| File name: | bsod.exe |
| Full analysis: | https://app.any.run/tasks/71ca8eba-8dbc-41bb-8c96-7ac0eff84431 |
| Verdict: | Malicious activity |
| Analysis date: | April 30, 2024, 15:11:20 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | 433FCB7926108F39141933654EEC59ED |
| SHA1: | 91AFED3A7185CBEEFC9F2E4B75B483F84C2093C2 |
| SHA256: | CE06A2ECE6DC4A4B0BF8A86381E590C81C572FF94460A59EA37E3EA54347A900 |
| SSDEEP: | 6144:JuDbE0WdeDH3gA2N67TTfvbScShx4DTjH0gzi5gnuDS4gfLBffGCtYGsdUcMgjTr:J9H1DS4gfLBnGCtYGsdUcjCU |
MALICIOUS
Drops the executable file immediately after the start
- bsod.exe (PID: 3968)
Changes the autorun value in the registry
- taskmgr.exe (PID: 928)
SUSPICIOUS
Reads security settings of Internet Explorer
- bsod.exe (PID: 3968)
Reads the Internet Settings
- bsod.exe (PID: 3968)
- taskmgr.exe (PID: 928)
Executable content was dropped or overwritten
- iexpress.exe (PID: 4048)
Process drops legitimate windows executable
- iexpress.exe (PID: 4048)
INFO
Reads the computer name
- bsod.exe (PID: 3968)
Checks supported languages
- bsod.exe (PID: 3968)
Reads the machine GUID from the registry
- bsod.exe (PID: 3968)
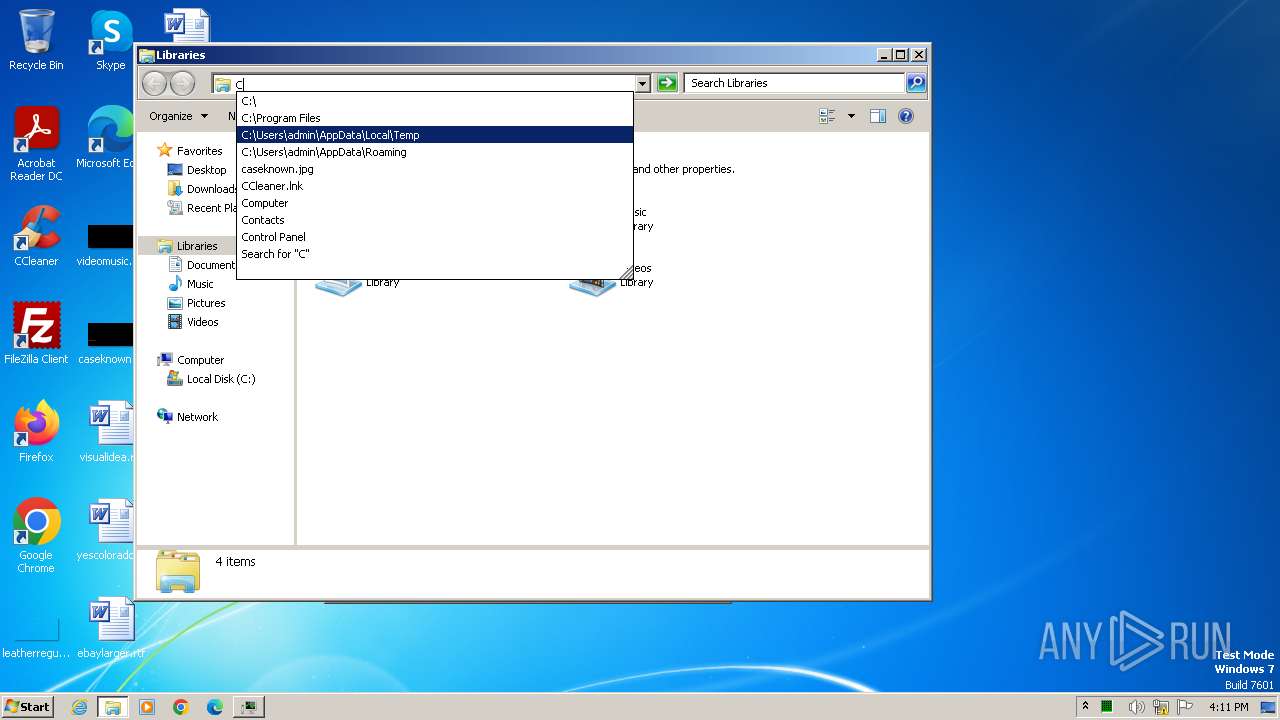
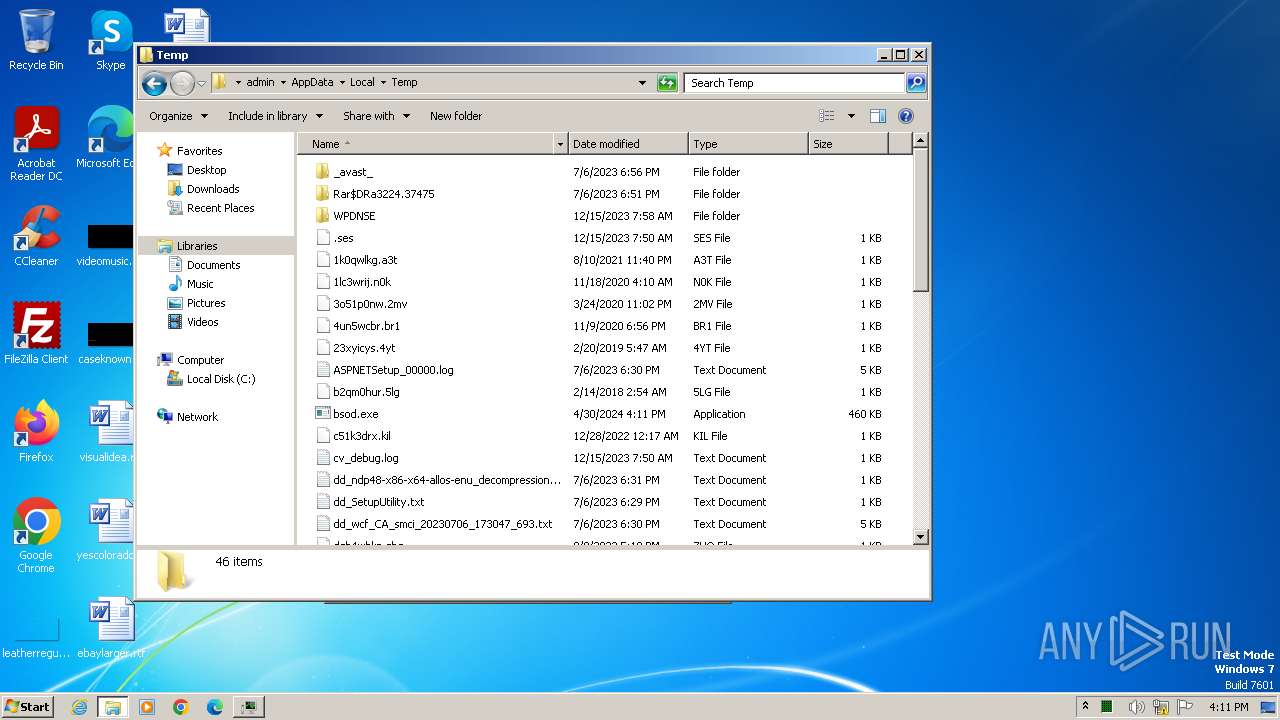
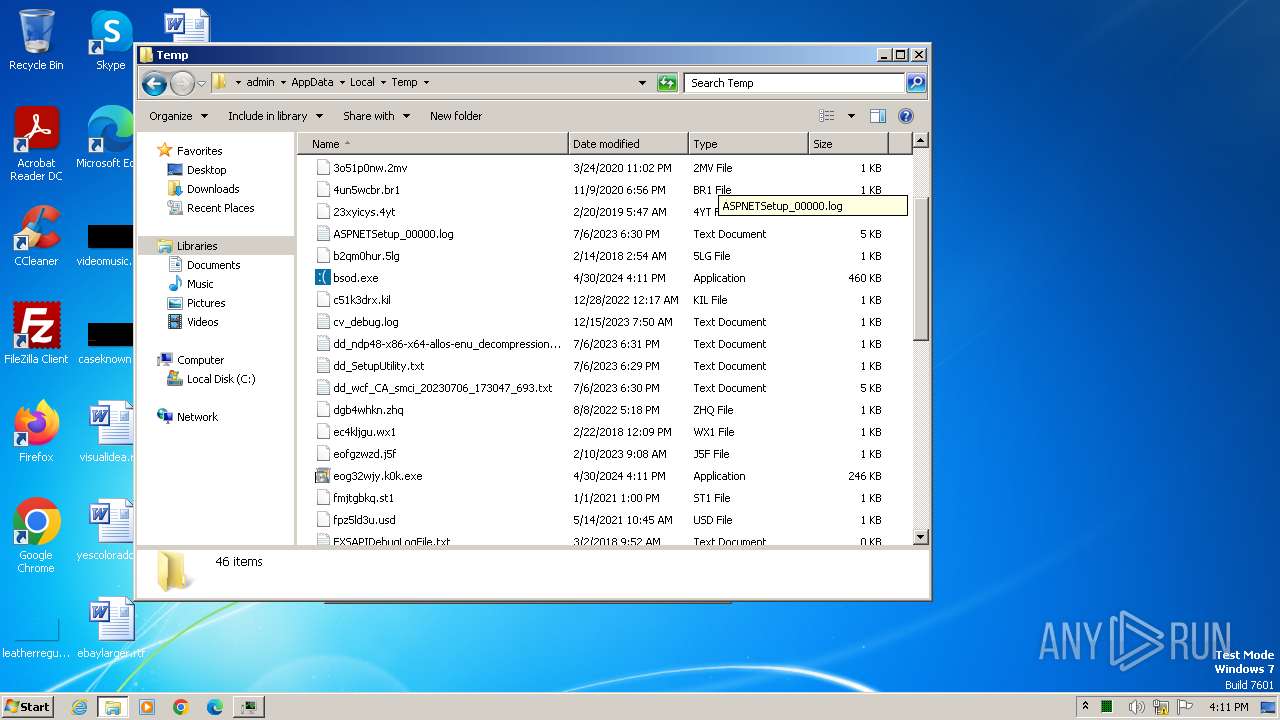
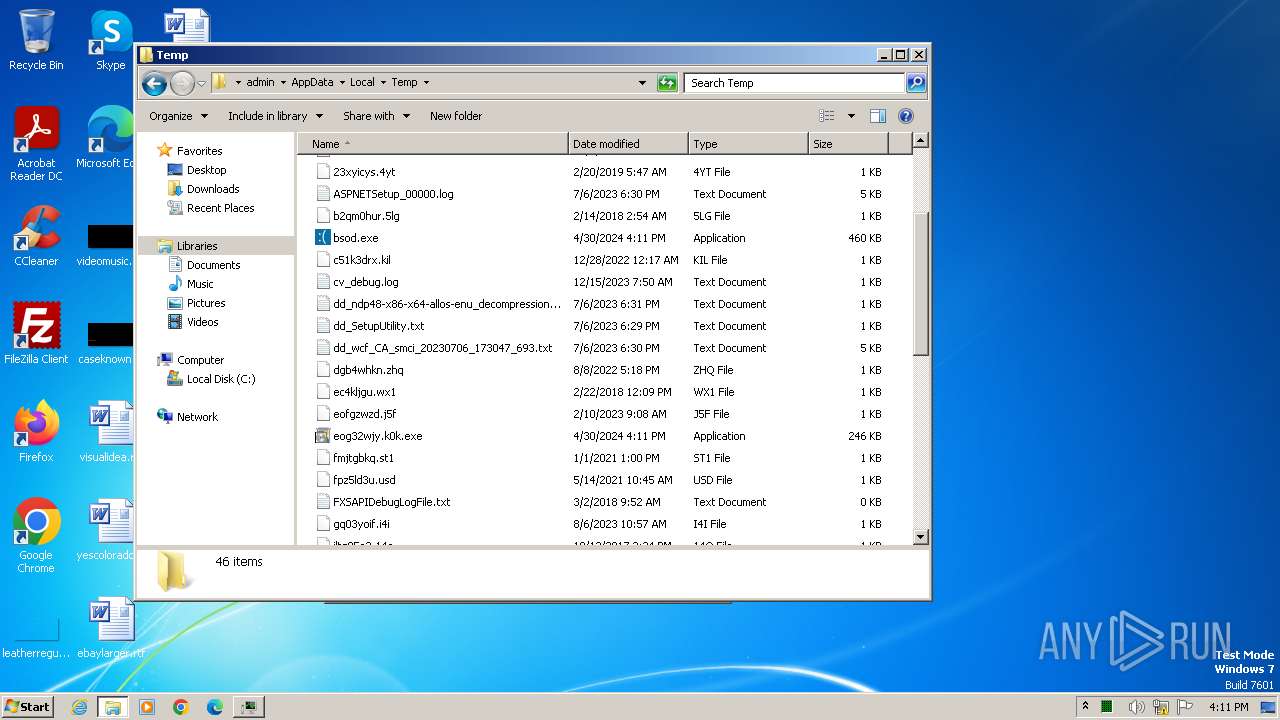
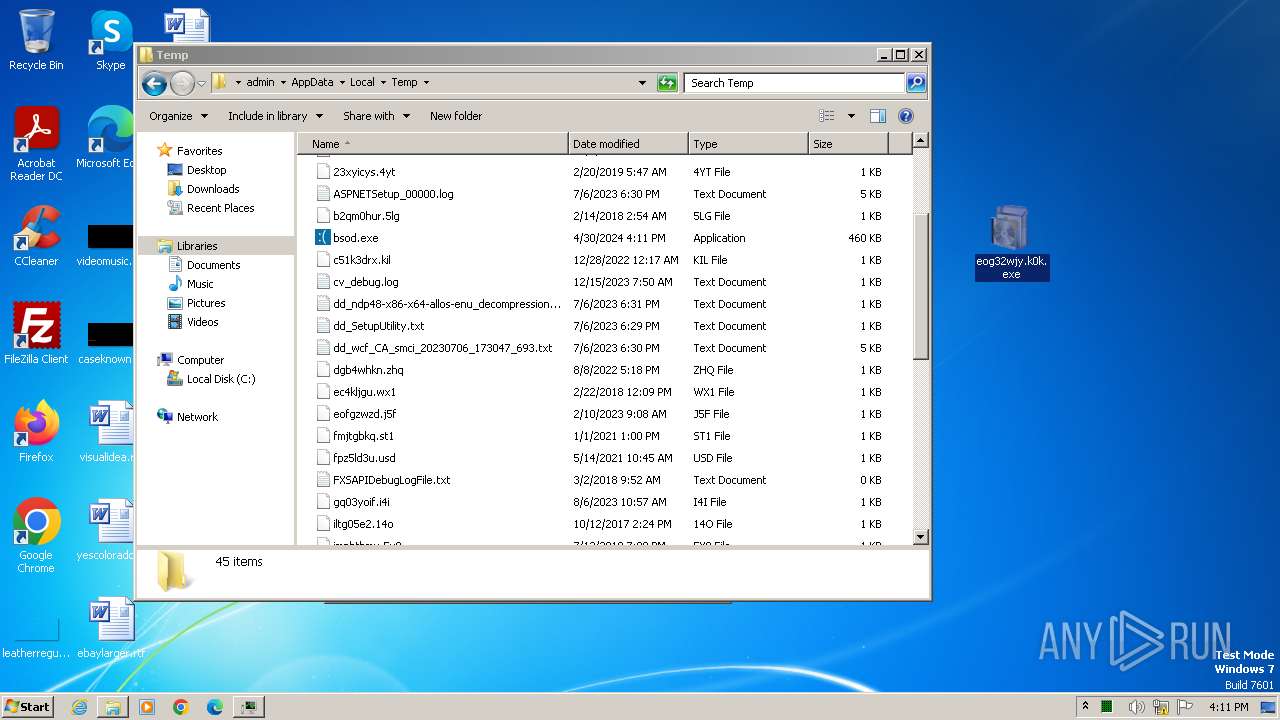
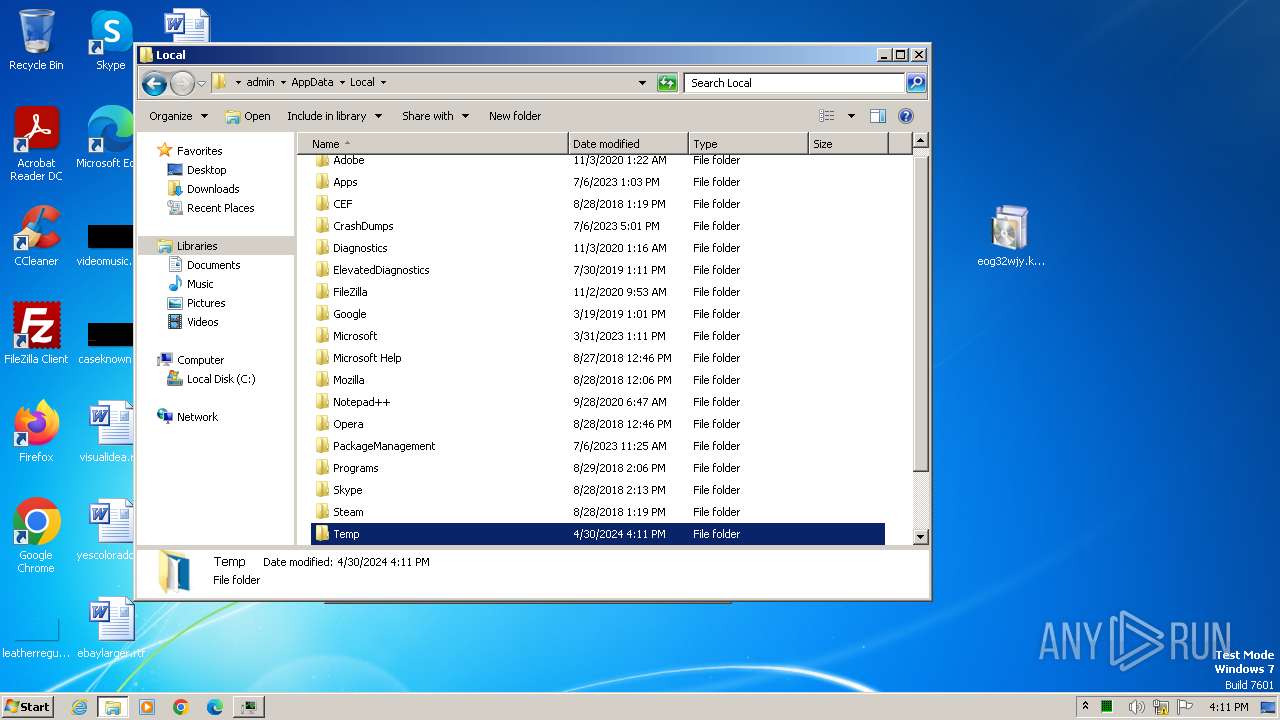
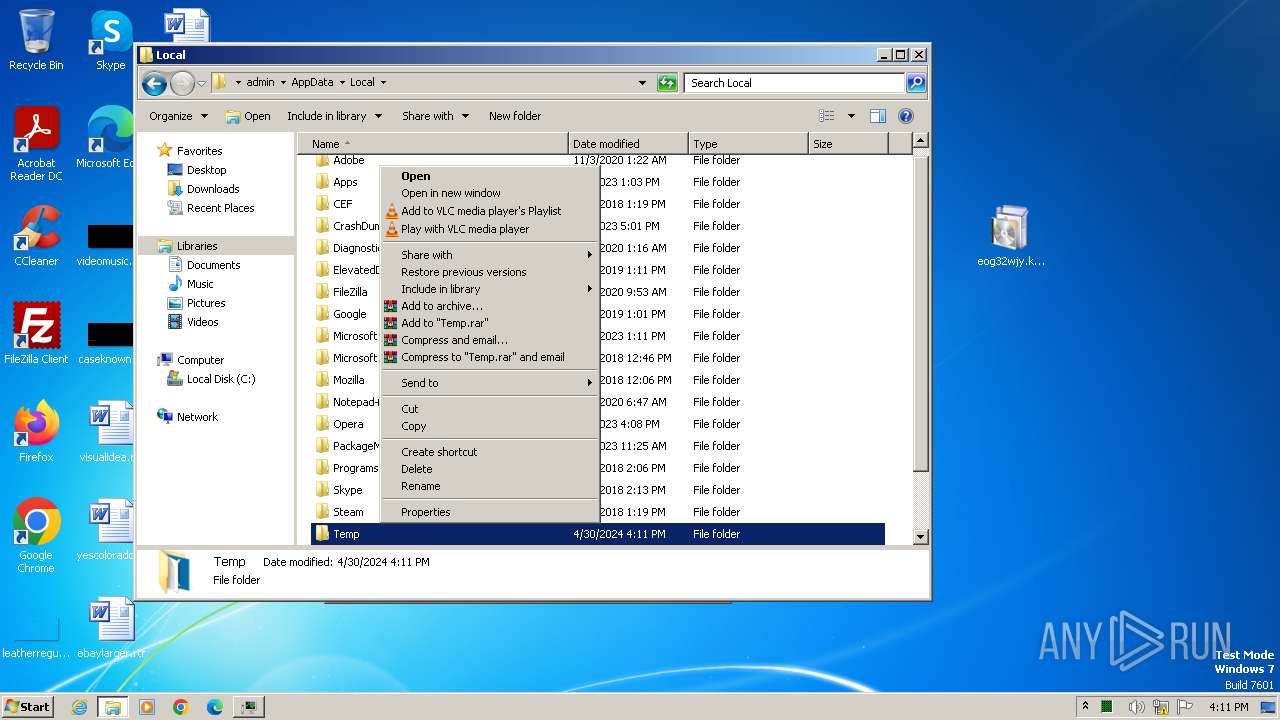
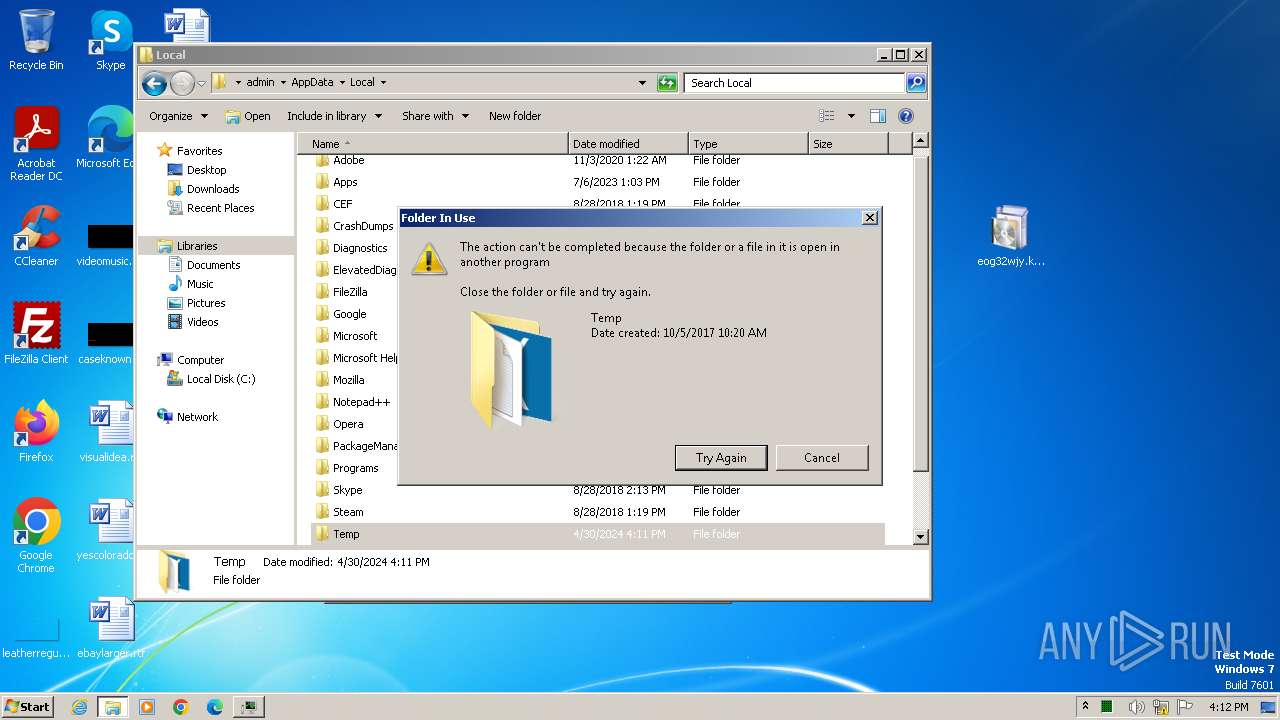
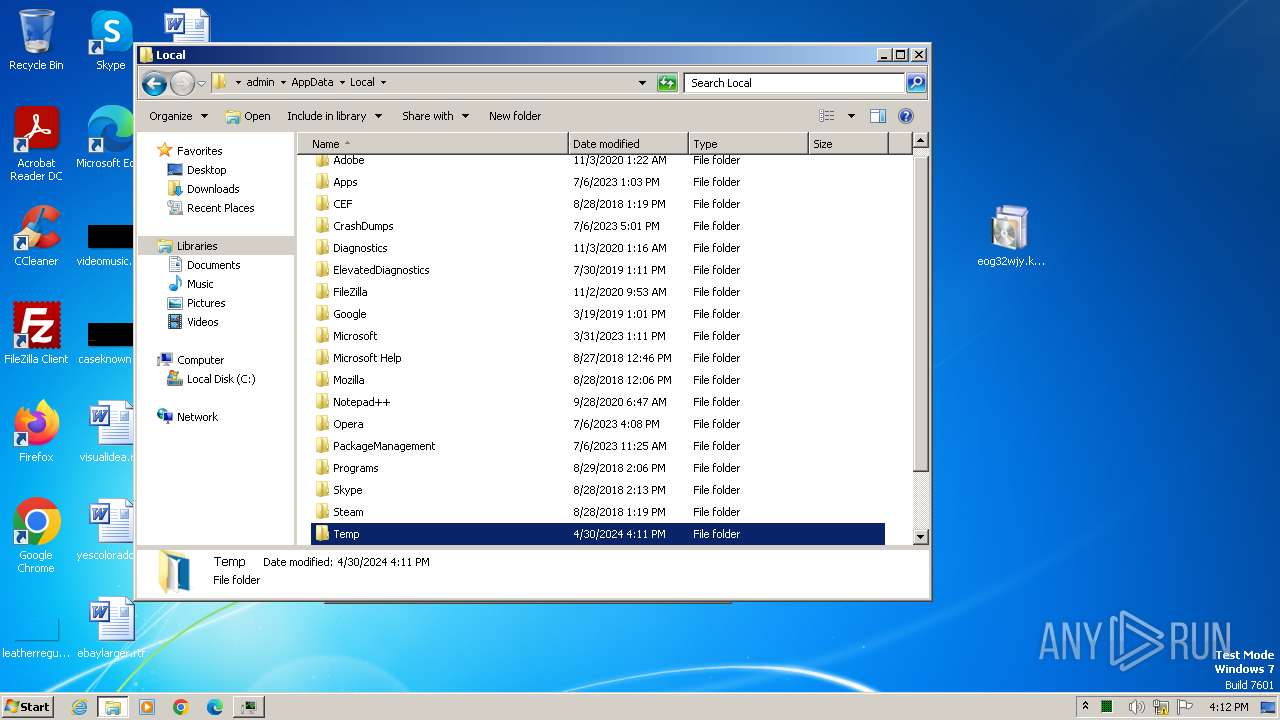
Create files in a temporary directory
- bsod.exe (PID: 3968)
- iexpress.exe (PID: 4048)
- makecab.exe (PID: 4056)
Drops the executable file immediately after the start
- iexpress.exe (PID: 4048)
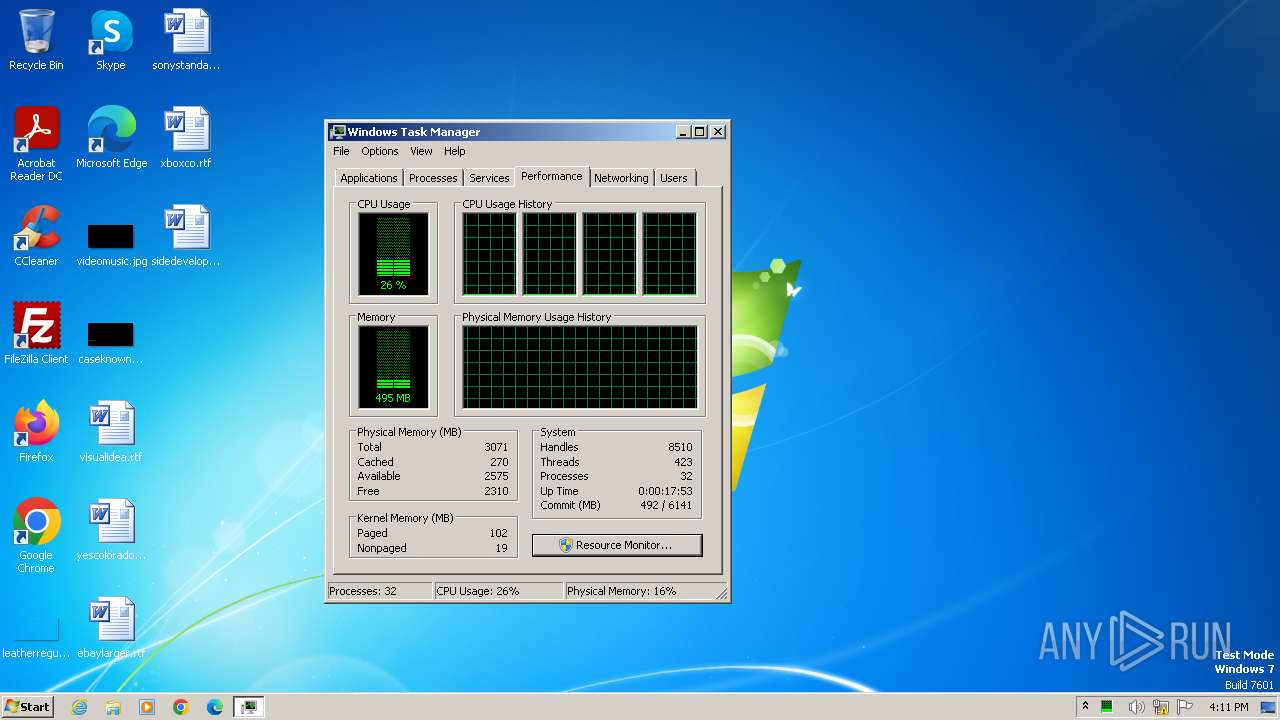
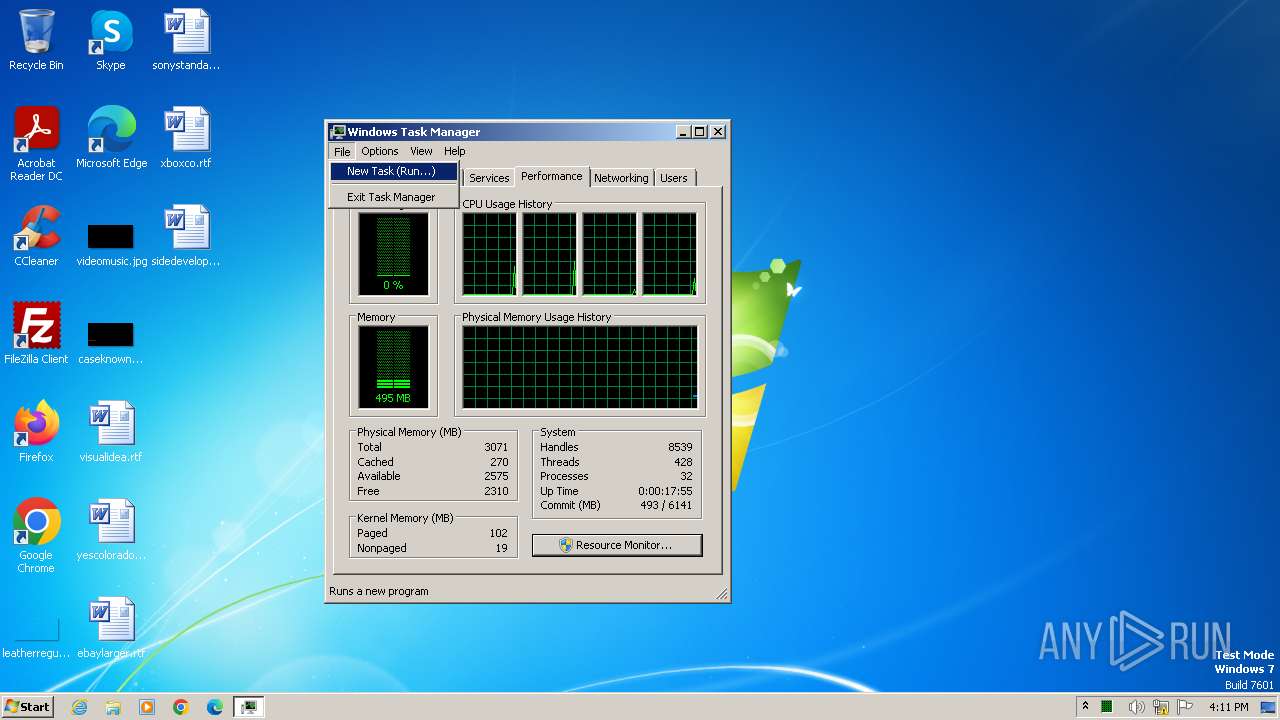
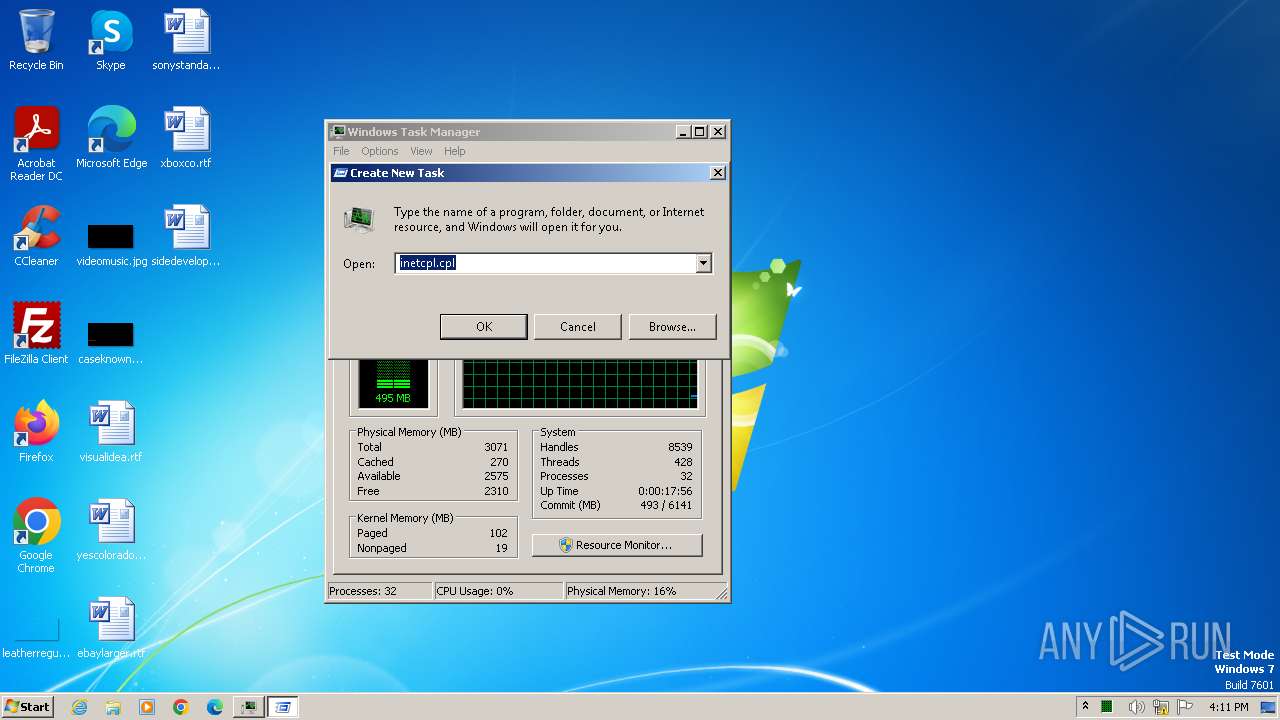
Manual execution by a user
- taskmgr.exe (PID: 928)
Reads security settings of Internet Explorer
- taskmgr.exe (PID: 928)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (63.1) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (23.8) |
| .dll | | | Win32 Dynamic Link Library (generic) (5.6) |
| .exe | | | Win32 Executable (generic) (3.8) |
| .exe | | | Generic Win/DOS Executable (1.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2024:04:29 17:14:25+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32 |
| LinkerVersion: | 48 |
| CodeSize: | 356352 |
| InitializedDataSize: | 113664 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x58f7a |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 3.4.0.0 |
| ProductVersionNumber: | 3.4.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
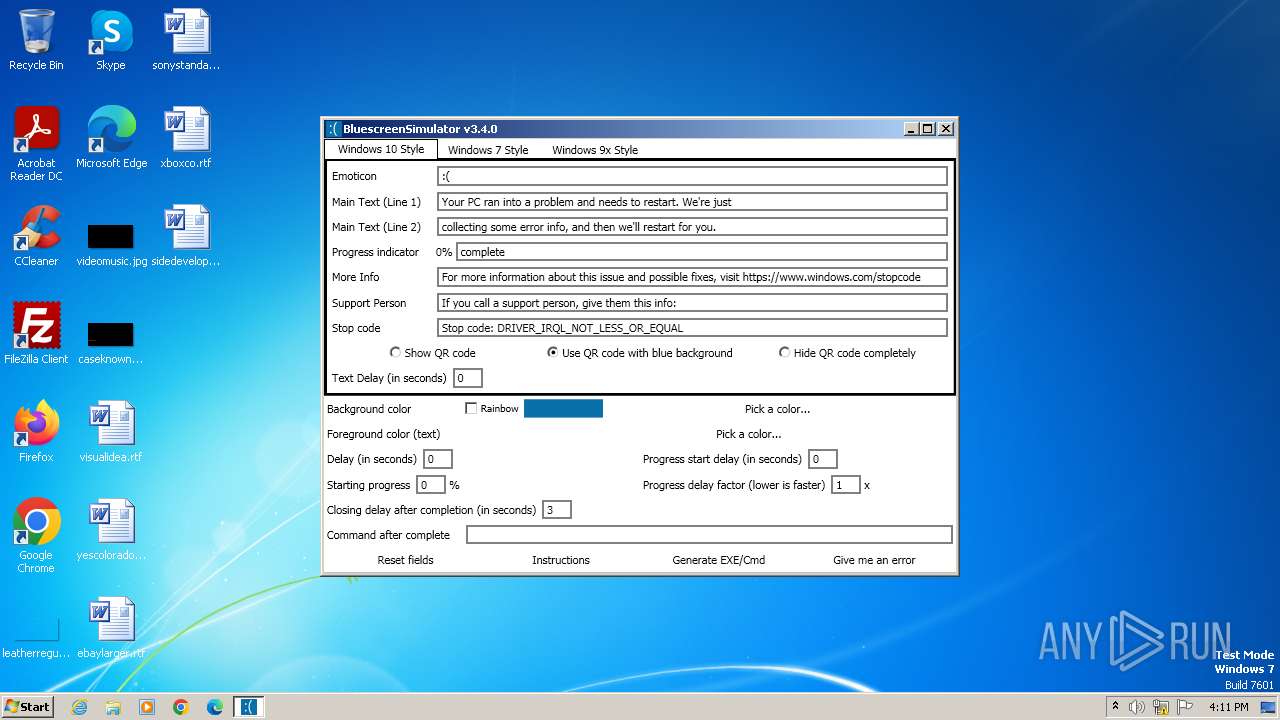
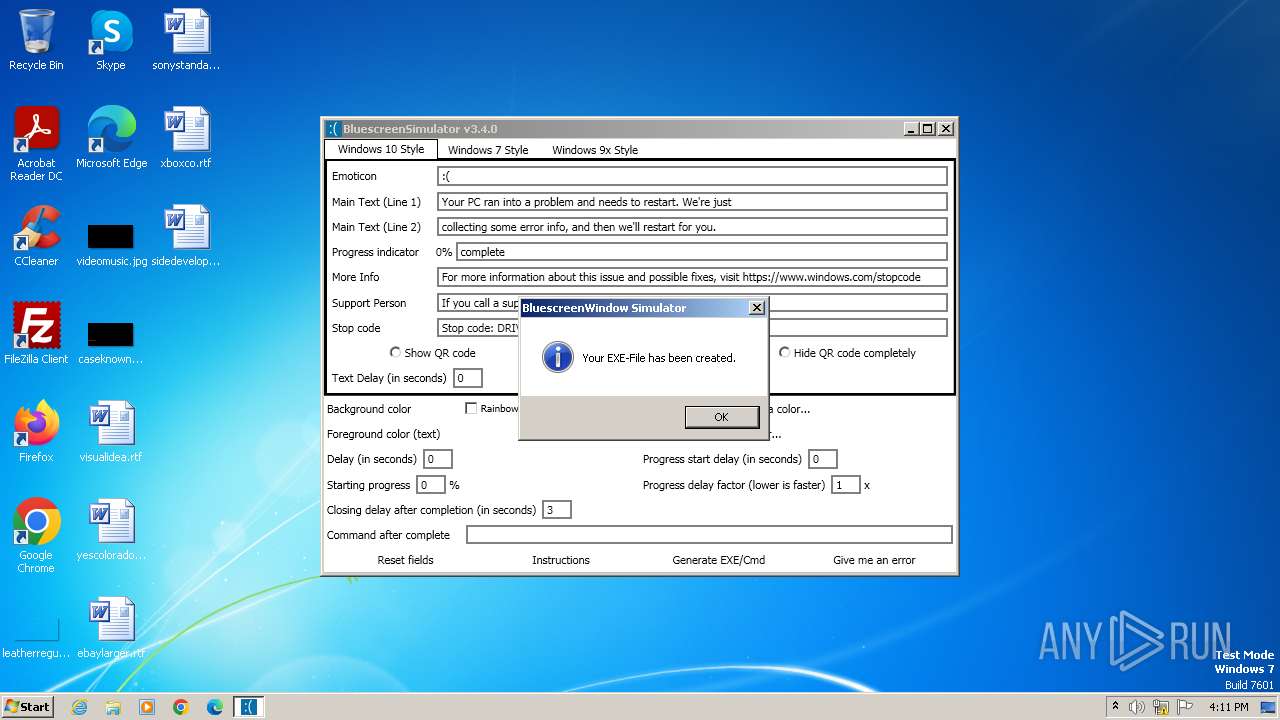
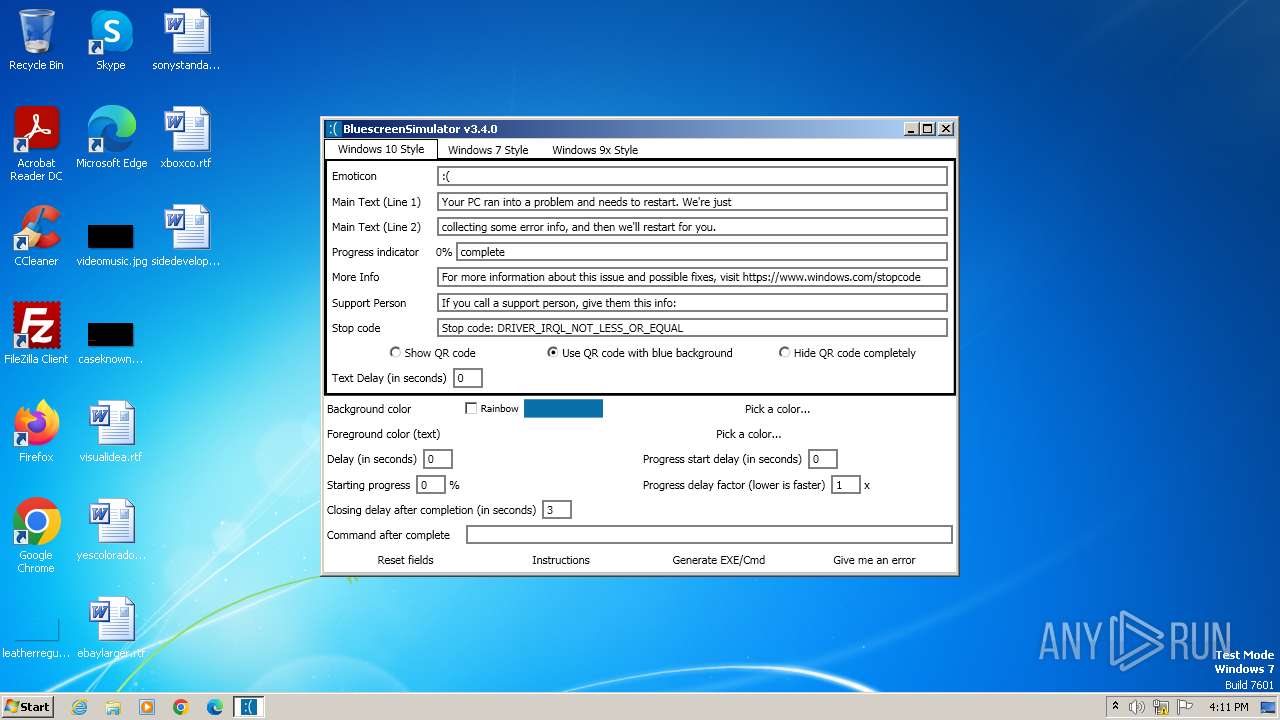
| Comments: | A program to simulate BSODs with lots of features. |
| CompanyName: | FlyTech Videos |
| FileDescription: | BluescreenSimulator |
| FileVersion: | 3.4.0 |
| InternalName: | BluescreenSimulator.exe |
| LegalCopyright: | © FlyTech Videos 2019 |
| LegalTrademarks: | - |
| OriginalFileName: | BluescreenSimulator.exe |
| ProductName: | BluescreenSimulator |
| ProductVersion: | 3.4.0 |
| AssemblyVersion: | 3.4.0.0 |
Total processes
39
Monitored processes
5
Malicious processes
1
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 928 | "C:\Windows\system32\taskmgr.exe" /4 | C:\Windows\System32\taskmgr.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Task Manager Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2036 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | taskmgr.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3968 | "C:\Users\admin\AppData\Local\Temp\bsod.exe" | C:\Users\admin\AppData\Local\Temp\bsod.exe | — | explorer.exe | |||||||||||
User: admin Company: FlyTech Videos Integrity Level: MEDIUM Description: BluescreenSimulator Exit code: 0 Version: 3.4.0 Modules
| |||||||||||||||
| 4048 | "C:\Windows\system32\iexpress.exe" /N C:\Users\admin\AppData\Local\Temp\\optionfile.SED | C:\Windows\System32\iexpress.exe | bsod.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Wizard Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
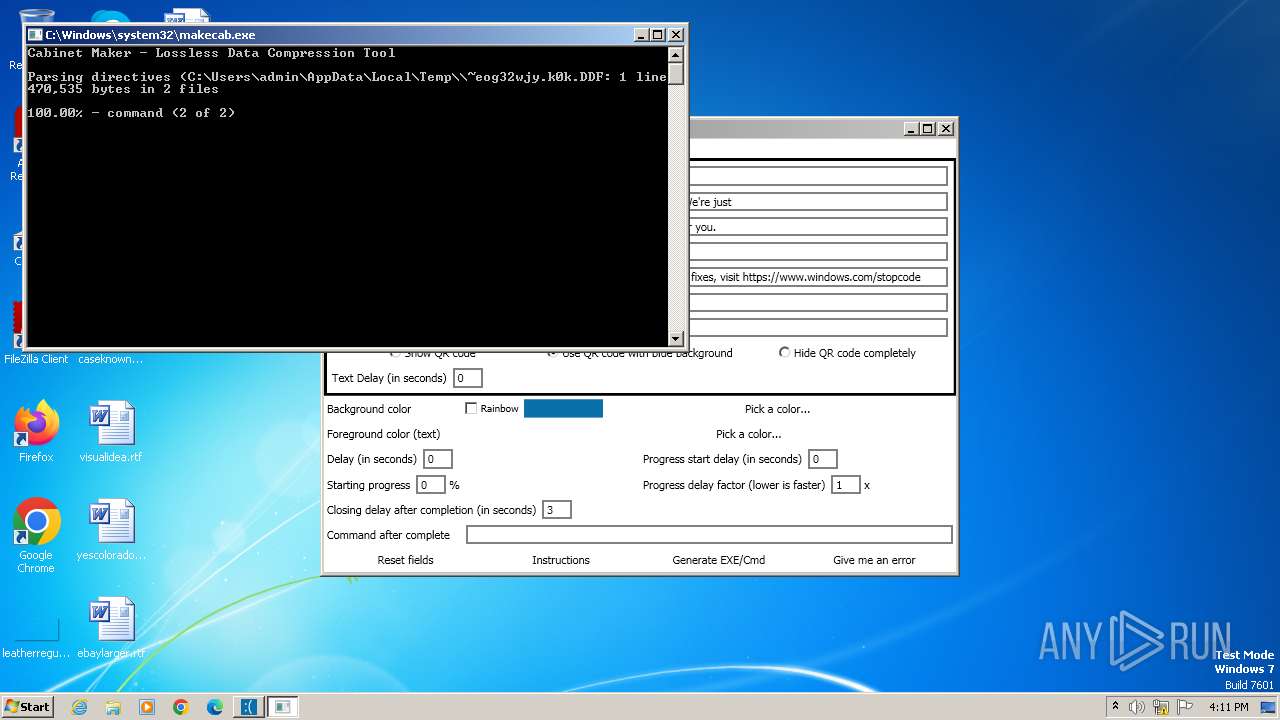
| 4056 | C:\Windows\system32\makecab.exe /f "C:\Users\admin\AppData\Local\Temp\\~eog32wjy.k0k.DDF" | C:\Windows\System32\makecab.exe | — | iexpress.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft® Cabinet Maker Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
3 648
Read events
3 570
Write events
78
Delete events
0
Modification events
| (PID) Process: | (3968) bsod.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3968) bsod.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3968) bsod.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3968) bsod.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (3968) bsod.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: bsod.exe | |||
| (PID) Process: | (3968) bsod.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\CTF\CUAS\DefaultCompositionWindow |
| Operation: | write | Name: | Left |
Value: 0 | |||
| (PID) Process: | (3968) bsod.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\CTF\CUAS\DefaultCompositionWindow |
| Operation: | write | Name: | Top |
Value: 0 | |||
| (PID) Process: | (928) taskmgr.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (928) taskmgr.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (928) taskmgr.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
Executable files
3
Suspicious files
4
Text files
5
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4056 | makecab.exe | C:\Users\admin\AppData\Local\Temp\cab_4056_8 | — | |
MD5:— | SHA256:— | |||
| 4056 | makecab.exe | C:\Users\admin\AppData\Local\Temp\inf_4056_2 | text | |
MD5:CB492B7DF9B5C170D7C87527940EFF3B | SHA256:DBA5166AD9DB9BA648C1032EBBD34DCD0D085B50023B839EF5C68CA1DB93A563 | |||
| 4056 | makecab.exe | C:\Users\admin\AppData\Local\Temp\~eog32wjy.k0k.RPT | text | |
MD5:79497AB071277A627882BA1DAFB775B0 | SHA256:DF83A7678884E68D8A89C9441CA11331EF00AAD70278C9D36EF6B3770D4763AD | |||
| 4056 | makecab.exe | C:\Users\admin\AppData\Local\Temp\~eog32wjy.k0k_LAYOUT.INF | binary | |
MD5:C13952E17D8850FB9A839968E4EA398A | SHA256:11AD75E008BE0B4855C1A93A963D1562FD9F4523E3F2E627DE50A1F4360E52DE | |||
| 4056 | makecab.exe | C:\Users\admin\AppData\Local\Temp\cab_4056_9 | binary | |
MD5:46DB99ED5D0ECC95F6444ACD52FAC1F2 | SHA256:99C293C16AA1FC1793C1E9BE8CEC3C40DA9CC3F9769EA49A67FCB6EF648E1420 | |||
| 4056 | makecab.exe | C:\Users\admin\AppData\Local\Temp\cab_4056_7 | binary | |
MD5:263F56281095B63906DCA191E5823E1C | SHA256:7DC5AAD4702B1DA72D5E9246363B8E7523D153B7E1CA05BFC140D0D699778914 | |||
| 4056 | makecab.exe | C:\Users\admin\AppData\Local\Temp\inf_4056_4 | text | |
MD5:304027E561744207EFE918F906CE1152 | SHA256:555A7AC39CE07E85A6AD89E4A1D74B29906D35A89836318D67AAC15FB5F7FF05 | |||
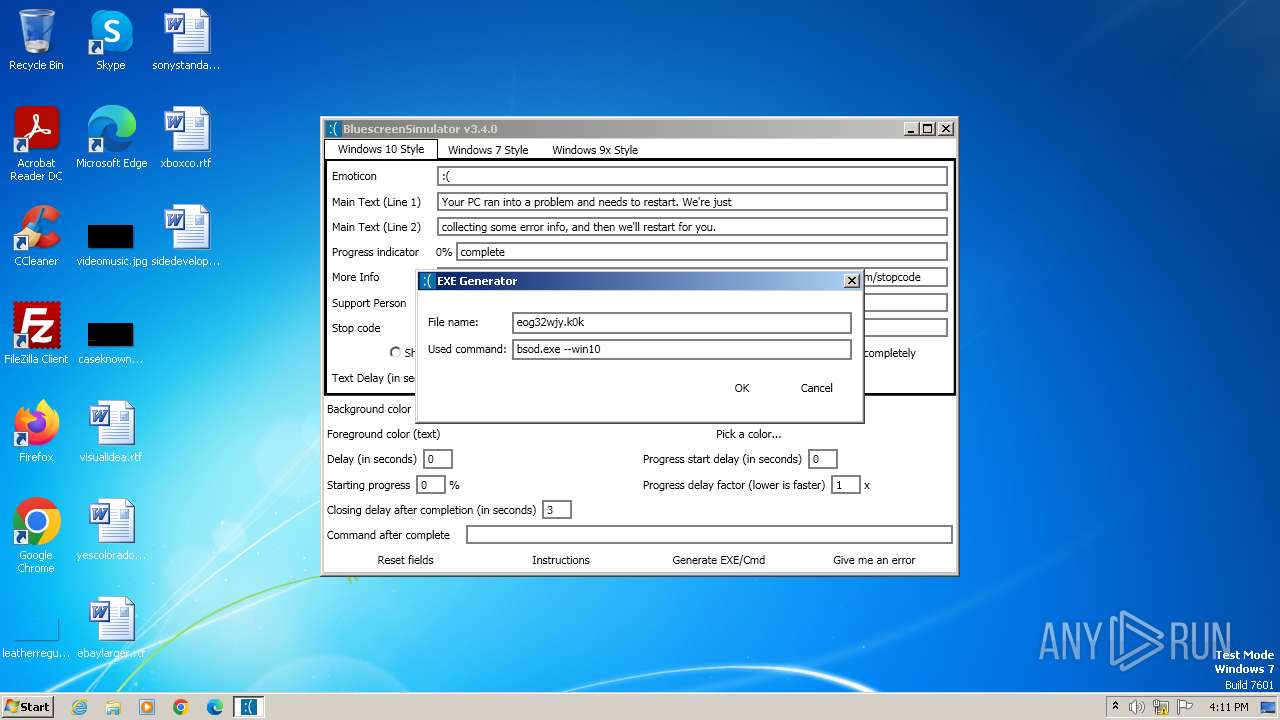
| 4048 | iexpress.exe | C:\Users\admin\AppData\Local\Temp\eog32wjy.k0k.exe | executable | |
MD5:6A92CEC8532056791C6832B2725D170D | SHA256:3D0E2C0CCFEEA27D4B7414B9DA0DE4707C2087134D3FF8AFE6FF59522A98E137 | |||
| 4048 | iexpress.exe | C:\Users\admin\AppData\Local\Temp\RCX4D95.tmp | executable | |
MD5:8C3EBB03AFF5DEDA2F5DBF04A5E5DD94 | SHA256:F90ACDC4BD816A9B86758B884FEAAB55C52503879EFC4DF4EDC09D359CCBFB09 | |||
| 3968 | bsod.exe | C:\Users\admin\AppData\Local\Temp\command | text | |
MD5:A8BD38325EC492A0DEB13A7D930F1747 | SHA256:41A7139792997581812967E329A84E16FB9683CA7AAAF074153C37654555A835 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
4
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 224.0.0.252:5355 | — | — | — | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1088 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |