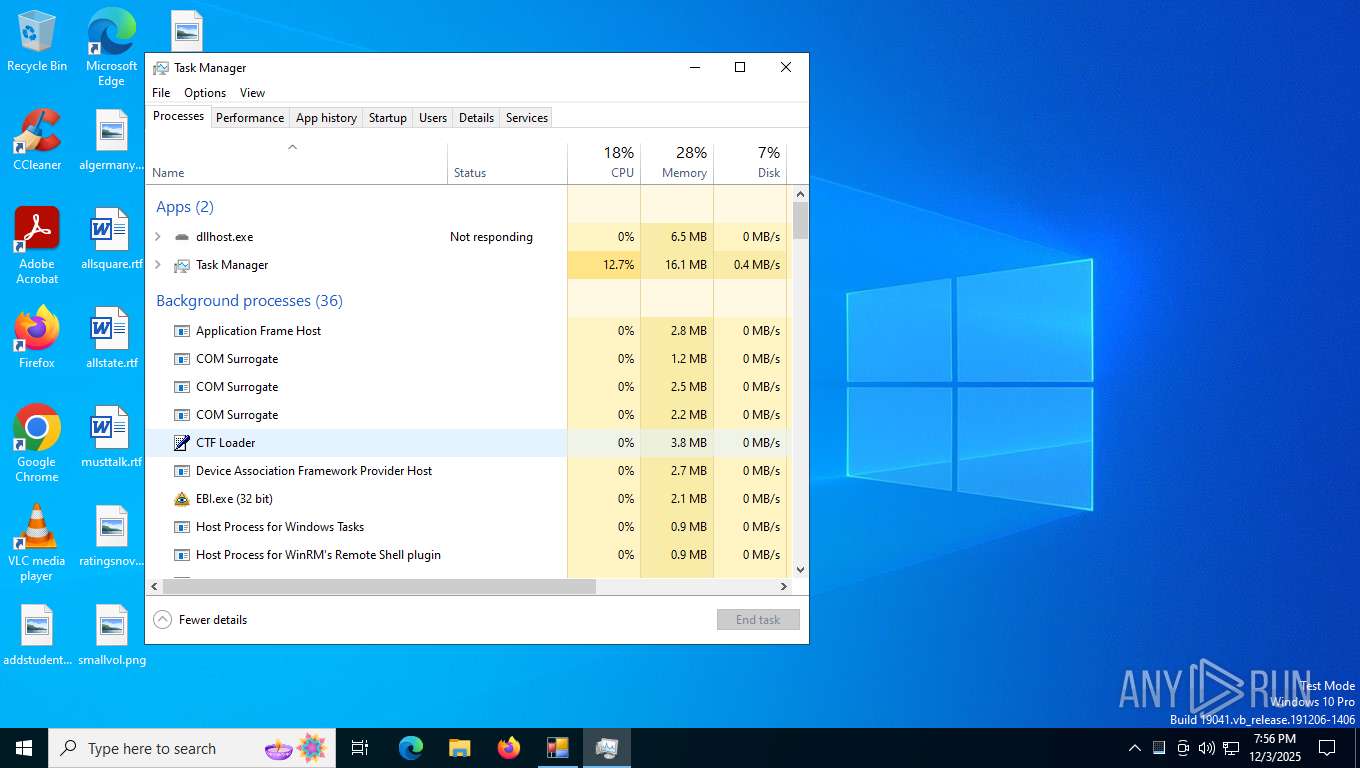
- dllhost.exe (PID: 7368)
- not.exe (PID: 7580)
- not.exe (PID: 7656)
- EBI.exe (PID: 7704)
Launching a file from a Registry key
- Usb.exe (PID: 7312)
- EBI.exe (PID: 7704)
Reads the computer name
- Usb.exe (PID: 7312)
- dllhost.exe (PID: 7368)
- not.exe (PID: 7656)
- EBI.exe (PID: 7704)
Process checks computer location settings
- Usb.exe (PID: 7312)
- not.exe (PID: 7656)
Creates files or folders in the user directory
- Usb.exe (PID: 7312)
- not.exe (PID: 7656)
- EBI.exe (PID: 7704)
Reads the machine GUID from the registry
- dllhost.exe (PID: 7368)
Reads security settings of Internet Explorer
- Taskmgr.exe (PID: 7916)
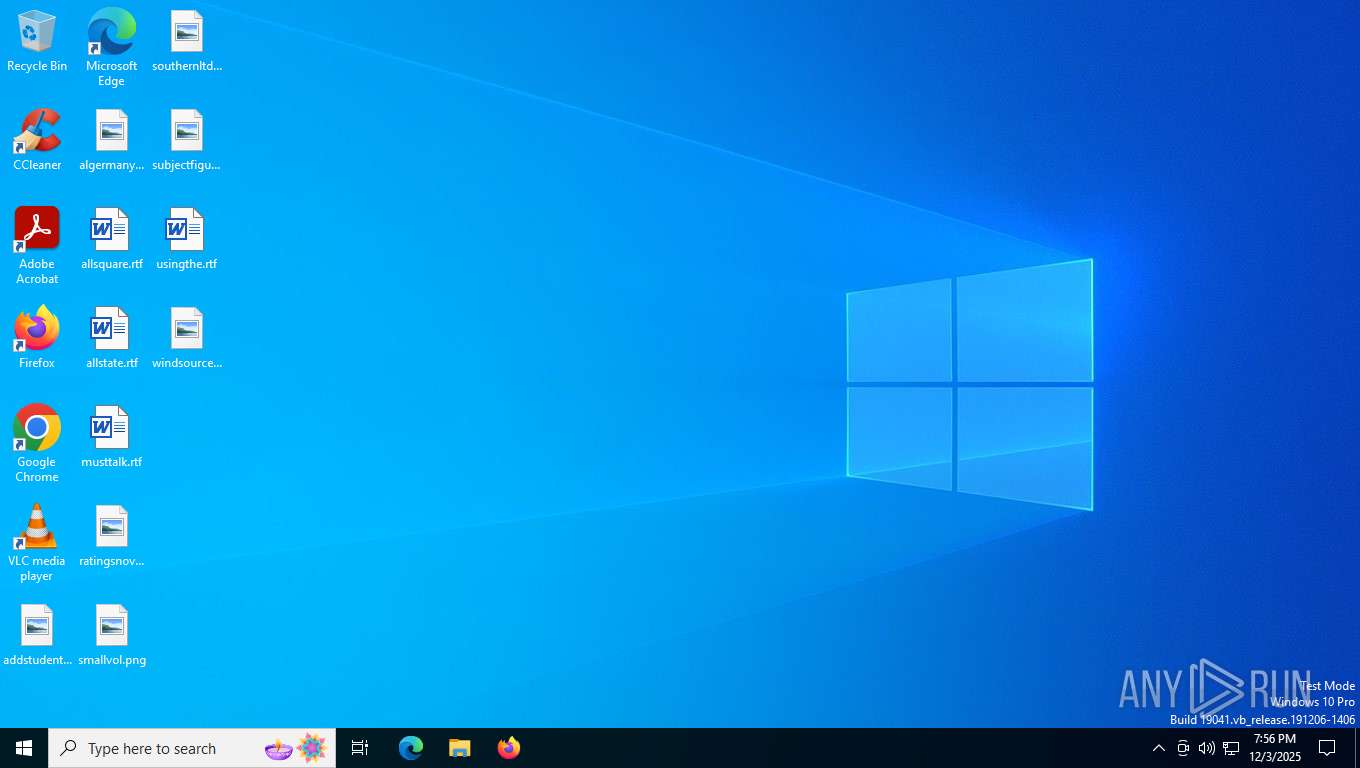
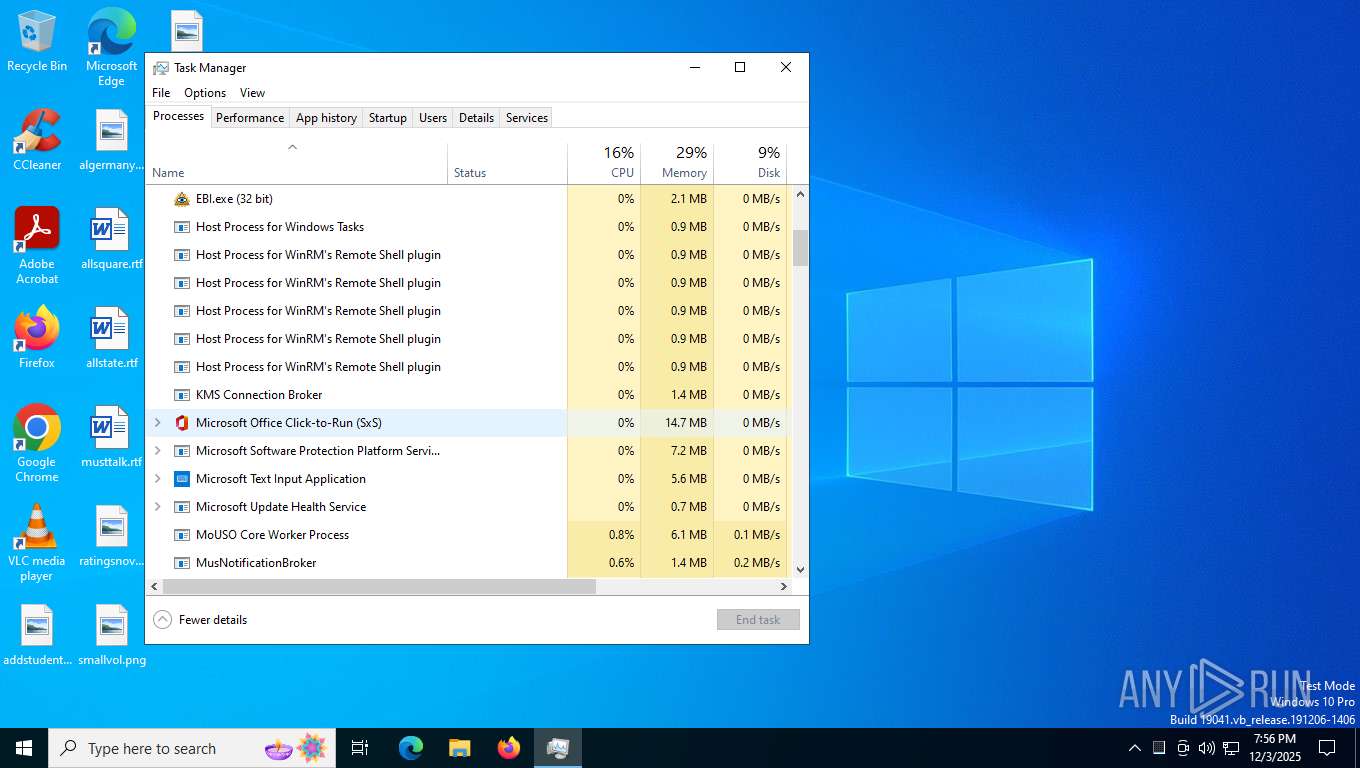
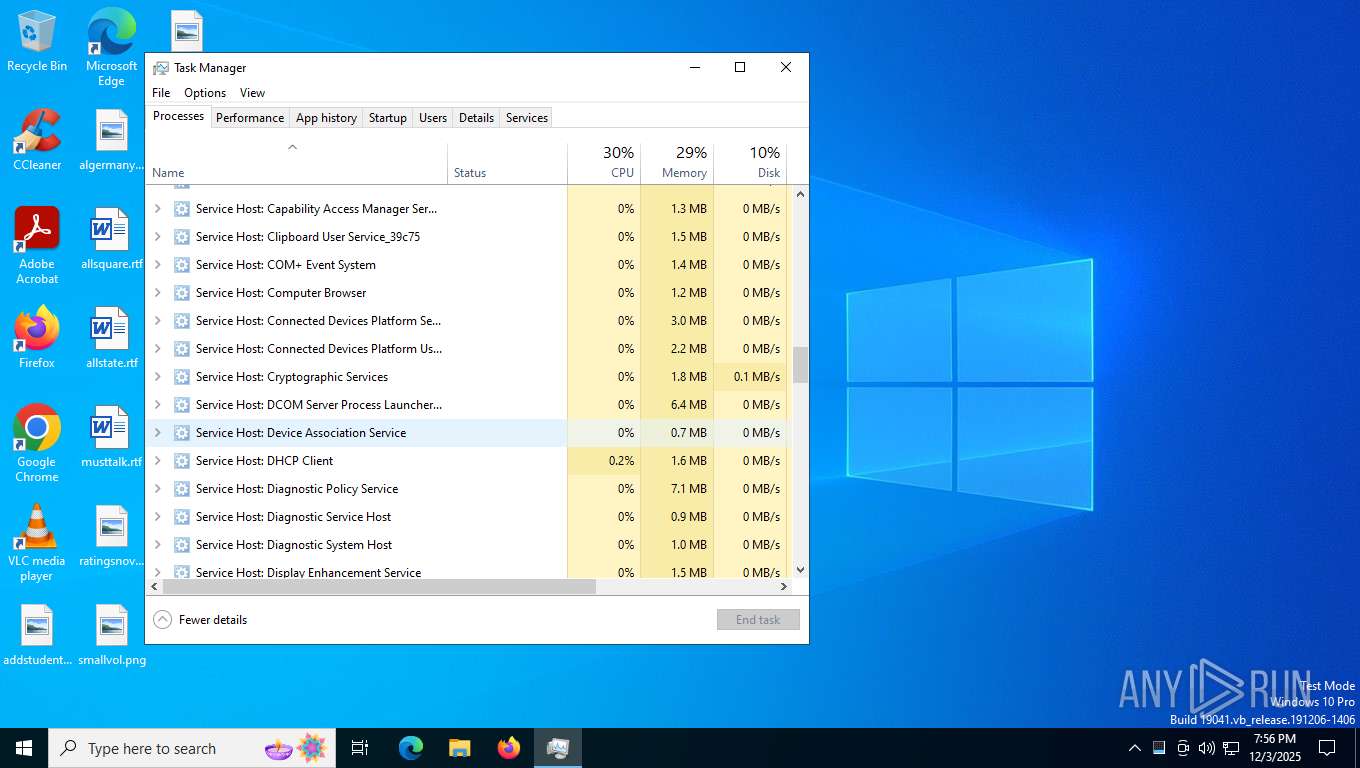
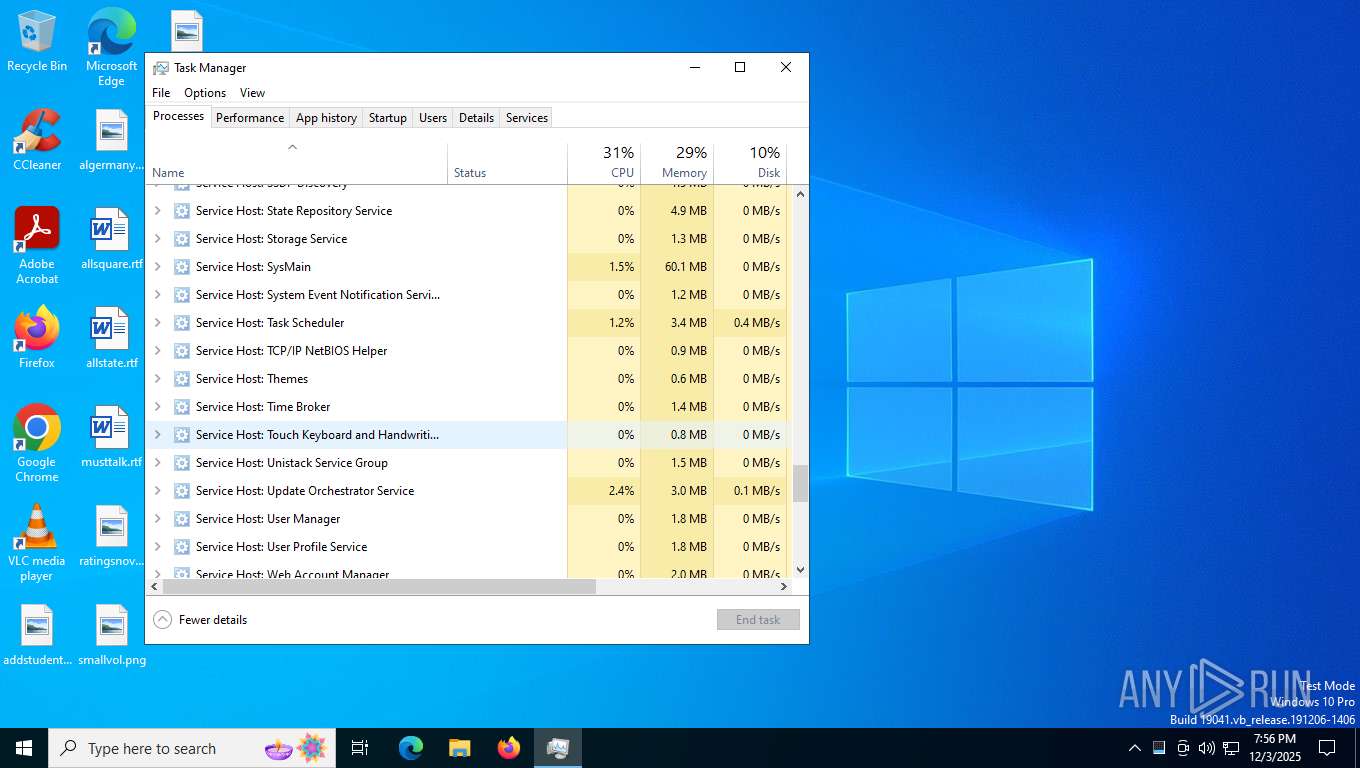
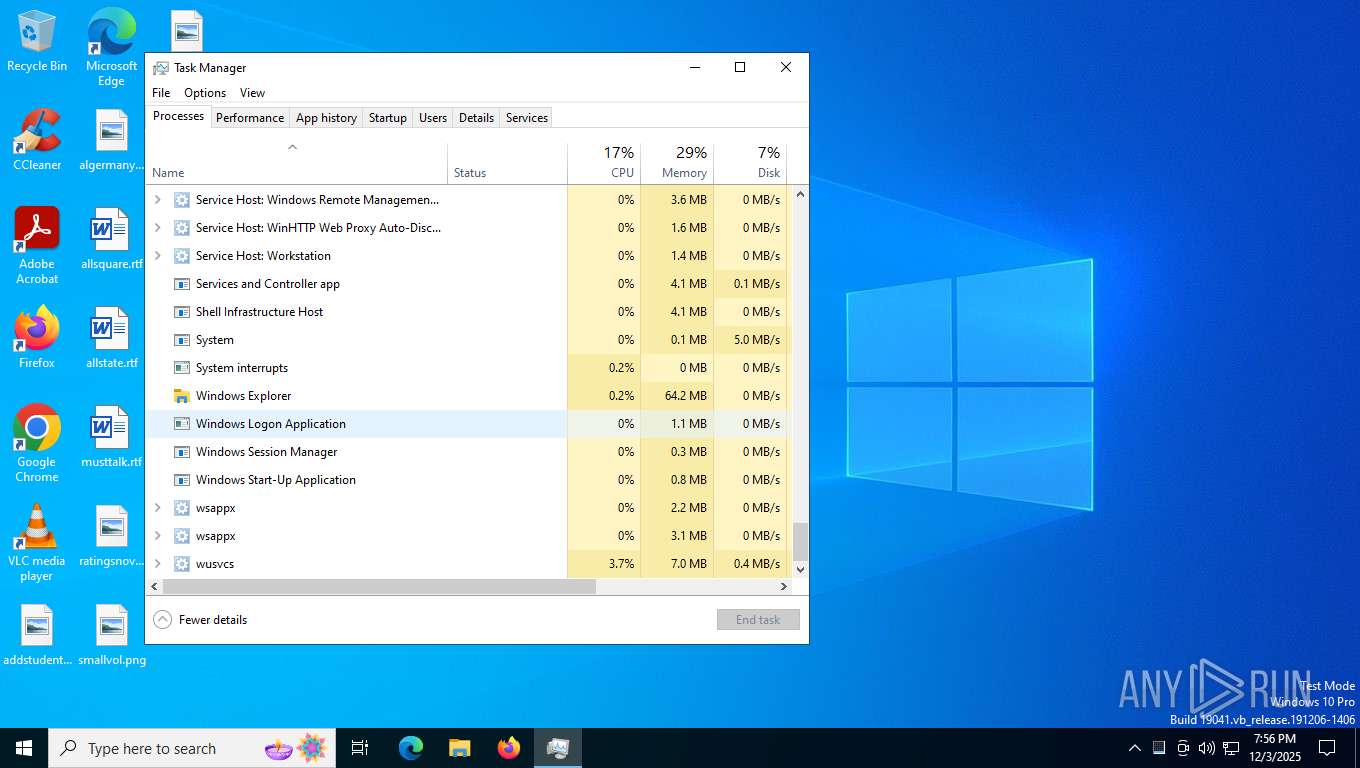
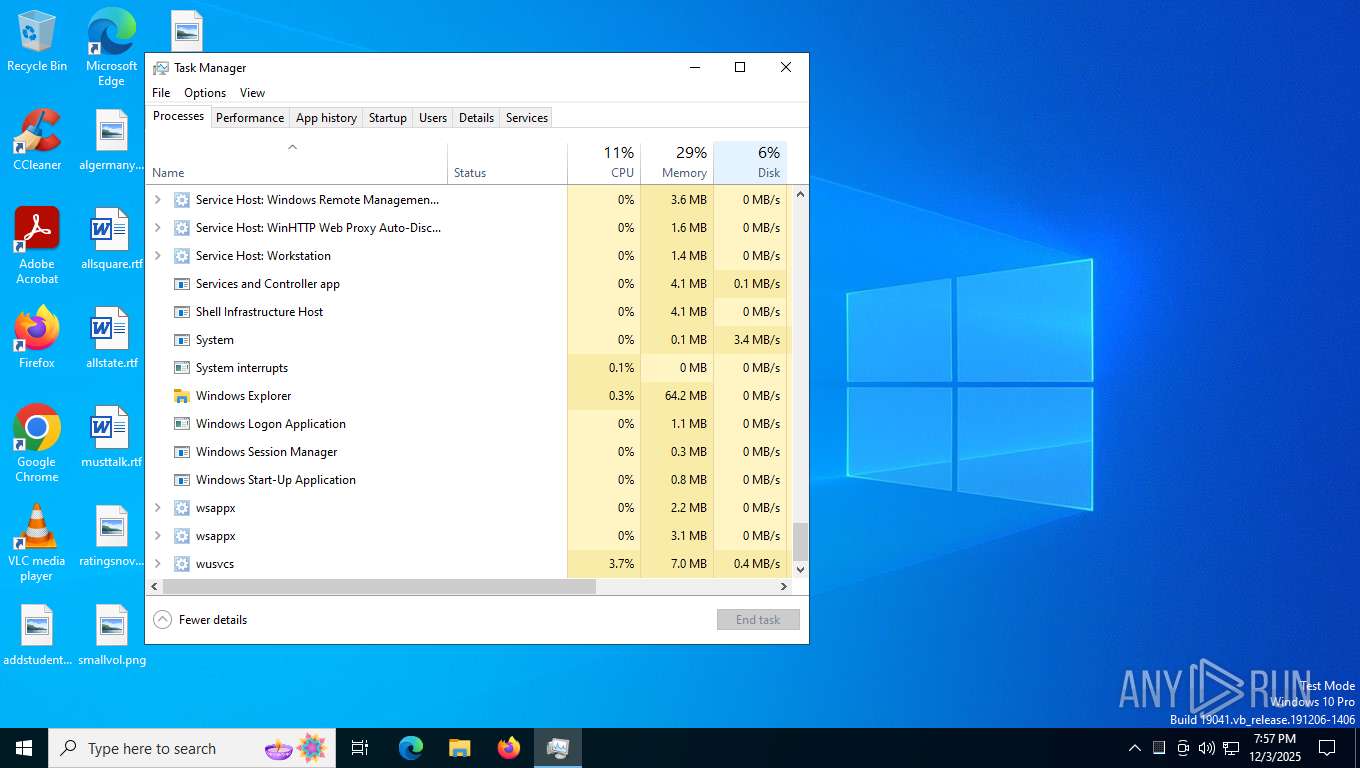
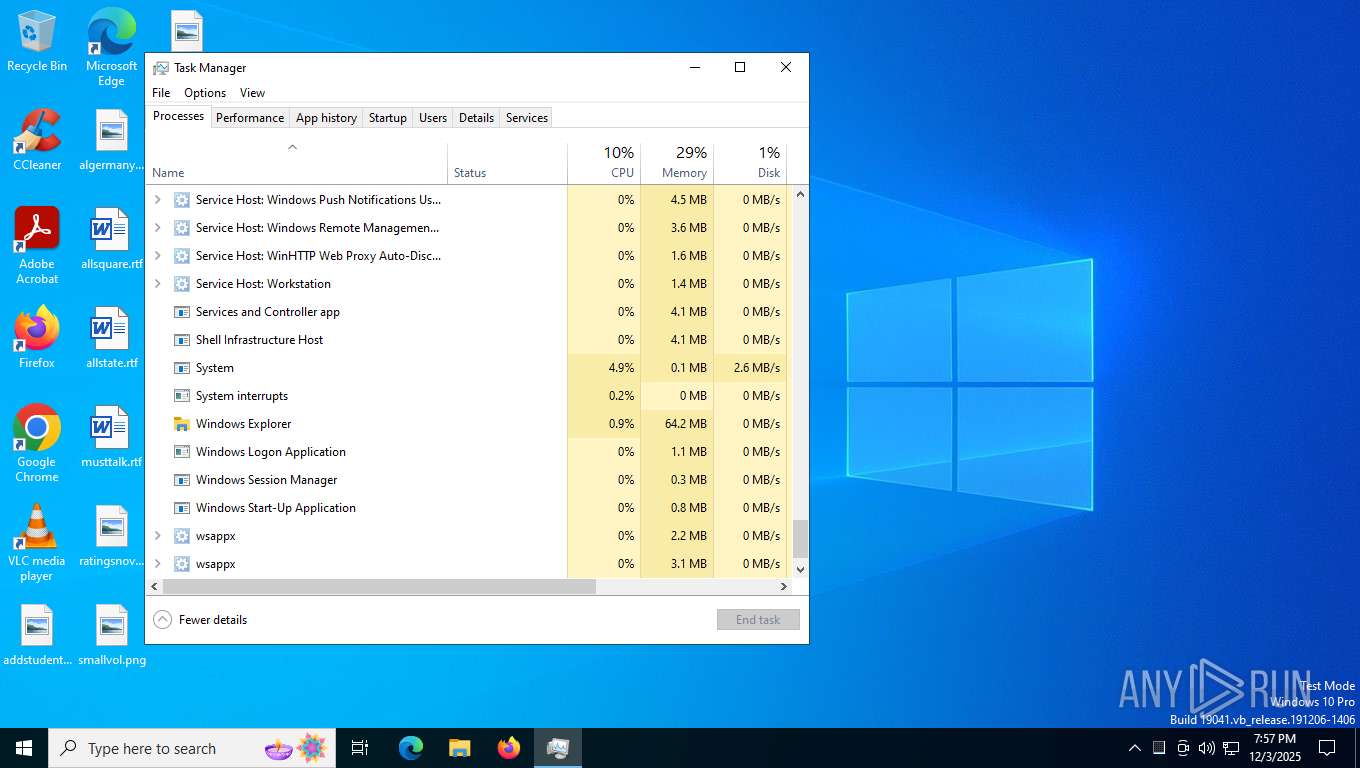
Manual execution by a user
- Taskmgr.exe (PID: 7916)
- Taskmgr.exe (PID: 7868)
UPX packer has been detected
- dllhost.exe (PID: 7368)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (51.6) |
|---|---|---|
| .exe | | | UPX compressed Win32 Executable (19) |
| .exe | | | Win32 EXE Yoda's Crypter (18.7) |
| .dll | | | Win32 Dynamic Link Library (generic) (4.6) |
| .exe | | | Win32 Executable (generic) (3.1) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2017:02:14 16:42:40+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 11 |
| CodeSize: | 6062592 |
| InitializedDataSize: | 101888 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x5ca08e |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.0.0.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| FileDescription: | |
| FileVersion: | 0.0.0.0 |
| InternalName: | scvhst.exe |
| LegalCopyright: | |
| OriginalFileName: | scvhst.exe |
| ProductVersion: | 0.0.0.0 |
| AssemblyVersion: | 0.0.0.0 |
Total processes
153
Monitored processes
9
Malicious processes
1
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2156 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7312 | "C:\Users\admin\AppData\Local\Temp\Usb.exe" | C:\Users\admin\AppData\Local\Temp\Usb.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Exit code: 4294967295 Version: 0.0.0.0 Modules
| |||||||||||||||
| 7368 | "C:\Users\admin\AppData\Roaming\dllhost.exe" | C:\Users\admin\AppData\Roaming\dllhost.exe | — | Usb.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Version: 0.0.0.0 Modules
| |||||||||||||||
| 7404 | "C:\Users\admin\AppData\Roaming\not.exe" | C:\Users\admin\AppData\Roaming\not.exe | — | Usb.exe | |||||||||||
User: admin Company: CyberGhost S.R.L. Integrity Level: MEDIUM Description: CyberGhost Exit code: 3221226540 Version: 6.0.3.2124 Modules
| |||||||||||||||
| 7580 | "C:\Users\admin\AppData\Roaming\not.exe" | C:\Users\admin\AppData\Roaming\not.exe | Usb.exe | ||||||||||||
User: admin Company: CyberGhost S.R.L. Integrity Level: HIGH Description: CyberGhost Exit code: 0 Version: 6.0.3.2124 Modules
| |||||||||||||||
| 7656 | "C:\Users\admin\AppData\Roaming\not.exe" | C:\Users\admin\AppData\Roaming\not.exe | not.exe | ||||||||||||
User: admin Company: CyberGhost S.R.L. Integrity Level: HIGH Description: CyberGhost Exit code: 0 Version: 6.0.3.2124 Modules
| |||||||||||||||
| 7704 | "C:\Users\admin\AppData\Roaming\SMOAOC\EBI.exe" | C:\Users\admin\AppData\Roaming\SMOAOC\EBI.exe | not.exe | ||||||||||||
User: admin Integrity Level: HIGH Modules
| |||||||||||||||
| 7868 | "C:\WINDOWS\system32\taskmgr.exe" /0 | C:\Windows\System32\Taskmgr.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Task Manager Exit code: 3221226540 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7916 | "C:\WINDOWS\system32\taskmgr.exe" /0 | C:\Windows\System32\Taskmgr.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Task Manager Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
6 352
Read events
6 339
Write events
12
Delete events
1
Modification events
| (PID) Process: | (7312) Usb.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | Windows Reference |
Value: "C:\Users\admin\AppData\Roaming\dllhost.exe" | |||
| (PID) Process: | (7312) Usb.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (7312) Usb.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (7312) Usb.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (7312) Usb.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (7704) EBI.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | EBI Start |
Value: C:\Users\admin\AppData\Roaming\SMOAOC\EBI.exe | |||
| (PID) Process: | (7916) Taskmgr.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\TaskManager |
| Operation: | delete value | Name: | Preferences |
Value: | |||
| (PID) Process: | (7916) Taskmgr.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\TaskManager |
| Operation: | write | Name: | Preferences |
Value: 0D00000060000000600000006800000068000000E3010000DC010000000001000000008000000080D8010080DF010080000100018900000034000000310300008C020000E80300000000000000000000000000000F000000010000000000000058AA2910F67F00000000000000000000000000002E0100001E0000008990000000000000FF00000001015002000000000D0000000000000098AA2910F67F00000000000000000000FFFFFFFF960000001E0000008B900000010000000000000000101001000000000300000000000000B0AA2910F67F00000000000000000000FFFFFFFF780000001E0000008C900000020000000000000001021200000000000400000000000000C8AA2910F67F00000000000000000000FFFFFFFF960000001E0000008D900000030000000000000000011001000000000200000000000000E8AA2910F67F00000000000000000000FFFFFFFF320000001E0000008A90000004000000000000000008200100000000050000000000000000AB2910F67F00000000000000000000FFFFFFFFC80000001E0000008E90000005000000000000000001100100000000060000000000000028AB2910F67F00000000000000000000FFFFFFFF040100001E0000008F90000006000000000000000001100100000000070000000000000050AB2910F67F00000000000000000000FFFFFFFF49000000490000009090000007000000000000000004250000000000080000000000000080AA2910F67F00000000000000000000FFFFFFFF49000000490000009190000008000000000000000004250000000000090000000000000070AB2910F67F00000000000000000000FFFFFFFF490000004900000092900000090000000000000000042508000000000A0000000000000088AB2910F67F00000000000000000000FFFFFFFF4900000049000000939000000A0000000000000000042508000000000B00000000000000A8AB2910F67F00000000000000000000FFFFFFFF490000004900000039A000000B0000000000000000042509000000001C00000000000000C8AB2910F67F00000000000000000000FFFFFFFFC8000000490000003AA000000C0000000000000000011009000000001D00000000000000F0AB2910F67F00000000000000000000FFFFFFFF64000000490000004CA000000D0000000000000000021508000000001E0000000000000010AC2910F67F00000000000000000000FFFFFFFF64000000490000004DA000000E000000000000000002150800000000030000000A000000010000000000000058AA2910F67F0000000000000000000000000000D70000001E0000008990000000000000FF00000001015002000000000400000000000000C8AA2910F67F0000000000000000000001000000960000001E0000008D900000010000000000000001011000000000000300000000000000B0AA2910F67F00000000000000000000FFFFFFFF640000001E0000008C900000020000000000000000021000000000000C0000000000000040AC2910F67F0000000000000000000003000000640000001E00000094900000030000000000000001021000000000000D0000000000000068AC2910F67F00000000000000000000FFFFFFFF640000001E00000095900000040000000000000000011001000000000E0000000000000090AC2910F67F0000000000000000000005000000320000001E00000096900000050000000000000001042001000000000F00000000000000B8AC2910F67F0000000000000000000006000000320000001E00000097900000060000000000000001042001000000001000000000000000D8AC2910F67F0000000000000000000007000000460000001E00000098900000070000000000000001011001000000001100000000000000F8AC2910F67F00000000000000000000FFFFFFFF640000001E0000009990000008000000000000000001100100000000060000000000000028AB2910F67F0000000000000000000009000000040100001E0000008F9000000900000000000000010110010000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000040000000B000000010000000000000058AA2910F67F0000000000000000000000000000D70000001E0000009E90000000000000FF0000000101500200000000120000000000000020AD2910F67F00000000000000000000FFFFFFFF2D0000001E0000009B90000001000000000000000004200100000000140000000000000040AD2910F67F00000000000000000000FFFFFFFF640000001E0000009D90000002000000000000000001100100000000130000000000000068AD2910F67F00000000000000000000FFFFFFFF640000001E0000009C900000030000000000000000011001000000000300000000000000B0AA2910F67F00000000000000000000FFFFFFFF640000001E0000008C90000004000000000000000102100000000000070000000000000050AB2910F67F000000000000000000000500000049000000490000009090000005000000000000000104210000000000080000000000000080AA2910F67F000000000000000000000600000049000000490000009190000006000000000000000104210000000000090000000000000070AB2910F67F0000000000000000000007000000490000004900000092900000070000000000000001042108000000000A0000000000000088AB2910F67F0000000000000000000008000000490000004900000093900000080000000000000001042108000000000B00000000000000A8AB2910F67F0000000000000000000009000000490000004900000039A00000090000000000000001042109000000001C00000000000000C8AB2910F67F000000000000000000000A00000064000000490000003AA000000A00000000000000000110090000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000200000008000000010000000000000058AA2910F67F0000000000000000000000000000C60000001E000000B090000000000000FF0000000101500200000000150000000000000088AD2910F67F00000000000000000000FFFFFFFF6B0000001E000000B1900000010000000000000000042500000000001600000000000000B8AD2910F67F00000000000000000000FFFFFFFF6B0000001E000000B2900000020000000000000000042500000000001800000000000000E0AD2910F67F00000000000000000000FFFFFFFF6B0000001E000000B490000003000000000000000004250000000000170000000000000008AE2910F67F00000000000000000000FFFFFFFF6B0000001E000000B390000004000000000000000004250000000000190000000000000040AE2910F67F00000000000000000000FFFFFFFFA00000001E000000B5900000050000000000000000042001000000001A0000000000000070AE2910F67F00000000000000000000FFFFFFFF7D0000001E000000B6900000060000000000000000042001000000001B00000000000000A0AE2910F67F00000000000000000000FFFFFFFF7D0000001E000000B790000007000000000000000004200100000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000010000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000DA00000000000000000000000000000000000000000000009D200000200000009100000064000000320000006400000050000000320000003200000028000000500000003C0000005000000050000000320000005000000050000000500000005000000050000000500000002800000050000000230000002300000023000000230000005000000050000000500000003200000032000000320000007800000078000000500000003C00000050000000500000009700000032000000780000003200000050000000500000005000000050000000000000000100000002000000030000000400000005000000060000000700000008000000090000000A0000000B0000000C0000000D0000000E0000000F000000100000001100000012000000130000001400000015000000160000001700000018000000190000001A0000001B0000001C0000001D0000001E0000001F000000200000002100000022000000230000002400000025000000260000002700000028000000290000002A0000002B0000002C00000000000000000000001F00000000000000B400000032000000D8000000640000006400000000000000000000000000000000000000000000000000000000000000000000000000000000000000DA000000000000000000000000000000000000009D200000200000009100000064000000320000009700000050000000320000003200000028000000500000003C000000500000005000000032000000500000005000000050000000500000005000000050000000500000002800000050000000230000002300000023000000230000005000000050000000500000003200000032000000320000007800000078000000500000003C0000005000000064000000780000003200000078000000780000003200000050000000500000005000000050000000C8000000000000000100000002000000030000000400000005000000060000000700000008000000090000000A0000000B0000000C0000000D0000000E0000000F000000100000001100000012000000130000001400000015000000160000001700000018000000190000001A0000001B0000001C0000001D0000001E0000001F000000200000002100000022000000230000002400000025000000260000002700000028000000290000002A0000002B0000002C0000002D0000002E0000002F00000000000000000000001F00000000000000B400000032000000D8000000640000006400000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000100000002000000030000000400000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000001000000000000000000000000000000 | |||
Executable files
5
Suspicious files
3
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7312 | Usb.exe | C:\Users\admin\AppData\Roaming\not.exe | executable | |
MD5:F3A80B0CC2F6550A23A403E9DF3BB37E | SHA256:D2DB9E65E782E909F5E26079206B6A0EC030DFB99B124022794A6A9610CEB15F | |||
| 7656 | not.exe | C:\Users\admin\AppData\Roaming\SMOAOC\EBI.00 | binary | |
MD5:DE81A26E53A3E8C26B94D5908311A6CB | SHA256:585BC565FE9C29E6A8307D4C0F018B8F80BF06898C592A65443A107011CB1C6E | |||
| 7704 | EBI.exe | C:\Users\admin\AppData\Roaming\URR\App_2025-12-03_19-56-38.html | html | |
MD5:00C35D0F74B138C03BAFB3976447AAD3 | SHA256:9A89A878B6EDDFC3DE3D8FA10B7D67506A2589346878CB1DE8B919F40328A4D0 | |||
| 7916 | Taskmgr.exe | C:\Users\admin\AppData\Local\D3DSCache\3534848bb9f4cb71\F4EB2D6C-ED2B-4BDD-AD9D-F913287E6768.lock | text | |
MD5:F49655F856ACB8884CC0ACE29216F511 | SHA256:7852FCE59C67DDF1D6B8B997EAA1ADFAC004A9F3A91C37295DE9223674011FBA | |||
| 7312 | Usb.exe | C:\Users\admin\AppData\Roaming\dllhost.exe | executable | |
MD5:BBC4D43A4CAF11DA5AD27C2204E5506C | SHA256:CE07940B60E29E1B3D8215A953FAF4A9A0F625E78A714A1318838F4057732399 | |||
| 7656 | not.exe | C:\Users\admin\AppData\Roaming\SMOAOC\EBI.02 | executable | |
MD5:3E3864C031D403C14AF56681D974AC39 | SHA256:64036312065535D9C80326EFA222F26F339C8ECD4DF8011DFA87B585F6488A6D | |||
| 7704 | EBI.exe | C:\Users\admin\AppData\Roaming\URR\EBI.004 | binary | |
MD5:9591F179E3DB4E495D134B96317B4E76 | SHA256:79950624C217322F17808DB122FA206365DF9356BF592B20FE9548D680E3D445 | |||
| 7656 | not.exe | C:\Users\admin\AppData\Roaming\SMOAOC\EBI.exe | executable | |
MD5:1D32291ECFD28F36EEB427E5055AB319 | SHA256:6C62358B47D09DA172053B103270EAB1A5A5377BAC7D8DC95ADEA61263B9830F | |||
| 7656 | not.exe | C:\Users\admin\AppData\Roaming\SMOAOC\EBI.01 | executable | |
MD5:687F7D400B10D23D2CC9CE01502F850B | SHA256:70F71C39799C63D868BDE460AB8AA81827307817B1ACF3C61A5F5652E0E40DC8 | |||
| 7704 | EBI.exe | C:\Users\admin\AppData\Roaming\URR\2025-12-03_19-56-38.004 | binary | |
MD5:26361949A81233CD021AFBB6E32287CE | SHA256:11F4384A4E325798DF726457135FF14E48EF1483FB811F9CF625C7BC4C3DBBB8 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
10
TCP/UDP connections
29
DNS requests
17
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3500 | svchost.exe | GET | 200 | 172.66.2.5:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5596 | MoUsoCoreWorker.exe | GET | 200 | 23.216.77.22:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
7272 | SIHClient.exe | GET | 200 | 23.52.181.212:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7272 | SIHClient.exe | GET | 200 | 23.52.181.212:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
7272 | SIHClient.exe | GET | 200 | 23.52.181.212:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.3.crl | unknown | — | — | whitelisted |
7272 | SIHClient.exe | GET | 200 | 23.216.77.28:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut_2010-06-23.crl | unknown | — | — | whitelisted |
7272 | SIHClient.exe | GET | 200 | 23.52.181.212:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Time-Stamp%20PCA%202010(1).crl | unknown | — | — | whitelisted |
7272 | SIHClient.exe | GET | 200 | 23.52.181.212:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.2.crl | unknown | — | — | whitelisted |
7272 | SIHClient.exe | GET | 200 | 23.52.181.212:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Signing%20CA%202.2.crl | unknown | — | — | whitelisted |
7272 | SIHClient.exe | GET | 200 | 23.52.181.212:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Signing%20CA%202.3.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
224 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
3500 | svchost.exe | 20.190.160.3:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5596 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
— | — | 92.123.104.12:443 | www.bing.com | AKAMAI-ASN1 | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
3500 | svchost.exe | 40.126.32.68:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
3500 | svchost.exe | 172.66.2.5:80 | ocsp.digicert.com | CLOUDFLARENET | US | whitelisted |
5596 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5596 | MoUsoCoreWorker.exe | 23.216.77.22:80 | crl.microsoft.com | AKAMAI-ASN1 | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |